The right preparation can turn an interview into an opportunity to showcase your expertise. This guide to Recordkeeping and Data Management interview questions is your ultimate resource, providing key insights and tips to help you ace your responses and stand out as a top candidate.
Questions Asked in Recordkeeping and Data Management Interview
Q 1. Explain the difference between records management and data management.
While both records management and data management deal with information, they differ significantly in scope and focus. Think of it like this: data management is about the what and how of information, while records management is about the why and when.
Data management encompasses the overall lifecycle of data, from creation and storage to usage, analysis, and eventual disposal. It’s a broad field concerning data quality, accessibility, and security, regardless of its legal or business value. Examples include database administration, data warehousing, data mining, and business intelligence initiatives.
Records management, on the other hand, is a specialized subset focused on the creation, maintenance, use, and final disposition of records – information created or received in the course of business activities and having sufficient value to justify its retention. This is governed by legal, regulatory, and business requirements. Examples include managing contracts, financial documents, legal correspondence, and employee records, all of which must be preserved and accessed according to specific rules and regulations. Records management ensures the organization can meet its legal, regulatory, and business obligations while efficiently utilizing storage resources.
Q 2. Describe your experience with different recordkeeping systems (e.g., electronic, physical).
My experience spans both physical and electronic recordkeeping systems. In my previous role, I managed a large archive of physical files, implementing a robust filing system with detailed indexing and metadata to ensure efficient retrieval. This involved developing and enforcing strict protocols for handling, storage, and security of sensitive documents, including a comprehensive disaster recovery plan.
More recently, I’ve focused on electronic recordkeeping, overseeing the implementation and maintenance of a comprehensive electronic document management system (EDMS). This involved migrating legacy paper records into a digital format, implementing robust metadata schemas, and establishing access controls based on user roles and data sensitivity. I’ve also utilized cloud-based solutions for secure storage and backup, along with the implementation of automated workflows to streamline routine recordkeeping tasks. My experience includes working with various systems, such as SharePoint, M-Files, and others.
Q 3. How do you ensure data integrity and accuracy?
Data integrity and accuracy are paramount. I ensure this through a multi-faceted approach. First, I establish clear data governance policies defining data standards, naming conventions, and validation rules. This includes implementing data quality checks at every stage of the data lifecycle. For example, we use data validation rules in our forms to ensure data consistency.
Second, I employ robust data validation techniques such as checksums and data comparisons to identify inconsistencies or errors. Third, I leverage technology, including automated data cleansing and reconciliation tools, to identify and correct inaccurate or incomplete data. Lastly, I promote a culture of data quality through staff training and awareness programs, emphasizing the importance of accuracy in data entry and recordkeeping. Regular audits and data quality reports further reinforce these efforts. Think of it as building a house: a strong foundation of data governance leads to a sturdy and reliable structure.
Q 4. What are the key principles of information governance?
Information governance is the overall framework for managing information throughout its lifecycle. It encompasses several key principles:
- Compliance: Adhering to all relevant legal, regulatory, and industry standards.
- Availability: Ensuring authorized users can access the necessary information when needed.
- Integrity: Maintaining the accuracy and completeness of information.
- Confidentiality: Protecting sensitive information from unauthorized access.
- Retention: Establishing clear policies for how long information must be retained.
- Disposition: Defining procedures for secure and compliant disposal of information.
- Accountability: Clearly defining roles and responsibilities for information management.
These principles work together to create a robust system that manages risk, ensures compliance, and supports effective decision-making. Think of it as a comprehensive roadmap for navigating the complex world of information.
Q 5. Explain your experience with metadata creation and management.
Metadata is critical for effective information retrieval and management. My experience includes developing and implementing metadata schemas tailored to specific record types and business needs. For instance, when implementing our EDMS, we created metadata fields for document type, author, creation date, keywords, and subject matter to aid in searching and retrieval. We also used controlled vocabularies to ensure consistency and accuracy.
I’ve also used metadata to automate workflows, such as automatically routing documents based on predefined metadata values. For example, all contracts with a specific value are automatically routed to the legal department. Furthermore, I’ve managed metadata through the use of enterprise metadata repositories and implemented metadata quality control measures to ensure accuracy and consistency throughout the organization. Effective metadata management is crucial for ensuring that information is easily discoverable, searchable, and usable.
Q 6. How do you handle sensitive data and maintain confidentiality?
Handling sensitive data requires a layered approach to security. This includes implementing strict access controls using role-based permissions, encryption both in transit and at rest, and regular security audits. We utilize data loss prevention (DLP) tools to monitor and prevent sensitive data from leaving the organization’s controlled environment.
Employee training on data security best practices is also a vital part of our strategy. We emphasize the importance of password security, safe handling of sensitive information, and reporting any suspicious activity. Furthermore, we comply with all relevant privacy regulations, such as GDPR and CCPA, ensuring compliance through regular reviews and updates to our policies and procedures. Data security is not just a technical issue; it’s a cultural one that requires commitment at every level.
Q 7. Describe your experience with data retention policies and procedures.
Data retention policies are crucial for legal compliance, risk mitigation, and efficient resource management. My experience includes developing and implementing retention policies that align with legal, regulatory, and business requirements. This includes conducting thorough assessments of record types and their retention requirements, considering factors like legal obligations, business needs, and storage costs.
For instance, we may retain financial records for seven years due to tax regulations, while employee personnel files might be kept for a shorter duration post-employment. The policies are documented and communicated clearly to all stakeholders. I’ve also implemented procedures for the timely and secure disposition of records after the retention period expires, adhering to appropriate destruction methods. Regular reviews and updates ensure policies stay current and relevant, reflecting changing legal and business landscapes.
Q 8. How do you prioritize competing demands in managing records and data?
Prioritizing competing demands in records and data management requires a structured approach. I use a framework that combines urgency, importance, and risk. Think of it like a triage system in a hospital – some cases are critical, others require immediate attention, and some can wait.
- Urgency: Tasks with immediate deadlines, such as regulatory compliance reports or urgent data requests, take precedence.
- Importance: Strategic initiatives, like implementing a new data governance framework or migrating to a new system, are vital for long-term success and are prioritized accordingly.
- Risk: Tasks with high potential negative consequences (e.g., data breaches, non-compliance penalties) are given top priority regardless of urgency or importance.
I utilize project management tools to track tasks, assign priorities, and monitor progress. This allows for a clear visualization of workload and resource allocation, enabling efficient management of competing demands. For example, if a critical security patch requires immediate deployment, even if it disrupts a planned data migration task, the security patch takes precedence due to the significantly higher risk.
Q 9. Explain your experience with data migration projects.
I have extensive experience in data migration projects, having led and participated in several large-scale migrations. My approach focuses on meticulous planning, rigorous testing, and comprehensive communication.
- Planning: This involves a detailed assessment of the source and target systems, defining migration scope, developing a detailed migration plan with timelines and milestones, and identifying potential risks and mitigation strategies. For instance, in a recent migration, we used data profiling tools to understand data quality issues in the legacy system before migration, allowing us to address potential data inconsistencies proactively.
- Testing: We employ rigorous testing methodologies, including unit testing, integration testing, and user acceptance testing (UAT), to ensure data integrity and system functionality. Automated testing tools are often integrated to streamline and accelerate this process.
- Communication: Throughout the process, I maintain open communication with stakeholders, keeping them informed of progress, challenges, and any potential impacts. Regular updates and status reports help ensure everyone is aligned and any issues are addressed promptly.
A recent project involved migrating a client’s 10-year-old customer database to a cloud-based solution. The meticulous planning and testing prevented data loss and ensured a smooth transition, resulting in improved data accessibility and enhanced system performance.
Q 10. How do you ensure compliance with relevant regulations (e.g., GDPR, HIPAA)?
Ensuring compliance with regulations like GDPR and HIPAA is paramount. My approach is proactive, involving a multi-faceted strategy.
- Policy Development and Implementation: We develop and implement comprehensive data governance policies and procedures aligned with relevant regulations. This includes policies on data collection, storage, processing, access control, and data deletion.
- Data Mapping and Inventory: We conduct thorough data mapping exercises to identify all personal data and sensitive information, ensuring we understand where it resides and how it’s processed. This creates a comprehensive data inventory critical for compliance audits.
- Privacy Impact Assessments (PIAs): For high-risk data processing activities, we conduct PIAs to proactively identify and mitigate potential privacy risks.
- Training and Awareness: We provide regular training to employees on data privacy and compliance requirements, ensuring everyone understands their responsibilities and the importance of data protection.
- Data Breach Response Plan: We have a well-defined data breach response plan in place, outlining steps to be taken in the event of a breach, including notification procedures and remediation strategies.
For instance, when dealing with HIPAA compliance, we strictly adhere to access control measures, ensuring only authorized personnel have access to protected health information (PHI), utilizing role-based access control (RBAC) and encryption.
Q 11. Describe your experience with data backup and recovery strategies.
Robust data backup and recovery strategies are crucial for business continuity and data protection. My approach incorporates several key elements:
- 3-2-1 Backup Strategy: We employ the 3-2-1 rule – maintaining three copies of data on two different media types, with one copy stored offsite. This ensures data redundancy and protection against data loss due to hardware failures, natural disasters, or cyberattacks.
- Regular Backups: Backups are scheduled regularly, with the frequency determined by the criticality of the data. For critical data, we might use continuous data protection (CDP) methods.
- Testing and Validation: We regularly test the backup and recovery processes to ensure their effectiveness. This includes restoring a subset of data to verify its integrity and the speed of recovery.
- Versioning and Retention Policies: We implement versioning to track changes over time and establish data retention policies to manage storage space and comply with legal and regulatory requirements.
For example, in a recent project, we implemented a cloud-based backup solution using a geographically dispersed architecture to ensure high availability and disaster recovery capabilities. This allowed us to recover from a ransomware attack with minimal data loss and downtime.
Q 12. How do you identify and resolve data quality issues?
Identifying and resolving data quality issues is an iterative process. It begins with defining what constitutes ‘good’ data and then implementing processes and tools to identify and rectify issues.
- Data Profiling: Using data profiling tools, we analyze data to identify anomalies, inconsistencies, and missing values. This provides a baseline understanding of data quality.
- Data Cleansing: We use various techniques to cleanse the data, such as correcting errors, standardizing formats, and removing duplicates.
- Data Validation: We implement data validation rules to ensure data integrity throughout the data lifecycle. This includes checks for data type, range, and format compliance.
- Root Cause Analysis: When recurring quality issues are identified, we conduct root cause analysis to understand the underlying causes and implement preventive measures to address the issues at their source.
For example, we might discover inconsistent data entry in a customer address field. We could then cleanse the data by standardizing the format and implementing data validation rules to prevent future inconsistencies.
Q 13. Explain your understanding of data warehousing and business intelligence.
Data warehousing is the process of storing and managing large volumes of data from various sources to support business intelligence (BI) activities. BI involves using data analysis techniques to extract insights and support decision-making.
A data warehouse is essentially a central repository of historical data, structured for efficient querying and analysis. It integrates data from various operational systems, often transforming and cleaning it in the process. This cleaned data is then used for reporting, analysis, and decision support. BI tools then allow users to interact with the data warehouse, creating dashboards, reports, and visualizations to help understand business trends and performance.
For example, a retail company might use a data warehouse to store sales data, customer information, and inventory data from various sources. BI tools can then be used to analyze this data to identify best-selling products, customer segmentation patterns, and predict future sales trends, guiding inventory management and marketing strategies.
Q 14. How do you use data analysis techniques to improve recordkeeping processes?
Data analysis plays a crucial role in improving recordkeeping processes. By analyzing data about record creation, access, storage, and disposition, we can identify inefficiencies, bottlenecks, and areas for improvement.
- Record Access Patterns: Analyzing access logs helps to understand which records are accessed most frequently, allowing us to optimize storage and retrieval methods. Frequently accessed records could be moved to faster storage.
- Record Retention: Analyzing record usage patterns helps to refine retention policies, ensuring compliance and efficient storage management. Records that are rarely accessed or no longer needed can be archived or destroyed according to established policies.
- Workflow Optimization: Data analysis can pinpoint bottlenecks in recordkeeping workflows, allowing for process re-engineering to streamline operations and improve efficiency. For example, identifying repetitive manual tasks that could be automated.
- Risk Assessment: Analyzing data on record breaches or security incidents can help identify vulnerabilities and improve data security measures.
For instance, if analysis reveals a high volume of rejected records due to incomplete metadata, we can improve the data entry process and train staff to ensure better data quality from the outset. This proactive approach minimizes costly rework and improves the overall efficiency of the recordkeeping system.
Q 15. Describe your experience with data visualization tools.
Data visualization is crucial for transforming raw data into actionable insights. My experience spans several tools, including Tableau, Power BI, and Qlik Sense. I’m proficient in creating various chart types – bar charts, line graphs, scatter plots, heatmaps – depending on the data and the insights we need to extract. For instance, in a previous role, we used Tableau to visualize customer churn rates, identifying key factors contributing to customer attrition. This allowed us to implement targeted retention strategies, resulting in a 15% reduction in churn within six months. I also have experience with creating interactive dashboards, allowing stakeholders to explore data dynamically and drill down into specifics.
Beyond the technical aspects, I prioritize clear and concise visualizations. A well-designed visualization should tell a story, immediately communicating key findings without requiring extensive explanation. I always consider the audience and tailor the visualization to their understanding and needs.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. How do you manage large volumes of data effectively?
Managing large datasets effectively requires a multi-faceted approach. It begins with a robust data governance framework that defines data standards, quality checks, and retention policies. This framework ensures data consistency and accuracy. Then, I leverage technologies like cloud storage (AWS S3, Azure Blob Storage) for scalable storage, and database management systems (SQL Server, PostgreSQL) for efficient data processing and querying. For extremely large datasets, I utilize big data technologies like Hadoop and Spark for distributed processing.
Furthermore, data deduplication and compression techniques significantly reduce storage needs and improve performance. Regular data cleansing is vital to remove inconsistencies and inaccuracies. Finally, I employ data sampling techniques when necessary, focusing analysis on representative subsets of the data for quicker insights without sacrificing accuracy in a statistically significant manner. For example, I once managed a dataset exceeding 10 terabytes by implementing a tiered storage approach, archiving less frequently accessed data to cheaper storage options.
Q 17. How do you collaborate with other departments to ensure effective data management?
Effective data management necessitates strong cross-departmental collaboration. I build relationships with key stakeholders in different departments—marketing, sales, finance, etc.—to understand their data needs and ensure data quality aligns with their requirements. This often involves regular meetings, workshops, and the creation of shared data dictionaries to define key terms and ensure everyone is working with the same definitions.
I advocate for data governance committees where representatives from each department can collaborate on data policies, standards, and resolution of data-related disputes. Using collaborative platforms like Microsoft Teams or SharePoint enables efficient document sharing, feedback, and tracking of data-related projects. Clear communication and a shared understanding of data governance principles are fundamental to success.
For example, in one project, I worked with the marketing team to develop a standardized system for collecting customer data, improving the accuracy and consistency of our marketing analytics.
Q 18. Explain your experience with data security best practices.
Data security is paramount. My approach involves implementing a multi-layered security strategy incorporating various best practices. This includes: access control using role-based permissions, data encryption both in transit and at rest, regular security audits and vulnerability assessments, and robust incident response planning. I’m familiar with various security frameworks, such as NIST Cybersecurity Framework and ISO 27001.
I champion the principle of least privilege – granting users only the access necessary to perform their job duties. Data loss prevention (DLP) tools are vital in monitoring and preventing sensitive data from leaving the organization’s control. Regular employee training on security awareness is crucial to mitigate human error, a major source of security breaches. We also maintain detailed audit logs to track all data access and modifications.
For example, in a previous role, I helped implement multi-factor authentication, significantly reducing the risk of unauthorized access.
Q 19. Describe your experience with implementing and maintaining a records management system.
I have extensive experience implementing and maintaining records management systems (RMS). This includes selecting appropriate software based on organizational needs (e.g., SharePoint, OpenText, M-Files), designing metadata schemas to effectively categorize and retrieve records, and developing comprehensive retention and disposition schedules that comply with legal and regulatory requirements. The implementation process involves careful planning, user training, and change management to ensure a smooth transition.
Ongoing maintenance includes regular system backups, performance monitoring, and updates to accommodate changing business needs and evolving regulations. I’ve worked with both cloud-based and on-premise RMS solutions, understanding the pros and cons of each approach. I also have experience with integrating the RMS with other enterprise systems to streamline workflows and improve data accessibility.
One project involved migrating a legacy paper-based recordkeeping system to a cloud-based RMS. This involved digitizing thousands of documents, implementing a robust metadata schema, and training staff on the new system. The result was improved efficiency, reduced storage costs, and enhanced accessibility to records.
Q 20. How do you assess the effectiveness of your recordkeeping and data management strategies?
Assessing the effectiveness of recordkeeping and data management strategies involves a combination of quantitative and qualitative measures. Quantitative measures include metrics such as data accuracy rates, data completeness, storage costs, and the time taken to retrieve information. Qualitative assessments involve user surveys, feedback sessions, and audits to assess user satisfaction and identify areas for improvement.
Key Performance Indicators (KPIs) are critical. We monitor KPIs such as the number of data breaches, the cost of non-compliance, and the time it takes to fulfill information requests. Regular reporting and analysis of these KPIs provide insights into the system’s overall performance and help identify areas where adjustments are needed. We also conduct periodic reviews of our retention policies to ensure they remain aligned with legal and business requirements.
For example, we might track the average time taken to respond to data requests. A consistent increase in this time indicates potential inefficiencies that need to be addressed.
Q 21. What are your preferred methods for data auditing?
Data auditing involves systematically examining data to ensure its accuracy, completeness, and compliance with regulations. My preferred methods include a combination of automated and manual techniques. Automated methods leverage tools and scripts to analyze large datasets, identifying anomalies and inconsistencies. For example, I might use SQL queries to identify duplicate records or missing values. Manual audits involve a more in-depth review of a sample of data records, validating data accuracy against source documents.
A risk-based approach is crucial. We prioritize audits on critical datasets and systems that pose the highest risk. The audit process typically includes defining audit objectives, selecting an appropriate sample of data, conducting the audit, documenting findings, and creating a remediation plan to address any identified issues. I ensure that the audit process is documented clearly and transparently, and that findings are communicated effectively to stakeholders.
For instance, I might use a combination of automated scripts to check for data integrity and manual reviews to validate compliance with specific regulations.
Q 22. Describe your experience with data modeling.
Data modeling is the process of creating a visual representation of data structures and their relationships. Think of it as designing a blueprint for your data before you build your database. My experience spans various modeling techniques, including entity-relationship diagrams (ERDs), which map out entities and their attributes and relationships, and UML diagrams for more complex systems. I’ve used these techniques in numerous projects, ranging from designing databases for customer relationship management (CRM) systems to developing data warehouses for business intelligence.
For instance, in a recent project involving a university’s student information system, I created an ERD to model the relationships between students, courses, instructors, and grades. This model clearly defined entities like ‘Student’ with attributes such as ‘StudentID’, ‘Name’, and ‘Address’, and their relationships, such as a ‘Student’ having many ‘Enrollments’ in ‘Courses’, each taught by an ‘Instructor’. This ensured data consistency and efficiency.
I also have experience with logical and physical data modeling, understanding the nuances of translating a conceptual model into a database-specific implementation. I’m proficient in tools like ERwin and Lucidchart to create and manage these models effectively.
Q 23. How do you handle conflicting data sources?
Conflicting data sources are a common challenge. My approach involves a multi-step process that prioritizes data quality and accuracy. First, I identify the sources of conflict. This often requires careful analysis of the data itself, understanding its origins and potential biases. Then, I assess the reliability and trustworthiness of each source. For instance, one source might be a primary record, like a formal document, while another might be derived data with potential inconsistencies.
Next, I employ reconciliation techniques. This could include using data quality rules, identifying and correcting erroneous data, or applying weighted averaging where appropriate. If the conflicts are irreconcilable, I document the discrepancies and flag them for further investigation. In some cases, data governance policies might dictate the priority given to particular data sources.
For example, in a project involving merging data from two customer databases, we encountered conflicting addresses for some customers. By cross-referencing with official identification documents and postal service records, we identified and corrected the inaccuracies, resulting in a unified and accurate customer database.
Q 24. Explain your understanding of different data formats and structures.
Understanding data formats and structures is fundamental to effective data management. I’m familiar with a wide range of formats, including relational databases (like MySQL and PostgreSQL), NoSQL databases (like MongoDB and Cassandra), CSV, JSON, XML, and binary formats. Each format has its strengths and weaknesses, and the choice depends on the specific application.
Relational databases excel at structured data with well-defined relationships, making them ideal for transactional systems. NoSQL databases are more flexible and scalable, handling unstructured or semi-structured data effectively, suitable for big data applications. CSV and JSON are frequently used for data exchange, offering simplicity and readability. XML provides a more complex, hierarchical structure for data representation.
My experience includes working with various database systems and transforming data between different formats using scripting languages such as Python and SQL. For instance, I’ve used Python with libraries like Pandas to efficiently clean, transform and load (ETL) data from CSV files into relational databases. I also understand the importance of schema design for different data formats, ensuring data integrity and efficient querying.
Q 25. Describe your experience with data encryption and access control.
Data encryption and access control are crucial for data security and privacy. My experience includes implementing various encryption methods, from symmetric encryption (like AES) for protecting data at rest and in transit, to asymmetric encryption (like RSA) for managing digital signatures and key exchange. I also understand the importance of implementing robust access control mechanisms based on the principle of least privilege – granting users only the necessary access rights to perform their duties.
I’ve worked with different access control models, including role-based access control (RBAC) and attribute-based access control (ABAC), to manage permissions effectively. My experience extends to working with encryption tools and libraries, and integrating them into database systems and applications. I am familiar with security protocols like TLS/SSL to secure data transmission and understand the significance of regular security audits to ensure ongoing data protection.
For instance, in a project involving sensitive health records, we employed AES encryption to protect the data at rest, and TLS/SSL to secure data transmission between the application and the database. We also implemented RBAC to restrict access based on user roles, ensuring that only authorized personnel could access the sensitive data.
Q 26. How do you stay up-to-date with current trends in recordkeeping and data management?
Staying current in the dynamic field of recordkeeping and data management is crucial. I achieve this through a multi-faceted approach. I actively participate in professional organizations like (mention relevant organizations), attending conferences and workshops to learn about the latest advancements and best practices. I regularly read industry publications, journals, and research papers.
I also actively engage in online communities and forums, participating in discussions and sharing knowledge with other professionals. Following influential thought leaders and industry experts on social media platforms keeps me abreast of current trends and emerging technologies. I actively pursue relevant certifications to enhance my skills and knowledge, demonstrating my commitment to continuous professional development.
Furthermore, I make it a point to evaluate and incorporate new technologies and techniques into my work, fostering an environment of continuous improvement and innovation within my team and organization.
Q 27. What are your strengths and weaknesses in this field?
My strengths lie in my analytical skills, problem-solving abilities, and my strong understanding of data governance principles. I excel at designing efficient and effective data management systems, ensuring data quality, security, and compliance. I’m a highly organized and detail-oriented individual capable of managing complex projects and meeting tight deadlines. My experience with various data technologies and my ability to communicate complex technical information clearly make me a valuable asset.
My area for improvement lies in expanding my expertise in specific emerging technologies, like advanced analytics and machine learning in the context of data management. I’m actively working to address this by undertaking relevant training and projects to broaden my knowledge base in these areas.
Q 28. How do you handle stressful situations involving data breaches or system failures?
Handling stressful situations, such as data breaches or system failures, requires a calm and methodical approach. My first step is to contain the situation, preventing further damage or data loss. This often involves quickly assessing the extent of the problem and activating established incident response plans.
Then, I focus on identifying the root cause of the incident, working collaboratively with relevant teams to address the issue swiftly and effectively. Open communication is paramount, keeping stakeholders informed of the situation and the steps taken to resolve it. After the immediate crisis is resolved, a thorough post-mortem analysis is performed to identify areas for improvement in our data security and disaster recovery strategies, helping to prevent similar incidents in the future. The emphasis is always on learning from the experience to enhance our resilience and preparedness.
For instance, when faced with a database server failure, we swiftly activated our disaster recovery plan, quickly switching to a backup server, minimizing downtime. Following the restoration, a comprehensive analysis of the failure and our recovery processes was undertaken, leading to improvements in our server monitoring and failover mechanisms.
Key Topics to Learn for Recordkeeping and Data Management Interview
- Data Governance and Compliance: Understand principles of data governance, relevant regulations (e.g., GDPR, HIPAA), and best practices for ensuring data integrity and compliance.
- Record Lifecycle Management: Master the stages of a record’s lifecycle (creation, storage, use, retention, and disposal), and how to apply appropriate policies and procedures at each stage.
- Data Security and Privacy: Discuss data security protocols, encryption methods, access control, and strategies for protecting sensitive information. Understand the ethical implications of data handling.
- Information Architecture and Metadata: Explain how to design efficient and effective systems for organizing and retrieving information. Understand the role of metadata in data discovery and management.
- Data Migration and Integration: Describe methods for migrating data between systems, ensuring data accuracy and consistency throughout the process. Understand data integration strategies and tools.
- Data Quality and Validation: Discuss techniques for ensuring data accuracy, completeness, consistency, and timeliness. Be prepared to discuss data cleansing and validation methods.
- Database Management Systems (DBMS): Demonstrate familiarity with common database systems (e.g., SQL, NoSQL) and their applications in recordkeeping and data management.
- Data Analysis and Reporting: Explain how to extract meaningful insights from data using analytical techniques and create effective reports to communicate findings.
- Disaster Recovery and Business Continuity: Discuss strategies for protecting data from loss or damage and ensuring business continuity in the event of a disaster.
- Problem-Solving and Analytical Skills: Be ready to discuss how you approach challenges related to data management, including identifying and resolving data inconsistencies or errors.
Next Steps
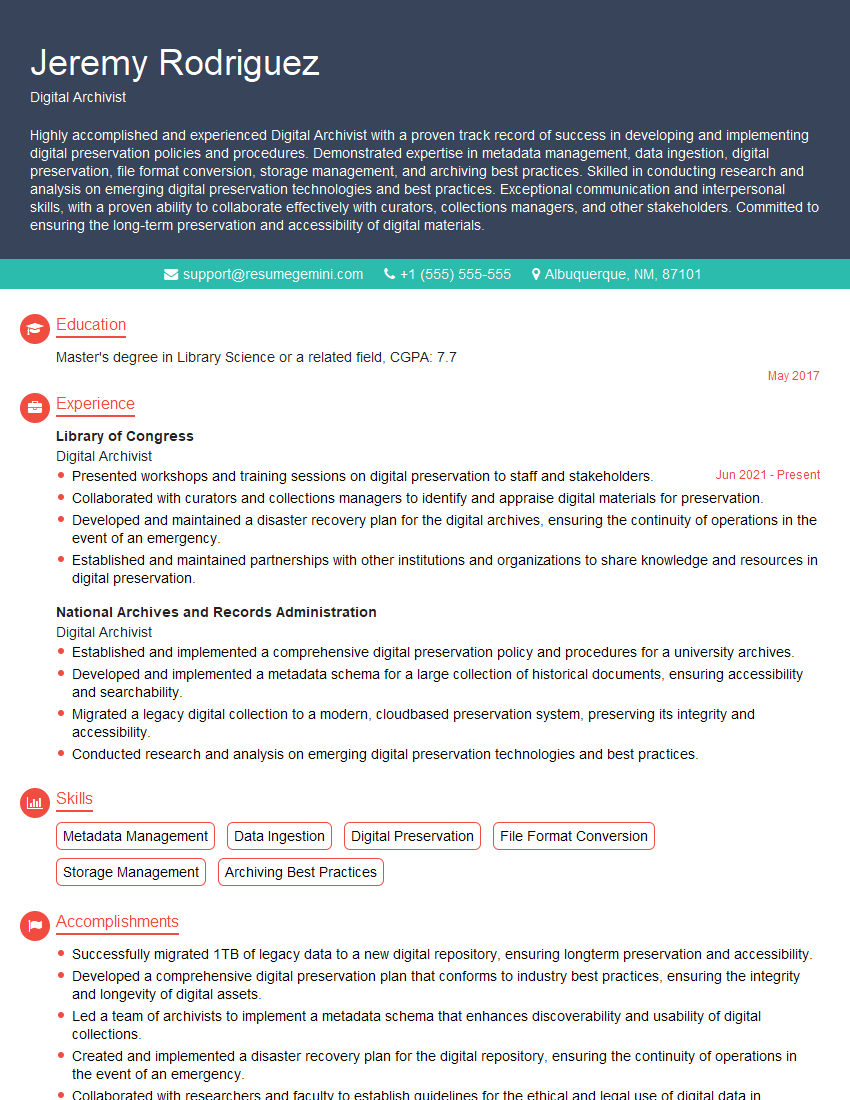
Mastering Recordkeeping and Data Management is crucial for career advancement in today’s data-driven world. These skills are highly sought after across various industries, offering excellent job prospects and potential for growth. To maximize your chances of landing your dream role, focus on building a strong, ATS-friendly resume that highlights your skills and experience. ResumeGemini is a trusted resource that can help you craft a compelling resume that showcases your qualifications effectively. They provide examples of resumes tailored to Recordkeeping and Data Management, helping you present yourself in the best possible light to potential employers. Invest time in building a powerful resume – it’s your first impression!
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good