The right preparation can turn an interview into an opportunity to showcase your expertise. This guide to Covert Surveillance interview questions is your ultimate resource, providing key insights and tips to help you ace your responses and stand out as a top candidate.
Questions Asked in Covert Surveillance Interview
Q 1. Describe your experience with various surveillance techniques, including physical and electronic methods.
My experience encompasses a wide range of surveillance techniques, both physical and electronic. Physical surveillance involves direct observation, often employing techniques like maintaining visual contact from a discreet distance, utilizing cover and concealment, and employing traffic and pedestrian patterns to blend in. This might involve following a subject on foot, using a vehicle, or even utilizing public transportation to remain unnoticed. Electronic surveillance, on the other hand, leverages technology. This includes utilizing various audio and video recording devices, ranging from sophisticated hidden cameras and microphones to GPS tracking devices and cell phone monitoring (within legal parameters, of course). I’ve worked extensively with both analog and digital systems, understanding their strengths and limitations in different environments. For instance, in a high-density urban area, a discreet, small camera hidden within an everyday object might be ideal, whereas in a rural setting, longer-range surveillance equipment might be more effective.
I’m also proficient in using specialized equipment like thermal imaging cameras (for night vision), enhanced audio recording devices to pick up faint conversations, and software for analyzing recorded footage and identifying patterns or key individuals. My experience covers both static surveillance (monitoring a fixed location) and mobile surveillance (following a subject).
Q 2. Explain your understanding of legal and ethical considerations in covert surveillance.
Legal and ethical considerations are paramount in covert surveillance. Operating outside the law can have severe consequences, including legal action and damage to reputation. My understanding is grounded in a thorough knowledge of relevant laws and regulations, which vary considerably depending on jurisdiction. In many places, surveillance must be justified by a compelling reason, such as national security or the prevention of serious crime. The use of covert surveillance frequently necessitates obtaining warrants or other forms of legal authorization.
Ethical considerations are equally important. Privacy is a fundamental human right, and covert surveillance should only be undertaken when absolutely necessary and proportionally justified. The potential harm to individuals’ privacy must be carefully weighed against the benefits of the surveillance. I always strive to minimize intrusion and adhere to a strict code of conduct which places ethical considerations at the forefront. Data collected is always handled responsibly and securely and disposed of according to legal and ethical standards.
Q 3. How would you select appropriate surveillance equipment for a specific operation?
Selecting appropriate surveillance equipment depends heavily on the specific operation parameters. Several key factors guide my decision-making process:
- Target Environment: Is it an urban, suburban, or rural setting? Indoor or outdoor? What are the lighting conditions?
- Target Subject: How mobile is the subject? What is their level of awareness?
- Operational Goals: What information needs to be gathered? Audio only? Video? GPS tracking?
- Legal and Ethical Constraints: Are there any legal restrictions on the types of surveillance equipment that can be used?
- Budget and Resources: What resources are available for equipment purchase and maintenance?
For example, for a long-term surveillance operation in a busy city center, I might choose small, high-definition cameras disguised as everyday objects to avoid detection. For a rural setting, where longer-range surveillance is needed, I might opt for cameras with night vision capabilities and a wider field of view. The selection process is always tailored to the specific requirements of the operation to maximize effectiveness while minimizing risk.
Q 4. Describe your experience in conducting surveillance while maintaining a low profile.
Maintaining a low profile during surveillance is crucial for success. This requires a combination of skills and experience. I’ve been trained in observation techniques, blending into the background, and avoiding drawing attention to myself. This involves understanding human behavior, anticipating the subject’s movements, utilizing natural cover and concealment, and maintaining situational awareness. I’ve honed my skills in using inconspicuous vehicles, maintaining appropriate distances, and avoiding patterns of behavior that might alert the subject.
For instance, in one operation, I followed a subject across several locations. My strategy involved using public transportation and blending in with pedestrian traffic, regularly changing my clothing, and never making direct eye contact. I also learned to anticipate the subject’s routines and adjusted my own to stay ahead, ensuring I wasn’t easily identified or followed.
Q 5. How do you handle unexpected situations or challenges during a surveillance operation?
Unexpected situations are inevitable in surveillance. My training emphasizes adaptability and problem-solving. I’ve developed contingency plans for various scenarios, including technical malfunctions, unexpected subject behavior, and interference from third parties. My response to these situations involves a combination of quick thinking, resourcefulness, and sound judgment.
For instance, if a surveillance device malfunctions, I have backup equipment and contingency plans in place. If the subject unexpectedly changes their routine, I reassess the situation, adjust my strategy, and seek alternative methods of surveillance if necessary. Communication with my team is key in handling unexpected challenges; a coordinated response minimizes risk and maximizes effectiveness.
Q 6. Explain your experience with counter-surveillance measures.
Understanding counter-surveillance measures is as important as implementing surveillance techniques. This involves recognizing the signs of detection, such as unusual behavior from the subject, unusual traffic patterns, or the presence of other surveillance equipment. I’m proficient in detecting sweeps for electronic bugs and employing countermeasures to minimize detection. This knowledge is crucial for operational security and maintaining the integrity of the surveillance operation.
For example, I’m adept at using detection equipment to sweep a room for hidden cameras or listening devices before commencing surveillance. I also understand how to mitigate the risk of detection by employing techniques such as using encrypted communications and employing various methods for data transmission and storage. This includes using specialized software to encrypt data, employing secure communication protocols, and using methods to obscure the transmission of data.
Q 7. How do you analyze and interpret surveillance data to draw meaningful conclusions?
Analyzing and interpreting surveillance data is a critical step. This involves reviewing video and audio recordings, GPS tracking data, and other relevant information to identify patterns, connections, and meaningful conclusions. I utilize both manual review and specialized software to enhance the analysis process. This includes using video editing tools to highlight specific events, facial recognition software to identify individuals, and data analysis tools to uncover relationships between seemingly disparate data points.
For instance, in one investigation, I used video analysis software to track the movement of a subject across multiple locations, identifying key individuals and places of interest that would have otherwise gone unnoticed. This information provided crucial insights into the subject’s activities, ultimately contributing to the success of the operation. The data analysis process is iterative, requiring careful review, cross-referencing, and triangulation of various data sources to ensure the accuracy and completeness of the findings. The process always ends with a detailed, comprehensive report.
Q 8. What software and hardware are you proficient with in relation to surveillance?
My proficiency in surveillance software and hardware spans a wide range. On the software side, I’m expert in video management systems (VMS) like Genetec Security Center and Milestone XProtect, proficient in analyzing footage using tools such as facial recognition software and video enhancement programs. I’m also experienced with various audio recording and analysis software. Hardware-wise, I’m highly familiar with a variety of covert cameras – including miniature cameras, body-worn cameras, and long-range lenses – along with audio recording devices, GPS trackers, and various communication systems used in surveillance operations. I understand the technical limitations and capabilities of each piece of equipment and can select the optimal tools for a given scenario. For instance, I would choose a long-range thermal camera for night-time surveillance in a rural area, while a miniature camera hidden in a pen would be better suited for close-quarters indoor observation.
- Software: Genetec Security Center, Milestone XProtect, facial recognition software, audio analysis tools.
- Hardware: Miniature cameras, body-worn cameras, long-range lenses, audio recorders, GPS trackers, covert communication systems.
Q 9. How do you ensure the confidentiality and security of surveillance data?
Data confidentiality and security are paramount in covert surveillance. We employ a multi-layered approach. Firstly, all data is encrypted both in transit and at rest, using robust encryption algorithms like AES-256. Secondly, access to surveillance data is strictly controlled through a system of user roles and permissions, ensuring only authorized personnel can view specific data. Thirdly, all equipment is regularly updated with the latest security patches to mitigate vulnerabilities. Furthermore, we maintain strict physical security protocols for storage and access to hardware and data storage media. Regular audits are conducted to verify compliance with security policies and to identify and address potential weaknesses. Data is stored securely in encrypted servers, often physically located in secure facilities with controlled access. Finally, we follow stringent data retention policies, adhering to all legal requirements regarding the storage and disposal of surveillance data.
Q 10. Describe your experience working independently and as part of a team.
I’m comfortable working both independently and as part of a team. Independent work often involves conducting surveillance operations requiring discretion and quick decision-making, such as solo stakeouts or discreet observation. This requires strong self-reliance, meticulous planning, and the ability to adapt to unexpected circumstances. For example, during a solo stakeout, I had to improvise a concealment strategy when my initial plan was compromised due to unforeseen construction work. I successfully adapted, choosing a secondary observation point that allowed me to maintain situational awareness without detection. Conversely, teamwork is crucial in complex operations involving multiple surveillance teams, coordinating efforts, and sharing intelligence. My experience working as part of a team includes collaboration on large-scale investigations, coordinating surveillance efforts across different locations, and efficiently sharing information.
Q 11. How do you maintain situational awareness during a surveillance operation?
Maintaining situational awareness during a surveillance operation is critical. It involves constantly scanning the environment, anticipating potential threats or changes, and adapting accordingly. This includes being aware of the subject’s movements, the surrounding environment, and potential risks. I use a combination of visual observation, auditory awareness, and the utilization of technology, such as GPS tracking and communication systems, to maintain a comprehensive understanding of the situation. For example, during a mobile surveillance operation, I pay close attention to potential escape routes, traffic patterns, and any unusual activity that might indicate a change in the subject’s behavior. Regular communication with other team members is crucial to ensure everyone is aware of any developments. A structured observation plan and contingency plans for various scenarios are also essential elements in maintaining situational awareness.
Q 12. How do you deal with difficult or uncooperative subjects?
Dealing with difficult or uncooperative subjects requires patience, tact, and a clear understanding of legal boundaries. My approach involves maintaining a professional demeanor, employing de-escalation techniques, and clearly communicating the purpose of the surveillance (when appropriate and legal). If necessary, I will utilize appropriate legal channels to obtain information or cooperation, prioritizing safety and avoiding any action that could be construed as harassment or intimidation. For instance, in a situation where a subject was initially hostile, I was able to de-escalate the situation by calmly explaining the legal framework under which we were operating and emphasizing the importance of cooperation for a safe and smooth resolution. Documentation of all interactions is paramount.
Q 13. Explain your understanding of different types of surveillance, such as stakeouts, mobile surveillance, and undercover operations.
Surveillance encompasses diverse methods, each suited for different scenarios. A stakeout involves observing a fixed location over an extended period, often requiring patience and discretion, and employing concealment to minimize detection. Mobile surveillance involves tracking a subject’s movements using vehicles, often requiring careful coordination and adherence to traffic laws. Undercover operations demand extensive preparation, assuming a false identity and blending into a target environment, often requiring an exceptional level of deception and improvisation. The choice of technique depends on the nature of the target, the objectives of the operation, and available resources. Successful implementation demands meticulous planning, attention to detail, and adherence to legal and ethical guidelines.
Q 14. What is your experience with GPS tracking and other location-based technologies?
My experience with GPS tracking and location-based technologies is extensive. I’m proficient in using various GPS trackers – ranging from small, covert devices to more sophisticated systems that provide real-time location data. I’m familiar with their limitations, such as signal interference and GPS jamming techniques. Understanding how to overcome these limitations is crucial. I’m also knowledgeable in using other location-based technologies, such as cellular triangulation and Wi-Fi tracking, to locate subjects when GPS tracking may not be feasible. This often involves integrating data from multiple sources to improve accuracy and reliability. For example, in one case, we successfully located a suspect by combining data from a compromised GPS tracker with cell tower triangulation data to pinpoint their approximate location.
Q 15. How do you ensure the legality of your surveillance activities?
Legal compliance is paramount in covert surveillance. Before any operation, I meticulously review and ensure adherence to all applicable laws and regulations, including those concerning privacy rights, wiretapping, and data protection. This involves thoroughly researching the specific jurisdiction and obtaining all necessary legal authorizations, such as warrants or court orders, depending on the nature of the surveillance. For instance, in a case involving suspected financial fraud, I would work closely with legal counsel to obtain a warrant specifying the targets, the methods of surveillance, and the duration of the operation. This ensures that all activities remain within the bounds of the law and mitigates the risk of legal repercussions. I maintain meticulous records of all legal authorizations and operational procedures to facilitate transparency and accountability.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. What is your experience with audio and video recording equipment?
My experience encompasses a wide range of audio and video recording equipment, from high-definition cameras with advanced zoom capabilities and low-light performance to miniature microphones capable of picking up conversations from a significant distance. I’m proficient in using both covert and overt recording devices. This includes selecting the appropriate equipment based on the specific surveillance environment, such as using miniature cameras hidden within everyday objects for covert operations or deploying more visible cameras with enhanced security features for overt surveillance. I’m also adept at utilizing advanced recording techniques, such as employing multiple cameras for different perspectives or using audio enhancement software to improve the clarity of recorded conversations. For example, in one operation, we used a network of miniature cameras disguised as smoke detectors, providing 360-degree coverage of the target location, all controlled remotely and recorded on encrypted servers.
Q 17. How familiar are you with data encryption and security protocols?
Data encryption and security are critical to protecting sensitive information gathered during covert surveillance. I am highly familiar with various encryption algorithms, including AES-256 and RSA, and I understand the importance of using strong passwords and implementing multi-factor authentication. I’m also experienced in using secure communication channels and data storage solutions to prevent unauthorized access to surveillance data. For example, I ensure that all data is encrypted both in transit and at rest. We use secure cloud storage platforms with robust security protocols, regularly update our software and hardware to patch security vulnerabilities, and maintain a strict access control policy to limit who can access and modify the gathered data. Data is regularly backed up and secured off-site to ensure data integrity and prevent loss. Furthermore, I understand and apply various security protocols, including VPNs and firewalls, to protect data from cyber threats.
Q 18. How do you handle the stress and pressure of covert surveillance work?
Covert surveillance can be demanding, requiring long hours, meticulous attention to detail, and the ability to remain calm under pressure. I manage stress through rigorous planning, ensuring all equipment is thoroughly tested and contingency plans are in place. Maintaining physical fitness and good health is important, as is the ability to prioritize tasks efficiently. I also employ relaxation techniques such as mindfulness meditation to manage stress and ensure clear thinking during challenging situations. Additionally, maintaining a strong team dynamic and open communication channels helps mitigate stress through mutual support and shared responsibility. A strong support system outside of work is equally vital for maintaining mental well-being and preventing burnout.
Q 19. Describe your experience in report writing and presenting surveillance findings.
I possess extensive experience in compiling detailed and accurate surveillance reports. My reports are structured to present findings clearly and concisely, using precise language and avoiding ambiguity. They include visual aids such as maps, timelines, and photographic evidence, accurately documenting all observations. For example, I might create a detailed timeline of a subject’s movements, supported by photographic and video evidence, or produce a concise report outlining suspicious activities or interactions. The report’s presentation is tailored to the audience, whether a client, legal team, or internal stakeholders. I am adept at presenting findings both verbally and visually, using clear, concise language, visual aids, and data visualization techniques to ensure effective communication of complex information. My presentations prioritize accuracy, clarity, and the ability to readily answer questions.
Q 20. What are your skills in observation and detail recognition?
Observation and detail recognition are fundamental skills in covert surveillance. Years of experience have honed my ability to identify subtle cues and anomalies that might otherwise go unnoticed. This includes recognizing patterns of behavior, remembering minute details, and accurately assessing situations. I am trained in various observation techniques, including systematic observation and mindful observation, which allows me to systematically scan environments, identify anomalies, and record details accurately. For example, I can quickly identify changes in a subject’s routine, recognize a specific vehicle or individual from a distance, and recall detailed descriptions of a location. This skill is crucial for identifying potential risks, interpreting evidence, and building a comprehensive understanding of the situation. Regular training and self-assessment helps me continuously improve these crucial skills.
Q 21. How do you prioritize tasks during a complex surveillance operation?
Prioritizing tasks in a complex surveillance operation requires a systematic approach. I utilize a risk assessment framework, identifying critical objectives and potential threats first. High-priority tasks, such as those that directly address the core objectives or mitigate significant risks, receive immediate attention. This involves a clear understanding of the overall mission objectives and coordinating actions among team members. Time management and communication are crucial; for example, a sudden change in the subject’s behavior might necessitate a shift in priorities, demanding quick adaptation and informed decision-making. I ensure that the team is constantly informed of the changing circumstances and understands the rationale behind the prioritization decisions. Flexibility and adaptability are key to successfully managing the constantly evolving nature of covert surveillance operations.
Q 22. How do you maintain your physical and mental fitness for demanding surveillance work?
Maintaining peak physical and mental fitness is paramount in covert surveillance, as the work demands long hours, intense focus, and often unpredictable situations. My regimen focuses on both aspects:
- Physical Fitness: I maintain a rigorous exercise routine incorporating cardiovascular training (running, swimming) and strength training to build endurance, stamina, and agility. This allows me to remain alert and capable during extended periods of observation, whether I’m on foot or using vehicles. For example, a recent operation required me to track a suspect across varied terrains, and my physical conditioning proved crucial in maintaining pace and remaining undetected.
- Mental Fitness: Mental resilience is equally important. Stress management techniques like mindfulness meditation and regular sleep are essential for maintaining focus and avoiding burnout. I also prioritize cognitive training through puzzles and memory exercises to keep my mind sharp and improve observational skills. During a particularly challenging case, my mindfulness practice helped me stay calm under pressure and maintain a clear perspective during crucial moments.
Essentially, it’s about creating a holistic approach to health; neglecting either the physical or mental side significantly impacts performance and effectiveness in this field.
Q 23. Describe your knowledge of relevant privacy laws and regulations.
Knowledge of privacy laws and regulations is fundamental and non-negotiable in covert surveillance. My understanding encompasses several key areas:
- Fourth Amendment (US): I am deeply familiar with the protection against unreasonable searches and seizures, understanding the requirements for warrants and probable cause. Every surveillance operation must be meticulously planned to ensure complete legal compliance. For instance, using a hidden camera in a private residence without a warrant would be a clear violation.
- State and Local Laws: Privacy laws vary by jurisdiction. I thoroughly research and understand the specific regulations in any area where I operate. For example, wiretapping laws are significantly different state-to-state, and violating them can lead to serious legal consequences.
- Data Protection Regulations (e.g., GDPR, CCPA): I understand the regulations regarding the collection, storage, and use of personal data. This includes maintaining secure data storage, adhering to retention policies, and ensuring informed consent when legally required. Any data collected during surveillance is handled with the utmost care and confidentiality.
My commitment to ethical and legal conduct is unwavering; operating within the bounds of the law is not simply a matter of compliance but a core principle that underpins the integrity of my work.
Q 24. How would you adapt your surveillance strategy to different environments?
Adaptability is key to successful surveillance. My approach changes drastically depending on the environment:
- Urban Environments: High-density populations require blending in seamlessly. This includes using public transportation, understanding pedestrian traffic patterns, and employing discreet observation techniques. I might use a combination of long-range observation with binoculars and close-range surveillance from a nearby cafe.
- Rural Environments: Open spaces require different strategies, including using vehicles for discreet observation, understanding terrain, and adapting to changing weather conditions. In such settings, understanding local wildlife and their sounds is valuable for avoiding detection.
- Indoor Environments: This might involve utilizing specialized audio and visual equipment, understanding building layouts, and being aware of security systems. Access control and maintaining a low profile are especially critical in these situations.
In each scenario, I tailor my approach based on risk assessment, the subject’s behavior, and resource availability. The strategy is not static but a dynamic process continuously adjusted to the specific context.
Q 25. What experience do you have with various types of surveillance cameras and their capabilities?
I have extensive experience with a wide array of surveillance cameras, from basic CCTV systems to sophisticated, high-resolution models with advanced features:
- CCTV Cameras: I’m proficient in installing, configuring, and maintaining both analog and IP-based CCTV systems, including dome cameras, bullet cameras, and PTZ (Pan-Tilt-Zoom) cameras. Understanding their limitations and strengths is crucial for effective placement and data acquisition.
- Thermal Imaging Cameras: These cameras detect heat signatures, useful for surveillance in low-light conditions or through obstructions. I’ve utilized them in several operations, particularly in night-time surveillance or when subjects are attempting to conceal themselves.
- Hidden Cameras: I’m experienced with various types of covert cameras, including those disguised as everyday objects. The selection process depends heavily on the specific environment and the level of discretion required.
- Body-Worn Cameras: These are beneficial for hands-free documentation and discreet recording during investigations. Understanding their operational limitations, such as battery life and storage capacity, is essential.
Understanding the strengths and weaknesses of each type is paramount. For instance, while thermal cameras offer excellent low-light capabilities, they may not capture high-quality image detail.
Q 26. Explain your understanding of image and video analysis techniques.
Image and video analysis is a critical skill in covert surveillance. It involves extracting meaningful information from visual data. My skills encompass:
- Facial Recognition: I can use software and techniques to identify individuals from video footage. This requires a thorough understanding of image quality, lighting conditions, and facial features.
- Object Recognition: I can identify vehicles, objects, and other items of interest within video recordings. This is invaluable in reconstructing events and identifying patterns.
- Video Enhancement: I use software to enhance image quality, such as improving resolution, adjusting contrast, and reducing noise, to extract finer details that may be crucial for identifying suspects or evidence.
- Tracking and Trajectory Analysis: I can track subjects’ movements through video, determining their routes and interactions. This involves analyzing multiple camera angles and correlating data points.
I utilize various software tools to perform these analyses efficiently and accurately, always keeping in mind the context of the investigation and the potential biases that can affect interpretations.
Q 27. How familiar are you with different types of audio recording devices and their limitations?
My familiarity with audio recording devices extends to a range of technologies, along with a clear understanding of their limitations:
- Parabolic Microphones: These directional microphones amplify distant sounds, useful for covert audio surveillance. However, they are susceptible to environmental noise and require careful positioning.
- Contact Microphones: These small microphones attach directly to surfaces, picking up vibrations. They’re incredibly discreet, but the sound quality can be affected by the surface material.
- Hidden Microphones: These devices are concealed within everyday objects. Their range and quality are limited by their size and construction.
- Digital Voice Recorders: These devices are essential for storing and managing recorded audio data. Understanding file formats, storage capacity, and data security are crucial.
One must also account for environmental factors impacting audio quality – background noise, distance, and obstacles all influence the clarity of the recording. I meticulously document the limitations of the devices used for each operation to ensure the reliability of the evidence collected.
Q 28. Describe your problem-solving skills in relation to technical malfunctions during surveillance.
Technical malfunctions during surveillance are unavoidable. My problem-solving approach is systematic and prioritizes a swift resolution:
- Identify the Problem: The first step involves accurately diagnosing the malfunction. Is it a power issue, a software glitch, or a hardware failure? This often involves carefully checking connections, verifying power sources, and reviewing error logs.
- Isolate the Source: Once the problem is identified, I try to isolate its source. This might involve testing individual components or running diagnostic software. I always keep spare equipment on hand for immediate replacements.
- Implement a Solution: Depending on the nature of the problem, solutions can range from simple troubleshooting steps to more complex repairs or replacements. I’m adept at improvising solutions using available resources when necessary.
- Document the Event: It’s essential to meticulously document the malfunction, the steps taken to resolve it, and any consequences it may have had on data collection. This documentation is invaluable for future operations and for demonstrating accountability.
For example, during a recent operation, a sudden power outage affected the surveillance system. I quickly deployed a backup power source, minimizing disruption and ensuring the integrity of the surveillance footage.
Key Topics to Learn for Covert Surveillance Interview
- Surveillance Techniques: Understanding various methods like visual surveillance, audio surveillance, electronic surveillance, and their legal and ethical implications.
- Equipment and Technology: Familiarity with cameras, microphones, recording devices, GPS trackers, and software used in covert operations; including their limitations and countermeasures.
- Surveillance Planning and Execution: Developing comprehensive surveillance plans, including risk assessment, target identification, resource allocation, and contingency planning. Practical application: Describe a scenario where you planned and executed a surveillance operation, highlighting problem-solving strategies.
- Data Analysis and Interpretation: Skills in analyzing collected data, identifying patterns, and drawing meaningful conclusions. This includes understanding how to present findings effectively.
- Legal and Ethical Considerations: Deep understanding of relevant laws and regulations governing surveillance activities; maintaining ethical standards and respecting privacy rights.
- Counter-Surveillance Techniques: Awareness of methods used to detect and avoid surveillance, and strategies to mitigate risks associated with detection.
- Report Writing and Documentation: Ability to clearly and concisely document surveillance activities, findings, and observations in a professional and legally compliant manner.
- Teamwork and Communication: Effective communication and collaboration skills, working effectively within a team environment to achieve common objectives.
- Problem-Solving and Critical Thinking: Ability to analyze complex situations, identify potential challenges, and develop effective solutions under pressure.
- Technological Proficiency: Demonstrating expertise in relevant software and hardware, including data management and analysis tools.
Next Steps
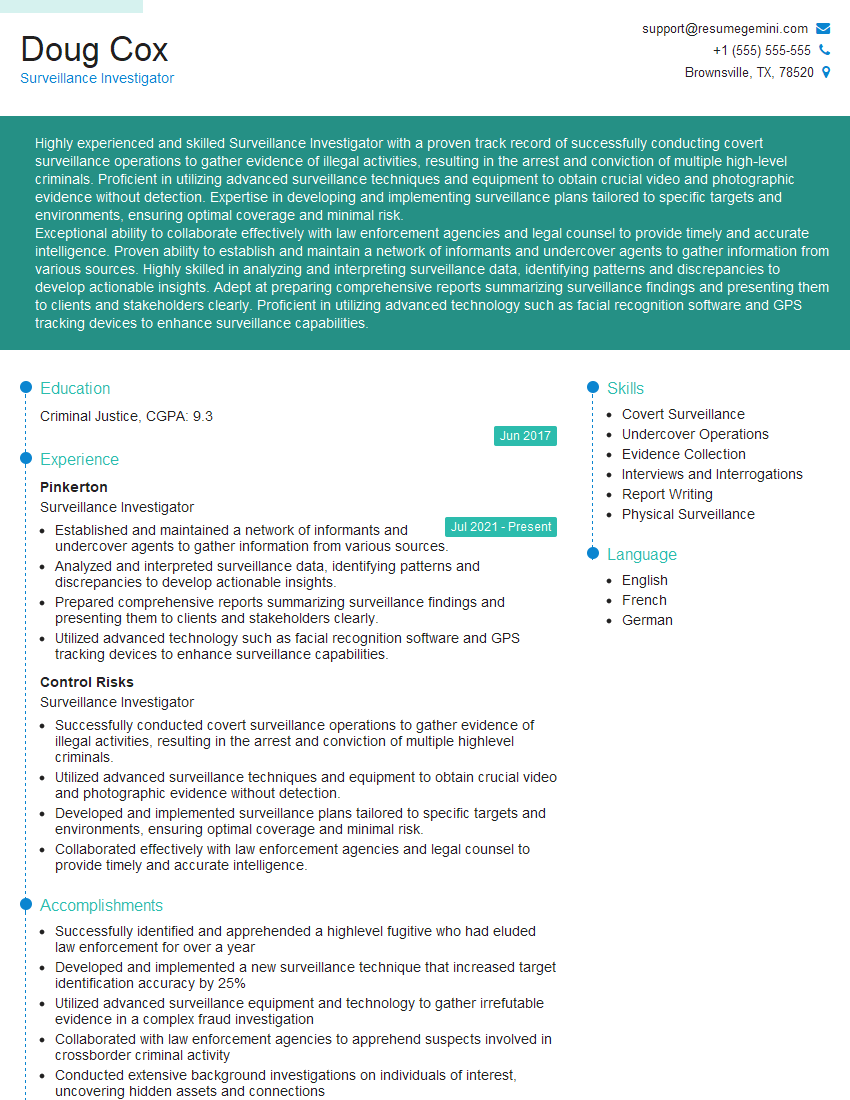
Mastering Covert Surveillance opens doors to exciting and challenging careers in law enforcement, private investigation, and security. To maximize your job prospects, a well-crafted, ATS-friendly resume is crucial. ResumeGemini is a trusted resource to help you build a professional and impactful resume that highlights your skills and experience effectively. Examples of resumes tailored to Covert Surveillance are available to help guide your resume creation process, showcasing your unique qualifications to potential employers.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Attention music lovers!
Wow, All the best Sax Summer music !!!
Spotify: https://open.spotify.com/artist/6ShcdIT7rPVVaFEpgZQbUk
Apple Music: https://music.apple.com/fr/artist/jimmy-sax-black/1530501936
YouTube: https://music.youtube.com/browse/VLOLAK5uy_noClmC7abM6YpZsnySxRqt3LoalPf88No
Other Platforms and Free Downloads : https://fanlink.tv/jimmysaxblack
on google : https://www.google.com/search?q=22+AND+22+AND+22
on ChatGPT : https://chat.openai.com?q=who20jlJimmy20Black20Sax20Producer
Get back into the groove with Jimmy sax Black
Best regards,
Jimmy sax Black
www.jimmysaxblack.com
Hi I am a troller at The aquatic interview center and I suddenly went so fast in Roblox and it was gone when I reset.
Hi,
Business owners spend hours every week worrying about their website—or avoiding it because it feels overwhelming.
We’d like to take that off your plate:
$69/month. Everything handled.
Our team will:
Design a custom website—or completely overhaul your current one
Take care of hosting as an option
Handle edits and improvements—up to 60 minutes of work included every month
No setup fees, no annual commitments. Just a site that makes a strong first impression.
Find out if it’s right for you:
https://websolutionsgenius.com/awardwinningwebsites
Hello,
we currently offer a complimentary backlink and URL indexing test for search engine optimization professionals.
You can get complimentary indexing credits to test how link discovery works in practice.
No credit card is required and there is no recurring fee.
You can find details here:
https://wikipedia-backlinks.com/indexing/
Regards
NICE RESPONSE TO Q & A
hi
The aim of this message is regarding an unclaimed deposit of a deceased nationale that bears the same name as you. You are not relate to him as there are millions of people answering the names across around the world. But i will use my position to influence the release of the deposit to you for our mutual benefit.
Respond for full details and how to claim the deposit. This is 100% risk free. Send hello to my email id: lukachachibaialuka@gmail.com
Luka Chachibaialuka
Hey interviewgemini.com, just wanted to follow up on my last email.
We just launched Call the Monster, an parenting app that lets you summon friendly ‘monsters’ kids actually listen to.
We’re also running a giveaway for everyone who downloads the app. Since it’s brand new, there aren’t many users yet, which means you’ve got a much better chance of winning some great prizes.
You can check it out here: https://bit.ly/callamonsterapp
Or follow us on Instagram: https://www.instagram.com/callamonsterapp
Thanks,
Ryan
CEO – Call the Monster App
Hey interviewgemini.com, I saw your website and love your approach.
I just want this to look like spam email, but want to share something important to you. We just launched Call the Monster, a parenting app that lets you summon friendly ‘monsters’ kids actually listen to.
Parents are loving it for calming chaos before bedtime. Thought you might want to try it: https://bit.ly/callamonsterapp or just follow our fun monster lore on Instagram: https://www.instagram.com/callamonsterapp
Thanks,
Ryan
CEO – Call A Monster APP
To the interviewgemini.com Owner.
Dear interviewgemini.com Webmaster!
Hi interviewgemini.com Webmaster!
Dear interviewgemini.com Webmaster!
excellent
Hello,
We found issues with your domain’s email setup that may be sending your messages to spam or blocking them completely. InboxShield Mini shows you how to fix it in minutes — no tech skills required.
Scan your domain now for details: https://inboxshield-mini.com/
— Adam @ InboxShield Mini
support@inboxshield-mini.com
Reply STOP to unsubscribe
Hi, are you owner of interviewgemini.com? What if I told you I could help you find extra time in your schedule, reconnect with leads you didn’t even realize you missed, and bring in more “I want to work with you” conversations, without increasing your ad spend or hiring a full-time employee?
All with a flexible, budget-friendly service that could easily pay for itself. Sounds good?
Would it be nice to jump on a quick 10-minute call so I can show you exactly how we make this work?
Best,
Hapei
Marketing Director
Hey, I know you’re the owner of interviewgemini.com. I’ll be quick.
Fundraising for your business is tough and time-consuming. We make it easier by guaranteeing two private investor meetings each month, for six months. No demos, no pitch events – just direct introductions to active investors matched to your startup.
If youR17;re raising, this could help you build real momentum. Want me to send more info?
Hi, I represent an SEO company that specialises in getting you AI citations and higher rankings on Google. I’d like to offer you a 100% free SEO audit for your website. Would you be interested?
Hi, I represent an SEO company that specialises in getting you AI citations and higher rankings on Google. I’d like to offer you a 100% free SEO audit for your website. Would you be interested?