The right preparation can turn an interview into an opportunity to showcase your expertise. This guide to Understanding of Cybersecurity Incident Response interview questions is your ultimate resource, providing key insights and tips to help you ace your responses and stand out as a top candidate.
Questions Asked in Understanding of Cybersecurity Incident Response Interview
Q 1. Describe the NIST Cybersecurity Framework.
The NIST Cybersecurity Framework (CSF) is a voluntary framework developed by the National Institute of Standards and Technology (NIST) to help organizations manage and reduce their cybersecurity risk. It’s not a prescriptive standard, meaning it doesn’t tell you exactly *what* to do, but rather *how* to organize your cybersecurity efforts. It provides a flexible approach adaptable to different organizations and their unique risk profiles.
The framework is built upon five core functions: Identify, Protect, Detect, Respond, and Recover. Each function is further broken down into categories, subcategories, and informational references to guide the implementation process.
- Identify: Understanding your assets, data, systems, and business environment; identifying the risks associated with each.
- Protect: Developing and implementing safeguards to limit or contain the impact of a cyberattack; this includes access control, data security, and awareness training.
- Detect: Implementing tools and processes to identify potential cyberattacks or security events; this includes intrusion detection systems, security information and event management (SIEM) systems, and regular vulnerability scans.
- Respond: Establishing and executing a plan to handle a cybersecurity incident, including containment, eradication, recovery, and post-incident activity.
- Recover: Restoring systems and data to normal operations, along with improving your defenses to prevent future attacks.
Imagine it like building a house: Identify is like surveying the land and designing the blueprints; Protect is like building the foundation and walls; Detect is like installing smoke detectors and alarms; Respond is like putting out the fire; and Recover is like rebuilding and reinforcing after the fire.
Q 2. Explain the difference between a vulnerability and an exploit.
A vulnerability is a weakness in a system or application that can be exploited by an attacker. Think of it as a crack in a wall. It’s a flaw in the design, implementation, operation, or internal controls of a system.
An exploit, on the other hand, is the method or tool used to take advantage of a vulnerability. It’s like a crowbar used to pry open that crack in the wall. Exploits can be malicious code, scripts, or techniques that leverage a vulnerability to gain unauthorized access or disrupt systems.
For example, a vulnerability might be a buffer overflow in a specific piece of software. The exploit would be the malicious code designed to trigger that buffer overflow and potentially execute arbitrary commands on the affected system.
Q 3. What are the key phases of incident response?
The key phases of incident response follow a well-defined lifecycle. While variations exist, a common model includes:
- Preparation: This proactive phase involves establishing policies, procedures, and training programs. It’s all about getting ready *before* an incident occurs. This includes forming an incident response team and defining communication plans.
- Identification: Detecting that an incident has occurred; this might involve alerts from security systems or user reports.
- Containment: Isolating the affected systems or data to prevent further damage or spread. This is crucial to minimize the impact of the incident.
- Eradication: Removing the threat completely; this might involve deleting malware, patching vulnerabilities, or replacing compromised hardware.
- Recovery: Restoring systems and data to their normal operational state. This involves restoring backups and ensuring business continuity.
- Post-Incident Activity: Analyzing the incident, identifying lessons learned, updating procedures, and conducting a root cause analysis to prevent similar incidents in the future.
Think of it like a medical emergency: Preparation is like having a well-stocked first aid kit; Identification is like recognizing the symptoms; Containment is like stabilizing the patient; Eradication is like removing the source of the injury; Recovery is like treating and healing; Post-incident Activity is like reviewing what happened to improve future response.
Q 4. How do you prioritize incidents?
Incident prioritization is critical because resources are limited. A common approach involves using a risk matrix that considers factors such as:
- Impact: How severely is the incident affecting the organization? (e.g., data breach, system outage, financial loss)
- Urgency: How quickly does the incident need to be addressed? (e.g., immediate threat, potential for escalation)
- Probability: How likely is the incident to occur or escalate?
A simple scoring system can be used, assigning points to each factor, and incidents are prioritized based on their total score. For instance, a high-impact, high-urgency incident will require immediate attention, while a low-impact, low-urgency incident might be addressed later. Consider using a documented incident response plan with a pre-defined prioritization scheme to ensure consistency.
Q 5. What are the common types of cyber threats?
The types of cyber threats are vast and evolving. Here are some common categories:
- Malware: Malicious software designed to damage, disrupt, or gain unauthorized access to systems (e.g., viruses, worms, ransomware, Trojans).
- Phishing: Attempts to trick users into revealing sensitive information (e.g., usernames, passwords, credit card details) through deceptive emails or websites.
- Denial-of-Service (DoS) Attacks: Flooding a system with traffic to make it unavailable to legitimate users.
- SQL Injection: Exploiting vulnerabilities in database applications to gain unauthorized access to data.
- Man-in-the-Middle (MitM) Attacks: Intercepting communication between two parties to steal data or manipulate the communication.
- Insider Threats: Malicious or negligent actions by individuals with legitimate access to systems or data.
- Advanced Persistent Threats (APTs): Sophisticated, long-term attacks often carried out by state-sponsored actors.
Q 6. Explain the concept of containment in incident response.
Containment is a critical phase of incident response focused on limiting the damage caused by a cybersecurity incident. The goal is to prevent the spread of malware, protect sensitive data, and maintain the integrity of the system. Containment strategies can include:
- Disconnecting infected systems from the network: This prevents the malware from spreading to other systems.
- Blocking malicious traffic at the network perimeter: Using firewalls and intrusion prevention systems to stop further attacks.
- Implementing access controls: Restricting access to the affected system to authorized personnel.
- Creating backups of affected systems: To enable restoration in case of data loss.
- Using endpoint detection and response (EDR) tools: To isolate compromised devices and prevent the malware from running.
Think of it as containing a fire – you wouldn’t want to let the flames spread throughout the entire building. Similarly, containment aims to stop the threat from causing wider damage.
Q 7. How do you conduct a root cause analysis?
Root cause analysis (RCA) is a systematic process to identify the underlying cause of an incident, not just the symptoms. The goal is to prevent similar incidents from happening in the future. Several techniques exist, but a common approach is the ‘5 Whys’ method.
Let’s say a system was compromised due to a phishing email.
- Why was the system compromised? Because a user clicked a malicious link in a phishing email.
- Why did the user click the malicious link? Because the email appeared legitimate and urgent.
- Why did the email appear legitimate? Because it mimicked a trusted source.
- Why was the user not trained to identify phishing emails? Because the security awareness training was insufficient.
- Why was the security awareness training insufficient? Because resources were limited, and the training was not frequently updated.
This reveals the root cause: insufficient security awareness training due to limited resources. Addressing this allows for better prevention, perhaps by increasing training budget and frequency or improving the quality of training material. More formal methods such as fault tree analysis or fishbone diagrams are also often employed for complex incidents.
Q 8. What are your preferred tools for incident response?
My preferred tools for incident response are diverse and depend on the specific nature of the incident, but generally include a core set of utilities. For network analysis, I rely heavily on tools like Wireshark for packet capture and analysis, and tcpdump for command-line based capture. For endpoint analysis, I utilize tools like Autopsy for digital forensics, and Sysmon for real-time monitoring and log collection. In terms of malware analysis, I use tools like Cuckoo Sandbox for automated analysis and a variety of disassemblers like IDA Pro for in-depth reverse engineering. Finally, for threat intelligence gathering, I use tools like VirusTotal and various open-source threat feeds.
The key is adaptability. A ‘one-size-fits-all’ approach is ineffective. The right toolset is chosen based on the specific indicators of compromise (IOCs) observed during the initial stages of the incident.
Q 9. Describe your experience with log analysis.
Log analysis is the backbone of effective incident response. My experience encompasses analyzing various log types, including system logs (Windows Event Logs, syslog), network logs (firewall logs, IDS/IPS logs), application logs, and database logs. I’m proficient in using various techniques like regular expressions (regex) to filter and extract relevant information. For instance, I might use a regex like ^\d{4}-\d{2}-\d{2} \d{2}:\d{2}:\d{2}.*ERROR.* to find all error messages from a specific log file containing a date and timestamp. I’m also experienced with using log aggregation and analysis tools like Splunk and the Elastic Stack (ELK) to correlate events across multiple systems and identify patterns indicative of malicious activity.
A recent example involved analyzing web server logs to identify a SQL injection attempt. By analyzing timestamps, IP addresses, and request parameters, I was able to pinpoint the malicious activity and take necessary containment steps.
Q 10. How do you handle evidence preservation during an incident?
Evidence preservation is paramount in incident response. My approach follows a strict chain of custody protocol. This begins with isolating the compromised system(s) to prevent further damage or evidence tampering. I then create forensic images of hard drives and other storage devices using tools like FTK Imager or dd. These images are then cryptographically hashed to ensure their integrity. All actions are meticulously documented, including timestamps, tools used, and any changes made. This documentation forms the chain of custody, which is crucial for legal admissibility.
The principle is simple: treat everything as evidence. Avoid making unnecessary changes to the system. If alterations are necessary, they are documented and justified.
Q 11. Explain your understanding of malware analysis.
Malware analysis involves identifying and understanding the behavior of malicious software. My experience includes both static and dynamic analysis techniques. Static analysis involves examining the malware’s code without executing it, often using disassemblers like IDA Pro to reverse engineer its functionality. Dynamic analysis involves executing the malware in a controlled environment (e.g., a sandbox like Cuckoo Sandbox) and monitoring its behavior. This involves observing network connections, file system modifications, and registry changes.
For example, I might use static analysis to identify the malware’s entry point and its key functionalities. Then, I’d use dynamic analysis to observe its behavior in a controlled environment, which could reveal the malware’s command-and-control server, its data exfiltration methods, or its encryption techniques. Understanding these aspects is crucial for developing remediation strategies and preventing future infections.
Q 12. How do you communicate incident updates to stakeholders?
Clear and timely communication is critical during an incident response. My approach involves establishing a communication plan at the outset, identifying key stakeholders and their communication preferences. I use a combination of methods, including regular email updates for less urgent information, and immediate phone calls or video conferencing for critical updates. I also use a centralized platform, perhaps a dedicated incident response management system or a collaborative workspace like Slack, to centralize all communication and track progress. Reports typically follow a standardized format, detailing the incident’s impact, the containment and eradication steps taken, and any ongoing investigations.
Transparency and accuracy are key. Stakeholders need to understand the situation, the actions being taken, and the potential risks.
Q 13. What is your experience with incident response playbooks?
Incident response playbooks are crucial for efficient and consistent responses. My experience includes developing and refining playbooks based on industry best practices and lessons learned from previous incidents. A playbook outlines the standard operating procedures (SOPs) for responding to specific types of incidents, including steps for detection, containment, eradication, recovery, and post-incident activity. Playbooks promote consistency across teams, reduce response times, and ensure that critical steps aren’t missed under pressure. They also help to improve the overall efficiency of the incident response process. A well-structured playbook guides responders through the steps involved, which is particularly helpful during complex incidents.
Regular review and updates to the playbooks are essential to incorporate new threats and evolving technologies.
Q 14. Describe your experience with SIEM systems.
SIEM (Security Information and Event Management) systems are vital for incident detection and response. My experience includes using various SIEM platforms such as Splunk, QRadar, and Graylog. I’m proficient in configuring alerts, creating dashboards for real-time monitoring, and correlating events from diverse sources to identify potential threats. SIEM systems play a key role in early threat detection by aggregating and analyzing security logs from various sources and identifying patterns that might indicate malicious activity. I can use SIEMs to analyze historical data to investigate past incidents and improve future response strategies. Furthermore, they provide valuable insights for security posture improvements.
For example, I might use a SIEM to create an alert that triggers when a large number of failed login attempts originate from a single IP address, a clear indication of a potential brute-force attack.
Q 15. How do you handle social engineering attacks?
Social engineering attacks exploit human psychology to gain unauthorized access to systems or information. Think of it like a con artist – they manipulate you into revealing sensitive data or performing actions that compromise security. Handling these attacks requires a multi-pronged approach.
- Employee Training: Regular security awareness training is paramount. This includes phishing simulations, realistic scenarios, and education on identifying suspicious emails, phone calls, or messages. For example, we’d train employees to spot inconsistencies in email addresses or suspicious links before clicking.
- Technical Controls: Implementing strong technical safeguards complements training. This involves using multi-factor authentication (MFA) for all accounts, robust spam filters, and intrusion detection systems (IDS) to monitor for suspicious activity. For instance, an IDS can flag unusual login attempts from unexpected locations.
- Incident Response Plan: Having a clear incident response plan is crucial. This should include procedures for reporting, investigating, and containing social engineering attempts. If a successful attack is detected, the plan helps us minimize damage and learn from the incident.
- Strong Security Culture: Cultivating a culture of security within the organization encourages employees to report suspicious activity promptly. This should be reinforced with clear communication channels and a non-punitive approach to reporting errors.
In my experience, a combination of these measures significantly reduces the success rate of social engineering attacks. For instance, during my time at [Previous Company Name], we implemented a comprehensive training program that resulted in a 70% reduction in successful phishing attacks within six months.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. Explain the concept of digital forensics.
Digital forensics is the application of scientific methods to recover and analyze digital evidence. Think of it as a detective investigating a crime scene, but instead of physical clues, we’re dealing with computer data. It’s used to investigate cybercrimes, security breaches, and internal misconduct.
- Data Acquisition: The process begins with carefully preserving and acquiring data from various sources like hard drives, mobile devices, and network devices. This must be done in a way that maintains the chain of custody to ensure evidence admissibility in court.
- Data Analysis: Next, we analyze the collected data to identify evidence related to the incident. This can involve recovering deleted files, reconstructing timelines of events, examining network traffic logs, and analyzing malware samples. Specialized tools are used for this purpose, many of which leverage scripting (e.g., Python) for custom analysis.
- Evidence Reporting: Finally, a comprehensive report is generated documenting the findings, including timelines, evidence, and conclusions. This report is crucial for remediation, legal actions, or informing future security improvements.
For example, in a data breach investigation, digital forensics helps to determine the source of the breach, the extent of data exfiltration, and the methods used by the attackers. This information is vital for containment, remediation, and legal proceedings.
Q 17. What is your experience with threat hunting?
Threat hunting is a proactive security approach focused on identifying threats that haven’t yet triggered alerts. It’s not waiting for an alarm to go off; it’s actively searching for adversaries. I’ve extensive experience in this field, utilizing several techniques.
- Hypothesis-Driven Hunting: This involves formulating hypotheses based on threat intelligence, recent attack trends, and known vulnerabilities within the organization’s systems. For example, if a new malware variant targeting a specific type of database is reported, I’d actively search for evidence of its presence on our systems.
- Data Analysis: This is pivotal in threat hunting, utilizing Security Information and Event Management (SIEM) systems, endpoint detection and response (EDR) tools, and network traffic logs to identify anomalous behavior. We often leverage scripting languages like Python to automate data analysis and identify subtle patterns.
- Threat Intelligence Integration: Incorporating threat intelligence feeds helps prioritize hunting efforts, focusing on the most relevant and likely threats.
In a past engagement, I successfully identified a previously unknown piece of malware by analyzing unusual network traffic patterns that were not flagged by our standard security tools. This proactive approach helped us prevent a potential data breach.
Q 18. How do you perform vulnerability assessments?
Vulnerability assessments are systematic evaluations of an organization’s systems and infrastructure to identify security weaknesses. It’s like a health checkup for your IT systems.
- Automated Scanning: Automated tools scan systems for known vulnerabilities, often using databases like the National Vulnerability Database (NVD). These tools check for outdated software, misconfigurations, and known exploits.
- Manual Penetration Testing (Often Part of VA): While automated scanning covers known vulnerabilities, manual penetration testing is often integrated with VAs and goes deeper, simulating real-world attacks to find more subtle weaknesses.
- Configuration Reviews: Manual reviews assess the security configuration of systems and applications. This helps identify misconfigurations that could lead to vulnerabilities. For example, checking if default credentials have been changed.
- Reporting and Remediation: The assessment culminates in a detailed report that prioritizes vulnerabilities based on their severity and likelihood of exploitation. This report guides remediation efforts.
For instance, during a recent vulnerability assessment, we discovered a critical vulnerability in a web application that could have allowed attackers to gain complete control. The timely identification and remediation prevented a significant security incident.
Q 19. Describe your experience with penetration testing.
Penetration testing, or pen testing, simulates real-world attacks to identify security weaknesses. Unlike vulnerability assessments, which focus on identifying known vulnerabilities, pen testing attempts to exploit those vulnerabilities and any unknown ones. It’s about actively trying to break into a system.
- Planning and Scoping: This stage defines the targets, objectives, and rules of engagement. It’s crucial to get explicit permission for all activities.
- Reconnaissance: Gathering information about the target systems and networks, similar to how a real attacker would.
- Scanning and Enumeration: Identifying potential entry points and gathering information about the target’s systems.
- Exploitation: Attempting to exploit identified vulnerabilities.
- Post-Exploitation: Once access is gained, the tester assesses the extent of compromise and explores potential lateral movement.
- Reporting: A comprehensive report is generated detailing the findings, the steps taken to gain access, and recommendations for remediation.
In one project, I conducted a penetration test that uncovered a previously unknown vulnerability in a network device, allowing unauthorized access to sensitive data. This demonstrated the value of penetration testing in identifying vulnerabilities that could be missed by other security assessments.
Q 20. How do you respond to ransomware attacks?
Responding to a ransomware attack requires a swift and methodical approach. Time is of the essence.
- Containment: Immediately isolate infected systems from the network to prevent the ransomware from spreading. This may involve disconnecting the affected system from the network and shutting down servers.
- Data Recovery: Attempt data recovery from backups. Regular, tested backups are crucial for ransomware recovery. This might require specialized tools and techniques depending on the type of ransomware.
- Forensic Investigation: Conduct a forensic investigation to determine the extent of the damage, how the ransomware was introduced, and the data that was exfiltrated. The information from this investigation guides future prevention measures.
- Remediation: Reinstall affected systems, update software and security measures, and implement enhanced security controls to prevent future attacks. This often includes patching systems and changing passwords.
- Communication and Notification: Inform relevant stakeholders, including management, law enforcement (if necessary), and potentially affected individuals.
- Consider Paying Ransom (Caution): Paying the ransom should be a last resort and only considered after careful consideration of the risks and implications. Not all ransoms lead to data recovery, and paying can encourage future attacks.
In a past incident, we were able to contain a ransomware attack within hours, minimizing the impact by having robust backups and incident response procedures. The rapid response minimized the disruption and financial loss.
Q 21. What is your experience with incident response frameworks (e.g., NIST, ISO 27001)?
Incident response frameworks, such as NIST Cybersecurity Framework and ISO 27001, provide structured approaches to managing cybersecurity incidents. They offer a common language and methodology for handling incidents effectively.
- NIST Cybersecurity Framework: This framework focuses on five core functions: Identify, Protect, Detect, Respond, and Recover. It’s a flexible framework allowing organizations to tailor it to their specific needs and risk tolerance. I’ve extensively used the NIST framework, adopting and adapting its guidance to develop tailored response plans.
- ISO 27001: This international standard outlines requirements for establishing, implementing, maintaining, and continually improving an information security management system (ISMS). Its focus is broader than just incident response, encompassing risk management, security controls, and incident management.
- Practical Application: Both frameworks inform my approach to incident handling. For example, when faced with a security incident, I use the NIST framework’s five functions as a guide, from identifying the affected systems (Identify) to implementing recovery procedures (Recover). ISO 27001’s guidance helps ensure compliance and strengthen the overall security posture of the organization.
My experience spans multiple projects where these frameworks provided the backbone for successful incident response. The structured approach ensured that incidents were handled efficiently and effectively, minimizing damage and ensuring swift recovery.
Q 22. How do you ensure incident response readiness?
Ensuring incident response readiness is like preparing for a fire—you wouldn’t wait until the flames erupt to assemble the fire extinguisher, would you? It requires a proactive, multi-faceted approach. This involves establishing a robust incident response plan, conducting regular tabletop exercises and simulations, and continuously training and equipping your team.
- Develop a comprehensive Incident Response Plan (IRP): This document outlines procedures for identifying, containing, eradicating, recovering from, and learning from security incidents. It should define roles, responsibilities, escalation paths, and communication protocols.
- Implement security monitoring and logging: Continuous monitoring of systems and networks is crucial for early threat detection. Robust logging provides essential forensic evidence during an investigation.
- Regularly test and update your IRP: Simulations, such as tabletop exercises and penetration testing, reveal weaknesses and highlight areas for improvement. Your IRP is a living document and needs consistent updates.
- Establish communication channels: Clear and efficient communication is paramount. Determine who needs to be notified and how (e.g., email, SMS, dedicated communication platform) during an incident.
- Maintain an inventory of critical assets and data: Knowing what you have to protect is fundamental to effective response. This includes servers, applications, databases, and sensitive data.
For example, we regularly conduct phishing simulations to assess employee awareness and response. The results help refine our training programs and improve our overall security posture.
Q 23. Explain the importance of incident response planning.
Incident response planning is the cornerstone of effective cybersecurity. A well-defined plan minimizes damage, reduces downtime, and safeguards reputation. Think of it as a roadmap guiding you through a crisis. Without it, you’re navigating a storm blindfolded.
- Minimizes damage: A well-rehearsed plan enables swift action, limiting the impact of a breach.
- Reduces downtime: Faster recovery translates to less disruption to business operations.
- Protects reputation: A swift and effective response can mitigate negative publicity and maintain customer trust.
- Facilitates compliance: Many regulations (e.g., GDPR, HIPAA) require organizations to have incident response plans in place.
- Improves incident handling efficiency: A documented process ensures consistent and efficient responses to incidents, regardless of who is involved.
For instance, a clear plan ensures that the right people are notified promptly, the appropriate systems are isolated quickly, and forensic evidence is preserved, minimizing the potential for further damage and enhancing the investigation.
Q 24. Describe your experience with incident response training and certifications.
My incident response training is extensive. I’ve completed numerous courses focusing on incident handling methodologies, digital forensics, malware analysis, and incident response management. I hold certifications such as GIAC Certified Incident Handler (GCIH) and SANS GIAC Security Essentials (GSEC), demonstrating my commitment to continuous professional development. My experience ranges from participating in hands-on incident response simulations to conducting real-world investigations.
In one instance, I participated in a week-long advanced incident response training that included a realistic simulated cyber attack scenario. This immersive exercise tested our team’s skills in containment, eradication, and recovery, while emphasizing the importance of collaboration and communication. It enhanced my practical understanding and abilities significantly.
Q 25. How do you measure the effectiveness of your incident response program?
Measuring the effectiveness of an incident response program involves both quantitative and qualitative metrics. We use Key Performance Indicators (KPIs) to track our success and identify areas for improvement.
- Mean Time to Detect (MTTD): How long it takes to identify an incident.
- Mean Time to Respond (MTTR): How long it takes to contain and remediate an incident.
- Mean Time to Recovery (MTTR): How long it takes to restore systems and data to a normal operational state.
- Incident frequency: Tracking the number of incidents over time helps gauge overall security effectiveness.
- Post-incident review effectiveness: Evaluating the lessons learned from each incident to refine our processes.
We also use qualitative measures, like feedback from post-incident reviews and internal audits, to assess the effectiveness of our response team’s actions and communication during an incident. Regular review of these metrics reveals areas for improvement, allowing for continuous refinement of our program.
Q 26. What are the legal and regulatory considerations in incident response?
Legal and regulatory considerations are paramount in incident response. Failing to comply can result in significant financial penalties and reputational damage. Key considerations include:
- Data privacy laws (e.g., GDPR, CCPA): These laws dictate how personal data must be handled and protected. In case of a breach, prompt notification is often legally mandated.
- Data breach notification laws: Many jurisdictions require organizations to notify affected individuals and regulatory bodies within a specific timeframe following a data breach.
- Industry-specific regulations (e.g., HIPAA, PCI DSS): These regulations outline specific security requirements and incident response procedures for particular industries.
- Forensics and evidence preservation: Legal holds and proper chain of custody procedures are crucial to ensure the admissibility of evidence in any subsequent legal proceedings.
- Legal counsel consultation: Seeking legal counsel early in the response process is essential to ensure compliance and protect the organization’s interests.
For example, under GDPR, organizations must report certain types of data breaches to the relevant supervisory authority within 72 hours. Failure to do so can result in substantial fines.
Q 27. How do you collaborate with other teams during an incident?
Collaboration is critical during an incident. It’s a team sport. I leverage established communication channels and clearly defined roles to ensure efficient cooperation.
- Establish a central communication hub: This could be a dedicated communication platform, a conference call, or a shared document repository.
- Define roles and responsibilities: Each team member should have a clearly defined role (e.g., incident commander, forensic investigator, communications lead).
- Regular status updates: Frequent communication keeps everyone informed about the situation’s progress.
- Utilize collaboration tools: Tools like ticketing systems, collaborative document editors, and communication platforms facilitate efficient communication and information sharing.
- Maintain a clear chain of command: A clear reporting structure prevents confusion and ensures decisions are made efficiently.
In practice, we use a dedicated communication platform to maintain a central record of all communications and actions taken during an incident. This ensures transparency and allows all stakeholders to remain informed.
Q 28. Describe a challenging incident response experience and how you overcame it.
One particularly challenging incident involved a sophisticated ransomware attack that encrypted a significant portion of our client’s critical data. The attackers used a previously unknown variant of ransomware, making initial analysis and decryption difficult.
We overcame this challenge by adopting a methodical, multi-pronged approach. First, we immediately isolated affected systems to prevent further spread. Second, we engaged specialized cybersecurity firms with expertise in ransomware decryption. Simultaneously, we focused on restoring data from backups, prioritizing critical systems. We also engaged in thorough forensic analysis to identify the attack vector and vulnerabilities. Effective communication with our client throughout the process was crucial to maintaining trust and confidence.
The experience highlighted the importance of having robust backups, proactive security measures (like endpoint detection and response), and partnerships with specialized cybersecurity firms. This incident also drove significant improvements in our security posture, including enhanced employee training on phishing awareness and improved security monitoring capabilities.
Key Topics to Learn for Understanding of Cybersecurity Incident Response Interview
- Incident Identification and Classification: Understanding the various types of security incidents (malware, phishing, denial-of-service, etc.) and their potential impact. Practical application: Analyzing log files to identify suspicious activity.
- Containment and Eradication: Techniques for isolating infected systems and removing malware. Practical application: Implementing network segmentation and utilizing endpoint detection and response (EDR) tools.
- Recovery and Remediation: Restoring systems and data to a secure state. Practical application: Developing and testing recovery plans, including data backups and system restore procedures.
- Forensic Analysis: Gathering and preserving digital evidence for investigation and legal purposes. Practical application: Understanding chain of custody and using forensic tools to analyze hard drives.
- Incident Response Planning and Communication: Developing and practicing incident response plans, including communication protocols with stakeholders. Practical application: Participating in tabletop exercises and creating communication templates.
- Vulnerability Management and Patching: Identifying and mitigating vulnerabilities in systems and applications. Practical application: Implementing a vulnerability scanning program and deploying security patches.
- Post-Incident Activity: Conducting post-incident reviews to identify lessons learned and improve future response capabilities. Practical application: Analyzing incident reports to identify areas for improvement in security policies and procedures.
- Legal and Regulatory Compliance: Understanding relevant laws and regulations related to data breaches and incident response. Practical application: Ensuring compliance with regulations like GDPR or CCPA.
Next Steps
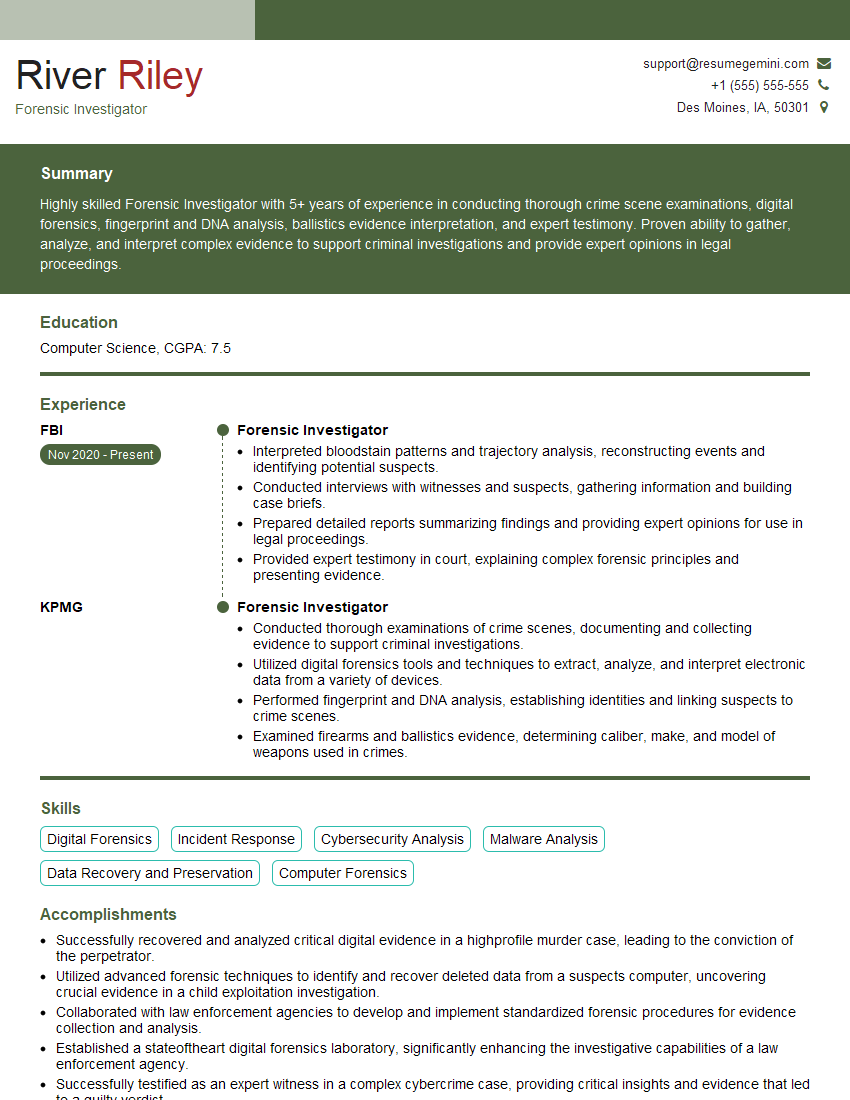
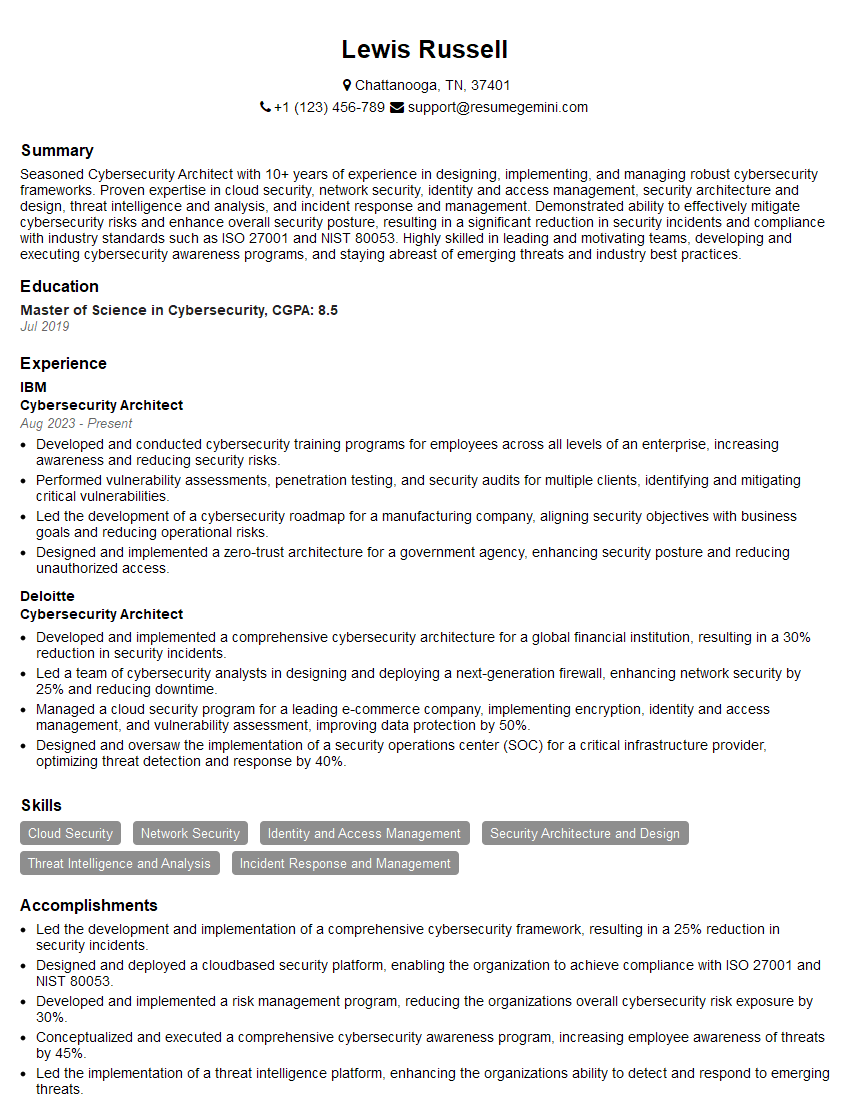
Mastering Cybersecurity Incident Response is crucial for career advancement in the ever-evolving cybersecurity landscape. Demonstrating a strong understanding of these concepts significantly enhances your job prospects. To further strengthen your application, focus on creating a compelling and ATS-friendly resume that highlights your skills and experience effectively. We encourage you to leverage ResumeGemini, a trusted resource for building professional resumes, to create a document that showcases your expertise. Examples of resumes tailored to Understanding of Cybersecurity Incident Response are available to help guide you. Investing time in crafting a strong resume is an investment in your future career success.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good