Are you ready to stand out in your next interview? Understanding and preparing for HUMINT interview questions is a game-changer. In this blog, we’ve compiled key questions and expert advice to help you showcase your skills with confidence and precision. Let’s get started on your journey to acing the interview.
Questions Asked in HUMINT Interview
Q 1. Explain the difference between HUMINT and other intelligence disciplines (SIGINT, OSINT, etc.).
HUMINT, or Human Intelligence, stands apart from other intelligence disciplines by focusing solely on information gathered from human sources. Unlike SIGINT (Signals Intelligence), which intercepts electronic communications, or OSINT (Open-Source Intelligence), which utilizes publicly available information, HUMINT relies on direct interaction and relationships with individuals possessing valuable knowledge. Consider it like this: SIGINT is like eavesdropping on a phone call, OSINT is like reading a newspaper, but HUMINT is like having a trusted informant tell you secrets directly. This direct interaction offers unparalleled depth and context, but also requires a far greater level of trust, risk management, and operational security.
- SIGINT: Focuses on electronic signals, including communications, radar, and electronic emissions.
- OSINT: Relies on publicly accessible data such as news articles, social media, and government reports.
- HUMINT: Relies on cultivated relationships with human sources who provide firsthand information.
- MASINT: Measures and Signatures Intelligence uses open-source, commercially available data to understand patterns and signatures.
- GEOINT: Geo-spatial Intelligence uses satellite imagery, mapping, and other geographical data.
The key difference lies in the method of acquisition. While other disciplines might passively collect data, HUMINT is an active, interpersonal process requiring sophisticated relationship building and management.
Q 2. Describe the process of developing and managing a HUMINT source.
Developing and managing a HUMINT source is a delicate, long-term process demanding patience, discretion, and strong interpersonal skills. It begins with identifying a potential source, someone with access to valuable information. This might involve extensive research, network analysis, and even chance encounters. The process can be broken down into several key stages:
- Identification and Assessment: Researching potential sources to determine their access to relevant information and their reliability.
- Recruitment: Building rapport and trust, ultimately persuading the source to cooperate. This often involves a slow, carefully crafted approach, addressing their motivations and concerns.
- Handling: Managing the relationship, providing appropriate compensation or protection, and regularly meeting to obtain information. This involves careful planning of meetings, secure communication methods, and maintaining operational security.
- Debriefing: Systematically extracting information in a way that is both thorough and sensitive. This frequently involves multiple debriefings, and careful note-taking of the source’s account.
- Assessment and Validation: Verifying the information’s accuracy and reliability through cross-referencing and corroboration. This crucial step helps to mitigate the risk of misinformation.
- Protection: Ensuring the source’s safety and security, sometimes involving relocation or other protective measures. This is paramount and could involve collaboration with other branches of the intelligence community.
Throughout the process, meticulous record-keeping is essential, including detailed accounts of interactions, payments, and any relevant information about the source. Regular reassessment of the source’s value and reliability is also critical.
Q 3. What are the ethical considerations involved in HUMINT collection?
Ethical considerations are paramount in HUMINT. The potential for abuse is significant, and maintaining the highest ethical standards is crucial for the integrity of the intelligence process and the safety of both the sources and the agency. Key ethical concerns include:
- Consent and Deception: The use of deception, while sometimes necessary, must be carefully considered and minimized. Sources should be fully informed about the risks involved, whenever possible.
- Coercion and Duress: Obtaining information through coercion, threats, or physical harm is strictly prohibited and unethical. Sources should cooperate willingly.
- Privacy and Confidentiality: Protecting the identity and privacy of sources is essential. Information obtained through HUMINT should be handled with the utmost discretion and security, consistent with applicable laws and regulations.
- Protection of Sources: Protecting sources from harm, both physical and reputational, is a fundamental ethical responsibility. Agencies must take appropriate steps to safeguard their sources.
- Legal and Regulatory Compliance: HUMINT operations must comply with all applicable laws and regulations, both domestically and internationally. This includes regulations regarding surveillance, data protection, and human rights.
These ethical considerations are woven into the fabric of HUMINT operations and require constant vigilance and consideration. Ethics training is integral to a HUMINT officer’s training and continued professional development.
Q 4. How do you assess the credibility and reliability of a HUMINT source?
Assessing the credibility and reliability of a HUMINT source is an ongoing process. It involves a combination of techniques and careful analysis. There is no single definitive method, but rather a holistic assessment drawing upon various indicators.
- Source Motivation: Understanding the source’s motivations—ideological, financial, or personal—is crucial. A source’s biases and agendas can impact the reliability of their information.
- Track Record: Assessing the source’s past performance and the accuracy of their previous information is vital. Consistent accuracy enhances credibility.
- Information Corroboration: Verifying the information received through independent means is essential. Cross-referencing with other sources or evidence strengthens the reliability of the information.
- Behavioral Analysis: Observing the source’s demeanor, consistency in their statements, and overall behavior can reveal valuable insights into their trustworthiness. Inconsistent statements are a red flag.
- Deception Detection Techniques: Skilled HUMINT officers employ various techniques to identify deceptive behavior. Careful questioning, observation, and the use of polygraph testing (where applicable and legally permissible) can aid in determining the truthfulness of the source.
The assessment is dynamic; a source’s reliability can change over time. Continuous monitoring and reassessment are essential for maintaining an accurate understanding of the source’s credibility.
Q 5. Explain the concept of ‘tradecraft’ in HUMINT.
Tradecraft in HUMINT refers to the specialized skills and techniques used in all aspects of the intelligence process. It encompasses everything from identifying and recruiting sources to handling sensitive information and maintaining operational security. Think of it as the ‘art and science’ of gathering intelligence from human sources.
- Surveillance: Observing targets without detection, utilizing various methods and technologies.
- Covert Communication: Securing communication channels to prevent interception and maintain anonymity.
- Source Recruitment & Handling: Building rapport, maintaining relationships, and managing sensitive interactions.
- Elicitation: Skillfully extracting information from individuals through questioning and observation.
- Operational Security (OPSEC): Protecting intelligence activities from compromise by maintaining secrecy and vigilance.
- Counterintelligence: Protecting against espionage and sabotage, identifying and neutralizing threats.
Effective tradecraft demands a high level of expertise and discipline. It’s a constantly evolving field, requiring continuous adaptation to new technologies and countermeasures. Continuous professional development through training is therefore crucial. Poor tradecraft can lead to compromised operations, damaged sources, and even the loss of life.
Q 6. Describe different methods used for HUMINT source recruitment.
HUMINT source recruitment involves a variety of methods, each tailored to the specific circumstances and the type of source being targeted. Some common methods include:
- Walk-ins: Individuals who voluntarily approach intelligence agencies with information.
- Pre-positioning of Assets: Identifying and cultivating relationships with potential sources long before an intelligence requirement arises.
- Targeted Recruitment: Identifying and actively recruiting individuals believed to possess valuable information, based on intelligence analysis.
- Networking: Leveraging existing networks and contacts to identify and recruit sources.
- Compromised individuals: Recruiting individuals who have been compromised or identified as having vulnerabilities.
- Brokering: Utilizing intermediaries or third parties to establish contact with sources.
Each method requires a different approach and necessitates careful consideration of ethical implications and operational security. Successful recruitment depends on building trust, understanding the source’s motivations, and offering incentives while managing risks. Every recruitment scenario requires careful planning and execution.
Q 7. How do you handle sensitive information obtained through HUMINT?
Handling sensitive information obtained through HUMINT requires strict adherence to security protocols and procedures. The goal is to protect the information’s integrity, confidentiality, and availability, while also protecting the source’s identity and safety.
- Classification: Assigning appropriate security classifications to the information based on its sensitivity.
- Access Control: Limiting access to the information based on need-to-know principles.
- Secure Storage: Storing the information in secure facilities and using secure methods (e.g., encrypted databases).
- Secure Communication: Using secure communication channels for transmitting the information.
- Data Destruction: Implementing secure methods for destroying the information when it is no longer needed.
- Source Protection: Taking steps to protect the source’s identity and safety from disclosure or harm.
Failure to properly handle sensitive information can have serious consequences, including compromising operations, jeopardizing sources, and causing significant damage to national security. Regular security training and adherence to established protocols are crucial.
Q 8. What are the challenges of operating in a clandestine environment for HUMINT?
Operating clandestinely in HUMINT presents a unique set of challenges, primarily revolving around risk mitigation and operational security. The very nature of the work – secretly gathering information from human sources – necessitates operating outside the bounds of normal visibility and legal frameworks.
- Maintaining Secrecy: The constant threat of exposure is paramount. A compromised agent or operation can have devastating consequences, including the loss of sources, mission failure, and potential harm to individuals.
- Building Trust: Establishing rapport and trust with human sources is crucial. This requires patience, skill in interpersonal communication, and a deep understanding of human psychology. Building this trust, however, can take considerable time and effort and is often fragile.
- Logistical Difficulties: Clandestine operations frequently involve operating in hostile or restrictive environments, potentially with limited resources and communication capabilities. This might mean working in dangerous locations, navigating complex legal landscapes or dealing with unreliable infrastructure.
- Ethical Considerations: HUMINT inherently involves navigating a grey area ethically. Balancing the need for information with the rights and safety of sources and the public is crucial. We must always adhere to strict ethical guidelines and legal boundaries.
- Counter-Intelligence Threats: The possibility of being identified and targeted by the opposing side is always present. This requires vigilance, sophisticated tradecraft, and constant adaptation to evolving threats.
For example, during a deployment in a politically unstable region, I had to navigate complex social structures and build trust with a source who was initially hesitant to cooperate due to fear of reprisal. It required weeks of careful relationship-building, showing empathy and demonstrating genuine commitment to their safety.
Q 9. How do you maintain operational security (OPSEC) in HUMINT operations?
Maintaining OPSEC in HUMINT is paramount to mission success and the safety of sources and operatives. It’s about minimizing the risk of exposure at every stage of an operation. This involves a multi-layered approach, constantly evaluating potential risks and implementing countermeasures.
- Compartmentalization: Restricting access to information on a need-to-know basis. Not everyone needs to know all aspects of the operation.
- Secure Communications: Employing encrypted channels and secure methods for communication with sources and within the team. This protects sensitive information from interception.
- Cover Stories and Legends: Developing plausible and believable cover stories for operatives and their activities to disguise their true purpose. This reduces the likelihood of drawing attention or suspicion.
- Physical Security: Choosing secure meeting locations and utilizing appropriate surveillance detection techniques. This might involve thorough background checks on locations and using counter-surveillance techniques.
- Source Handling Procedures: Establishing secure communication protocols and meeting procedures with sources to prevent their compromise or discovery.
- Traffic Analysis: Monitoring communication patterns to identify potential leaks or compromise.
For instance, when working with a source in a high-surveillance environment, I employed secure encrypted communication channels, used a complex, regularly changed meeting schedule in untraceable locations and ensured all communication was kept concise and limited to critical information only.
Q 10. How do you analyze and interpret HUMINT data to produce actionable intelligence?
Analyzing and interpreting HUMINT data requires a systematic approach combining critical thinking, contextual understanding, and analytical skills. It’s not simply about collecting information; it’s about transforming raw data into actionable intelligence that supports decision-making.
- Data Validation: Cross-referencing information from multiple sources to verify its accuracy and credibility. Inconsistencies need careful investigation.
- Contextualization: Understanding the historical, political, social, and cultural context surrounding the information. This allows for a more nuanced interpretation.
- Pattern Recognition: Identifying recurring themes, trends, and relationships within the data. This helps to reveal deeper insights.
- Correlation: Integrating HUMINT with other intelligence disciplines (SIGINT, IMINT, OSINT) to create a more comprehensive picture. This improves the reliability and completeness of the intelligence assessment.
- Threat Assessment: Evaluating the significance and potential impact of the information on national security or other objectives. This defines priorities and actions.
For example, during an investigation, I received conflicting information from two different sources. By cross-referencing it with open-source information and comparing communication patterns, I was able to verify the more accurate information and determine the source of the conflicting intelligence. This ultimately allowed me to create a precise and reliable intelligence report.
Q 11. Describe your experience with using different HUMINT techniques.
My experience encompasses a broad range of HUMINT techniques, adapted to specific operational contexts and requirements. These techniques are not mutually exclusive and often complement each other.
- Source Recruitment and Development: This involves identifying potential sources, building rapport, and managing relationships to obtain information reliably over time. I’ve successfully recruited sources through various methods, including cultivating existing relationships and using network analysis.
- Elicitation: Employing skilled questioning techniques to extract information from a source, while remaining mindful of the emotional dynamics and respecting their cooperation. This can range from casual conversations to highly structured interviews.
- Surveillance and Observation: Discreetly monitoring individuals or locations to gather visual information relevant to the intelligence objectives. It is vital to minimize risk and maintain secrecy.
- Debriefing: Conducting systematic interviews to obtain detailed information from sources, using a structured approach to maximize information extraction while maintaining the source’s confidence.
- Open Source Intelligence (OSINT) Gathering: Gathering relevant information from publicly available sources. OSINT provides context and can augment data from human sources.
In one case, I successfully used a combination of elicitation techniques and surveillance to uncover a smuggling operation by observing patterns in behavior and logistics and extracting key details through carefully worded conversations with an unwitting accomplice.
Q 12. Explain how you would handle a compromised HUMINT source.
Handling a compromised HUMINT source is a critical situation demanding immediate and decisive action to mitigate damage and protect remaining assets. The process involves a series of steps, prioritizing damage control and future security.
- Damage Assessment: Determining the extent of the compromise, identifying what information was exposed, and who may have access to it. This is crucial in order to determine the scope of the problem.
- Source Protection: Taking immediate steps to protect the source from harm, potentially relocating them or altering their cover story. Their safety is a top priority.
- Operational Adjustments: Reviewing and modifying operational procedures to prevent future compromises. This might involve changes to communication methods or source handling protocols.
- Counter-Intelligence Measures: Investigating how the compromise occurred, identifying any potential leaks within the organization, and taking steps to eliminate those vulnerabilities.
- Intelligence Review: Assessing the credibility and integrity of intelligence previously obtained from the compromised source. Existing analysis may need reassessment.
For example, when a source was unexpectedly compromised, I immediately initiated a series of measures including relocating the source, altering their communications protocol, and launching a comprehensive internal investigation to identify the points of failure and prevent further incidents.
Q 13. How do you debrief a HUMINT source effectively?
Effectively debriefing a HUMINT source requires a structured approach that builds trust, encourages open communication, and maximizes information gathering while minimizing potential risk to the source and mission.
- Rapport Building: Creating a relaxed and comfortable atmosphere to encourage the source to share information freely. This begins before the formal debrief begins, building a positive relationship over time.
- Structured Questioning: Employing techniques that facilitate the collection of accurate, detailed information, from open-ended questions to probing for deeper understanding.
- Active Listening: Paying close attention to both verbal and nonverbal cues. Understanding body language, tone, and hesitation can add more meaning to the source’s information.
- Information Validation: Cross-checking information against other sources and intelligence to verify its accuracy and reliability. This helps to build a complete picture of the events.
- Documentation: Maintaining a detailed record of the debriefing session, including the date, time, location, individuals present, and all information shared by the source. This is vital for accountability and clarity.
During a debrief, I employed a combination of open-ended questions, targeted follow-up questions, and active listening to extract a maximum of relevant information from the source. I also made sure to reassure the source of their safety and anonymity, fostering a sense of trust and encouraging complete cooperation. This resulted in a rich body of intelligence that significantly benefited our investigation.
Q 14. Describe your experience with writing intelligence reports based on HUMINT.
Writing intelligence reports based on HUMINT requires a clear, concise, and objective style that effectively communicates the findings to decision-makers. The report needs to be organized, analytical and focused on providing actionable intelligence.
- Structured Format: Following a standardized format, including an executive summary, background information, analysis, conclusions, and recommendations. This ensures clarity and easy understanding.
- Clarity and Conciseness: Using precise language and avoiding jargon or unnecessary details. The report must be readily accessible to a wide range of readers.
- Objectivity and Impartiality: Presenting information fairly and avoiding subjective interpretations or opinions. Facts should be clearly separated from assumptions.
- Source Attribution: Clearly identifying the source of information and assessing their credibility. This allows recipients to evaluate the reliability of the intelligence.
- Actionable Intelligence: Focusing on the implications of the findings and providing specific recommendations for action. This focuses on how this information can be used to solve problems.
In one instance, I drafted a report analyzing the operational capabilities of a terrorist cell, based on information gathered from several human sources. My report included a detailed assessment of their strengths and weaknesses, identified potential targets, and recommended specific countermeasures, effectively informing policy and tactical decisions.
Q 15. How do you evaluate the value of HUMINT information?
Evaluating HUMINT information involves a multifaceted assessment focusing on its relevance, reliability, and timeliness. Relevance considers whether the information directly addresses the intelligence requirement. Reliability hinges on the source’s credibility, track record, and corroboration with other intelligence. Timeliness is crucial; outdated information is often useless. We use a scoring system, weighting each factor, to generate a numerical value representing the information’s overall worth. For instance, highly reliable information directly addressing a critical need receives a higher score than less reliable information of marginal relevance. This scoring helps prioritize analysis and dissemination efforts.
Example: Imagine we’re tracking a weapons shipment. Information from a known reliable source specifying the shipment’s exact location and departure time would score much higher than a vague rumor from an unverified source.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. Explain your understanding of different types of HUMINT reporting formats.
HUMINT reporting formats vary depending on urgency and detail. Spot reports provide immediate, concise updates on urgent events. Think of them as quick situation summaries. Sitreps (situation reports) offer a broader, more detailed picture of a situation over a specific period. Analytical reports delve deeper, analyzing information and drawing conclusions. Narrative reports provide a detailed account of an event or interaction, like a detailed debriefing of a clandestine meeting. The choice depends on the intelligence requirement. A suspected imminent attack might call for a spot report, while long-term monitoring might necessitate a detailed analytical report.
Q 17. How do you deal with conflicting information from multiple HUMINT sources?
Conflicting information from multiple HUMINT sources requires careful analysis and triangulation. We assess the credibility of each source – their track record, motivation, and potential biases. We also look for corroborating evidence from other sources, including SIGINT, IMINT, or OSINT. Cross-referencing helps identify inconsistencies and potential inaccuracies. If a reliable source contradicts a less reliable one, we prioritize the more credible information. Sometimes, the conflict itself might be significant intelligence; it could point to deception or competing factions. We may need to conduct further investigation to resolve the discrepancies.
Example: Two sources provide information about an upcoming terrorist attack. One, a known reliable informant, pinpoints the target and time; the other, a less reliable source, claims a different location. We’d prioritize investigating the first source’s information further while not dismissing the second entirely, as the discrepancy might hint at a decoy attack.
Q 18. Describe your understanding of the legal and regulatory framework governing HUMINT.
The legal and regulatory framework governing HUMINT is complex and varies by country. It generally encompasses laws relating to privacy, surveillance, and human rights. In many countries, activities like warrantless surveillance are highly restricted; appropriate authorization is required. The handling of classified information is governed by strict rules about access, storage, and dissemination. Ethical considerations are paramount; deception, coercion, and physical harm are usually prohibited. Failure to adhere to these regulations can lead to serious legal consequences, including criminal prosecution.
Q 19. How do you prioritize HUMINT collection efforts?
Prioritizing HUMINT collection efforts requires a strategic approach focusing on intelligence requirements and available resources. We use a system that assesses the value of information based on its relevance to national security priorities, the potential impact of the information, and the feasibility of acquiring it. High-priority targets receive more resources and attention. We also consider the availability of reliable sources, the operational risks involved, and the potential for counterintelligence threats.
Example: During a crisis, information related to immediate threats to national security might take precedence over long-term strategic goals. The allocation of resources – human agents, funding, and technology – reflects this prioritization.
Q 20. Explain your experience with using technology to support HUMINT operations.
Technology plays an increasingly significant role in HUMINT. Secure communication systems, including encrypted messaging and data storage, are essential for maintaining operational security. Data analysis tools assist in identifying patterns, connections, and trends within large datasets derived from HUMINT. Geographic Information Systems (GIS) are used to visualize locations, movements, and relationships between individuals and entities. Social media monitoring tools can provide valuable insights into individuals’ activities and affiliations. These technological tools enhance the efficiency and effectiveness of HUMINT operations.
Q 21. How do you manage risk in HUMINT operations?
Managing risk in HUMINT operations is critical. This involves identifying potential threats to sources, agents, and operations. Risks include exposure, compromise, capture, and the potential for unintended consequences. We mitigate these risks through robust operational security procedures, including secure communication channels, controlled access to information, and stringent vetting processes for sources and agents. Contingency planning, including escape routes and emergency communication protocols, is essential. Regular risk assessments are conducted to identify and address emerging threats and vulnerabilities.
Q 22. How do you build rapport and trust with HUMINT sources?
Building rapport and trust with HUMINT sources is the cornerstone of successful intelligence gathering. It’s a process built on empathy, active listening, and demonstrating genuine respect for the source’s perspective. Think of it like building any strong relationship – it takes time, patience, and consistent effort.
- Active Listening: Truly listen to understand their concerns, motivations, and fears. Avoid interrupting and show that you value their input.
- Empathy and Understanding: Put yourself in their shoes. Understand their background, their situation, and what motivates them to share information. This often involves understanding their needs and fears.
- Demonstrating Reliability and Discretion: This is paramount. Keep your promises, maintain confidentiality, and only ask for what is necessary. If you reveal something you shouldn’t have, you’ve lost credibility immediately.
- Building a Relationship, Not Just an Information Exchange: Focus on establishing a long-term relationship built on mutual respect. This involves occasional check-ins, even if information isn’t being exchanged. Consider this a long-term investment.
- Reciprocity: Whenever possible and ethically sound, be willing to provide something of value in return for the information shared, this could be non-monetary, like helping a source with a problem or protecting their identity.
For example, I once worked with a source who was hesitant to provide information due to past betrayals. It took several months of building trust, demonstrating my discretion, and proving my commitment to their safety before they felt comfortable sharing sensitive intelligence.
Q 23. Explain your understanding of deception and counter-deception techniques in HUMINT.
Deception and counter-deception are inherent parts of HUMINT. Sources may intentionally mislead, while intelligence officers must employ strategies to detect and mitigate deception. It’s a continuous game of cat and mouse.
- Deception Techniques: Sources might employ misinformation (providing false information), disinformation (spreading false information to create a specific narrative), or camouflage (concealing their true intentions or identity).
- Counter-Deception Techniques: This involves verifying information from multiple sources, employing behavioral analysis (examining body language and demeanor for inconsistencies), cross-referencing information with open-source intelligence, and using deception detection technologies where available.
- Psychological manipulation: Sources might use psychological manipulation to gain the officer’s trust or to alter the course of an investigation. Therefore, it’s crucial to be aware of psychological manipulation tactics and ensure that biases do not cloud judgement.
A real-world example involves verifying a source’s claim about an impending attack. Instead of solely relying on one source, we would cross-reference this information with other intelligence, conduct physical surveillance, and analyze open-source data for corroboration.
Q 24. How do you protect the identity of HUMINT sources?
Protecting the identity of HUMINT sources is critical and requires stringent measures. The safety of our sources is paramount. Compromising a source can have severe repercussions, including imprisonment or death for the source, and the loss of future intelligence.
- Code Names and Pseudonyms: We use code names and pseudonyms to prevent direct association with real identities.
- Secure Communication Channels: This includes encrypted messaging, secure voice communication, and secure in-person meetings in controlled environments.
- Limited Access to Information: Only individuals with a need-to-know should have access to information that could compromise a source’s identity.
- Data Security Protocols: All data is handled according to the highest security protocols, including secure storage, access controls, and data destruction procedures.
- Compartmentalization: This critical procedure ensures different team members are aware of limited information regarding the source.
For example, if a source is providing information about a criminal organization, we might only reveal to those on the operation the source’s code name and other identifying factors crucial to the operation. The source’s true identity would remain known only to a few trusted individuals, and the rest of the team would not know their name, appearance, or residence.
Q 25. Describe your experience with covert communication techniques.
Covert communication techniques are essential for maintaining secrecy and security in HUMINT operations. These techniques range from simple methods to sophisticated technologies, always tailored to the specific operational context.
- Dead Drops: A discreet location where information is exchanged without direct contact. This could be a specific location, time, or object.
- Steganography: Hiding information within seemingly innocuous media, such as images or text files.
- Encrypted Messaging Applications: Secure messaging apps like Signal or similar platforms allow for encrypted communication, protecting messages from interception. This should only be used with the authorization from appropriate officials.
- Secure Voice Communication: This involves using secure channels for voice conversations, including encryption and secure telephone technologies.
- In-person meetings with stringent security protocols: This might involve carefully selecting meeting locations, using counter-surveillance techniques, and employing strict communication protocols.
For instance, we might use a dead drop to receive a flash drive containing encrypted data from a source who operates under strict surveillance.
Q 26. Explain how you would handle a situation where a HUMINT source provides unreliable information.
Handling unreliable information from a HUMINT source requires a methodical approach. It’s crucial to maintain the relationship while carefully verifying the information.
- Verification: The information must be independently verified using other sources and intelligence. This could include open-source intelligence, technical intelligence, or other HUMINT sources.
- Source Evaluation: We would assess the source’s reliability and motivations. This could involve reviewing past information provided by the source and determining their track record.
- Further Interaction with Source: Instead of dismissing the source, it’s crucial to engage in further interactions. This allows to gauge whether the information was intentional misinformation or an honest mistake. It is also a chance to probe the source for further information, which might reveal more contextual information and help clarify the nature of the unreliable data.
- Deception Detection: Behavioral analysis and other deception detection techniques can be used to ascertain the source’s credibility.
- Documenting the Discrepancies: Maintaining a detailed record of the inconsistencies found is paramount. This allows for the proper assessment of the situation and informs future operational decisions.
For example, if a source provides information about an impending attack, but that information contradicts other intelligence, we would not immediately dismiss it. Instead, we would investigate further, possibly by using additional methods to determine the source of the discrepancy and its significance.
Q 27. How do you utilize open-source information to support your HUMINT efforts?
Open-source intelligence (OSINT) plays a crucial role in supporting HUMINT efforts. It provides context, corroboration, and leads for further investigation. It’s often the first step in any investigation.
- Contextual Information: OSINT provides background information on individuals, organizations, and events, enriching the understanding of the HUMINT information obtained.
- Corroboration: OSINT data can be used to verify or refute information provided by HUMINT sources, increasing the confidence in the intelligence gathered.
- Lead Generation: OSINT can identify potential HUMINT sources or uncover additional information that requires further HUMINT investigation.
- Trend Analysis: Analyzing OSINT data over time can help identify emerging patterns or trends that might indicate future events or actions.
For example, if a HUMINT source mentions a specific company involved in illicit activities, we would use OSINT to investigate the company’s background, financial records, and public statements to corroborate the source’s information. This may also uncover other individuals or entities associated with the company that are potential HUMINT sources.
Q 28. What are the key differences between strategic and tactical HUMINT?
Strategic and tactical HUMINT differ primarily in their scope and objectives. Think of it like a military operation: strategic HUMINT is the overall war plan, while tactical HUMINT is the battle plan.
- Strategic HUMINT: Focuses on long-term intelligence needs, providing insights into the overall intentions, capabilities, and vulnerabilities of adversaries or targets at the strategic level. It informs high-level decision-making and provides overall national security assessments.
- Tactical HUMINT: Focuses on immediate intelligence requirements, providing timely information for short-term operations or specific tasks. It directly supports the execution of specific missions or operations and is crucial for informed decisions and risk assessments at the operational level.
For example, strategic HUMINT might involve identifying the long-term intentions of a foreign government, while tactical HUMINT might involve gathering information about a specific terrorist cell planning an imminent attack. Both are essential, but they operate at different levels and contribute to different aspects of intelligence-led decision-making.
Key Topics to Learn for HUMINT Interview
- Source Selection & Development: Understand the principles of identifying, recruiting, and managing human intelligence sources. Consider the ethical and legal implications.
- Elicitation Techniques: Learn various methods for extracting information from sources, emphasizing rapport building, active listening, and non-verbal communication. Practice applying these in simulated scenarios.
- Information Assessment & Analysis: Develop skills in evaluating the credibility and reliability of information gathered from human sources. Understand how to identify biases and inconsistencies.
- Rapport Building & Interpersonal Skills: Recognize the critical role of trust and empathy in successful HUMINT operations. Practice active listening, nonverbal communication, and building relationships.
- Deception Detection: Explore methods and techniques for identifying deception in verbal and nonverbal communication. Consider the challenges and limitations of deception detection.
- Security & Operational Tradecraft: Understand the importance of operational security and the potential risks associated with HUMINT operations. Familiarize yourself with basic security protocols and best practices.
- Legal & Ethical Considerations: Understand the legal framework governing HUMINT activities and the ethical responsibilities involved in working with human sources.
- Report Writing & Documentation: Develop clear and concise writing skills for documenting HUMINT findings. Understand the importance of accurate and detailed reporting.
Next Steps
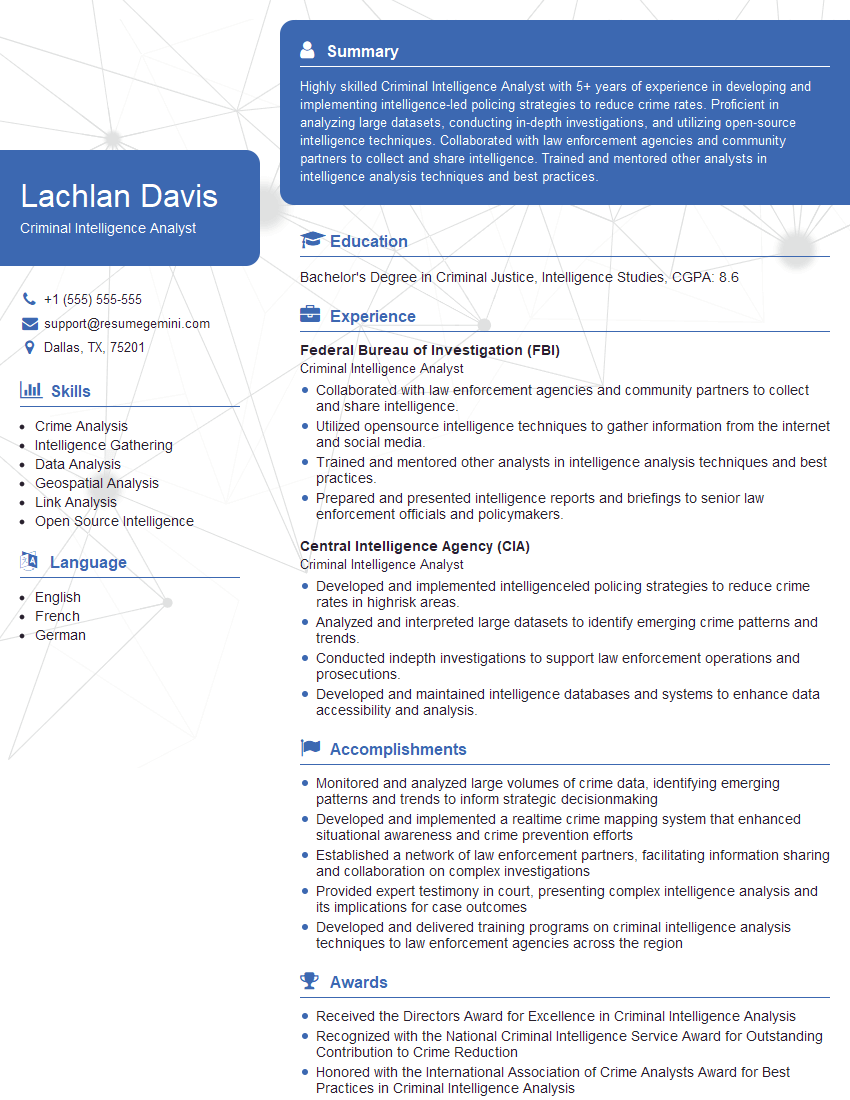
Mastering HUMINT opens doors to a dynamic and impactful career, offering opportunities for growth and contributing to critical national security objectives. To maximize your job prospects, focus on creating a strong, ATS-friendly resume that effectively showcases your skills and experience. ResumeGemini is a trusted resource that can help you build a professional and impactful resume tailored to the HUMINT field. Examples of resumes specifically tailored to HUMINT roles are available to guide you.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good