Cracking a skill-specific interview, like one for Consul, requires understanding the nuances of the role. In this blog, we present the questions you’re most likely to encounter, along with insights into how to answer them effectively. Let’s ensure you’re ready to make a strong impression.
Questions Asked in Consul Interview
Q 1. Explain Consul’s architecture and its key components.
Consul is a distributed, highly available, and data center-aware service mesh solution. Its architecture is based on a cluster of Consul servers that maintain a consistent view of the system’s state. This state includes service registrations, health checks, and configuration data. Key components include:
- Consul Servers: These form the core of the Consul cluster. They are responsible for storing and replicating the consistent state of the system. They manage service discovery, health checks, and configuration data. A minimum of three servers is recommended for high availability.
- Consul Clients: These are agents that run on each service instance. They register the service with the Consul servers, report their health status, and retrieve information about other services. Clients communicate with servers to perform these actions, but do not participate in the internal consensus mechanisms of the server cluster.
- DNS and HTTP APIs: Consul provides both DNS and HTTP APIs for service discovery. This allows services to find each other using familiar tools and programming paradigms. Applications can use DNS to resolve service names to IP addresses, or they can use the HTTP API to programmatically query service information.
- Key/Value Store: Consul offers a distributed key/value store, providing a consistent, highly available place to store configuration data. This is useful for storing application settings or secrets that need to be accessible by all service instances.
Imagine a symphony orchestra. The Consul servers are like the conductor, keeping track of all the instruments (services) and ensuring they play in harmony. The Consul clients are the individual musicians, reporting their readiness and following the conductor’s instructions.
Q 2. Describe the different Consul modes (client, server).
Consul operates in two main modes: client and server.
- Server Mode: Consul servers form a Raft-based consensus cluster. They are responsible for maintaining the consistent state of the system, handling service registrations, health checks, and replicating data across the cluster. They need to be highly available and fault-tolerant. Think of them as the core brain of the Consul system.
- Client Mode: Consul clients register their services with the servers, perform health checks, and discover other services. They don’t directly communicate with each other; all communication happens via the servers. They are lighter weight and can be deployed more easily than servers. They are the ‘workers’ of the Consul system, executing tasks, reporting, and consuming information from the servers.
A common setup involves multiple client nodes and a cluster of at least three server nodes to ensure high availability and fault tolerance. If you only had client nodes, you wouldn’t have a persistent, shared view of your service catalogue and other critical data.
Q 3. How does Consul handle service discovery?
Consul handles service discovery by using a combination of service registration and DNS/HTTP APIs. When a service starts, its client registers itself with the Consul servers, providing information like its hostname, IP address, port, and any associated tags or metadata. The Consul servers maintain a catalog of all registered services.
To discover a service, other services can query the Consul servers using the DNS or HTTP API. For example, if a service is registered with the name api, another service can resolve api.service.consul (assuming a configured DNS domain) to obtain the IP addresses and ports of all currently running instances of the api service. The HTTP API allows for programmatic access to this information, useful for more complex orchestration needs.
This mechanism ensures services can locate and communicate with each other dynamically, even if the IP addresses or the number of instances change over time.
Q 4. Explain Consul’s health checking mechanisms.
Consul offers various health checking mechanisms to ensure only healthy services are discovered and used. These checks are defined during service registration and run periodically. There are several types of checks:
- Service Checks: These are custom checks that the service itself performs, reporting its health status to Consul. This could involve checking database connections, external API endpoints, or internal resource usage. This ensures the service itself is aware of its health.
- Agent Checks: These are checks performed by the Consul agent on the host machine. They can monitor things like CPU usage, disk space, or network connectivity. This provides an overall system health perspective.
The results of these checks are used to mark services as healthy or unhealthy in the Consul catalog. Only healthy services will be returned when querying the service discovery APIs. Think of it as a constant health check to identify any ‘sick’ services before they affect others.
Q 5. How does Consul achieve high availability?
Consul achieves high availability through its distributed architecture and the use of Raft consensus. The Consul servers form a Raft cluster, which ensures that a majority of servers must agree on the system’s state. This makes the system resilient to individual server failures. The data is replicated across all servers, ensuring consistency even if some servers go down.
To ensure even higher availability, it’s crucial to have at least three servers, as a majority (2 out of 3) is needed for the system to remain operational. Data center awareness is also crucial. Consul can be configured to work across multiple data centers, providing geographic redundancy. If one data center fails, services in other data centers can continue to operate.
This is like having multiple backups of your essential information. If one location fails, you still have access to what you need to keep your operations running smoothly.
Q 6. What are Consul’s key features for service mesh?
Consul plays a crucial role in service mesh architectures by providing service discovery, health checks, and configuration management. Its key features for service mesh include:
- Service Discovery: Consul’s service discovery mechanism allows services to automatically find and communicate with each other.
- Health Checking: The robust health checking capabilities ensure that only healthy services are used, preventing failures and improving reliability.
- Configuration Management: Consul’s key/value store can be used to store and distribute configuration data to services, simplifying configuration management and ensuring consistency.
- Connect (optional): Consul Connect provides a secure service-to-service communication layer. It manages identities and authorization policies to control inter-service communication, enabling mTLS (mutual TLS) by default, ensuring secure connections between microservices.
By providing these features, Consul simplifies the management and operation of complex microservice-based applications. It offers a centralized, consistent way to manage and monitor the services, helping reduce operational complexity and improve application resilience.
Q 7. How do you configure Consul for different environments (dev, staging, prod)?
Configuring Consul for different environments (development, staging, and production) usually involves managing separate Consul clusters for each environment. This isolates environments and helps prevent unintended changes from affecting production. Key aspects to consider:
- Separate Clusters: Deploy independent Consul clusters for each environment (dev, staging, prod). This is the most robust strategy for isolating environments and preventing misconfigurations in production.
- Configuration Management: Use a configuration management tool (like Ansible, Terraform, or Chef) to manage the configuration of Consul across different environments. This ensures consistency and simplifies deployment.
- Data Separation: Services registered in one environment should not be accessible from others. This prevents unintended cross-environment communication.
- Scaling: Scale the number of servers in each cluster based on the environment’s needs. Production clusters generally require more servers for higher availability and capacity.
- Security: Implement appropriate security measures, including access controls and encryption, for each environment. Production environments require more robust security controls. Consider using ACLs (Access Control Lists).
Using different clusters is analogous to having separate sets of tools for different tasks. You wouldn’t use your kitchen knives for car repairs; similarly, a separate Consul cluster ensures clear boundaries between your different environments.
Q 8. Describe Consul’s key-value store and its use cases.
Consul’s key-value store is a distributed, highly available data store that allows you to store and retrieve arbitrary data. Think of it like a giant, globally accessible dictionary. You can use it to store configuration settings, secrets, or any other data your application needs. It’s crucial for consistency and easy access across your distributed system.
Use Cases:
- Configuration Management: Instead of hardcoding settings in your applications, store them in Consul’s key-value store. This allows you to easily update settings without redeploying your applications. For example, you might store database connection strings or API keys.
- Feature Flags: Control the rollout of new features by storing boolean flags in the key-value store. Your application checks the flag before enabling the feature, allowing for easy toggling and A/B testing.
- Secrets Management: While not ideal for long-term storage of highly sensitive data, Consul can securely store less sensitive secrets like API keys for third-party services. Combine this with appropriate ACLs (explained later) for enhanced security.
- External Data Storage: Store any arbitrary data that your application needs to share efficiently across multiple instances. This can be anything from application-specific data to cache information.
Example: You could store a database connection string under the key /database/connection with the value "postgresql://user:password@host:port/database". Your application would then retrieve this value from Consul at runtime.
Q 9. Explain Consul’s ACL (Access Control Lists) and how to implement them.
Consul’s Access Control Lists (ACLs) are a crucial security feature that allows you to control access to different parts of your Consul cluster. This is essential for preventing unauthorized access to sensitive data and maintaining the security posture of your system. Think of ACLs like access rights for a file system, but applied to your Consul data.
Implementing ACLs:
- Create ACL Tokens: You start by creating ACL tokens with specific policies defining what actions (read, write, deny) they are allowed to perform on which parts of the key-value store or service catalog. These tokens should be treated like passwords.
- Define Policies: Policies specify which resources the token can access. They use a structured syntax, defining the resource type (e.g., key, service), the key prefix (e.g.,
/config/), and the allowed actions. - Assign Tokens to Users or Systems: Each service, application or person needing access to Consul gets assigned a token with an appropriate policy.
- Configure Clients: Your applications and tools that interact with Consul must be configured to use these tokens for authentication. This typically involves setting an environment variable or command-line argument.
Example Policy (Consul CLI):
policy create -name read_only_config -rule "key " + "prefix /config/*"This creates a policy called read_only_config that allows read-only access to keys with the prefix /config/.
Best Practices: Use the principle of least privilege, granting only the necessary access to each token. Regularly review and update ACL policies as your needs evolve. Consider using short-lived tokens to enhance security.
Q 10. How does Consul integrate with other tools in your DevOps ecosystem?
Consul seamlessly integrates with a wide range of tools in a DevOps ecosystem. Its capabilities extend beyond service discovery, enabling orchestration and configuration management within your infrastructure.
- Kubernetes: Consul can integrate with Kubernetes as a service mesh, providing service discovery and traffic management. The Consul operator automates the deployment and management of Consul within a Kubernetes cluster.
- Terraform: Terraform allows you to provision and manage Consul infrastructure as code, enabling automation and consistency across different environments.
- Docker: Consul agents can run inside Docker containers, allowing for easy deployment and integration with containerized applications. Consul’s service registration and health checks work seamlessly with Docker’s lifecycle.
- CI/CD pipelines: Consul can be incorporated into CI/CD pipelines to automate the deployment and configuration of applications, ensuring consistency and repeatability.
- Monitoring tools (e.g., Prometheus, Grafana): Consul exposes metrics that can be scraped by monitoring tools, providing visibility into its health and performance.
Example: A common workflow involves using Terraform to provision a Consul cluster, then using Docker to deploy applications that register themselves with Consul, and finally using Kubernetes for orchestration, all monitored via Prometheus and visualized in Grafana.
Q 11. How would you troubleshoot a service registration failure in Consul?
Troubleshooting a service registration failure in Consul involves a systematic approach, starting with the basics and progressing to more advanced diagnostics.
- Check the Service’s Health: Verify that the service itself is running correctly and healthy. If the service is down, it won’t register with Consul.
- Examine Consul Agent Logs: Check the logs of the Consul agent on the machine where the service is running. Look for error messages related to registration failures. These logs often provide clues about the root cause.
- Verify Network Connectivity: Ensure the service can communicate with the Consul agents. Check for firewall rules, network segmentation, or DNS resolution issues that might prevent registration.
- Inspect Consul UI: The Consul UI provides a comprehensive overview of registered services and their health. Check if the service appears in the list and verify its health status.
- Review the Service Definition: Ensure that the service’s registration configuration (e.g., service name, address, port) is correct and matches what Consul expects.
- Check Agent Configuration: Ensure the Consul agent is configured correctly and running smoothly. Check the agent’s configuration file for any errors or misconfigurations.
- Examine Consul Server Health: If using a distributed Consul cluster, verify that all Consul servers are running and healthy. A server outage can prevent service registration.
Common Causes: Network issues, misconfiguration of the service registration, Consul agent issues, firewall rules are frequently observed causes.
Q 12. How would you monitor Consul’s performance and health?
Monitoring Consul’s performance and health is crucial for ensuring the reliability and availability of your system. There are several ways to approach this:
- Consul’s Built-in Monitoring: Consul itself provides metrics via its HTTP API. These metrics cover various aspects of its operation, including agent health, server load, and key-value store performance.
- External Monitoring Tools: Use monitoring systems such as Prometheus and Grafana to collect and visualize Consul’s metrics, providing dashboards for quick assessment of its health.
- Consul’s UI: The Consul UI provides a visual representation of the cluster’s health, showing the status of agents, servers, and services.
- Log Monitoring: Regularly review Consul’s logs for errors and warnings. These logs offer invaluable information about potential problems.
- Check Disk Space: Monitor disk space on the Consul servers to ensure there’s sufficient space for storing data.
Key Metrics to Monitor:
- Agent Health: Ensure all Consul agents are healthy and reporting correctly.
- Server Load: Monitor CPU, memory, and disk I/O usage of Consul servers.
- Key-Value Store Size and Performance: Track the size of the key-value store and its performance metrics (e.g., read and write latency).
- Service Registration Success Rate: Monitor the success rate of service registration, looking for failures or trends.
Alerting: Configure alerts based on key metrics to be notified of potential problems promptly. For instance, an alert can be triggered if a server’s CPU usage exceeds a certain threshold.
Q 13. Explain Consul’s role in microservices architecture.
In a microservices architecture, Consul plays a vital role as a central service discovery and configuration management system. Microservices, being independent units, need a way to find and interact with each other dynamically. Consul acts as this central nervous system.
- Service Discovery: Each microservice registers itself with Consul, providing information about its location (IP address and port), health status, and any other relevant metadata.
- Health Checking: Consul actively monitors the health of registered services using health checks. These checks ensure only healthy services are used by clients.
- Service Routing and Load Balancing: Consul can be used to route traffic to healthy instances of a service, automatically distributing load across available instances.
- Configuration Management: Consul’s key-value store enables centralized configuration management for microservices. Configuration settings can be easily updated and distributed without requiring restarts.
- Secure Communication: Consul integrates with tools for securing communication between services such as TLS, ensuring data security.
Example: An e-commerce application might have separate microservices for product catalog, order processing, and payment gateway. Consul would allow these services to discover each other and communicate seamlessly. If one instance of the product catalog service fails, Consul would direct traffic to healthy instances, ensuring high availability.
Q 14. Compare and contrast Consul with other service discovery tools (e.g., etcd, ZooKeeper).
Consul, etcd, and ZooKeeper are all popular distributed key-value stores often used for service discovery and configuration management. While they share similarities, key differences exist:
| Feature | Consul | etcd | ZooKeeper |
|---|---|---|---|
| Focus | Service discovery, key-value store, configuration management, secrets management, monitoring | Distributed key-value store, often used for service discovery and configuration | Distributed coordination service, suitable for building highly reliable distributed applications |
| Ease of Use | Generally considered easier to use, with a user-friendly UI and comprehensive documentation. | Simpler API than ZooKeeper, but less feature-rich than Consul. | Steeper learning curve, more complex API. |
| Features | Broad range of features beyond basic key-value storage, including health checks, service mesh capabilities, ACLs, and more. | Strong emphasis on consistency and reliability. | Provides features like leader election, distributed locking, and atomic broadcasts. |
| Scalability | Highly scalable, supports large clusters. | Highly scalable, widely used in production environments. | Scalable, but performance can degrade with very large clusters. |
| Maturity | Mature and widely adopted in production. | Mature and widely used. | Very mature, long-standing technology. |
In Summary:
- Consul offers a broader set of features, simpler management, and a user-friendly interface, making it a good all-around choice.
- etcd is a strong, reliable, and performant key-value store ideal when consistency is paramount.
- ZooKeeper is better suited for scenarios needing low-level primitives for distributed coordination, rather than direct service discovery.
The best choice depends on specific requirements and priorities. Consider factors such as scalability needs, operational complexity, features required, and existing infrastructure when making a decision.
Q 15. Describe your experience with Consul’s configuration language.
Consul primarily uses a declarative configuration language, most often expressed in JSON or HCL (HashiCorp Configuration Language). This means you describe the desired state of your system—the services, their health checks, and other settings—and Consul ensures that state is maintained. It’s similar to infrastructure-as-code tools like Terraform. Instead of writing imperative scripts, you define what you want, and Consul figures out how to achieve it. For example, you define a service with its address, port, and health check in a JSON file, and Consul registers and manages it accordingly. This approach is much more manageable and reproducible than manually configuring each component.
The choice between JSON and HCL depends on personal preference and project standards. HCL is often favored for its readability and structured syntax, particularly useful for complex configurations, while JSON offers wider familiarity and simpler parsing for those coming from other contexts. Both offer the ability to specify key-value pairs, allowing granular control over Consul’s behavior. Understanding this declarative nature is critical to effectively managing Consul across various environments.
Example (JSON):
{
"service": {
"name": "my-service",
"address": "192.168.1.100",
"port": 8080,
"check": {
"http": "http://192.168.1.100:8080/health",
"interval": "10s"
}
}
}Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. How do you manage Consul’s configuration across multiple environments?
Managing Consul’s configuration across multiple environments (development, staging, production) requires a robust approach that leverages configuration management tools and practices. Simply copying configuration files between environments is risky and error-prone. Instead, I employ a combination of techniques. First, I use a version control system (like Git) to track all configuration files, ensuring easy auditing and rollback capabilities. Second, I employ a configuration management tool, such as Terraform or Ansible, to manage Consul’s deployment and configuration across different environments. This enables me to define the configuration for each environment in a separate, version-controlled file or module. This approach ensures consistency and reduces the risk of human error.
Another important aspect is parameterization. Instead of hardcoding values like IP addresses or ports in configuration files, I use environment variables or configuration management variables. This allows the same configuration file to be used across multiple environments with different values applied based on the environment. For example, the database connection string would be different in development, staging, and production.
Finally, I use a structured approach to organize configurations, using folders to represent different environments. This makes it easier to understand, manage, and deploy configurations across different stages of the application lifecycle. By combining these approaches, configuration management across different environments becomes systematic, controlled, and auditable.
Q 17. Explain how Consul handles service updates and rolling deployments.
Consul handles service updates and rolling deployments gracefully through its service health checks and its ability to dynamically register and deregister services. When a service is updated, the new version is registered with Consul, typically along with a new service ID or a tagged version. While the old version is still functioning, Consul’s health checks continue to monitor both. The load balancer, which could be integrated with Consul or a separate service mesh, gradually shifts traffic from the old version to the new version based on the health status reported by the checks. This approach ensures minimal disruption during the update.
This process is often automated through tools like Kubernetes or custom scripts. The automation ensures that the transition is controlled and can be rolled back easily if necessary. If the new version reports unhealthy status, the load balancer will continue directing traffic to the old and proven version. This ensures high availability and minimizes service downtime during deployments. Consul’s service discovery mechanism seamlessly integrates with this process, making it transparent to the clients consuming those services. They just always connect to a healthy instance, regardless of versions.
Q 18. Describe Consul’s capabilities for service segmentation and isolation.
Consul provides service segmentation and isolation primarily through its ACL (Access Control Lists) and intent-based policies. ACLs allow you to define granular permissions, controlling which users or services can access particular parts of the Consul cluster and which services they can discover. You can create different policies for different teams or applications. For example, you might have one set of ACLs for the development team and another for the production team. This ensures that they cannot accidentally interfere with each other’s deployments or access sensitive data.
Furthermore, Consul’s intent-based policies enable more sophisticated control over network segmentation. You can define policies that specify which services can communicate with which other services, regardless of their location or physical network structure. This helps to isolate services and prevent unauthorized access or communication between different parts of your application. This level of fine-grained control is crucial for security and helps to contain the impact of potential vulnerabilities.
Q 19. How do you secure Consul against unauthorized access?
Securing Consul involves a multi-layered approach, starting with network-level security. This includes using firewalls to restrict access to the Consul servers and only allowing authorized IPs or subnets to interact with the cluster. Next, Consul’s built-in Access Control Lists (ACLs) are critical. ACLs enable fine-grained control over who can perform operations, like registering services, querying the catalog, or modifying configuration. You create and manage ACL tokens, assigning permissions to specific users or services. This prevents unauthorized modification and access to the Consul cluster and its managed services.
Mutual Transport Layer Security (mTLS) enhances communication security within the Consul cluster itself. This ensures that only authorized Consul agents and servers communicate with each other, encrypting traffic and authenticating each peer. Regular security audits and vulnerability scanning are crucial to maintain a robust security posture. Finally, monitoring and logging are essential. By monitoring access attempts and evaluating logs, you can identify and address potential security threats promptly. Properly configuring and managing these security features is crucial for maintaining a secure and reliable Consul cluster. The principle of least privilege should always be adopted when granting ACL permissions.
Q 20. How does Consul handle failures and ensure resilience?
Consul is designed for high availability and resilience. Its architecture relies on a distributed consensus protocol (typically Raft) to ensure data consistency across multiple Consul servers. If one server fails, the others continue to operate seamlessly. This fault tolerance is built into the core of Consul. The health checks that are defined for each service are essential for resilience. They allow Consul to detect failing services and automatically remove them from the service catalog. Clients then automatically connect to healthy instances.
Furthermore, Consul’s configuration replication ensures that even if a server is unavailable, other servers have a copy of the configuration. Replication techniques prevent data loss or service disruptions. Regular backups are important as a secondary safeguard against data loss. You can also configure Consul to automatically detect and handle network partitions. This prevents split-brain scenarios, which can lead to inconsistencies in the service catalog. Combining these features guarantees high availability and resilience even in challenging network conditions.
Q 21. Describe your experience using the Consul API.
I have extensive experience using the Consul API, primarily the HTTP API. I’ve utilized it for various tasks, including programmatically registering and deregistering services, querying the health status of services, configuring ACLs, and managing key-value pairs in Consul’s storage. The API allows for automation of many Consul tasks, integrating it seamlessly into CI/CD pipelines and other automation processes. It’s important to be familiar with the various endpoints and how to construct appropriate HTTP requests and handle the responses. For example, I frequently use the API to dynamically manage service registrations during deployments and for automating health checks.
Example (using curl to register a service):
curl -X PUT -d '{"name":"myservice","address":"192.168.1.100","port":8080}' http://consul-server:8500/v1/agent/service/registerThis command registers a service with Consul using the HTTP API. Using the API allows for scripting, automating and extending Consul’s capabilities beyond its web UI. It’s essential for any advanced management and integration with other systems.
Q 22. Explain the concept of Consul Connect and its benefits.
Consul Connect is a service mesh built into Consul that simplifies service-to-service communication. Instead of relying on complex configurations and potentially insecure network setups, Connect provides a secure, encrypted, and automatically managed connection between services. Think of it as a secure tunnel for inter-service communication within your application.
- Simplified Configuration: No more wrestling with IP addresses, port numbers, or complex firewall rules. Connect automatically handles service discovery and routing.
- Enhanced Security: All communication is encrypted using mTLS (mutual Transport Layer Security), ensuring data confidentiality and integrity. No more exposing services directly to the network.
- Improved Observability: Connect integrates with Consul’s monitoring and logging capabilities, giving you better insights into service communication patterns and potential problems.
- Automatic Service Discovery: Services automatically find and connect to each other without requiring manual configuration. This is especially beneficial in microservices architectures where services are frequently deployed and updated.
Example: Imagine you have a microservice architecture with a user authentication service and an order processing service. With Connect, you simply register these services with Consul, and Connect automatically establishes a secure connection between them. No manual configuration of IP addresses, ports, or firewalls is required. If the order processing service needs to authenticate a user, it simply calls the authentication service using its service name – Connect handles the underlying network details.
Q 23. How would you use Consul’s intention-based networking?
Consul’s intention-based networking allows you to define the desired connectivity between services using declarative policies, rather than managing complex network configurations. This is achieved using Connect’s intention and proxy features.
How to Use it: You define policies that specify which services can communicate with each other, effectively establishing a virtual network. For example, you might define a policy stating that the ‘database’ service can only be accessed by the ‘api’ service. Consul then uses its service mesh to enforce this policy, automatically routing traffic and blocking unauthorized access. This greatly simplifies the management of network access control and improves security.
Example: Let’s say you have three services: ‘web’, ‘api’, and ‘database’. To enforce the rule that only the ‘api’ service can talk to the ‘database’ service, you would use a Consul Connect intention policy to define this explicit relationship. Then, if the ‘web’ service attempts to directly access the database, the connection will be blocked.
consul connect intention
--name=database-access
--service=api
--target-service=databaseThis ensures the ‘database’ only accepts traffic from the ‘api’ service, preventing direct access from the ‘web’ service and other unauthorized services. This is far easier to manage than configuring firewalls or IP tables.
Q 24. Describe a scenario where Consul’s service mesh capabilities were crucial.
In a recent project involving a large e-commerce platform, Consul’s service mesh capabilities were essential for handling high traffic volumes and ensuring seamless operation during peak shopping seasons. We had a multitude of microservices, each responsible for specific functionalities like product catalog, shopping cart, payment processing, etc.
The Challenge: Maintaining secure and reliable communication between these services with a traditional approach (using IP addresses and firewalls) would have been complex, error-prone, and difficult to scale. Dynamic scaling of services during peak load further complicated the task.
The Solution: We leveraged Consul Connect to create a secure and resilient service mesh. Each microservice was registered with Consul, and Connect automatically managed the service discovery and secure communication between them. This approach offered several crucial advantages:
- Improved Scalability: As traffic increased, Consul Connect automatically managed the routing and scaling of services without requiring manual intervention.
- Enhanced Security: mTLS ensured that only authorized services could communicate with each other, greatly reducing the risk of security breaches.
- Simplified Management: Managing the inter-service communication became significantly easier; we didn’t need to manually configure IP addresses, firewall rules, or worry about network configurations.
Without Consul Connect, managing the communication between the numerous services, securing them, and ensuring reliable operation during peak loads would have been an extremely challenging and time-consuming endeavor.
Q 25. How would you implement multi-datacenter federation with Consul?
Consul’s multi-datacenter federation allows you to seamlessly manage and connect services across geographically distributed datacenters. This provides high availability and fault tolerance.
Implementation: You create a federation between your Consul datacenters by designating one datacenter as the primary and configuring the others as federated members. The primary datacenter acts as the central point of coordination for service discovery across all datacenters.
Steps:
- Configure Consul Servers: Install and configure Consul servers in each datacenter.
- Establish Federation: In the primary datacenter, configure the Consul servers to accept federation from other datacenters. The other datacenters will then join the federation by specifying the primary datacenter’s address.
- Define Service Policies: Define how services across datacenters interact and replicate configurations. You’ll define what services should be accessible and from which locations.
- Monitor and Manage: Monitor the health of the federation and manage service deployments and configurations across all datacenters. Use Consul’s UI or CLI tools to monitor cluster health, replication status, and service availability.
Example: You might have one Consul datacenter in the US East coast and another in the US West coast. By federating these datacenters, services deployed in either region will be discoverable and accessible by services in the other region, providing geographic redundancy and reduced latency for users in different regions. If one datacenter fails, services in the other datacenter will continue to operate without interruption.
Q 26. How would you migrate an existing service discovery system to Consul?
Migrating from an existing service discovery system to Consul involves a phased approach to minimize disruption and ensure a smooth transition.
Steps:
- Assessment and Planning: Analyze the existing system, identify all services, their dependencies, and how they use the current service discovery. Plan a migration strategy, considering the complexity of your services and the downtime tolerance.
- Parallel Run: Deploy Consul alongside your existing system. Gradually register a subset of your services with Consul. This allows you to test Consul in a production environment and address any integration issues before a full cutover.
- Service Registration: Develop scripts or automate the process of registering your services with Consul, using service names and tags appropriately. This may require modifications to your application code to use the Consul client libraries.
- Testing and Validation: Thoroughly test the integration of your applications with Consul. Pay close attention to service discovery, health checks, and overall functionality.
- Cutover: Once testing is complete, switch over to Consul. This may be done gradually, moving services one at a time or in groups, or with a ‘big bang’ approach, depending on your risk tolerance and assessment.
- Monitoring and Optimization: Monitor the performance and stability of Consul after the migration. Make adjustments as needed to optimize the configuration and ensure optimal performance.
Important Considerations: The migration complexity depends heavily on the existing system’s architecture, scale, and the features used. Carefully plan the migration timeline, considering potential downtime and resource requirements. Proper testing and monitoring are crucial for a successful migration.
Q 27. Explain your experience with Consul’s monitoring and alerting capabilities.
Consul offers robust monitoring and alerting capabilities, providing critical insights into the health and performance of your services and infrastructure.
Monitoring: Consul’s health checks allow you to monitor the health status of individual services. It provides real-time visibility of service availability and performance metrics such as CPU usage, memory consumption, and network latency. This information is accessible through the Consul UI or via its API.
Alerting: Consul integrates with various alerting systems, allowing you to configure alerts based on service health, metrics thresholds, or other events. You can define custom rules and notifications to receive alerts via email, PagerDuty, or other tools. For example, you can configure an alert that triggers when a service becomes unhealthy or if a critical metric exceeds a predefined threshold.
Experience: I’ve extensively used Consul’s monitoring and alerting capabilities in several projects. In one case, we integrated Consul with Prometheus and Grafana to create a comprehensive monitoring dashboard that provided real-time insights into the health and performance of our microservices. The alerting features proved invaluable for rapid identification and resolution of service outages and performance bottlenecks, allowing us to proactively address potential issues before they affected our users.
Example: We defined alerts for critical services to notify our team immediately upon failure. This included email notifications and PagerDuty alerts for critical services. We were able to quickly diagnose and resolve issues, significantly reducing downtime and improving the overall resilience of our application.
Key Topics to Learn for Consul Interview
- Service Discovery: Understand Consul’s core function as a service discovery and configuration management tool. Explore its architecture and how it registers, discovers, and manages services within a distributed system.
- Key-Value Store: Learn how Consul’s distributed key-value store works, its use cases for configuration management and storing application data, and best practices for its utilization.
- Health Checks: Grasp the importance of health checks in maintaining service availability. Understand how to configure and interpret health check results to ensure application resilience.
- Consul’s API: Familiarize yourself with Consul’s API, allowing for programmatic interaction with its features. Explore its capabilities for automation and integration with other tools.
- Security: Understand Consul’s security features, including ACLs (Access Control Lists), encryption, and authentication mechanisms. Know how to configure secure Consul deployments.
- High Availability and Clustering: Learn how Consul achieves high availability and fault tolerance through clustering. Understand the implications of different deployment topologies.
- Practical Applications: Explore real-world scenarios where Consul is used, such as microservices orchestration, configuration management for cloud-native applications, and service mesh integration.
- Troubleshooting and Problem Solving: Develop your ability to diagnose and resolve common Consul-related issues. This includes understanding log analysis and debugging techniques.
- Comparison with other tools: While not a direct interview question, comparing and contrasting Consul with similar tools (e.g., etcd, ZooKeeper) demonstrates a broader understanding of the landscape.
Next Steps
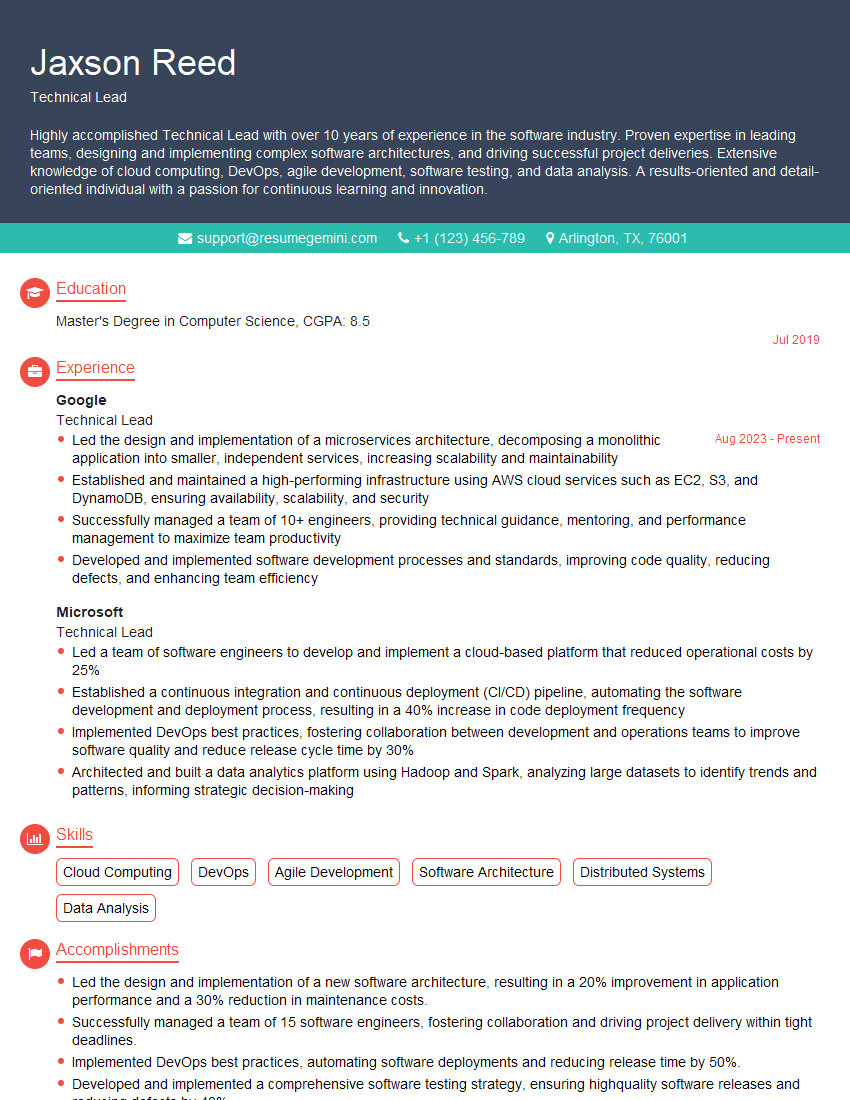
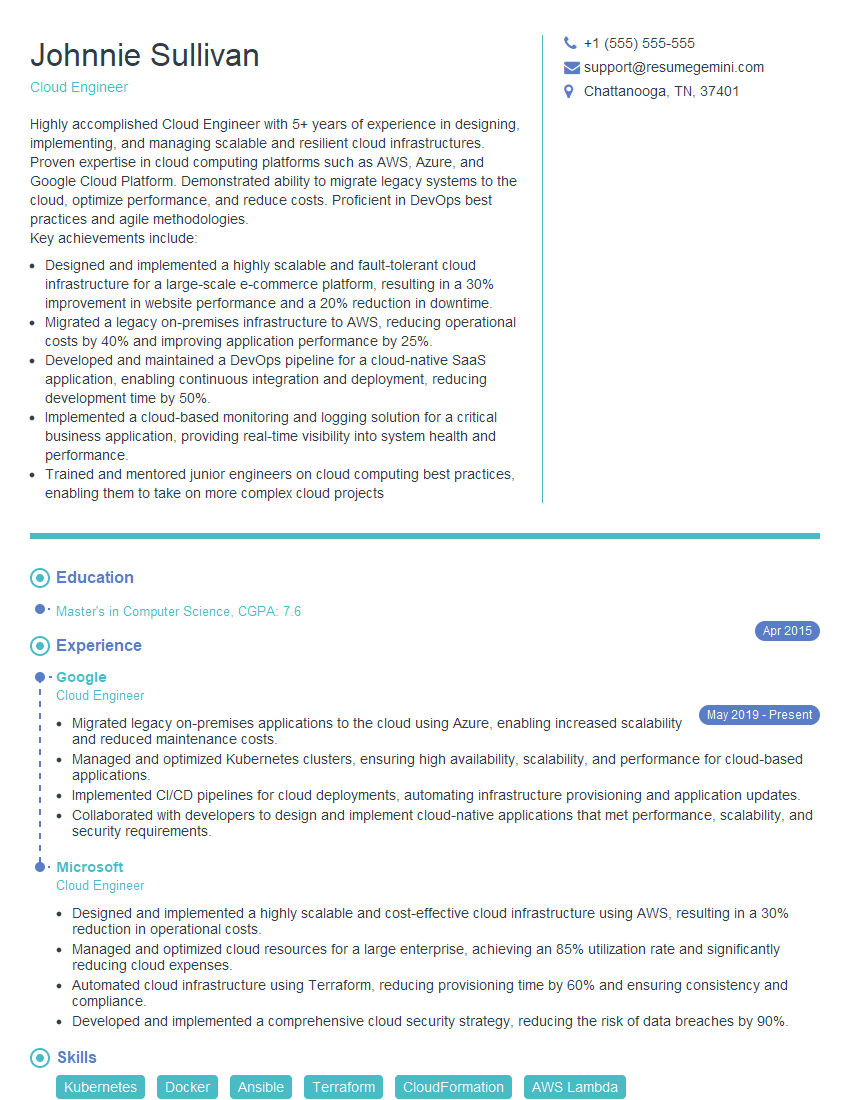
Mastering Consul significantly enhances your prospects in the rapidly growing field of cloud-native computing and microservices architecture. Demonstrating proficiency in Consul showcases valuable skills highly sought after by employers. To maximize your chances of landing your dream role, invest time in crafting an ATS-friendly resume that effectively highlights your skills and experience. ResumeGemini is a trusted resource to help you build a professional and impactful resume. Examples of resumes tailored specifically for Consul roles are available for your review, helping you showcase your skills in the best possible light.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Attention music lovers!
Wow, All the best Sax Summer music !!!
Spotify: https://open.spotify.com/artist/6ShcdIT7rPVVaFEpgZQbUk
Apple Music: https://music.apple.com/fr/artist/jimmy-sax-black/1530501936
YouTube: https://music.youtube.com/browse/VLOLAK5uy_noClmC7abM6YpZsnySxRqt3LoalPf88No
Other Platforms and Free Downloads : https://fanlink.tv/jimmysaxblack
on google : https://www.google.com/search?q=22+AND+22+AND+22
on ChatGPT : https://chat.openai.com?q=who20jlJimmy20Black20Sax20Producer
Get back into the groove with Jimmy sax Black
Best regards,
Jimmy sax Black
www.jimmysaxblack.com
Hi I am a troller at The aquatic interview center and I suddenly went so fast in Roblox and it was gone when I reset.
Hi,
Business owners spend hours every week worrying about their website—or avoiding it because it feels overwhelming.
We’d like to take that off your plate:
$69/month. Everything handled.
Our team will:
Design a custom website—or completely overhaul your current one
Take care of hosting as an option
Handle edits and improvements—up to 60 minutes of work included every month
No setup fees, no annual commitments. Just a site that makes a strong first impression.
Find out if it’s right for you:
https://websolutionsgenius.com/awardwinningwebsites
Hello,
we currently offer a complimentary backlink and URL indexing test for search engine optimization professionals.
You can get complimentary indexing credits to test how link discovery works in practice.
No credit card is required and there is no recurring fee.
You can find details here:
https://wikipedia-backlinks.com/indexing/
Regards
NICE RESPONSE TO Q & A
hi
The aim of this message is regarding an unclaimed deposit of a deceased nationale that bears the same name as you. You are not relate to him as there are millions of people answering the names across around the world. But i will use my position to influence the release of the deposit to you for our mutual benefit.
Respond for full details and how to claim the deposit. This is 100% risk free. Send hello to my email id: lukachachibaialuka@gmail.com
Luka Chachibaialuka
Hey interviewgemini.com, just wanted to follow up on my last email.
We just launched Call the Monster, an parenting app that lets you summon friendly ‘monsters’ kids actually listen to.
We’re also running a giveaway for everyone who downloads the app. Since it’s brand new, there aren’t many users yet, which means you’ve got a much better chance of winning some great prizes.
You can check it out here: https://bit.ly/callamonsterapp
Or follow us on Instagram: https://www.instagram.com/callamonsterapp
Thanks,
Ryan
CEO – Call the Monster App
Hey interviewgemini.com, I saw your website and love your approach.
I just want this to look like spam email, but want to share something important to you. We just launched Call the Monster, a parenting app that lets you summon friendly ‘monsters’ kids actually listen to.
Parents are loving it for calming chaos before bedtime. Thought you might want to try it: https://bit.ly/callamonsterapp or just follow our fun monster lore on Instagram: https://www.instagram.com/callamonsterapp
Thanks,
Ryan
CEO – Call A Monster APP
To the interviewgemini.com Owner.
Dear interviewgemini.com Webmaster!
Hi interviewgemini.com Webmaster!
Dear interviewgemini.com Webmaster!
excellent
Hello,
We found issues with your domain’s email setup that may be sending your messages to spam or blocking them completely. InboxShield Mini shows you how to fix it in minutes — no tech skills required.
Scan your domain now for details: https://inboxshield-mini.com/
— Adam @ InboxShield Mini
support@inboxshield-mini.com
Reply STOP to unsubscribe
Hi, are you owner of interviewgemini.com? What if I told you I could help you find extra time in your schedule, reconnect with leads you didn’t even realize you missed, and bring in more “I want to work with you” conversations, without increasing your ad spend or hiring a full-time employee?
All with a flexible, budget-friendly service that could easily pay for itself. Sounds good?
Would it be nice to jump on a quick 10-minute call so I can show you exactly how we make this work?
Best,
Hapei
Marketing Director
Hey, I know you’re the owner of interviewgemini.com. I’ll be quick.
Fundraising for your business is tough and time-consuming. We make it easier by guaranteeing two private investor meetings each month, for six months. No demos, no pitch events – just direct introductions to active investors matched to your startup.
If youR17;re raising, this could help you build real momentum. Want me to send more info?
Hi, I represent an SEO company that specialises in getting you AI citations and higher rankings on Google. I’d like to offer you a 100% free SEO audit for your website. Would you be interested?
Hi, I represent an SEO company that specialises in getting you AI citations and higher rankings on Google. I’d like to offer you a 100% free SEO audit for your website. Would you be interested?