The thought of an interview can be nerve-wracking, but the right preparation can make all the difference. Explore this comprehensive guide to Digital Forensics and Incident Response interview questions and gain the confidence you need to showcase your abilities and secure the role.
Questions Asked in Digital Forensics and Incident Response Interview
Q 1. Explain the process of acquiring digital evidence.
Acquiring digital evidence is the crucial first step in any digital forensic investigation. It involves creating a forensically sound copy of the original data, ensuring its integrity and admissibility in court. This process, often referred to as ‘imaging,’ requires specialized tools and techniques to avoid altering the original evidence.
The process typically involves:
- Preparation: This includes securing the scene, documenting everything, and identifying all potential sources of digital evidence (computers, phones, servers, cloud storage etc.).
- Imaging: Creating a bit-stream copy of the storage device. This is done using write-blocking devices to prevent accidental modification of the original data. Tools like EnCase, FTK Imager, and dd are commonly used. A hash value (like SHA-256) is generated for both the original and the copy to verify their identicality later.
- Verification: Comparing the hash values of the original and the copy to ensure a perfect match. Any discrepancy indicates a problem with the imaging process.
- Authentication: This involves documenting the entire process, including who handled the evidence, when, and where, establishing the chain of custody.
Example: Imagine investigating a suspected data breach. Before touching any computer, you would photograph the scene, note the computer’s power state, and document its location. Then, using a write-blocking device, you would create a bit-stream image of the hard drive, generating and recording its SHA-256 hash. This ensures that the evidence remains unaltered and can be presented in court.
Q 2. Describe the different types of digital forensics examinations.
Digital forensic examinations cover a wide range of specialties. They can be broadly categorized as follows:
- Network Forensics: Investigating network intrusions, data breaches, and malware propagation by analyzing network traffic, logs, and other network-related data.
- Computer Forensics: Examining computers and other digital devices to recover deleted files, reconstruct events, and identify malicious activities.
- Mobile Device Forensics: Analyzing smartphones and tablets to extract data like call logs, messages, location data, and application data. This often involves specialized tools and techniques to bypass security features.
- Database Forensics: Investigating databases to identify data breaches, unauthorized access, or data manipulation. This involves analyzing database logs, schema, and data itself.
- Cloud Forensics: Examining data stored in cloud environments like AWS, Azure, or Google Cloud. This requires understanding the specific cloud provider’s infrastructure and logging mechanisms.
- Memory Forensics: Analyzing the contents of computer memory to capture live data, like running processes, network connections, and malware behavior, often crucial for investigating active attacks.
Many investigations will involve multiple types of examinations. For example, an investigation into a ransomware attack might involve network forensics to trace the attack vector, computer forensics to analyze the infected machine, and memory forensics to understand the malware’s actions in real-time.
Q 3. What are the common challenges in digital forensics investigations?
Digital forensics investigations present several challenges:
- Data Volatility: Data stored in RAM is volatile and easily lost when a system is powered off, making memory forensics crucial but time-sensitive.
- Data Volume: The sheer volume of data generated and stored today makes analysis time-consuming and resource-intensive. Analyzing terabytes or even petabytes of data can require specialized tools and significant expertise.
- Data Encryption: Encrypted files pose a significant hurdle, requiring specialized tools or techniques to potentially decrypt them, often relying on passwords or keys.
- Data Hiding Techniques: Attackers employ sophisticated methods to hide data, making its discovery challenging. This includes steganography, data carving, and other obfuscation techniques.
- Legal and Ethical Considerations: Investigators must always adhere to strict legal and ethical guidelines regarding data privacy and access, requiring meticulous documentation and warrants when necessary.
- Anti-forensics Techniques: Attackers actively try to prevent forensic analysis, using techniques to wipe drives, destroy evidence, or obfuscate their actions.
Example: Identifying a specific piece of malware within a massive dataset extracted from a compromised server requires efficient searching, filtering, and malware signature analysis, demanding significant skill and technological resources.
Q 4. Explain the chain of custody and its importance in digital forensics.
The chain of custody is a meticulous record documenting the handling of evidence from the moment it is collected to its presentation in court. It’s a critical aspect of digital forensics, ensuring the evidence’s integrity and admissibility. Any break in the chain can compromise the case.
The chain of custody documentation typically includes:
- Date and time of seizure: When the evidence was acquired.
- Location of seizure: Where the evidence was found.
- Person(s) seizing the evidence: Who collected the evidence.
- Description of the evidence: Detailed description of the device or data.
- Hash value(s): Cryptographic hash values to verify data integrity.
- Storage location: Where the evidence is stored.
- Access log: A record of who accessed the evidence and when.
- Transfer of custody: Documentation of each time the evidence was transferred to another individual.
Importance: A complete and unbroken chain of custody assures the court that the evidence presented is genuine and hasn’t been tampered with. Without it, the evidence may be deemed inadmissible, jeopardizing the entire investigation.
Example: If a hard drive is seized, every person who handles it, along with the date and time, must be recorded. Any changes, analysis, or transport must be documented, creating an unbroken trail. If a step is missed, doubts about the evidence’s authenticity will arise.
Q 5. What are some common malware analysis techniques?
Malware analysis techniques aim to understand a malware sample’s behavior, functionality, and origins. These techniques can be broadly categorized into static and dynamic analysis.
- Static Analysis: Examining the malware without executing it. This involves inspecting the code, identifying strings, looking for suspicious functions, and analyzing the malware’s structure. Tools like disassemblers (e.g., IDA Pro) and debuggers are commonly used.
- Dynamic Analysis: Observing the malware’s behavior while it’s running in a controlled environment (e.g., a sandbox). This involves monitoring system calls, network activity, registry changes, and file system operations. Tools like sandboxes (e.g., Cuckoo Sandbox) and debuggers are employed.
- Behavioral Analysis: Observing the malware’s actions and effects on the system. This involves monitoring its interactions with the operating system, other applications, and network resources.
- Reverse Engineering: Deconstructing the malware to understand its inner workings. This often involves disassembling the code and tracing its execution flow.
Example: A static analysis of a malware file might reveal strings indicating its target or functionality. A dynamic analysis, performed in a sandbox, could reveal network connections to a command-and-control server or files being encrypted. Combining both allows for a more complete understanding of the malware’s capabilities and malicious intentions.
Q 6. How do you handle encrypted files during a forensic investigation?
Encrypted files present a major challenge in forensic investigations. The approach depends on the type of encryption and available information.
- Password cracking: If the encryption uses a password, various techniques can be used to crack it, from simple dictionary attacks to more sophisticated brute-force methods. However, this can be time-consuming and may not be successful.
- Key recovery: If the encryption key is known or can be recovered, decryption is straightforward. This might involve examining system memory, registry keys, or other data sources for the key.
- Known plaintext attack: If a portion of the encrypted data and its corresponding plaintext are known, it might be possible to deduce the encryption key and decrypt the rest of the data.
- Cryptanalysis: This involves employing advanced mathematical techniques to analyze and potentially break the encryption algorithm, though this is usually complex and time-consuming.
- Third-party decryption tools: Specialized tools can assist in decrypting certain types of encryption. It is critical to validate any third-party tools used.
Important Note: While attempting to decrypt files, maintaining the integrity of the original encrypted files is crucial. A copy should always be worked on to preserve the original evidentiary value.
Example: Encountering a BitLocker-encrypted drive, the investigator might try to obtain the recovery key from the user or the system’s recovery partition, failing which advanced cracking tools may be applied (with caution and legal consideration).
Q 7. What are the key steps in incident response?
Incident response follows a structured methodology to handle security incidents. While variations exist, a common framework includes:
- Preparation: Proactive measures taken before an incident occurs. This includes establishing incident response plans, defining roles and responsibilities, and creating a communication strategy.
- Identification: Detecting the incident, often triggered by alerts from security systems or user reports. This involves understanding the nature and scope of the incident.
- Containment: Isolating the affected systems or networks to prevent further damage or spreading of the attack. This could involve disconnecting affected devices from the network, disabling user accounts, or shutting down servers.
- Eradication: Removing the cause of the incident. This could involve uninstalling malware, patching vulnerabilities, or restoring data from backups.
- Recovery: Restoring systems and data to a functional state. This might involve reinstalling software, restoring data from backups, and reconfiguring systems.
- Lessons Learned: Analyzing the incident to identify vulnerabilities, improve security practices, and prevent similar incidents in the future. This involves documenting findings, creating recommendations, and implementing changes.
Example: If a ransomware attack is detected, the incident response team might first contain the attack by disconnecting infected systems from the network, then eradicate the ransomware by removing infected files, and finally recover data from backups. A post-incident review would analyze how the attack occurred and implement preventive measures to avoid future incidents.
Q 8. Describe your experience with incident response methodologies (e.g., NIST, SANS).
My incident response experience is deeply rooted in established methodologies like NIST Cybersecurity Framework and SANS Institute’s incident handling guide. I’ve consistently applied the core principles of these frameworks throughout my career, adapting them to diverse situations. NIST’s framework, with its focus on Identify, Protect, Detect, Respond, and Recover, provides a robust structure for proactive and reactive measures. I’ve leveraged the ‘Identify’ phase to establish baselines and vulnerability assessments, crucial for preventing future incidents. In the ‘Detect’ phase, my experience includes implementing and monitoring Security Information and Event Management (SIEM) systems to proactively identify threats. The ‘Respond’ phase is where my expertise lies; I’ve led numerous incident response efforts, utilizing containment, eradication, recovery, and post-incident activity procedures as defined by NIST. SANS’s methodology emphasizes a more hands-on approach, focusing on detailed investigation and root cause analysis. I’ve particularly found their techniques for evidence collection and chain of custody maintenance invaluable. I’ve successfully utilized both frameworks in numerous cases, often blending their strengths to achieve optimal outcomes. For instance, during a recent ransomware attack, I used NIST’s framework to coordinate the recovery process and SANS’s methodology for deep dive analysis, determining the attacker’s tactics and creating preventative measures.
Q 9. How do you prioritize incidents during a response?
Prioritizing incidents requires a systematic approach. I typically use a combination of factors, including the impact on the organization, the potential for escalation, and the urgency of the situation. This often involves a risk assessment matrix. For example, a critical system outage impacting revenue generation would be prioritized higher than a minor security vulnerability with limited impact. I use a scoring system considering factors like: Impact (data loss, financial implications, reputational damage); Urgency (speed of escalation, potential for further damage); and Probability (likelihood of successful exploitation). Higher scores naturally receive top priority. A simple example might involve assigning weights: Impact (5), Urgency (3), Probability (2). An incident scoring 20 would require immediate attention over one scoring 5. Tools like SIEM systems can automate much of this, generating alerts based on pre-defined thresholds, enabling quick identification of high-priority incidents. Communication is key, I always keep stakeholders informed of the prioritization process and the reasoning behind it.
Q 10. What tools and technologies are you familiar with for digital forensics and incident response?
My toolkit includes a broad range of digital forensics and incident response tools and technologies. For example, I’m proficient in using EnCase and FTK Imager for disk imaging and analysis, Autopsy for open-source forensic analysis, and Wireshark for network traffic analysis. For malware analysis, I’m comfortable with tools like Cuckoo Sandbox and Process Monitor. I use SIEM platforms such as Splunk and QRadar for log analysis and threat detection. I also have experience with various scripting languages such as Python and PowerShell for automating tasks and developing custom tools. Finally, I’m well-versed in cloud forensics, utilizing tools and techniques for investigating incidents within cloud environments like AWS and Azure.
Q 11. Explain the concept of volatile and non-volatile memory.
Volatile memory, like RAM, loses its contents when power is removed. Think of it like a whiteboard; the information is there as long as you keep writing and erasing, but once you wipe the board clean, it’s gone. Non-volatile memory, such as hard drives or SSDs, retains data even when power is lost. It’s like a permanent notebook; whatever you write remains there until you actively erase it. In a digital forensics investigation, capturing data from volatile memory is crucial because it provides real-time snapshots of system processes, running applications, and network connections. This data is often ephemeral, revealing current activity and potentially malicious processes. Non-volatile memory provides a historical record of activities, helping reconstruct past events. Therefore, capturing and analyzing both volatile and non-volatile memory is vital for a comprehensive forensic investigation.
Q 12. How do you handle data breaches and data leaks?
Handling data breaches and data leaks involves a multi-stage process. The first step is to contain the breach, limiting further damage. This involves isolating affected systems, blocking malicious actors, and preventing further data exfiltration. Next is eradication; removing the threat from the environment – this might include malware removal, patching vulnerabilities, or resetting compromised accounts. The third phase is recovery, restoring data from backups or implementing alternative solutions. Finally, post-incident activities are crucial. This includes conducting a thorough root cause analysis to prevent future incidents, communicating with affected parties, and reporting to relevant authorities. A crucial step is identifying the scope of the breach – which data was compromised and who was affected. This informs the communication plan, legal considerations and remediation strategies. Documentation throughout this entire process is essential, maintaining a detailed record of every step taken. The entire procedure should follow incident response best practices, including regulatory compliance (e.g., GDPR, CCPA).
Q 13. Describe your experience with network forensics.
Network forensics is a crucial part of my expertise. It involves analyzing network traffic to identify security breaches, track malicious activity, and gather evidence for investigations. I’m proficient in using tools like Wireshark to capture and analyze network packets. I can identify malicious traffic patterns, reconstruct attack sequences, and pinpoint the source and destination of attacks. My experience includes analyzing network logs to identify suspicious login attempts, data exfiltration, and other malicious activity. I also use techniques such as NetFlow analysis to gain a broader overview of network traffic patterns and identify anomalies. A real-world example: I once investigated a suspected insider threat by analyzing network traffic logs to identify unauthorized access attempts to sensitive data. By analyzing the timestamps, source IPs, and the specific files accessed, I was able to pinpoint the responsible employee and the extent of the data breach. This required careful correlation of network data with other sources, like security logs and system event logs, to build a comprehensive timeline of the events.
Q 14. What are the legal and ethical considerations in digital forensics?
Legal and ethical considerations are paramount in digital forensics. Every action must adhere to the law and respect individual rights. Key aspects include obtaining proper authorization before conducting investigations, ensuring the chain of custody is maintained to ensure the integrity of evidence, and following all relevant legal procedures like obtaining warrants when necessary. Ethical considerations include respecting privacy rights, handling data responsibly, and ensuring the accuracy and objectivity of findings. Maintaining confidentiality is essential. For example, I’ve had instances where I needed to balance the need to thoroughly investigate a potential breach with the right to privacy of employees. In such cases, I ensure only relevant data is analyzed, always within the bounds of legal permissions and ethical guidelines. Understanding the legal framework – like the Computer Fraud and Abuse Act (CFAA) in the US, or the GDPR in Europe – is vital to conducting ethical and legally sound investigations.
Q 15. Explain the differences between intrusion detection and intrusion prevention systems.
Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) are both crucial security tools, but they differ significantly in their approach to threats. An IDS passively monitors network traffic and system activity for malicious behavior, alerting administrators when suspicious activity is detected. Think of it as a security guard observing activity – they can see a potential problem but can’t directly stop it. An IPS, on the other hand, actively prevents intrusions by blocking or modifying malicious traffic. It’s like having a security guard with the power to physically stop someone from entering.
Here’s a table summarizing the key differences:
| Feature | IDS | IPS |
|---|---|---|
| Functionality | Detection only; alerts administrators | Detection and prevention; blocks or modifies malicious traffic |
| Impact on network traffic | Minimal; passive monitoring | Significant; actively modifies or blocks traffic |
| Response Time | Slower; relies on manual intervention after detection | Faster; immediate response to threats |
| Deployment | Can be deployed inline or in a monitoring mode | Typically deployed inline |
| False Positives | Higher potential for false positives | Higher potential for false positives, but mitigation strategies can reduce this |
For example, an IDS might detect a port scan, alerting the security team. An IPS, in contrast, could automatically block the port scan attempts before they can escalate. Choosing between an IDS and an IPS or using both depends on the specific security requirements and risk tolerance of an organization.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. What is the significance of hashing in digital forensics?
Hashing is a cornerstone of digital forensics because it provides a unique ‘fingerprint’ for a file or data set. A cryptographic hash function takes an input (like a file) and produces a fixed-size string of characters (the hash). Even a tiny change in the original file will result in a completely different hash value. This property is invaluable for ensuring data integrity.
In digital forensics, hashing is used to:
- Verify data integrity: We can calculate the hash of a piece of evidence at the time of seizure and then recalculate it later. If the hashes match, we can be confident that the evidence hasn’t been tampered with.
- Identify duplicate files: By hashing files, we can quickly identify duplicates without having to compare the entire content of each file.
- Search for specific files: Hash values can be used to search for specific files across large datasets.
For instance, imagine investigating a malware infection. We might hash the suspected malicious executable at the scene. Later in the lab, we can compare this hash to known malware databases to identify the specific malware variant. If the hashes match, we have strong evidence that the suspected file is indeed the malicious software.
Q 17. How do you ensure the integrity of digital evidence?
Ensuring the integrity of digital evidence is paramount in digital forensics. A compromised chain of custody or altered evidence can invalidate an entire investigation. We utilize several techniques to guarantee integrity:
- Hashing: As discussed earlier, hashing allows us to verify that the evidence hasn’t been modified.
- Chain of custody documentation: This meticulously documented process tracks every person who handles the evidence, from seizure to analysis and disposal. Each step is time-stamped and signed, creating an unbroken chain of custody. A gap in the chain can severely compromise the evidence’s admissibility in court.
- Write-blocking devices: These devices prevent any modification of the original evidence during the forensic imaging process. They ensure that the data is copied without altering it in any way. This is crucial for maintaining the integrity of the original data source.
- Forensic imaging: A bit-stream copy of the original storage device is created, preserving every sector, even those seemingly empty. This clone is then used for analysis, while the original remains untouched.
- Using validated forensic tools: Employing tools that have been rigorously tested and are free from bugs or vulnerabilities is essential. The integrity of a forensic tool can directly affect the integrity of the digital evidence.
These measures, when implemented correctly, establish a robust and verifiable chain of custody, demonstrating that the evidence presented has not been tampered with and remains reliable.
Q 18. Describe your experience with log analysis.
Log analysis is a crucial aspect of incident response and digital forensics. It involves examining system logs – including security logs, application logs, web server logs, and database logs – to identify patterns, anomalies, and security breaches. My experience encompasses analyzing various log types from diverse operating systems and applications.
I’m proficient in using log management tools such as Splunk, ELK stack (Elasticsearch, Logstash, Kibana), and Graylog. My process typically involves:
- Data collection: Gathering logs from various sources, ensuring complete and accurate data.
- Data normalization and filtering: Cleaning and structuring the data to facilitate analysis, filtering out unnecessary or irrelevant entries.
- Pattern identification: Using regular expressions, statistical analysis, and anomaly detection techniques to identify unusual or suspicious activities.
- Correlation analysis: Connecting seemingly disparate log entries to uncover the complete picture of an incident.
- Timeline reconstruction: Creating a chronological timeline of events to track the progression of an attack or breach.
For example, during an investigation of a data breach, I once analyzed web server logs to identify the source of unauthorized access, user activity leading up to the breach, and the extent of data compromised. The log analysis revealed a sophisticated SQL injection attack, allowing me to pinpoint the vulnerability and recommend mitigations.
Q 19. Explain your understanding of the different types of cyber threats.
The landscape of cyber threats is constantly evolving, but some common categories include:
- Malware: This broad category encompasses viruses, worms, trojans, ransomware, and spyware. Malware aims to damage, disrupt, or gain unauthorized access to systems.
- Phishing and social engineering: These attacks exploit human psychology to trick individuals into revealing sensitive information or clicking malicious links.
- Denial-of-Service (DoS) attacks: These attacks flood a system or network with traffic, making it unavailable to legitimate users.
- Man-in-the-middle (MITM) attacks: The attacker intercepts communication between two parties, eavesdropping or manipulating the data.
- SQL injection: This attack targets database applications, allowing attackers to execute malicious SQL code.
- Cross-site scripting (XSS): This attack injects malicious scripts into websites, compromising user sessions or stealing sensitive data.
- Zero-day exploits: These attacks target vulnerabilities that are unknown to the vendor, making them difficult to defend against.
- Advanced Persistent Threats (APTs): Highly sophisticated and persistent attacks, often state-sponsored, aimed at long-term infiltration and data theft.
Understanding the diverse nature of these threats is crucial for developing effective security strategies and incident response plans. The specific threats an organization faces will depend on their industry, size, and online presence.
Q 20. What is your experience with vulnerability scanning and penetration testing?
I have extensive experience in vulnerability scanning and penetration testing. Vulnerability scanning involves automated tools to identify known weaknesses in systems and applications. Penetration testing, also known as ethical hacking, simulates real-world attacks to assess the effectiveness of security controls. It goes beyond simple vulnerability scanning by actively attempting to exploit identified vulnerabilities.
My experience includes using tools such as Nessus, OpenVAS, Metasploit, and Nmap. My penetration testing methodology typically follows a structured approach, including:
- Planning and scoping: Defining the objectives, targets, and permissible activities.
- Reconnaissance: Gathering information about the target system.
- Vulnerability scanning: Identifying potential weaknesses.
- Exploitation: Attempting to exploit identified vulnerabilities.
- Post-exploitation: Assessing the impact of a successful exploitation.
- Reporting: Documenting findings, including identified vulnerabilities, their severity, and remediation recommendations.
For example, in a recent penetration test, I identified a critical vulnerability in a web application that could have allowed attackers to gain complete control of the system. My report included detailed steps on how to reproduce the vulnerability, its potential impact, and specific code changes to remediate the issue.
Q 21. How do you document your findings in a forensic investigation?
Forensic documentation is crucial for maintaining the integrity of the investigation and ensuring that findings are presented accurately and defensibly. My documentation follows a standardized format, typically including:
- Case file: A central repository for all case-related information, including initial reports, evidence logs, and final reports.
- Chain of custody documentation: Meticulously detailing the handling of evidence, ensuring its integrity.
- Evidence logs: Recording all evidence collected, its source, and any actions taken.
- Forensic imaging reports: Detailed reports of the forensic imaging process, including hash values and verification.
- Timeline of events: A chronological reconstruction of the events based on log analysis and other evidence.
- Analysis reports: Thorough reports of the forensic analysis, including methodology, findings, and interpretations.
- Conclusions and recommendations: Summarizing the findings and suggesting specific steps to improve security.
All documentation is written in a clear, concise, and objective manner, avoiding speculation and ensuring that all claims are supported by evidence. The format and level of detail are adapted based on the specific requirements of the investigation, potentially including courtroom admissibility considerations.
Q 22. Describe your experience with different operating systems (Windows, Linux, macOS) in a forensic context.
My experience spans various operating systems crucial in digital forensics. Understanding the nuances of each is paramount for effective investigation.
- Windows: I’m proficient in analyzing Windows systems, from older versions like Windows XP to the latest iterations. This includes understanding the registry, file system structures (NTFS), event logs, and prefetch data. For instance, I’ve successfully recovered deleted files from Windows systems using tools like FTK Imager and Autopsy, reconstructing timelines of user activity from the event logs to pinpoint the source of a data breach.
- Linux: My Linux expertise covers various distributions, from Ubuntu to CentOS. I understand the intricacies of the ext4 file system, log files, and the command-line interface which is frequently needed for low-level analysis. I’ve worked on cases involving Linux servers, recovering critical data from compromised systems. This involved using tools like The Sleuth Kit (TSK) to carve files from disk images and analyze file metadata.
- macOS: I’m experienced in macOS forensics, focusing on the Apple File System (APFS), its unique features, and how data is handled differently compared to Windows or Linux. I’ve analyzed macOS systems for malware infections, recovering critical data and identifying attack vectors. This often involves working with the keychain, plist files, and system logs.
My approach always involves creating forensic images to preserve the original evidence integrity, followed by thorough analysis using appropriate tools and techniques specific to each operating system. The goal is always to uncover the complete story and build a robust, defensible case.
Q 23. How do you handle situations with limited resources during an investigation?
Resource limitations are a common challenge in digital forensics. My approach prioritizes efficiency and strategic resource allocation.
- Prioritization: I begin by clearly defining the scope of the investigation and prioritizing tasks based on their importance to the case. This involves focusing on high-value targets and identifying the most critical data points first.
- Tool Selection: I carefully select tools based on their efficiency and resource requirements. For instance, I might opt for command-line tools like
grepandfindover GUI-based applications when dealing with large datasets on resource-constrained machines. This minimizes the impact of resource consumption and speeds up the investigation. - Data Filtering: Instead of blindly analyzing all data, I use filters and search criteria to quickly isolate relevant information. This significantly reduces processing time and allows me to focus on the crucial details.
- Collaboration: In scenarios with extremely limited resources, collaboration with other investigators or forensic labs becomes vital. This allows us to share resources and expertise, leveraging collective strengths to overcome limitations.
For example, I once worked on a case with limited storage space. I utilized data carving techniques to extract only the essential files, saving significant storage space while preserving the integrity of the evidence.
Q 24. Explain your understanding of data recovery techniques.
Data recovery techniques are central to digital forensics. They involve retrieving data that has been deleted, corrupted, or otherwise lost. Understanding the underlying principles of storage media is crucial.
- File Carving: This involves reconstructing files from raw disk data based on file headers and footers. It’s invaluable when dealing with fragmented files or systems where file system metadata is damaged. Tools like
scalpelandforemostare often utilized. - Data Recovery Software: Software like Recuva or PhotoRec can recover deleted files by identifying file signatures and reconstructing deleted entries from file system metadata. This works well for accidental deletions.
- Disk Imaging: Creating a forensic image of the storage device is a fundamental step. This preserves the original evidence while allowing analysis on a separate drive, preventing accidental modification or destruction of the original data.
- Advanced Techniques: For severely damaged media, more sophisticated techniques are needed. This could involve specialized labs, equipment (e.g., cleanroom), and methods for working with physically damaged hard drives.
Imagine a scenario where a hard drive has failed. Using a combination of disk imaging and data recovery software, I could create an image of the drive and then employ specialized software to recover recoverable data even if the file system itself is corrupted.
Q 25. What is your experience with cloud forensics?
Cloud forensics is an increasingly important area, requiring specialized skills and tools. It differs significantly from traditional computer forensics due to the distributed nature of cloud environments.
- API Access: Many cloud providers offer APIs that allow investigators to access log data and user activity. Understanding these APIs is crucial for efficient data collection.
- Data Location: Identifying where data is stored within a cloud environment is critical and can be challenging. Cloud environments distribute data across multiple servers and geographical locations.
- Legal Considerations: Obtaining data from cloud providers often necessitates legal processes and warrants due to data privacy laws.
- Specialized Tools: Cloud forensics often utilizes specialized tools designed for analyzing cloud-based data and logs. These tools are often provider-specific.
In a recent case involving a cloud-based email compromise, I used the provider’s API to retrieve email logs, user activity data, and other relevant information. This allowed me to trace the attacker’s activities and identify the point of compromise.
Q 26. How familiar are you with various file systems (NTFS, FAT, ext4)?
Understanding different file systems is essential for effective digital forensics. Each file system has its own structure and metadata, impacting how data is stored and accessed.
- NTFS (New Technology File System): This is the primary file system used by Windows. I have extensive experience working with NTFS, including its journaling features, security descriptors, and alternate data streams. Understanding NTFS is crucial for finding hidden or deleted files.
- FAT (File Allocation Table): FAT file systems (FAT16, FAT32) are older and simpler than NTFS, commonly found on older Windows systems, USB drives, and some embedded devices. I’m experienced in analyzing FAT systems and understanding their limitations compared to NTFS.
- ext4 (Fourth Extended Filesystem): This is the most common file system used in Linux systems. I’m proficient in navigating ext4 file structures, understanding its journaling features, and recovering deleted data.
Knowing these file systems allows me to effectively analyze data, interpret metadata, and recover deleted files, regardless of the underlying operating system.
Q 27. Describe your experience with memory forensics.
Memory forensics is a critical area, involving the analysis of computer memory (RAM) to obtain live system information. It’s crucial for identifying running processes, network connections, and malware activity.
- Live Acquisition: Memory acquisition needs to be done quickly and carefully. A live acquisition captures the RAM data while the system is running, while a crash dump grabs the memory post-system crash or shutdown. Both techniques have unique advantages and limitations.
- Memory Analysis Tools: Specialized tools, such as Volatility and Rekall, are crucial for analyzing memory images. These tools can identify running processes, network connections, and malware artifacts.
- Artifact Identification: Memory analysis allows identifying malware processes, network connections, and other critical artifacts that might not be present on the hard drive.
In a recent incident response, I used Volatility to analyze a memory image and discovered evidence of malware communication with a command-and-control server. This was crucial in identifying and neutralizing the threat.
Key Topics to Learn for Digital Forensics and Incident Response Interview
- Network Forensics: Understanding network protocols, packet analysis, and intrusion detection systems. Practical application: Analyzing network traffic logs to identify malicious activity and compromised systems.
- Disk Forensics: Mastering file carving, data recovery techniques, and understanding file systems. Practical application: Recovering deleted files and reconstructing events from a compromised hard drive.
- Memory Forensics: Analyzing volatile memory (RAM) to identify running processes, malware, and system activity. Practical application: Investigating active malware infections and recovering system state information.
- Incident Response Methodology: Understanding frameworks like NIST Cybersecurity Framework and the incident response lifecycle (preparation, identification, containment, eradication, recovery, lessons learned). Practical application: Developing and implementing incident response plans for different scenarios.
- Malware Analysis: Identifying malware types, analyzing their behavior, and understanding reverse engineering techniques. Practical application: Determining the capabilities and impact of malicious software.
- Digital Evidence Collection and Preservation: Mastering chain of custody, legal aspects, and data acquisition methods. Practical application: Ensuring the integrity and admissibility of digital evidence in legal proceedings.
- Log Analysis: Interpreting system logs, security logs, and application logs to identify anomalies and security breaches. Practical application: Correlating events from different log sources to reconstruct attack timelines.
- Vulnerability Assessment and Penetration Testing: Understanding common vulnerabilities and ethical hacking techniques to improve security posture. Practical application: Identifying and mitigating potential weaknesses in systems and networks.
Next Steps
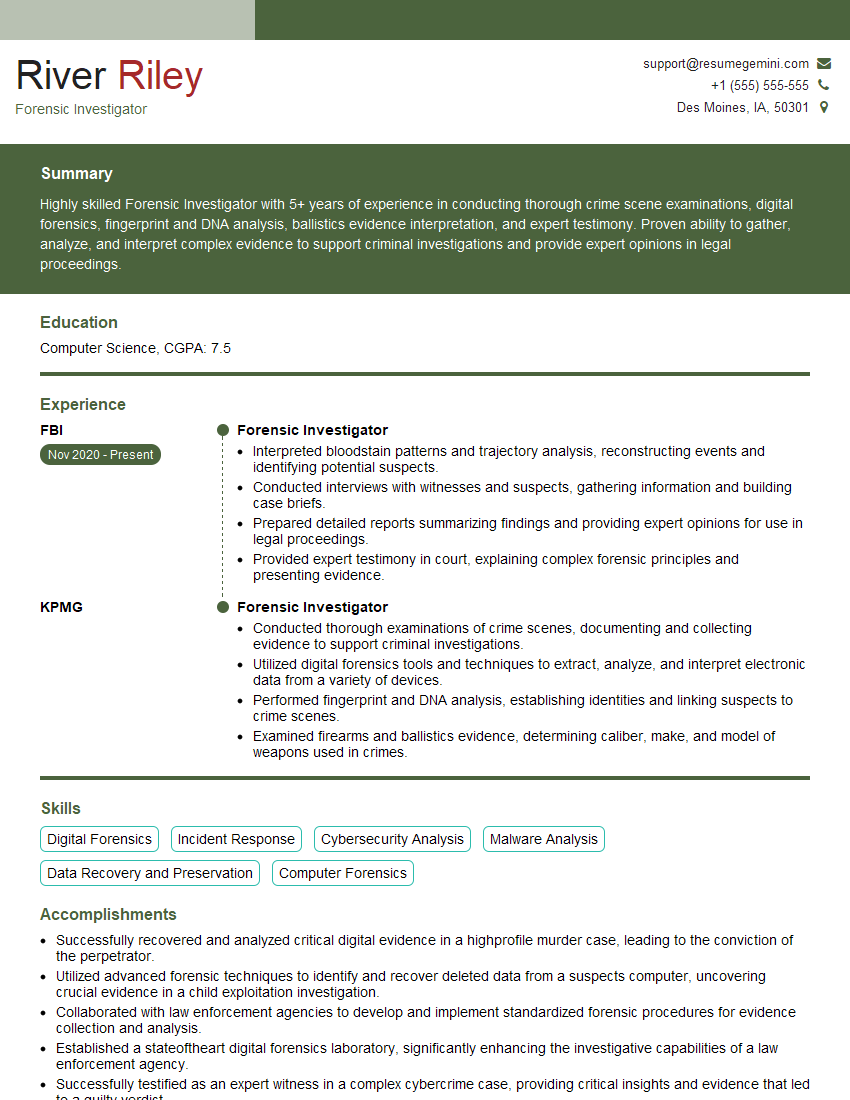
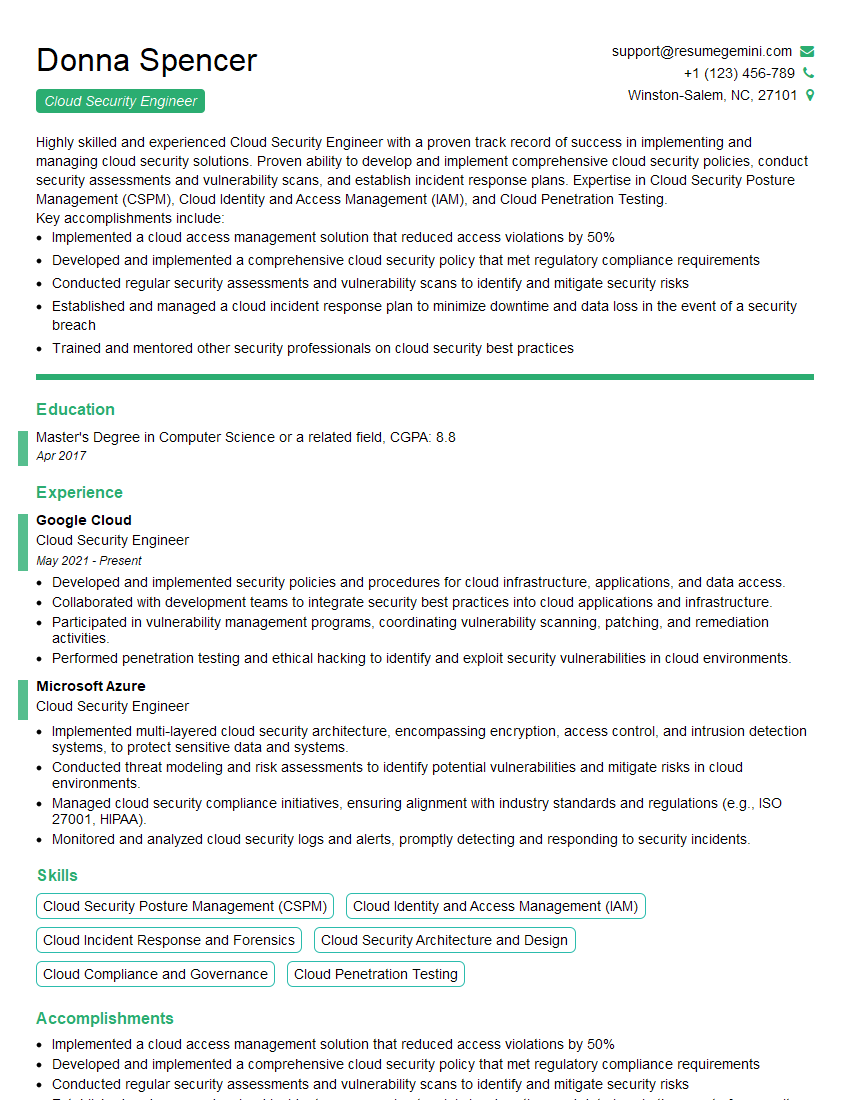
Mastering Digital Forensics and Incident Response opens doors to exciting and rewarding careers in cybersecurity. This field is constantly evolving, offering opportunities for continuous learning and professional growth. To maximize your job prospects, crafting a compelling and ATS-friendly resume is crucial. ResumeGemini is a trusted resource that can help you build a professional resume that highlights your skills and experience effectively. ResumeGemini provides examples of resumes tailored specifically to Digital Forensics and Incident Response roles, ensuring your application stands out from the competition. Invest time in refining your resume – it’s your first impression!
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Attention music lovers!
Wow, All the best Sax Summer music !!!
Spotify: https://open.spotify.com/artist/6ShcdIT7rPVVaFEpgZQbUk
Apple Music: https://music.apple.com/fr/artist/jimmy-sax-black/1530501936
YouTube: https://music.youtube.com/browse/VLOLAK5uy_noClmC7abM6YpZsnySxRqt3LoalPf88No
Other Platforms and Free Downloads : https://fanlink.tv/jimmysaxblack
on google : https://www.google.com/search?q=22+AND+22+AND+22
on ChatGPT : https://chat.openai.com?q=who20jlJimmy20Black20Sax20Producer
Get back into the groove with Jimmy sax Black
Best regards,
Jimmy sax Black
www.jimmysaxblack.com
Hi I am a troller at The aquatic interview center and I suddenly went so fast in Roblox and it was gone when I reset.
Hi,
Business owners spend hours every week worrying about their website—or avoiding it because it feels overwhelming.
We’d like to take that off your plate:
$69/month. Everything handled.
Our team will:
Design a custom website—or completely overhaul your current one
Take care of hosting as an option
Handle edits and improvements—up to 60 minutes of work included every month
No setup fees, no annual commitments. Just a site that makes a strong first impression.
Find out if it’s right for you:
https://websolutionsgenius.com/awardwinningwebsites
Hello,
we currently offer a complimentary backlink and URL indexing test for search engine optimization professionals.
You can get complimentary indexing credits to test how link discovery works in practice.
No credit card is required and there is no recurring fee.
You can find details here:
https://wikipedia-backlinks.com/indexing/
Regards
NICE RESPONSE TO Q & A
hi
The aim of this message is regarding an unclaimed deposit of a deceased nationale that bears the same name as you. You are not relate to him as there are millions of people answering the names across around the world. But i will use my position to influence the release of the deposit to you for our mutual benefit.
Respond for full details and how to claim the deposit. This is 100% risk free. Send hello to my email id: lukachachibaialuka@gmail.com
Luka Chachibaialuka
Hey interviewgemini.com, just wanted to follow up on my last email.
We just launched Call the Monster, an parenting app that lets you summon friendly ‘monsters’ kids actually listen to.
We’re also running a giveaway for everyone who downloads the app. Since it’s brand new, there aren’t many users yet, which means you’ve got a much better chance of winning some great prizes.
You can check it out here: https://bit.ly/callamonsterapp
Or follow us on Instagram: https://www.instagram.com/callamonsterapp
Thanks,
Ryan
CEO – Call the Monster App
Hey interviewgemini.com, I saw your website and love your approach.
I just want this to look like spam email, but want to share something important to you. We just launched Call the Monster, a parenting app that lets you summon friendly ‘monsters’ kids actually listen to.
Parents are loving it for calming chaos before bedtime. Thought you might want to try it: https://bit.ly/callamonsterapp or just follow our fun monster lore on Instagram: https://www.instagram.com/callamonsterapp
Thanks,
Ryan
CEO – Call A Monster APP
To the interviewgemini.com Owner.
Dear interviewgemini.com Webmaster!
Hi interviewgemini.com Webmaster!
Dear interviewgemini.com Webmaster!
excellent
Hello,
We found issues with your domain’s email setup that may be sending your messages to spam or blocking them completely. InboxShield Mini shows you how to fix it in minutes — no tech skills required.
Scan your domain now for details: https://inboxshield-mini.com/
— Adam @ InboxShield Mini
support@inboxshield-mini.com
Reply STOP to unsubscribe
Hi, are you owner of interviewgemini.com? What if I told you I could help you find extra time in your schedule, reconnect with leads you didn’t even realize you missed, and bring in more “I want to work with you” conversations, without increasing your ad spend or hiring a full-time employee?
All with a flexible, budget-friendly service that could easily pay for itself. Sounds good?
Would it be nice to jump on a quick 10-minute call so I can show you exactly how we make this work?
Best,
Hapei
Marketing Director
Hey, I know you’re the owner of interviewgemini.com. I’ll be quick.
Fundraising for your business is tough and time-consuming. We make it easier by guaranteeing two private investor meetings each month, for six months. No demos, no pitch events – just direct introductions to active investors matched to your startup.
If youR17;re raising, this could help you build real momentum. Want me to send more info?
Hi, I represent an SEO company that specialises in getting you AI citations and higher rankings on Google. I’d like to offer you a 100% free SEO audit for your website. Would you be interested?
Hi, I represent an SEO company that specialises in getting you AI citations and higher rankings on Google. I’d like to offer you a 100% free SEO audit for your website. Would you be interested?