The thought of an interview can be nerve-wracking, but the right preparation can make all the difference. Explore this comprehensive guide to High Value Asset Protection interview questions and gain the confidence you need to showcase your abilities and secure the role.
Questions Asked in High Value Asset Protection Interview
Q 1. Explain your understanding of risk assessment methodologies for high-value assets.
Risk assessment for high-value assets isn’t just about identifying threats; it’s about understanding their likelihood and potential impact. We use a multi-layered approach, starting with a comprehensive asset inventory. This includes not only the physical assets like artwork, jewelry, or real estate but also intangible assets such as intellectual property or valuable data. Next, we identify potential threats. This can range from natural disasters and accidental damage to theft, vandalism, cyberattacks, or even internal threats. For each threat, we analyze its likelihood – how probable is it to occur? – and its impact – what would be the financial, reputational, or operational consequences if it did occur? This is often visualized using a risk matrix, which helps prioritize vulnerabilities. For instance, a high-likelihood, high-impact threat like a fire in a building housing valuable art would demand immediate attention and robust mitigation strategies, far more than a low-likelihood threat like a sophisticated cyberattack targeting a relatively obscure database.
Methodologies like Failure Mode and Effects Analysis (FMEA) and HAZOP (Hazard and Operability Study) are employed to systematically identify and assess potential failures in security systems or procedures. Quantitative methods, involving statistical data analysis of past incidents, might also inform the risk assessment. Ultimately, the goal is to generate a prioritized list of vulnerabilities, guiding the allocation of resources for protective measures.
Q 2. Describe your experience implementing and managing security systems for high-value assets.
My experience spans over 15 years, encompassing projects with diverse high-value assets, from securing private art collections and luxury yachts to protecting high-tech research facilities and sensitive data centers. In one project, for example, we implemented a multi-layered security system for a private art collection housed in a renovated historical building. This involved integrating state-of-the-art CCTV systems with advanced analytics for threat detection, sophisticated access control systems with biometric authentication, and environmental monitoring systems to prevent damage from temperature fluctuations or humidity changes. We also developed a comprehensive emergency response plan, coordinating with local law enforcement and specialist art recovery teams. In another engagement, we focused on cyber security for a tech startup with highly valuable intellectual property. This included implementing robust firewalls, intrusion detection systems, and penetration testing to identify and address vulnerabilities. My role involved not only the initial design and implementation of these systems but also ongoing monitoring, maintenance, and system upgrades to ensure continuous protection. Regular training for personnel on security protocols was another crucial aspect, forming a vital element of our security architecture.
Q 3. What are the key differences between physical and cyber security threats to high-value assets?
While both physical and cyber security threats target high-value assets, their methods and impact differ significantly. Physical threats involve direct attacks on the physical asset itself. This could include theft, vandalism, sabotage, or damage from natural disasters. For instance, a burglary targeting a jewellery collection or a fire damaging a historical building housing valuable artifacts are examples of physical threats. Cyber security threats, on the other hand, target digital assets or systems used to control physical assets. This could range from data breaches and ransomware attacks to denial-of-service attacks and sophisticated phishing scams. Think of a cyberattack targeting a smart home system to gain access to the house or a data breach leading to the theft of intellectual property. The key difference lies in the nature of the attack – physical versus digital – and the assets targeted. Often, they are interconnected, with a cyberattack potentially compromising a physical security system and vice-versa.
Q 4. How would you develop a comprehensive security plan for a high-net-worth individual?
A comprehensive security plan for a high-net-worth individual (HNWI) requires a holistic approach, considering all aspects of their life, assets, and vulnerabilities. The process begins with a thorough risk assessment, identifying potential threats to their person, property, and reputation. This might include analyzing travel patterns, identifying potential stalking or kidnapping risks, assessing the security of their residences and other properties, and evaluating vulnerabilities in their digital footprint. The plan would then incorporate a range of security measures, including:
- Physical Security: Fortified residences, advanced alarm systems, CCTV surveillance, access control systems, security personnel, and vehicle protection.
- Cyber Security: Robust firewalls, intrusion detection systems, data encryption, anti-virus software, secure password management, and regular security audits of all devices and systems.
- Personal Security: Executive protection services, threat assessment and mitigation, travel security planning, and personal safety training.
- Reputational Security: Crisis management planning, media relations training, and proactive measures to protect their reputation against potential attacks or scandals.
- Legal and Insurance: Proper insurance coverage to address potential financial losses, consultation with legal experts regarding asset protection and privacy.
The plan must be dynamic, regularly reviewed and updated in light of evolving threats and changing circumstances. Regular security briefings and training for the HNWI and their staff are vital elements to ensure its effectiveness.
Q 5. Explain your experience in investigating theft or loss of high-value assets.
My experience in investigating the theft or loss of high-value assets involves a multi-stage process. It starts with securing the scene, preserving evidence, and interviewing witnesses. In one case involving the theft of valuable artwork from a private collection, we collaborated with law enforcement, forensic specialists, and art recovery experts. We meticulously documented the scene, analyzed security footage, and investigated potential points of entry. We also conducted thorough background checks on individuals with access to the premises and reviewed insurance policies to ensure proper documentation and claims processes. The process involved close coordination with insurers, legal counsel, and international law enforcement agencies, if the stolen items crossed national borders. Technological investigation is often crucial – we might analyze digital records, GPS data, or communications records to trace the assets or identify perpetrators. The end goal is to recover the assets, identify culprits, and prevent future incidents. Thorough documentation at every stage is essential for evidence gathering and potential legal proceedings.
Q 6. How do you prioritize security threats and allocate resources effectively?
Prioritizing security threats and allocating resources effectively involves a structured approach. We leverage the risk assessment findings to identify high-impact, high-likelihood threats. These threats are prioritized for immediate mitigation. For instance, a vulnerability identified in the physical security system of a building holding valuable assets would take precedence over a less likely cyber threat, even if the cyber threat’s potential impact is high. Resources – personnel, technology, and budget – are then allocated based on this prioritized list. A cost-benefit analysis is often conducted to ensure that security investments are justified and proportionate to the risk involved. We frequently employ risk-based decision-making frameworks, prioritizing mitigation strategies that offer the highest reduction in risk for the lowest cost. Regular review and adjustments to the plan are crucial to adapt to evolving risks and changing circumstances. This ensures that the resources are always targeted at the most critical vulnerabilities.
Q 7. Describe your experience with security technology, such as CCTV, access control systems, and alarm systems.
My experience with security technology is extensive. I’ve designed, implemented, and managed various systems, including CCTV networks with advanced analytics capabilities such as facial recognition and intrusion detection, sophisticated access control systems integrating biometric authentication and smart card readers, and integrated alarm systems that incorporate fire detection, intrusion detection, and environmental monitoring. For instance, in one project, we implemented a CCTV system for a large corporate campus that integrated video analytics to detect suspicious activities, such as loitering or unauthorized entry. The system automatically alerted security personnel, enabling rapid response. We also used access control systems to restrict entry to sensitive areas based on user roles and permissions. Alarm systems provided real-time monitoring of various security parameters and enabled immediate response to critical events. The choice and integration of these systems are always customized to the specific needs of the client and the nature of the assets being protected. Regular testing and maintenance of these systems are crucial to ensure their effectiveness and reliability.
Q 8. How would you handle a security breach involving high-value assets?
Handling a security breach involving high-value assets requires a swift, coordinated response. My approach follows a structured methodology focusing on containment, investigation, recovery, and prevention.
Containment: The immediate priority is to isolate the breach to prevent further damage. This involves disconnecting affected systems, restricting access, and securing any compromised data. Think of it like containing a fire – you need to stop the spread before tackling the source.
Investigation: A thorough investigation is launched to determine the root cause, extent of the breach, and any compromised assets. Forensic specialists are deployed to analyze logs, systems, and data to identify vulnerabilities and the methods used by attackers. This is like a crime scene investigation, meticulously piecing together the events to understand what happened.
Recovery: This stage focuses on restoring systems, recovering data, and ensuring business continuity. Depending on the severity, this could involve restoring from backups, implementing recovery procedures, and potentially engaging third-party specialists for data recovery or system restoration.
Prevention: Once the breach is contained and investigated, a comprehensive review of security protocols and controls is carried out to identify vulnerabilities and implement preventative measures. This could include updating security software, strengthening access controls, enhancing monitoring, and implementing employee training programs.
For instance, in a scenario where a ransomware attack encrypted a company’s critical financial data, my team would immediately isolate the affected servers, launch a forensic investigation to determine the point of entry and the type of ransomware, negotiate with (or if necessary, overcome) the attacker for data recovery, and then implement multi-factor authentication and enhanced network segmentation to prevent future attacks.
Q 9. What are your strategies for mitigating insider threats?
Mitigating insider threats requires a multi-layered approach focusing on prevention, detection, and response.
- Prevention: This includes robust background checks for employees, strong access control policies (least privilege principle), regular security awareness training, and clear guidelines on acceptable use of company resources. Think of it as building a strong, locked fortress to deter unauthorized entry.
- Detection: Continuous monitoring of system activity, user behavior analytics, and audit logs can help identify suspicious patterns or anomalous behavior. This is akin to having security guards patrolling the fortress and using surveillance systems to detect any unusual activity.
- Response: A clear incident response plan detailing procedures for investigating and addressing insider threats is crucial. This plan should outline steps for containing the breach, recovering compromised data, and taking disciplinary action against the perpetrator.
For example, we might implement data loss prevention (DLP) software to monitor sensitive data movement, set up user access monitoring to detect unusual login attempts or access patterns outside of normal working hours, and have clear policies about personal devices and USB usage to mitigate risks of data leaks or malicious software installation.
Q 10. Describe your experience with crisis management and emergency response protocols.
My experience in crisis management and emergency response involves developing and implementing comprehensive plans for various scenarios, from natural disasters to cyberattacks. This involves close collaboration with key stakeholders, law enforcement, and potentially insurance providers.
Planning: We develop detailed plans outlining roles, responsibilities, communication protocols, and recovery procedures. Regular drills and simulations help refine these plans and ensure everyone is well-prepared. This involves establishing clear communication channels and designated points of contact for quick and effective coordination during emergencies.
Response: During a crisis, my role is to activate the plan, coordinate response teams, and ensure the safety of personnel and assets. We prioritize effective communication to keep stakeholders informed and manage public perception. The goal is to minimize disruption and ensure a swift recovery.
Recovery: After the immediate crisis, we conduct a thorough post-incident analysis to identify lessons learned and areas for improvement. This informs updates to our plans and protocols to enhance future preparedness.
For instance, during a recent incident involving a server failure, we activated our emergency response plan, switched to a redundant server within minutes, ensuring minimal downtime and maintaining business operations. We then conducted a thorough review to enhance backup procedures and improve recovery times.
Q 11. How do you ensure compliance with relevant security regulations and industry best practices?
Ensuring compliance with security regulations and industry best practices is paramount. This involves a multi-pronged approach:
- Understanding Regulations: We stay abreast of relevant regulations like GDPR, CCPA, HIPAA (depending on the nature of the assets and industry), and other applicable laws. This ensures we understand the requirements and can implement compliant security measures.
- Implementing Controls: We design and implement security controls that meet or exceed regulatory requirements. This could involve implementing data encryption, access control mechanisms, security information and event management (SIEM) systems, and regular vulnerability assessments.
- Auditing and Monitoring: Regular security audits and penetration testing help identify weaknesses and verify that security controls are effective. Continuous monitoring allows us to quickly detect and respond to security threats.
- Documentation: Maintaining comprehensive documentation on security policies, procedures, and compliance efforts is critical for demonstrating our commitment to regulatory compliance and transparency.
For example, when handling personal data, we strictly adhere to GDPR regulations by implementing measures for data minimization, purpose limitation, and data subject rights. We meticulously document all our compliance activities to facilitate audits and demonstrate our adherence to regulations.
Q 12. Explain your understanding of insurance and risk transfer strategies for high-value assets.
Insurance and risk transfer strategies are crucial for protecting high-value assets. Understanding various insurance policies and their limitations is vital for effective risk management.
Types of Insurance: Different types of insurance cover various risks. These may include property insurance, cyber insurance, business interruption insurance, and specialized policies for high-value items like artwork or jewelry. The selection depends on the specific nature of the assets and the associated risks.
Risk Assessment: A comprehensive risk assessment is crucial to determine the appropriate level of insurance coverage. This involves identifying potential threats and vulnerabilities and assessing the likelihood and potential impact of each risk.
Policy Selection: Choosing the right policy involves carefully reviewing policy terms, conditions, coverage limits, and deductibles. It’s critical to ensure that the coverage aligns with the value of the assets and the level of risk.
Risk Mitigation: Insurance should be considered as part of a broader risk management strategy, not a complete solution. Implementing robust security measures to mitigate risks can lower insurance premiums and reduce the likelihood of claims.
For example, a museum might obtain specialized insurance for valuable artifacts, complemented by robust security measures, including alarm systems, security guards, and climate control. A technology company might have cyber insurance to cover data breaches, combined with advanced cybersecurity systems to prevent attacks.
Q 13. What are the common vulnerabilities in high-value asset protection and how can they be addressed?
High-value assets are vulnerable to various threats. Understanding these vulnerabilities is key to effective protection.
- Physical Threats: Theft, vandalism, natural disasters (fire, flood, earthquake), and accidental damage pose significant risks.
- Cyber Threats: Data breaches, ransomware attacks, malware, and denial-of-service attacks can compromise data integrity and availability.
- Insider Threats: Malicious or negligent employees can pose a significant risk, potentially leading to data theft or sabotage.
- Operational Risks: Process failures, inadequate security controls, and lack of employee training can increase vulnerability.
Addressing Vulnerabilities: Addressing these vulnerabilities requires a combination of physical and cyber security measures. This includes robust physical security (access controls, surveillance, alarm systems), strong cybersecurity protocols (encryption, firewalls, intrusion detection systems), employee training, and business continuity planning. Regular security assessments and vulnerability scans are critical for identifying and mitigating emerging threats.
Q 14. How would you assess the security of a physical location housing high-value assets?
Assessing the security of a physical location housing high-value assets is a multi-step process.
- Physical Security Assessment: This involves examining the perimeter security (fencing, gates, lighting), access control systems (entry points, keycard systems, surveillance cameras), alarm systems, and security personnel. We look for vulnerabilities like weak points in the perimeter, inadequate lighting, insufficient surveillance coverage, or insufficient security personnel.
- Environmental Assessment: This considers factors like environmental risks (flooding, fire hazards), potential natural disasters, and building security (structural integrity, fire suppression systems).
- Internal Security: This involves evaluating internal security measures within the building, including access controls to sensitive areas, data protection measures, and security procedures.
- Technology Assessment: We assess the security of technology systems, such as network infrastructure, data storage systems, and security monitoring systems.
- Personnel Assessment: This examines security awareness training, background checks of personnel, and established security protocols for employees and visitors.
This comprehensive approach helps identify vulnerabilities and develop a tailored security plan to mitigate risks. It’s like conducting a thorough health check for the location, identifying its strengths and weaknesses to develop a robust security plan, making it as impregnable as possible.
Q 15. Describe your experience with conducting security audits and vulnerability assessments.
Security audits and vulnerability assessments are crucial for identifying weaknesses in an organization’s high-value asset protection strategy. My approach involves a multi-layered process. First, I conduct a thorough risk assessment, identifying potential threats and vulnerabilities specific to the organization’s assets, location, and operational environment. This includes reviewing existing security measures, physical infrastructure, access control systems, and personnel practices. Then, I perform penetration testing, simulating real-world attacks to exploit weaknesses and assess the effectiveness of current security controls. This might involve social engineering exercises, network scans, and attempts to bypass physical security measures. Finally, I prepare a comprehensive report detailing findings, including prioritized vulnerabilities and recommendations for remediation. For example, during an audit for a high-net-worth individual’s art collection, I identified vulnerabilities in the climate control system which could have damaged the artwork. My recommendations resulted in system upgrades and enhanced monitoring, mitigating the risk significantly.
- Risk Assessment: Identifying potential threats and vulnerabilities.
- Penetration Testing: Simulating real-world attacks to test security.
- Reporting & Remediation: Providing detailed findings and recommendations.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. How familiar are you with different types of surveillance technologies and their applications?
My familiarity with surveillance technologies is extensive, encompassing both traditional and modern systems. I’m proficient in CCTV systems, including IP-based cameras with advanced analytics like facial recognition and intrusion detection. I also have experience with access control systems (ACS), incorporating biometric authentication, RFID readers, and integrated security management systems. Furthermore, I’m knowledgeable in advanced surveillance techniques like drone surveillance for perimeter security and thermal imaging for detecting hidden threats. The application of these technologies depends entirely on the specific asset and threat profile. For instance, a high-security vault might leverage a combination of CCTV, motion sensors, and biometric access control, while a large estate could benefit from a drone-based perimeter patrol supplemented by strategically placed CCTV cameras.
- CCTV & Analytics: IP-based cameras with advanced features.
- Access Control Systems (ACS): Biometric, RFID, and integrated systems.
- Advanced Surveillance: Drone surveillance, thermal imaging.
Q 17. What are your methods for verifying the authenticity and provenance of high-value assets?
Verifying the authenticity and provenance of high-value assets requires a multi-faceted approach. This begins with thorough documentation review, including certificates of authenticity, purchase records, and any relevant historical information. I utilize various authentication methods depending on the asset type. For artwork, this might involve consulting with art experts, analyzing the piece for stylistic consistency, and comparing it against known works by the artist. For jewelry, gemological analysis might be necessary, using specialized equipment to determine the quality and authenticity of precious stones. Chain of custody is crucial; I ensure a clear and unbroken record of the asset’s ownership and handling from acquisition to its current location. For example, while assessing a collection of antique furniture, I worked with a renowned furniture expert who confirmed the age and authenticity through detailed examination of joinery techniques and wood types.
- Documentation Review: Certificates of authenticity, purchase records.
- Expert Consultation: Art experts, gemologists, etc.
- Scientific Analysis: Gemological testing, material analysis.
- Chain of Custody Verification: Ensuring a complete ownership history.
Q 18. How do you balance security measures with the operational needs of the organization?
Balancing security with operational needs requires a delicate touch. Overly restrictive security measures can hamper productivity and workflow. My approach focuses on a risk-based approach – prioritizing security measures based on the level of risk associated with specific assets and operational activities. I work closely with the organization to understand their operational requirements and design security solutions that seamlessly integrate into their workflows. For example, instead of completely restricting access to a sensitive area, we might implement a two-factor authentication system that is minimally disruptive. This approach allows us to maintain strong security while ensuring smooth operations. Flexibility and adaptability are key. We must continually reassess the balance between security and operational needs as the threat landscape evolves and the organization’s requirements change.
Q 19. Describe your experience with developing and delivering security training programs.
I have extensive experience developing and delivering security awareness training programs tailored to the specific needs of different organizations and their employees. My programs are not just lecture-based but incorporate interactive elements like simulations and real-life scenarios to enhance engagement and knowledge retention. For example, a program for a financial institution might focus on phishing awareness and safe handling of sensitive data, whereas a program for an art gallery might highlight security procedures specific to handling and transporting valuable artworks. Post-training assessments and ongoing reinforcement are vital to ensure sustained improvement in security practices.
- Tailored Curriculum: Specific to the organization’s needs and risk profile.
- Interactive Methods: Simulations, case studies, real-life examples.
- Ongoing Reinforcement: Regular updates, refresher courses, and assessments.
Q 20. What are your strategies for maintaining a secure environment in a dynamic and rapidly changing threat landscape?
Maintaining a secure environment in a dynamic threat landscape requires a proactive and adaptable strategy. This involves continuous monitoring of the threat landscape for emerging vulnerabilities and attack vectors, incorporating threat intelligence into our risk assessments and security planning. We leverage advanced technologies such as intrusion detection systems (IDS) and security information and event management (SIEM) systems to detect and respond to threats in real-time. Regular security audits and vulnerability assessments are crucial to identify weaknesses before they can be exploited. Moreover, a robust incident response plan is essential to minimize damage and ensure business continuity in the event of a security breach. Regular drills and simulations help test the effectiveness of the plan and train personnel for effective response.
Q 21. How do you stay up-to-date on the latest trends and technologies in high-value asset protection?
Staying up-to-date is paramount in this field. I achieve this through several methods: I actively participate in professional organizations and attend industry conferences and webinars, networking with other experts and learning about the latest threats and technologies. I subscribe to relevant industry publications and journals, and I regularly review security advisories and vulnerability reports from reputable sources. Furthermore, I actively engage in online professional development courses and certifications to maintain my expertise in emerging security technologies and best practices. This ongoing learning is essential for adapting to the constantly evolving threat landscape and ensuring that our security measures remain effective.
Q 22. Describe a time you had to make a difficult decision related to security, and explain your reasoning.
One of the most challenging decisions I faced involved a high-net-worth client who insisted on keeping a significant portion of their valuable art collection in their primary residence despite our assessment highlighting significant security vulnerabilities. The residence lacked state-of-the-art security systems and was situated in a neighborhood with a rising crime rate. My reasoning hinged on balancing the client’s autonomy with our professional responsibility to mitigate risk.
Ultimately, I presented a tiered approach. We outlined the risks associated with the current situation, quantifying the potential financial and emotional losses. We then proposed a phased implementation of enhanced security measures, starting with immediate upgrades like improved alarm systems and security personnel, while also advocating for long-term solutions such as a secured vault facility. This approach acknowledged their preferences while demonstrably mitigating the security risks. The client appreciated the collaborative approach and opted for the phased improvement plan, ultimately strengthening the security posture without compromising the client’s wishes entirely. This situation underscored the importance of transparent communication and risk assessment when dealing with discerning clientele.
Q 23. How would you handle a situation where there’s a conflict between security protocols and client preferences?
Conflict between security protocols and client preferences is a common occurrence in high-value asset protection. The key is finding a balance that prioritizes security without compromising the client’s comfort and needs. My approach involves a structured discussion and negotiation process.
- Understanding Client Needs: First, I thoroughly understand the client’s concerns and reasons behind their preferences. Are there specific aspects of the security protocols causing discomfort? Is there a misalignment in understanding the risk?
- Risk Assessment: I reassess the security risks, outlining the potential consequences of deviating from established protocols. I present this information clearly and factually, using visuals and data to support the assessment.
- Negotiated Solution: Based on the risk assessment and client’s concerns, I propose alternative solutions that minimize risk while accommodating their preferences as much as possible. This might involve adjusting certain security measures, providing alternative technology or strategies, or offering additional training or education.
- Documentation: Any compromise reached is meticulously documented, outlining the agreed-upon security protocols, exceptions, and the rationale behind them. This ensures transparency and accountability.
For example, a client may resist installing certain surveillance technologies due to privacy concerns. We might negotiate a solution where surveillance is limited to specific areas or uses anonymized data, ensuring a balance between security and privacy.
Q 24. How familiar are you with international security protocols and regulations?
I possess extensive familiarity with international security protocols and regulations. My experience encompasses working with clients and assets across various jurisdictions, requiring me to navigate diverse legal and regulatory landscapes. This includes understanding and complying with data protection laws like GDPR (General Data Protection Regulation), international sanctions regulations, and asset protection laws in various countries.
I also stay abreast of evolving threats and best practices globally, leveraging resources like Interpol and national security agencies’ publications. Understanding these regulations is crucial not just for compliance but also for implementing robust security strategies that are effective and legally sound, regardless of location.
Q 25. How do you evaluate the effectiveness of your security measures?
Evaluating the effectiveness of security measures is an ongoing process. It’s not a one-time assessment but a continuous cycle of monitoring, analysis, and improvement. My approach involves several key steps:
- Regular Audits: We conduct routine audits of security systems and procedures, checking for vulnerabilities and weaknesses. These audits cover everything from physical security (e.g., access control, perimeter security) to cybersecurity (e.g., network security, data encryption).
- Vulnerability Assessments: We conduct penetration testing and vulnerability scans to identify potential weaknesses that could be exploited by malicious actors. These assessments help us proactively address potential threats before they become real-world problems.
- Incident Response: A robust incident response plan is essential for effectively handling security breaches. Regular drills and simulations test our readiness and response capabilities.
- Key Performance Indicators (KPIs): We track relevant KPIs, such as the number of security incidents, response times, and system uptime, to monitor the effectiveness of our security measures over time. This data provides insights into areas that need improvement.
- Technology Updates: The security landscape is constantly evolving. We regularly update our technologies and protocols to reflect the latest best practices and counter emerging threats.
By employing a multi-faceted approach that combines regular testing and monitoring with a commitment to continuous improvement, we ensure that our security measures remain robust and effective.
Q 26. Describe your experience with working with law enforcement agencies.
My experience with law enforcement agencies has been primarily collaborative. I have worked closely with various agencies, including local police departments and federal investigative bodies, on cases involving asset recovery, fraud investigations, and security breaches. This collaboration is often vital in situations requiring expertise in asset tracing, evidence preservation, and coordinating security responses.
I understand the importance of maintaining open communication and providing timely and accurate information to law enforcement. Building trust and establishing a strong working relationship is paramount for effective collaboration. My approach emphasizes professionalism, strict adherence to legal protocols, and a commitment to providing the necessary information and support to assist with their investigations.
Q 27. What are your salary expectations for this role?
My salary expectations for this role are in the range of $250,000 to $350,000 annually, commensurate with my experience and expertise in high-value asset protection. This is based on my extensive experience, proven track record of success, and in-depth knowledge of both domestic and international security protocols. I am open to discussing this further based on the specifics of the role and the overall compensation package.
Q 28. Do you have any questions for me?
Yes, I have a few questions. First, could you elaborate on the specific types of high-value assets this role would involve protecting? Secondly, what are the company’s existing security protocols and infrastructure? And finally, what are the opportunities for professional development and advancement within the organization?
Key Topics to Learn for High Value Asset Protection Interview
- Risk Assessment and Mitigation: Understanding the unique vulnerabilities of high-value assets (real estate, art, intellectual property, etc.) and developing strategies to minimize potential losses. Practical application: Developing a risk mitigation plan for a specific high-value asset class.
- Insurance and Indemnification: Exploring various insurance options and understanding the intricacies of policy coverage, claims processes, and indemnification agreements. Practical application: Analyzing different insurance policies to determine the best fit for a client’s portfolio.
- Legal and Regulatory Compliance: Navigating relevant laws and regulations concerning asset protection, including international implications and tax considerations. Practical application: Researching and summarizing the legal ramifications of a specific asset protection strategy.
- Security and Surveillance Technologies: Familiarizing yourself with advanced security systems, monitoring technologies, and their applications in protecting high-value assets. Practical application: Evaluating the effectiveness of different security measures for a specific asset.
- Financial Due Diligence and Fraud Prevention: Understanding how to perform thorough due diligence on assets and implementing strategies to prevent fraud and theft. Practical application: Developing a due diligence checklist for acquiring a high-value asset.
- Crisis Management and Disaster Recovery: Developing plans and strategies for responding to and recovering from various crises that could impact high-value assets. Practical application: Creating a crisis management plan for a specific scenario (e.g., natural disaster, theft).
- Wealth Preservation Strategies: Exploring various legal and financial strategies for preserving and transferring wealth across generations while minimizing tax liabilities and protecting assets from creditors. Practical application: Comparing different trust structures and their suitability for high net worth individuals.
Next Steps
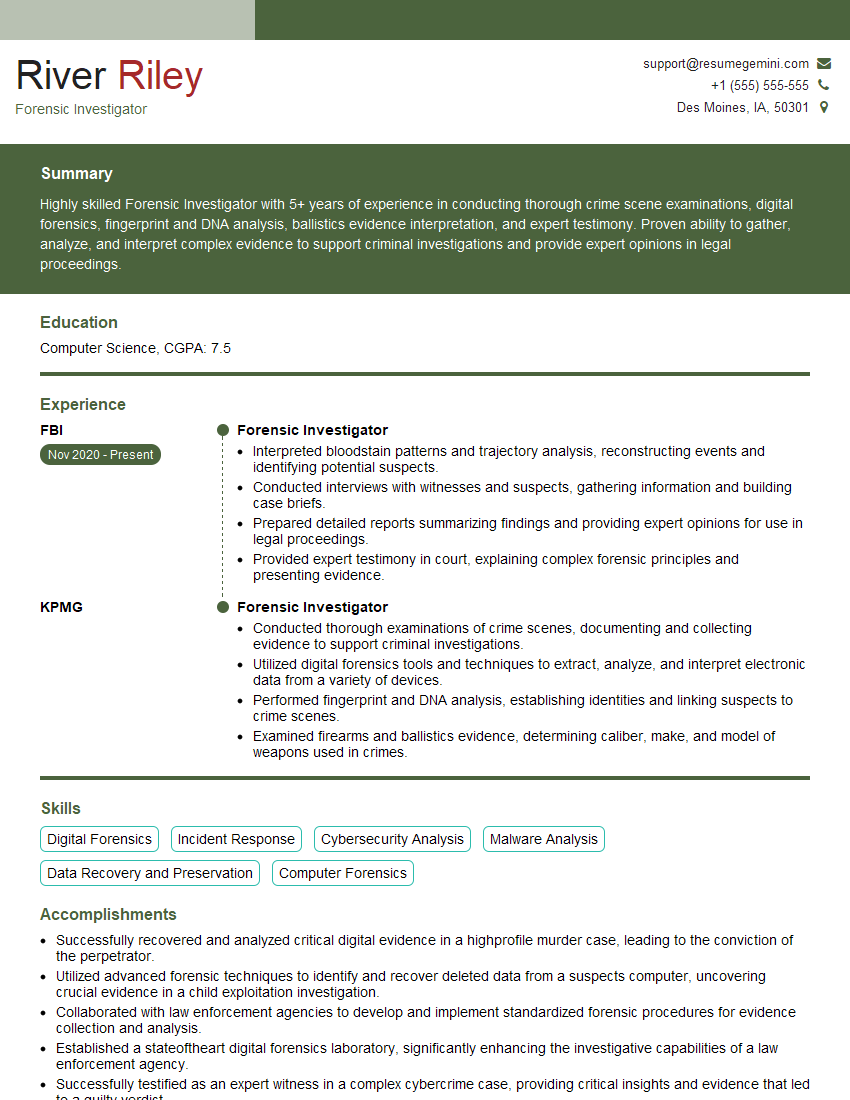
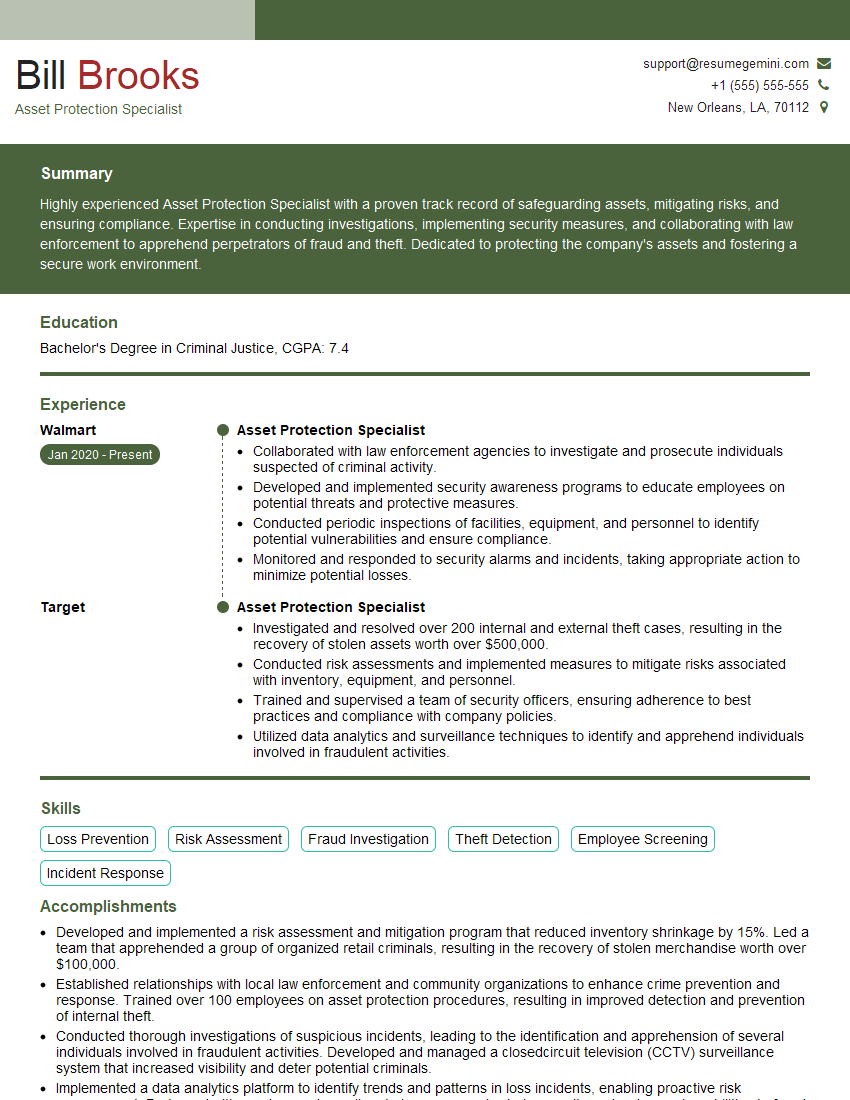
Mastering High Value Asset Protection opens doors to exciting and rewarding career opportunities in a specialized and high-demand field. To maximize your job prospects, crafting a compelling and ATS-friendly resume is crucial. ResumeGemini is a trusted resource that can significantly enhance your resume-building experience. By utilizing ResumeGemini, you can create a professional document that showcases your skills and experience effectively. Examples of resumes tailored to High Value Asset Protection are available to help you get started.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Attention music lovers!
Wow, All the best Sax Summer music !!!
Spotify: https://open.spotify.com/artist/6ShcdIT7rPVVaFEpgZQbUk
Apple Music: https://music.apple.com/fr/artist/jimmy-sax-black/1530501936
YouTube: https://music.youtube.com/browse/VLOLAK5uy_noClmC7abM6YpZsnySxRqt3LoalPf88No
Other Platforms and Free Downloads : https://fanlink.tv/jimmysaxblack
on google : https://www.google.com/search?q=22+AND+22+AND+22
on ChatGPT : https://chat.openai.com?q=who20jlJimmy20Black20Sax20Producer
Get back into the groove with Jimmy sax Black
Best regards,
Jimmy sax Black
www.jimmysaxblack.com
Hi I am a troller at The aquatic interview center and I suddenly went so fast in Roblox and it was gone when I reset.
Hi,
Business owners spend hours every week worrying about their website—or avoiding it because it feels overwhelming.
We’d like to take that off your plate:
$69/month. Everything handled.
Our team will:
Design a custom website—or completely overhaul your current one
Take care of hosting as an option
Handle edits and improvements—up to 60 minutes of work included every month
No setup fees, no annual commitments. Just a site that makes a strong first impression.
Find out if it’s right for you:
https://websolutionsgenius.com/awardwinningwebsites
Hello,
we currently offer a complimentary backlink and URL indexing test for search engine optimization professionals.
You can get complimentary indexing credits to test how link discovery works in practice.
No credit card is required and there is no recurring fee.
You can find details here:
https://wikipedia-backlinks.com/indexing/
Regards
NICE RESPONSE TO Q & A
hi
The aim of this message is regarding an unclaimed deposit of a deceased nationale that bears the same name as you. You are not relate to him as there are millions of people answering the names across around the world. But i will use my position to influence the release of the deposit to you for our mutual benefit.
Respond for full details and how to claim the deposit. This is 100% risk free. Send hello to my email id: lukachachibaialuka@gmail.com
Luka Chachibaialuka
Hey interviewgemini.com, just wanted to follow up on my last email.
We just launched Call the Monster, an parenting app that lets you summon friendly ‘monsters’ kids actually listen to.
We’re also running a giveaway for everyone who downloads the app. Since it’s brand new, there aren’t many users yet, which means you’ve got a much better chance of winning some great prizes.
You can check it out here: https://bit.ly/callamonsterapp
Or follow us on Instagram: https://www.instagram.com/callamonsterapp
Thanks,
Ryan
CEO – Call the Monster App
Hey interviewgemini.com, I saw your website and love your approach.
I just want this to look like spam email, but want to share something important to you. We just launched Call the Monster, a parenting app that lets you summon friendly ‘monsters’ kids actually listen to.
Parents are loving it for calming chaos before bedtime. Thought you might want to try it: https://bit.ly/callamonsterapp or just follow our fun monster lore on Instagram: https://www.instagram.com/callamonsterapp
Thanks,
Ryan
CEO – Call A Monster APP
To the interviewgemini.com Owner.
Dear interviewgemini.com Webmaster!
Hi interviewgemini.com Webmaster!
Dear interviewgemini.com Webmaster!
excellent
Hello,
We found issues with your domain’s email setup that may be sending your messages to spam or blocking them completely. InboxShield Mini shows you how to fix it in minutes — no tech skills required.
Scan your domain now for details: https://inboxshield-mini.com/
— Adam @ InboxShield Mini
support@inboxshield-mini.com
Reply STOP to unsubscribe
Hi, are you owner of interviewgemini.com? What if I told you I could help you find extra time in your schedule, reconnect with leads you didn’t even realize you missed, and bring in more “I want to work with you” conversations, without increasing your ad spend or hiring a full-time employee?
All with a flexible, budget-friendly service that could easily pay for itself. Sounds good?
Would it be nice to jump on a quick 10-minute call so I can show you exactly how we make this work?
Best,
Hapei
Marketing Director
Hey, I know you’re the owner of interviewgemini.com. I’ll be quick.
Fundraising for your business is tough and time-consuming. We make it easier by guaranteeing two private investor meetings each month, for six months. No demos, no pitch events – just direct introductions to active investors matched to your startup.
If youR17;re raising, this could help you build real momentum. Want me to send more info?
Hi, I represent an SEO company that specialises in getting you AI citations and higher rankings on Google. I’d like to offer you a 100% free SEO audit for your website. Would you be interested?
Hi, I represent an SEO company that specialises in getting you AI citations and higher rankings on Google. I’d like to offer you a 100% free SEO audit for your website. Would you be interested?