Feeling uncertain about what to expect in your upcoming interview? We’ve got you covered! This blog highlights the most important Knowledge of Safety and Security Procedures interview questions and provides actionable advice to help you stand out as the ideal candidate. Let’s pave the way for your success.
Questions Asked in Knowledge of Safety and Security Procedures Interview
Q 1. Describe your experience with developing and implementing safety protocols.
Developing and implementing safety protocols requires a systematic approach, starting with a thorough hazard identification process. This involves identifying potential hazards through workplace inspections, job hazard analyses, and employee feedback. For example, in a manufacturing plant, we’d analyze machinery operation, material handling, and chemical usage to pinpoint risks like machinery malfunction, slips, trips, and falls, or chemical exposure.
Once hazards are identified, we prioritize them based on their severity and likelihood of occurrence, using a risk matrix. This allows us to focus resources on the most critical risks first. After prioritization, we develop control measures – engineering controls (e.g., machine guarding), administrative controls (e.g., training programs, safe work procedures), and personal protective equipment (PPE) – to mitigate these risks.
Finally, we implement the protocols through training, communication, and regular monitoring. We use various methods such as safety meetings, toolbox talks, and practical demonstrations to ensure employees understand and follow the protocols. Regular audits and inspections are crucial to ensure ongoing compliance and identify any needed improvements. In one project, I implemented a new lockout/tagout procedure in a chemical processing plant, reducing near-miss incidents by 40% within six months.
Q 2. Explain your understanding of OSHA regulations.
My understanding of OSHA regulations is comprehensive. OSHA (Occupational Safety and Health Administration) sets and enforces standards to ensure safe and healthful working conditions. These standards cover a vast array of topics, including hazard communication, personal protective equipment (PPE), machine guarding, fall protection, confined space entry, and emergency action plans.
I’m familiar with the General Duty Clause, which mandates employers to provide a workplace free from recognized hazards, even if there isn’t a specific OSHA standard addressing that hazard. I also understand the importance of recordkeeping, incident reporting, and employee training requirements stipulated by OSHA. For instance, I have experience ensuring compliance with OSHA’s Hazard Communication Standard, which requires the proper labeling, safety data sheets (SDS), and employee training on hazardous chemicals. Regularly reviewing and updating our safety programs ensures ongoing compliance with all relevant OSHA regulations.
Q 3. How would you conduct a risk assessment for a new facility?
Conducting a risk assessment for a new facility is a crucial step to proactively address potential safety and security hazards. It begins with a thorough walkthrough of the facility, including all areas, equipment, and processes. We’d then identify potential hazards, considering factors like building design, machinery, chemicals, employee activities, and external threats. This might involve analyzing blueprints, interviewing stakeholders, and researching industry best practices.
Next, we evaluate the likelihood and severity of each hazard. This is often done using a risk matrix, a tool that assigns a risk level (low, medium, high) based on the combination of likelihood and severity. For example, a high-likelihood, high-severity hazard would require immediate attention. Once the risks are assessed, we develop control measures to mitigate identified hazards, ranging from engineering controls like installing safety guards on machinery to administrative controls such as implementing strict safety procedures and training programs. Finally, we document all findings and create a comprehensive risk assessment report that informs the development and implementation of safety and security protocols for the facility.
Q 4. What are the key elements of a comprehensive security plan?
A comprehensive security plan is multifaceted and should incorporate several key elements. First, a thorough risk assessment is critical to identify vulnerabilities and potential threats. This assessment should include internal and external threats, natural disasters, and potential security breaches. Understanding these threats is the foundation for creating effective security measures.
Next, physical security measures are vital, encompassing things like access control systems (keycard access, security cameras), perimeter security (fences, gates, lighting), and alarm systems. Cybersecurity is also paramount, requiring robust systems to protect against cyberattacks, data breaches, and unauthorized access to sensitive information. This involves measures like firewalls, intrusion detection systems, and regular security audits.
Furthermore, a comprehensive plan includes emergency response procedures, detailing steps to take in case of a security breach or other emergency. Regular training and drills for employees are essential to ensure everyone knows their roles and responsibilities. Finally, ongoing monitoring and evaluation of the security plan is crucial, allowing for adjustments based on evolving threats and vulnerabilities. This cyclical process of assessment, implementation, and evaluation ensures a continuously improving security posture.
Q 5. Describe your experience with incident response and investigation.
I have extensive experience with incident response and investigation. My approach involves a systematic process starting with immediate actions to secure the scene, ensuring the safety of personnel, and containing the incident to prevent further damage or harm. This might involve isolating a compromised system, evacuating personnel, or contacting emergency services.
Once the immediate threat is addressed, a thorough investigation begins, gathering evidence, interviewing witnesses, and reviewing security logs and data. This is crucial for understanding the root cause of the incident. The investigation should be impartial, factual, and well-documented. In one instance, I investigated a data breach, tracing the source to a phishing attack. The investigation’s findings led to improved employee security awareness training and the implementation of enhanced security protocols to prevent future occurrences.
Following the investigation, a detailed report is compiled, outlining findings, recommendations for corrective action, and preventive measures. This report informs the implementation of changes to prevent similar incidents. This entire process underscores the importance of clear communication, collaboration, and a focus on continuous improvement.
Q 6. How would you handle a security breach?
Handling a security breach requires swift and decisive action. My first step would be to contain the breach to prevent further damage or compromise. This involves isolating affected systems, preventing unauthorized access, and notifying relevant personnel. Simultaneously, I would initiate an incident response plan, following established procedures. This typically involves a team with defined roles and responsibilities.
Next, I’d begin a thorough investigation to determine the nature and extent of the breach, identify the source, and assess any damage. This might involve working with external cybersecurity experts, depending on the complexity of the situation. After the investigation, I would focus on remediation, restoring affected systems, patching vulnerabilities, and implementing preventative measures to mitigate future risks. Finally, I’d conduct a post-incident review to identify lessons learned and improve our security posture. Transparency with stakeholders, including affected individuals and regulatory bodies, is vital throughout the entire process.
Q 7. How familiar are you with various security technologies (e.g., CCTV, access control)?
I’m very familiar with a range of security technologies, including CCTV (Closed-Circuit Television) systems, access control systems, intrusion detection systems, and network security tools. I understand the capabilities and limitations of each technology and can assess their suitability for different applications.
For example, I’ve designed and implemented CCTV systems that integrate with video analytics for enhanced threat detection and response. In other projects, I’ve worked with access control systems to manage personnel access to restricted areas, using various authentication methods such as keycards, biometric scanners, and PIN codes. I also have experience in the deployment and management of intrusion detection systems, ensuring they’re properly configured and integrated with other security systems to provide a comprehensive security solution. Choosing the appropriate technologies and integrating them effectively requires a thorough understanding of the facility’s specific security needs and risks.
Q 8. What are your strategies for employee safety training?
My employee safety training strategies are built on a multi-faceted approach focusing on engagement, relevance, and reinforcement. I believe in moving beyond simple compliance training to foster a genuine safety culture.
Needs Assessment: I begin by identifying specific hazards and risks within the workplace. This involves analyzing job tasks, accident history, and regulatory requirements to tailor training to actual needs.
Modular Training: Instead of one large session, I prefer modular training, delivering information in bite-sized chunks. This improves comprehension and retention. For example, training on forklift operation might be broken into classroom theory, simulator practice, and hands-on supervised practice.
Interactive Methods: Passive lectures are ineffective. I incorporate interactive elements like simulations, case studies, and group discussions. For example, a scenario-based training on fire safety can effectively demonstrate proper evacuation procedures.
Regular Refresher Training: Safety regulations change, and employee knowledge can fade. I schedule regular refresher courses and incorporate new information seamlessly. This ensures continuous improvement and up-to-date knowledge.
Feedback and Evaluation: Post-training assessments and feedback mechanisms are essential. This allows me to identify areas needing improvement and track the effectiveness of the training programs. This data helps refine future training strategies.
Q 9. How do you ensure compliance with relevant safety and security standards?
Ensuring compliance with safety and security standards requires a proactive and systematic approach. It’s not enough to simply have policies; consistent monitoring and enforcement are crucial.
Regular Audits: I conduct regular safety audits to identify any deviations from established standards. These audits are based on checklists, visual inspections, and employee interviews.
Documentation and Record Keeping: Meticulous record-keeping is essential. This includes maintaining training records, audit reports, incident reports, and corrective action plans. This documentation provides evidence of compliance during inspections.
Staying Updated: Safety regulations are constantly evolving. I stay informed about changes through professional organizations, industry publications, and government websites. I integrate these updates into training materials and company policies.
Addressing Non-Compliance: When non-compliance is identified, I implement corrective action plans immediately. This includes addressing the root cause of the issue, implementing preventative measures, and retraining employees if necessary. For example, if a safety audit reveals improper use of machinery, I implement retraining and stricter enforcement of safety protocols.
Collaboration: Working collaboratively with regulatory bodies and safety professionals ensures that our practices align with best practices and legal requirements.
Q 10. Explain your experience in emergency preparedness and response.
My experience in emergency preparedness and response focuses on developing robust plans and ensuring efficient execution. I believe in a proactive, rather than reactive, approach.
Risk Assessment: I conduct thorough risk assessments to identify potential emergencies, such as fires, natural disasters, or security breaches.
Emergency Response Plan Development: Based on the risk assessment, I develop comprehensive emergency response plans that detail procedures for evacuation, communication, first aid, and post-emergency recovery. These plans include designated roles, emergency contact information, and assembly points.
Emergency Drills and Training: Regular drills and simulations are vital to ensure employees are familiar with emergency procedures. I conduct drills that are realistic and simulate different scenarios, allowing for feedback and improvement.
Communication Systems: Effective communication is critical. I ensure that we have reliable communication systems in place, including emergency alerts, public address systems, and backup communication methods.
Post-Incident Review: After an emergency, I conduct a thorough review to identify areas for improvement and update the emergency response plan accordingly. This iterative process ensures continuous enhancement of preparedness.
For example, during a recent fire drill, I observed that communication to a specific area was delayed. We subsequently implemented a secondary communication system for that area to address this weakness.
Q 11. Describe your proficiency in conducting safety audits.
Conducting safety audits requires a structured and systematic approach, combining technical expertise with observational skills.
Planning and Preparation: Before the audit, I carefully plan the scope, objectives, and methodology. This involves reviewing existing safety documentation, identifying key areas for inspection, and developing a checklist.
On-site Inspection: During the audit, I conduct a thorough inspection of the workplace, paying close attention to potential hazards, compliance with regulations, and employee practices. I use checklists and take detailed notes and photographs.
Data Analysis and Reporting: After the inspection, I analyze the collected data to identify trends, patterns, and areas needing improvement. I prepare a comprehensive report that includes findings, recommendations, and corrective actions.
Follow-up: I follow up on the implementation of corrective actions and verify that the identified issues have been resolved. This may involve further inspections or interviews with staff.
Use of Technology: I utilize technology such as safety management software to track audit findings, generate reports, and manage corrective actions efficiently. This improves accuracy and streamlines the auditing process.
Q 12. How do you manage and mitigate workplace hazards?
Managing and mitigating workplace hazards is a continuous process that requires a proactive approach.
Hazard Identification: I use various methods to identify hazards, including risk assessments, job safety analyses, incident investigations, and employee feedback. For example, using a checklist during a routine inspection may reveal inadequate lighting near a staircase.
Hazard Control: Once hazards are identified, I prioritize control measures based on the hierarchy of controls: elimination, substitution, engineering controls, administrative controls, and personal protective equipment (PPE). Eliminating the hazard is always the best solution, but often, this is not feasible, therefore other controls are implemented.
Implementation and Monitoring: Once control measures are implemented, I monitor their effectiveness through regular inspections, employee feedback, and data analysis. This allows for adjustments and improvements as needed.
Employee Involvement: Actively involving employees in the hazard identification and control process fosters a safety culture and improves the effectiveness of hazard management.
Documentation: Maintaining records of hazard identification, control measures, and monitoring results is crucial for compliance and continuous improvement.
Q 13. How do you prioritize risks based on likelihood and impact?
Prioritizing risks involves a structured approach that considers both the likelihood and impact of potential incidents. A common method is using a risk matrix.
Risk Assessment Matrix: I use a risk matrix that plots likelihood (e.g., low, medium, high) against impact (e.g., minor, moderate, major, catastrophic). This produces a visual representation of the relative risk of different hazards.
Quantitative and Qualitative Data: The matrix incorporates both quantitative data (e.g., accident statistics) and qualitative factors (e.g., expert opinions). For instance, a low-likelihood, high-impact risk like a major equipment failure might require preventative maintenance and backup systems.
Prioritization: Risks are prioritized based on their position within the risk matrix. High-likelihood, high-impact risks receive immediate attention and resources. Medium risks are addressed proactively, while low risks might require monitoring.
Regular Review: Risks and their prioritization are regularly reviewed and updated as conditions change or new information becomes available. This dynamic approach ensures that mitigation efforts remain relevant.
Q 14. What are your methods for communicating safety and security information?
Effective communication of safety and security information is paramount. A multi-channel strategy is most effective.
Formal Training: Training sessions provide in-depth information and allow for interactive learning and clarification.
Regular Meetings: Team meetings and safety committee meetings provide platforms for discussing safety concerns, sharing best practices, and addressing incidents.
Visual Aids: Signage, posters, and safety alerts placed strategically throughout the workplace serve as visual reminders.
Digital Communication: Email, intranet, and mobile apps enable efficient communication of safety updates, alerts, and training materials.
Feedback Mechanisms: Providing channels for employee feedback, such as suggestion boxes and reporting systems, allows for proactive identification of hazards and concerns. For instance, I’ve used an anonymous reporting system to receive valuable information on potential safety issues without fear of retribution.
Q 15. How do you handle conflicts concerning safety procedures?
Handling conflicts regarding safety procedures requires a calm, structured approach prioritizing safety. I begin by actively listening to all parties involved, ensuring everyone feels heard and understood. This helps identify the root of the disagreement – is it a misunderstanding of the procedure, a concern about feasibility, or something else?
Once the issue is clear, I’ll collaboratively explore solutions. This might involve reviewing the procedure itself to identify any ambiguities or areas for improvement, demonstrating the rationale behind the procedure, or finding alternative approaches that address concerns while maintaining safety standards. Documentation is crucial; I meticulously record all discussions, agreed-upon solutions, and any subsequent actions. For persistent or serious conflicts, involving a supervisor or relevant authority is essential to ensure a fair and effective resolution.
For example, if a team disagrees on the use of specific personal protective equipment (PPE), I would gather all perspectives, review the relevant safety regulations and risk assessments, and perhaps conduct a practical demonstration of the correct PPE usage and its benefits. The goal isn’t to win the argument, but to find the safest and most practical solution for everyone involved.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. Describe your experience with implementing security awareness training.
In my previous role at Acme Corp, I developed and implemented a comprehensive security awareness training program. This involved a multi-faceted approach, combining online modules with interactive workshops and regular communication campaigns. The online modules covered topics such as phishing awareness, password security, data handling, and physical security protocols. The workshops allowed for hands-on exercises and Q&A sessions, fostering a more engaging learning environment. We also used regular email newsletters, posters, and short video clips to reinforce key concepts and keep security top-of-mind.
The training was tailored to different roles and levels within the organization, acknowledging the varying levels of security responsibilities. We measured effectiveness through pre- and post-training assessments, phishing simulations, and ongoing feedback mechanisms. Based on these evaluations, we iteratively refined the program, ensuring its relevance and impact. The program led to a significant reduction in phishing incidents and improved overall security posture. A key success factor was focusing on engaging content and demonstrating the practical relevance of security measures to employees’ daily work.
Q 17. How familiar are you with different types of security threats (e.g., physical, cyber)?
My familiarity with security threats spans a wide range, encompassing physical, cyber, and even social engineering threats. Physical threats include unauthorized access to facilities, theft of equipment or data, and acts of vandalism or sabotage. I’m proficient in assessing physical security vulnerabilities, such as inadequate surveillance, weak access control, or unsecured perimeters. I’ve worked with various physical security systems, from CCTV and access control systems to alarm systems and security personnel.
Cyber threats encompass a broader landscape, including malware attacks, phishing scams, denial-of-service attacks, and data breaches. I understand the importance of network security, data encryption, and incident response planning. I’m familiar with various security protocols and best practices for mitigating cyber risks. Social engineering threats, like manipulation or deception to gain access to information or systems, are equally important. These are often the weakest link in security chains, requiring training and awareness programs to address.
Understanding these diverse threat vectors is critical for developing a comprehensive and effective security strategy. Each threat requires a tailored response and preventative measures.
Q 18. What are your experience with security system monitoring and maintenance?
My experience with security system monitoring and maintenance involves both proactive and reactive measures. Proactive maintenance includes regular system checks, software updates, and testing of various functionalities. This ensures optimal performance and prevents potential failures. I am proficient in using various monitoring tools to track system health, identify anomalies, and generate reports. For example, I have experience using intrusion detection systems (IDS) and security information and event management (SIEM) tools to monitor network traffic and identify potential threats in real-time.
Reactive maintenance involves responding to alarms, investigating incidents, and troubleshooting system failures. I follow established procedures for addressing security breaches and system malfunctions, which include documenting the incident, taking corrective action, and reporting to relevant stakeholders. I’ve handled situations ranging from minor equipment malfunctions to major security breaches, always prioritizing the restoration of security and minimizing disruption.
Q 19. Explain your understanding of data security best practices.
Data security best practices revolve around the CIA triad: Confidentiality, Integrity, and Availability. Confidentiality ensures that only authorized individuals can access sensitive data. This involves access control measures like user authentication, authorization, and encryption. Integrity maintains the accuracy and completeness of data, protecting it from unauthorized modification or deletion. This requires data validation, version control, and regular backups.
Availability ensures that authorized users have timely and reliable access to data when needed. This is achieved through redundancy, failover mechanisms, and disaster recovery planning. Beyond the CIA triad, other crucial practices include regular security audits, vulnerability assessments, and incident response planning. Data loss prevention (DLP) tools can help prevent sensitive data from leaving the organization’s control. Employee training on data security best practices is also paramount.
Consider the example of a healthcare organization handling patient medical records. Strict access controls, encryption both in transit and at rest, and robust auditing mechanisms are critical for maintaining confidentiality. Data validation ensures accurate record-keeping, and regular backups guarantee data availability in case of system failures.
Q 20. How do you ensure the confidentiality, integrity, and availability of sensitive data?
Ensuring the confidentiality, integrity, and availability (CIA triad) of sensitive data requires a multi-layered approach. Confidentiality is maintained through access controls (limiting who can access data based on roles and permissions), encryption (transforming data into an unreadable format), and secure data storage (using encrypted databases and secure cloud services).
Integrity is protected through data validation (checking for accuracy and completeness), version control (tracking changes to data), and hashing (creating unique digital fingerprints of data to detect tampering). Availability is ensured via redundant systems (having backup systems in place), disaster recovery planning (having a plan to restore data and systems after an outage), and regular backups (creating copies of data for recovery).
For instance, a financial institution protecting customer financial data would use strong encryption, multi-factor authentication, regular security audits, and robust disaster recovery procedures. These measures would work together to guarantee confidentiality, integrity, and availability of sensitive financial information.
Q 21. How would you investigate a workplace accident to determine root cause?
Investigating a workplace accident to determine its root cause requires a systematic approach, often following a structured methodology like the “5 Whys” technique or a more formal root cause analysis (RCA) process. I would start by securing the accident scene, ensuring the safety of everyone involved, and documenting the immediate circumstances. This includes taking photographs, collecting witness statements, and reviewing any available security footage.
Next, I’d gather all relevant information, including the employee’s training records, equipment maintenance logs, and relevant safety policies. The “5 Whys” technique involves repeatedly asking “why” to uncover the underlying causes. For example, if a worker fell from a ladder, I might ask: Why did the worker fall? (The ladder was unstable). Why was the ladder unstable? (It wasn’t properly secured). Why wasn’t it secured? (The worker wasn’t properly trained). Why wasn’t the worker properly trained? (There was a gap in the training program). Why was there a gap in the training program? (Insufficient resources allocated to training).
A more formal RCA might use techniques like fault tree analysis or fishbone diagrams to visually map out contributing factors. The goal is to move beyond immediate causes to identify underlying systemic issues. Finally, I’d develop corrective actions to prevent similar accidents in the future, which might include revising safety procedures, providing additional training, or improving equipment maintenance.
Q 22. Describe your experience with creating and maintaining safety documentation.
Creating and maintaining safety documentation is crucial for ensuring a safe and compliant workplace. My experience involves developing comprehensive safety manuals, standard operating procedures (SOPs), risk assessments, and emergency response plans. I utilize a structured approach, starting with a thorough needs analysis to identify potential hazards and risks specific to the environment. This involves consultations with various stakeholders, including employees, management, and external safety consultants.
For example, in my previous role at a manufacturing facility, I developed a detailed safety manual that included sections on machine guarding, lockout/tagout procedures, personal protective equipment (PPE) usage, and emergency evacuation protocols. This manual was regularly updated and reviewed, incorporating lessons learned from incident investigations and changes in regulations. I also developed training programs to ensure employees understood and adhered to the procedures documented in the manual. Furthermore, I employed a document management system to ensure version control and easy access to the most up-to-date information for all personnel. This system includes a revision history and a clear approval process for updates, ensuring that everyone is working with the latest version.
Q 23. How would you manage a crisis situation involving a security incident?
Managing a security incident requires a calm, decisive, and systematic approach. My response would follow a well-defined crisis management protocol, prioritizing the safety and security of personnel and assets. The first step involves immediate assessment of the situation, determining the nature and extent of the incident. This includes identifying casualties, assessing damage, and securing the scene to prevent further incidents or evidence compromise.
Next, I would activate the emergency response plan, contacting emergency services (police, fire department, medical) as needed and initiating communication protocols to inform relevant stakeholders, including employees, clients, and potentially the media. Throughout the process, detailed documentation is critical, recording all actions taken, timelines, and communications. After the immediate crisis is contained, a thorough investigation would be conducted to identify root causes and implement corrective actions to prevent recurrence. For example, if a data breach occurs, I’d immediately isolate affected systems, initiate forensic analysis to identify the extent of the breach, and notify affected parties in accordance with relevant regulations like GDPR.
Q 24. What are your strategies for preventing workplace violence?
Preventing workplace violence is a multifaceted issue requiring a proactive and comprehensive strategy. My approach focuses on creating a culture of respect and zero tolerance for violence, combined with robust security measures. This involves implementing a comprehensive workplace violence prevention program that includes training for all employees on recognizing and responding to warning signs, de-escalation techniques, and reporting procedures.
Strategies include establishing clear policies prohibiting harassment and violence, creating a confidential reporting system, providing employees with resources and support, and regularly reviewing security measures such as access control, surveillance systems, and emergency response plans. Regular safety audits and employee feedback sessions are essential to identify potential risks and address them promptly. For instance, I might introduce a buddy system for employees working late hours, improve lighting in parking lots, and implement mandatory anger management training for employees with a history of conflict. This proactive approach fosters a positive work environment where everyone feels safe and respected.
Q 25. How familiar are you with building codes and fire safety regulations?
I am very familiar with building codes and fire safety regulations, including the International Building Code (IBC) and the National Fire Protection Association (NFPA) standards. My knowledge encompasses aspects like fire detection and suppression systems, emergency exits, occupancy limits, accessibility requirements, and means of egress.
I understand the importance of regular inspections to ensure compliance and identify potential hazards. I have experience reviewing blueprints to ensure compliance with relevant codes during the design phase of construction projects, as well as conducting post-construction inspections to verify adherence to the approved plans. Further, my understanding extends to the application of these codes across different building types, considering factors like occupancy classifications and the specific hazards associated with different industries. For example, I know the specific fire suppression requirements for a high-rise building versus a warehouse.
Q 26. Describe your experience with working with regulatory bodies and conducting inspections.
I have extensive experience working with regulatory bodies, including OSHA (Occupational Safety and Health Administration) and local fire marshals. This includes conducting self-inspections, preparing documentation for audits, and collaborating with inspectors to address any identified deficiencies. I am adept at understanding and interpreting regulatory requirements, ensuring compliance through proactive measures and corrective actions.
For instance, in a previous role, I collaborated with OSHA inspectors during a routine inspection, providing them with all necessary documentation and addressing their concerns promptly. This proactive approach resulted in a successful inspection without any citations. I also have experience developing and delivering training programs for employees on regulatory compliance, including specific training modules on hazard communication, lockout/tagout procedures, and emergency response planning. A key aspect of my work is maintaining detailed records of all inspections, findings, and corrective actions.
Q 27. How do you adapt safety and security procedures to different environments and situations?
Adapting safety and security procedures to different environments and situations requires a flexible and adaptable approach. It begins with a thorough risk assessment specific to the environment, considering factors such as the nature of the work, the physical layout, and the potential hazards present.
For example, the safety procedures for a construction site will differ significantly from those of an office environment. A construction site necessitates stringent protocols regarding fall protection, heavy machinery operation, and site-specific hazards like trenches and excavations. Conversely, an office environment might prioritize security measures such as access control, cybersecurity, and emergency evacuation plans tailored to the building’s layout. I always tailor safety and security plans to address specific risks, ensuring that they are practical, effective, and relevant to the unique needs of the location and the tasks performed.
Q 28. What are your long-term career goals in safety and security?
My long-term career goals in safety and security involve progressing to a leadership role where I can leverage my expertise to implement comprehensive safety programs across large organizations. I aspire to become a recognized leader in the field, contributing to the development and improvement of safety standards and best practices.
I am particularly interested in specializing in risk management and developing innovative strategies for proactively identifying and mitigating risks. I envision myself mentoring and training others, fostering a culture of safety and security within organizations, and ultimately making a significant contribution to enhancing workplace safety across various industries. This includes pursuing further certifications and professional development opportunities to remain at the forefront of this ever-evolving field.
Key Topics to Learn for Knowledge of Safety and Security Procedures Interview
- Emergency Response Procedures: Understanding and applying protocols for various emergencies (fire, evacuation, medical emergencies). This includes knowing your role in an emergency team and practicing effective communication under pressure.
- Security Protocols and Access Control: Knowledge of physical security measures (locks, alarms, surveillance), access control systems (keycards, biometric systems), and procedures for handling security breaches or suspicious activity. Be prepared to discuss practical examples of how you’ve implemented or enforced security protocols.
- Risk Assessment and Mitigation: Identifying potential safety and security risks, analyzing their likelihood and impact, and developing strategies to mitigate those risks. Consider how you would approach a risk assessment in a specific workplace scenario.
- Health and Safety Regulations: Familiarity with relevant legislation and industry best practices related to health and safety. Demonstrate understanding of legal compliance and its practical application in the workplace.
- Incident Reporting and Investigation: Understanding the procedures for reporting incidents, conducting thorough investigations, and documenting findings. This includes accurate record-keeping and adherence to reporting timelines.
- Safety Training and Awareness: Experience in conducting or participating in safety training programs, and promoting a safety-conscious culture within a team or organization. Discuss your role in fostering a safe working environment.
- Data Security and Confidentiality: Understanding procedures for protecting sensitive information, both physical and digital, and adhering to data privacy regulations. Discuss practical examples of data security measures you have implemented or followed.
Next Steps
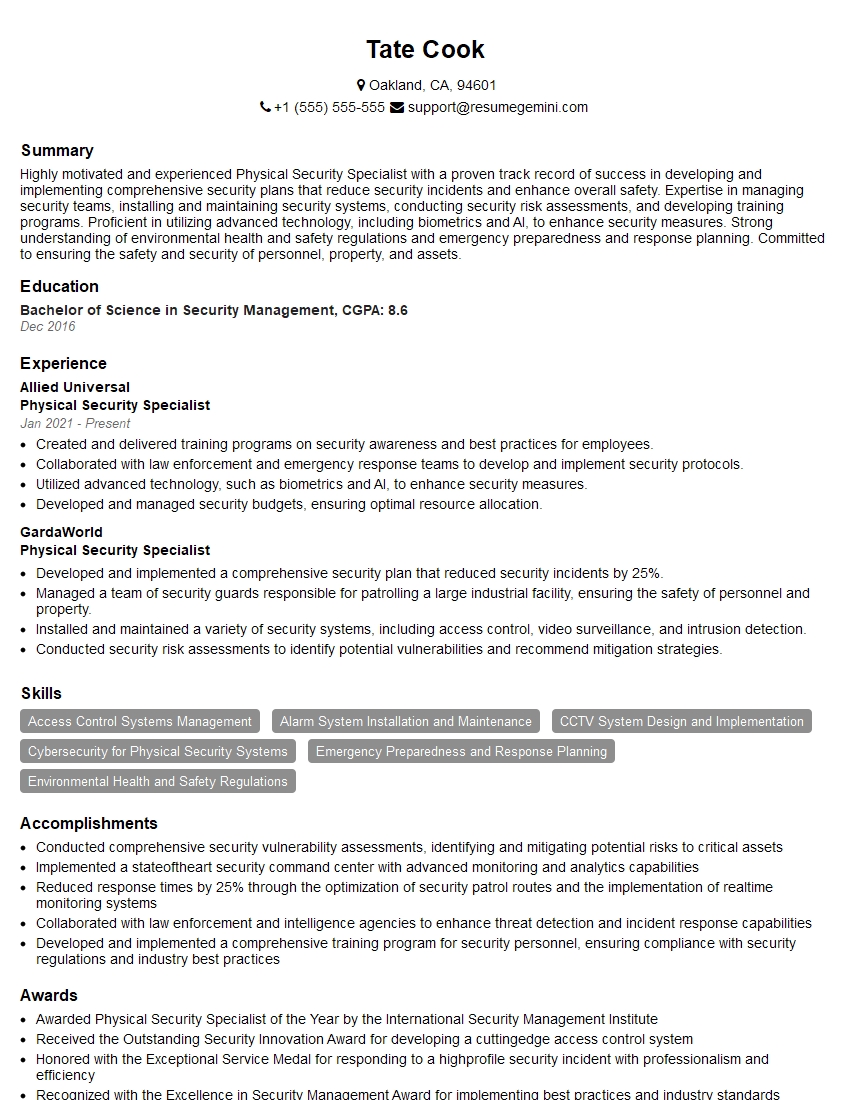
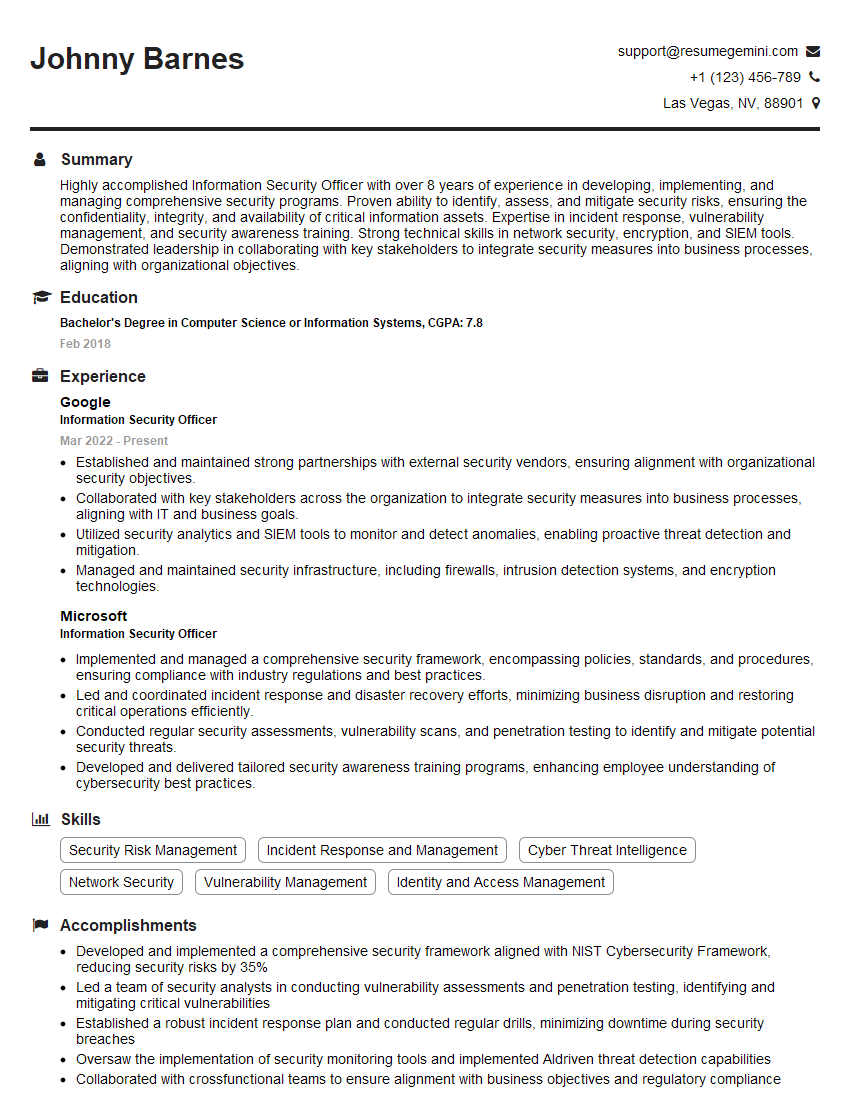
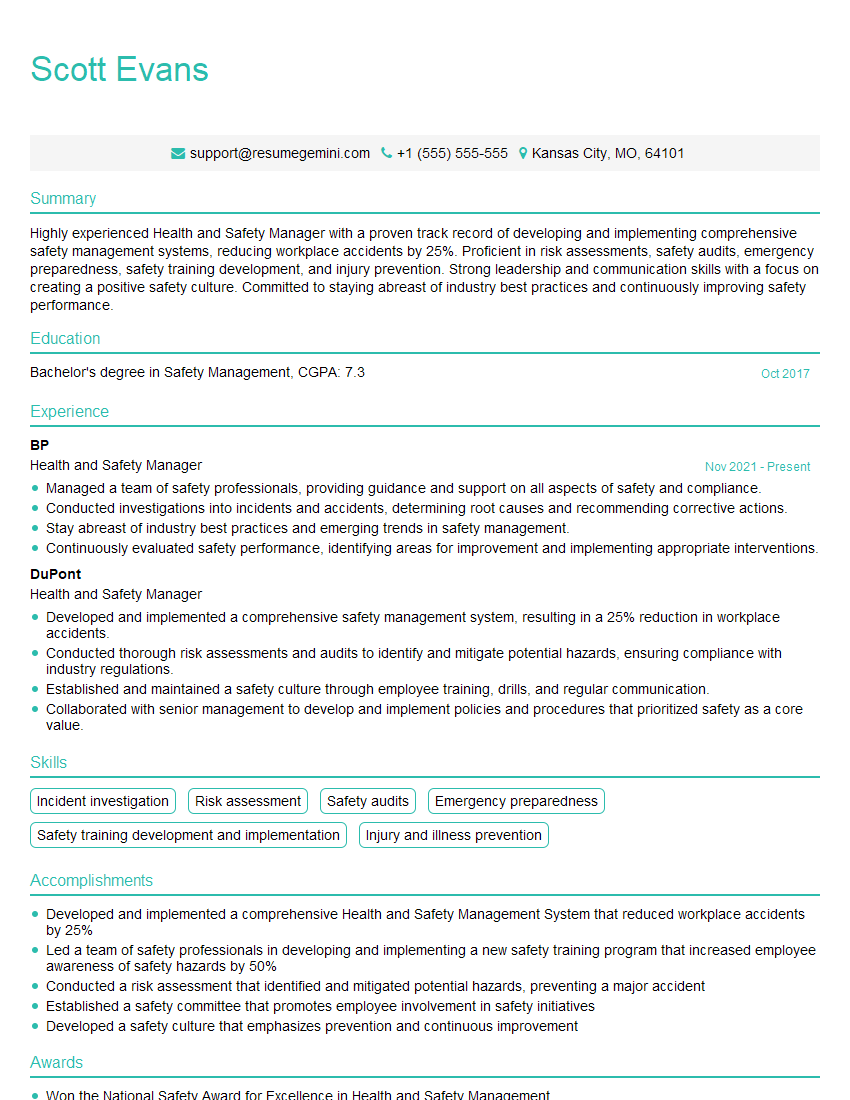
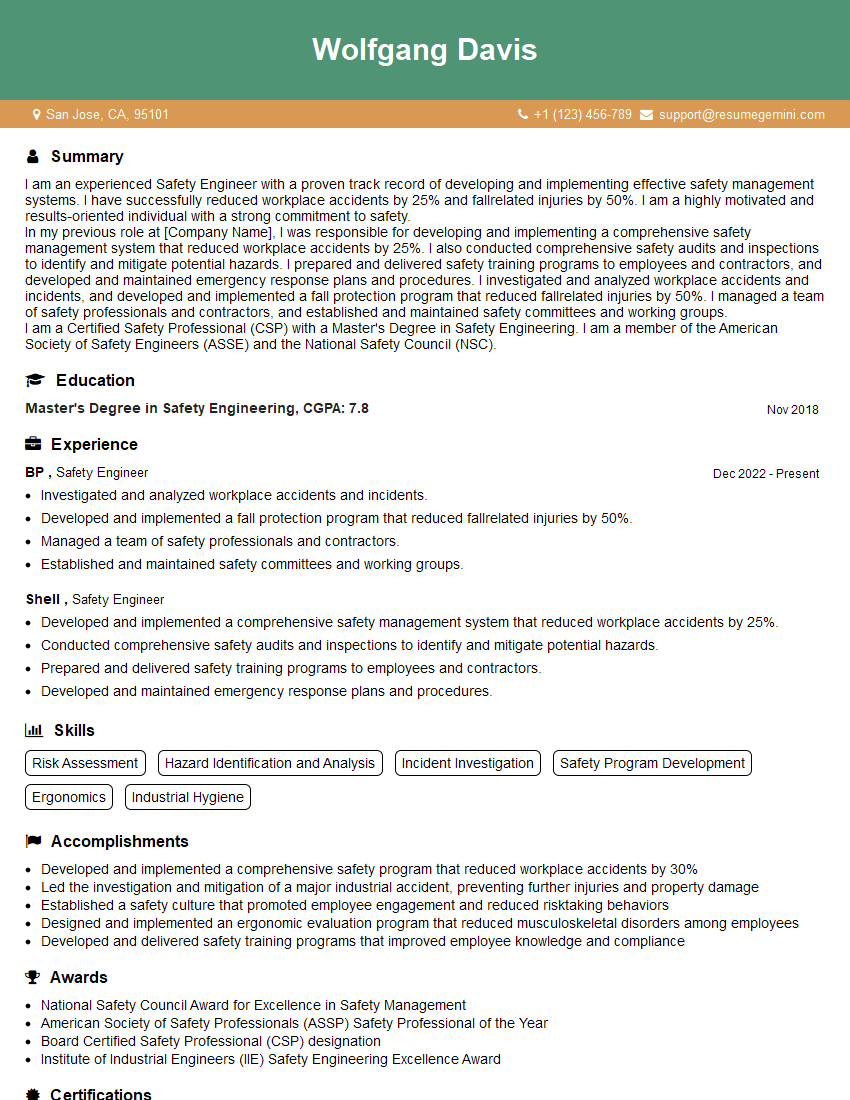
Mastering Knowledge of Safety and Security Procedures is crucial for career advancement in many fields, demonstrating your commitment to a safe and secure working environment. A strong resume is your key to unlocking opportunities. Building an ATS-friendly resume significantly increases your chances of getting noticed by recruiters. We recommend using ResumeGemini, a trusted resource, to build a professional and impactful resume. ResumeGemini provides examples of resumes tailored to Knowledge of Safety and Security Procedures to help you craft a compelling application that showcases your skills and experience effectively.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Attention music lovers!
Wow, All the best Sax Summer music !!!
Spotify: https://open.spotify.com/artist/6ShcdIT7rPVVaFEpgZQbUk
Apple Music: https://music.apple.com/fr/artist/jimmy-sax-black/1530501936
YouTube: https://music.youtube.com/browse/VLOLAK5uy_noClmC7abM6YpZsnySxRqt3LoalPf88No
Other Platforms and Free Downloads : https://fanlink.tv/jimmysaxblack
on google : https://www.google.com/search?q=22+AND+22+AND+22
on ChatGPT : https://chat.openai.com?q=who20jlJimmy20Black20Sax20Producer
Get back into the groove with Jimmy sax Black
Best regards,
Jimmy sax Black
www.jimmysaxblack.com
Hi I am a troller at The aquatic interview center and I suddenly went so fast in Roblox and it was gone when I reset.
Hi,
Business owners spend hours every week worrying about their website—or avoiding it because it feels overwhelming.
We’d like to take that off your plate:
$69/month. Everything handled.
Our team will:
Design a custom website—or completely overhaul your current one
Take care of hosting as an option
Handle edits and improvements—up to 60 minutes of work included every month
No setup fees, no annual commitments. Just a site that makes a strong first impression.
Find out if it’s right for you:
https://websolutionsgenius.com/awardwinningwebsites
Hello,
we currently offer a complimentary backlink and URL indexing test for search engine optimization professionals.
You can get complimentary indexing credits to test how link discovery works in practice.
No credit card is required and there is no recurring fee.
You can find details here:
https://wikipedia-backlinks.com/indexing/
Regards
NICE RESPONSE TO Q & A
hi
The aim of this message is regarding an unclaimed deposit of a deceased nationale that bears the same name as you. You are not relate to him as there are millions of people answering the names across around the world. But i will use my position to influence the release of the deposit to you for our mutual benefit.
Respond for full details and how to claim the deposit. This is 100% risk free. Send hello to my email id: lukachachibaialuka@gmail.com
Luka Chachibaialuka
Hey interviewgemini.com, just wanted to follow up on my last email.
We just launched Call the Monster, an parenting app that lets you summon friendly ‘monsters’ kids actually listen to.
We’re also running a giveaway for everyone who downloads the app. Since it’s brand new, there aren’t many users yet, which means you’ve got a much better chance of winning some great prizes.
You can check it out here: https://bit.ly/callamonsterapp
Or follow us on Instagram: https://www.instagram.com/callamonsterapp
Thanks,
Ryan
CEO – Call the Monster App
Hey interviewgemini.com, I saw your website and love your approach.
I just want this to look like spam email, but want to share something important to you. We just launched Call the Monster, a parenting app that lets you summon friendly ‘monsters’ kids actually listen to.
Parents are loving it for calming chaos before bedtime. Thought you might want to try it: https://bit.ly/callamonsterapp or just follow our fun monster lore on Instagram: https://www.instagram.com/callamonsterapp
Thanks,
Ryan
CEO – Call A Monster APP
To the interviewgemini.com Owner.
Dear interviewgemini.com Webmaster!
Hi interviewgemini.com Webmaster!
Dear interviewgemini.com Webmaster!
excellent
Hello,
We found issues with your domain’s email setup that may be sending your messages to spam or blocking them completely. InboxShield Mini shows you how to fix it in minutes — no tech skills required.
Scan your domain now for details: https://inboxshield-mini.com/
— Adam @ InboxShield Mini
support@inboxshield-mini.com
Reply STOP to unsubscribe
Hi, are you owner of interviewgemini.com? What if I told you I could help you find extra time in your schedule, reconnect with leads you didn’t even realize you missed, and bring in more “I want to work with you” conversations, without increasing your ad spend or hiring a full-time employee?
All with a flexible, budget-friendly service that could easily pay for itself. Sounds good?
Would it be nice to jump on a quick 10-minute call so I can show you exactly how we make this work?
Best,
Hapei
Marketing Director
Hey, I know you’re the owner of interviewgemini.com. I’ll be quick.
Fundraising for your business is tough and time-consuming. We make it easier by guaranteeing two private investor meetings each month, for six months. No demos, no pitch events – just direct introductions to active investors matched to your startup.
If youR17;re raising, this could help you build real momentum. Want me to send more info?
Hi, I represent an SEO company that specialises in getting you AI citations and higher rankings on Google. I’d like to offer you a 100% free SEO audit for your website. Would you be interested?
Hi, I represent an SEO company that specialises in getting you AI citations and higher rankings on Google. I’d like to offer you a 100% free SEO audit for your website. Would you be interested?