Are you ready to stand out in your next interview? Understanding and preparing for MIS Systems interview questions is a game-changer. In this blog, we’ve compiled key questions and expert advice to help you showcase your skills with confidence and precision. Let’s get started on your journey to acing the interview.
Questions Asked in MIS Systems Interview
Q 1. Explain the difference between data, information, and knowledge.
Data, information, and knowledge represent a hierarchy of increasingly refined understanding. Think of it like this: data is the raw material, information is the processed material, and knowledge is the finished product.
Data: Raw, unorganized facts and figures. Examples include a customer’s name, age, and purchase history stored individually in a database. It’s like having a pile of bricks – no inherent meaning on its own.
Information: Data that has been processed, organized, structured, or interpreted in a way that makes it meaningful and useful. For instance, analyzing a customer’s purchase history might reveal that they frequently buy specific product categories; this becomes information. It’s like building a wall with the bricks – the wall has structure and purpose.
Knowledge: Information that has been understood, analyzed, and applied in a way that provides insights or solutions. Recognizing from the customer’s purchasing patterns that they’re likely interested in a particular new product and proactively offering it – that’s knowledge. It’s like building a house from the wall – the finished structure has value and functionality.
Q 2. Describe the different types of MIS systems.
MIS systems are categorized based on their scope and functionality. Here are some key types:
Transaction Processing Systems (TPS): These systems handle routine, day-to-day transactions. Examples include point-of-sale (POS) systems in retail stores or order processing systems. They focus on efficiency and accuracy in handling large volumes of transactions.
Management Information Systems (MIS): These provide reports and summaries of data to support management decision-making. Think of sales reports, inventory levels, or customer demographics – MIS helps managers monitor performance and identify trends.
Decision Support Systems (DSS): These systems assist managers in making complex, non-routine decisions. They often utilize data analysis tools like statistical modeling or what-if scenarios. Imagine a DSS helping a marketing manager predict the success of a new product based on market research.
Executive Information Systems (EIS): These high-level systems provide summarized, strategic information to executives. EIS focuses on long-term planning and overall organizational performance. It’s like a dashboard showing key performance indicators (KPIs) for the entire company.
Expert Systems (ES): These systems utilize artificial intelligence to mimic the decision-making ability of human experts. They’re often used in specialized areas like medical diagnosis or financial analysis.
Q 3. What is a database management system (DBMS) and what are its key functions?
A Database Management System (DBMS) is software that interacts with end users, applications, and the database itself to capture and analyze data. Think of it as the intermediary between you and the data you need. Its key functions include:
Data Definition: Defining the structure of the database, including tables, fields, and data types. It’s like creating a blueprint for your data.
Data Manipulation: Adding, deleting, modifying, and retrieving data. This is the day-to-day interaction with the database.
Data Security: Controlling access to the database to ensure data integrity and confidentiality. Setting up user permissions and encryption are part of this.
Data Integrity: Ensuring data accuracy, consistency, and validity. This involves implementing constraints and validation rules.
Data Backup and Recovery: Protecting the database from data loss through regular backups and disaster recovery plans.
Q 4. Explain the concept of data normalization and its importance.
Data normalization is the process of organizing data to reduce redundancy and improve data integrity. Imagine a spreadsheet with repeated customer information on each order – that’s redundancy. Normalization breaks down the data into smaller, more manageable tables, linked through relationships. This reduces data inconsistencies and makes the database more efficient.
The importance lies in:
Reduced Data Redundancy: Less storage space, easier updates.
Improved Data Integrity: Consistent and accurate data.
Increased Data Flexibility: Easier to add, modify, or delete data.
It usually involves several ‘normal forms,’ with each form addressing a specific type of redundancy. For example, First Normal Form (1NF) eliminates repeating groups of data within a table, Second Normal Form (2NF) removes redundant data that depends on only part of the primary key, and Third Normal Form (3NF) removes data that’s dependent on non-key attributes.
Q 5. What are the different types of database models?
Different database models represent data in different ways. Here are a few:
Relational Model: The most common model, using tables with rows and columns. Relationships between tables are established through keys. Most popular DBMSs (like MySQL, PostgreSQL, Oracle) are relational.
Hierarchical Model: Data is organized in a tree-like structure with a parent-child relationship. This model is less flexible than the relational model.
Network Model: An extension of the hierarchical model allowing multiple parent-child relationships. More complex than hierarchical but offers more flexibility.
Object-Oriented Model: Data is represented as objects with attributes and methods. This model is well-suited for complex applications requiring multimedia data handling.
NoSQL (Not Only SQL): A broader term encompassing various non-relational database models, including document, key-value, graph, and column-family databases. These are often used for large-scale, distributed applications.
Q 6. Describe the role of an ERP system in an organization.
An Enterprise Resource Planning (ERP) system integrates all facets of a business, from planning and purchasing to manufacturing, sales, and finance. Imagine it as a central nervous system for your company. It’s a massive software application that helps streamline processes and improve efficiency by centralizing data.
The role of an ERP system includes:
Integrated Data: Provides a single source of truth, eliminating data silos.
Improved Efficiency: Automates processes and reduces manual work.
Better Decision-Making: Offers real-time insights into business performance.
Enhanced Collaboration: Improves communication and coordination between departments.
Increased Scalability: Adapts to the changing needs of the business as it grows.
Examples of ERP systems include SAP, Oracle, and Microsoft Dynamics 365. Choosing the right ERP system depends heavily on the company’s specific needs and size.
Q 7. What are the key components of a network infrastructure?
A network infrastructure’s key components ensure smooth communication and data flow. These include:
Hardware: This includes routers, switches, network interface cards (NICs), servers, cables, and wireless access points. Routers direct traffic between networks, switches connect devices within a network, and NICs allow computers to connect to the network.
Software: This includes operating systems for servers and network devices, network management software, and security software like firewalls and intrusion detection systems. These manage network traffic and security.
Protocols: These are rules and standards that govern how data is transmitted over the network. Examples include TCP/IP, which underpins the internet, and HTTP, used for web communication. They ensure devices can understand each other.
Network Topology: This is the physical or logical layout of the network. Common topologies include star, bus, ring, and mesh networks. The choice of topology affects performance and reliability.
Security: Protecting the network from unauthorized access and malicious activities. Firewalls, intrusion detection systems, and encryption play a crucial role here. Security is paramount for data integrity and confidentiality.
Q 8. Explain the difference between LAN and WAN.
LAN, or Local Area Network, and WAN, or Wide Area Network, are both types of computer networks, but they differ significantly in their geographic scope and ownership. Think of it like this: a LAN is your home network, connecting your devices, while a WAN is like the internet, connecting networks across vast distances.
- LAN: A LAN connects devices within a limited geographical area, such as a home, office, or school. It’s typically owned and managed by a single organization. Speeds are generally faster due to shorter distances. Examples include a network connecting computers in a single building or a home network connecting several devices via Wi-Fi.
- WAN: A WAN connects devices across a larger geographical area, often spanning cities, states, or even countries. It’s often made up of interconnected LANs and is usually owned and managed by multiple organizations (like internet service providers). Speeds can vary greatly, and are generally slower than LANs due to longer distances and multiple points of connection. The internet is the prime example of a WAN.
The key difference boils down to scale and ownership. LANs are local and privately managed, offering faster speeds, while WANs are expansive, publicly or privately managed, and offer varying speeds.
Q 9. What are the different types of network topologies?
Network topologies describe the physical or logical layout of a network. Choosing the right topology impacts factors like performance, scalability, and fault tolerance. There are several common types:
- Bus Topology: Imagine a single highway (the bus) where all devices connect. Simple to implement, but a single point of failure—if the bus fails, the entire network goes down.
- Star Topology: This is the most common topology, where all devices connect to a central hub or switch. Easy to manage and troubleshoot, and failure of one device doesn’t affect the rest. This is what most home and office networks utilize.
- Ring Topology: Devices are connected in a closed loop, data travels in one direction. Fair data access, but a single point of failure can bring down the network.
- Mesh Topology: Multiple connections between devices provide redundancy. Highly reliable and fault-tolerant, but complex and expensive to implement. Often used in critical infrastructure networks.
- Tree Topology: A hierarchical structure resembling an upside-down tree. Combines aspects of bus and star topologies. Scalable, but can become complex to manage as it grows.
The choice of topology depends on the specific needs of the network, balancing factors like cost, reliability, and scalability. A small home network might use a star topology, while a large corporate network might utilize a mesh topology for critical applications.
Q 10. Describe your experience with SQL and its applications in MIS.
SQL, or Structured Query Language, is the standard language for interacting with relational databases. My experience with SQL spans several years, and I’ve used it extensively in various MIS projects to manage and analyze data. In MIS, SQL is crucial for extracting, transforming, and loading (ETL) data from various sources, as well as for generating reports and creating data-driven insights.
For instance, I’ve used SQL to:
- Develop data warehousing solutions: Creating complex queries to extract data from multiple operational systems and load it into a central data warehouse for analysis.
- Build reporting systems: Designing and implementing SQL queries to generate customized reports for different stakeholders, visualizing key performance indicators (KPIs) and business trends.
- Implement data cleansing processes: Using SQL to identify and correct inconsistencies, duplicates, and errors in data sets to ensure data quality.
- Automate data processes: Creating stored procedures and functions in SQL to automate repetitive tasks, such as data backups and data updates.
An example of a simple SQL query to retrieve data would be:
SELECT * FROM Customers WHERE Country='USA';This query retrieves all information from the ‘Customers’ table where the ‘Country’ is ‘USA’. In an MIS context, this could be used to generate a report on US-based customers.
Q 11. How do you ensure data security in an MIS system?
Data security in an MIS system is paramount. A multi-layered approach is essential, combining technical and procedural safeguards. My approach incorporates the following key strategies:
- Access Control: Implementing role-based access control (RBAC) to restrict access to sensitive data based on user roles and responsibilities. Only authorized personnel should have access to specific information.
- Data Encryption: Encrypting data both in transit (using HTTPS or VPNs) and at rest (using database encryption) to protect against unauthorized access, even if a breach occurs.
- Regular Backups: Implementing a robust backup and recovery strategy to protect against data loss due to hardware failure, cyberattacks, or human error. Regular testing of backups is vital.
- Intrusion Detection and Prevention: Employing intrusion detection and prevention systems (IDS/IPS) to monitor network traffic for suspicious activity and prevent unauthorized access.
- Security Awareness Training: Educating users on best practices for data security, such as strong password management, phishing awareness, and secure data handling.
- Regular Security Audits: Conducting regular security audits and penetration testing to identify vulnerabilities and ensure the effectiveness of security measures.
These measures, when implemented effectively, provide a layered approach to minimize the risk of data breaches and protect the confidentiality, integrity, and availability of data within an MIS system.
Q 12. What are the ethical considerations involved in managing MIS systems?
Ethical considerations are central to managing MIS systems. Decisions made regarding data collection, storage, use, and sharing have significant ethical implications. Key concerns include:
- Privacy: Ensuring the privacy of individuals’ data by adhering to data protection regulations (like GDPR or CCPA) and implementing robust data privacy policies. Minimizing data collection and ensuring transparency in data usage are critical.
- Data Security: Protecting data from unauthorized access, use, disclosure, disruption, modification, or destruction. This involves implementing strong security measures and regularly assessing vulnerabilities.
- Accuracy and Integrity: Maintaining the accuracy and integrity of data to ensure reliable decision-making. Implementing data validation and quality control procedures are crucial.
- Transparency and Accountability: Being transparent about data collection and usage practices, and taking accountability for data breaches or misuse. Regular reporting on data governance practices is essential.
- Bias and Discrimination: Avoiding bias and discrimination in data analysis and decision-making. This requires careful consideration of data sources and algorithms used in analysis.
Ethical considerations are not merely compliance issues; they build trust with users and stakeholders, contributing to the long-term success and reputation of any organization utilizing an MIS system.
Q 13. Explain your understanding of cloud computing and its impact on MIS.
Cloud computing represents a paradigm shift in how IT resources are managed and accessed. It involves delivering computing services—including servers, storage, databases, networking, software, analytics, and intelligence—over the Internet (“the cloud”) instead of on-premises hardware. This has a profound impact on MIS systems.
The impact of cloud computing on MIS can be seen in several areas:
- Reduced Costs: Organizations can avoid the capital expenditure associated with purchasing and maintaining hardware and software. They pay only for the resources they consume.
- Increased Scalability and Flexibility: Cloud resources can be easily scaled up or down depending on demand, providing flexibility and agility for businesses.
- Improved Collaboration: Cloud-based MIS systems facilitate collaboration among geographically dispersed teams by providing a central repository for data and applications.
- Enhanced Data Security: Cloud providers often invest heavily in security infrastructure, providing better security than many organizations can achieve on their own. However, choosing a reputable provider with strong security practices is crucial.
- Access to Advanced Technologies: Cloud platforms offer access to advanced technologies such as artificial intelligence (AI), machine learning (ML), and big data analytics, enhancing MIS capabilities.
However, cloud computing also presents challenges, including concerns about data security, vendor lock-in, and the need for robust governance policies. Proper planning and due diligence are vital for successful cloud adoption in MIS.
Q 14. Describe your experience with Business Intelligence (BI) tools.
Business Intelligence (BI) tools are software applications used to collect, analyze, and present business data to support better decision-making. My experience with BI tools includes using several leading platforms to develop interactive dashboards, reports, and data visualizations.
I’ve utilized tools such as:
- Tableau: A powerful visual analytics platform for creating interactive dashboards and reports from various data sources. I’ve used Tableau to create dashboards visualizing key performance indicators (KPIs), sales trends, and customer behavior. Its user-friendly drag-and-drop interface makes it a powerful tool for both technical and non-technical users.
- Power BI: Microsoft’s BI platform, providing data modeling, report creation, and data visualization capabilities. I’ve used Power BI to integrate data from various sources, including Excel spreadsheets and SQL databases, and create interactive dashboards to track business metrics.
- Qlik Sense: A self-service BI tool for data discovery and exploration. Its associative engine allows users to explore data relationships intuitively. I’ve used it for ad-hoc analysis and insightful data explorations.
My experience extends beyond just using these tools; I’m also proficient in designing data models, creating ETL pipelines to prepare data for analysis, and ensuring data integrity within the BI environment. In an MIS context, BI tools are essential for turning raw data into actionable insights, driving strategic decision-making and improving operational efficiency.
Q 15. How do you handle conflicting priorities in an MIS project?
Conflicting priorities in MIS projects are inevitable. My approach involves a structured prioritization process. First, I clearly define project goals and objectives, ensuring everyone understands the ‘why’ behind each task. Then, I employ a prioritization matrix, often using a weighted scoring system based on factors like urgency, business impact, and risk. For example, I might assign weights to criteria such as ‘criticality to project success’ and ‘impact on revenue,’ allowing for a quantitative comparison of tasks. This helps to objectively rank tasks even when subjective opinions conflict. Finally, I use a transparent communication strategy to keep all stakeholders informed about the prioritization decisions, ensuring buy-in and managing expectations. This might involve regular project status meetings, updated Gantt charts, and clear explanations of any changes to the project plan. This process minimizes disruptions and ensures we focus on the most critical aspects of the project.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. Explain your experience with project management methodologies (e.g., Agile, Waterfall).
My experience spans both Agile and Waterfall methodologies. I’ve found that the best approach often depends on the specific project context. Waterfall is well-suited for projects with clearly defined requirements and minimal anticipated changes, like implementing a standard ERP system. The sequential nature allows for thorough planning and testing before moving to the next phase. However, for projects requiring flexibility and iterative development, like building a data analytics dashboard, Agile is far superior. The iterative sprints, daily stand-ups, and continuous feedback loops ensure adaptability to evolving needs and allow for quick course corrections. In practice, I’ve led teams using Scrum (an Agile framework), effectively utilizing sprint planning, daily scrums, sprint reviews, and retrospectives to deliver working software incrementally. I’m adept at selecting the appropriate methodology or even adopting a hybrid approach combining aspects of both, tailoring the process to the project’s unique demands.
Q 17. How do you troubleshoot technical issues in an MIS system?
Troubleshooting technical issues in an MIS system requires a systematic approach. My process starts with identifying the problem’s scope and impact, gathering relevant information from logs, monitoring tools, and user reports. I then systematically isolate the problem by employing techniques such as divide and conquer (breaking down the issue into smaller components), and by using process of elimination (testing various potential causes). For example, if a report is failing to generate, I would first check data source connectivity, then the query syntax, before considering server-side issues. Debugging tools like integrated debuggers and network analyzers are crucial in pinpointing the root cause. I leverage my experience in different technologies – databases, servers, networking – to identify the potential failure points effectively. I always document the troubleshooting steps, solutions, and outcomes to facilitate future problem-solving and knowledge sharing.
Q 18. What are your preferred methods for data analysis and reporting?
My preferred methods for data analysis and reporting involve a combination of tools and techniques. I’m proficient in using SQL for data extraction and manipulation, creating complex queries to answer specific business questions. I leverage business intelligence (BI) tools like Tableau and Power BI for data visualization and creating interactive dashboards. These tools allow me to present complex data in an easily understandable way for different stakeholders. I also use statistical software packages like R or Python (with libraries like Pandas and NumPy) for advanced analytics and statistical modeling. When constructing reports, I prioritize clarity, accuracy, and the effective communication of key findings. The format and level of detail vary based on the audience – a concise summary for executives versus a detailed analysis for technical teams.
Q 19. Describe your experience with data mining techniques.
My experience with data mining techniques includes applying various algorithms for pattern discovery and prediction. I’ve worked with association rule mining (e.g., Apriori algorithm) to identify relationships between variables in large datasets. For instance, I used this to discover product combinations frequently purchased together in an e-commerce setting, informing marketing and inventory strategies. I also have experience with classification techniques (e.g., decision trees, support vector machines) for predicting categorical outcomes. For example, I’ve built models to predict customer churn, enabling proactive intervention. Clustering algorithms (e.g., K-means) were employed to segment customer bases into distinct groups with shared characteristics, guiding targeted marketing campaigns. The choice of algorithm depends critically on the data characteristics, business objectives, and desired outcomes. Each application involves data preprocessing, model training, evaluation, and iterative refinement.
Q 20. How do you ensure data integrity in an MIS system?
Ensuring data integrity in an MIS system is paramount. My approach is multi-faceted. First, I implement data validation rules at the point of entry, preventing invalid or inconsistent data from being inserted. For instance, using constraints in database design (e.g., data type constraints, check constraints) ensures data conforms to predefined rules. Second, I employ data cleansing techniques to identify and correct errors in existing data. This includes handling missing values, resolving inconsistencies, and standardizing data formats. Third, regular data audits are performed to verify data accuracy and completeness, which might involve comparing data across different sources or verifying data against known standards. Finally, I utilize database backup and recovery mechanisms to mitigate the risk of data loss. A robust version control system tracks changes to the data and allows for rollback if necessary. By combining preventative measures, corrective actions, and robust safeguards, we maintain the reliability and trustworthiness of the system’s data.
Q 21. What are the key performance indicators (KPIs) you would track in an MIS system?
The key performance indicators (KPIs) I track in an MIS system depend on the specific business context and objectives. However, some common and crucial KPIs include: system uptime and availability, transaction processing speed, data accuracy and completeness, user satisfaction, and the cost of system maintenance. For example, tracking system uptime helps identify performance bottlenecks and potential service disruptions. Monitoring transaction processing speed ensures the efficiency of business processes. Data accuracy and completeness are critical for decision-making. User satisfaction measures usability and effectiveness. Analyzing the cost of maintenance helps optimize resource allocation. These KPIs, along with others tailored to the specific business needs, are tracked using monitoring tools and reporting dashboards, allowing for proactive identification and mitigation of potential issues.
Q 22. Explain your experience with system integration and interoperability.
System integration involves connecting different MIS systems to share data and resources seamlessly. Interoperability ensures these systems can exchange information regardless of their underlying technologies. Think of it like building a network of roads connecting different cities – each city (system) might have its own unique infrastructure, but the roads (integration methods) allow smooth travel (data exchange) between them.
In my previous role at Acme Corporation, I led the integration of our CRM (Customer Relationship Management) system with our ERP (Enterprise Resource Planning) system. This involved mapping data fields, developing custom APIs (Application Programming Interfaces), and implementing robust error handling. The result was a significant improvement in data accuracy and a reduction in manual data entry, leading to a 20% increase in operational efficiency. We used a combination of ETL (Extract, Transform, Load) processes and real-time data synchronization depending on the specific data requirements.
Another project involved integrating our legacy inventory management system with a new e-commerce platform. This required careful consideration of data migration strategies and the development of a secure data bridge. We used a phased approach, first migrating historical data and then setting up real-time integration for new orders and inventory updates. This minimized disruption to the business during the transition.
Q 23. How do you stay updated on the latest trends and technologies in MIS?
Staying updated in the dynamic field of MIS requires a multi-pronged approach. I regularly read industry publications like CIO magazine and InformationWeek, attend conferences such as Gartner Symposium/ITxpo and participate in online communities like those on LinkedIn and Reddit dedicated to MIS and related technologies. I also actively pursue relevant certifications, such as those offered by CompTIA or ISACA, to demonstrate my commitment to continuous learning and professional development.
Furthermore, I leverage online learning platforms such as Coursera and edX to keep abreast of emerging technologies like AI, machine learning, and cloud computing, and their impact on MIS. Following influential thought leaders on social media and subscribing to relevant newsletters further enriches my understanding of the latest trends and best practices.
Q 24. Describe a time you had to make a critical decision regarding an MIS system.
During a major system upgrade at Beta Solutions, we faced a critical decision regarding the implementation timeline. The original schedule was overly ambitious, risking a significant disruption to our daily operations. After carefully assessing the risks and benefits, I recommended a phased rollout instead of a ‘big bang’ approach. This meant prioritizing the most crucial functionalities for initial release, followed by incremental updates. My recommendation, though initially met with some resistance due to the extended timeframe, ultimately proved to be the correct decision.
The phased rollout significantly minimized the risk of system failure and data loss. It allowed us to thoroughly test each phase, addressing any bugs or issues before proceeding. The end result was a smoother transition, higher user satisfaction, and ultimately, a successful system upgrade without any major disruptions to the business.
Q 25. How do you handle pressure and meet deadlines in a fast-paced MIS environment?
The MIS environment is inherently fast-paced, demanding efficient time management and stress resilience. My approach involves meticulous planning, prioritization, and effective delegation. I use project management methodologies like Agile to break down complex tasks into manageable sprints, enabling consistent progress tracking and facilitating timely adaptations to changing requirements. I also prioritize open communication with my team and stakeholders, ensuring everyone is aware of priorities and potential roadblocks.
Furthermore, I proactively identify and address potential bottlenecks, leveraging tools like Kanban boards for visualizing workflow and optimizing resource allocation. In high-pressure situations, I maintain a calm demeanor, focusing on problem-solving rather than reacting emotionally. My ability to remain organized and detail-oriented, coupled with effective communication, ensures that deadlines are consistently met and projects are successfully completed.
Q 26. Explain your understanding of cybersecurity threats and mitigation strategies.
Cybersecurity threats are a constant concern in MIS, demanding a layered security approach. These threats range from phishing attacks and malware to insider threats and denial-of-service attacks. Mitigation strategies include implementing robust access controls, such as multi-factor authentication, regular security audits, and employee training programs focusing on security awareness. We also need strong firewalls, intrusion detection systems (IDS), and intrusion prevention systems (IPS) to protect the network perimeter.
Data encryption, both in transit and at rest, is crucial to safeguard sensitive information. Regular vulnerability scanning and penetration testing help identify and address security weaknesses proactively. Incident response planning is equally vital; having a well-defined process in place to handle security breaches is crucial for minimizing damage and ensuring business continuity. A key element of this is maintaining up-to-date security patches and software updates across all systems.
Q 27. Describe your experience with disaster recovery and business continuity planning.
Disaster recovery and business continuity planning are essential for ensuring operational resilience. This involves developing strategies to mitigate the impact of unforeseen events, such as natural disasters or cyberattacks. This includes creating a comprehensive disaster recovery plan outlining steps to restore systems and data in the event of a failure. This plan should detail backup and recovery procedures, including data backups to offsite locations and the availability of failover systems.
Regular testing of the disaster recovery plan is crucial to ensure its effectiveness. This involves conducting simulated disaster drills to identify and address any weaknesses. Furthermore, business continuity planning focuses on maintaining essential business functions during disruptions. This might involve establishing alternative work locations, redundant systems, and communication protocols to ensure business operations continue with minimal interruption. My experience includes implementing and testing DR plans involving cloud-based failover systems and geographically dispersed data centers.
Q 28. What are your salary expectations for this role?
My salary expectations for this role are in the range of [Insert Salary Range] per year. This is based on my experience, skills, and the responsibilities associated with this position. I am open to discussing this further and am confident that my contributions will far outweigh the investment.
Key Topics to Learn for MIS Systems Interview
- Database Management Systems (DBMS): Understanding relational databases (SQL, MySQL), NoSQL databases, data modeling, and database design principles. Practical application: Designing a database schema for a specific business problem.
- Network and Security: Knowledge of network topologies, protocols (TCP/IP, HTTP), cybersecurity threats, and security best practices. Practical application: Explaining how to secure a company network from common vulnerabilities.
- Systems Analysis and Design: Understanding the software development lifecycle (SDLC), UML diagrams, requirements gathering, and system implementation. Practical application: Describing your approach to analyzing a business problem and designing a technological solution.
- Business Intelligence (BI) and Data Analytics: Familiarity with data warehousing, data mining, reporting tools, and data visualization techniques. Practical application: Explaining how to use data analytics to improve business decision-making.
- Cloud Computing: Understanding cloud service models (IaaS, PaaS, SaaS), cloud platforms (AWS, Azure, GCP), and cloud security. Practical application: Discussing the benefits and challenges of migrating on-premise systems to the cloud.
- Project Management: Understanding project management methodologies (Agile, Waterfall), risk management, and project planning. Practical application: Describing your experience managing a technology project from initiation to completion.
- IT Service Management (ITSM): Understanding ITIL framework, incident management, problem management, and change management. Practical application: Explaining how to improve the efficiency and effectiveness of IT services.
Next Steps
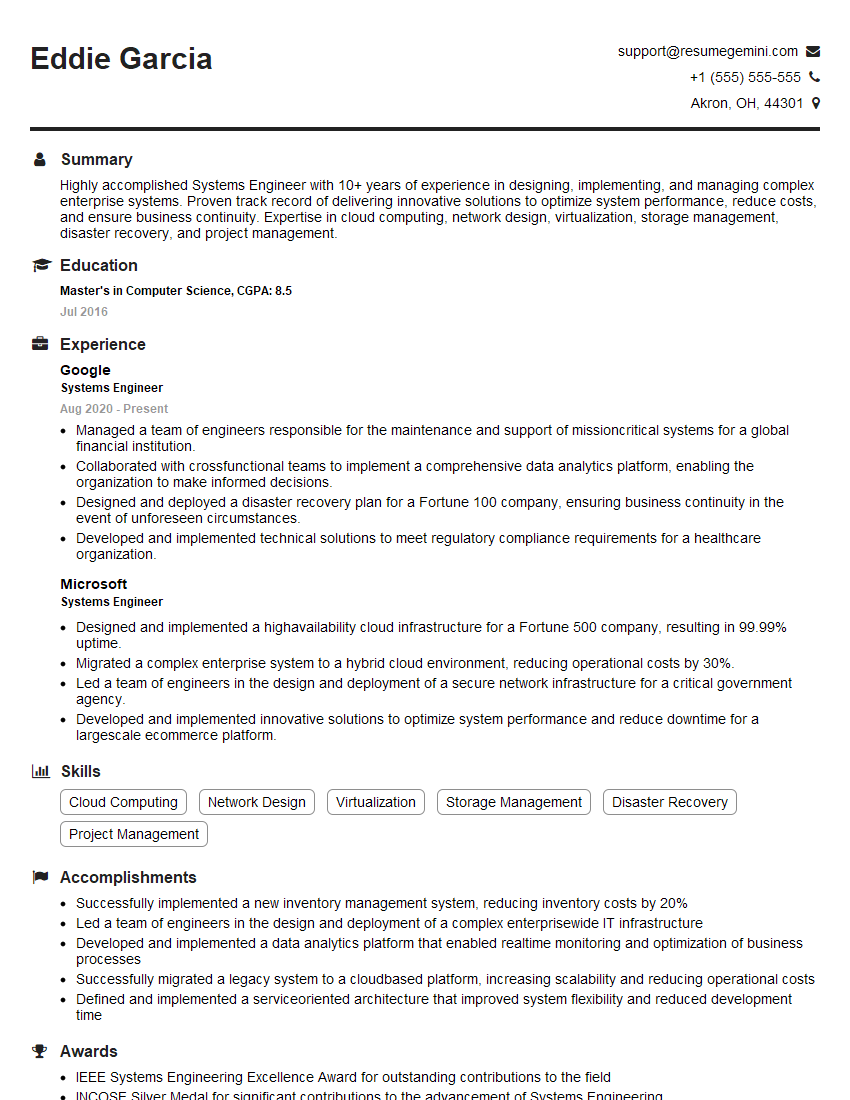
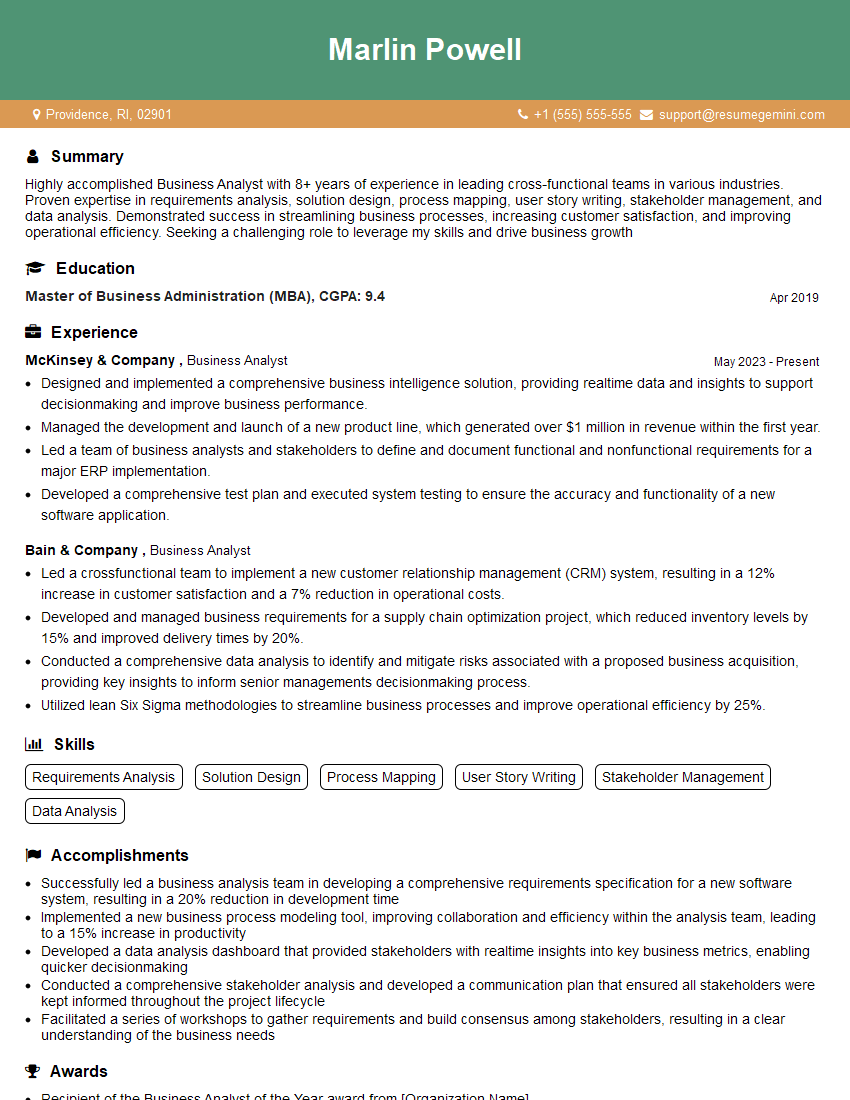
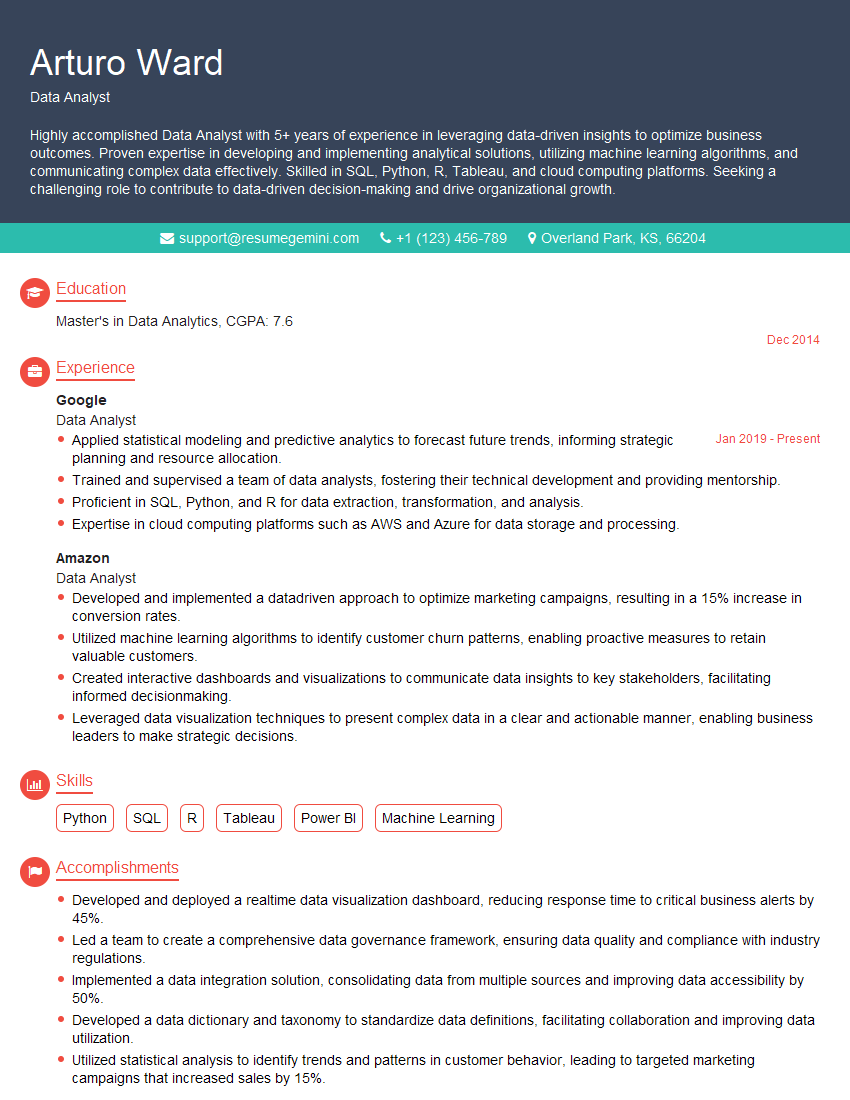
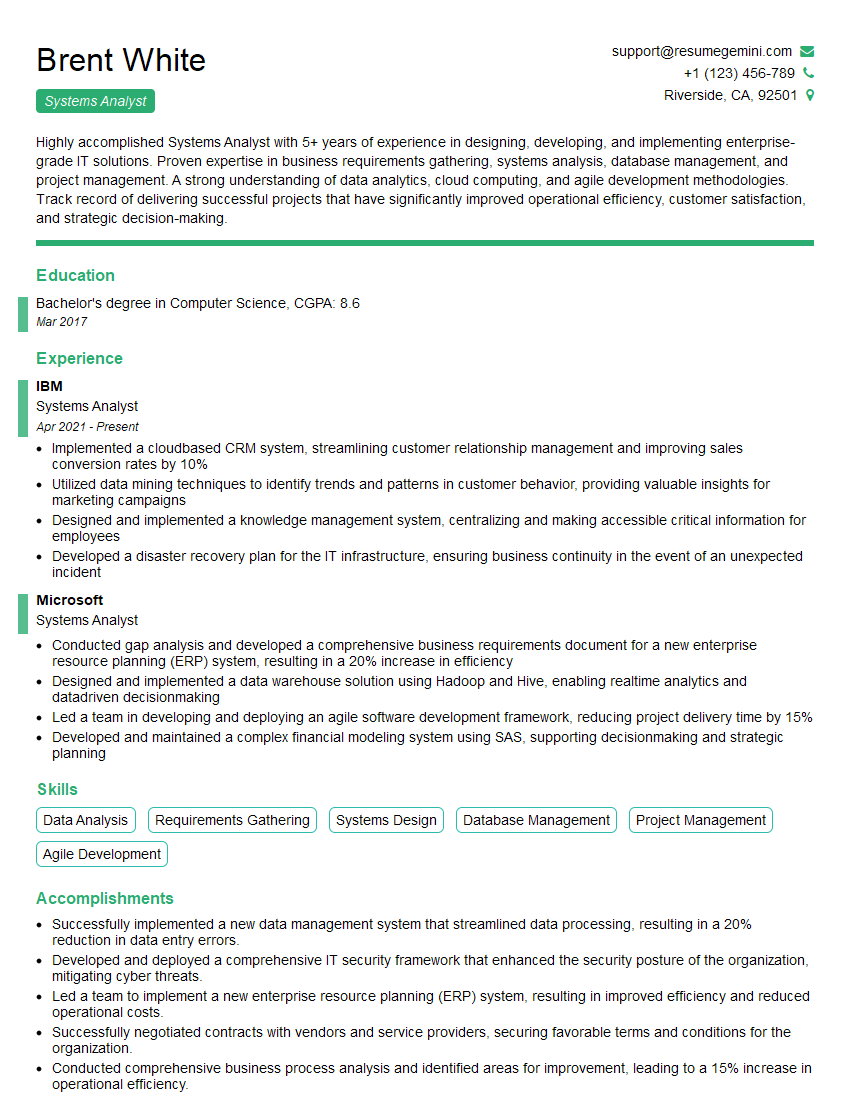
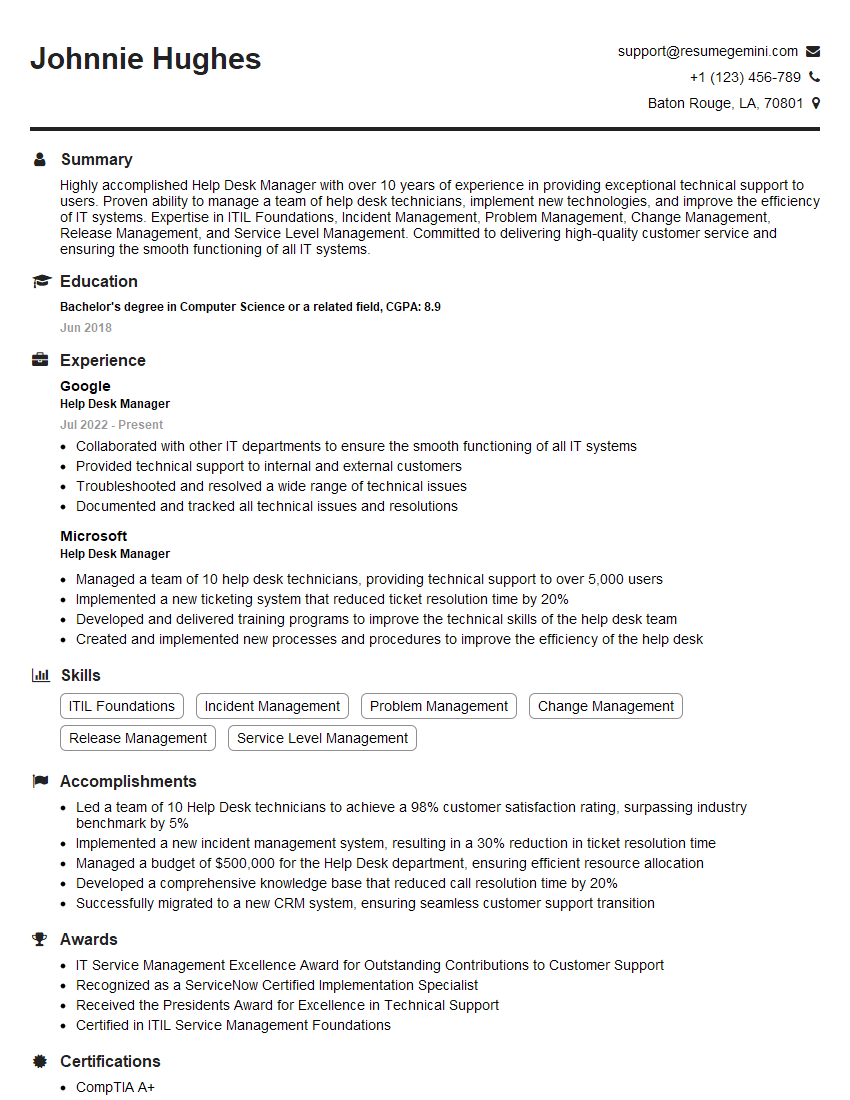
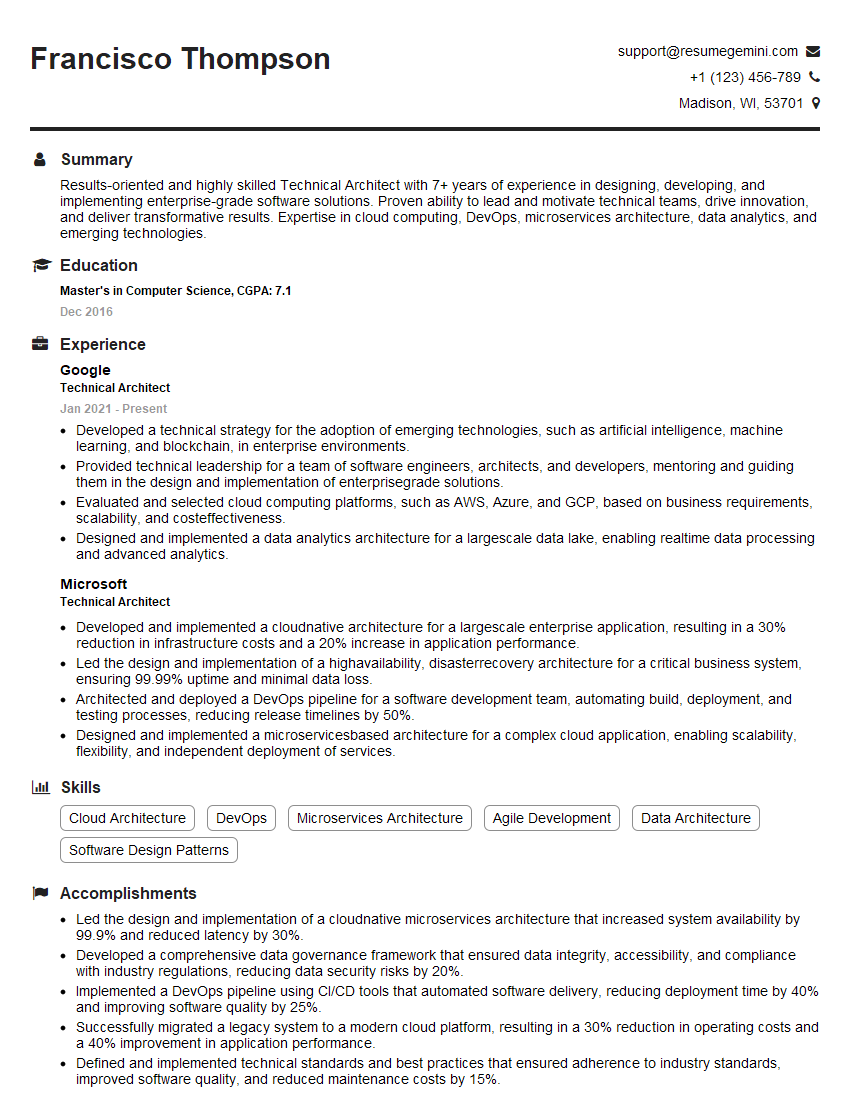
Mastering MIS Systems is crucial for a thriving career in technology, opening doors to exciting roles with significant impact. To maximize your job prospects, a well-crafted, ATS-friendly resume is essential. ResumeGemini can help you build a powerful resume that showcases your skills and experience effectively. ResumeGemini provides examples of resumes tailored to MIS Systems professionals, giving you a head start in crafting a compelling application.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Attention music lovers!
Wow, All the best Sax Summer music !!!
Spotify: https://open.spotify.com/artist/6ShcdIT7rPVVaFEpgZQbUk
Apple Music: https://music.apple.com/fr/artist/jimmy-sax-black/1530501936
YouTube: https://music.youtube.com/browse/VLOLAK5uy_noClmC7abM6YpZsnySxRqt3LoalPf88No
Other Platforms and Free Downloads : https://fanlink.tv/jimmysaxblack
on google : https://www.google.com/search?q=22+AND+22+AND+22
on ChatGPT : https://chat.openai.com?q=who20jlJimmy20Black20Sax20Producer
Get back into the groove with Jimmy sax Black
Best regards,
Jimmy sax Black
www.jimmysaxblack.com
Hi I am a troller at The aquatic interview center and I suddenly went so fast in Roblox and it was gone when I reset.
Hi,
Business owners spend hours every week worrying about their website—or avoiding it because it feels overwhelming.
We’d like to take that off your plate:
$69/month. Everything handled.
Our team will:
Design a custom website—or completely overhaul your current one
Take care of hosting as an option
Handle edits and improvements—up to 60 minutes of work included every month
No setup fees, no annual commitments. Just a site that makes a strong first impression.
Find out if it’s right for you:
https://websolutionsgenius.com/awardwinningwebsites
Hello,
we currently offer a complimentary backlink and URL indexing test for search engine optimization professionals.
You can get complimentary indexing credits to test how link discovery works in practice.
No credit card is required and there is no recurring fee.
You can find details here:
https://wikipedia-backlinks.com/indexing/
Regards
NICE RESPONSE TO Q & A
hi
The aim of this message is regarding an unclaimed deposit of a deceased nationale that bears the same name as you. You are not relate to him as there are millions of people answering the names across around the world. But i will use my position to influence the release of the deposit to you for our mutual benefit.
Respond for full details and how to claim the deposit. This is 100% risk free. Send hello to my email id: [email protected]
Luka Chachibaialuka
Hey interviewgemini.com, just wanted to follow up on my last email.
We just launched Call the Monster, an parenting app that lets you summon friendly ‘monsters’ kids actually listen to.
We’re also running a giveaway for everyone who downloads the app. Since it’s brand new, there aren’t many users yet, which means you’ve got a much better chance of winning some great prizes.
You can check it out here: https://bit.ly/callamonsterapp
Or follow us on Instagram: https://www.instagram.com/callamonsterapp
Thanks,
Ryan
CEO – Call the Monster App
Hey interviewgemini.com, I saw your website and love your approach.
I just want this to look like spam email, but want to share something important to you. We just launched Call the Monster, a parenting app that lets you summon friendly ‘monsters’ kids actually listen to.
Parents are loving it for calming chaos before bedtime. Thought you might want to try it: https://bit.ly/callamonsterapp or just follow our fun monster lore on Instagram: https://www.instagram.com/callamonsterapp
Thanks,
Ryan
CEO – Call A Monster APP
To the interviewgemini.com Owner.
Dear interviewgemini.com Webmaster!
Hi interviewgemini.com Webmaster!
Dear interviewgemini.com Webmaster!
excellent
Hello,
We found issues with your domain’s email setup that may be sending your messages to spam or blocking them completely. InboxShield Mini shows you how to fix it in minutes — no tech skills required.
Scan your domain now for details: https://inboxshield-mini.com/
— Adam @ InboxShield Mini
Reply STOP to unsubscribe
Hi, are you owner of interviewgemini.com? What if I told you I could help you find extra time in your schedule, reconnect with leads you didn’t even realize you missed, and bring in more “I want to work with you” conversations, without increasing your ad spend or hiring a full-time employee?
All with a flexible, budget-friendly service that could easily pay for itself. Sounds good?
Would it be nice to jump on a quick 10-minute call so I can show you exactly how we make this work?
Best,
Hapei
Marketing Director
Hey, I know you’re the owner of interviewgemini.com. I’ll be quick.
Fundraising for your business is tough and time-consuming. We make it easier by guaranteeing two private investor meetings each month, for six months. No demos, no pitch events – just direct introductions to active investors matched to your startup.
If youR17;re raising, this could help you build real momentum. Want me to send more info?
Hi, I represent an SEO company that specialises in getting you AI citations and higher rankings on Google. I’d like to offer you a 100% free SEO audit for your website. Would you be interested?
Hi, I represent an SEO company that specialises in getting you AI citations and higher rankings on Google. I’d like to offer you a 100% free SEO audit for your website. Would you be interested?