Interviews are more than just a Q&A session—they’re a chance to prove your worth. This blog dives into essential Proficient in Incident Response and Recovery interview questions and expert tips to help you align your answers with what hiring managers are looking for. Start preparing to shine!
Questions Asked in Proficient in Incident Response and Recovery Interview
Q 1. Describe your experience with the incident response lifecycle.
The incident response lifecycle is a structured process for handling security incidents. Think of it like a well-organized emergency response team – each step is crucial for minimizing damage and restoring normalcy. It typically involves these phases:
- Preparation: This involves developing an incident response plan, establishing communication protocols, identifying key personnel, and conducting regular training exercises. This is like pre-planning for a potential fire – you know where the exits are, who’s in charge, and what the procedures are.
- Identification: This phase involves detecting a security incident, whether it’s a malicious intrusion, a system failure, or a data breach. This is like noticing the smoke alarm going off.
- Containment: This crucial step focuses on isolating the affected systems or data to prevent further damage or spread of the incident. This is like containing the fire – closing doors to prevent it from spreading.
- Eradication: This stage involves removing the root cause of the incident, such as malware or a compromised account. Think of putting out the fire with a fire extinguisher.
- Recovery: This stage is about restoring affected systems to their normal operational state. This is like repairing the damage after the fire – replacing furniture, cleaning up, and re-opening the building.
- Post-Incident Activity: This final phase involves reviewing the incident, updating the incident response plan, and conducting lessons learned sessions. It’s like analyzing the fire to identify what went wrong and how to prevent it from happening again.
In a recent incident involving a ransomware attack, we followed this lifecycle meticulously. Early identification through our SIEM system allowed us to swiftly contain the spread by isolating affected servers. Eradication involved a combination of malware removal tools and system reimaging. Post-incident analysis led to improvements in our security architecture and employee training programs.
Q 2. Explain the difference between containment and eradication in incident response.
Containment and eradication are distinct but related phases of incident response. Imagine a virus outbreak – containment is like quarantining the infected individuals to prevent further spread, while eradication is about eliminating the virus itself.
Containment focuses on isolating the threat to limit its impact. This might involve disconnecting infected systems from the network, blocking malicious IP addresses, or disabling compromised accounts. The goal is to stop the bleeding. For instance, if a malware infection is detected on a single workstation, containment would involve disconnecting that workstation from the network.
Eradication aims to completely remove the threat. This could involve deleting malware, patching vulnerabilities, or restoring systems from backups. In our ransomware example, eradication included completely wiping and reimaging affected servers, ensuring no remnants of the malware remained. The goal is a complete cure.
Q 3. What are the key components of a comprehensive incident response plan?
A comprehensive incident response plan (IRP) is the roadmap for navigating security incidents. It should be a living document, regularly reviewed and updated. Key components include:
- Incident Response Team: Clearly defined roles and responsibilities for each team member, ensuring a coordinated response. This should include escalation paths and communication channels.
- Communication Plan: Established procedures for communicating with stakeholders, including internal teams, management, and external parties (like law enforcement if necessary).
- Escalation Procedures: A defined process for escalating incidents based on severity and impact. This should outline who is notified at each level and the required actions.
- Data Backup and Recovery Plan: Procedures for backing up critical data and restoring systems in the event of an incident. Regular testing is crucial here.
- Forensic Analysis Procedures: Methods for collecting and analyzing evidence to determine the root cause of the incident and aid in future prevention.
- Legal and Regulatory Compliance: A section addressing legal and regulatory requirements, including data privacy laws and reporting obligations.
- Post-Incident Review: A structured process for reviewing the incident response, identifying areas for improvement, and updating the plan.
A well-defined IRP acts as a safety net, providing a framework for responding effectively and consistently to various incidents.
Q 4. How do you prioritize incidents based on severity and impact?
Incident prioritization is critical in incident response. We utilize a combination of severity and impact to determine urgency. Think of it as a triage system in a hospital – the most critical cases are treated first.
Severity refers to the technical characteristics of the incident. For example, a critical vulnerability exploit is far more severe than a minor denial-of-service attempt.
Impact considers the potential consequences of the incident on the organization. Data breaches impacting sensitive customer information have a much higher impact than a minor service interruption.
We typically use a scoring system that combines severity and impact to assign a priority level to each incident. High-severity, high-impact incidents are addressed immediately. A simple example would be: Severity (1-5, 5 being most severe) and Impact (1-5, 5 being highest impact). An incident with a severity of 5 and impact of 5 would be top priority.
Q 5. What tools and technologies are you proficient in for incident response?
My toolset for incident response is extensive and keeps evolving with the threat landscape. I’m proficient in various tools, including:
- Security Information and Event Management (SIEM) systems: Such as Splunk and QRadar, for log analysis and threat detection.
- Endpoint Detection and Response (EDR) solutions: Like CrowdStrike and Carbon Black, for monitoring endpoint activity and responding to threats.
- Network monitoring tools: Wireshark, tcpdump for analyzing network traffic and identifying malicious activity.
- Forensic analysis tools: Autopsy, FTK Imager for acquiring and analyzing digital evidence.
- Malware analysis tools: Sandbox environments and debuggers for analyzing malicious software.
- Vulnerability scanners: Nessus, OpenVAS for identifying system vulnerabilities.
The specific tools I use often depend on the nature of the incident. For example, during a ransomware attack, I’d heavily utilize EDR and forensic tools to gather evidence and recover data. During a phishing campaign, I’d focus on SIEM and email security tools.
Q 6. Describe your experience with forensic analysis techniques.
Forensic analysis is crucial for understanding the root cause of an incident and gathering evidence for legal or regulatory purposes. My experience encompasses various techniques:
- Data Acquisition: Creating forensic images of hard drives and other storage devices using tools like FTK Imager to ensure data integrity and prevent tampering. This is crucial for preserving the evidence in its original state.
- Network Forensics: Analyzing network traffic logs and packets to identify malicious activity, such as intrusion attempts or data exfiltration. We often use tools like Wireshark for this.
- Memory Forensics: Analyzing the contents of computer memory (RAM) to identify malware or other malicious processes that might not be visible on the hard drive. This helps identify active threats.
- Log Analysis: Examining system and application logs to reconstruct the sequence of events that led to the incident. SIEM systems are invaluable here.
- Malware Analysis: Analyzing malicious code to understand its functionality, origins, and potential impact. Sandbox environments are crucial here to test malware safely.
In a recent case involving a suspected insider threat, memory forensics played a vital role in identifying the specific user who initiated the malicious activity, even though they had attempted to cover their tracks.
Q 7. How do you handle sensitive data during an incident response?
Handling sensitive data during an incident response is paramount. We adhere to strict data privacy regulations and internal policies. Our approach includes:
- Data Encryption: Encrypting sensitive data at rest and in transit to protect it from unauthorized access. Encryption is crucial even if data is compromised.
- Access Control: Restricting access to sensitive data to only authorized personnel on a need-to-know basis. Principle of least privilege is applied rigorously.
- Data Minimization: Collecting only the necessary data to address the incident. We avoid unnecessary collection of personal information to minimize risk.
- Secure Storage: Storing sensitive data in secure locations, both physically and logically, with appropriate access controls. This includes using secure cloud storage.
- Incident Reporting: Reporting data breaches and other security incidents to relevant authorities and affected individuals as required by law or company policy. Transparency and timely notification are key.
We treat all data with the utmost care and follow a strict chain of custody to maintain its integrity throughout the investigation. In any case involving potentially compromised Personal Identifiable Information (PII), we follow stringent notification protocols to comply with data protection regulations such as GDPR and CCPA.
Q 8. Explain your approach to root cause analysis after an incident.
Root cause analysis (RCA) is crucial after any security incident to prevent recurrence. My approach follows a structured methodology, often employing the “5 Whys” technique combined with a more formal framework like the Fishbone diagram. I begin by gathering all available data – logs, system information, network traces – to establish a timeline of events. Then, I systematically ask “why” five times, probing deeper into each answer to uncover the underlying cause. This helps move beyond surface-level symptoms to the fundamental problem.
For example, if a server was compromised (symptom), the “5 Whys” might proceed as follows:
- Why? Because a vulnerability was exploited.
- Why? Because the system wasn’t patched.
- Why? Because patching was delayed due to resource constraints.
- Why? Because the vulnerability management process wasn’t efficient.
- Why? Because there was a lack of automation and prioritization in the patching process.
The final “why” often points to a systemic issue needing a broader solution, such as improved vulnerability management or staff training. The Fishbone diagram visually organizes these contributing factors, helping to identify interdependencies and leverage points for improvement. I always document the entire process, creating a detailed RCA report that becomes a valuable learning experience and helps inform future preventative measures.
Q 9. How do you communicate effectively during an incident response?
Effective communication during an incident is paramount. My approach involves a multi-faceted strategy emphasizing clarity, timeliness, and audience tailoring. I use a combination of communication channels to reach different stakeholders simultaneously. For instance, I might use a dedicated incident management system for internal updates, providing real-time status reports and task assignments. For executives, I offer concise, high-level summaries focusing on impact and remediation efforts. For affected users, I provide clear, simple instructions, ensuring they understand the situation and any required actions. I maintain a consistent communication cadence, avoiding information overload while keeping everyone informed on progress.
Transparency and honesty are vital. If I’m uncertain about something, I’ll clearly state that and provide a timeline for updates. Regular status meetings and well-defined roles and responsibilities maintain order and minimize confusion during a crisis. Ultimately, I strive to create a collaborative environment where everyone feels informed and empowered to contribute to the resolution.
Q 10. Describe a challenging incident response experience and your role in resolving it.
During a ransomware attack on a major client, I played a pivotal role. The attackers encrypted crucial business data and demanded a significant ransom. My first step was to isolate affected systems to prevent further spread. Simultaneously, I coordinated with the forensic team to gather evidence – crucial for potential legal action and insurance claims. We established a clean recovery environment and began restoring data from backups. However, due to a recent system upgrade, some backups were corrupted. This required creative problem-solving – we painstakingly recovered lost data by using shadow copies and file fragments. We were able to fully restore a critical portion of data within 48 hours, minimizing the business disruption. While full recovery took longer, the swift initial response prevented catastrophic financial losses.
This experience highlighted the importance of robust backup and recovery strategies and regular security audits. It also underscored the value of inter-team collaboration and adaptability in crisis management.
Q 11. What are your preferred methods for malware analysis?
My malware analysis approach is multifaceted, employing a combination of static and dynamic analysis techniques in a sandboxed environment. Static analysis involves examining the malware without executing it, using tools like disassemblers (e.g., IDA Pro) and debuggers to understand the code’s structure, functions, and potential behavior. This helps identify strings, embedded URLs, and other indicators of compromise (IOCs).
Dynamic analysis, on the other hand, involves running the malware in a controlled environment, like a virtual machine, to observe its behavior in real-time. I use sandboxing tools and network monitoring systems to capture network activity, registry changes, and file system modifications. This reveals the malware’s actions, such as communication with command-and-control servers, data exfiltration, or system compromise attempts.
I always prioritize safety. All analysis is performed in isolated, virtualized environments to prevent infection of my own systems or the client’s network. Furthermore, I carefully document all steps and findings, creating detailed reports that facilitate effective remediation and future threat intelligence.
Q 12. How do you ensure the integrity of evidence during an investigation?
Maintaining evidence integrity is crucial. My process adheres strictly to established forensics principles, encompassing the following:
- Chain of Custody: I meticulously document every step, including who handled the evidence, when, and where, ensuring a clear and unbroken chain of custody. This is vital for legal admissibility.
- Hashing: I generate cryptographic hashes (e.g., SHA-256) of all evidence before and after any analysis. This verifies data integrity – any changes will alter the hash, alerting me to potential tampering.
- Write Blocking: I use write-blocking tools to prevent accidental modification of evidence during analysis. This ensures the original data remains untouched.
- Imaging: I create forensic images of hard drives or other storage devices, generating bit-by-bit copies. This ensures the original evidence remains untouched while providing a working copy for analysis.
- Secure Storage: All evidence is stored in a secure, tamper-proof location, adhering to all relevant legal and organizational policies.
These measures ensure the evidence remains reliable and trustworthy throughout the investigation, crucial for effective resolution and potential legal proceedings.
Q 13. What is your experience with vulnerability management and patching?
I have extensive experience in vulnerability management and patching. My approach involves a proactive and systematic strategy incorporating vulnerability scanning, risk assessment, and prioritized patching. I utilize automated vulnerability scanning tools to regularly assess systems and applications, identifying known vulnerabilities and potential weaknesses. I then leverage a risk-based approach, prioritizing patches based on the severity of the vulnerability and its potential impact on the organization.
Furthermore, I employ a robust patching management system that ensures timely and efficient deployment of security updates. I work closely with IT operations to minimize disruptions during patching, scheduling updates during low-activity periods and carefully testing patches in a staging environment before rollout. Regular audits and reporting mechanisms monitor the effectiveness of the vulnerability management and patching processes, allowing for continual improvement and adaptation to evolving threats.
Q 14. Explain your understanding of different types of security incidents (e.g., malware, phishing, DDoS).
Security incidents encompass a broad spectrum of threats. I have experience handling various types, including:
- Malware: This includes viruses, worms, trojans, ransomware, and spyware. My response involves containing the infection, eradicating the malware, recovering affected data, and strengthening security defenses to prevent future attacks.
- Phishing: This involves deceptive attempts to obtain sensitive information, often through emails or websites. My approach includes educating users, implementing robust anti-phishing filters, and investigating compromised accounts to prevent further attacks.
- Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) attacks: These overwhelm systems with traffic, disrupting services. My response typically involves mitigation strategies like traffic filtering, rate limiting, and working with internet service providers to block malicious traffic.
- Insider Threats: These are security risks posed by individuals within the organization. My approach combines security awareness training, access control measures, and auditing to minimize the risk of malicious or negligent insider activity.
- Data Breaches: This involves unauthorized access to sensitive data. My response involves containing the breach, investigating the cause, notifying affected parties, and implementing remedial measures to prevent future breaches.
Each incident type requires a tailored response, but the underlying principles of containment, eradication, recovery, and post-incident analysis remain constant. Understanding the nuances of different threats is critical for effective incident response.
Q 15. How do you collaborate with other teams (e.g., IT, legal) during an incident?
Collaboration during an incident is paramount. Think of it like a well-oiled machine – each team has a crucial role, and seamless communication is the engine. I initiate collaboration early and often, using a variety of communication channels – from dedicated incident response chat rooms to formal email updates, depending on the urgency and sensitivity of the information.
With the IT team, my focus is on technical aspects: identifying the root cause, containing the breach, and implementing remediation strategies. For example, during a ransomware attack, I would work closely with IT to isolate affected systems, review backups, and determine the feasibility of recovery.
Legal is involved to ensure compliance, manage potential legal ramifications, and guide communication to affected parties. For instance, during a data breach, legal would advise on notification requirements, public statements, and regulatory reporting obligations (like GDPR or CCPA).
Effective communication and clear roles are crucial. Regular updates, shared documentation, and clearly defined responsibilities prevent confusion and ensure everyone is working towards the same goal. I use collaborative tools like shared documents and project management software to track progress and ensure transparency.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. What are your experience with various incident response frameworks (e.g., NIST, ISO 27001)?
I have extensive experience with several incident response frameworks, most notably NIST Cybersecurity Framework and ISO 27001. NIST provides a flexible, risk-based approach, focusing on identify, protect, detect, respond, and recover. I’ve used its guidance to develop and refine our incident response plan, customizing it to our specific organizational context and threat landscape.
ISO 27001, on the other hand, focuses on establishing an Information Security Management System (ISMS). While not solely an incident response framework, its principles are foundational. Its emphasis on risk assessment, policy development, and continuous improvement directly supports a robust incident response capability.
My experience involves applying these frameworks practically. For instance, in one case, we used the NIST framework’s ‘detect’ function to identify a malicious insider threat through unusual access patterns flagged by our SIEM. The ‘respond’ function guided our actions in isolating the user’s access, and the ‘recover’ function outlined the steps to strengthen access control policies.
Q 17. How do you document and report on incidents?
Documentation and reporting are vital for accountability, learning, and continuous improvement. My approach follows a structured format:
- Incident Report: This includes a timeline of events, a description of the incident, affected systems, the root cause analysis, and the containment and recovery actions. I use a standardized template to ensure consistency and completeness.
- Evidence Collection: This involves securing logs, network captures, and other relevant data. This is crucial for forensic analysis and legal purposes.
- Lessons Learned Report: After the incident is resolved, I create a report summarizing what went well, what could have been improved, and recommendations for enhancing our incident response plan. This is crucial for proactive measures.
All documentation is stored securely and maintained according to our data retention policies. Reports are shared with relevant stakeholders, including management and external parties where appropriate.
Q 18. What are your experience with incident response playbooks?
Incident response playbooks are like detailed instruction manuals for handling various incident types. I have extensive experience developing, testing, and maintaining them. A well-structured playbook reduces response time and improves efficiency by outlining pre-defined steps, roles, responsibilities, and communication protocols.
Our playbooks cover different scenarios, from phishing attacks to data breaches to denial-of-service attacks. Each playbook includes:
- Incident identification and triage procedures
- Containment and eradication steps
- Recovery procedures and communication plan
- Post-incident activity checklist
Regularly reviewing and updating playbooks is essential. We conduct simulations and table-top exercises to test their effectiveness and identify areas for improvement. This ensures that our playbooks remain relevant and effective in the face of evolving threats.
Q 19. Describe your experience with security information and event management (SIEM) systems.
SIEM systems are invaluable during incident response. Think of them as a central nervous system for security monitoring, providing real-time visibility into security events across the organization. My experience with SIEM systems involves utilizing their capabilities for:
- Log aggregation and analysis: Correlating logs from various sources to identify security events and potential threats.
- Threat detection: Utilizing SIEM’s built-in rules and anomaly detection capabilities to alert on suspicious activity.
- Incident investigation: Using the SIEM data to reconstruct the timeline of an incident, identifying the source, and determining the impact.
- Forensics analysis: Extracting relevant data for forensic investigation and legal purposes.
I’m proficient in using various SIEM platforms (e.g., Splunk, QRadar) and configuring them to meet our specific security needs. For instance, I’ve developed custom rules and dashboards to detect and respond to specific types of attacks we’ve identified as high-risk in our threat model.
Q 20. How do you handle escalation procedures during a critical incident?
Escalation procedures are critical during major incidents. Our escalation process is clearly defined and documented in our incident response plan. It outlines communication paths, notification lists, and escalation criteria.
Typically, escalation involves informing the appropriate management levels based on the severity and impact of the incident. For example, a minor security incident might be handled within the security team, whereas a significant data breach would require immediate escalation to senior management and potentially even the board of directors.
Clear communication is vital during escalations. I ensure concise and accurate updates are provided to all relevant stakeholders, and I proactively manage expectations. The escalation process includes regular status updates to keep everyone informed about the progress of the incident response. We use communication channels appropriate to the urgency and sensitivity of the situation (e.g., phone calls for immediate critical situations, email updates for less urgent matters).
Q 21. What is your approach to post-incident activity (e.g., remediation, lessons learned)?
Post-incident activity is crucial for learning and prevention. It’s not just about fixing the problem; it’s about ensuring it doesn’t happen again. My approach involves several key steps:
- Remediation: Implementing the necessary fixes to prevent future occurrences. This might involve patching vulnerabilities, updating security controls, or implementing new security measures.
- Recovery: Restoring systems and data to their pre-incident state. We prioritize critical systems and data based on their business impact.
- Root Cause Analysis: Conducting a thorough investigation to determine the root cause of the incident. We use techniques like the five whys to get to the core of the problem.
- Lessons Learned Review: Holding a formal review with the incident response team and relevant stakeholders. This session involves documenting the findings, identifying areas for improvement, and updating our incident response plan and playbooks accordingly.
- Documentation and Reporting: Finalizing incident reports and sharing them with relevant parties. The lessons learned report helps prevent future occurrences.
The post-incident activity is as important as the incident response itself. It is through this process that we continuously improve our security posture and minimize our vulnerabilities.
Q 22. How do you stay up-to-date with the latest threats and vulnerabilities?
Staying current in the ever-evolving landscape of cybersecurity threats requires a multi-pronged approach. It’s not just about reading news articles; it’s about actively engaging with the threat intelligence community.
Threat Intelligence Platforms: I subscribe to several reputable threat intelligence platforms like [mention specific platforms, e.g., ThreatConnect, Recorded Future] that provide real-time threat feeds, vulnerability reports, and analysis of emerging attack vectors. This allows me to proactively identify potential threats and adjust our security posture accordingly.
Security Research and Publications: I regularly follow security researchers and blogs (e.g., Krebs on Security, SANS Institute) to keep abreast of the latest exploits, malware techniques, and emerging trends. Reading peer-reviewed papers and attending industry conferences expands my knowledge of advanced persistent threats (APTs) and other sophisticated attack methods.
Vulnerability Scanning and Penetration Testing: I actively participate in vulnerability scanning and penetration testing exercises, both internally and externally. This hands-on experience allows me to understand how real-world attacks work and how to effectively mitigate them. This is more than just running automated tools; it’s about understanding the underlying vulnerabilities and developing effective countermeasures.
Industry Certifications and Training: Continuing education is critical. I maintain several industry certifications (e.g., CISSP, SANS certifications) and regularly participate in advanced training courses focused on incident response and threat hunting techniques.
Think of it like this: staying up-to-date with cybersecurity threats is like being a doctor staying updated on new diseases. You can’t just read old textbooks; you need to be aware of the latest research, outbreaks, and treatment methods.
Q 23. What is your understanding of regulatory compliance requirements related to incident response?
Regulatory compliance in incident response is paramount. It varies depending on the industry and geographic location, but some key regulations I’m intimately familiar with include GDPR (General Data Protection Regulation), CCPA (California Consumer Privacy Act), HIPAA (Health Insurance Portability and Accountability Act), and PCI DSS (Payment Card Industry Data Security Standard).
GDPR: Focuses on data breaches and requires organizations to notify authorities and affected individuals within 72 hours of discovery. It emphasizes data minimization, purpose limitation, and accountability.
CCPA: Similar to GDPR, but specific to California residents, requiring businesses to provide transparency about data collection and provide consumers with control over their personal data. Breach notification is also a critical element.
HIPAA: Governs the protection of patient health information (PHI). Stricter regulations apply to healthcare organizations regarding data breaches and incident response procedures.
PCI DSS: Mandates security standards for organizations handling credit card information. Failing to adhere to these standards can result in significant penalties.
My understanding goes beyond simply knowing the regulations; I can implement and document compliant incident response plans, conduct regular compliance audits, and train personnel on their roles and responsibilities within a regulatory framework. For example, a well-documented incident response plan, incorporating best practices aligned with relevant regulations, is a key element of demonstrating compliance.
Q 24. Describe your experience with threat hunting.
Threat hunting is proactive, unlike incident response which is reactive. It involves actively searching for malicious activity within a network, even in the absence of an alert. My experience includes utilizing a variety of techniques to identify advanced persistent threats (APTs) and other sophisticated attacks.
Hypothesis-driven hunting: I often start with a hypothesis about potential threats based on current threat intelligence. For instance, I might hypothesize that a specific malware family is targeting our organization based on recent reports. I would then use various tools and techniques to test this hypothesis.
Data analysis and correlation: I’m proficient in using Security Information and Event Management (SIEM) systems and other security tools to analyze log data, network traffic, and endpoint activity to identify suspicious patterns or anomalies that might indicate a compromise. This includes using various correlation rules and techniques to link seemingly disparate events together.
Endpoint detection and response (EDR): I have extensive experience leveraging EDR solutions to hunt for threats on individual endpoints. EDR tools provide rich telemetry that can be analyzed to detect malicious behavior, such as unusual file execution, network connections, or registry modifications.
Threat intelligence integration: I incorporate threat intelligence feeds into my hunting activities, using indicators of compromise (IOCs) to search for known malicious activity within our environment. For example, I recently used a list of known malicious IP addresses from a threat intelligence feed to identify compromised systems in our network.
Imagine threat hunting as a detective investigating a crime before it occurs. Instead of waiting for a crime to happen, I’m proactively searching for evidence of potential threats and vulnerabilities.
Q 25. What is your experience with log analysis and data correlation?
Log analysis and data correlation are fundamental to effective incident response. It’s about turning raw data into actionable intelligence. My experience encompasses various tools and techniques to analyze massive datasets, identify patterns, and understand the sequence of events during an incident.
SIEM Systems: I’m adept at using SIEM systems (e.g., Splunk, QRadar) to collect, analyze, and correlate security logs from various sources, including firewalls, intrusion detection systems, and endpoint security tools. This allows me to reconstruct attack timelines, identify compromised systems, and pinpoint the root cause of an incident.
Querying and Scripting: I can write effective queries (e.g., using Splunk SPL or similar query languages) to extract relevant data from log files. I also utilize scripting languages like Python to automate the analysis process and develop custom tools for data correlation and visualization. For example, I wrote a Python script that automatically extracts specific events from multiple log sources and creates a timeline of the incident.
Data Visualization: I’m experienced in using data visualization tools to present findings in a clear and concise manner, making complex information easily understandable for both technical and non-technical audiences. This includes creating visualizations to represent the attack timeline, affected systems, and other relevant information.
Regular Expressions (Regex): I proficiently use regular expressions to parse log files and identify specific patterns or anomalies within the data. This allows for highly efficient filtering and analysis of large volumes of log data.
Think of it like assembling a jigsaw puzzle – log analysis and data correlation are like finding the pieces and putting them together to reveal the complete picture of an attack.
Q 26. How do you measure the effectiveness of your incident response process?
Measuring the effectiveness of an incident response process is crucial. It’s not just about successfully containing an incident; it’s about continuous improvement. I utilize several key metrics:
Mean Time to Detect (MTTD): How long it takes to identify an incident. Lower MTTD indicates a more effective process.
Mean Time to Respond (MTTR): How long it takes to contain and remediate an incident. Lower MTTR is the goal.
Mean Time to Recovery (MTTR): How long it takes to restore systems and data to a normal operational state.
Incident containment rate: Percentage of incidents successfully contained before significant damage occurs.
Post-Incident Review (PIR) Effectiveness: Conducting thorough post-incident reviews and implementing corrective actions are key to continual process improvement. PIRs identify weaknesses and allow us to refine our strategies for future incidents.
Cost of an incident: Estimating the financial costs associated with incidents. This includes costs related to recovery, legal fees, and reputational damage. This is critical to identifying areas of cost savings through improved incident response processes.
These metrics are tracked using a combination of automated tools and manual processes. Regular reporting and analysis provide insights for continuous improvement. For example, a consistently high MTTD would signal the need for improvements in threat detection capabilities, such as implementing advanced threat detection tools or enhancing security monitoring processes.
Q 27. What are your salary expectations?
My salary expectations are commensurate with my experience and skills, and are competitive within the current market for incident response professionals with my qualifications and track record. I am open to discussing a compensation package that reflects the value I bring to your organization. I would be happy to provide more details after understanding the specifics of the role and its responsibilities within your company.
Key Topics to Learn for Proficient in Incident Response and Recovery Interview
- Incident Identification and Classification: Understanding the various types of security incidents (malware, phishing, DDoS, etc.) and their potential impact. Practical application involves developing a structured approach to triage and prioritize incidents based on severity and urgency.
- Incident Containment and Eradication: Mastering techniques to isolate affected systems, prevent further damage, and remove malicious code or activity. This includes practical experience with tools and methodologies for forensic analysis and malware removal.
- Recovery and Restoration: Developing strategies for restoring systems and data to a pre-incident state, minimizing downtime and data loss. Practical application might involve using backups, system imaging, and disaster recovery plans.
- Root Cause Analysis: Understanding how to investigate the root cause of security incidents to prevent future occurrences. This requires strong analytical skills and the ability to trace the attack path.
- Communication and Collaboration: Effective communication with stakeholders during an incident, including reporting, updates, and post-incident reviews. Practical application includes preparing clear and concise reports for management and technical teams.
- Security Information and Event Management (SIEM): Understanding how to leverage SIEM tools for incident detection, monitoring, and analysis. Practical application includes configuring alerts, analyzing logs, and correlating events.
- Vulnerability Management: Understanding the importance of proactively identifying and mitigating vulnerabilities to reduce the likelihood of incidents. This involves knowledge of vulnerability scanning, penetration testing, and patching.
- Incident Response Planning and Tabletop Exercises: Developing and practicing incident response plans through tabletop exercises to ensure preparedness and coordination among team members.
Next Steps
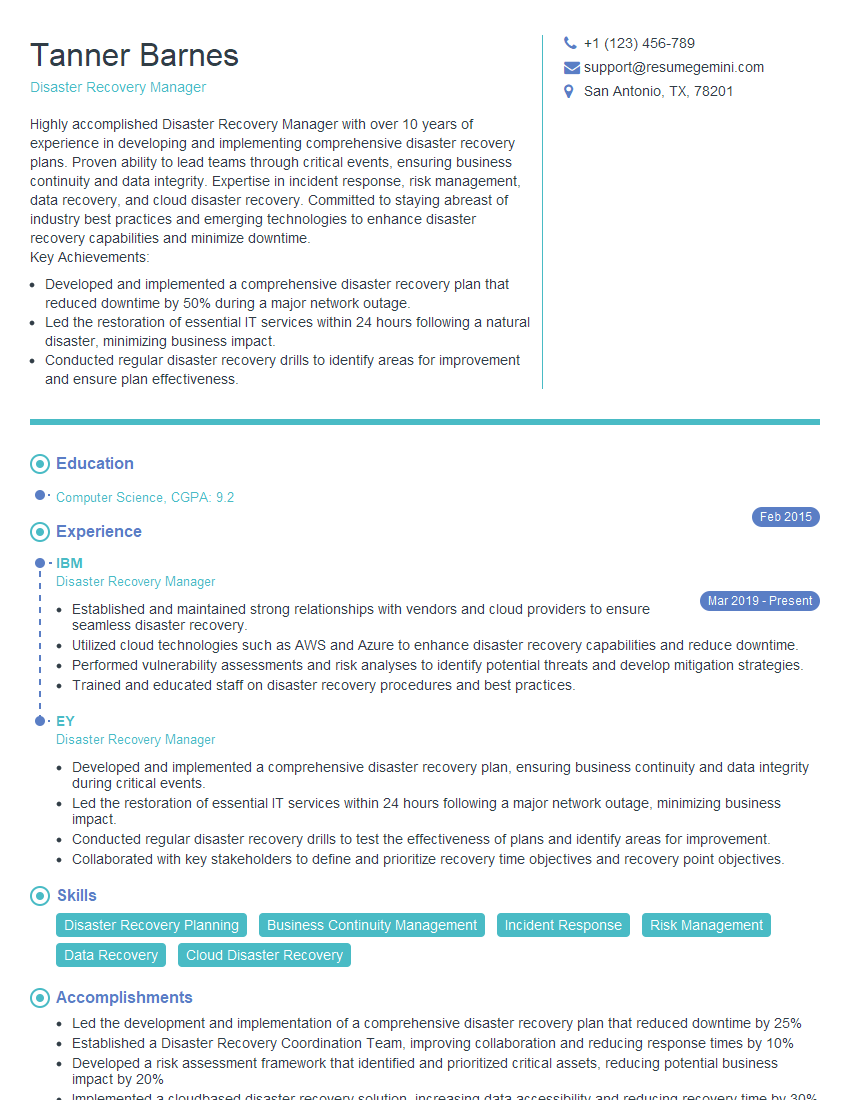
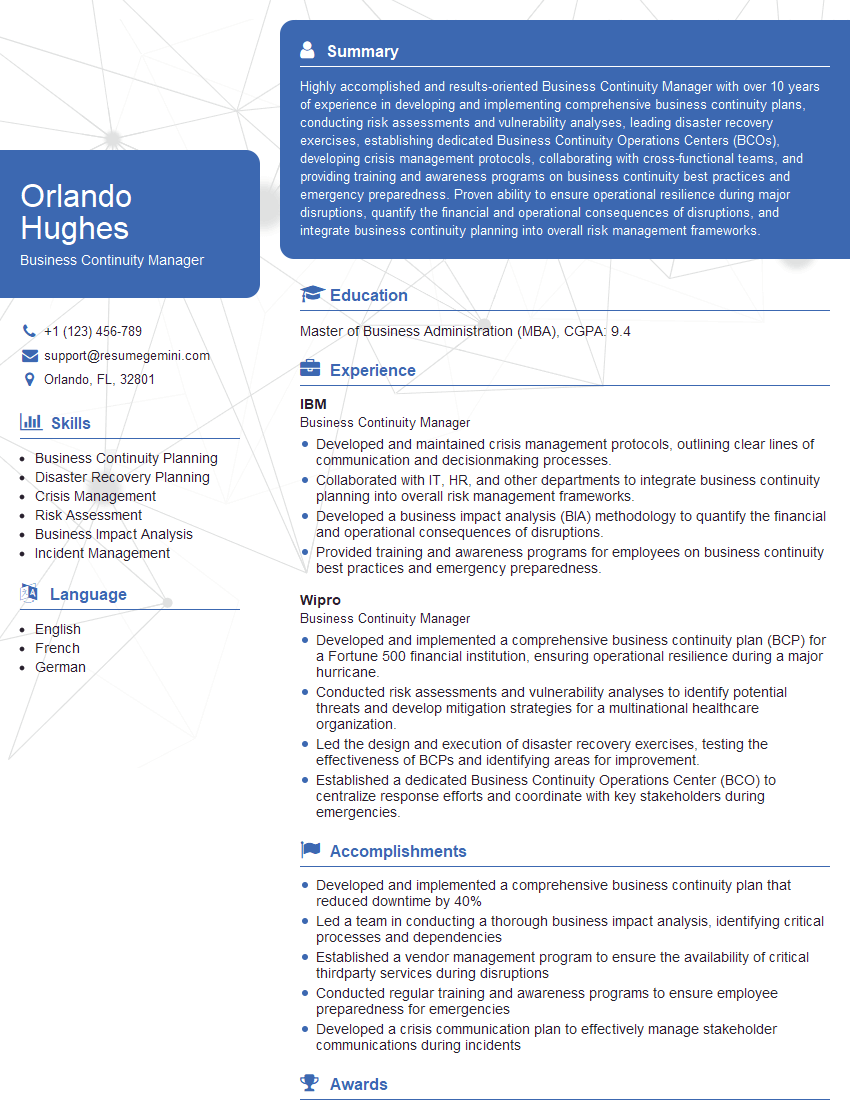
Mastering incident response and recovery is crucial for career advancement in cybersecurity, opening doors to specialized roles and increased earning potential. To maximize your job prospects, creating an ATS-friendly resume is essential. ResumeGemini is a trusted resource that can help you build a professional and impactful resume that highlights your skills and experience. ResumeGemini provides examples of resumes tailored to Proficient in Incident Response and Recovery, allowing you to create a compelling document that showcases your expertise and increases your chances of landing your dream job.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Attention music lovers!
Wow, All the best Sax Summer music !!!
Spotify: https://open.spotify.com/artist/6ShcdIT7rPVVaFEpgZQbUk
Apple Music: https://music.apple.com/fr/artist/jimmy-sax-black/1530501936
YouTube: https://music.youtube.com/browse/VLOLAK5uy_noClmC7abM6YpZsnySxRqt3LoalPf88No
Other Platforms and Free Downloads : https://fanlink.tv/jimmysaxblack
on google : https://www.google.com/search?q=22+AND+22+AND+22
on ChatGPT : https://chat.openai.com?q=who20jlJimmy20Black20Sax20Producer
Get back into the groove with Jimmy sax Black
Best regards,
Jimmy sax Black
www.jimmysaxblack.com
Hi I am a troller at The aquatic interview center and I suddenly went so fast in Roblox and it was gone when I reset.
Hi,
Business owners spend hours every week worrying about their website—or avoiding it because it feels overwhelming.
We’d like to take that off your plate:
$69/month. Everything handled.
Our team will:
Design a custom website—or completely overhaul your current one
Take care of hosting as an option
Handle edits and improvements—up to 60 minutes of work included every month
No setup fees, no annual commitments. Just a site that makes a strong first impression.
Find out if it’s right for you:
https://websolutionsgenius.com/awardwinningwebsites
Hello,
we currently offer a complimentary backlink and URL indexing test for search engine optimization professionals.
You can get complimentary indexing credits to test how link discovery works in practice.
No credit card is required and there is no recurring fee.
You can find details here:
https://wikipedia-backlinks.com/indexing/
Regards
NICE RESPONSE TO Q & A
hi
The aim of this message is regarding an unclaimed deposit of a deceased nationale that bears the same name as you. You are not relate to him as there are millions of people answering the names across around the world. But i will use my position to influence the release of the deposit to you for our mutual benefit.
Respond for full details and how to claim the deposit. This is 100% risk free. Send hello to my email id: lukachachibaialuka@gmail.com
Luka Chachibaialuka
Hey interviewgemini.com, just wanted to follow up on my last email.
We just launched Call the Monster, an parenting app that lets you summon friendly ‘monsters’ kids actually listen to.
We’re also running a giveaway for everyone who downloads the app. Since it’s brand new, there aren’t many users yet, which means you’ve got a much better chance of winning some great prizes.
You can check it out here: https://bit.ly/callamonsterapp
Or follow us on Instagram: https://www.instagram.com/callamonsterapp
Thanks,
Ryan
CEO – Call the Monster App
Hey interviewgemini.com, I saw your website and love your approach.
I just want this to look like spam email, but want to share something important to you. We just launched Call the Monster, a parenting app that lets you summon friendly ‘monsters’ kids actually listen to.
Parents are loving it for calming chaos before bedtime. Thought you might want to try it: https://bit.ly/callamonsterapp or just follow our fun monster lore on Instagram: https://www.instagram.com/callamonsterapp
Thanks,
Ryan
CEO – Call A Monster APP
To the interviewgemini.com Owner.
Dear interviewgemini.com Webmaster!
Hi interviewgemini.com Webmaster!
Dear interviewgemini.com Webmaster!
excellent
Hello,
We found issues with your domain’s email setup that may be sending your messages to spam or blocking them completely. InboxShield Mini shows you how to fix it in minutes — no tech skills required.
Scan your domain now for details: https://inboxshield-mini.com/
— Adam @ InboxShield Mini
support@inboxshield-mini.com
Reply STOP to unsubscribe
Hi, are you owner of interviewgemini.com? What if I told you I could help you find extra time in your schedule, reconnect with leads you didn’t even realize you missed, and bring in more “I want to work with you” conversations, without increasing your ad spend or hiring a full-time employee?
All with a flexible, budget-friendly service that could easily pay for itself. Sounds good?
Would it be nice to jump on a quick 10-minute call so I can show you exactly how we make this work?
Best,
Hapei
Marketing Director
Hey, I know you’re the owner of interviewgemini.com. I’ll be quick.
Fundraising for your business is tough and time-consuming. We make it easier by guaranteeing two private investor meetings each month, for six months. No demos, no pitch events – just direct introductions to active investors matched to your startup.
If youR17;re raising, this could help you build real momentum. Want me to send more info?
Hi, I represent an SEO company that specialises in getting you AI citations and higher rankings on Google. I’d like to offer you a 100% free SEO audit for your website. Would you be interested?
Hi, I represent an SEO company that specialises in getting you AI citations and higher rankings on Google. I’d like to offer you a 100% free SEO audit for your website. Would you be interested?