Unlock your full potential by mastering the most common DevOps Configuration Management Tools (e.g., Jenkins, Puppet) interview questions. This blog offers a deep dive into the critical topics, ensuring you’re not only prepared to answer but to excel. With these insights, you’ll approach your interview with clarity and confidence.
Questions Asked in DevOps Configuration Management Tools (e.g., Jenkins, Puppet) Interview
Q 1. Explain the difference between Puppet, Chef, and Ansible.
Puppet, Chef, and Ansible are all popular configuration management tools, but they differ in their approach and architecture. Think of them as three different chefs preparing a meal (your infrastructure):
- Puppet: Uses a declarative approach. You describe the desired state of your system (the recipe), and Puppet figures out how to get there. It’s like giving a chef a detailed list of ingredients and the final dish; they handle the cooking process. It uses a master-agent architecture, where a central Puppet master server manages the configuration of client nodes (agents).
- Chef: Also uses a declarative approach, but with a more robust infrastructure and extensive community support. It’s like having a chef who follows a highly detailed cookbook with a lot of pre-built recipes for various tasks. Chef also employs a master-agent architecture, but its infrastructure is designed for scaling and complex environments.
- Ansible: Employs a simpler, agentless architecture. It uses SSH to connect to and manage nodes directly, making it easier to set up and more lightweight. It’s like having a chef who directly interacts with your ingredients and cooking equipment, without any need for a central kitchen or helpers. Ansible utilizes a more procedural approach, where you define the steps to achieve the desired state.
In essence, Puppet and Chef are well-suited for large, complex infrastructures requiring strong central control, while Ansible shines in simpler setups where ease of use and speed are prioritized. The best choice depends on the specific needs of your project.
Q 2. Describe your experience with Jenkins pipelines and their components.
My experience with Jenkins pipelines involves extensively utilizing the declarative pipeline syntax for its improved readability and maintainability. A typical pipeline might include stages for building, testing, and deploying applications. Key components I leverage are:
- Stages: Logical groupings of steps within the pipeline. Examples include
build,test,deploy, andpromote. - Steps: Individual tasks within a stage, such as running shell scripts (
sh 'mvn clean package'), invoking Gradle builds, or interacting with version control systems (git checkout). - Parameters: Allow for flexible pipeline execution by accepting input values, such as environment names or build versions (
parameters { string(name: 'BRANCH', defaultValue: 'main', description: 'Git branch to build') }). - Post steps: Actions to perform after the pipeline completes, regardless of success or failure (like sending email notifications).
- Environment variables: Define reusable variables across the pipeline for better organization and maintainability.
- Plugins: Extending the pipeline’s functionality with plugins for specific tasks, like deploying to cloud providers or integrating with other CI/CD tools.
For instance, I’ve built pipelines that automatically deploy code to different environments (development, staging, production) based on branch merging events. Robust error handling and logging mechanisms are crucial for ensuring pipeline stability and troubleshooting issues quickly.
Q 3. How do you manage code deployments using Jenkins?
I manage code deployments using Jenkins pipelines by leveraging the power of its extensibility and integration capabilities. This often involves creating a multi-stage pipeline that handles various aspects of the deployment process:
- Code Checkout: The pipeline begins by checking out the code from the version control system (e.g., Git) based on the branch or tag.
- Build: Next, the code is built using appropriate tools (e.g., Maven, Gradle). Any necessary unit and integration tests are executed.
- Artifact Creation: A deployable artifact (e.g., WAR file, Docker image) is created. This artifact is then stored in an artifact repository (e.g., Nexus, Artifactory).
- Deployment: The pipeline uses plugins to deploy the artifact to target servers or cloud environments. Examples include plugins for deploying to AWS, Azure, Kubernetes, or simply using SSH to copy the artifact and run deployment scripts on the target.
- Post-Deployment Verification: After deployment, the pipeline may perform checks to validate the successful deployment. This might include running smoke tests or verifying the availability of the application.
Furthermore, I utilize techniques like blue/green deployments or canary releases for minimizing downtime and risks during deployment. The entire process is meticulously documented and configured within Jenkins, allowing for easy monitoring, reproducibility, and rollback if needed. The deployment process is designed to be idempotent – meaning repeated execution will have the same effect as a single execution.
Q 4. What are the benefits of Infrastructure as Code (IaC)?
Infrastructure as Code (IaC) is the practice of managing and provisioning infrastructure through code rather than manual processes. Think of it as treating your servers and network configurations like software code, allowing for version control, automated deployments, and improved reproducibility.
- Improved Consistency and Repeatability: IaC ensures that infrastructure is consistently provisioned across different environments. This eliminates the variability inherent in manual configuration.
- Automation: It allows for automated provisioning and management of infrastructure, saving time and reducing human error.
- Version Control and Collaboration: Infrastructure code is stored in version control systems, enabling collaboration, tracking changes, and rollback capabilities.
- Increased Agility: Changes to infrastructure can be implemented faster and more reliably, facilitating faster iteration cycles.
- Cost Optimization: IaC can help reduce infrastructure costs through better resource utilization and automation.
For example, using tools like Terraform or CloudFormation, we can define the entire infrastructure (servers, networks, databases) in code and have it automatically created and updated in a cloud environment. This dramatically reduces manual overhead and ensures consistency.
Q 5. How do you handle version control in your configuration management workflows?
Version control is absolutely central to my configuration management workflows. I always store all configuration files (Puppet manifests, Chef cookbooks, Ansible playbooks, Terraform configurations, etc.) in a version control system like Git. This provides numerous benefits:
- Audit Trail: Tracking all changes to the infrastructure configuration is crucial for troubleshooting and auditing purposes.
- Collaboration: Multiple team members can collaborate on the configuration code effectively.
- Rollback: In case of errors or misconfigurations, the code can be easily reverted to a previous working version.
- Branching and Merging: Allows for experimenting with new configurations in isolated branches before merging them into the main branch.
- Code Reviews: Improves code quality and consistency by allowing for code reviews before merging changes into the main branch.
I follow a branching strategy (e.g., Gitflow) and enforce strict code review procedures to ensure code quality and consistency across environments. We use pull requests and thorough testing before deploying any changes to production.
Q 6. Explain the concept of idempotency in configuration management.
Idempotency in configuration management means that applying a configuration multiple times will have the same effect as applying it once. It’s a fundamental principle that guarantees consistency and prevents unintended side effects.
Imagine a chef preparing a dish. If the recipe is idempotent, repeating the steps (applying the recipe again) won’t change the final dish, even if some steps have already been executed. This is crucial in infrastructure management because it allows you to safely re-run configurations without worrying about unexpected changes or errors. Non-idempotent actions, on the other hand, might lead to accumulating changes or even damage, much like repeatedly adding more salt to a dish than the recipe calls for.
Ensuring idempotency in your configuration management scripts is achieved through careful design and using appropriate tools and techniques. For example, in Puppet, using resources with proper declaration and ensuring that they correctly handle the “ensure” parameter will guarantee idempotency. Ansible, by its nature, tends towards idempotency in its module design, though it’s vital to always ensure the modules themselves adhere to the principle.
Q 7. How do you troubleshoot failed Puppet runs?
Troubleshooting failed Puppet runs involves a systematic approach, utilizing several key techniques:
- Examine the Puppet logs: The Puppet master and agent logs provide detailed information about the failure, including error messages and the resources that failed to be applied. Look for specific error messages and trace the execution path to the source of the problem.
- Check the Puppet agent’s status: Verify the status of the Puppet agent on the affected node. It may have encountered network issues or other problems that prevented it from communicating with the master.
- Inspect the affected resources: Identify the specific Puppet resources that caused the failure. Examine their manifests to ensure they are correctly written and configured. Pay close attention to dependencies and resource relationships.
- Use the `puppet apply –verbose` command: To debug locally, you can use this command to simulate a Puppet run and get more verbose output for debugging purposes.
- Review the node’s configuration: Check if the affected node has any specific configurations or settings that might be conflicting with the Puppet manifests.
- Test changes in a staging environment: Prior to deploying changes in production, use staging environments to test any modifications to configurations and avoid production disruptions.
By following these steps, carefully inspecting logs, and iteratively narrowing down the problem, we can effectively diagnose and resolve failed Puppet runs, ensuring the stability and reliability of our infrastructure.
Q 8. Describe your experience with different Jenkins plugins.
Jenkins plugins extend its functionality dramatically. My experience spans a wide range, including essential plugins for source code management (like the Git plugin), build tools (Maven Integration plugin, Gradle plugin), testing frameworks (JUnit plugin), and deployment (Deploy to container Plugin, Deploy to application server plugin). I’ve also used plugins for artifact management (Artifactory plugin, Nexus plugin), code analysis (SonarQube plugin), and notification (Email-ext plugin, Slack Notification plugin). For example, in a recent project, we used the Pipeline plugin to create a highly customizable and reusable CI/CD pipeline, leveraging the Groovy DSL for complex build logic. The Pipeline plugin, along with the Git plugin, allowed us to automate the entire process from code commit to deployment, drastically reducing manual effort and increasing the frequency of releases. Another instance involved using the Kubernetes plugin for automating deployments to a Kubernetes cluster, simplifying the process significantly.
Selecting the right plugins is critical. I always consider factors like maintainability, security, and community support before integrating a plugin into a Jenkins instance. Poorly maintained plugins can introduce vulnerabilities and hinder the stability of the CI/CD pipeline.
Q 9. How do you manage secrets in your CI/CD pipeline?
Managing secrets securely is paramount. Simply hardcoding passwords or API keys directly into scripts is extremely risky. My preferred approach leverages Jenkins Credentials Binding plugin. This allows you to store sensitive data securely within Jenkins, and then reference them in your build jobs without ever exposing the actual values in scripts. This ensures that even if someone gains access to your build files, they won’t have the necessary credentials.
For more complex scenarios, particularly in multi-stage pipelines or when dealing with numerous secrets, I often integrate with dedicated secrets management tools like HashiCorp Vault or AWS Secrets Manager. These tools provide robust features like encryption at rest and transit, access control, and audit logging. The integration would typically involve fetching the secrets from the management tool during the pipeline execution and using environment variables to pass them to the build steps. This ensures centralized management and better auditing capabilities.
Example (Jenkinsfile with Vault integration):
withCredentials([vaultSecret(secret: 'my-secret', secretName: 'my-secret-name')]) {
env.API_KEY = credentials('my-secret').secret
// Use API_KEY in your build steps
}Q 10. What are the best practices for managing configuration files?
Configuration management is crucial for consistency and repeatability. Best practices include using a version control system (like Git) to track all configuration files, leveraging configuration management tools (like Puppet or Ansible) for automated deployment and management, and employing a structured approach to organizing configuration files. This means avoiding hardcoded values wherever possible and instead using environment variables or external configuration files.
For example, I often utilize a combination of a central configuration repository and environment-specific overrides. This allows me to maintain a single source of truth while adapting configurations to different environments (development, testing, production). This approach also facilitates easier rollbacks – if a problem arises in production, reverting to the previous configuration is simplified. The use of templating engines (e.g., Jinja2) further helps in managing complex configurations effectively, allowing for parameterized configurations and reducing redundancy.
Q 11. Explain different approaches to handling dependencies in Puppet manifests.
Puppet uses various approaches to manage dependencies between resources. The most common is using the require and before metaparameters. require establishes a hard dependency; the resource will not be processed until the required resource is successfully managed. before defines a soft dependency; the resource will be processed before the dependent resource but the success of the before resource isn’t strictly enforced.
Another approach is utilizing classes and defining dependencies between them. Classes encapsulate related resources and improve modularity. A class can declare dependencies on other classes using the require keyword, ensuring a proper order of execution. Finally, Puppet’s catalog compilation automatically handles many dependencies, but explicit dependency management helps improve predictability and error detection.
Example:
class apache {
package { 'httpd': ensure => installed }
service { 'httpd': ensure => running }
}
class mysql {
package { 'mysql-server': ensure => installed }
service { 'mysql': ensure => running }
}
class webapp {
require Class['apache']
require Class['mysql']
# ... webapp resources
}Q 12. How do you implement rollback strategies in your deployments?
Robust rollback strategies are critical for mitigating deployment failures. My approach typically involves versioning deployments (e.g., using Git tags or semantic versioning) and automating the rollback process. This often involves maintaining a history of deployed configurations. In simpler scenarios, simply reverting to the previous configuration or the previous deployment artifact might suffice. This can be easily done with infrastructure-as-code tools and version control.
For more complex deployments (especially in microservices architectures), a blue-green or canary deployment strategy is beneficial. Blue-green involves maintaining two identical environments (blue and green), deploying to one, and switching traffic only after validation. Canary deployments gradually roll out the new version to a small subset of users, allowing for early detection and mitigation of issues before a full-scale rollout. These strategies require more infrastructure, but their reliability surpasses simpler methods. Automated rollback scripts and procedures are essential for speed and efficiency.
Q 13. What are some common challenges in implementing CI/CD?
Implementing CI/CD comes with its challenges. One common hurdle is integrating disparate systems. Connecting source code management, build tools, testing frameworks, and deployment environments seamlessly can be complex. Another significant challenge is managing dependencies. Untracked or poorly managed dependencies can break builds and deployments unpredictably. Ensuring proper testing across different environments is also a common challenge, particularly when handling complex configurations or intricate infrastructure.
Furthermore, maintaining consistent configurations across environments (dev, test, prod) requires careful planning and automation. Security is another critical area. Securing credentials and managing access control throughout the pipeline is crucial. Finally, achieving continuous integration and delivery requires a cultural shift. Development teams need to adopt practices like frequent commits, automated testing, and continuous feedback to fully benefit from a CI/CD pipeline.
Q 14. Describe your experience with monitoring and logging in a DevOps environment.
Monitoring and logging are crucial for maintaining the health and stability of a DevOps environment. I typically employ a combination of tools and strategies for effective monitoring and logging. For instance, I’d use centralized logging solutions like Elasticsearch, Fluentd, and Kibana (the ELK stack) or the more modern Elastic Stack to collect and analyze logs from various sources, such as application servers, databases, and infrastructure components. This offers a comprehensive view of system performance and aids in identifying bottlenecks or errors quickly.
For infrastructure monitoring, tools such as Prometheus, Grafana, and Nagios are commonly used to track key metrics, such as CPU usage, memory consumption, network traffic, and disk I/O. These metrics provide insights into system health and resource utilization. Alerting mechanisms are crucial; I set up alerts based on predefined thresholds to proactively notify the team about potential issues. Combining log analysis and infrastructure monitoring paints a complete picture of system behavior and allows for proactive problem-solving. The key is to establish comprehensive dashboards and alerting systems that provide real-time visibility into the health and performance of the DevOps environment.
Q 15. Explain how you ensure security in your configuration management practices.
Security in configuration management is paramount. It’s not just about securing the tools themselves, but the entire process, from code to production. My approach is multi-layered and incorporates several key strategies.
- Least Privilege: I strictly adhere to the principle of least privilege. This means users and processes only have access to the resources absolutely necessary for their tasks. This minimizes the impact of potential breaches. For example, in Puppet, I’d use role-based access control (RBAC) to restrict what users can modify.
- Secure Configuration Repositories: My configuration files are stored in secure repositories like Git, using appropriate access controls. We use SSH keys instead of passwords for authentication and employ code review to ensure security best practices are followed in the configuration itself.
- Encryption: Sensitive data, like passwords or API keys, are never stored directly in configuration files. Instead, we use secure secrets management systems such as HashiCorp Vault or AWS Secrets Manager, integrating them with our CI/CD pipeline.
- Regular Audits and Penetration Testing: We regularly audit our configuration management practices and conduct penetration testing to identify vulnerabilities and improve our security posture. This isn’t just about finding holes; it’s about understanding how attackers might try to exploit them.
- Immutable Infrastructure: I strongly favor immutable infrastructure. This minimizes the attack surface by creating new servers instead of modifying existing ones, ensuring a consistent and known configuration. Any issues are resolved by deploying a new, corrected instance.
For instance, in a recent project, we discovered a potential vulnerability in our Puppet manifests that could allow unauthorized modification. Through thorough code review and penetration testing, we were able to identify and remediate this vulnerability before it caused any real damage.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. How do you handle parallel deployments in Jenkins?
Handling parallel deployments in Jenkins efficiently requires careful planning and the use of appropriate plugins. Simply running multiple jobs concurrently can lead to conflicts and instability. My approach involves:
- Jenkins Pipeline: I leverage Jenkins Pipelines to orchestrate deployments. Pipelines allow for the definition of complex deployment stages, including parallel execution of tasks.
- Parameterized Builds: Parameters allow for flexible deployment targeting. Different environments (dev, test, prod) can be deployed to simultaneously, but each in its isolated space.
- Multibranch Pipelines: These pipelines automatically create and manage pipelines for different branches, enabling parallel deployments from various development branches without conflicts.
- Resource Management: Jenkins plugins provide control over node allocation for parallel jobs to prevent resource contention. We ensure sufficient resources (CPU, memory) are available for each parallel deployment.
- Deployment Strategies: We use deployment strategies like blue/green or canary deployments to further mitigate risk. These strategies allow for gradual rollout and easy rollback if something goes wrong in one of the parallel deployments.
pipeline { agent any stages { stage('Deploy to Dev') { parallel { stage('Deploy to Staging') { //Parallel deployment to separate environments } stage('Deploy to Prod') { //Parallel deployment to separate environments } } } } }
This example shows a simplified pipeline using parallel stages for simultaneous deployments to different environments. Each stage would contain the specific steps for deploying to that environment.
Q 17. What are some common anti-patterns to avoid in configuration management?
Several anti-patterns can sabotage your configuration management efforts. Avoiding them is crucial for maintainability and reliability. Here are a few common ones:
- Configuration Drift: This happens when the actual state of a system diverges from its desired configuration. This leads to inconsistencies and makes troubleshooting difficult. We actively combat this using techniques like automated audits and infrastructure-as-code.
- Hardcoding Values: Embedding sensitive information directly in configuration files is a major security risk. Always use secrets management systems and parameterized builds instead.
- Overly Complex Manifests or Scripts: Large, convoluted scripts make configuration management difficult to maintain and understand. We strive for modularity, reusability, and clear documentation.
- Lack of Version Control: Not using version control for configuration files is unthinkable. It prevents tracking changes, rollback capabilities, and collaboration.
- Ignoring Testing: Insufficient testing (unit, integration, and system testing) increases the risk of deployment failures and creates instability. Robust testing is an integral part of our workflow.
- One-size-fits-all Approach: Trying to use a single configuration for multiple environments often leads to problems. Employ environment-specific configurations and parameterized builds.
Imagine a scenario where a developer hardcodes a database password directly into a Puppet manifest. This is a severe security risk and is easily avoided by using a secrets management solution.
Q 18. Explain your experience with different testing strategies in CI/CD.
Testing is a crucial component of any effective CI/CD pipeline. My experience encompasses several testing strategies:
- Unit Testing: These tests verify individual components or modules of the application. I use frameworks like JUnit (for Java) or pytest (for Python) to create and run these tests.
- Integration Testing: These tests check the interaction between different components or modules. We frequently employ mocking and stubbing techniques to isolate the components under test.
- System Testing (End-to-End): These tests verify the entire system, from the user interface to the database. This can include UI testing with Selenium or Cypress.
- Performance Testing: Tools like JMeter or Gatling are used to assess the performance and scalability of the application under different load conditions.
- Security Testing: Regular security scans (static and dynamic code analysis) and penetration testing are essential to identify and mitigate security vulnerabilities.
In a recent project, we implemented a comprehensive test suite using a combination of unit, integration, and system tests. This drastically reduced the number of bugs reaching production and improved the overall quality of our software.
Q 19. How do you ensure your configuration management is scalable and maintainable?
Scalability and maintainability are key considerations in configuration management. Achieving these requires a well-structured approach:
- Modular Design: Break down configurations into reusable modules. This promotes code reuse, reduces redundancy, and simplifies maintenance.
- Version Control: Using Git (or a similar system) is essential for tracking changes, collaborating with colleagues, and easily rolling back to previous versions.
- Infrastructure as Code (IaC): Tools like Terraform or CloudFormation allow for automated provisioning and management of infrastructure, enhancing scalability and consistency.
- Automated Testing: Regular automated testing helps ensure the integrity and stability of configurations as the system grows.
- Documentation: Comprehensive documentation is essential for understanding, maintaining, and extending the configuration management system.
- Idempotency: Ensure configurations are idempotent, meaning that applying them multiple times yields the same result. This is crucial for both scalability and consistency. This prevents unintentional overwrites or disruptions to the system
For example, instead of manually configuring servers, we use Terraform to provision and manage them automatically. This makes adding new servers or scaling the system incredibly simple.
Q 20. Describe your experience with different deployment strategies (e.g., blue/green, canary).
Different deployment strategies offer various trade-offs in terms of risk, downtime, and complexity. My experience includes:
- Blue/Green Deployments: Maintain two identical environments (blue and green). Deploy the new version to the green environment, then switch traffic once testing is complete. Minimal downtime and easy rollback.
- Canary Deployments: Gradually roll out the new version to a small subset of users. Monitor performance and behavior before deploying to the entire user base. Minimizes risk of widespread issues.
- Rolling Deployments: Incrementally update instances one by one. Minimizes downtime but requires careful monitoring during the rollout.
- A/B Deployments: Route a portion of traffic to the new version while the rest continues using the old version. Allows for direct comparison of the two versions.
The choice of deployment strategy depends on factors like application complexity, risk tolerance, and downtime constraints. For a critical application, a blue/green or canary deployment might be preferable to minimize the impact of potential issues.
Q 21. How do you handle configuration drift?
Configuration drift is a persistent challenge. Addressing it proactively is crucial for maintaining system stability and reliability. My approach involves:
- Automated Configuration Audits: Regularly compare the desired state (defined in configuration management tools) with the actual state of the system. Tools within Puppet or Chef can automatically check this. Any discrepancies indicate drift.
- Infrastructure as Code (IaC): Using IaC minimizes drift because the desired state is explicitly defined in code. Changes are managed and tracked effectively.
- Configuration Management Tools: Leverage the built-in features of tools like Puppet or Chef to enforce the desired state and report any deviations. This can be accomplished through Puppet’s reporting features, for example.
- Continuous Monitoring: Implement continuous monitoring to detect changes to the system that aren’t reflected in the configuration management system. This can indicate drift or unauthorized modifications.
- Automated Remediation: Where possible, automate the remediation of configuration drift. This can be done through automated scripts or tools that automatically correct deviations from the desired state.
For example, if an audit reveals that a particular server’s package versions don’t match the defined configuration, I might use a Puppet agent to automatically update the packages, bringing the server back into compliance.
Q 22. How do you manage infrastructure provisioning using tools like Terraform or CloudFormation?
Infrastructure provisioning tools like Terraform and CloudFormation allow us to define and manage our infrastructure as code (IaC). Instead of manually configuring servers, networks, and other resources, we write declarative code that describes the desired state. These tools then automate the process of creating and updating that infrastructure.
Terraform, for example, uses a HashiCorp Configuration Language (HCL) to define resources. You define your infrastructure in a series of `.tf` files, and Terraform handles the provisioning across various cloud providers (AWS, Azure, GCP) or on-premises environments. A simple example might be creating an EC2 instance:
resource "aws_instance" "example" {ami = "ami-0c55b31ad2299a701"; instance_type = "t2.micro"}CloudFormation, AWS’s own IaC tool, utilizes YAML or JSON templates to define stacks of resources. It’s deeply integrated with the AWS ecosystem, offering fine-grained control over AWS services. Both tools support version control, allowing for tracking changes, collaboration, and rollbacks. The key benefit is consistency, reproducibility, and automation, reducing manual errors and improving deployment speed.
In a recent project, we used Terraform to provision a multi-region Kubernetes cluster. By defining the cluster’s components – nodes, master nodes, networking – in code, we ensured consistency across regions and simplified deployments, scaling, and updates significantly. The ability to version control our infrastructure definitions allowed for easier troubleshooting and rollback in case of errors.
Q 23. Explain your understanding of GitOps.
GitOps is a way of managing infrastructure and applications using Git as the single source of truth. Essentially, all changes to your infrastructure are treated as code, tracked in a Git repository, and deployed automatically. This approach promotes collaboration, auditing, and automation. It leverages Git’s features like branching, merging, and pull requests to manage and review infrastructure changes.
Think of it like this: instead of manually making changes to your production servers, you create a pull request updating the infrastructure configuration files in Git. After review and approval, a CI/CD pipeline automatically applies those changes to your infrastructure, either directly or through tools like Argo CD or FluxCD. This allows for easy rollback and auditing of changes through Git history. Observability and traceability are naturally built-in.
A key aspect is the use of a declarative approach; you define the desired state in your Git repository, and the GitOps tool manages the process of bringing your current infrastructure in line with that defined state. This simplifies the complexity of managing your infrastructure at scale, whilst ensuring reproducibility and consistency.
Q 24. How do you approach automating infrastructure testing?
Automating infrastructure testing is crucial for ensuring reliability and stability. My approach involves a multi-layered strategy, encompassing unit, integration, and system tests.
- Unit Tests: These verify individual components, like a Terraform module or a specific CloudFormation resource. We use tools like Terratest for Terraform and various AWS SDKs for CloudFormation testing.
- Integration Tests: These focus on interactions between components. For instance, we might test the communication between a load balancer and the backend servers provisioned via Terraform. We often leverage tools that automate the testing process and report on the results.
- System Tests: These are end-to-end tests that verify the entire infrastructure meets the specified requirements. They often involve simulating real-world scenarios and using tools like Ansible or Chef to perform checks and validations.
We also incorporate infrastructure-as-code (IaC) scanning tools to detect potential vulnerabilities or compliance issues early in the development cycle. Continuous integration and continuous deployment (CI/CD) pipelines integrate these tests to ensure they are run automatically with every code change.
In a past project, we implemented a comprehensive testing suite for a multi-cloud setup. This involved writing unit tests for individual Terraform modules that defined resources in both AWS and Azure, integration tests that checked cross-cloud communication, and system tests that verified the entire application was functioning correctly across both cloud providers. This significantly reduced the risk of deployment failures.
Q 25. What are your preferred methods for managing infrastructure logs?
Managing infrastructure logs efficiently is paramount for troubleshooting and monitoring. My preferred methods involve a centralized logging solution, combining various tools and techniques.
- Centralized Log Management: We typically use a centralized logging platform like Elasticsearch, Fluentd, and Kibana (the ELK stack) or similar solutions like Splunk or Graylog. This allows us to aggregate logs from various sources – servers, applications, and infrastructure components – into a single location for analysis.
- Log Aggregation from Multiple Sources: We use agents or forwarders on our servers and applications to collect and send logs to the central repository. This simplifies the process of analyzing logs from disparate sources.
- Log Rotation and Retention Policies: We establish clear policies for log rotation and retention to manage storage space and ensure only relevant logs are kept.
- Structured Logging: We encourage structured logging, using formats like JSON, to facilitate efficient searching, filtering, and analysis. This makes finding specific information in the log files far easier.
A well-structured logging system greatly simplifies troubleshooting. When an issue arises, we can quickly analyze relevant logs to pinpoint the root cause and take corrective action. In one recent project, our centralized logging system helped us quickly identify and resolve a network connectivity problem by analyzing network logs and server logs simultaneously.
Q 26. Describe your experience with integrating configuration management with monitoring tools.
Integrating configuration management with monitoring tools is essential for achieving comprehensive observability and proactive issue management. This integration enables automated alerts, real-time insights into infrastructure health, and improved response times.
For example, we might use Puppet or Chef to manage the configuration of servers, ensuring that specific software packages and settings are in place. Simultaneously, we utilize monitoring tools like Prometheus, Grafana, or Datadog to track key metrics such as CPU utilization, memory usage, and network traffic on those servers. The integration can involve using custom scripts or plugins that fetch data directly from the configuration management tools or relying on the monitoring tools’ native capabilities to monitor infrastructure elements defined in IaC.
We can then create alerts triggered when specific thresholds are exceeded, for instance, a high CPU utilization or a failed service check. This proactive approach allows for quicker issue resolution and avoids potential service disruptions. In a recent project, we integrated Puppet with Nagios. When Puppet detected a configuration drift, it triggered an alert in Nagios, allowing the operations team to promptly address the issue.
Q 27. How would you handle a production outage caused by a configuration management issue?
Handling a production outage caused by a configuration management issue requires a swift and methodical response. My approach follows these steps:
- Immediate Mitigation: The first priority is to contain the outage and restore service. This might involve reverting to a previous known good configuration using version control systems and rollback mechanisms built into our CI/CD pipelines. Our infrastructure-as-code tools such as Terraform and CloudFormation allows for quick rollbacks.
- Root Cause Analysis: Once service is restored, a thorough investigation is conducted to identify the root cause of the outage. This involves reviewing logs, configuration changes, and alerts. We utilize our monitoring systems to track down any potential underlying issues.
- Incident Postmortem: A postmortem meeting is held with relevant teams to analyze the incident, identify areas for improvement, and prevent recurrence. This should include documentation of the event and detailed steps taken.
- Process Improvement: Based on the postmortem findings, changes are made to our processes and tools to prevent similar incidents in the future. This might involve strengthening testing procedures, improving alerting mechanisms, or updating our operational guidelines.
During a real production outage, calm and systematic action is crucial. Clear communication across teams, robust monitoring tools, and well-defined incident management processes are key to minimizing downtime and preventing future occurrences.
Key Topics to Learn for DevOps Configuration Management Tools (e.g., Jenkins, Puppet) Interview
- Jenkins Fundamentals: Understanding Jenkins architecture, pipeline creation (declarative and scripted), plugin management, and best practices for build automation.
- Jenkins Practical Application: Building and deploying applications using Jenkins pipelines, integrating with version control systems (Git), and implementing continuous integration/continuous delivery (CI/CD) workflows.
- Puppet Core Concepts: Grasping Puppet’s declarative approach to infrastructure management, understanding manifests, modules, and catalogs, and working with Puppet’s resource abstraction.
- Puppet in Practice: Configuring servers and deploying applications using Puppet, managing infrastructure as code (IaC), and troubleshooting common Puppet issues.
- Version Control & Collaboration: Efficiently using Git for code management within your CI/CD pipelines. Understanding branching strategies and collaborative workflows.
- Configuration Management Best Practices: Implementing idempotency, ensuring scalability and maintainability of your configurations, and understanding security considerations.
- Troubleshooting & Problem Solving: Develop your ability to diagnose and resolve issues related to build failures, configuration drift, and deployment problems in CI/CD pipelines.
- Cloud Integration: Understanding how to integrate your configuration management tools with cloud platforms (AWS, Azure, GCP) for automated deployments and infrastructure provisioning.
- Monitoring and Logging: Implementing robust monitoring and logging to track the health and performance of your CI/CD pipelines and managed infrastructure.
Next Steps
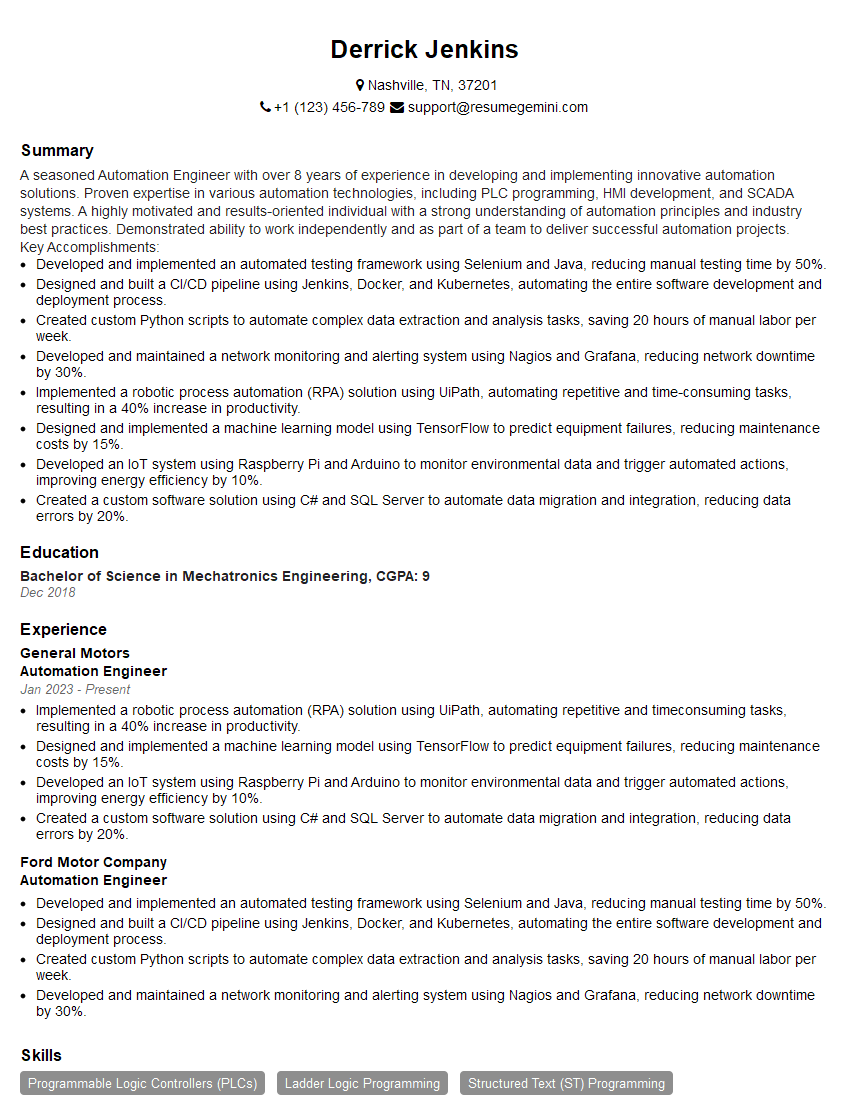
Mastering DevOps Configuration Management tools like Jenkins and Puppet is crucial for accelerating your career in the dynamic field of DevOps. These skills are highly sought after, demonstrating your ability to automate processes, improve efficiency, and enhance the reliability of software delivery. To maximize your job prospects, it’s vital to present your skills effectively. Creating an ATS-friendly resume is key to getting your application noticed. ResumeGemini is a trusted resource that can help you build a professional and impactful resume, highlighting your expertise in DevOps Configuration Management. Examples of resumes tailored to DevOps Configuration Management Tools (e.g., Jenkins, Puppet) are available to guide you.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good