Unlock your full potential by mastering the most common Ability to Conduct Investigations interview questions. This blog offers a deep dive into the critical topics, ensuring you’re not only prepared to answer but to excel. With these insights, you’ll approach your interview with clarity and confidence.
Questions Asked in Ability to Conduct Investigations Interview
Q 1. Describe your experience conducting thorough background checks.
Conducting thorough background checks involves systematically gathering and verifying information about an individual to assess their suitability for a particular role or to understand their past activities. This goes beyond simply reviewing a resume; it requires accessing and analyzing various data sources to paint a comprehensive picture.
My experience encompasses using a variety of methods, including:
- Online Searches: Utilizing search engines, social media platforms (LinkedIn, Facebook, etc.), and public records databases to uncover publicly available information.
- Criminal Record Checks: Accessing national and local databases to identify any criminal convictions or pending charges. I understand the nuances of interpreting these records, considering expungements and sealed records appropriately.
- Credit Reports: Reviewing credit history to gauge financial responsibility. This isn’t about judging someone’s financial situation, but assessing potential risk factors relevant to the specific investigation.
- Reference Checks: Contacting previous employers and professional references to verify employment history, job performance, and character. I employ structured interview techniques to elicit unbiased and valuable feedback.
- Education Verification: Contacting educational institutions to confirm degrees and certifications claimed by the candidate.
For instance, in one case, a candidate’s resume claimed extensive international experience. My background check revealed discrepancies in their claimed dates of employment, leading to further investigation that uncovered significant inaccuracies.
Q 2. Explain your process for gathering and verifying evidence.
Gathering and verifying evidence is a meticulous process requiring a systematic approach. It’s like building a case, piece by piece, ensuring each piece is solid and verifiable.
My process involves:
- Identifying Potential Sources: This includes witnesses, documents, physical evidence, digital data, and expert opinions relevant to the investigation.
- Gathering Information: Employing appropriate methods for acquiring evidence – this might involve interviews, document reviews, site visits, forensic analysis, or data acquisition.
- Verifying Information: This is crucial. I cross-reference information from multiple sources, corroborating facts and seeking independent verification wherever possible. For example, I might verify a witness’s statement by reviewing security footage or other supporting documents.
- Documenting Evidence: Maintaining a detailed chain of custody for physical evidence and a thorough record of all information gathered, including dates, times, sources, and methods of acquisition. This adheres to strict legal and ethical standards.
- Analyzing Evidence: Assessing the credibility and relevance of each piece of evidence in the context of the overall investigation. This often requires careful interpretation and critical thinking.
For example, in a fraud investigation, I once cross-referenced financial records with employee time sheets and emails, revealing a pattern of falsified expense reports.
Q 3. How do you prioritize tasks in a complex investigation?
Prioritizing tasks in a complex investigation requires a strategic approach that balances urgency, importance, and available resources. I use a risk-based prioritization framework.
My approach involves:
- Identifying Key Objectives: Clearly defining the goals of the investigation, breaking down the overall objective into smaller, manageable tasks.
- Assessing Risk: Evaluating the potential impact of each task on the overall investigation. High-risk tasks, those with the potential for significant consequences if not addressed promptly, get priority.
- Resource Allocation: Considering the resources (time, personnel, budget) available to complete each task. I balance the urgency of a task with the resources needed to complete it effectively.
- Time Management: Developing a realistic timeline for completing the investigation. Using project management tools and techniques to track progress and adjust priorities as needed.
- Regular Review and Adjustment: Continuously monitoring progress, re-evaluating priorities as new information emerges, and adapting the plan accordingly.
Think of it like firefighting: you address the most immediate threats first (high-risk, high-impact) before tackling smaller issues.
Q 4. What techniques do you use to interview witnesses effectively?
Effective witness interviews are crucial for gathering accurate and reliable information. I utilize techniques that build rapport, encourage open communication, and minimize bias.
My techniques include:
- Preparation: Thoroughly researching the witness and the relevant facts before the interview. This allows me to ask informed and targeted questions.
- Building Rapport: Creating a comfortable and non-judgmental atmosphere to encourage the witness to share information freely. This involves active listening and demonstrating empathy.
- Open-Ended Questions: Using open-ended questions that prompt detailed responses rather than simple “yes” or “no” answers.
- Active Listening: Paying close attention to both verbal and non-verbal cues, clarifying ambiguous statements, and summarizing key points to ensure understanding.
- Follow-up Questions: Asking probing questions to clarify inconsistencies or explore details further.
- Note-Taking: Maintaining detailed notes of the interview, including direct quotes and observations about the witness’s demeanor.
For example, I might start an interview by explaining the purpose of the investigation and assuring the witness of confidentiality (where applicable), creating a foundation of trust.
Q 5. How do you handle conflicting information during an investigation?
Conflicting information is common in investigations. Handling it requires careful analysis, verification, and a commitment to finding the truth. It’s like solving a puzzle with some missing or contradictory pieces.
My approach involves:
- Identifying the Discrepancies: Carefully reviewing all information to pinpoint areas of conflict.
- Analyzing the Sources: Evaluating the credibility and reliability of each source of information. Consider factors such as bias, motivation, and memory reliability.
- Seeking Additional Evidence: Gathering more evidence to resolve the discrepancies. This may involve interviewing additional witnesses, reviewing documents, or conducting further analysis.
- Reconciling the Differences: Attempting to find common ground or explanations for the inconsistencies. Sometimes, seemingly conflicting information can be reconciled by finding a deeper truth.
- Documenting All Information: Clearly documenting all conflicting information and the steps taken to resolve the discrepancies. Transparency in this process is vital.
I might, for instance, find that two witnesses offer different accounts of an event. By reviewing security footage and corroborating with other evidence, I might uncover that one witness’s perspective was limited or influenced by bias.
Q 6. Describe your experience with data analysis in investigations.
Data analysis plays a critical role in modern investigations, enabling the identification of patterns, anomalies, and correlations that might otherwise be missed. It’s like having a powerful magnifying glass for uncovering hidden connections.
My experience includes:
- Data Extraction and Cleaning: Gathering data from various sources (databases, spreadsheets, logs) and cleaning it to ensure accuracy and consistency.
- Statistical Analysis: Employing statistical methods to identify trends, outliers, and relationships within the data.
- Data Visualization: Creating charts, graphs, and other visualizations to effectively communicate findings.
- Data Mining Techniques: Using data mining algorithms to discover hidden patterns and insights within large datasets.
- Specific Software: Proficiency in using various data analysis tools, including SQL, statistical packages (like R or SPSS), and data visualization software.
In one case, I used data analysis to identify fraudulent transactions by analyzing patterns in large financial datasets, uncovering anomalies that pointed to specific individuals involved in the scheme.
Q 7. How do you maintain objectivity and impartiality during an investigation?
Maintaining objectivity and impartiality is paramount in conducting credible investigations. It’s about letting the facts guide the conclusions, not letting personal biases or preconceived notions cloud judgment. It’s akin to being a judge in a courtroom.
My approach focuses on:
- Awareness of Biases: Recognizing my own potential biases and actively working to mitigate their influence on my investigations.
- Evidence-Based Reasoning: Focusing solely on the evidence gathered during the investigation, rather than relying on assumptions or speculation.
- Fair and Impartial Procedures: Following established procedures and protocols to ensure fairness and equity in the investigation.
- Open-mindedness: Remaining open to alternative explanations and perspectives, even if they contradict initial assumptions.
- Seeking External Review: When appropriate, seeking input from colleagues or external experts to validate findings and ensure objectivity.
For example, if I have a strong suspicion about a particular individual’s involvement, I consciously avoid focusing solely on that individual, instead systematically examining all potential leads and evidence to ensure a fair and thorough investigation.
Q 8. Explain your understanding of legal and ethical considerations in investigations.
Legal and ethical considerations are paramount in any investigation. They form the bedrock upon which the entire process rests, ensuring fairness, accuracy, and adherence to the law. Legally, we must always operate within the bounds of applicable laws and regulations, which vary depending on jurisdiction and the nature of the investigation (e.g., data privacy laws like GDPR or HIPAA, employment laws, criminal codes). This includes obtaining proper authorization before accessing data or interviewing individuals, respecting individual rights (like the right to remain silent), and ensuring evidence is collected and handled legally. Ethically, we’re guided by principles of integrity, objectivity, impartiality, and confidentiality. This means avoiding bias, conducting a thorough and unbiased investigation, protecting confidential information, and being transparent about the process, where appropriate. For instance, in a workplace misconduct investigation, I would ensure all parties involved are treated fairly, given opportunities to present their side of the story, and that any disciplinary actions are consistent with company policy and legal requirements. Failure to adhere to these principles can lead to legal repercussions, reputational damage, and compromised integrity of the investigation.
Q 9. How do you document your findings and conclusions?
Meticulous documentation is crucial for the credibility and defensibility of any investigation. My approach involves creating a comprehensive and auditable trail of all activities. This typically starts with a detailed case file, including initial reports, outlines of the investigation plan, and a log of all actions taken. Each interview, data source, or piece of evidence is carefully documented; I use detailed notes, recordings (with informed consent), and screenshots. I maintain a chain of custody for physical evidence, ensuring its integrity. Findings are presented in a clear, concise, and objective report, using evidence to support all conclusions. The report typically includes an executive summary, a methodology section detailing the investigation process, a presentation of the evidence, analysis of that evidence, and the conclusions drawn. For example, if I found evidence of fraud, the report would detail the methods used to detect the fraud, the evidence supporting that finding (e.g., financial documents, email exchanges), and analysis explaining how the evidence proves the fraudulent activity. The entire process is designed to withstand scrutiny, and any potential legal challenges.
Q 10. Describe a time you had to overcome a significant obstacle in an investigation.
During an investigation into a complex data breach, I encountered a significant obstacle: the encryption of critical server logs. The hackers had encrypted the logs, rendering standard forensic techniques useless. Overcoming this required a multi-faceted approach. First, I consulted with cybersecurity experts to explore different decryption techniques, including brute-force and known-vulnerability exploits. Simultaneously, I broadened my scope, focusing on less-encrypted data sources like network traffic logs and user activity logs. Through careful correlation of data from various sources, we were able to piece together a significant portion of the attacker’s actions, even without the decrypted server logs. This highlighted the importance of a flexible approach and the ability to adapt investigative techniques based on the challenges encountered. The final report successfully identified the breach vector and the extent of the data compromise, despite the initial setback.
Q 11. How do you handle sensitive and confidential information?
Handling sensitive and confidential information requires the utmost care and adherence to strict protocols. I always operate within the framework of applicable privacy laws and company policies. Access to sensitive data is strictly controlled, and only authorized personnel with a need-to-know basis are granted access. Data is encrypted both in transit and at rest, using industry-standard encryption methods. Secure storage systems are used, and physical security measures are employed to protect sensitive documents and devices. All investigations are conducted with respect for privacy; individuals are informed about the investigation’s purpose and the use of their data. I maintain detailed logs of all access to sensitive information. In the event of a data breach, I would follow established incident response plans, promptly notifying relevant authorities and stakeholders. Treating sensitive data with this level of care is critical to maintaining trust and complying with the law.
Q 12. What software or tools are you proficient in using for investigations?
My proficiency extends to various software and tools used in investigations. I’m adept at using forensic software like EnCase and FTK for data recovery and analysis. I’m also experienced with network monitoring and analysis tools such as Wireshark, and security information and event management (SIEM) systems like Splunk and QRadar for log analysis. For data visualization and reporting, I utilize tools such as Tableau and Power BI. Proficiency in scripting languages like Python is invaluable for automating tasks and developing custom analysis tools. Furthermore, I am comfortable using cloud-based investigation platforms and collaborating effectively using secure communication and file-sharing tools.
Q 13. How do you identify and mitigate risks during an investigation?
Risk identification and mitigation are integral to a successful investigation. I begin by assessing potential risks early in the process, considering factors like data security breaches, legal challenges, reputational damage, and the emotional impact on individuals involved. I develop a risk mitigation plan that addresses each identified risk. This might involve implementing additional security measures, obtaining legal counsel, establishing communication protocols with stakeholders, or carefully managing the release of information. For example, if a risk assessment reveals a high likelihood of data leakage, the mitigation plan might include implementing stricter access controls, encrypting sensitive data, and conducting regular security audits. Regularly reviewing and updating the risk mitigation plan throughout the investigation ensures its effectiveness in adapting to changing circumstances. A proactive approach to risk management minimizes disruption and enhances the overall success of the investigation.
Q 14. Describe your experience with different types of investigative methodologies.
My experience encompasses a wide range of investigative methodologies, tailoring my approach to the specific nature of each case. I’m proficient in conducting interviews, using both structured and unstructured techniques, depending on the information needed and the interviewee’s cooperation level. I’m experienced in forensic data analysis, extracting evidence from various sources, including computers, mobile devices, and network infrastructure. I’ve employed surveillance techniques (where legally permissible), utilizing various technologies. Furthermore, I’ve conducted background checks, open-source intelligence (OSINT) gathering, and financial analysis, depending on the investigation’s requirements. My understanding of different investigative models, such as the scientific method and the investigative cycle, allows me to systematically approach each investigation, ensuring comprehensive and reliable results. The selection of specific methodologies always depends on the circumstances and the legal and ethical considerations involved.
Q 15. How do you ensure the accuracy and reliability of your findings?
Ensuring accuracy and reliability in investigations is paramount. It’s like building a strong house – you need a solid foundation. This foundation rests on several key pillars:
- Rigorous Methodology: I meticulously follow established investigative protocols. This involves a detailed plan outlining each step, from initial data collection to final analysis. For example, in a fraud investigation, this might include a timeline analysis, document review, witness interviews, and potentially forensic accounting.
- Multiple Sources of Evidence: I never rely on a single source. Corroborating information from multiple independent sources – witness testimonies, documents, databases, physical evidence – is crucial for verifying the accuracy of my findings. Think of it like triangulation in surveying – using multiple points to pinpoint a precise location.
- Chain of Custody: Maintaining a meticulous chain of custody for all evidence is essential. This ensures the integrity and admissibility of the evidence in any subsequent legal proceedings. Every step in the handling of evidence, from collection to analysis, is carefully documented.
- Data Validation and Verification: I employ robust data validation techniques to ensure the accuracy and completeness of the information gathered. This includes checking for inconsistencies, anomalies, and potential biases. In a financial investigation, this might involve cross-referencing data across multiple accounting systems.
- Peer Review (where applicable): When appropriate, I actively seek peer review of my findings to ensure objectivity and identify any potential blind spots in my analysis. A fresh pair of eyes can often identify subtle errors or biases that might otherwise go unnoticed.
By adhering to these principles, I maximize the accuracy and reliability of my investigative findings, providing a solid basis for informed decisions and action.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. What is your experience with report writing and presentation of findings?
I have extensive experience in crafting clear, concise, and compelling investigative reports. My reports are designed to be easily understood by a diverse audience, from technical experts to non-technical stakeholders. I’ve presented findings in various formats, adapting my approach to the specific audience and context.
- Structured Reporting: I utilize a structured approach to reporting, typically following a logical flow: introduction, methodology, findings, conclusions, and recommendations. This ensures clarity and facilitates easy comprehension.
- Visual Aids: I effectively incorporate visual aids like charts, graphs, and timelines to illustrate key findings and make complex information more accessible. Data visualization makes it easier to identify patterns and trends.
- Data Presentation: I’m adept at presenting data in a variety of formats, including spreadsheets, databases, and presentation software. I can tailor the format to best suit the audience and the type of data presented.
- Executive Summaries: I always include a concise executive summary that highlights the most critical findings and recommendations. This allows busy stakeholders to quickly grasp the essence of the investigation.
- Oral Presentations: I’m confident and experienced in presenting my findings orally, answering questions effectively, and engaging with the audience. I tailor my presentation style to the audience’s level of understanding.
For example, in one case, I presented a complex financial fraud scheme to a board of directors. By using clear visuals and concise language, I was able to successfully communicate the critical findings and secure their support for implementing remedial measures.
Q 17. How familiar are you with relevant legislation and regulations?
My understanding of relevant legislation and regulations is comprehensive and up-to-date. This knowledge is fundamental to conducting legally sound and ethically responsible investigations. I’m familiar with laws related to data privacy, evidence admissibility, and the rights of individuals involved in investigations.
- Data Privacy Laws (e.g., GDPR, CCPA): I’m well-versed in data privacy regulations and ensure all investigative activities comply with these laws. This includes obtaining appropriate consents, anonymizing data where necessary, and maintaining the confidentiality of sensitive information.
- Evidence Admissibility: I understand the rules of evidence and ensure that all evidence collected is admissible in court or other relevant proceedings. This includes proper chain of custody, documentation, and preservation of evidence.
- Legal Rights: I’m aware of the rights of individuals involved in investigations, including the right to legal counsel, the right to remain silent, and the right to due process. I ensure that all investigative activities respect these rights.
- Industry-Specific Regulations: My knowledge extends to industry-specific regulations relevant to the subject matter of the investigation. For instance, investigations in the financial sector require knowledge of banking regulations and securities laws.
- Ongoing Learning: I actively participate in continuing education to stay abreast of changes and updates in relevant legislation and regulations. This ensures my investigative work remains compliant and effective.
This deep understanding of legal frameworks enables me to navigate the complexities of investigations while adhering to the highest ethical standards.
Q 18. Describe your experience working independently and as part of a team.
I thrive in both independent and collaborative work environments. My experience demonstrates proficiency in both modes, allowing me to adapt seamlessly to various investigative needs.
- Independent Work: When working independently, I exhibit strong self-discipline, time management skills, and the ability to prioritize tasks effectively. I am comfortable taking ownership of projects from initiation to completion, independently managing resources and timelines. For example, I once conducted a thorough background check on a candidate entirely independently, adhering to strict deadlines and reporting protocols.
- Teamwork: As part of a team, I actively contribute, share knowledge, and collaborate effectively with diverse individuals. I believe in clear communication, mutual respect, and a shared commitment to achieving common goals. I’ve been a valuable member of several investigative teams where effective collaboration was crucial to uncovering complex scenarios.
- Communication: Irrespective of the work setting, I prioritize clear and concise communication. I ensure regular updates and transparent information sharing, maintaining stakeholders informed about progress and challenges.
My adaptability enables me to seamlessly integrate into different team dynamics and contribute meaningfully regardless of the work structure.
Q 19. How do you handle pressure and tight deadlines in an investigation?
Handling pressure and tight deadlines is an inherent aspect of investigative work. I approach these situations systematically and strategically.
- Prioritization: I prioritize tasks based on urgency and impact, focusing on critical aspects first. This ensures that the most important aspects of the investigation are addressed promptly.
- Time Management: I utilize effective time management techniques such as creating detailed timelines, setting realistic deadlines for each phase, and regularly monitoring progress. This ensures I stay on track and meet deadlines.
- Resource Management: I effectively manage resources, including personnel, technology, and information, to maximize efficiency and minimize delays. This includes delegating tasks appropriately and seeking assistance when necessary.
- Stress Management: I recognize the importance of self-care and utilize stress management techniques, such as regular breaks and mindful practices, to maintain focus and productivity under pressure. This helps prevent burnout and maintains efficiency.
- Flexibility and Adaptability: I’m flexible and adaptable, readily adjusting my approach to unexpected challenges or changes in circumstances. This allows me to effectively respond to evolving situations and maintain momentum.
In one instance, I was tasked with completing a critical investigation within a remarkably short timeframe. By prioritizing tasks, effectively managing my resources, and maintaining a calm and focused approach, I successfully delivered the findings on time and to the required standard.
Q 20. How do you stay updated on the latest investigative techniques and technologies?
Staying updated on the latest investigative techniques and technologies is a continuous process. It’s akin to a doctor constantly updating their medical knowledge – crucial for providing the best possible service.
- Professional Development: I actively participate in professional development activities, including workshops, conferences, and online courses, to stay abreast of the latest advancements in investigative methodologies and technologies. This includes attending conferences and webinars related to forensic accounting, digital forensics, and investigative techniques.
- Industry Publications: I regularly read industry publications, journals, and online resources to stay informed on emerging trends and best practices in investigation. This keeps me current on new software, data analysis techniques, and legal changes.
- Networking: I maintain a strong professional network by actively participating in industry events and connecting with other investigators. This allows for knowledge sharing and the exchange of best practices.
- Technology Exploration: I explore and experiment with new investigative technologies and software, assessing their potential applications to improve efficiency and effectiveness. This often involves researching and testing new data analysis tools and forensic software.
- Mentorship: I seek mentorship from experienced investigators to learn from their expertise and receive guidance on emerging trends and best practices.
This ongoing commitment to professional development ensures I’m equipped with the most current knowledge and tools, allowing me to conduct investigations effectively and efficiently.
Q 21. Describe your experience in analyzing financial records during an investigation.
Analyzing financial records is a core competency for me, requiring both technical expertise and a keen eye for detail. It’s like being a detective with a magnifying glass, scrutinizing numbers to uncover hidden patterns and anomalies.
- Data Extraction and Organization: I’m proficient in extracting and organizing financial data from various sources, including accounting software, databases, and physical documents. This includes using tools like SQL and specialized data analysis software.
- Data Reconciliation: I skillfully reconcile financial data across multiple sources to identify discrepancies and inconsistencies. This requires attention to detail and a methodical approach.
- Trend Analysis: I analyze financial trends and patterns to identify potential irregularities, fraud, or other financial misconduct. This might involve identifying unusual transactions, inconsistencies in accounting entries, or deviations from established norms.
- Forensic Accounting Techniques: I’m familiar with various forensic accounting techniques, including data mining, benford’s law, and other analytical methods to detect and investigate financial fraud. These advanced techniques allow for a more comprehensive analysis of financial data.
- Financial Statement Analysis: I can critically analyze financial statements, including balance sheets, income statements, and cash flow statements, to assess the financial health of an organization and detect potential issues. This provides a broader context for investigating specific transactions.
In one investigation, I uncovered a complex embezzlement scheme by analyzing bank statements, accounting records, and expense reports. My analysis revealed patterns of unusual transactions that led to the successful identification and prosecution of the perpetrator.
Q 22. How do you assess the credibility of sources and information?
Assessing source credibility is paramount in any investigation. It’s like being a detective sifting through clues – some are reliable, others misleading. My approach involves a multi-faceted assessment. I consider the source’s expertise: Are they an eyewitness, an expert in the field, or someone with a potential bias? I look at their motivation: Do they stand to gain or lose from providing specific information? I also scrutinize the consistency of their statements – do they align with other evidence, or are there contradictions? Finally, I examine the corroboration – can the information be verified through independent sources? For example, a witness’s account might be supported by CCTV footage, or an expert’s opinion might be backed by scientific literature.
- Expertise: A cybersecurity expert’s opinion on a data breach is more credible than a layperson’s.
- Motivation: A competitor might provide biased information about a company’s financial status.
- Consistency: Discrepancies in a witness’s statements raise red flags, requiring further investigation.
- Corroboration: A suspect’s confession corroborated by forensic evidence significantly strengthens the case.
Q 23. Explain your understanding of chain of custody procedures.
Chain of custody refers to the meticulous documentation of who has handled evidence from the moment it’s collected until it’s presented in court. Think of it like a relay race – every handoff needs to be recorded. Maintaining an unbroken chain of custody is vital to ensuring the evidence’s admissibility in court and prevents any claims of tampering or contamination. This process involves a detailed log, including the date, time, location, and individuals who handled the evidence. Each transfer is signed and witnessed, creating an auditable trail. For instance, if a piece of digital evidence is seized, the investigator will document its retrieval, secure storage (often in a tamper-evident bag), and any analysis performed, noting the exact date and time of each step. Failure to maintain a proper chain of custody can lead to the evidence being deemed inadmissible, severely undermining an investigation.
Q 24. How do you manage the time constraints involved in investigations?
Time constraints are a constant challenge in investigations. My strategy involves prioritizing tasks based on their urgency and importance, using a technique similar to project management. I begin by defining the scope of the investigation, setting realistic deadlines for each stage, and allocating resources accordingly. This might involve creating a detailed timeline, outlining key milestones, and potentially employing specialized tools for case management. I also leverage efficient techniques, such as interviewing multiple witnesses concurrently where appropriate and using technology like data analytics to accelerate data processing. Effective communication with stakeholders is key to managing expectations and preventing delays. In some cases, prioritizing certain lines of inquiry while acknowledging resource limitations is necessary.
Q 25. Describe your experience with forensic interviewing techniques.
Forensic interviewing techniques are crucial for obtaining reliable and admissible statements, especially from vulnerable individuals or children. My experience includes training in techniques that prioritize the interviewee’s well-being and minimize the risk of suggestibility. This involves creating a comfortable and safe environment, using open-ended questions, avoiding leading questions, and carefully documenting the interview. Active listening skills are paramount, focusing not only on the words spoken but also on the interviewee’s body language and emotional state. I also understand the importance of building rapport and establishing trust. For instance, in interviewing a child witness, I would focus on using age-appropriate language and taking breaks when needed to avoid overwhelming them. The goal is to obtain truthful and accurate information without traumatizing or influencing the witness.
Q 26. How do you deal with unexpected challenges that arise during an investigation?
Unexpected challenges are inevitable. My approach involves adapting my strategy on the fly, always maintaining a flexible mindset. This might involve seeking additional resources or expertise, re-evaluating the investigation’s scope, or altering the timeline. For example, if a key witness becomes unavailable, I’d explore alternative methods of obtaining information, like reviewing relevant documents or interviewing other potential witnesses. A crucial element is proactive risk assessment; anticipating potential obstacles helps formulate contingency plans. Maintaining open communication with stakeholders ensures collaboration and allows for informed decision-making in these unexpected situations.
Q 27. What are your strategies for identifying key witnesses in an investigation?
Identifying key witnesses is like finding the pieces of a jigsaw puzzle that reveal the whole picture. My strategies involve analyzing all available information to determine who possesses crucial knowledge about the case. This includes reviewing initial reports, witness statements, and physical evidence. Networking and collaboration with other investigators or law enforcement agencies are crucial in uncovering potential witnesses. Public records, social media, and other online resources can also provide valuable leads. Building trust and rapport with potential witnesses is also essential in encouraging cooperation and obtaining truthful accounts. Sometimes, a seemingly insignificant individual can hold a crucial piece of information. Careful consideration of potential motives and biases of every individual encountered is equally critical.
Q 28. Describe a situation where you had to adapt your investigative approach.
In one investigation involving a complex cybercrime, my initial approach focused heavily on technical analysis. However, it became apparent that the technical data alone wasn’t sufficient to establish intent or motive. I had to adapt my approach by incorporating traditional investigative methods, like interviewing suspects and witnesses, and analyzing financial records. This combined approach allowed me to build a stronger case, providing a more complete picture of the crime’s circumstances. The initial focus on technical evidence provided a solid foundation, but supplementing it with human intelligence and financial analysis proved indispensable in securing a successful resolution.
Key Topics to Learn for Ability to Conduct Investigations Interview
- Planning and Strategy: Developing a comprehensive investigation plan, including defining objectives, identifying resources, and outlining timelines. Practical application: Creating a detailed plan for investigating a data breach, outlining steps and required evidence.
- Data Collection and Analysis: Gathering relevant evidence from various sources (interviews, documents, databases), analyzing data for patterns and inconsistencies, and ensuring data integrity. Practical application: Using data analysis techniques to identify fraudulent activity within financial records.
- Interviewing Techniques: Conducting effective interviews to gather information, build rapport, and identify inconsistencies. Practical application: Employing active listening and open-ended questions to elicit truthful responses during witness interviews.
- Report Writing and Presentation: Clearly and concisely documenting findings, presenting evidence logically, and drawing accurate conclusions. Practical application: Preparing a detailed investigative report summarizing findings and recommendations for corrective action.
- Legal and Ethical Considerations: Understanding relevant laws, regulations, and ethical guidelines pertaining to investigations. Practical application: Ensuring all investigative activities comply with privacy laws and maintain confidentiality.
- Technological Tools and Techniques: Familiarity with software and tools used in investigations (e.g., data analysis software, forensic tools). Practical application: Using forensic software to recover deleted files from a hard drive.
- Problem-Solving and Critical Thinking: Analyzing complex situations, identifying key issues, and developing effective solutions. Practical application: Determining the root cause of a recurring security vulnerability.
Next Steps
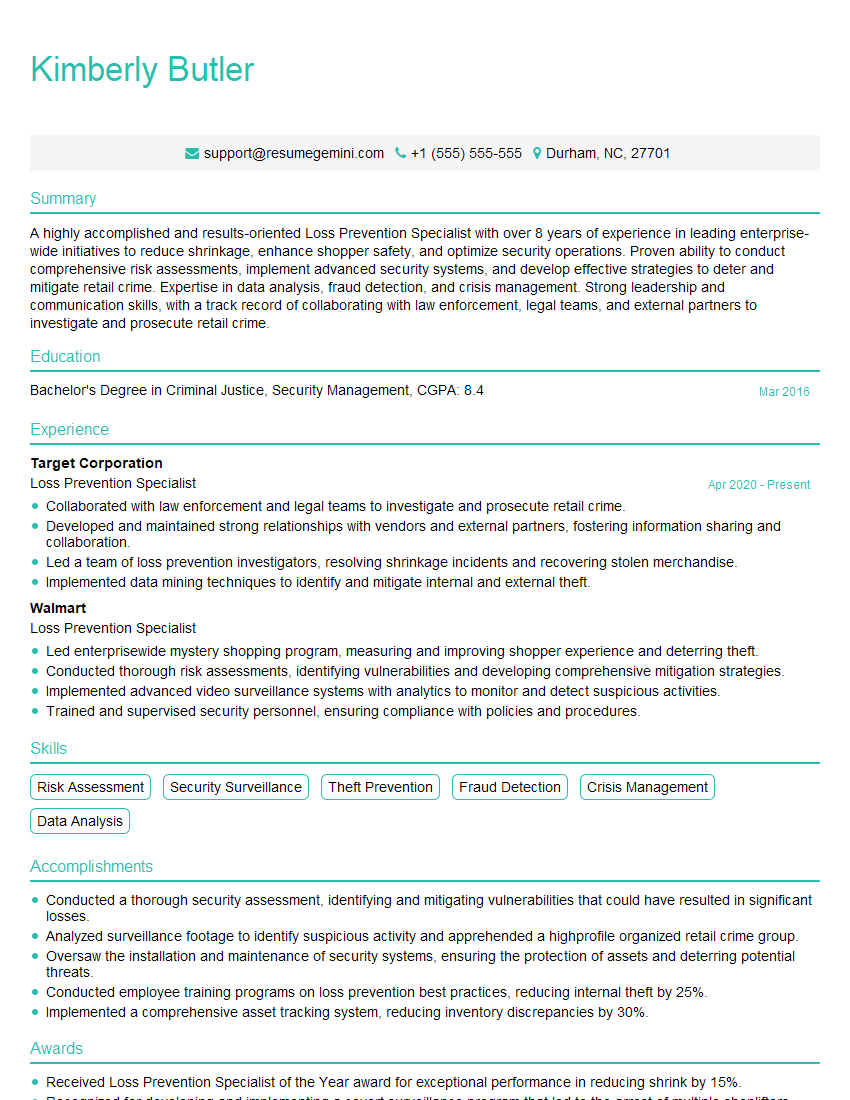
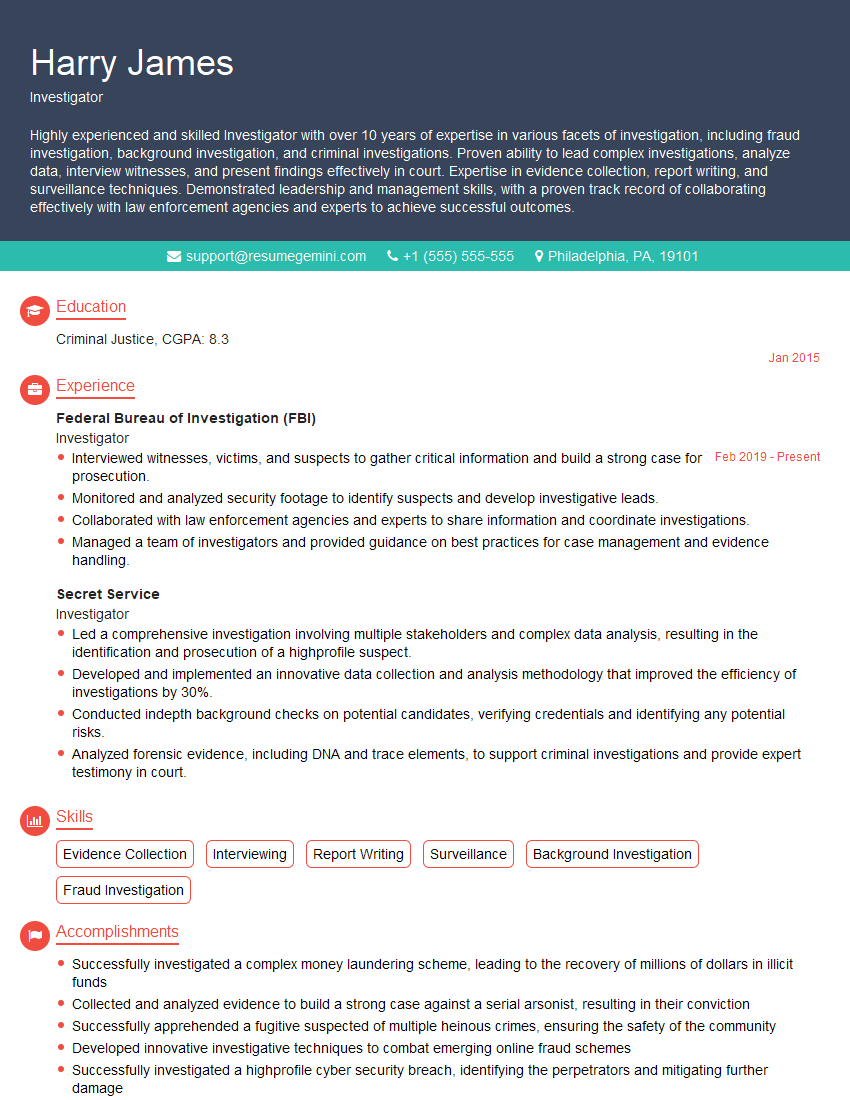
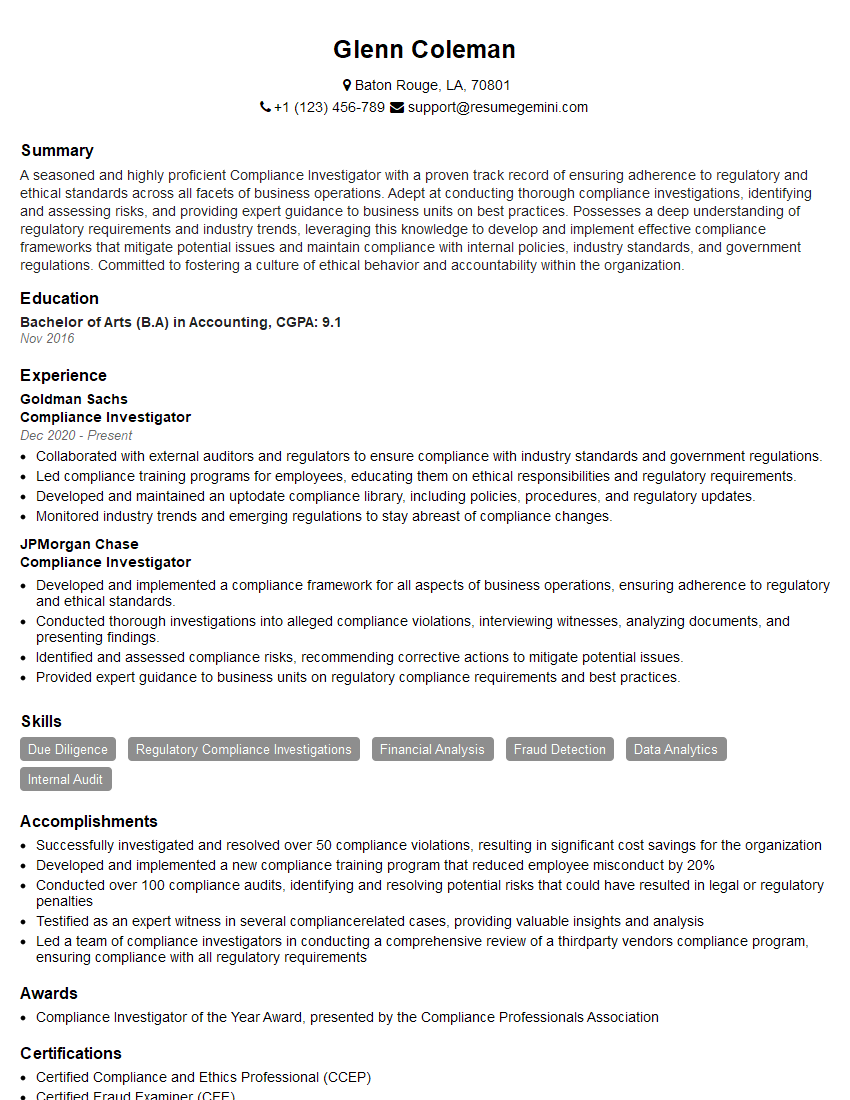
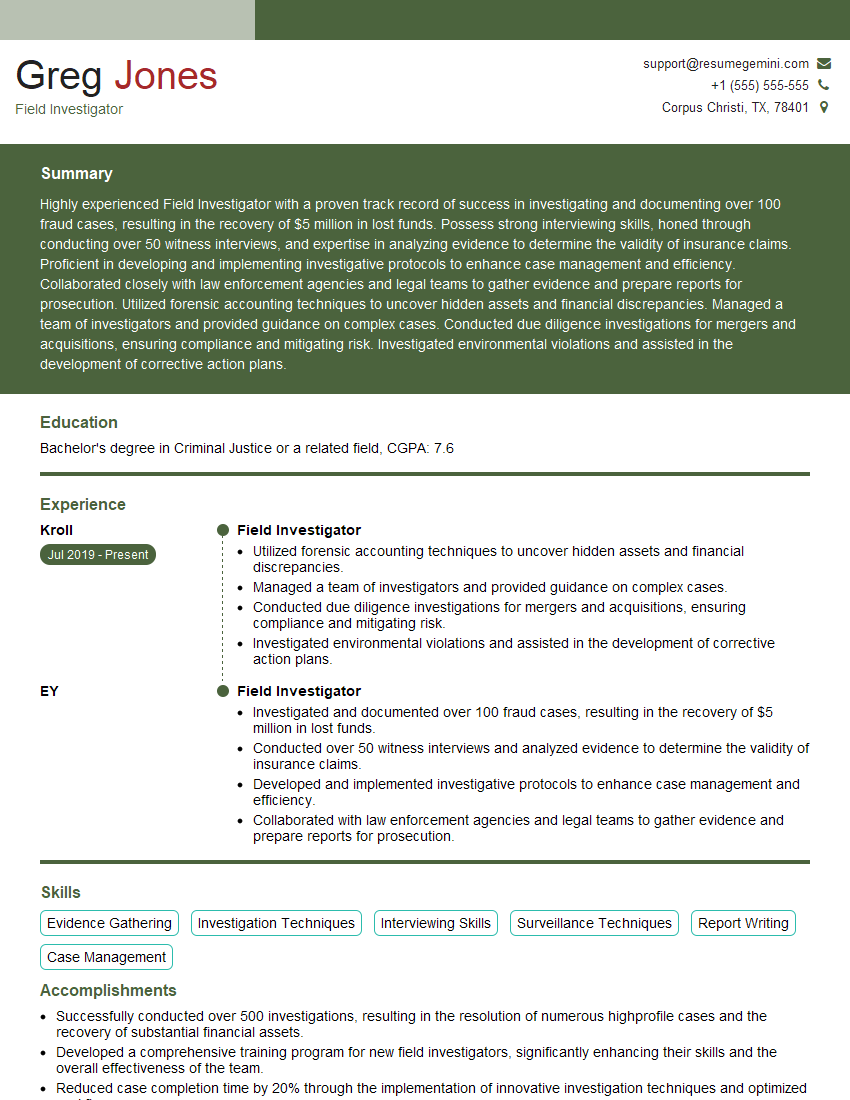
Mastering the ability to conduct investigations is crucial for career advancement in many fields, opening doors to leadership roles and specialized opportunities. A strong resume is essential to showcase your skills and experience effectively to potential employers. Creating an ATS-friendly resume significantly increases your chances of getting noticed. ResumeGemini is a trusted resource that can help you build a professional and impactful resume tailored to highlight your investigation abilities. Examples of resumes tailored specifically for candidates with expertise in Ability to Conduct Investigations are available to help you craft your best application.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good