Every successful interview starts with knowing what to expect. In this blog, we’ll take you through the top Experience in CounterIntelligence interview questions, breaking them down with expert tips to help you deliver impactful answers. Step into your next interview fully prepared and ready to succeed.
Questions Asked in Experience in CounterIntelligence Interview
Q 1. Describe your experience identifying and assessing potential counterintelligence threats.
Identifying and assessing potential counterintelligence threats requires a multifaceted approach combining analytical skills, investigative techniques, and a deep understanding of geopolitical landscapes. It starts with understanding the organization’s vulnerabilities – its assets, people, and processes – and then mapping those vulnerabilities against potential threats. This might involve analyzing foreign intelligence services’ known tactics, techniques, and procedures (TTPs), open-source intelligence (OSINT) to uncover potential threats, and assessing the risk posed by specific individuals or groups.
For example, during my time at [Previous Organization Name – Redacted for Security], we identified a potential threat from a foreign entity attempting to infiltrate our organization through a seemingly legitimate business partnership. By meticulously examining the partner’s background, financial records, and communication patterns, we discovered inconsistencies and suspicious activities which were then escalated, and the partnership was terminated.
Assessing the threat requires quantifying the likelihood and potential impact of the threat. This might involve assigning a risk score based on several factors, including the adversary’s capabilities, motivations, and the organization’s protective measures. This structured approach ensures resources are allocated effectively and prioritizes higher-risk threats.
Q 2. Explain your understanding of HUMINT, SIGINT, and OSINT collection methods.
HUMINT (Human Intelligence), SIGINT (Signals Intelligence), and OSINT (Open-Source Intelligence) are three crucial intelligence collection methods in counterintelligence. HUMINT involves gathering information from human sources, such as informants, defectors, or undercover agents. SIGINT focuses on intercepting and analyzing electronic communications, such as radio transmissions, phone calls, and computer network traffic. OSINT involves collecting information from publicly available sources, such as news articles, social media, and government websites.
In practice, these methods are often used in conjunction. For instance, OSINT might reveal suspicious activity, leading to further investigation through HUMINT or SIGINT. During my work on [Project Name – Redacted for Security], we successfully used OSINT to identify a potential target’s network, confirmed this through SIGINT monitoring their communications, and then validated it through carefully cultivated HUMINT sources.
Each method has strengths and limitations. HUMINT can provide deep insights but requires careful source handling. SIGINT can reveal vast amounts of data but requires sophisticated technology and analysis. OSINT is easily accessible but might not be reliable or complete. The effectiveness of counterintelligence hinges on integrating these methods strategically and adapting based on the specific threat landscape.
Q 3. How would you handle a suspected leak of classified information?
Handling a suspected leak of classified information requires a swift and coordinated response. The first step is to immediately contain the potential damage by limiting access to affected systems and information. This is followed by a thorough investigation to identify the source, method, and extent of the leak. This investigation would use a combination of technical analysis (forensics on systems), interviews, and possibly polygraph examinations.
The investigation team should maintain strict chain of custody and documentation to ensure the integrity of the evidence gathered. If the leak is confirmed, appropriate disciplinary or legal actions are taken, based on the severity and nature of the breach. The organization’s security protocols should also be reviewed and strengthened to prevent future leaks. Transparency with relevant authorities (e.g., law enforcement) might also be necessary depending on the sensitivity of the information.
For example, I once handled a suspected leak where an employee had accessed sensitive data beyond their authorized level. Using system logs and cross-referencing with employee access logs, we quickly isolated the employee and their activity, preventing further dissemination. A detailed internal investigation, along with notification of relevant agencies, followed.
Q 4. What are the key elements of a successful counterintelligence operation?
A successful counterintelligence operation relies on several key elements: Intelligence gathering and analysis (accurate, timely, and relevant information), Proactive threat identification (anticipating threats before they materialize), Effective security measures (protecting assets and personnel), Strong communication and coordination (collaboration across teams and agencies), Compartmentalization (limiting access to sensitive information), and Legal and ethical considerations (ensuring all actions comply with the law and organizational values).
Crucially, it also relies on well-trained personnel with expertise in various disciplines, including investigation, technical analysis, and human intelligence handling. Successful operations often depend on deceptive maneuvers to mislead adversaries or outsmart their tactics. Finally, post-operation analysis is critical to identify areas of improvement and adapt future counterintelligence strategies.
Think of a successful counterintelligence operation like a chess game: it requires careful planning, anticipating your opponent’s moves, utilizing all available resources strategically, and adapting to unexpected developments. The goal is not just to react to threats, but to proactively prevent them from occurring in the first place.
Q 5. Describe your experience in threat modeling and risk assessment.
Threat modeling and risk assessment are fundamental to counterintelligence. Threat modeling involves identifying potential threats to an organization’s assets and operations. This could range from cyberattacks to physical intrusions, espionage, or sabotage. Risk assessment quantifies the likelihood and impact of each identified threat, allowing for a prioritized response. These assessments often use structured methodologies, such as the Diamond Model of Intrusion, to visualize the threat landscape.
My experience in threat modeling involves employing a variety of techniques, from structured threat modeling methodologies to brainstorming sessions with security experts and stakeholders. The output of these assessments is a risk register, which prioritizes threats and identifies mitigating controls. During my time at [Previous Organization Name – Redacted for Security], I led the development of a comprehensive threat model for our critical infrastructure, identifying vulnerabilities and implementing security controls to mitigate identified risks.
Threat modeling and risk assessment are iterative processes. As the threat landscape evolves, these assessments must be regularly reviewed and updated to ensure their continued relevance and effectiveness. Failure to regularly update these assessments can lead to inadequate protection against emerging threats.
Q 6. How do you identify and mitigate insider threats?
Insider threats pose a significant risk, as individuals with legitimate access can exploit their position to compromise organizational security. Identifying insider threats requires a multi-layered approach. This begins with robust background checks and security awareness training for all employees. Continuous monitoring of employee activity, including access logs, network traffic, and data usage patterns, is crucial. Anomaly detection systems can flag unusual behavior that might indicate malicious activity. Furthermore, regular security audits and vulnerability assessments highlight potential weaknesses that insiders could exploit.
Mitigating insider threats involves implementing strong access controls, limiting privileges based on the principle of least privilege, and regular reviews of employee access rights. Data loss prevention (DLP) tools can monitor sensitive data movement and prevent unauthorized exfiltration. A robust whistleblower program encourages employees to report suspicious activity without fear of retribution. Finally, fostering a strong organizational culture of security awareness and responsibility is paramount.
A notable example in my career involved detecting an insider threat through anomalous network activity. A thorough investigation, using network forensics and employee interviews, revealed an employee attempting to exfiltrate sensitive data. Swift action prevented the data breach.
Q 7. Explain your understanding of counterintelligence deception techniques.
Counterintelligence deception techniques involve manipulating adversaries to reveal their intentions, capabilities, or activities. These techniques range from planting disinformation to creating false trails to mislead adversaries and divert their attention from sensitive operations or assets. A classic example is the use of double agents, where an individual secretly works for both the target organization and the opposing intelligence service, providing misleading information.
These techniques require careful planning, execution, and risk assessment, as they could backfire if not implemented correctly. Success hinges on understanding the adversary’s mindset, capabilities, and likely reactions. The use of deception also involves strict operational security to maintain the integrity and secrecy of the operation. It’s crucial to understand the legal and ethical implications before engaging in any deceptive counterintelligence tactic, always ensuring compliance with national and international law.
The effectiveness of these techniques is often measured by their ability to obtain valuable intelligence or disrupt adversary operations. Ethical considerations are paramount in any counterintelligence operation involving deception, requiring careful assessment of the potential consequences and rigorous adherence to established guidelines.
Q 8. How familiar are you with relevant laws and regulations pertaining to counterintelligence?
My familiarity with laws and regulations pertaining to counterintelligence is extensive. I possess a deep understanding of the Espionage Act, the Foreign Intelligence Surveillance Act (FISA), and other relevant statutes, both domestically and internationally. This includes a thorough grasp of the legal limitations on surveillance, data collection, and the handling of classified information. For instance, I’m well-versed in the nuances of the Fourth Amendment and how it applies to national security investigations, understanding the warrant requirements and exceptions. Furthermore, I’m aware of the specific regulations governing the handling of human intelligence sources, ensuring all operations adhere to legal and ethical standards. My experience includes regular review and updates on relevant legal precedents and legislative changes to maintain compliance and best practices.
I understand that the legal landscape is dynamic, constantly evolving to reflect technological advancements and shifting geopolitical situations. Therefore, staying abreast of these changes is paramount, and I actively participate in professional development to ensure my knowledge remains current and applicable. This includes attending relevant legal seminars and workshops, reviewing legal updates from reputable sources, and consulting with legal counsel when necessary.
Q 9. Describe your experience with counterintelligence investigations.
Throughout my career, I’ve been involved in a wide range of counterintelligence investigations, from relatively straightforward cases involving insider threats to complex, multi-national operations targeting sophisticated espionage rings. One particular case involved identifying and neutralizing a foreign intelligence service’s attempt to infiltrate a key government agency. This entailed developing and deploying a multifaceted investigative strategy that included surveillance, source development, and the use of advanced analytical techniques to identify patterns and predict adversary behavior. We successfully identified the agent, thwarted their operation, and brought them to justice.
Another significant experience involved analyzing a large-scale cyber intrusion into a critical infrastructure organization. This required collaborating with technical experts to understand the nature of the attack, tracing the origins of the intrusion, and identifying the perpetrators. The investigation involved coordinating with multiple agencies, both domestically and internationally, to effectively gather and analyze evidence. These experiences have honed my skills in investigative techniques, strategic planning, and collaborative problem-solving within a complex and often high-stakes environment.
Q 10. How do you prioritize and manage competing counterintelligence priorities?
Prioritizing competing counterintelligence priorities requires a structured and analytical approach. I utilize a risk-based prioritization framework, which involves assessing the potential impact of each threat, the likelihood of its occurrence, and the resources required to mitigate it. This allows for a systematic ranking of priorities, ensuring that the most critical threats are addressed first. For example, a threat involving the potential compromise of highly sensitive national security information would be prioritized over a less impactful threat, even if the latter requires fewer resources.
Furthermore, I regularly review and revise these priorities based on new information and emerging threats. This dynamic approach allows for adaptability and responsiveness to evolving circumstances. Effective communication and collaboration among team members are also critical, to ensure that everyone understands the priorities and works towards common goals. This includes clearly defining roles and responsibilities and establishing mechanisms for efficient information sharing.
Q 11. What are some common vulnerabilities exploited in counterintelligence operations?
Common vulnerabilities exploited in counterintelligence operations often stem from human factors and technological weaknesses. Human vulnerabilities include things like social engineering, blackmail, coercion, and insider threats, whereby individuals with access to sensitive information are compromised or persuaded to leak information. This often exploits personal weaknesses or financial difficulties. Technological vulnerabilities can include software vulnerabilities, unsecured networks, and weak passwords that allow unauthorized access to sensitive systems and data. Physical security weaknesses such as inadequate access controls or surveillance gaps also provide opportunities for infiltration.
For example, a foreign intelligence service might use social media to identify and target individuals with access to classified information, using tailored phishing attacks or other means of manipulation. Addressing these vulnerabilities requires a multi-layered approach involving robust security protocols, comprehensive employee training programs, regular security assessments, and proactive measures to identify and mitigate potential threats. It also includes maintaining a strong organizational culture of security awareness and responsibility.
Q 12. How would you assess the credibility of a potential source of intelligence?
Assessing the credibility of a potential intelligence source is crucial and involves a multi-faceted approach. First, I would verify their identity and background thoroughly, checking for any inconsistencies or red flags. This would involve reviewing their past actions, motivations, and relationships. Next, I’d analyze their information for accuracy and consistency, comparing it to information from other sources and verifying it using multiple independent methods. This triangulation of information is essential to confirm its reliability.
The source’s motivations also need careful consideration. Are they acting out of genuine concern for national security, seeking personal gain, or are they acting under duress or coercion? Understanding their biases and potential vulnerabilities is critical to assessing the reliability of the information they provide. Finally, I would consider the context in which the information was obtained and assess the source’s access and capability to obtain such information. Building rapport and trust is crucial, but critical analysis of the information is equally important to minimize the risk of misinformation.
Q 13. Explain your experience with analyzing large datasets for counterintelligence purposes.
My experience with analyzing large datasets for counterintelligence purposes is significant. I am proficient in using various data analysis tools and techniques, including statistical modeling, machine learning, and network analysis, to identify patterns and anomalies indicative of espionage or other threats. For instance, I’ve used network analysis to visualize communication patterns among suspected agents, revealing hidden connections and associations. This involves processing large volumes of communication data (emails, phone records, etc.) to uncover suspicious clusters and links.
Statistical modeling and machine learning techniques allow for the identification of unusual behavior or patterns in datasets that might indicate malicious activity. For example, I may analyze financial transactions to identify unusual money flows that might be linked to illicit activities, such as bribery or money laundering. The effective use of these tools and the interpretation of the results requires a strong understanding of both technical aspects and counterintelligence principles. The process involves cleaning the data, defining the relevant features, and applying the appropriate algorithms, always mindful of protecting privacy and adhering to relevant regulations.
Q 14. How do you maintain operational security in a counterintelligence context?
Maintaining operational security (OPSEC) in counterintelligence is paramount. It involves proactively identifying and mitigating vulnerabilities that could compromise an operation or expose agents and sources. This begins with careful planning and execution of every operation, focusing on minimizing the risk of detection and compromise. This includes controlling communication methods, using secure channels for classified information, and restricting access to sensitive materials on a strict need-to-know basis.
Techniques for maintaining OPSEC include using secure communications, employing compartmentalization to limit the number of individuals with access to sensitive information, and regularly reviewing security protocols to adapt to evolving threats and vulnerabilities. It is also important to conduct thorough background checks on personnel to ensure their trustworthiness and loyalty. Regular security awareness training is crucial for personnel to understand their roles and responsibilities in maintaining OPSEC. A culture of security consciousness is vital; everyone must be aware of the risks and actively contribute to mitigating them. Ignoring even the smallest security lapse can jeopardize an entire operation.
Q 15. Describe your experience with developing and implementing counterintelligence strategies.
Developing and implementing counterintelligence strategies involves a multifaceted approach that begins with a thorough understanding of the threat landscape. This includes identifying potential adversaries, their capabilities, and their likely intentions. I have extensive experience in this area, having led the development and implementation of strategies for both proactive threat mitigation and reactive incident response.
For example, in a previous role, we identified a pattern of intellectual property theft targeting our company’s research and development division. Our counterintelligence strategy involved a multi-pronged approach: enhanced physical security measures, improved cybersecurity protocols (including advanced intrusion detection systems and data loss prevention tools), a comprehensive employee awareness training program focusing on insider threats, and the covert deployment of countermeasures to identify and track the perpetrators. This strategy resulted in the successful identification and neutralization of the threat actors.
Another key element is the use of deception, which involves misleading adversaries to reveal their intentions or capabilities. This could involve the strategic deployment of misinformation, carefully controlled leaks of information, or the use of honeypots to trap malicious actors. Properly executed, these deception techniques can significantly disrupt and degrade an adversary’s ability to gather intelligence.
- Threat Assessment: A comprehensive analysis of potential threats and vulnerabilities.
- Vulnerability Mitigation: Implementing measures to reduce risks associated with identified vulnerabilities.
- Deception and Misinformation: Strategically deploying false information or creating traps to catch adversaries.
- Human Intelligence (HUMINT) Operations: Utilizing human sources to gather intelligence.
- Signal Intelligence (SIGINT) Operations: Intercepting and analyzing electronic communications.
- Open Source Intelligence (OSINT) Collection: Gathering information from publicly available sources.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. How would you manage a counterintelligence crisis?
Managing a counterintelligence crisis requires swift, decisive action and a calm, controlled approach, even under immense pressure. My experience shows that a structured approach is critical. First, I would immediately activate a crisis management team composed of individuals with relevant expertise across all necessary areas.
The team’s first priority is containment: Limiting the damage caused by the incident through immediate actions such as securing compromised systems, isolating affected personnel, and coordinating with law enforcement if necessary. Next, we would conduct a thorough investigation to determine the extent of the breach, identify the perpetrators, and understand their motivations and methods. This investigation would leverage available resources, including technical analysis, human intelligence, and open-source intelligence. Parallel to the investigation, a communication strategy would be developed and implemented, informing relevant stakeholders and managing public perception.
Finally, lessons learned from the crisis would be carefully documented to improve future counterintelligence strategies. This includes refining existing security measures, developing new protocols to address identified weaknesses, and providing updated training to enhance staff awareness and preparedness.
For example, in a past crisis where a foreign intelligence service attempted to infiltrate our organization, our immediate response involved isolating suspected compromised systems, conducting forensic analysis to determine the extent of data exfiltration, and launching a coordinated counter-operation that resulted in the disruption of the foreign intelligence service’s efforts and the identification of their operatives.
Q 17. What is your familiarity with various counterintelligence technologies and tools?
My familiarity with counterintelligence technologies and tools is extensive. This includes advanced surveillance technologies, data analytics platforms, and cybersecurity tools. I am proficient in using various software and hardware for data analysis, network monitoring, and intrusion detection.
- Network Intrusion Detection Systems (NIDS): Tools that monitor network traffic for malicious activity.
- Security Information and Event Management (SIEM) Systems: Systems that collect and analyze security logs from various sources.
- Data Loss Prevention (DLP) Tools: Tools that prevent sensitive data from leaving the organization’s network.
- Forensic Software: Software used to analyze digital evidence.
- Geospatial Intelligence (GEOINT) Software: Software used to analyze geographic data.
- Open Source Intelligence (OSINT) tools: Tools and techniques for gathering information from publicly available sources.
I understand the importance of integrating these technologies effectively to create a comprehensive security posture. For instance, combining data from NIDS and SIEM systems allows for a more holistic view of potential threats, enabling quicker and more effective response. My experience also encompasses the ethical and legal considerations associated with using these powerful tools.
Q 18. How would you handle pressure and stress in a high-stakes counterintelligence situation?
High-stakes counterintelligence situations are inherently stressful. Managing stress and pressure effectively is crucial for maintaining clear thinking and making sound judgments. I employ several strategies to mitigate stress, including:
- Maintaining a calm and methodical approach: Focusing on the immediate priorities and breaking down complex problems into smaller, manageable tasks.
- Effective time management: Prioritizing tasks based on urgency and importance.
- Regular self-assessment: Recognizing my own limitations and seeking support when needed.
- Strong team communication: Open and honest communication with team members to ensure everyone is informed and working collaboratively.
- Physical and mental wellbeing: Maintaining a healthy lifestyle through exercise, proper nutrition, and adequate rest.
In high-pressure situations, maintaining composure is paramount. I’ve learned that panic is the enemy of effective counterintelligence work. By staying focused, relying on my training, and employing a systematic approach, I can effectively navigate even the most challenging scenarios.
Q 19. Describe your experience working with cross-functional teams on counterintelligence matters.
Cross-functional collaboration is essential in counterintelligence. I possess significant experience working with diverse teams, including technical specialists, legal counsel, public relations professionals, and law enforcement. Successful collaboration requires clear communication, mutual respect, and a shared understanding of the objectives.
In my previous role, we worked extensively with a team of cybersecurity experts, legal advisors, and law enforcement agencies to investigate and resolve a complex case of industrial espionage. The success of this collaboration was due to establishing a clear chain of command, defining roles and responsibilities, and maintaining open communication channels. This involved regular briefings, shared intelligence platforms, and collaborative decision-making processes.
Effective cross-functional teamwork necessitates not only technical expertise but also strong interpersonal skills and the ability to build rapport and trust. I consistently strive to foster a collaborative environment where diverse perspectives are valued and utilized to achieve common goals.
Q 20. How familiar are you with geopolitical factors influencing counterintelligence operations?
Geopolitical factors are deeply intertwined with counterintelligence operations. Understanding the global political landscape, including international relations, economic conditions, and regional conflicts, is crucial for anticipating threats and developing effective counterintelligence strategies.
For example, the rise of great power competition influences the types of espionage and sabotage we might expect. Similarly, economic sanctions and trade wars can create opportunities for espionage aimed at obtaining valuable economic intelligence. Regional conflicts can generate increased risk of actions aimed at destabilizing governments or disrupting critical infrastructure. I regularly analyze geopolitical developments to understand potential implications for counterintelligence and adapt our strategies accordingly.
This awareness is vital to predicting adversaries’ motivations, understanding their likely targets, and anticipating their tactics. Geopolitical expertise enables a more nuanced and effective counterintelligence approach.
Q 21. How do you stay up-to-date on the latest counterintelligence techniques and threats?
Staying current in the dynamic field of counterintelligence requires continuous learning and adaptation. I regularly engage in several activities to maintain my knowledge and skills:
- Professional Development: Attending conferences, workshops, and training courses on emerging threats and technologies.
- Networking: Engaging with colleagues and experts in the field to share information and best practices.
- Reading Industry Publications: Keeping abreast of new research, techniques, and trends through journals and reports.
- Monitoring Open Sources: Actively monitoring news, social media, and online forums for emerging threats and adversary activities.
- Cybersecurity Awareness: Staying updated on the latest cyber threats and vulnerabilities.
Continuous learning is not just a professional obligation but also a personal commitment. The ever-evolving nature of threats requires a proactive and adaptable mindset. The rapid advancement of technology and evolving geopolitical dynamics necessitate constant vigilance and continuous professional development.
Q 22. Explain your experience in developing and delivering counterintelligence briefings.
Developing and delivering counterintelligence briefings requires a structured approach that ensures the information is not only accurate but also impactful for the audience. I begin by carefully analyzing the intelligence gathered, identifying key threats and vulnerabilities. This involves rigorously assessing the credibility of sources and verifying information through multiple channels. Then, I tailor the briefing to the specific audience, considering their level of understanding and their need-to-know. For example, a briefing for senior executives would focus on strategic implications, while a briefing for operational teams would emphasize tactical actions. My briefings utilize a clear, concise style, avoiding jargon wherever possible, and often incorporate visual aids like maps, charts, and timelines to enhance comprehension and retention. I also prioritize interactive elements, encouraging questions and discussion to foster a collaborative understanding of the threat landscape. Finally, I always ensure the briefing is delivered in a secure environment, protecting classified information.
For instance, during my time at [Previous Organization Name], I prepared a briefing on a potential foreign intelligence operation targeting our company’s proprietary technology. The briefing involved detailed analysis of intercepted communications, travel patterns, and financial transactions, all meticulously vetted for accuracy. The presentation successfully alerted senior management to the threat, leading to proactive security measures and ultimately preventing a significant data breach.
Q 23. Describe your approach to ethical considerations in counterintelligence work.
Ethical considerations are paramount in counterintelligence work. My approach is grounded in strict adherence to legal and regulatory frameworks, including [mention relevant laws and regulations, e.g., the Foreign Intelligence Surveillance Act (FISA)]. I believe in transparency and accountability, ensuring that all actions are justifiable and documented. This includes carefully weighing the potential impact on individuals’ privacy rights and civil liberties, always seeking the least intrusive method to achieve the counterintelligence objective. Furthermore, I prioritize collaboration and communication with internal legal counsel and relevant oversight bodies to ensure all activities are ethically sound. I’ve found that a proactive, ethical approach not only protects individuals’ rights but also strengthens the integrity and credibility of the counterintelligence operation.
One specific example involves a situation where we had strong suspicion of insider threat, but lacked definitive proof. Instead of launching an immediate, potentially invasive, investigation, we opted for a more targeted approach, focusing on data security enhancements and training for employees. This mitigated the risk while prioritizing the privacy and dignity of our personnel.
Q 24. How would you respond to a counterintelligence deception attempt?
Responding to a counterintelligence deception attempt requires a combination of vigilance, skepticism, and methodical investigation. My first step would be to identify the nature of the deception, carefully analyzing all available information to determine the intent and scope of the operation. This could involve verifying information through multiple independent sources, using technical methods to analyze digital communications, or employing human intelligence techniques to gather contextual information. Crucially, I would maintain a calm and controlled demeanor, avoiding any actions that might tip off the deceiver. Instead, I would carefully orchestrate a response that allows me to gather further information while simultaneously mitigating any potential damage. This may involve a controlled disclosure of misinformation to test the deceiver’s capabilities or to learn more about their goals and capabilities.
For example, if confronted with a suspected phishing attempt, instead of immediately reporting it, I would analyze the email, its sender, and its content for inconsistencies and clues to the attacker’s identity. I would carefully monitor further interactions, potentially even engaging in controlled responses to gather intelligence on the attacker.
Q 25. How do you ensure the accuracy and reliability of counterintelligence information?
Ensuring the accuracy and reliability of counterintelligence information is fundamental. I employ a multi-faceted approach, prioritizing the verification of information from multiple independent sources and utilizing various analytical techniques. This includes triangulating information from open sources, human intelligence, signals intelligence, and other technical means. Each piece of information is rigorously assessed for its credibility and potential biases. I also use techniques such as source corroboration, information cross-checking, and pattern analysis to identify inconsistencies or contradictions. Documenting the source and method of acquisition for each piece of information is crucial for maintaining transparency and accountability.
An example would be cross-referencing information from a human source with satellite imagery and communication intercepts to confirm the location and activities of a suspected foreign agent.
Q 26. Explain your experience in using data analytics to identify patterns and anomalies related to counterintelligence threats.
Data analytics plays a crucial role in modern counterintelligence. My experience involves leveraging various analytical tools and techniques to identify patterns and anomalies related to counterintelligence threats. This includes using statistical methods to analyze large datasets of communication metadata, financial transactions, travel records, and other relevant information. I use anomaly detection algorithms to identify unusual patterns that might indicate espionage or sabotage. Machine learning techniques can help predict potential threats and prioritize investigations. Visualization tools are essential to communicate findings effectively to stakeholders.
For example, I’ve used network analysis to map relationships between individuals suspected of involvement in an intelligence operation, revealing previously unknown connections and highlighting key players. Similarly, I have utilized data mining techniques to uncover hidden patterns in financial transactions that suggested a possible money laundering scheme linked to espionage.
Q 27. Describe your experience in coordinating with law enforcement or other agencies in counterintelligence matters.
Coordinating with law enforcement and other agencies is crucial for effective counterintelligence. My experience includes establishing and maintaining strong working relationships with various agencies, such as the FBI, CIA, and local law enforcement. Effective coordination requires clear communication, regular briefings, and adherence to established protocols and legal frameworks. I’ve found that a collaborative approach, built on mutual trust and respect, enhances the efficiency and effectiveness of counterintelligence operations. This collaboration allows for the sharing of information, pooling of resources, and the coordination of investigative efforts, ultimately leading to a more comprehensive and effective response to threats.
In a past investigation involving a suspected industrial espionage case, I collaborated closely with the FBI to share intelligence, coordinate investigative steps, and ensure compliance with legal procedures. This collaborative effort led to a successful prosecution of the individuals involved.
Q 28. How do you protect sensitive information during counterintelligence investigations?
Protecting sensitive information during counterintelligence investigations is critical. I employ a multi-layered approach that incorporates strict adherence to security protocols, classification guidelines, and data handling procedures. This includes using encrypted communication channels, employing secure storage methods for sensitive documents and data, and limiting access to information on a strict need-to-know basis. Regular security audits and vulnerability assessments are essential to identify and mitigate potential weaknesses in our security infrastructure. Personnel are trained on appropriate handling of classified information, and rigorous background checks are conducted on all individuals with access to sensitive materials. Furthermore, regular training and awareness campaigns reinforce security protocols and ensure that personnel understand the importance of information security.
For example, I’ve implemented a system that uses multi-factor authentication and encryption to protect access to highly sensitive databases, ensuring only authorized personnel with the appropriate clearance can access the information.
Key Topics to Learn for Experience in CounterIntelligence Interview
- Threat Assessment and Analysis: Understanding methodologies for identifying, assessing, and prioritizing threats to organizational security and national interests. Practical application includes analyzing intelligence reports to identify potential threats and vulnerabilities.
- Investigation Techniques: Mastering various investigative approaches, including open-source intelligence gathering, interviewing techniques, and evidence analysis. Practical application includes developing and executing investigative plans to uncover covert activities.
- Counterintelligence Operations: Knowledge of defensive and offensive counterintelligence operations, including deception, misinformation, and security awareness training. Practical application includes designing and implementing security protocols to protect sensitive information.
- Security Awareness and Training: Understanding how to educate and train personnel on recognizing and responding to counterintelligence threats. Practical application includes delivering engaging and effective security awareness programs.
- Legal and Ethical Considerations: Familiarity with relevant laws, regulations, and ethical guidelines governing counterintelligence activities. Practical application includes ensuring all activities are conducted within legal and ethical boundaries.
- Technological Aspects: Understanding the role of technology in counterintelligence, including cybersecurity, data analysis, and communication security. Practical application includes utilizing technology to detect and mitigate cyber threats.
- Report Writing and Briefing: Developing clear, concise, and persuasive reports and briefings for senior management. Practical application includes presenting complex intelligence findings in an easily understandable format.
Next Steps
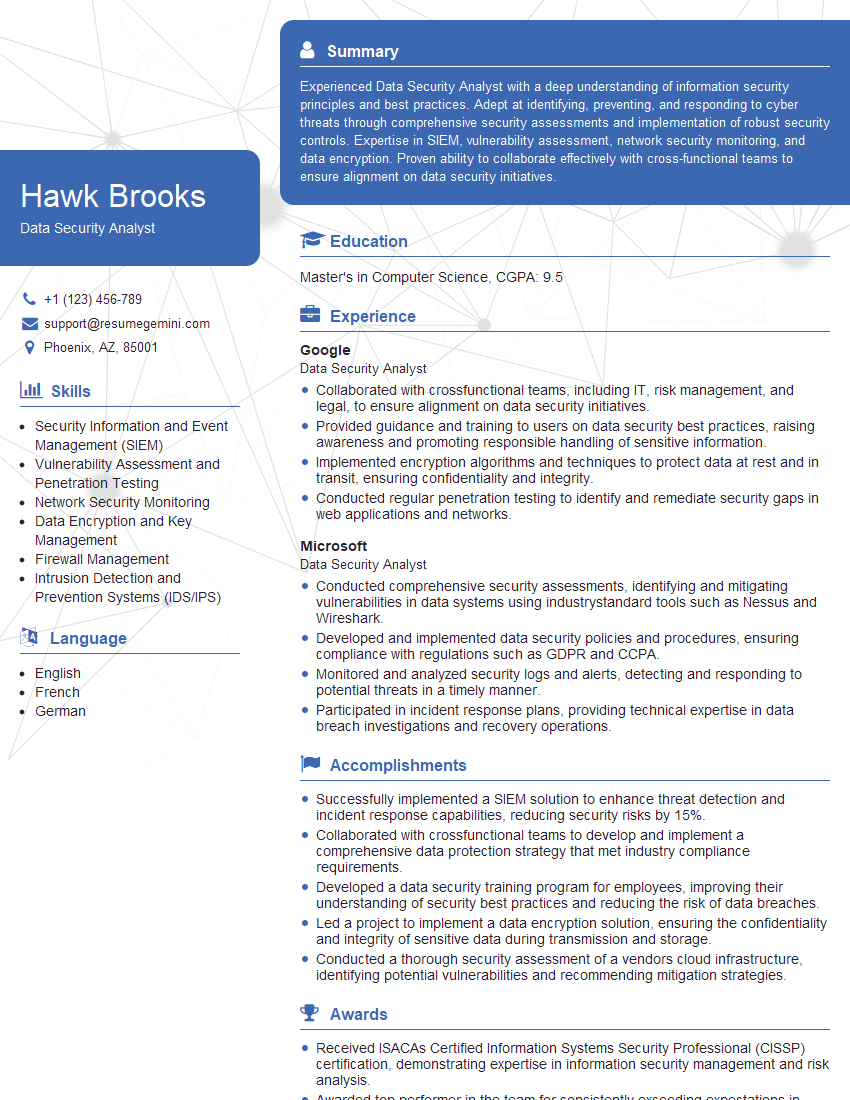
Mastering Experience in CounterIntelligence opens doors to challenging and rewarding careers in national security, law enforcement, and the private sector. Building a strong foundation in these key areas significantly increases your chances of success in securing your dream role. To enhance your job prospects, creating an ATS-friendly resume is crucial. ResumeGemini is a trusted resource to help you build a professional and impactful resume that showcases your skills and experience effectively. Examples of resumes tailored to Experience in CounterIntelligence are available within ResumeGemini to guide you in crafting your own compelling application.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good