Cracking a skill-specific interview, like one for Intelligence, Surveillance, and Reconnaissance (ISR) Operations, requires understanding the nuances of the role. In this blog, we present the questions you’re most likely to encounter, along with insights into how to answer them effectively. Let’s ensure you’re ready to make a strong impression.
Questions Asked in Intelligence, Surveillance, and Reconnaissance (ISR) Operations Interview
Q 1. Explain the difference between HUMINT, SIGINT, IMINT, and OSINT.
ISR relies on various intelligence disciplines, each offering a unique perspective. HUMINT (Human Intelligence), SIGINT (Signals Intelligence), IMINT (Imagery Intelligence), and OSINT (Open-Source Intelligence) are key components. Let’s differentiate them:
- HUMINT: This involves gathering information from human sources, like spies, informants, or defectors. Think of it like a network of trusted contacts providing inside information. For example, a HUMINT operation might involve recruiting a source within a terrorist organization to provide details on upcoming attacks.
- SIGINT: This focuses on intercepting and analyzing communications signals, such as radio transmissions, satellite communications, and computer network traffic. Imagine listening to a conversation between two suspects planning a crime, but remotely. An example of SIGINT would be monitoring radio chatter from a suspected smuggling operation.
- IMINT: This uses imagery, typically from satellites, drones, or aircraft, to gather intelligence. Think of it as visual reconnaissance. For instance, IMINT could be satellite imagery analyzing the construction of a new military facility.
- OSINT: This leverages publicly available information from sources like news reports, social media, and academic publications. It’s like being a detective using readily accessible clues. A classic OSINT example would be using publicly available flight manifests to track the movements of a person of interest.
Each discipline has its own strengths and limitations, and effective ISR often involves combining multiple sources for a more comprehensive picture.
Q 2. Describe the process of target acquisition and tracking.
Target acquisition and tracking is a cyclical process. It begins with identifying a potential target of interest based on intelligence reports or other leads. Then, we move into locating and confirming the target’s identity and position. This often involves employing a combination of IMINT, SIGINT, and HUMINT. Let’s outline the steps:
- Intelligence Gathering: We start with available information on the target’s potential locations, habits, and associates.
- Initial Location: Using a combination of sensors and intelligence, we try to pinpoint the target’s location.
- Confirmation: We employ multiple methods (e.g., different sensors, confirming information from different sources) to verify the target’s identity and location.
- Tracking: Once confirmed, we begin monitoring the target’s movements and activities. This often involves sustained surveillance, potentially across different modalities.
- Reporting: Throughout this process, regular reports are generated on the target’s activities and status.
Imagine tracking a suspected drug trafficker. We might start with financial records (OSINT), then use satellite imagery (IMINT) to find his warehouse, and intercept his communications (SIGINT) to confirm his plans. Continuous monitoring ensures we maintain awareness of his actions.
Q 3. What are the ethical considerations in ISR operations?
Ethical considerations in ISR are paramount. We must adhere to strict legal and moral guidelines to ensure operations are conducted responsibly and lawfully. Key ethical considerations include:
- Privacy: ISR operations often involve collecting sensitive information about individuals. We must ensure that any surveillance is conducted legally and proportionally, respecting individual privacy rights. This involves careful consideration of the legal framework and obtaining necessary approvals before any surveillance activity commences.
- Proportionality: The intrusiveness of the surveillance should be proportionate to the threat posed. For example, mass surveillance might be justified in a large-scale emergency but would be unethical for everyday police work.
- Accountability: Clear lines of accountability must be established for all ISR activities. This ensures that anyone responsible for conducting the operations can be held accountable for any violations of law or ethical principles.
- Transparency: While complete transparency may be impossible for security reasons, transparency should be maximized to the extent that is consistent with operational security. This often involves establishing oversight mechanisms.
- Targeting: There needs to be strict guidelines in place on who can be targeted, ensuring that collateral damage is minimized.
A good analogy is that ISR is a powerful tool, like a surgeon’s scalpel. It can be used to save lives but could cause grievous harm if mishandled. Ethics ensures we use it responsibly.
Q 4. How do you assess the reliability of intelligence sources?
Assessing the reliability of intelligence sources is crucial. We use a multi-faceted approach. It’s not enough to simply accept information at face value. The reliability is determined using several criteria:
- Source Track Record: Past accuracy of information provided. Has this source given reliable information before?
- Source Motivation: What are the source’s incentives? Are they seeking money, revenge, or recognition? Biased information needs to be viewed cautiously.
- Source Corroboration: Does the information align with data from other sources? Multiple sources supporting the same information significantly increases credibility.
- Information Plausibility: Does the information seem reasonable and consistent with known facts? Outlandish claims require extra scrutiny.
- Method of Collection: How was the information obtained? Was it from a reliable method? (e.g. direct observation vs. hearsay).
Think of it like a jury considering evidence. We look at multiple pieces of evidence, their source, and whether they corroborate each other before reaching a conclusion. A single unreliable source might provide misleading information; corroboration from multiple reliable sources strengthens the reliability of the intelligence.
Q 5. Explain the concept of ‘fusion’ in intelligence analysis.
Intelligence fusion is the process of combining information from different sources and disciplines to create a more comprehensive and accurate understanding of a situation. It’s about getting the ‘big picture’ rather than just isolated pieces of data. This synergistic approach greatly increases the value of each individual piece of intelligence.
For instance, combining IMINT showing troop movements (location, numbers, equipment) with SIGINT indicating communications (orders, plans, morale) and HUMINT reports on local attitudes paints a far richer and more accurate picture than any single intelligence source could offer. The result is a stronger understanding of the overall situation, leading to better decision-making.
Effective fusion involves not only combining data but also analyzing relationships, identifying inconsistencies, and generating insights that wouldn’t be apparent from examining individual sources in isolation. The process often requires sophisticated analytical tools and experienced analysts skilled in interpreting diverse forms of data.
Q 6. What are some common challenges in ISR data analysis?
Analyzing ISR data presents numerous challenges:
- Data Volume: Modern ISR systems generate massive amounts of data, making analysis a daunting task. Processing and managing this volume requires advanced technologies and efficient analysis techniques.
- Data Variety: Data comes in various formats, from textual reports to images, signals, and sensor data. Integrating and making sense of this heterogeneity requires sophisticated data fusion techniques.
- Data Velocity: Information needs to be processed and analyzed quickly to be relevant, requiring real-time or near real-time analytical capabilities.
- Data Veracity: Ensuring the accuracy and reliability of data from multiple sources is crucial. Distinguishing between accurate and misleading information is a continuous challenge.
- Data Ambiguity: Data can be open to interpretation; different analysts might draw differing conclusions from the same dataset.
The sheer volume of data alone can be overwhelming, requiring efficient filtering, organization, and visualization techniques. The process needs a well-structured system and skilled analysts to manage and interpret the information correctly.
Q 7. How do you handle conflicting information from different sources?
Conflicting information is common in intelligence analysis. Resolving these conflicts requires a methodical approach:
- Identify and Document: First, we meticulously document all conflicting pieces of information, noting their source, date, and collection method.
- Evaluate Sources: We assess the reliability and credibility of each source, considering their track record and potential biases (as discussed earlier).
- Analyze Context: We examine the context in which each piece of information was obtained. Were there factors that might have influenced the accuracy?
- Look for Corroboration: We try to find independent sources to corroborate either side of the conflict. More sources supporting a particular claim increase its likelihood.
- Reconcile or Suspend Judgment: If possible, we try to reconcile the conflicting information, finding a common thread or explanation. Sometimes, we have to suspend judgment if we lack sufficient evidence to resolve the conflict.
Imagine two sources reporting on the number of enemy troops in a specific location. One states 100, the other 500. We’d examine each source’s reliability, the methods used, and look for other evidence, perhaps aerial imagery, to help resolve the discrepancy. Until we have sufficient evidence, we may have to acknowledge the uncertainty.
Q 8. Describe your experience with specific ISR technologies.
My experience with ISR technologies spans a wide range, encompassing both traditional and cutting-edge systems. I’ve extensively worked with various sensor platforms, including electro-optical/infrared (EO/IR) sensors for high-resolution imagery and thermal detection, which are crucial for identifying targets, assessing their activities, and even determining their emotional state through subtle heat signature changes. I’m also proficient with radar systems, both ground-based and airborne, for long-range surveillance, target tracking, and weather monitoring; crucial in challenging conditions where optical systems may be limited. Furthermore, my experience includes working with signals intelligence (SIGINT) systems, intercepting and analyzing communications to gain actionable intelligence. Specifically, I’ve utilized software defined radios (SDRs) to process and analyze various communication types, from simple radio transmissions to complex encrypted data streams. Lastly, I’ve worked with geospatial intelligence (GEOINT) systems, integrating data from various sources to create comprehensive situational awareness. This often involves working with sophisticated Geographic Information Systems (GIS) software to analyze and present data visually.
For example, during a recent operation, we successfully used a combination of EO/IR and SIGINT to track a high-value target’s movement and communication patterns, leading to a successful apprehension. The high-resolution thermal imagery allowed us to identify the target even in low-light conditions, while SIGINT provided real-time information on their location and intended destination. This successful integration highlighted the synergistic nature of different ISR capabilities.
Q 9. How do you prioritize targets for surveillance?
Prioritizing targets for surveillance involves a systematic approach that considers several factors. It’s not simply about choosing the ‘most important’ target, but rather, optimizing resource allocation for maximum impact. The process generally involves a multi-step evaluation using a framework often termed the ‘Prioritization Matrix‘ or similar. This matrix generally incorporates the following factors:
- Threat Level: How dangerous or harmful is the target? This considers the potential impact of their activities.
- Vulnerability: How susceptible is the target to our surveillance and subsequent action? This assesses our ability to effectively gather intelligence.
- Value: What actionable intelligence can we gain from surveillance? High-value targets may provide information about a larger network or operation.
- Resource Requirements: How much time, personnel, and equipment will be needed to effectively monitor the target? This is crucial for efficient resource allocation.
- Urgency: How quickly do we need information? Time-sensitive targets require immediate attention.
These factors are often weighted and scored, enabling a quantitative ranking of potential targets. For instance, a target with a high threat level, high vulnerability, and high value, but low resource requirements would be prioritized over a target with similar threat and value, but high resource requirements and low vulnerability. This matrix allows for a transparent and data-driven approach to target selection, ensuring that limited resources are applied strategically.
Q 10. What are the legal limitations of ISR operations?
The legal limitations of ISR operations are complex and vary significantly depending on the jurisdiction and the specific nature of the operation. Generally, these limitations stem from domestic and international law, aiming to protect individual privacy rights, national sovereignty, and prevent unnecessary harm. Key legal considerations include:
- Domestic laws regarding surveillance: Most countries have laws that regulate domestic surveillance, often requiring warrants or other legal authorizations before conducting surveillance activities, outlining the parameters under which data can be collected and ensuring respect for privacy rights.
- International law: International humanitarian law (IHL) and international human rights law (IHRL) place significant constraints on the conduct of ISR operations, especially in conflict zones. These laws regulate the targeting of individuals and property, emphasizing the principles of distinction, proportionality, and precaution to prevent civilian harm. The use of lethal force in ISR operations is stringently regulated and requires strict adherence to these principles.
- Privacy rights: ISR operations often raise concerns about the potential violation of privacy rights. Balancing national security needs with individual privacy rights remains a major challenge, requiring careful consideration of the legal framework, and use of procedures that minimize potential infringement.
Non-compliance can lead to legal repercussions, including criminal charges, civil lawsuits, and diplomatic disputes. Therefore, strict adherence to all applicable legal frameworks is paramount in ISR operations.
Q 11. Explain your understanding of the Intelligence Cycle.
The Intelligence Cycle is a cyclical process used to manage the collection, analysis, and dissemination of intelligence. It’s a continuous loop, not a linear process, and consists of five key phases:
- Planning and Direction: This phase defines the intelligence requirements, identifies the gaps in knowledge, and sets the overall objectives for the intelligence effort.
- Collection: This involves gathering raw data from various sources using a range of ISR technologies and human intelligence (HUMINT) methods. This phase requires careful planning and coordination to ensure the efficiency and effectiveness of the collection efforts.
- Processing: Raw data from various sources undergoes cleaning, formatting, and organization. This prepares the data for analysis.
- Analysis and Production: This is where raw data transforms into actionable intelligence. Analysts carefully evaluate the information, identify patterns, and draw conclusions, producing intelligence assessments and reports.
- Dissemination: The final phase involves distributing the intelligence to the relevant decision-makers and consumers in a timely and effective manner. This ensures that timely and accurate information reaches those who need it.
Each phase is interconnected and feeds into the next, creating a continuous loop. For instance, the dissemination phase might reveal new intelligence requirements, starting the cycle anew. A failure at any phase can compromise the overall effectiveness of the intelligence process. Think of it as a well-oiled machine; if one part fails, the entire system suffers.
Q 12. Describe your experience with data visualization and presentation.
My experience with data visualization and presentation is extensive. I’m proficient in using various software tools to transform complex ISR data into clear, concise, and easily understandable visual representations. This includes using GIS software like ArcGIS and QGIS to map geospatial data, creating interactive dashboards to monitor real-time intelligence, and employing visualization tools such as Tableau and Power BI to represent complex data trends and relationships effectively. I’ve developed various charts, graphs, maps, and other visual aids to communicate findings effectively to both technical and non-technical audiences.
For instance, in a recent project, I used ArcGIS to create an interactive map visualizing the movement patterns of a group of individuals over time. This map allowed us to quickly identify key locations and timings, facilitating timely interventions. The ability to clearly visualize complex datasets is not merely a skill but a fundamental requirement for effective intelligence analysis and communication.
Q 13. How do you ensure the security and integrity of ISR data?
Ensuring the security and integrity of ISR data is paramount. A breach could have severe consequences, potentially compromising ongoing operations, jeopardizing sources, or revealing sensitive information to adversaries. Our security protocols are multi-layered and cover the entire ISR lifecycle, from data collection to dissemination. These measures include:
- Data Encryption: All sensitive data is encrypted both in transit and at rest, using strong encryption algorithms to protect it from unauthorized access.
- Access Control: Strict access control mechanisms, including role-based access control (RBAC), ensure that only authorized personnel can access sensitive data, restricting access based on their job role and security clearance.
- Data Integrity Checks: Regular checks are conducted to verify the integrity of the data, ensuring it hasn’t been tampered with or corrupted.
- Secure Data Storage: Data is stored in secure, redundant systems with robust backup and recovery mechanisms to ensure its availability and prevent data loss.
- Regular Security Audits: Our systems undergo regular security audits and penetration testing to identify and address vulnerabilities before they can be exploited.
- Personnel Security: Thorough background checks and security clearances are required for all personnel involved in handling sensitive ISR data.
These measures are not independent but work together to form a robust security framework that effectively protects the confidentiality, integrity, and availability of our ISR data.
Q 14. How do you adapt ISR strategies to different environments?
Adapting ISR strategies to different environments is critical for operational success. The effectiveness of specific ISR technologies and techniques can vary drastically depending on environmental factors such as terrain, weather, and the presence of electronic countermeasures (ECM). Adaptability requires a thorough understanding of these factors and the ability to select the right tools and techniques for the specific situation. This involves:
- Environmental Assessment: A comprehensive assessment of the operational environment is conducted to identify potential challenges and opportunities. This assessment considers factors such as terrain, weather, communications infrastructure, and potential adversary capabilities.
- Sensor Selection: The selection of appropriate sensor platforms and technologies is crucial. For instance, in dense urban environments, ground-penetrating radar might be necessary for locating targets hidden underground, whereas in mountainous regions, airborne sensors with long-range capabilities would be favored.
- Operational Tactics: Operational tactics must be adjusted to address environmental limitations. For example, poor weather conditions might necessitate alternative data collection methods or a delay in operations.
- Countermeasures: Strategies are developed to counter anticipated challenges such as electronic jamming or deception. This often involves the use of redundant communication systems or specialized sensor platforms with countermeasures built in.
- Contingency Planning: Robust contingency plans are essential to handle unexpected situations. This ensures the mission’s continuity even if unexpected challenges arise.
Flexibility and adaptability are key to effective ISR operations in any environment. A ‘one-size-fits-all’ approach is rarely successful. Understanding the unique characteristics of each environment allows for tailored strategies that maximize effectiveness and minimize risk.
Q 15. What are the key performance indicators (KPIs) for ISR operations?
Key Performance Indicators (KPIs) for ISR operations are multifaceted and depend heavily on the specific mission objectives. However, some common and crucial KPIs include:
- Timeliness of Intelligence: How quickly is actionable intelligence delivered to decision-makers? This is critical for time-sensitive operations. A delay can render intelligence obsolete.
- Accuracy of Intelligence: The reliability and correctness of the gathered information. This involves minimizing false positives and negatives. High accuracy builds trust and confidence in the intelligence product.
- Completeness of Intelligence: Does the intelligence provide a comprehensive picture of the situation? Incomplete intelligence can lead to misinterpretations and poor decision-making. We aim for a holistic view.
- Relevance of Intelligence: Does the intelligence directly address the mission’s objectives? Irrelevant data wastes resources and time. Focus is key.
- Cost-Effectiveness: The balance between the resources (personnel, equipment, time) expended and the value of the intelligence gained. We strive for maximum return on investment.
- System Uptime/Reliability: The percentage of time ISR systems are operational and functioning correctly. Downtime directly impacts intelligence gathering capabilities.
- Personnel Safety: The absence of injuries or casualties during operations. This is paramount and non-negotiable.
These KPIs are constantly monitored and analyzed to assess mission effectiveness and identify areas for improvement. Regular reporting and feedback mechanisms are crucial for maintaining high standards.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. Describe a time you had to troubleshoot a technical problem during an ISR mission.
During a counter-narcotics operation in the Amazon rainforest, our primary UAV experienced a critical malfunction – loss of GPS signal due to dense canopy cover. This severely hampered our ability to maintain real-time situational awareness and target tracking.
My immediate response involved a three-pronged approach:
- Initiate Backup Systems: We switched to secondary navigation systems utilizing inertial navigation and terrain following radar. This ensured the UAV remained airborne and avoided crashing.
- Coordinate with Ground Teams: We established communication with ground teams equipped with alternative geolocation systems (e.g., long-range radar) to receive positional updates and recalibrate our targeting. This was a crucial back-up for the loss of GPS.
- Problem Diagnosis and Solution: While maintaining operational continuity, I initiated a diagnostic check on the UAV’s GPS receiver. We identified a software glitch and subsequently remotely updated the UAV’s software to resolve the problem. The glitch affected the UAV’s ability to integrate the signal correctly.
Through coordinated action and immediate problem-solving, we mitigated the impact of the technical failure and successfully completed the mission, albeit with a slight delay. The incident also highlighted the importance of redundancy and robust backup systems in ISR operations.
Q 17. How familiar are you with different types of sensors and their capabilities?
My familiarity with various sensors is extensive. I possess practical experience in operating and interpreting data from a wide range of sensor modalities, including:
- Electro-Optical/Infrared (EO/IR) Sensors: These provide high-resolution imagery during both day and night operations, enabling target identification and tracking. EO captures visible light, while IR captures heat signatures.
- Radar Sensors: These sensors penetrate clouds and darkness, offering valuable all-weather surveillance capabilities. They can detect moving targets and map terrain.
- Signals Intelligence (SIGINT) Sensors: These intercept and analyze electronic signals, providing intelligence on communications, radar emissions, and other electronic activities. SIGINT is critical for understanding enemy capabilities and intentions.
- Geospatial Intelligence (GEOINT) Sensors: These include satellite imagery, aerial photography, and mapping systems which provide critical context for understanding the operational environment. These are often combined with other intelligence sources.
- Acoustic Sensors: These detect and analyze sounds, valuable in underwater surveillance and detecting specific events or activities. Their use depends heavily on the environment.
I understand the strengths and limitations of each sensor type and how to integrate their data for a comprehensive intelligence picture. Sensor selection depends heavily on the specific mission objectives and environmental conditions.
Q 18. How do you manage risk in ISR operations?
Risk management in ISR operations is paramount. It involves a proactive approach incorporating several key steps:
- Risk Assessment: A thorough evaluation of potential threats and hazards before, during, and after an operation. This includes environmental factors, technical malfunctions, adversary actions, and personnel safety.
- Mitigation Strategies: Developing and implementing plans to reduce or eliminate identified risks. This may involve employing redundant systems, employing robust communication protocols, and establishing contingency plans.
- Contingency Planning: Developing alternative strategies in case of unexpected events or failures. This ensures operational flexibility and resilience.
- Communication and Coordination: Maintaining clear and consistent communication between all team members and stakeholders. This ensures that everyone is aware of potential risks and mitigation strategies.
- Continuous Monitoring: Regularly monitoring the operational environment and adapting risk mitigation plans as needed. Situational awareness is constantly evolving.
- Post-Mission Debriefing: A thorough analysis of the operation to identify lessons learned and areas for improvement in risk management. Continuous learning is a priority.
A structured risk management process is essential for minimizing threats, ensuring mission success, and protecting personnel.
Q 19. Explain your understanding of geospatial intelligence (GEOINT).
Geospatial Intelligence (GEOINT) is intelligence derived from the exploitation and analysis of imagery and geospatial information. It provides a critical context for understanding the operational environment and informs decision-making. Think of it as the ‘where’ of intelligence.
GEOINT sources include:
- Satellite Imagery: High-resolution images from satellites provide broad area coverage and are valuable for monitoring infrastructure, identifying targets, and assessing environmental conditions.
- Aerial Photography: Images captured from aircraft, providing detailed information on specific areas of interest.
- Mapping and Charting Data: Topographical maps, charts, and other geospatial data provide context for understanding terrain, infrastructure, and other geographic features.
GEOINT is often combined with other intelligence disciplines (SIGINT, HUMINT, etc.) to create a complete and accurate picture of the situation. For example, analyzing satellite imagery of a suspected weapons facility might reveal the layout and size of the complex, while SIGINT analysis could indicate communication patterns within the facility, leading to a comprehensive understanding.
Q 20. How do you maintain situational awareness during an operation?
Maintaining situational awareness (SA) during an ISR operation is a continuous and dynamic process, requiring constant monitoring of multiple data streams. Think of it as having a 360-degree view of the environment.
Key methods for maintaining SA include:
- Sensor Fusion: Combining data from various sensor types (EO/IR, radar, SIGINT) to create a comprehensive picture of the operational environment.
- Information Sharing: Real-time communication and information sharing with all stakeholders, including ground teams, analysts, and command centers. Keeping everyone informed is vital.
- Data Analysis and Interpretation: Rapid analysis of incoming sensor data to identify changes and trends in the situation. Interpreting data correctly is essential.
- Use of Mapping and Visualization Tools: Utilizing advanced mapping and visualization tools to create a dynamic and interactive representation of the operational environment.
- Human Intelligence (HUMINT) Integration: Incorporating human intelligence and reports from ground sources to supplement sensor data and enhance situational awareness.
Effective SA allows for proactive decision-making, quick response to unexpected events, and overall mission success.
Q 21. Describe your experience with communication systems in ISR operations.
My experience with communication systems in ISR operations spans various platforms and technologies, encompassing both secure and non-secure communication networks.
I’m proficient in:
- Satellite Communications (SATCOM): Utilizing satellite networks for reliable long-range communication, even in remote or challenging environments. I understand the limitations of satellite bandwidth.
- High-Frequency (HF) Radio: Employing HF radio for long-range communication, especially in areas with limited or no other communication infrastructure. HF is susceptible to interference.
- Very High Frequency (VHF) and Ultra High Frequency (UHF) Radio: Utilizing these frequencies for short-to-medium range communication, commonly used for air-to-ground and ground-to-ground communication. Line-of-sight is usually necessary.
- Data Links: Employing secure data links for transmitting large volumes of sensor data in real time. Secure transfer of data is key.
- Network Security: Implementing security protocols and measures to protect sensitive communication from interception and unauthorized access. Cybersecurity is paramount.
I understand the importance of redundant communication systems and maintaining secure communication channels during sensitive operations. Selecting the correct communication system is critical to mission success.
Q 22. How do you collaborate with other intelligence disciplines?
Collaboration in ISR is crucial because no single intelligence discipline holds all the answers. Effective ISR relies on a synergistic approach, integrating information from various sources. I frequently collaborate with Human Intelligence (HUMINT) collectors to validate imagery analysis from GEOINT (Geospatial Intelligence) sources. For example, if satellite imagery reveals suspicious activity at a specific location, I would work with HUMINT personnel to gather on-the-ground corroboration or further details. Similarly, SIGINT (Signals Intelligence) data can pinpoint communications associated with identified targets, providing temporal context to the GEOINT imagery and HUMINT reports. This integrated approach leads to a more complete and accurate intelligence picture. I also regularly participate in inter-agency briefings, sharing insights and coordinating efforts with analysts from other government organizations, like the FBI or CIA, ensuring a unified understanding of the threat landscape. Effective collaboration relies heavily on clear communication, shared data platforms, and a strong understanding of each discipline’s strengths and limitations.
Q 23. What are some best practices for data handling and reporting in ISR?
Data handling and reporting in ISR demand meticulous attention to detail and strict adherence to security protocols. Best practices begin with clear data provenance—knowing exactly where the data originated, its processing steps, and any potential biases. This is documented throughout the intelligence cycle, from collection to dissemination. We use secure databases and data management systems to store and access sensitive information. Access control is paramount; only authorized personnel with appropriate clearances can view the data. For reporting, standardized templates ensure consistency and clarity. Reports undergo rigorous quality control, including peer review and validation against other intelligence sources. Data is classified appropriately to reflect its sensitivity, adhering to government regulations. For example, using a system like ArcGIS for mapping or Palantir for data fusion allows for robust data management and visualization while maintaining security. The reporting process follows strict protocols including redaction, classification marking and handling guidelines to protect classified information.
Q 24. How do you stay updated on current events and emerging technologies relevant to ISR?
Staying abreast of current events and emerging technologies is vital in the dynamic world of ISR. I regularly monitor reputable news sources like the New York Times, Financial Times and specialized publications such as Jane’s Defence Weekly, focusing on geopolitical developments and technological advancements. Furthermore, I actively participate in professional organizations, attend conferences, and pursue relevant training courses to stay updated on the latest techniques and technologies. I subscribe to industry newsletters and participate in online forums focused on SIGINT, GEOINT, and MASINT (Measurement and Signature Intelligence). The advancements in AI, machine learning, and big data analytics are profoundly impacting ISR, providing new possibilities for automated target recognition, predictive analysis, and real-time information processing. I actively investigate how these technologies can enhance our capabilities.
Q 25. Describe your experience with intelligence reporting and briefing.
My experience with intelligence reporting and briefing spans several years. I’ve crafted numerous intelligence products ranging from short, concise assessments to comprehensive reports detailing complex operational scenarios. My reporting style focuses on clarity, accuracy, and objectivity. I strive to tailor my briefings to the audience, adjusting the level of technical detail based on their background and needs. For instance, when briefing senior military leaders, I focus on high-level strategic implications, while briefings for tactical units require detailed information about specific targets and threats. I’ve also presented findings in various formats, including visual aids (maps, charts, and images) and interactive presentations. A recent project involved analyzing satellite imagery to assess the capabilities of a potential adversary’s military infrastructure. My report included detailed analysis of the imagery, corroborating evidence from other intelligence sources, and concluding assessments of the adversary’s capabilities and intentions. I then presented this information to senior decision-makers.
Q 26. How do you ensure the accuracy and validity of intelligence products?
Ensuring the accuracy and validity of intelligence products is paramount. We employ a multi-layered approach to validation, starting with rigorous source verification. Is the source credible? Is the information independently verifiable? We cross-reference information from multiple, independent sources to corroborate findings and identify potential inconsistencies. When analyzing imagery, we use image exploitation techniques, comparing multiple images and applying contextual knowledge. We also carefully assess potential biases within the data, considering the limitations of each source. For example, a single HUMINT report needs corroboration from other sources. Triangulation of information, using different intelligence disciplines, is key. Finally, regular quality control checks and peer reviews are conducted to ensure accuracy and validity before dissemination. We also maintain a detailed record of our analytical methodology, allowing for transparency and scrutiny.
Q 27. What are the limitations of different ISR methods?
Each ISR method has inherent limitations. GEOINT, while providing valuable visual information, can be limited by weather conditions, cloud cover, and the resolution of the imagery. SIGINT is susceptible to encryption, jamming, and the challenge of interpreting vast amounts of data. HUMINT is reliant on the reliability and trustworthiness of human sources, who might be biased, misinformed, or deliberately deceptive. MASINT, while highly technical, may be limited by the availability of appropriate sensors or the complexity of signal analysis. For example, relying solely on GEOINT to track a mobile target might be challenging due to the target’s mobility and the limitations of imaging frequency. Therefore, a comprehensive ISR approach integrates multiple methods to overcome these individual limitations and provide a robust intelligence picture.
Q 28. Explain your experience with using software tools for ISR analysis.
My experience with ISR analysis software is extensive. I am proficient in using various Geographic Information Systems (GIS) software such as ArcGIS for geospatial analysis and mapping. I am also adept at using commercially available software for imagery exploitation and analysis. I have experience working with specialized software for processing and analyzing SIGINT data. Furthermore, I have utilized data fusion software, such as Palantir, to integrate information from different intelligence sources into a cohesive picture. These tools significantly enhance the speed and accuracy of analysis, allowing for more effective decision-making. I routinely use scripting languages such as Python to automate tasks such as image processing and data extraction, thereby increasing efficiency and reducing human error. For example, I use Python to automate the process of extracting metadata from satellite imagery, a task that would be extremely time-consuming if done manually.
Key Topics to Learn for Intelligence, Surveillance, and Reconnaissance (ISR) Operations Interview
- Intelligence Cycle: Understand the complete process from requirements to dissemination, including planning, collection, processing, analysis, and production of intelligence.
- Sensor Technologies: Familiarize yourself with various sensor types (e.g., satellite imagery, SIGINT, HUMINT), their capabilities, limitations, and appropriate applications in different operational environments.
- Data Fusion and Analysis: Learn techniques for integrating data from multiple sources to create a coherent and actionable intelligence picture. Practice interpreting complex datasets and drawing meaningful conclusions.
- Geospatial Intelligence (GEOINT): Develop a strong understanding of map reading, image interpretation, and the use of GIS software for analyzing geographic information.
- Signals Intelligence (SIGINT): Explore the collection, analysis, and interpretation of communications and electronic signals. Understand the ethical and legal considerations related to SIGINT.
- Human Intelligence (HUMINT): Learn about the principles of human intelligence gathering, including source recruitment, handling, and debriefing. Understand the importance of rapport building and information validation.
- Cyber Intelligence (CYINT): Gain familiarity with cyber threat intelligence, network security, and the role of CYINT in ISR operations.
- Mission Planning and Execution: Understand the process of planning and executing ISR missions, including target selection, resource allocation, and risk assessment.
- Ethical and Legal Considerations: Be prepared to discuss the ethical and legal frameworks governing ISR operations, including privacy concerns and the rules of engagement.
- Problem-Solving and Critical Thinking: Practice applying your knowledge to real-world scenarios, focusing on analytical skills and decision-making under pressure.
Next Steps
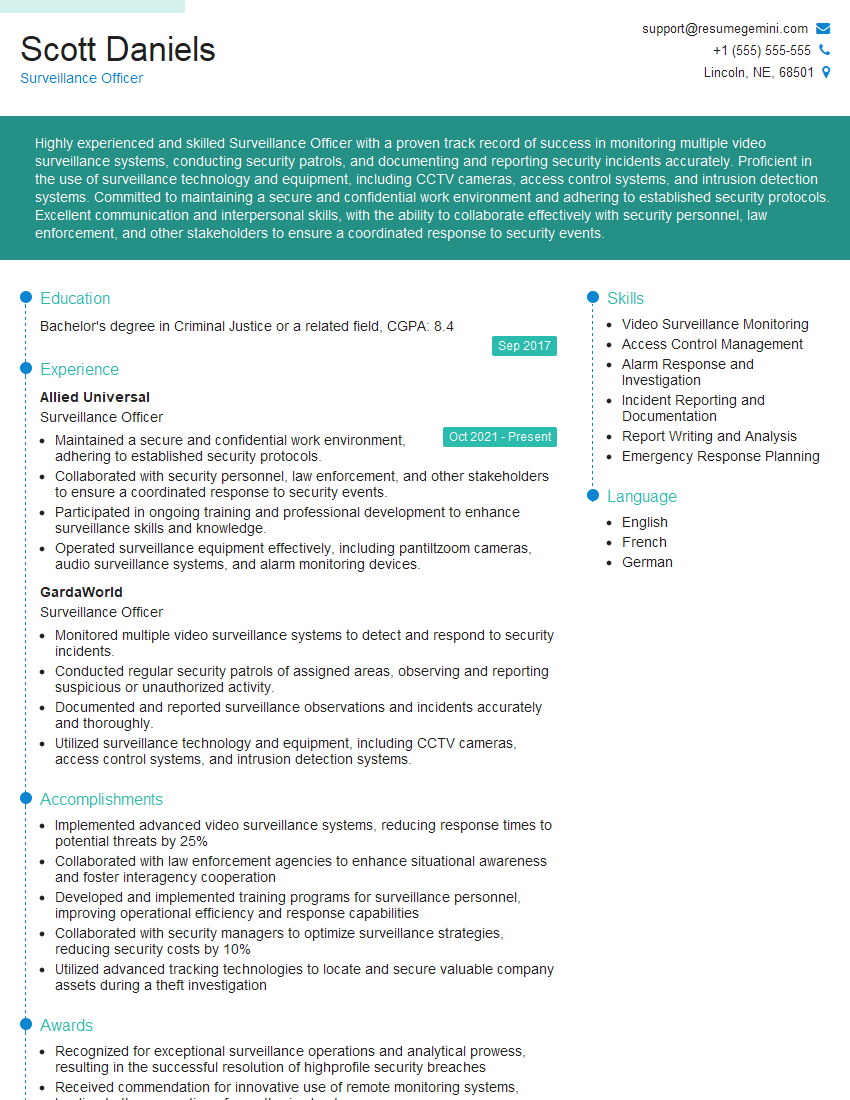
Mastering Intelligence, Surveillance, and Reconnaissance (ISR) Operations significantly enhances your career prospects within the intelligence community and related fields. A strong understanding of these concepts demonstrates valuable skills and expertise sought after by employers. To increase your chances of securing your dream role, creating an ATS-friendly resume is crucial. ResumeGemini is a trusted resource that can help you build a professional and impactful resume tailored to the specific requirements of ISR positions. Examples of resumes optimized for Intelligence, Surveillance, and Reconnaissance (ISR) Operations are available to guide you through the process. Take the next step and craft a resume that highlights your unique qualifications and expertise.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good