The thought of an interview can be nerve-wracking, but the right preparation can make all the difference. Explore this comprehensive guide to Advanced Electronic Warfare Techniques interview questions and gain the confidence you need to showcase your abilities and secure the role.
Questions Asked in Advanced Electronic Warfare Techniques Interview
Q 1. Explain the differences between Electronic Support Measures (ESM), Electronic Attack (EA), and Electronic Protection (EP).
Electronic Warfare (EW) encompasses three core disciplines: Electronic Support Measures (ESM), Electronic Attack (EA), and Electronic Protection (EP). Think of it like a military operation: ESM is intelligence gathering, EA is offensive action, and EP is defense.
ESM (Electronic Support Measures): This involves passively receiving and analyzing electromagnetic emissions to identify, locate, and identify the emitters. It’s like being a spy, listening in on enemy communications to understand their plans and capabilities. Examples include detecting radar signals to determine the type of radar and its location, or intercepting enemy communications to gather intelligence.
EA (Electronic Attack): This is the offensive aspect of EW, actively disrupting or denying enemy systems. It’s the equivalent of launching a counter-offensive, disabling enemy capabilities. Examples include jamming enemy radar to prevent them from tracking friendly aircraft, or disrupting enemy communication networks to hinder their coordination.
EP (Electronic Protection): This focuses on protecting friendly forces from enemy EA. It’s the defensive shield, protecting your own systems. Examples include using jamming techniques to disrupt enemy jamming signals, using low probability of intercept (LPI) radar, or employing stealth technologies to reduce the chances of detection.
Q 2. Describe your experience with different types of radar jamming techniques.
My experience with radar jamming techniques spans various methods, categorized by their approach.
Noise Jamming: This involves broadcasting a wideband noise signal to mask the target’s radar return. It’s the simplest but often least effective method, akin to shouting over someone to drown out their message.
Deceptive Jamming: This technique generates false targets, luring the radar away from the actual target. Imagine creating a decoy to distract an enemy pursuer. Examples include range-gated jamming, which creates false returns at specific ranges, and repeater jamming, where the jammer retransmits the radar signal with a delay.
Swept-Frequency Jamming: This involves rapidly changing the jamming frequency to cover a wide range, making it difficult for the radar to track the jammer. It’s like quickly changing radio channels to prevent someone from intercepting your conversation.
Spot Jamming: This technique focuses on jamming a specific radar frequency, disrupting the specific signal used by a particular radar system.
Self-Screening Jamming: This technique is deployed by the target itself, preventing the radar from effectively tracking its position and velocity. This is analogous to using a shield to deflect an incoming attack.
In practice, effective jamming often involves a combination of these techniques, tailored to the specific radar system and operational context. The selection depends on factors like the enemy’s radar capabilities, the operational environment, and the desired level of disruption.
Q 3. How do you analyze electronic signals to identify threats and vulnerabilities?
Analyzing electronic signals involves a multi-stage process beginning with signal acquisition, followed by signal processing and finally signal exploitation. This requires specialized equipment and expertise.
Signal Acquisition: This stage uses antennas and receivers to capture the electronic signals. The sensitivity, bandwidth, and direction-finding capabilities of the receiving equipment are critical.
Signal Processing: Raw signals are often noisy and require sophisticated digital signal processing (DSP) techniques for filtering, demodulation, and feature extraction. This stage includes techniques like Fourier transforms to determine the frequency content, and waveform analysis to identify modulation types. Advanced algorithms can identify patterns and anomalies.
Signal Exploitation: The processed data is then analyzed to identify the emitter, determine its characteristics (type, location, etc.), and assess potential vulnerabilities. This often involves comparing the acquired signals against a database of known emitters or leveraging machine learning for signal classification.
For example, analyzing the pulse repetition frequency (PRF) and pulse width of a radar signal can help determine its type and range capabilities. Identifying unique modulation schemes or identifying communication protocols allows for identification of the communications systems being used. This analysis enables us to understand the threat landscape and identify vulnerabilities which can then be exploited to design effective countermeasures or to better protect our own systems.
Q 4. What are your experiences with developing and implementing EW countermeasures?
My experience in developing and implementing EW countermeasures involves a systematic approach:
Threat Assessment: Identifying the specific threats and their capabilities is paramount. This involves understanding the enemy’s EW systems, their tactics, and their potential impact on friendly operations.
Countermeasure Design: Based on the threat assessment, appropriate countermeasures are designed. This often involves selecting suitable jamming techniques, designing antennas, and integrating the system with other platforms.
System Integration: The countermeasure system is then integrated with the platform (aircraft, ship, etc.), ensuring seamless operation and compatibility with other systems. This includes considering power requirements, physical space constraints, and electromagnetic compatibility (EMC).
Testing and Evaluation: Rigorous testing is conducted to validate the effectiveness of the countermeasure against the identified threats. This involves simulating realistic operational scenarios and evaluating system performance under various conditions.
Deployment and Maintenance: Once validated, the countermeasure is deployed and requires ongoing maintenance and upgrades to account for evolving threats.
For instance, I was involved in a project where we developed a sophisticated jamming system for a naval vessel to counter advanced radar threats. This involved designing a highly agile jamming system capable of defeating multiple simultaneous threats, requiring careful consideration of frequency agility, power management, and antenna design.
Q 5. Explain the concept of frequency hopping and its application in EW.
Frequency hopping involves rapidly switching between different frequencies to transmit or receive signals. Imagine it like constantly changing radio channels to avoid being intercepted. This technique is crucial in EW for several reasons:
Enhanced Anti-Jamming Capabilities: A jammer targeting a specific frequency will be less effective when the signal is constantly changing frequencies.
Improved Security: Frequency hopping makes it more difficult for adversaries to intercept and decode communications.
Reduced Probability of Intercept (POI): The rapid frequency changes reduce the time a signal spends on any single frequency, making it harder to detect.
In EW, frequency hopping is implemented in various systems, including communication systems and radar systems. The hopping pattern (sequence of frequencies and dwell times) is crucial and is usually designed to be unpredictable, making it difficult for an adversary to predict the next frequency. Sophisticated algorithms and pseudo-random number generators are often employed to create effective hopping patterns.
Q 6. Describe your familiarity with various types of antennas and their applications in EW systems.
My familiarity with antennas in EW systems encompasses various types, each suited for specific applications:
Dipole Antennas: Simple, versatile, and widely used in various EW applications, but their directional characteristics are limited.
Yagi-Uda Antennas: Offer high gain and directivity, making them suitable for both receiving and transmitting signals with high accuracy. Often used for direction-finding and narrowband jamming.
Horn Antennas: Provide good directivity and are commonly used for wideband applications, particularly in radar systems.
Phased Array Antennas: Highly versatile and capable of electronically steering the beam without physically moving the antenna, enabling rapid scanning and beamforming for precise targeting. Essential for modern EW systems.
The choice of antenna depends on factors like the frequency range, desired gain, beamwidth, and size constraints. For example, phased array antennas are preferred in applications requiring fast beam steering and rapid frequency agility, while smaller, simpler antennas might be more appropriate for size-constrained environments.
Q 7. How do you ensure the electromagnetic compatibility (EMC) of EW systems?
Ensuring electromagnetic compatibility (EMC) in EW systems is crucial to prevent interference and ensure reliable operation. It’s like orchestrating a complex symphony where all instruments need to play in harmony.
Shielding: Using conductive enclosures to prevent electromagnetic emissions from interfering with other systems or escaping to unintended locations.
Filtering: Employing filters to block unwanted frequencies and prevent interference from other sources.
Grounding: Providing a low-impedance path to ground to prevent the buildup of static electricity and reduce interference.
Careful Component Selection: Choosing components with appropriate EMC characteristics and using appropriate layouts to minimize electromagnetic interference.
Testing and Verification: Rigorous testing is performed to ensure that the system meets EMC standards and avoids causing interference with other systems. This often involves specialized EMC chambers and testing procedures.
Failure to ensure EMC can lead to system malfunctions, unexpected interference, and compromised operational security. Therefore, careful consideration of EMC throughout the design, development, and testing phases is vital in ensuring the effectiveness and reliability of EW systems.
Q 8. What are the key challenges in integrating EW systems into existing platforms?
Integrating Electronic Warfare (EW) systems into existing platforms presents several significant challenges. These challenges stem from the need to seamlessly blend sophisticated EW capabilities with the platform’s existing architecture, software, and operational constraints. One major hurdle is power consumption; EW systems are power-hungry, potentially exceeding the capacity of smaller platforms.
Another key challenge involves weight and size. Adding bulky EW equipment can negatively impact a platform’s performance and maneuverability. Electromagnetic Compatibility (EMC) is paramount; the EW system must not interfere with the platform’s other electronic systems, and vice versa, requiring careful design and testing. Software integration is also complex, necessitating careful consideration of system interfaces, data formats, and control protocols. Finally, cost and maintenance considerations play a significant role; sophisticated EW systems are expensive to develop, integrate, and maintain, often requiring specialized training and expertise.
For example, integrating advanced jamming capabilities onto a legacy fighter jet might require significant modifications to the aircraft’s structure, power system, and avionics suite. This would entail careful consideration of all the aforementioned challenges, potentially leading to extensive testing and system re-design.
Q 9. Explain your understanding of digital signal processing (DSP) in the context of EW.
Digital Signal Processing (DSP) is the backbone of modern EW systems. It enables the rapid and efficient processing of the vast amounts of radio frequency (RF) data collected by EW receivers. In the context of EW, DSP algorithms are employed for a multitude of tasks, including signal detection, classification, geolocation, and jamming. Imagine trying to find a specific radio station amidst a chaotic mix of broadcasting signals – DSP algorithms perform this crucial function with remarkable precision.
Key DSP techniques used in EW include Fast Fourier Transforms (FFTs) for spectral analysis, adaptive filtering for noise reduction and signal enhancement, and waveform recognition algorithms for identifying threats. The ability to process signals in real-time is critical, making efficient DSP algorithms paramount for effective EW operations. Furthermore, advanced DSP techniques like machine learning and artificial intelligence are increasingly being leveraged to automate complex tasks such as threat identification and response optimization.
//Example of simple FFT application (Conceptual) float[] inputSignal = ...; // Input RF data float[] fftOutput = fft(inputSignal); // Perform FFT //Analyze fftOutput for frequency components Q 10. How do you evaluate the effectiveness of EW systems?
Evaluating the effectiveness of EW systems is a multifaceted process requiring both quantitative and qualitative measures. Quantitative measures might involve analyzing the system’s ability to successfully jam or disrupt enemy communications or radar systems. This can be measured by the reduction in enemy system effectiveness (e.g., a percentage decrease in radar detection range or successful communication attempts). We could also quantify the system’s probability of detection and classification of hostile signals, or its jamming effectiveness against specific threat types.
Qualitative measures focus on broader aspects such as system reliability, ease of use, and maintainability. Real-world operational testing, including field exercises and live-fire tests, are crucial for obtaining realistic performance data. Survivability analysis assesses the EW system’s ability to withstand enemy countermeasures. Data analysis and modeling are crucial in combining quantitative and qualitative assessments to provide a holistic evaluation. In essence, effectiveness is judged by how well the system contributes to achieving the overall mission objectives in a complex operational context.
Q 11. Describe your experience with EW simulation and modeling tools.
My experience encompasses a wide range of EW simulation and modeling tools, including both commercial-off-the-shelf (COTS) and custom-developed solutions. I’ve extensively used tools like MATLAB and its associated toolboxes (e.g., Phased Array System Toolbox, Signal Processing Toolbox) for simulating various aspects of EW systems, from antenna array design and signal propagation to signal processing algorithms and jamming strategies. Moreover, I’ve worked with specialized EW simulators which provide detailed modeling of radar systems, communication networks, and EW countermeasures. These tools enable the analysis of complex scenarios including Electronic Support Measures (ESM), Electronic Attack (EA), and Electronic Protection (EP) in various environments.
Furthermore, I have experience creating custom models using languages like C++ and Python, leveraging libraries like NumPy and SciPy for specific aspects of EW system design and analysis not fully covered by COTS tools. This allows for a deeper level of customization and more precise modelling of particular system components or operational scenarios. These simulations are invaluable for testing and evaluating system performance before costly and time-consuming field trials.
Q 12. What are the ethical considerations in the development and use of EW technologies?
The ethical considerations surrounding EW technologies are significant and multifaceted. The potential for unintended consequences, such as civilian casualties or disruption of essential services, must be carefully considered throughout the entire lifecycle of an EW system – from development to deployment and use.
Ethical frameworks must guide the design and deployment of EW systems, emphasizing proportionality, minimizing collateral damage, and adhering to international laws and norms. Transparency in EW operations is also crucial, with appropriate measures to avoid deception or misinformation. It’s imperative to have clear operational guidelines and rules of engagement to mitigate the risks of escalation and unintended conflict. Regular ethical reviews and audits, independent oversight of EW programs and the involvement of ethicists in the design process, are all crucial to ensuring responsible development and use of these potent technologies. A system might be technically effective, but still ethically questionable if it poses unacceptable risks to non-combatants.
Q 13. How do you address the challenges of EW in contested or congested electromagnetic environments?
Contested or congested electromagnetic environments pose immense challenges to EW operations. The presence of numerous signals, both friendly and hostile, creates significant interference and complicates the detection, identification, and tracking of specific threats. Strategies for addressing these challenges involve advanced signal processing techniques such as adaptive filtering to enhance weak signals in noise and space-time adaptive processing to mitigate interference from multiple sources. Furthermore, advanced algorithms for signal separation and classification are vital.
Cognitive EW is a promising approach, enabling EW systems to adapt and learn in real-time based on the observed electromagnetic environment. Cybersecurity is another crucial aspect, as EW systems are increasingly reliant on networked communications and sophisticated software. Protecting against cyberattacks and ensuring system integrity is crucial for maintaining operational effectiveness. Employing robust communication protocols and employing techniques like frequency hopping and spread spectrum are vital in countering interference and jamming threats.
Q 14. Explain your understanding of different types of electronic warfare threats.
Electronic Warfare threats encompass a wide spectrum of capabilities, broadly categorized into Electronic Support Measures (ESM), Electronic Attack (EA), and Electronic Protection (EP).
- ESM involves passively detecting and identifying enemy electronic emissions, providing crucial intelligence on enemy capabilities and intentions. This includes radar emissions, communication signals, and other electronic signals. Think of it as electronic reconnaissance.
- EA focuses on actively disrupting or denying enemy use of the electromagnetic spectrum. This can range from simple jamming to sophisticated techniques that spoof or deceive enemy systems, potentially causing them to malfunction or provide false information. This involves attacking enemy systems.
- EP involves protecting friendly forces from enemy EA. This includes techniques such as low probability of intercept (LPI) radar, frequency hopping, spread spectrum, and electronic countermeasures (ECM) to jam or deceive enemy systems aiming to disrupt friendly forces. This involves protecting our systems.
Specific threat types within these categories include sophisticated radar systems employing advanced techniques such as pulse compression and low probability of intercept (LPI) technologies, sophisticated communication systems using advanced encryption and frequency agility, and cyber-based attacks targeting EW systems themselves. Each threat necessitates tailored EW countermeasures, and understanding the threat landscape is crucial for effective EW operations.
Q 15. Describe your experience with the development and testing of EW algorithms.
My experience encompasses the entire lifecycle of EW algorithm development, from conception and design through rigorous testing and validation. I’ve worked extensively on algorithms for electronic support measures (ESM), electronic attack (EA), and electronic protection (EP). For example, in one project, we developed a novel algorithm for radar signal identification and classification using advanced signal processing techniques like wavelet transforms and machine learning. This involved developing the algorithm in MATLAB, then transitioning it to a low-latency, real-time embedded system using C++. Rigorous testing involved simulated scenarios using specialized EW testbeds, as well as field testing where the algorithm was integrated into a real-world EW system and evaluated against live radar signals. We used a combination of statistical metrics, such as accuracy, precision, and recall, as well as operational metrics such as time-to-decision to evaluate performance. Another project focused on developing adaptive jamming algorithms to counter sophisticated radar threats. This involved designing algorithms that could learn and adapt to changing radar waveforms in real time.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. How do you ensure the security of EW systems against cyber attacks?
Securing EW systems against cyberattacks is paramount. We employ a multi-layered defense-in-depth strategy. This starts with secure coding practices, implementing rigorous code reviews, and using static and dynamic analysis tools to identify vulnerabilities before deployment. Beyond that, we incorporate robust authentication and authorization mechanisms, including multi-factor authentication and role-based access control, to limit access to sensitive system components. Network security is critical; we utilize firewalls, intrusion detection/prevention systems (IDS/IPS), and regularly monitor network traffic for suspicious activity. Furthermore, we regularly update the firmware and software of EW systems to patch known vulnerabilities. Regular security audits and penetration testing are conducted to identify and mitigate potential weaknesses. Finally, data encryption at rest and in transit is essential to protect sensitive information. Think of it like a castle with multiple layers of walls and defenses, making it significantly harder for attackers to breach.
Q 17. Explain the role of AI and Machine Learning in modern Electronic Warfare.
AI and Machine Learning are revolutionizing modern Electronic Warfare. In ESM, AI algorithms can rapidly analyze massive amounts of RF data to identify threats, classify emitters, and predict their behavior far more efficiently than traditional methods. For instance, AI can identify sophisticated radar signals that are designed to evade traditional signal processing techniques. In EA, AI enables the development of intelligent jamming techniques that adapt to the enemy’s tactics and dynamically optimize jamming parameters to maximize effectiveness. AI can even learn to anticipate enemy responses and proactively adjust jamming strategies. In EP, AI can predict potential threats and optimize the electronic protection measures, automatically adjusting the system’s configuration to minimize vulnerability. Machine learning algorithms, trained on large datasets of radar signals and jamming techniques, empower EW systems to autonomously adapt to complex and evolving threat environments. Imagine a self-learning system that continuously improves its performance through experience, identifying new threats and responding effectively, ultimately providing a decisive advantage on the battlefield.
Q 18. Describe your experience with EW system maintenance and troubleshooting.
My experience in EW system maintenance and troubleshooting involves both hardware and software aspects. Hardware maintenance includes preventative maintenance tasks like cleaning, component replacement, and calibrating sensitive equipment. Troubleshooting involves systematically identifying the source of malfunctions using diagnostic tools and techniques. For software troubleshooting, I use debugging tools and methodologies, analyzing log files, and working closely with software engineers to resolve issues. During a recent field operation, we experienced an unexpected system failure. Using a combination of diagnostic tools and logs, we isolated the problem to a faulty power supply unit, replacing it quickly to restore functionality. A systematic approach, coupled with a deep understanding of the system architecture, is key to resolving complex problems in a timely manner.
Q 19. What are the key performance indicators (KPIs) for EW systems?
Key Performance Indicators (KPIs) for EW systems vary depending on the specific mission. However, common KPIs include:
- Probability of Intercept (POI): The likelihood of detecting an enemy signal.
- Probability of Kill (Pk): The likelihood of successfully jamming or neutralizing an enemy signal.
- False Alarm Rate (FAR): The rate at which the system generates false alarms.
- Time-to-Decision (TTD): The time it takes for the system to identify and respond to a threat.
- System Availability: The percentage of time the system is operational.
- Mean Time Between Failures (MTBF): A measure of the system’s reliability.
Q 20. How do you handle unexpected situations or malfunctions during EW operations?
Handling unexpected situations during EW operations requires a calm, systematic approach. My training emphasizes a structured troubleshooting methodology, starting with an assessment of the situation and its potential impact. This involves gathering all available data (system logs, sensor readings, etc.) to determine the root cause. The next step is to prioritize actions based on the severity of the problem. If the malfunction is critical, immediate countermeasures may be implemented, while less critical issues can be addressed later. Clear communication within the team is vital; keeping everyone informed and coordinating actions helps ensure a swift and efficient resolution. Finally, after resolving the issue, a post-incident review is conducted to identify lessons learned and prevent similar situations from occurring in the future. This approach transforms a potentially chaotic situation into a controlled and effective response.
Q 21. Explain your understanding of spectrum management and its relevance to EW.
Spectrum management is the process of regulating and controlling the use of the radio frequency (RF) spectrum. It’s critical to EW because effective EW operations depend heavily on the availability and use of specific frequencies. Efficient spectrum management ensures that friendly forces have access to the necessary frequencies for their EW systems while minimizing interference and maximizing operational effectiveness. Conversely, understanding enemy spectrum usage is crucial for effective EA and EP strategies. For example, identifying gaps in enemy spectrum allocation can help optimize our jamming strategies or find frequencies for our own communication systems. Lack of coordination can lead to friendly fire incidents, where one system interferes with another. Therefore, careful planning and coordination of spectrum usage across all systems is vital for mission success. The process often involves detailed analysis of the electromagnetic environment, including both natural and man-made interference sources. This contributes to developing robust and effective EW strategies.
Q 22. Describe your experience with different types of EW platforms (e.g., airborne, ground, naval).
My experience spans various EW platforms, encompassing airborne, ground, and naval systems. In airborne EW, I’ve worked extensively with systems integrated onto platforms like fighter jets and AWACS aircraft, focusing on jamming, electronic support measures (ESM), and electronic attack (EA). This involved analyzing radar signals, developing countermeasures, and optimizing system performance in diverse operational environments. Ground-based EW has been another key area, where I’ve been involved in designing and deploying fixed and mobile systems for battlefield surveillance and protection. This included integrating sensors, command-and-control systems, and developing strategies for effective jamming and deception. Finally, my naval EW experience includes working on shipboard systems, concentrating on protecting naval assets from enemy radar and missile threats. This involved understanding the unique challenges of maritime environments, such as the propagation of electromagnetic waves over water, and designing effective countermeasures. Each platform presents unique challenges related to size, power constraints, and environmental factors, requiring specialized system design and operational strategies.
For example, airborne platforms demand highly compact and lightweight systems, while ground-based systems can be larger and more robust. Naval systems must withstand harsh maritime conditions, including salt spray and vibrations. My work has included addressing these specific challenges across different platforms to optimize EW effectiveness.
Q 23. How do you stay updated with the latest advancements in EW technologies?
Staying updated in the rapidly evolving field of EW necessitates a multi-pronged approach. I regularly attend conferences like the IEEE International Symposium on Phased Array Systems and Technology, and various defense industry trade shows to learn about the latest advancements. I also actively participate in professional organizations like the Association of Old Crows, which offers access to peer-reviewed publications, workshops, and networking opportunities with leading experts. Furthermore, I subscribe to specialized journals and technical publications, focusing on areas like cognitive EW, AI-driven signal processing, and advanced jamming techniques. Open-source intelligence (OSINT) analysis plays a significant role, allowing me to track technological developments and emerging threats from various sources. Finally, I constantly engage in self-directed learning, exploring new research papers and online courses to remain at the forefront of this dynamic field.
Q 24. What are the legal and regulatory frameworks governing the use of EW?
The legal and regulatory framework governing EW is complex and varies considerably depending on the jurisdiction and specific application. International law, particularly the laws of armed conflict, significantly impact the use of EW in military settings. The principles of proportionality and distinction are paramount, emphasizing the need to minimize harm to civilians and civilian infrastructure. National laws and regulations further define the permissible use of EW within a country’s borders and in international operations. For example, many nations have strict regulations governing the use of jamming against civilian communications systems. International treaties and agreements, such as the International Telecommunication Union (ITU) Radio Regulations, also set standards for the use of the radio frequency spectrum and aim to prevent harmful interference. Compliance with these regulations is crucial, requiring careful planning, coordination, and ongoing monitoring of EW activities to ensure legality and mitigate any potential risks.
A key aspect is ensuring that EW operations do not cause undue interference with essential services like air traffic control or emergency communications. The potential for unintended consequences necessitates rigorous testing, robust risk assessments, and adherence to established protocols.
Q 25. Explain the concept of cognitive Electronic Warfare.
Cognitive Electronic Warfare (CEW) represents a significant advancement over traditional EW techniques. Unlike conventional EW, which relies on pre-programmed responses to known threats, CEW uses artificial intelligence (AI) and machine learning (ML) to adapt and learn in real-time. This involves the use of algorithms that can analyze vast amounts of data from diverse sources, including radar signals, communication intercepts, and geospatial information, to identify patterns, predict enemy behavior, and optimize countermeasures. This allows for a more dynamic and effective response to unforeseen threats, particularly in complex and rapidly changing environments. Imagine a scenario where an enemy employs a novel jamming technique. A traditional EW system might be ineffective, but a CEW system could quickly learn the characteristics of the new jamming signal, adapt its countermeasures, and neutralize the threat.
Key components of CEW include advanced signal processing, AI-driven decision-making, and automated countermeasure selection. The ability to learn and adapt autonomously is a defining characteristic of CEW, making it significantly more resilient and effective against sophisticated adversaries. It’s important to note that the development and deployment of CEW require substantial computational power and sophisticated algorithms, leading to ongoing research and development in this critical area.
Q 26. Describe your experience with collaborative EW systems and network-centric warfare.
My experience with collaborative EW systems and network-centric warfare is extensive. In modern warfare, EW is rarely a stand-alone activity; it’s deeply integrated with other aspects of military operations. Effective EW relies on seamless information sharing and coordination across various platforms and units. I’ve worked on projects involving the integration of EW systems into larger network-centric environments, leveraging data fusion from multiple sensors and platforms to provide a comprehensive situational awareness picture. This enables better decision-making, optimized resource allocation, and enhanced overall effectiveness. For instance, a ground-based EW system might detect an enemy radar, share that information with airborne platforms, which in turn use their EW capabilities to suppress the threat while simultaneously providing targeting information for friendly forces.
The ability to share data in real-time is crucial, necessitating the use of secure communication networks and standardized data formats. Furthermore, collaborative EW necessitates robust cybersecurity measures to protect sensitive information and prevent unauthorized access or manipulation. Effective collaboration requires clear communication protocols, standardized data formats, and a well-defined command structure to ensure that all EW assets are coordinated and contribute to the overall operational objectives.
Q 27. How do you manage risk and uncertainty in EW projects?
Managing risk and uncertainty in EW projects requires a structured approach. We begin by identifying potential risks through thorough risk assessments, considering factors such as technological limitations, environmental conditions, and adversary capabilities. These assessments involve analyzing historical data, modeling potential scenarios, and leveraging expertise from various domains. Mitigation strategies are then developed to address these risks, which could involve selecting robust technologies, implementing redundancy, and developing contingency plans. Regular testing and evaluation are critical throughout the project lifecycle, enabling us to validate our assumptions, identify unforeseen issues, and adapt our strategies as necessary. Uncertainty is managed through scenario planning, exploring a range of possible outcomes and developing flexible responses to adapt to changing conditions. This iterative process allows us to refine our approach and minimize the impact of unforeseen events.
For example, when integrating a new EW system onto an aircraft, we would consider risks associated with weight and power limitations, electromagnetic interference, and the system’s performance in extreme weather conditions. Mitigation strategies could involve careful system design, rigorous testing, and the implementation of backup systems.
Q 28. Explain your understanding of the impact of EW on military operations.
Electronic Warfare profoundly impacts military operations, influencing nearly every aspect of the battlespace. At its core, EW provides situational awareness by detecting and identifying enemy radar and communication systems. This information is crucial for planning operations, avoiding detection, and targeting enemy assets. Offensive EW capabilities, such as jamming and deception, can degrade enemy systems, disrupt communication, and protect friendly forces. Defensive EW capabilities safeguard friendly assets from enemy attacks by detecting and countering threats. The effectiveness of EW can significantly impact the outcome of battles, influencing the success of offensive and defensive operations. Consider a scenario where an enemy is using a sophisticated air defense system. Effective EW could suppress that system, enabling friendly aircraft to penetrate enemy airspace and execute their mission. Conversely, a lack of effective EW could lead to significant losses in both personnel and equipment.
Furthermore, the integration of EW with other military capabilities, such as cyber warfare and intelligence gathering, enhances the overall operational effectiveness. Successful EW operations necessitate advanced signal processing techniques, sophisticated algorithms, and highly trained personnel. The ever-evolving nature of EW necessitates continuous adaptation and improvement to maintain a technological advantage in the increasingly complex battlespace.
Key Topics to Learn for Advanced Electronic Warfare Techniques Interview
- Electronic Attack (EA): Understanding various EA techniques, including jamming, spoofing, and deception. Explore the theoretical underpinnings of these methods and their practical applications in modern conflicts.
- Electronic Protection (EP): Mastering EP strategies, focusing on methods to mitigate the effects of enemy EA. Analyze different countermeasures and their effectiveness in various scenarios. Consider practical challenges in implementing EP systems.
- Electronic Support (ES): Develop a strong understanding of signal intelligence (SIGINT) gathering, analysis, and interpretation. Discuss practical applications of ES in situational awareness and targeting.
- Cyber Electromagnetic Activities (CEMA): Explore the intersection of cyber warfare and electronic warfare, understanding the vulnerabilities and potential exploitation within networked systems.
- Advanced Signal Processing Techniques: Familiarize yourself with digital signal processing (DSP) algorithms and their application in EW systems. Prepare to discuss practical applications and challenges related to signal identification and classification.
- EW System Design and Integration: Understand the principles of designing and integrating EW systems into platforms. Consider the challenges of system compatibility and performance optimization.
- EW Doctrine and Strategy: Familiarize yourself with current EW doctrine and strategic applications in modern military operations. Be prepared to discuss the ethical considerations involved.
- Problem-solving and analytical skills: Practice applying your knowledge to complex EW scenarios, demonstrating your ability to troubleshoot and devise effective solutions under pressure.
Next Steps
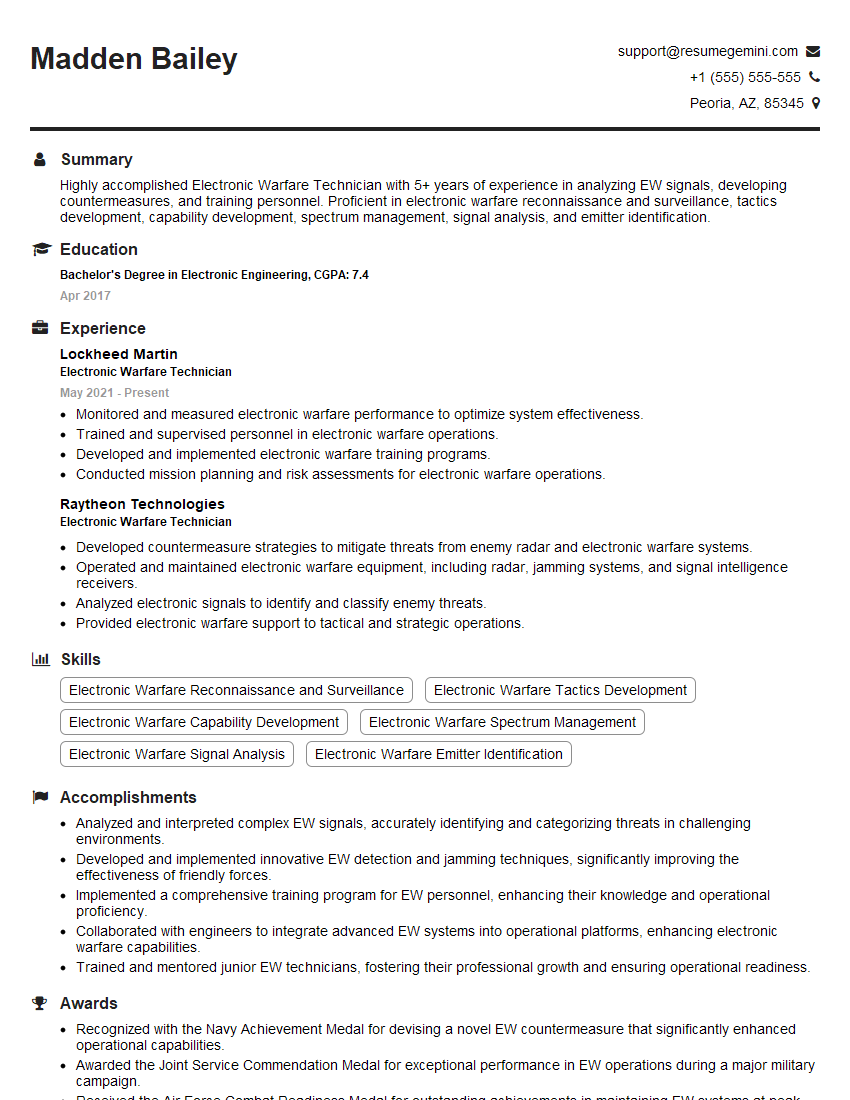
Mastering Advanced Electronic Warfare Techniques opens doors to exciting and impactful careers in defense and technology. To maximize your job prospects, a well-crafted, ATS-friendly resume is crucial. ResumeGemini is a trusted resource that can help you build a professional resume that showcases your skills and experience effectively. ResumeGemini provides examples of resumes tailored to Advanced Electronic Warfare Techniques, ensuring your application stands out from the competition. Invest time in crafting a compelling narrative that highlights your unique contributions and achievements in this field – it’s an investment in your future success.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good