Cracking a skill-specific interview, like one for AllSource Intelligence Analysis, requires understanding the nuances of the role. In this blog, we present the questions you’re most likely to encounter, along with insights into how to answer them effectively. Let’s ensure you’re ready to make a strong impression.
Questions Asked in AllSource Intelligence Analysis Interview
Q 1. Explain the difference between Open Source Intelligence (OSINT) and Human Intelligence (HUMINT).
Open Source Intelligence (OSINT) and Human Intelligence (HUMINT) are two distinct but often complementary intelligence gathering methods. OSINT focuses on publicly available information, like news articles, social media posts, government reports, and academic papers. Think of it as detective work using readily accessible clues. HUMINT, on the other hand, relies on information gathered from human sources, often through direct interaction with individuals or networks. This involves cultivating relationships, conducting interviews, and managing informants – essentially, building a network of trusted contacts to gain insights.
The key difference lies in the source and accessibility of information. OSINT is passive and requires analysis of existing data, while HUMINT is active and necessitates direct human interaction, often involving considerable risk and relationship management. For example, analyzing Twitter feeds for public sentiment regarding a political event is OSINT, while interviewing a government official for inside information is HUMINT.
Q 2. Describe your experience with data analysis techniques used in All-Source Intelligence.
My experience with data analysis in All-Source Intelligence involves a multi-faceted approach. I’m proficient in various techniques, including:
- Statistical Analysis: Identifying trends and patterns within large datasets from diverse sources by employing techniques such as regression analysis, correlation analysis, and anomaly detection. For example, identifying a spike in certain online searches correlated with a specific event.
- Network Analysis: Mapping relationships between individuals, organizations, or events to reveal connections and influence networks. I’ve used tools to visualize and analyze these relationships, uncovering hidden links and key players in complex situations.
- Text Mining and Natural Language Processing (NLP): Extracting meaningful information from unstructured textual data, like news reports or social media posts, through techniques such as sentiment analysis and topic modeling. This helps us understand public opinion or the narrative surrounding a particular event.
- Geospatial Analysis: Using geographic information systems (GIS) to analyze the spatial distribution of events, assets, or actors. This is crucial for understanding operational contexts and predicting future actions.
I also integrate these techniques iteratively, refining analysis based on new information and feedback. This allows for a dynamic and adaptive approach to intelligence analysis.
Q 3. How do you evaluate the credibility and reliability of information from different sources?
Evaluating the credibility and reliability of information is paramount in All-Source Intelligence. My approach involves a multi-layered assessment:
- Source Assessment: Determining the reputation, bias, and potential motives of the information source. Is it a known reliable news agency, a biased blog, or a potential disinformation campaign?
- Methodological Assessment: Examining how the information was obtained. Was it through direct observation, hearsay, or analysis of other sources? The method significantly impacts the reliability.
- Cross-Referencing: Corroborating information from multiple independent sources to verify accuracy and identify inconsistencies. Confirmation from diverse, trusted sources drastically enhances confidence.
- Content Analysis: Scrutinizing the information itself for internal consistency, plausibility, and potential manipulation. This includes checking for logical fallacies or indicators of propaganda.
I use a weighted scoring system to combine these assessments, providing a comprehensive reliability score for each piece of information. This ensures a more objective and informed analysis.
Q 4. What are the key challenges in fusing data from diverse intelligence sources?
Fusing data from diverse sources presents several key challenges:
- Data Inconsistency: Different sources may use varying formats, terminology, and levels of detail, making integration difficult. Standardization and data cleaning are crucial.
- Data Redundancy and Completeness: Some sources may overlap significantly, while others might contain missing information. Managing redundancy and addressing gaps requires careful planning and resource allocation.
- Data Bias and Inaccuracy: Sources may have inherent biases or inaccuracies, requiring critical evaluation and weighting during fusion.
- Data Security and Privacy: Protecting sensitive information during the fusion process while ensuring compliance with regulations is critical.
- Technological Limitations: Integrating various data formats and software tools can present technical difficulties.
Addressing these challenges often requires a combination of technical solutions (e.g., data standardization tools, secure data platforms) and analytical skills (e.g., data cleaning, quality control, and conflict resolution).
Q 5. Explain your understanding of the intelligence cycle.
The intelligence cycle is a cyclical process involving six key steps:
- Planning and Direction: Identifying the intelligence requirements and establishing priorities. What information do we need, and why?
- Collection: Gathering raw data from various sources, including OSINT, HUMINT, SIGINT (signals intelligence), IMINT (imagery intelligence), and MASINT (measurement and signature intelligence).
- Processing: Converting raw data into a usable format. This involves cleaning, organizing, and categorizing the information.
- Analysis and Production: Interpreting the processed information to create an intelligence product that answers the initial requirements. This includes identifying patterns, drawing inferences, and assessing implications.
- Dissemination: Sharing the intelligence product with relevant decision-makers in a timely and appropriate manner.
- Feedback: Evaluating the effectiveness of the intelligence product and using the feedback to improve future cycles. Did it meet the initial needs? What adjustments are required?
It’s a continuous loop, with each stage informing and refining the others. Think of it as a feedback mechanism for iterative improvement.
Q 6. Describe your experience with specific intelligence analysis tools and software.
I have extensive experience with various intelligence analysis tools and software, including:
- Palantir Gotham: A powerful platform for data integration, analysis, and visualization. I have used it to analyze large datasets from various sources, identify patterns, and build predictive models.
- Maltego: A link analysis tool that facilitates the visualization and analysis of relationships between entities. Useful for mapping networks and identifying key players.
- Open-Source intelligence tools: I am proficient in using a range of tools for web scraping, social media monitoring, and data extraction from various online sources. This includes tools like
python libraries like Scrapy and Beautiful Soup. - GIS software (e.g., ArcGIS): For geospatial analysis and visualizing data on maps. This is crucial for understanding location-based patterns.
My proficiency extends beyond simply using these tools; I understand their limitations and biases, applying them strategically to maximize analytical efficacy.
Q 7. How do you handle conflicting information from different sources?
Handling conflicting information requires a systematic approach:
- Identify and Document: First, clearly identify the conflicting pieces of information and document the source for each. What are the specific points of disagreement?
- Evaluate Sources: Assess the credibility and reliability of each source using the methods described previously. Which sources are more trustworthy?
- Reconcile Discrepancies: Try to identify the root cause of the conflict. Is it due to biases, errors, or deliberate misinformation? Can the conflict be resolved by additional information or a more nuanced interpretation?
- Qualitative Assessment: If the conflict cannot be resolved conclusively, a qualitative judgment might be necessary. Which piece of information is more plausible or supports the overall analytical picture?
- Transparency: Document all conflicting information and the reasoning behind the final assessment. This allows for transparency and traceability, which is crucial for effective intelligence work.
Remember, acknowledging uncertainty and highlighting conflicting information demonstrates critical thinking and intellectual honesty. It is better to acknowledge uncertainty than to present a potentially misleading, overconfident conclusion.
Q 8. How do you prioritize intelligence requirements and allocate resources effectively?
Prioritizing intelligence requirements and allocating resources effectively is crucial for maximizing impact. It’s like running a well-oiled machine; you need the right parts in the right places at the right time. I use a multi-step process. First, I analyze incoming requests, assessing their urgency, relevance to overall strategic goals, and the potential impact of fulfilling them. This involves a careful consideration of the available resources – personnel, technology, time, and budget. I then employ a prioritization matrix, often using a combination of factors like impact, feasibility, and urgency, to rank the requests. A simple example would be a 3×3 matrix, scoring each factor (low, medium, high) and calculating a weighted score. Requests with high scores receive priority. Finally, I allocate resources based on these priorities, ensuring transparency and accountability throughout the process. This may involve negotiating timelines or adjusting resource allocation as new information emerges.
For example, in a situation where we’re investigating a potential cyberattack, a request for real-time threat monitoring would understandably take precedence over a request for a long-term analysis of social media trends. This is because the immediate threat requires immediate action and resource allocation.
Q 9. Describe your approach to writing clear and concise intelligence reports.
Clear and concise intelligence reporting is vital for effective decision-making. Imagine receiving a lengthy, ambiguous report – it’s frustrating and counterproductive! My approach focuses on providing the most relevant information in a structured and easily digestible manner. I start by clearly defining the audience and their needs. This determines the level of technical detail and the type of analysis required. The report then follows a standardized format: Executive Summary, Background, Analysis, Findings, and Conclusions/Recommendations. Each section is concise, using strong verbs and avoiding jargon whenever possible. Visual aids, such as charts and maps, are used to enhance understanding, making complex data more accessible. I always review and edit the report multiple times, focusing on clarity, accuracy, and brevity. Finally, I rigorously check for grammatical errors and typos, maintaining professional standards.
For instance, when reporting on potential threats to national security, I would ensure the executive summary clearly outlines the identified threats, their potential impact, and recommended countermeasures. The full report would then provide detailed background information and supporting evidence.
Q 10. How do you ensure the security and confidentiality of sensitive intelligence information?
Securing sensitive intelligence information is paramount. It’s like guarding a national treasure – negligence can have devastating consequences. My approach is multi-layered, incorporating robust physical, technical, and procedural security measures. Physical security involves access controls, secure storage facilities, and stringent handling procedures. Technical security encompasses data encryption, access controls (usernames, passwords, multi-factor authentication), and secure networks and databases. Regular security audits and vulnerability assessments are integral components of this strategy. Procedurally, I strictly adhere to ‘need-to-know’ protocols, ensuring information is only accessible to authorized personnel. Regular training on security awareness is provided to staff to reinforce these measures and to address emerging threats. Furthermore, data destruction protocols are rigorously followed when information is no longer required, minimizing the risk of breaches.
Q 11. What are some ethical considerations in All-Source Intelligence analysis?
Ethical considerations are at the heart of All-Source Intelligence analysis. It’s about using our powers responsibly and ethically. We must adhere to strict guidelines and regulations, ensuring that intelligence gathering and analysis are conducted lawfully and ethically. Key ethical considerations include respecting privacy, protecting human rights, and ensuring the accuracy and objectivity of our assessments. We must avoid bias and ensure transparency in our methodologies and findings. Misinformation, manipulation of data, and the potential for misuse of intelligence are critical concerns. Therefore, we maintain rigorous quality control procedures and follow strict ethical guidelines to prevent the spread of misinformation. In addition, we are always aware of the potential for our findings to be misused and take steps to mitigate that risk.
Q 12. Describe your experience with geospatial intelligence (GEOINT) analysis.
I have extensive experience utilizing geospatial intelligence (GEOINT), which involves analyzing imagery, maps, and geographic data to understand events and locations. My experience includes using GEOINT software to interpret satellite imagery, aerial photographs, and maps to identify patterns, track movements, and assess infrastructure. I’ve utilized this to support various operations, including identifying potential terrorist training camps, tracking the movement of illicit goods, and assessing the impact of natural disasters. I’m proficient in using various GEOINT tools and techniques, such as image analysis, georeferencing, and 3D modeling, to create compelling visualizations and enhance situational understanding. For example, during a crisis response, I used GEOINT to rapidly assess the extent of damage to infrastructure, helping to prioritize relief efforts.
Q 13. How do you identify and assess potential threats and risks?
Identifying and assessing potential threats and risks is a core function of intelligence analysis. I employ a structured approach, combining open-source intelligence (OSINT), human intelligence (HUMINT), and other relevant sources. This begins with identifying potential threats through careful analysis of intelligence reports, news articles, social media, and other open sources. The next step is to assess these threats, considering their likelihood, potential impact, and vulnerability of targets. This often involves creating threat models to visualize potential scenarios and their consequences. I use a variety of analytical frameworks and methodologies to perform these assessments. Finally, I provide recommendations for mitigating identified risks, balancing cost-effectiveness and potential impact. For instance, in identifying a potential cyber threat, I might analyze network traffic, vulnerability databases, and threat intelligence feeds to understand the nature of the threat, its potential impact, and recommended mitigation strategies.
Q 14. What strategies do you use to identify and analyze patterns and trends in data?
Identifying and analyzing patterns and trends in data is at the core of All-Source Intelligence. I employ a variety of techniques, including data mining, statistical analysis, and network analysis. Data mining involves using algorithms to uncover hidden patterns and relationships within large datasets. Statistical analysis helps to quantify those patterns and assess their significance. Network analysis helps in understanding connections between individuals, groups, and events. I utilize specialized software and tools to support this analysis. Furthermore, visualization techniques, like creating charts, graphs, and maps, are crucial for communicating findings. For example, in analyzing social media data, I might use network analysis to identify key influencers and potential hotspots of unrest, facilitating early warning of potential conflicts or events. The process is iterative, often requiring adjustments based on new findings and evolving circumstances.
Q 15. How do you stay current with the latest developments in the intelligence field?
Staying current in the dynamic field of intelligence requires a multi-pronged approach. It’s not just about reading reports; it’s about actively engaging with the community and the information itself. I leverage several key strategies:
- Subscription to leading journals and publications: I regularly subscribe to and thoroughly read publications such as Studies in Intelligence (CIA), Intelligence and National Security, and other relevant academic journals. This keeps me abreast of theoretical advancements and emerging trends.
- Attendance at conferences and workshops: Participating in industry conferences and workshops provides invaluable networking opportunities and exposure to the latest research and best practices. I actively engage in discussions and learn from leading experts in the field.
- Online communities and professional networks: I am an active member of online professional groups and forums where analysts share insights, discuss current events, and debate methodologies. These platforms are crucial for staying informed about breaking developments and diverse perspectives.
- Continuous learning through online courses and webinars: Platforms like Coursera, edX, and various government and university offerings provide excellent opportunities for skill enhancement and knowledge updates in specific areas like data analytics, geopolitical analysis, and emerging technologies relevant to intelligence.
- Monitoring open-source intelligence (OSINT) proactively: I consistently monitor key OSINT sources to identify emerging trends and potential threats, utilizing a variety of tools and techniques to collect and analyze information efficiently.
This holistic approach ensures I remain at the forefront of the intelligence field, effectively adapting to evolving threats and technologies.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. Explain your understanding of different intelligence collection methods.
Intelligence collection methods are diverse and constantly evolving. They can be broadly categorized as:
- Human Intelligence (HUMINT): This involves gathering information from human sources, through methods like interviews, debriefings, and covert operations. This is often the most valuable but also the riskiest method. For example, recruiting a source within a terrorist organization to provide information on their plans.
- Signals Intelligence (SIGINT): This focuses on intercepting and analyzing communications, such as radio transmissions, satellite communications, and internet traffic. Think intercepting encrypted communications to gain insight into a foreign government’s plans.
- Open Source Intelligence (OSINT): This involves analyzing publicly available information, such as news articles, social media posts, academic publications, and government documents. This is a crucial method due to its readily accessible nature and often overlooked wealth of information.
- Imagery Intelligence (IMINT): This utilizes satellite imagery, aerial photography, and other visual data to gather information on geographic locations, infrastructure, and military movements. An example would be analyzing satellite images to track the movement of troops or equipment.
- Measurement and Signature Intelligence (MASINT): This involves analyzing technical data such as electromagnetic emissions, acoustic signals, or nuclear radiation to identify objects or events. This could involve using acoustic sensors to detect the launch of a missile.
- Cyber Intelligence (CYINT): This involves gathering information from the cyberspace, analyzing data from computer networks, databases, and social media platforms. This is increasingly important in today’s digital world, allowing analysts to track cyber threats and malicious actors.
Effective intelligence analysis often involves integrating data from multiple sources, combining HUMINT insights with technical data from SIGINT or IMINT, for a more comprehensive picture.
Q 17. How familiar are you with various data visualization techniques for presenting intelligence findings?
Data visualization is paramount for effectively communicating intelligence findings. I’m proficient in a wide range of techniques, selecting the most appropriate method depending on the data and audience. My experience includes:
- Maps and Geographic Information Systems (GIS): Using GIS software to visualize geographic data, such as the location of terrorist attacks or the spread of a disease.
- Charts and graphs: Employing various charts like bar charts, line graphs, and scatter plots to display trends, patterns, and correlations within the data, for instance, to show the relationship between economic indicators and political instability.
- Networks and relationship diagrams: Visualizing complex relationships between individuals, organizations, or entities using network graphs. This allows understanding complex networks like terrorist cells or financial transactions.
- Sankey diagrams: Illustrating flows and relationships between different data points, such as the movement of resources or the flow of information within a network.
- Infographics: Creating visually appealing and easily understandable summaries of complex information, combining multiple visual elements for effective communication.
The key is to choose the visualization method that best communicates the story, ensuring clarity, accuracy, and impact for the intended audience. Overly complex visualizations can be counterproductive, so simplicity and clarity are crucial.
Q 18. Describe your experience with predictive intelligence analysis.
Predictive intelligence analysis involves forecasting future events based on current and historical data. It’s not about predicting the future with certainty, but rather assessing probabilities and identifying potential scenarios. My experience includes:
- Trend analysis: Identifying long-term trends and patterns to extrapolate potential future developments. For example, analyzing population growth trends in a region to predict potential resource scarcity or migration patterns.
- Scenario planning: Developing multiple potential future scenarios based on different assumptions and variables. This helps to prepare for a range of possibilities, such as planning for different outcomes of a potential political crisis.
- Statistical modeling: Using statistical methods to identify correlations and predict probabilities. This might involve predicting the likelihood of a specific event based on various predictive indicators.
- Machine learning algorithms: Leveraging machine learning techniques to analyze large datasets and identify patterns that may not be easily discernible by humans. This could involve using algorithms to detect patterns of suspicious financial transactions.
The effectiveness of predictive analysis relies heavily on the quality and completeness of the data, as well as the appropriate selection and application of analytical methods. The outcome is not a definitive prediction, but a range of possibilities and probabilities to inform decision-making.
Q 19. How do you incorporate social media intelligence into your analysis?
Social media intelligence (SOCMINT) is a critical component of modern intelligence analysis. I utilize SOCMINT by:
- Monitoring relevant hashtags and keywords: Tracking conversations and trends related to specific topics, events, or individuals. This could involve monitoring hashtags related to a specific political movement or a natural disaster.
- Identifying key influencers and opinion leaders: Analyzing the influence and reach of individuals and groups on social media platforms to understand the spread of information and the formation of public opinion.
- Sentiment analysis: Assessing the overall sentiment (positive, negative, neutral) expressed towards particular topics or individuals. This helps to gauge public perception of certain events or policies.
- Network analysis: Identifying connections and relationships between individuals and groups based on their social media activity. This can reveal hidden networks or relationships relevant to intelligence gathering.
- Utilizing specialized SOCMINT tools: Employing various tools and techniques to efficiently collect, process, and analyze social media data, respecting ethical considerations and legal boundaries.
However, it’s crucial to be aware of the limitations of SOCMINT. Data on social media can be biased, unreliable, and easily manipulated. Therefore, verification and triangulation with other sources are essential for accurate analysis.
Q 20. Describe your experience with intelligence assessments and briefings.
I have extensive experience in preparing intelligence assessments and delivering briefings. My approach focuses on clarity, accuracy, and impact. This includes:
- Thorough research and analysis: I conduct thorough research to ensure the accuracy and completeness of the information presented in the assessment or briefing.
- Clear and concise writing: I prioritize clear and concise writing, avoiding jargon and technical terms whenever possible, ensuring the information is easily understood by the intended audience.
- Structured presentation: I utilize a structured approach to presenting information, typically using a logical flow that begins with the key findings and then moves into supporting details and evidence.
- Data visualization: I incorporate appropriate data visualization techniques to enhance the understanding and impact of the information, tailoring visuals to the specific audience and context.
- Tailoring the communication to the audience: I carefully tailor the content and delivery of the briefing to meet the specific needs and level of understanding of the audience, ensuring the information is relevant and accessible.
I’ve presented briefings to various audiences, from senior executives to technical specialists, always adapting my style and content to ensure effective communication of complex intelligence information.
Q 21. How do you handle pressure and tight deadlines in an intelligence setting?
The intelligence field often involves working under pressure and tight deadlines. My approach to managing this involves:
- Prioritization and time management: I effectively prioritize tasks, focusing on the most critical elements first and managing my time efficiently. This includes breaking down large tasks into smaller, manageable components.
- Effective communication and collaboration: I maintain open communication with my team and stakeholders, ensuring everyone is informed and working towards the same goals. Collaboration is key to managing workload effectively.
- Stress management techniques: I utilize various stress management techniques, such as mindfulness and regular exercise, to maintain my focus and productivity under pressure. It’s crucial to maintain well-being during high-stress periods.
- Flexibility and adaptability: I remain flexible and adaptable, recognizing that priorities can shift rapidly in the intelligence world. The ability to adjust plans and strategies as needed is essential.
- Automation and tools: I leverage various analytical tools and automation techniques to streamline my workflows and increase efficiency. This saves time and reduces manual effort, allowing for quicker delivery under tight deadlines.
By combining efficient work practices with self-care strategies, I maintain productivity and accuracy even under significant time pressure.
Q 22. How familiar are you with specific intelligence community directives and regulations?
My familiarity with intelligence community directives and regulations is extensive. I’ve worked directly with documents such as Executive Order 12333 (governing intelligence activities), and understand the implications of the Privacy Act and other relevant legislation regarding the handling of sensitive information. This understanding informs every aspect of my analytical work, from data collection and analysis to reporting and dissemination. For example, I understand the strict guidelines surrounding the use of human intelligence (HUMINT) and the necessary oversight to ensure compliance and protect sources and methods. I am also well-versed in the specific regulations governing the handling of classified information at different classification levels, ensuring appropriate security protocols are followed at all times. This includes understanding the specific markings, storage, and dissemination requirements for classified data.
Q 23. How do you collaborate effectively with analysts from different disciplines?
Effective collaboration with analysts from different disciplines is crucial in all-source intelligence. I approach this by focusing on clear communication, active listening, and a strong understanding of each discipline’s unique perspectives and methodologies. For instance, when working with a signals intelligence (SIGINT) analyst, I ensure I understand the technical limitations and strengths of their data, appreciating the contextual nuances they bring. Similarly, with open-source intelligence (OSINT) analysts, I understand how their information, while readily available, requires critical evaluation to assess reliability and biases. To foster this collaboration, I often initiate collaborative brainstorming sessions to share insights, identify potential biases, and cross-reference findings. We use shared platforms and document management systems to ensure we all work from the same updated data, allowing for simultaneous review and feedback. This inclusive process fosters a shared understanding of the intelligence picture and ensures a more robust analysis.
Q 24. Describe a time you had to work with incomplete or ambiguous data. How did you proceed?
In a recent project analyzing a potential transnational criminal network, we had limited financial transaction data. Instead of abandoning the analysis, I employed several strategies to compensate for this gap. First, I leveraged open-source information—news articles, social media posts, and company registries—to identify potential associates and business activities. Second, I applied network analysis techniques using available data points to identify key nodes and relationships within the network, even with incomplete data. Third, I used Bayesian reasoning to incorporate the limited available data, allowing for probabilistic assessments of the likelihood of various hypotheses. This approach, using a combination of qualitative and quantitative methods, helped to develop a plausible narrative even with incomplete data. The result was a comprehensive analysis that, while acknowledging the data limitations, presented a well-supported assessment of the network’s structure and activities.
Q 25. How do you handle disagreements with colleagues regarding the interpretation of intelligence data?
Disagreements are inevitable in intelligence analysis, especially when interpreting ambiguous data. My approach prioritizes respectful discussion and a commitment to evidence-based reasoning. I encourage colleagues to articulate their interpretations clearly, supporting their arguments with specific evidence. We systematically review the data together, focusing on potential biases and alternative interpretations. If we remain unable to reach a consensus, I advocate for including all differing perspectives in the final report, clearly outlining the areas of disagreement and the supporting evidence for each interpretation. This transparency is essential for maintaining the integrity of the analysis and allowing for informed decision-making by policymakers. In essence, I view disagreement not as a failure but as an opportunity to strengthen the analysis by thoroughly exploring all possible perspectives.
Q 26. What is your experience using analytic frameworks such as the Diamond Model or the Analyst’s Notebook?
I have extensive experience using analytic frameworks like the Diamond Model and Analyst’s Notebook. The Diamond Model (actor, infrastructure, capability, and victim) provides a structured approach to understanding complex events. I regularly use it to organize information about various threat actors, mapping their capabilities and identifying potential targets and vulnerabilities. Analyst’s Notebook, on the other hand, offers a powerful visual platform for network analysis and link charting. I use it to visualize complex relationships between entities, quickly identify patterns and anomalies, and generate hypotheses based on visual representation of the data. For example, in a recent case involving a cyberattack, Analyst’s Notebook allowed me to visualize the connections between various compromised systems, quickly identifying the attack vector and the likely origin of the malicious activity.
Q 27. Describe your proficiency in using specific data analysis software such as Palantir or ArcGIS.
My proficiency with data analysis software extends to both Palantir and ArcGIS. Palantir’s powerful data integration capabilities allow me to combine data from disparate sources (e.g., HUMINT reports, SIGINT intercepts, and OSINT data) creating a cohesive and readily searchable intelligence picture. I leverage its advanced visualization features to identify complex relationships and patterns. ArcGIS, with its robust geospatial capabilities, is invaluable when analyzing location-based data, allowing for the creation of detailed maps that visually represent the movement of individuals, the deployment of resources, or the spread of events. For example, by integrating data from social media, news reports, and government databases into ArcGIS, I can map the spread of a specific type of disinformation campaign across a region, identifying key patterns and influential nodes.
Key Topics to Learn for AllSource Intelligence Analysis Interview
- Data Collection & Integration: Understanding various data sources (open-source, classified, etc.), methods for data collection, and techniques for integrating diverse data types into a cohesive intelligence picture.
- Information Analysis & Synthesis: Applying analytical frameworks (e.g., OSINT, HUMINT, SIGINT) to evaluate credibility, identify biases, and synthesize information from multiple sources to draw insightful conclusions.
- Threat Assessment & Risk Management: Analyzing information to assess potential threats, predict future trends, and develop effective risk mitigation strategies. This includes understanding different threat models and methodologies.
- Report Writing & Communication: Mastering the art of clearly and concisely communicating complex intelligence findings to a diverse audience through well-structured reports and presentations.
- Technological Proficiency: Demonstrating familiarity with relevant software and tools used in intelligence analysis, such as data visualization platforms, analytical software, and database management systems.
- Ethical Considerations & Legal Frameworks: Understanding the ethical implications of intelligence analysis and adhering to relevant legal frameworks and regulations.
- Problem-Solving & Critical Thinking: Applying critical thinking skills to analyze complex problems, identify key assumptions, and develop creative solutions in ambiguous situations.
Next Steps
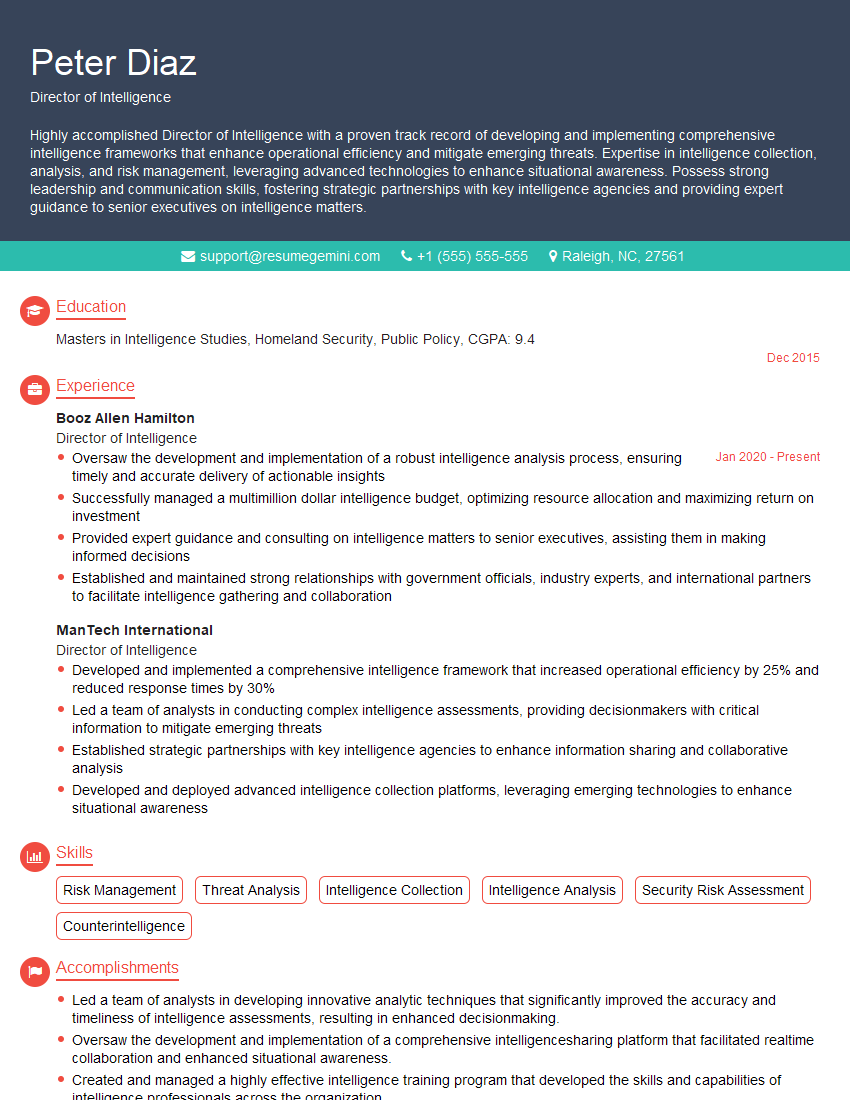
Mastering AllSource Intelligence Analysis opens doors to exciting and impactful career opportunities within the intelligence community and beyond. Proficiency in this field demonstrates valuable analytical, critical thinking, and problem-solving skills highly sought after by employers. To maximize your job prospects, creating a strong, ATS-friendly resume is crucial. ResumeGemini is a trusted resource to help you build a professional and effective resume that highlights your skills and experience. We provide examples of resumes tailored to AllSource Intelligence Analysis roles to guide you through the process. Take the next step towards your dream career – craft a compelling resume today!
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good