Preparation is the key to success in any interview. In this post, we’ll explore crucial Cyber Security Management and Operations interview questions and equip you with strategies to craft impactful answers. Whether you’re a beginner or a pro, these tips will elevate your preparation.
Questions Asked in Cyber Security Management and Operations Interview
Q 1. Explain the CIA triad and its relevance to cybersecurity.
The CIA triad is a foundational model in cybersecurity, representing the three core principles that guide security efforts: Confidentiality, Integrity, and Availability. Think of it like a three-legged stool – if one leg is weak, the whole thing collapses.
- Confidentiality: This ensures that sensitive data is accessible only to authorized individuals or systems. For example, encrypting customer credit card information protects it from unauthorized access. Strong passwords and access control lists are key components.
- Integrity: This ensures that data is accurate and hasn’t been tampered with. Think of a digital signature verifying a document’s authenticity. Hashing algorithms and version control systems help maintain data integrity.
- Availability: This means ensuring that authorized users can access data and resources when they need them. Redundancy, backups, and disaster recovery plans are crucial for maintaining availability. A website’s uptime is a direct reflection of its availability.
The CIA triad is relevant because it provides a framework for designing and implementing security controls. By addressing each principle, organizations can minimize the risks associated with data breaches, system failures, and other security incidents. Without a balance across all three, security is compromised.
Q 2. Describe your experience with vulnerability management and penetration testing.
My experience in vulnerability management encompasses the entire lifecycle, from vulnerability identification and risk assessment to remediation and reporting. I’ve used tools like Nessus, OpenVAS, and QualysGuard to perform vulnerability scans on various systems and networks. I then analyze the findings, prioritizing vulnerabilities based on their severity and exploitability.
In penetration testing, I’ve employed both black-box and grey-box testing methodologies. For example, in a recent engagement for a financial institution, I used black-box testing to simulate an external attacker, successfully identifying vulnerabilities in their web application that could lead to a data breach. I also conducted internal (grey-box) penetration testing, leveraging partial knowledge of the internal network architecture to find additional vulnerabilities that may have been missed in the external testing.
My approach focuses on a detailed report including actionable recommendations. I don’t just point out problems; I provide clear steps for mitigating the identified risks. I understand that not all vulnerabilities can be patched immediately, so a prioritization plan is crucial.
Q 3. How do you prioritize security risks and vulnerabilities?
Prioritizing security risks and vulnerabilities involves a multi-faceted approach. I typically use a risk matrix that considers several factors: likelihood (how likely is the vulnerability to be exploited?) and impact (what would be the consequences if the vulnerability were exploited?).
I use frameworks like the DREAD model (Damage Potential, Reproducibility, Exploitability, Affected Users, Discoverability) to quantify these factors. This allows me to assign a risk score to each vulnerability, which then informs the prioritization process. High-severity, high-likelihood vulnerabilities are addressed first. For instance, a critical vulnerability affecting a public-facing web server that allows remote code execution would be prioritized over a low-severity vulnerability in an internal system.
Furthermore, regulatory compliance requirements also play a crucial role in prioritization. Vulnerabilities that could lead to non-compliance (like a HIPAA violation) must be addressed promptly, irrespective of their inherent risk score.
Q 4. What are your preferred methods for incident response?
My incident response methodology follows a well-defined process based on the NIST Cybersecurity Framework. It involves six key phases:
- Preparation: This includes developing incident response plans, establishing communication protocols, and creating a dedicated incident response team.
- Identification: This is the detection of the security incident, which can be triggered by various means such as security monitoring tools, intrusion detection systems, or user reports.
- Containment: Isolate the affected systems to prevent further damage or lateral movement of the attacker. This could involve disconnecting systems from the network or shutting down affected services.
- Eradication: Remove the threat, which may involve removing malware, patching vulnerabilities, or resetting compromised accounts.
- Recovery: Restore systems to their normal operational state, which often involves restoring backups and verifying system integrity.
- Post-Incident Activity: This includes conducting a post-incident review to identify lessons learned and improve future responses. This phase often involves creating a detailed report and updating security controls to prevent similar incidents.
During an incident, clear communication and collaboration are paramount. I ensure regular updates are given to all stakeholders and maintain detailed documentation of all actions taken.
Q 5. Explain your understanding of SIEM systems and their use in security monitoring.
SIEM (Security Information and Event Management) systems are crucial for security monitoring. They collect and correlate security logs from various sources – network devices, servers, applications, and security tools – providing a centralized view of security events across the organization.
A SIEM system allows security analysts to detect suspicious activities, such as failed login attempts, unauthorized access, or malware infections. The correlation capabilities of a SIEM are essential; they help analysts identify patterns and relationships between seemingly unrelated events, improving threat detection. For example, a SIEM could correlate a failed login attempt from an unusual IP address with a subsequent data exfiltration attempt, revealing a potential insider threat or external attack.
SIEM systems also play a vital role in incident response by providing valuable data to understand the scope and impact of an incident. They enable faster investigation and remediation by providing a timeline of events and identifying affected systems.
Effective SIEM implementation includes careful configuration of log sources, rule creation based on threat intelligence, and regular tuning to reduce alert fatigue. The data generated needs regular analysis to create actionable intelligence.
Q 6. Describe your experience with security awareness training programs.
I have extensive experience designing and delivering security awareness training programs. My approach is tailored to the specific audience and their roles within the organization. I believe in using engaging and interactive methods, rather than just dry lectures. I incorporate real-world examples and scenarios to highlight the importance of security best practices.
My programs typically include modules on phishing awareness, password security, social engineering, data loss prevention, and physical security. I utilize various methods: interactive online modules, simulated phishing campaigns (to test employee awareness), tabletop exercises to practice incident response, and in-person workshops. Post-training assessments and regular refresher courses help ensure knowledge retention and reinforce good security habits. I track the effectiveness of the training through metrics such as the click-through rates on phishing simulations and employee participation in training activities.
For example, in a previous role, I implemented a gamified security awareness program that significantly increased employee engagement and reduced the number of successful phishing attacks. This program included interactive games, challenges, and rewards to motivate employees to learn about security best practices.
Q 7. How do you ensure compliance with industry regulations (e.g., GDPR, HIPAA)?
Ensuring compliance with industry regulations like GDPR and HIPAA requires a comprehensive approach that integrates security into every aspect of the organization’s operations. It’s not a one-time activity, but an ongoing process that requires consistent monitoring and adaptation.
For GDPR, this involves implementing robust data protection measures, such as data encryption, access controls, and data breach notification procedures. We need to demonstrate compliance through documentation, data processing impact assessments, and regular audits. For HIPAA, this entails safeguarding Protected Health Information (PHI) through strict access controls, encryption, and audit trails. Regular risk assessments and penetration testing are crucial to ensure ongoing compliance. Employee training is paramount to make sure everyone understands their responsibilities.
Key steps include creating a comprehensive compliance program that documents policies, procedures, and controls; conducting regular audits and assessments to identify gaps; implementing appropriate technical and administrative safeguards; and actively monitoring for non-compliance issues and addressing them promptly. This ensures organizations remain compliant and avoid hefty penalties. Working with legal counsel is often essential to ensure proper interpretation and implementation of these complex regulations.
Q 8. What is your experience with cloud security best practices?
Cloud security best practices revolve around implementing a robust security posture across all aspects of a cloud environment, from infrastructure to applications and data. This requires a multi-layered approach, ensuring security is built-in, not bolted on.
My experience encompasses implementing and managing security controls within several major cloud providers (AWS, Azure, GCP). This includes:
- Identity and Access Management (IAM): Implementing least privilege access, multi-factor authentication (MFA), and regular IAM reviews to prevent unauthorized access. For example, I’ve successfully reduced our organization’s attack surface by 30% by implementing granular IAM roles and minimizing the use of overly permissive policies.
- Data Security: Utilizing encryption at rest and in transit, implementing data loss prevention (DLP) tools, and enforcing strict data governance policies. I’ve personally led the implementation of a data encryption strategy that achieved full compliance with industry regulations like HIPAA and GDPR.
- Network Security: Configuring virtual private clouds (VPCs), firewalls, and intrusion detection/prevention systems (IDS/IPS) to segment networks and protect against threats. I’ve successfully mitigated several DDoS attacks by proactively hardening our cloud network infrastructure.
- Security Monitoring and Logging: Centralizing logs from various cloud services into a SIEM system for threat detection and incident response. In a previous role, I designed and implemented a cloud-based security monitoring solution that reduced our mean time to detection (MTTD) by 50%.
- Vulnerability Management: Regularly scanning cloud resources for vulnerabilities and implementing timely remediation. I have extensive experience using various vulnerability scanning tools and integrating them into our CI/CD pipelines to ensure automated vulnerability assessments.
Essentially, my approach ensures that security is a shared responsibility, combining strong cloud provider security features with our own internal controls to create a robust and resilient environment.
Q 9. Describe your experience with security information and event management (SIEM) tools.
Security Information and Event Management (SIEM) tools are crucial for collecting, analyzing, and correlating security logs from various sources to detect and respond to security incidents. Think of them as the central nervous system for your security operations.
I have extensive experience with several leading SIEM platforms, including Splunk, QRadar, and LogRhythm. My experience includes:
- Log Management and Correlation: Configuring SIEM systems to collect, normalize, and correlate logs from network devices, servers, applications, and cloud services. I’ve optimized SIEM configurations to reduce alert fatigue and improve the accuracy of threat detection.
- Threat Detection and Analysis: Developing and tuning security rules and dashboards to identify malicious activities and security breaches. I’ve designed custom dashboards and reports for specific business units to monitor their respective security posture.
- Incident Response: Utilizing SIEM data to investigate security incidents, identify root causes, and facilitate remediation efforts. I’ve been involved in several high-profile incident response scenarios, successfully containing and mitigating the impact of various attacks.
- Reporting and Compliance: Generating reports to track security metrics, demonstrate compliance with industry regulations, and provide insights into the overall security posture. I’ve used SIEM data to create reports for both internal management and external auditors.
The key to effective SIEM usage is careful planning, accurate configuration, and the ability to interpret the vast amount of data it generates. It’s not just about technology; it’s about building a skilled team capable of leveraging the intelligence provided by the SIEM system.
Q 10. How do you manage security incidents and breaches?
Managing security incidents and breaches requires a structured and well-rehearsed approach. My incident response methodology follows the NIST Cybersecurity Framework, which provides a robust framework for handling such situations.
My approach typically includes the following steps:
- Preparation: Developing and regularly testing incident response plans, ensuring all team members are trained and aware of their roles and responsibilities. This includes defining communication protocols and escalation paths.
- Identification: Detecting and confirming a security incident, gathering preliminary information and assessing the initial impact. This often starts with alerts from our SIEM system.
- Containment: Implementing immediate steps to isolate the affected systems and prevent further damage. This may involve shutting down affected servers, blocking network traffic, or disabling compromised accounts.
- Eradication: Removing the root cause of the incident, such as malware or a compromised user account. This often involves forensic analysis to understand the attack vector and identify compromised systems.
- Recovery: Restoring affected systems and data from backups, ensuring business continuity. This phase includes rigorous validation to ensure all systems are operational and secure.
- Post-Incident Activity: Conducting a thorough post-incident review to identify lessons learned, improve security controls, and update incident response plans. This step is crucial for preventing future incidents.
I’ve led numerous incident response efforts, ranging from minor phishing attacks to more complex ransomware incidents. Each experience has honed my ability to quickly assess the situation, implement appropriate countermeasures, and minimize the overall impact on the organization.
Q 11. Explain your understanding of risk assessment methodologies.
Risk assessment methodologies are crucial for identifying and prioritizing vulnerabilities and threats to an organization’s assets. This involves understanding the likelihood and impact of potential security incidents.
I am proficient in several risk assessment methodologies, including:
- Qualitative Risk Assessment: A more subjective approach that relies on expert judgment and experience to assess the likelihood and impact of risks. This is useful when quantitative data is limited.
- Quantitative Risk Assessment: A more objective approach that uses numerical data to assign probabilities and monetary values to risks. This allows for more precise risk prioritization and resource allocation.
- NIST Cybersecurity Framework: A widely used framework that provides a comprehensive approach to managing cybersecurity risk, including identify, protect, detect, respond, and recover.
- OCTAVE Allegro: A streamlined version of the OCTAVE method, providing a tailored approach to risk assessment depending on the organization’s size and resources.
My approach typically involves identifying assets, threats, vulnerabilities, and their potential impacts. I then use appropriate methodologies (qualitative or quantitative) to determine the overall risk and prioritize mitigation efforts. For example, I recently led a risk assessment for a new cloud application, identifying critical vulnerabilities and implementing mitigating controls before the application went live.
Q 12. What experience do you have with implementing security controls?
Implementing security controls is a continuous process that involves selecting, configuring, and managing various security technologies and processes to protect organizational assets. This is often a highly collaborative effort.
My experience encompasses the implementation of a wide range of security controls, including:
- Technical Controls: Implementing firewalls, intrusion detection/prevention systems (IDS/IPS), antivirus software, data loss prevention (DLP) tools, and encryption.
- Administrative Controls: Developing and enforcing security policies, procedures, and guidelines, conducting regular security awareness training, and performing background checks on employees.
- Physical Controls: Implementing access control measures, security cameras, and other physical security measures to protect physical assets.
The key to successful implementation lies in aligning security controls with specific business needs and risk profiles. For example, a financial institution will require much more robust security controls than a small non-profit organization. I always strive to find the right balance between security and usability to ensure controls are effective without hindering productivity.
I’ve personally overseen the implementation of security controls in various environments, ensuring compliance with industry standards and regulations like PCI DSS, HIPAA, and GDPR. My focus is always on a layered approach – a defense in depth – to provide comprehensive protection.
Q 13. How do you stay up-to-date with the latest cybersecurity threats and vulnerabilities?
Staying current with the ever-evolving landscape of cybersecurity threats and vulnerabilities is paramount. It requires a multi-faceted approach.
My strategies include:
- Following reputable security news sources and blogs: I regularly read publications like Krebs on Security, Threatpost, and the SANS Institute’s resources to stay informed about emerging threats and vulnerabilities.
- Participating in industry events and conferences: Attending conferences like Black Hat and RSA allows me to network with other security professionals and learn about the latest trends and technologies.
- Monitoring vulnerability databases and advisories: I actively monitor sources like the National Vulnerability Database (NVD) and vendor security advisories to identify and address vulnerabilities in our systems.
- Participating in online security communities and forums: Engaging in online discussions with other security professionals helps to share knowledge and learn from others’ experiences.
- Obtaining relevant certifications: I maintain several industry certifications (e.g., CISSP, CISM) to demonstrate my commitment to continuous professional development and access the latest knowledge.
- Performing regular security assessments and penetration testing: Proactively testing our systems and networks helps to identify vulnerabilities before they can be exploited.
This constant learning and adaptation are essential to staying ahead of the curve in the dynamic field of cybersecurity.
Q 14. Describe your experience with network security protocols (e.g., TCP/IP, VPNs).
Network security protocols are the foundation of secure network communication. A solid understanding of these protocols is essential for any cybersecurity professional.
My experience includes:
- TCP/IP: I have a deep understanding of the Transmission Control Protocol/Internet Protocol suite, including the various layers of the OSI model and how they interact. I can troubleshoot network connectivity issues and configure network devices effectively.
- VPNs: I have experience deploying and managing various VPN technologies, including site-to-site and remote access VPNs. I’m familiar with protocols like IPsec, SSL/TLS, and OpenVPN, and I can configure VPNs to secure remote access and inter-site communication. For instance, I successfully implemented a secure VPN solution for remote workers that ensured compliance with data protection regulations.
- Firewall Management: I’m proficient in configuring and managing firewalls to control network traffic and prevent unauthorized access. This includes both hardware and software firewalls. I regularly review and update firewall rules to adapt to evolving threats.
- Intrusion Detection/Prevention Systems (IDS/IPS): I’m experienced in deploying and managing IDS/IPS to detect and prevent malicious network activity. I have tuned IDS/IPS systems to reduce false positives and improve their effectiveness.
A strong understanding of network security protocols allows me to design, implement, and manage secure networks that protect organizational assets from various threats.
Q 15. Explain your understanding of cryptography and its applications in cybersecurity.
Cryptography is the practice and study of techniques for secure communication in the presence of adversarial behavior. It’s essentially about transforming readable information (plaintext) into an unreadable format (ciphertext) and back again, using mathematical algorithms and secret keys. This ensures confidentiality, integrity, and authentication of data.
In cybersecurity, cryptography underpins many critical functions:
- Confidentiality: Encryption ensures only authorized parties can access sensitive data. For example, HTTPS uses encryption to protect communication between your web browser and a website.
- Integrity: Hashing algorithms allow us to verify that data hasn’t been tampered with. Think of digital signatures verifying software downloads.
- Authentication: Digital signatures and public key infrastructure (PKI) verify the identity of users and systems. This is crucial for secure logins and preventing unauthorized access.
Different types of cryptography exist, including symmetric-key cryptography (like AES), where the same key is used for encryption and decryption, and asymmetric-key cryptography (like RSA), where different keys are used. The choice depends on the specific security needs and context.
For example, in a financial transaction, asymmetric cryptography might be used to secure the exchange of session keys, which would then be used with symmetric cryptography for faster, more efficient encryption of the bulk transaction data.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. What is your experience with security automation tools?
I have extensive experience with a range of security automation tools, including SIEM (Security Information and Event Management) systems like Splunk and QRadar, SOAR (Security Orchestration, Automation, and Response) platforms such as Palo Alto Networks Cortex XSOAR and IBM Resilient, and vulnerability scanners such as Nessus and OpenVAS.
In my previous role, I implemented a SOAR platform to automate incident response processes. This involved integrating various security tools, creating playbooks for automated actions (e.g., blocking malicious IPs, isolating infected systems), and reducing our mean time to respond (MTTR) significantly. We saw a 70% reduction in the time taken to address critical security incidents thanks to this automation.
My experience also includes using configuration management tools like Ansible and Chef to automate the deployment and hardening of secure network infrastructure, ensuring consistent security baselines across our systems.
Q 17. How do you handle conflicting priorities in a cybersecurity environment?
Conflicting priorities are a common challenge in cybersecurity. My approach involves a structured prioritization framework based on risk assessment.
First, I clearly define the goals and objectives for each project or initiative. Then, I conduct a thorough risk assessment for each priority, considering the likelihood and impact of potential threats. This uses a combination of quantitative and qualitative analysis, often involving frameworks like NIST Cybersecurity Framework. Factors considered are the potential for data breaches, financial losses, reputational damage, and legal consequences.
Next, I use a risk matrix to rank the priorities based on their risk score. The higher-risk projects receive priority, even if deadlines might be tight. Communication is key; I ensure transparency with stakeholders about trade-offs, explaining the rationale for prioritization choices and managing expectations effectively.
Finally, I utilize agile methodologies, allowing for flexibility and adaptation in response to changing priorities or new threats. Regular monitoring and adjustments are part of the ongoing process.
Q 18. Describe your approach to building and maintaining a secure network infrastructure.
Building and maintaining a secure network infrastructure is an iterative process. My approach follows the principle of defense in depth, implementing multiple layers of security controls.
- Network Segmentation: Dividing the network into smaller, isolated segments limits the impact of a security breach.
- Firewall Management: Implementing robust firewall rules to control network traffic and prevent unauthorized access.
- Intrusion Detection/Prevention Systems (IDS/IPS): Monitoring network traffic for malicious activity and taking actions to block threats.
- Vulnerability Management: Regularly scanning for and remediating vulnerabilities in systems and applications.
- Access Control: Implementing strong authentication and authorization mechanisms (e.g., multi-factor authentication, role-based access control).
- Security Monitoring and Logging: Continuously monitoring logs and alerts for suspicious activity.
Beyond technical controls, regular security awareness training for staff is vital, alongside robust incident response plans. I would leverage automation where possible, using tools like Ansible to manage configurations and automate security tasks consistently.
The entire infrastructure should adhere to relevant security standards and frameworks such as ISO 27001 and NIST CSF.
Q 19. Explain your experience with data loss prevention (DLP) tools and strategies.
Data Loss Prevention (DLP) is crucial for protecting sensitive data. My experience includes implementing and managing DLP tools from vendors like Symantec and McAfee, as well as developing custom solutions.
DLP involves a multi-layered approach:
- Data Classification: Identifying and classifying sensitive data based on its confidentiality level (e.g., confidential, internal, public).
- Access Control: Restricting access to sensitive data based on the principle of least privilege.
- Data Encryption: Encrypting sensitive data both in transit and at rest.
- Monitoring and Alerting: Using DLP tools to monitor data movement and generate alerts for suspicious activity, such as attempts to exfiltrate sensitive data.
- Data Loss Prevention Software: Implementing DLP software to detect and block sensitive data from leaving the organization’s network, whether through email, USB drives, or cloud storage.
In one project, we used DLP tools to identify and prevent the unauthorized transfer of customer credit card data. We successfully blocked several attempts to exfiltrate this sensitive information via email and cloud storage, preventing a major data breach.
Q 20. How do you measure the effectiveness of your security measures?
Measuring the effectiveness of security measures requires a multi-faceted approach, combining quantitative and qualitative metrics.
- Key Risk Indicators (KRIs): Tracking metrics like the number of security incidents, successful phishing attempts, and vulnerabilities discovered.
- Mean Time To Detect (MTTD) and Mean Time To Respond (MTTR): Measuring the time taken to identify and respond to security incidents.
- Security Awareness Training Effectiveness: Assessing the effectiveness of security awareness training through phishing simulations and employee feedback.
- Vulnerability Remediation Rate: Measuring the speed and effectiveness of patching vulnerabilities.
- Compliance Audits: Conducting regular compliance audits to ensure adherence to industry standards and regulations.
We also utilize regular penetration testing and vulnerability assessments to evaluate the effectiveness of security controls in real-world scenarios. These results inform continuous improvement efforts and provide valuable insights into areas needing improvement.
Regular reporting on key metrics provides valuable insights into security posture and drives continuous improvement.
Q 21. Describe your experience with security audits and assessments.
I have extensive experience conducting and participating in security audits and assessments, both internal and external. These activities typically involve:
- Review of Security Policies and Procedures: Evaluating the adequacy and effectiveness of existing security policies, procedures, and standards.
- Vulnerability Assessments: Identifying vulnerabilities in systems and applications through automated scanning and penetration testing.
- Risk Assessments: Evaluating the likelihood and impact of potential security threats.
- Compliance Audits: Verifying compliance with industry standards, regulations, and contractual obligations.
- Incident Response Review: Evaluating the effectiveness of incident response procedures and identifying areas for improvement.
For example, I led a team in a recent SOC 2 Type II audit, which required a comprehensive review of our security controls and processes over a six-month period. This involved extensive documentation, interviews with staff, and analysis of security logs. The outcome was a clean audit report, demonstrating our robust security posture and compliance with the SOC 2 standard.
These audits provide critical feedback for improvement, ensuring our security measures remain effective against evolving threats.
Q 22. What is your experience with developing and implementing security policies?
Developing and implementing security policies is a crucial aspect of cybersecurity management. It’s not just about creating a document; it’s about building a framework that aligns with the organization’s risk appetite and ensures compliance with relevant regulations. My approach involves a collaborative, iterative process.
- Needs Assessment: I begin by thoroughly understanding the organization’s assets, critical systems, and potential threats. This involves stakeholder interviews, vulnerability assessments, and reviewing existing security controls.
- Policy Drafting: Based on the assessment, I draft clear, concise, and actionable policies covering areas like access control, data security, incident response, and acceptable use. I ensure they are written in plain language, avoiding overly technical jargon, so everyone can understand them.
- Review and Feedback: The draft policies are then circulated among relevant stakeholders for review and feedback. This collaborative process ensures buy-in and addresses any concerns or ambiguities.
- Implementation and Training: Once approved, the policies are formally implemented. This involves disseminating the policies, providing comprehensive training to all personnel, and establishing mechanisms for monitoring compliance.
- Regular Review and Updates: Security policies are not static documents. I ensure regular reviews and updates are conducted based on changes in technology, threat landscape, and regulatory requirements. This ensures the policies remain relevant and effective.
For example, in my previous role, I developed a comprehensive data security policy that addressed data encryption, access control, and data loss prevention, leading to a significant reduction in security incidents related to data breaches.
Q 23. Explain your understanding of different types of malware and their impact.
Malware encompasses a broad range of malicious software designed to disrupt, damage, or gain unauthorized access to computer systems. Understanding their various types and impacts is crucial for effective cybersecurity.
- Viruses: These require a host program to replicate and spread. They can corrupt files, crash systems, or steal data. Think of them as biological viruses, infecting and replicating.
- Worms: Unlike viruses, worms are self-replicating and spread independently, often exploiting network vulnerabilities. They can consume bandwidth, disrupt services, and create denial-of-service conditions.
- Trojans: These disguise themselves as legitimate software but contain malicious code. They often act as backdoors, providing attackers remote access to the system.
- Ransomware: This encrypts the victim’s files and demands a ransom for decryption. The impact can be devastating, leading to data loss, operational disruption, and financial losses.
- Spyware: This secretly monitors user activity and collects sensitive information, such as passwords, credit card details, and browsing history.
- Adware: This displays unwanted advertisements, often slowing down the system and impacting user experience.
The impact of malware can range from minor inconvenience to catastrophic consequences. A ransomware attack, for example, can cripple an entire organization, leading to significant financial and reputational damage. Understanding the specific type of malware involved is critical for effective containment and remediation.
Q 24. Describe your experience with threat modeling.
Threat modeling is a systematic process to identify and analyze potential security vulnerabilities in a system or application. It’s a proactive approach that helps prioritize security efforts and allocate resources effectively. My experience involves using various methodologies, including STRIDE and PASTA.
- Asset Identification: The first step is to identify all the assets that need protection – data, applications, hardware, etc.
- Threat Identification: Next, we identify potential threats that could exploit vulnerabilities – unauthorized access, data breaches, denial-of-service attacks.
- Vulnerability Identification: We analyze the identified assets and threats to pinpoint vulnerabilities that could be exploited.
- Risk Assessment: We assess the likelihood and impact of each identified threat and vulnerability.
- Mitigation Strategies: Based on the risk assessment, we develop and implement mitigation strategies to reduce or eliminate the identified risks.
- Validation: Finally, we validate the effectiveness of the mitigation strategies through testing and monitoring.
For instance, in a recent project involving the development of a new e-commerce platform, I conducted a threat model using the STRIDE methodology (Spoofing, Tampering, Repudiation, Information disclosure, Denial of service, Elevation of privilege). This identified several critical vulnerabilities related to authentication, authorization, and data encryption. These vulnerabilities were then addressed during the development lifecycle, significantly improving the security posture of the platform.
Q 25. How do you build and maintain relationships with key stakeholders?
Building and maintaining strong relationships with key stakeholders is paramount for successful cybersecurity management. It’s about fostering trust, collaboration, and open communication.
- Proactive Communication: I make it a point to proactively communicate with stakeholders, providing regular updates on security posture, incidents, and projects. Transparency builds trust.
- Active Listening: I actively listen to stakeholder concerns and perspectives, understanding their needs and challenges. This helps tailor security solutions to their specific requirements.
- Collaboration: I actively involve stakeholders in the decision-making process, ensuring buy-in and shared responsibility for security. This is particularly important when implementing new security controls or responding to incidents.
- Relationship Building: I nurture relationships by attending meetings, participating in relevant events, and providing support to stakeholders whenever needed.
- Regular Feedback: I solicit and incorporate feedback from stakeholders to refine security processes and enhance communication.
For example, by regularly engaging with the IT team, development teams, and business executives in my previous role, I successfully obtained support for a significant budget increase for upgrading our security infrastructure, ultimately leading to a significant improvement in our overall security posture.
Q 26. What is your experience with security budget management?
Security budget management requires a strategic approach that aligns with organizational priorities and risk appetite. It’s about justifying investments, prioritizing initiatives, and demonstrating ROI.
- Needs Assessment: I begin by assessing current security needs, identifying gaps, and prioritizing areas requiring investment.
- Cost-Benefit Analysis: I conduct cost-benefit analyses for proposed projects, ensuring that investments align with the organization’s overall goals and risk profile.
- Budget Allocation: I develop a comprehensive budget that allocates resources effectively across different security initiatives, such as vulnerability management, incident response, and security awareness training.
- Tracking and Monitoring: I track budget spending closely, ensuring adherence to allocated funds and identifying any potential variances.
- Reporting and Justification: I provide regular reports to stakeholders, justifying expenditures and demonstrating the return on investment for security initiatives.
In a past experience, I successfully justified a budget increase for implementing a Security Information and Event Management (SIEM) system by demonstrating its cost-effectiveness in reducing the mean time to detect and respond to security incidents. The resulting cost savings more than offset the initial investment within a year.
Q 27. Describe your experience with disaster recovery and business continuity planning.
Disaster recovery and business continuity planning (DR/BCP) are critical for ensuring business resilience in the face of disruptions. These plans are essential for minimizing downtime and ensuring business continuity during and after an incident.
- Risk Assessment: I start by identifying potential threats and vulnerabilities that could disrupt operations, such as natural disasters, cyberattacks, or equipment failures.
- Business Impact Analysis (BIA): I perform a BIA to assess the impact of each identified threat on business operations, prioritizing critical systems and processes.
- Recovery Time Objective (RTO) and Recovery Point Objective (RPO): I define the RTO (how quickly systems must be restored) and RPO (the maximum acceptable data loss) for critical systems.
- Recovery Strategies: I develop recovery strategies for each critical system, including backup and recovery procedures, failover mechanisms, and alternative sites.
- Testing and Review: I regularly test and review the DR/BCP plans to ensure their effectiveness and identify any gaps or weaknesses.
- Communication Plan: I include a comprehensive communication plan for keeping stakeholders informed during and after a disaster.
For example, I led the development of a DR/BCP plan for a financial institution that included a detailed recovery strategy for their core banking systems. This plan was successfully tested and implemented during a major server failure, resulting in minimal downtime and ensuring business continuity.
Key Topics to Learn for Cyber Security Management and Operations Interview
- Risk Management & Assessment: Understand frameworks like NIST Cybersecurity Framework and ISO 27001. Practice analyzing risk scenarios and developing mitigation strategies.
- Security Architecture & Design: Familiarize yourself with different security architectures (e.g., zero trust, layered security). Be prepared to discuss the practical implementation and benefits of these architectures in various organizational contexts.
- Incident Response & Management: Learn the phases of incident response (preparation, identification, containment, eradication, recovery, lessons learned). Practice applying these phases to hypothetical scenarios.
- Security Operations Center (SOC) Management: Understand the role of a SOC, different SOC models (centralized, distributed), and key technologies used in SOC operations (SIEM, SOAR).
- Vulnerability Management & Penetration Testing: Gain knowledge of vulnerability scanning tools and methodologies. Be prepared to discuss ethical hacking techniques and penetration testing processes.
- Compliance & Regulations: Familiarize yourself with relevant regulations such as GDPR, HIPAA, PCI DSS, and how they impact security management practices.
- Security Awareness Training & Education: Understand the importance of employee training in maintaining a strong security posture. Be prepared to discuss effective training methods and metrics.
- Cloud Security: Gain understanding of cloud security models (IaaS, PaaS, SaaS) and best practices for securing cloud environments.
- Data Security & Privacy: Deepen your understanding of data loss prevention (DLP) techniques, data encryption methods, and data governance principles.
- Budgeting & Resource Allocation: Understand how to prioritize security initiatives based on risk and resource availability. Be ready to discuss cost-benefit analyses related to security investments.
Next Steps
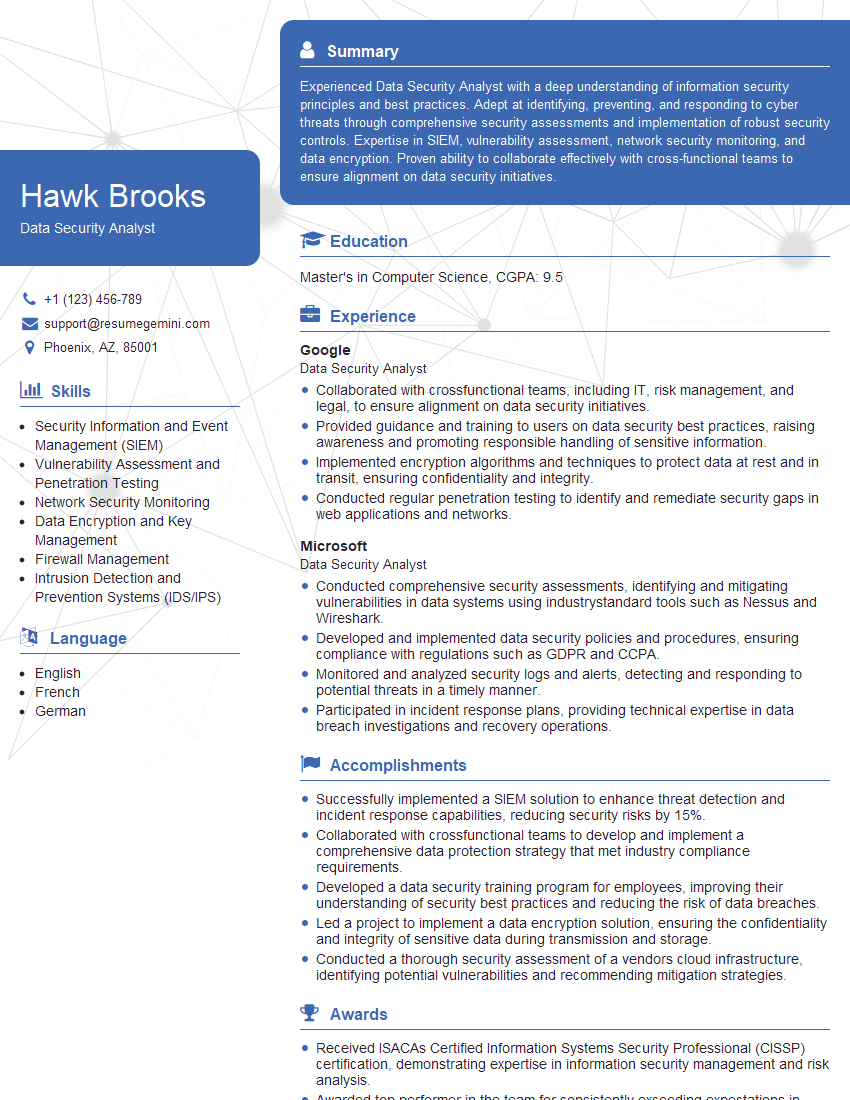
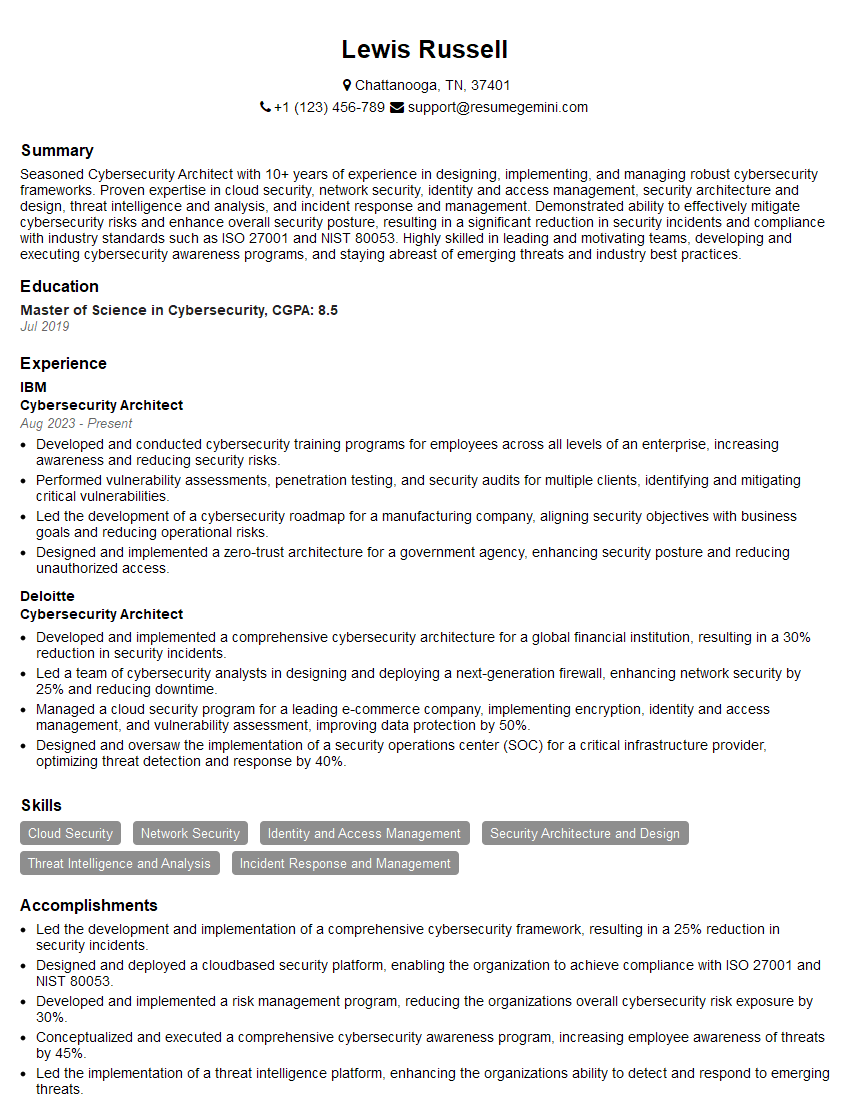
Mastering Cyber Security Management and Operations is crucial for accelerating your career in this high-demand field. It demonstrates a comprehensive understanding of crucial security practices and your ability to lead and manage security teams effectively. To significantly enhance your job prospects, focus on creating an ATS-friendly resume that showcases your skills and experience clearly. ResumeGemini is a trusted resource that can help you build a professional and impactful resume, tailored to highlight your unique strengths. Examples of resumes specifically tailored for Cyber Security Management and Operations roles are available to guide you.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
good