Feeling uncertain about what to expect in your upcoming interview? We’ve got you covered! This blog highlights the most important Electronic Warfare Systems Operation interview questions and provides actionable advice to help you stand out as the ideal candidate. Let’s pave the way for your success.
Questions Asked in Electronic Warfare Systems Operation Interview
Q 1. Describe the electromagnetic spectrum and its relevance to Electronic Warfare.
The electromagnetic spectrum is the range of all types of electromagnetic radiation. Think of it like a rainbow, but instead of visible light, it encompasses everything from extremely low-frequency radio waves to incredibly high-energy gamma rays. Electronic Warfare (EW) leverages this spectrum extensively. Different parts of the spectrum are used for various communication and detection systems, such as radar, communications, and navigation. EW systems operate within this spectrum to detect, disrupt, or protect against these systems. For example, radar systems operate primarily in the microwave portion of the spectrum, while many communication systems utilize radio frequencies. Understanding the specific frequencies used by enemy systems is critical for effective EW operations.
In essence, the electromagnetic spectrum is the battlefield for EW. EW systems are designed to either sense and exploit emissions within this spectrum (Electronic Support Measures), deliberately interfere with emissions (Electronic Attack), or protect friendly systems from these effects (Electronic Protection).
Q 2. Explain the difference between Electronic Support Measures (ESM), Electronic Attack (EA), and Electronic Protection (EP).
Electronic Warfare is broadly categorized into three key areas: Electronic Support Measures (ESM), Electronic Attack (EA), and Electronic Protection (EP). They work together to achieve battlefield dominance.
- Electronic Support Measures (ESM): This is the ‘listening’ aspect of EW. ESM systems passively detect and analyze electromagnetic emissions from enemy systems – think of it as electronic reconnaissance. They identify the type of emitter (radar, communication, etc.), its frequency, location, and other characteristics. This information is crucial for situational awareness and informing subsequent EA or EP actions.
- Electronic Attack (EA): This is the ‘offensive’ part of EW. EA systems actively jam or disrupt enemy electromagnetic emissions. This can involve generating noise to mask signals, spoofing systems with false information, or even directing energy to damage enemy equipment. The goal is to deny the enemy the use of their sensors and communication systems.
- Electronic Protection (EP): This is the ‘defensive’ aspect. EP systems protect friendly forces from enemy EA. Techniques include employing countermeasures (such as chaff and flares), using low probability of intercept (LPI) communication, and implementing frequency hopping to make it harder to track friendly signals.
Imagine a battle: ESM is like the scout, identifying enemy positions and capabilities. EA is the artillery, disrupting enemy operations. EP is the armor, shielding friendly forces from attack.
Q 3. What are the key components of a typical Electronic Warfare system?
A typical Electronic Warfare system comprises several key components working in concert. These include:
- Receivers: These are highly sensitive antennas and receivers that detect and capture electromagnetic signals across a wide range of frequencies. They are the ‘ears’ of the system.
- Signal Processors: Sophisticated computers analyze the captured signals, identifying emitters, their location, and other important parameters. They perform the ‘brainwork’ of the system.
- Transmitters (for EA): Used in EA operations, these transmit jamming signals or deceptive signals to disrupt enemy systems. These are the ‘voice’ of the system in offensive actions.
- Antennas: These direct the transmission and reception of electromagnetic signals. Different antenna types are used for various tasks, depending on the frequency and directionality requirements.
- Control and Display System: A human-machine interface allows operators to monitor the situation, select jamming strategies, and manage the system’s actions. This is the ‘command center’ of the system.
- Databases: These contain information on known enemy emitter signatures, helping with identification.
The sophistication and integration of these components vary greatly depending on the specific EW system’s role and capabilities.
Q 4. How does an Electronic Warfare system detect and identify enemy radar signals?
An Electronic Warfare system detects and identifies enemy radar signals through a process of signal analysis. The receivers capture the incoming radar signals, which are then processed to extract key characteristics such as:
- Frequency: The specific frequency band used by the radar.
- Pulse Repetition Interval (PRI): The time between successive radar pulses.
- Pulse Width: The duration of each radar pulse.
- Modulation type: The way the radar signal is modulated, which provides information about the type of radar.
- Signal strength: This helps to estimate the distance to the radar.
This information is then compared against a database of known radar signatures. Sophisticated signal processing algorithms analyze the unique characteristics of the signal, making the identification possible. Techniques like spectral analysis, pulse-train analysis and pattern recognition are used for accurate identification. The system can then determine the type of radar, its location, and possibly even its operational mode.
Imagine it like a detective identifying a suspect by their voice, gait, and clothing (signal characteristics). The database acts as a ‘mugshot’ collection, helping identify the culprit (radar type).
Q 5. Explain the concept of radar frequency agility and its impact on Electronic Warfare.
Radar frequency agility is a technique used by modern radars to change their operating frequency rapidly and unpredictably. This makes it significantly more difficult for EW systems to effectively jam the radar. Instead of operating on a single frequency, the radar jumps between multiple frequencies, making it harder to maintain a constant jamming signal.
The impact on Electronic Warfare is significant. Simple, fixed-frequency jammers become ineffective against agile radars. To counter this, EW systems need to employ advanced techniques such as:
- Wideband Jamming: Jamming across a broader frequency range, increasing the chances of affecting the radar regardless of its frequency hops.
- Adaptive Jamming: Using intelligent algorithms to quickly detect and respond to the radar’s frequency changes, maintaining effective jamming.
- Sophisticated signal processing: Advanced algorithms are necessary to track the radar’s frequency hops and adapt jamming strategies.
Frequency agility introduces a significant technological challenge in the ongoing arms race between radar developers and EW specialists.
Q 6. Describe different techniques used for jamming radar signals.
Various techniques are used for jamming radar signals, each with its own advantages and disadvantages:
- Noise Jamming: This involves transmitting a broad spectrum of noise that masks the radar signal, making it difficult for the radar to detect targets. It is simple but can be inefficient in terms of power.
- Sweep Jamming: The jammer rapidly sweeps across a range of frequencies, attempting to disrupt the radar regardless of its frequency agility. It’s effective against simpler radar systems.
- Barrage Jamming: Similar to sweep jamming, but the frequency sweeping is more random and unpredictable.
- Spot Jamming: Targeting the specific frequency used by the radar at a given moment. This requires precise knowledge of the radar’s frequency and is very effective but requires advanced signal intelligence.
- Deceptive Jamming: Generating false radar signals to confuse and mislead the radar, causing it to generate false targets or misinterpret its environment. This is a more sophisticated technique.
The choice of jamming technique depends on factors like the type of radar, the level of frequency agility, the power available to the jammer, and the overall EW strategy.
Q 7. What are the challenges in deploying Electronic Warfare systems in a contested environment?
Deploying Electronic Warfare systems in a contested environment presents numerous challenges:
- High levels of electronic interference: The dense electromagnetic environment makes it difficult to distinguish between friendly and enemy signals. This adds complexity to signal processing and identification.
- Anti-jamming technologies: Modern radars and communication systems are equipped with advanced anti-jamming measures, making it more difficult to disrupt their operation.
- Threat detection and location: Pinpointing the sources of enemy emissions in a noisy environment can be very challenging. Accurate identification is crucial for effective jamming.
- Self-protection: EW systems themselves are vulnerable to enemy attacks. They need to be protected from direct energy attacks and other forms of countermeasures.
- Coordination and communication: Effective EW operations require seamless coordination among multiple EW platforms and other forces. Secure and reliable communication is critical.
- Rapid technological advances: The constant evolution of both radar and EW systems necessitates continuous upgrades and adaptation to maintain effectiveness.
These factors underscore the need for advanced EW systems, sophisticated training, and well-coordinated operational strategies to be successful in contested environments.
Q 8. How do Electronic Warfare systems contribute to situational awareness?
Electronic Warfare (EW) systems significantly enhance situational awareness by providing a comprehensive picture of the electromagnetic environment. They achieve this by detecting, identifying, and analyzing enemy radar, communication, and other electronic emissions. Think of it like having a sophisticated ‘electronic ear’ and ‘eye’ that can ‘see’ beyond the limitations of visual or acoustic sensors.
For example, detecting an enemy radar system allows us to pinpoint its location, understand its capabilities (e.g., range, frequency), and anticipate potential threats. Similarly, intercepting enemy communications can reveal their intentions, troop movements, and operational plans. This information is then integrated with data from other intelligence sources to build a complete picture of the battlefield and the enemy’s capabilities.
In a practical scenario, consider a naval fleet approaching a hostile coastline. EW systems would actively scan for enemy radar emissions, identifying the types of radar, their locations, and even their operational modes (search, track, fire control). This knowledge helps the fleet to effectively maneuver, employ countermeasures, and optimize their own sensor systems to maximize survivability and mission success.
Q 9. Explain the principles of Electronic Protection and its importance.
Electronic Protection (EP) focuses on defending friendly forces from hostile electronic attacks. It’s about reducing our vulnerability to enemy EW actions. This involves a layered defense strategy, employing techniques like jamming, deception, and physical protection to neutralize or mitigate enemy threats.
Imagine a stealth aircraft attempting to penetrate enemy airspace. EP systems on board would be actively monitoring the electromagnetic environment for hostile radar and electronic attacks. If detected, these systems could employ jamming techniques to disrupt enemy radar tracking or use decoys to mislead enemy targeting systems. EP is crucial for ensuring the survivability of our assets and personnel in contested electromagnetic environments.
The importance of EP cannot be overstated. A successful EP strategy significantly increases the survivability and effectiveness of military operations, allowing friendly forces to operate effectively while minimizing losses.
Q 10. Describe the role of SIGINT (Signals Intelligence) in Electronic Warfare.
Signals Intelligence (SIGINT) is a critical component of Electronic Warfare, providing the crucial information needed for effective EW operations. SIGINT focuses on the interception, analysis, and exploitation of foreign electronic emissions. This intelligence informs the development of EW tactics, techniques, and procedures (TTPs).
For example, SIGINT might intercept enemy communications revealing the timing and location of an impending offensive. This information could then be used to develop a jamming strategy to disrupt enemy communications during the attack, thereby hindering their coordination and effectiveness. SIGINT data can also reveal the technical characteristics of enemy radar systems, informing the design and deployment of effective jamming countermeasures.
In essence, SIGINT provides the ‘eyes and ears’ for EW, enabling a proactive and adaptive response to the evolving electronic battlefield.
Q 11. How do you analyze intercepted signals to determine their origin and purpose?
Analyzing intercepted signals to determine their origin and purpose is a complex process that involves a multi-step approach. It starts with signal characterization, identifying its fundamental parameters such as frequency, modulation type, and bandwidth.
Next, we use signal databases and geolocation techniques to determine the likely source. This often involves comparing the signal characteristics to known systems and considering factors like signal strength and propagation paths. Advanced signal processing techniques, like direction-finding and time-difference-of-arrival (TDOA), can help pinpoint the signal’s location.
Finally, understanding the signal’s purpose requires examining its content and context. This involves decryption (if encrypted), protocol analysis, and comparing it to known communication protocols and military tactics. Expert analysts using sophisticated software tools and their knowledge of specific military systems and communication protocols work together to piece together the puzzle.
For example, identifying a specific type of radar signal, its frequency band, and the use of specific pulse repetition frequencies (PRFs) might indicate a particular type of radar and, by comparing it to known enemy deployments, its potential location and role.
Q 12. What are the ethical considerations surrounding the use of Electronic Warfare?
The ethical considerations surrounding the use of Electronic Warfare are complex and significant. The primary concern is the potential for unintended consequences and collateral damage. Jamming civilian communications, for instance, can have severe repercussions, leading to disruptions in essential services like air traffic control, emergency response, and healthcare.
International law and the laws of armed conflict impose strict limitations on the use of EW. The principle of proportionality dictates that the military advantage gained from EW operations must not outweigh the potential harm to civilians or civilian infrastructure. Furthermore, maintaining transparency and avoiding deception to mislead the enemy are crucial ethical considerations.
Strict adherence to international laws and regulations, coupled with comprehensive risk assessments and mitigation strategies, are crucial for minimizing the ethical implications and ensuring responsible use of EW capabilities.
Q 13. Explain the concept of ‘spectral management’ in Electronic Warfare.
Spectral management in Electronic Warfare refers to the coordinated planning and control of the use of the electromagnetic spectrum to maximize operational effectiveness while minimizing interference. It’s about managing the ‘electronic airspace’ to avoid collisions and ensure efficient use of radio frequencies.
Imagine a complex battlefield with numerous friendly and enemy systems operating simultaneously. Effective spectral management ensures that our own systems don’t interfere with each other, and that our EW systems are deployed in a way that maximizes their effectiveness against enemy systems without causing unintended interference with civilian or friendly systems.
This involves careful frequency allocation, coordination among different EW platforms, and the use of advanced signal processing techniques to minimize interference and optimize performance. Poor spectral management can lead to degraded performance, mission failure, and even friendly fire incidents. It’s about achieving a harmony in the electronic chaos of the battlefield.
Q 14. How does Electronic Warfare interact with other military domains (e.g., cyber warfare)?
Electronic Warfare interacts extensively with other military domains. Its relationship with cyber warfare is particularly significant. Both domains involve the manipulation and exploitation of information and systems, but they operate at different layers.
EW primarily operates at the physical layer, dealing directly with radio frequency emissions. Cyber warfare, on the other hand, often focuses on manipulating software, data, and network systems. However, these domains are increasingly convergent. For example, cyberattacks can disrupt EW systems, while EW can be used to disable or degrade cyber warfare infrastructure.
Consider a scenario where an enemy attempts to use a cyberattack to disable our EW systems. This could render us vulnerable to enemy electronic attacks. Simultaneously, we might use EW techniques to disrupt the enemy’s command and control networks, which are heavily reliant on networked systems. This highlights the interconnectedness and interdependence between these crucial military domains. Successful military operations require coordinated efforts across all domains, including a close collaboration between EW and cyber warfare specialists.
Q 15. Describe various types of Electronic Attack techniques.
Electronic Attack (EA) encompasses various techniques aimed at degrading or denying an adversary’s use of the electromagnetic spectrum. These techniques can be broadly categorized as:
- Jamming: This involves transmitting interfering signals to disrupt or mask enemy communications, radar, or navigation systems. Think of it like shouting over someone on a phone call – you’re making it difficult for them to understand the conversation. Different jamming techniques exist, including noise jamming (broadband interference), sweep jamming (hopping across frequencies), and deceptive jamming (simulating friendly signals).
- Spoofing: This involves transmitting false signals to deceive enemy systems. For example, a spoofed GPS signal could lead enemy aircraft to a wrong location. This is like sending a fake map to mislead someone.
- Deception: This involves using a variety of techniques, often in combination with spoofing and jamming, to create false information and mislead the enemy, potentially diverting their attention or resources.
- Disruption: Techniques designed to disable or damage enemy electronic systems through high-power microwave pulses, for example. This is a more aggressive form of EA, potentially causing permanent damage.
The choice of EA technique depends on the specific target, the operational environment, and the desired effect. For instance, during a naval engagement, jamming enemy radar might be prioritized, while in an air-to-air combat scenario, spoofing GPS signals could be more effective.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. What are the limitations of Electronic Warfare systems?
Electronic Warfare (EW) systems, while powerful, have inherent limitations:
- Limited Range and Bandwidth: Jamming and other EA techniques have limited range and are often constrained by available bandwidth. A powerful jammer might be effective only within a specific geographic area or frequency band.
- Vulnerability to Countermeasures: Enemy forces employ various countermeasures such as frequency hopping, spread spectrum techniques, and adaptive signal processing to mitigate the effects of EA. It’s a continuous arms race.
- Self-Jamming and Friendly Fire: EW systems can inadvertently interfere with friendly forces’ communications or sensors. Careful coordination and precise targeting are crucial to avoid this.
- Dependence on Intelligence: Effective EW operations require accurate intelligence about enemy systems and their operating frequencies. Incomplete or outdated information significantly reduces effectiveness.
- Technological Limitations: The effectiveness of EW systems is constantly challenged by technological advancements in the opponent’s systems, requiring continuous upgrades and adaptation.
These limitations highlight the importance of careful planning, coordination, and the integration of EW capabilities with other military assets.
Q 17. Explain the importance of maintaining situational awareness during Electronic Warfare operations.
Maintaining situational awareness is paramount during EW operations. Without it, effective EW employment is impossible. Think of it like playing chess blindfolded – you’d quickly be defeated. Situational awareness provides context and allows for:
- Effective Targeting: Knowing the location, capabilities, and activities of enemy systems allows for precise targeting of EA efforts.
- Predictive Analysis: Understanding enemy tactics and likely responses enables proactive countermeasures.
- Coordination with Friendly Forces: Situational awareness facilitates seamless coordination with friendly units to avoid interference and maximize the impact of EW actions.
- Assessment of Effectiveness: Continuous monitoring of the electromagnetic environment provides insights into the success or failure of EA techniques, allowing for adaptive adjustments.
Situational awareness is achieved through a combination of intelligence gathering, sensor data fusion, and effective communication across all involved units. It is a dynamic process requiring constant attention and adjustment.
Q 18. How do you mitigate the effects of enemy jamming on friendly systems?
Mitigating the effects of enemy jamming requires a multi-faceted approach:
- Frequency Hopping: Quickly changing operating frequencies makes it difficult for jammers to track and effectively disrupt communications or radar systems.
- Spread Spectrum Techniques: Spreading the signal across a wider bandwidth reduces the impact of narrowband jamming.
- Adaptive Signal Processing: Employing algorithms that can detect and compensate for jamming signals in real-time.
- Redundancy and Backup Systems: Having alternative communication or navigation systems ensures operational continuity if one system is jammed.
- Directional Antennas: Focusing the transmission signal reduces interference from unwanted sources and improves signal-to-noise ratio.
- Electronic Protection (EP): Implementing measures designed to safeguard systems from the effects of jamming, including signal processing techniques to improve signal quality.
The best mitigation strategy often involves combining several of these techniques, tailored to the specific threat and the system being protected. The selection process heavily relies on understanding both the friendly system limitations and the adversary’s jamming capabilities.
Q 19. Describe your experience with Electronic Warfare simulation and training tools.
My experience with EW simulation and training tools spans various platforms, from individual operator training systems to large-scale, combined arms simulations. I’ve extensively used tools such as OneSAF (One Semi-Automated Forces) and proprietary simulations for specific EW systems. These tools allow for:
- Realistic Threat Replication: Simulations realistically model enemy EW capabilities, allowing trainees to practice against a wide range of threats.
- Safe Experimentation: Operators can safely experiment with different EA techniques and countermeasures without risk to real-world assets.
- After-Action Reviews: Detailed data logs and performance metrics facilitate post-exercise analysis and improvement.
- Collaboration and Teamwork: Simulations provide a platform for training combined arms operations, fostering interoperability and teamwork between different units and systems.
I’ve also been involved in developing and validating new simulation scenarios, ensuring that they accurately reflect real-world operational challenges and provide valuable training experiences.
Q 20. What are some common Electronic Warfare countermeasures?
Common Electronic Warfare countermeasures aim to negate or reduce the effectiveness of enemy EA actions. These include:
- Frequency Agility: Quickly switching to different frequencies to avoid jamming.
- Spread Spectrum: Spreading the signal across a wider bandwidth to make jamming less effective.
- Adaptive Signal Processing: Using algorithms to identify and mitigate jamming signals in real-time.
- Directed Energy Weapons (DEWs): High-power microwave weapons can disable or destroy enemy electronic systems. This is a more advanced and aggressive countermeasure.
- Electronic Protection (EP): A broad category that includes techniques and technologies to protect friendly systems from electronic attack.
- Intelligence Gathering: Understanding the adversary’s EW capabilities is essential for developing effective countermeasures.
The selection of appropriate countermeasures depends on the specific threat, the capabilities of friendly forces, and the operational context. Effective EW necessitates a comprehensive approach, often incorporating multiple countermeasures simultaneously.
Q 21. How do you ensure the security and integrity of Electronic Warfare data?
Ensuring the security and integrity of EW data is crucial to maintain operational effectiveness and prevent intelligence leaks. This involves a layered approach:
- Data Encryption: Encrypting all sensitive EW data, both in transit and at rest, prevents unauthorized access.
- Access Control: Implementing strict access control measures to limit access to EW data based on the need-to-know principle.
- Network Security: Securing EW networks with firewalls, intrusion detection systems, and other security protocols to prevent unauthorized access and data breaches.
- Data Integrity Checks: Implementing mechanisms to detect and prevent data tampering or alteration.
- Regular Audits and Assessments: Conducting regular security audits and vulnerability assessments to identify and address security weaknesses.
- Personnel Security: Thorough background checks and security clearances for personnel with access to sensitive EW data. This includes regular security training and awareness sessions.
The security of EW data is an ongoing process requiring constant vigilance and adaptation to emerging threats. Data breaches can have severe operational and strategic consequences, requiring a robust security framework and strict adherence to protocols.
Q 22. Explain the process of troubleshooting malfunctions in Electronic Warfare systems.
Troubleshooting Electronic Warfare (EW) system malfunctions requires a systematic approach, combining technical expertise with a methodical process. Think of it like diagnosing a complex medical condition – you need to gather evidence, form a hypothesis, and test your theories.
- Initial Assessment: This involves identifying the specific malfunction. Is it a complete system failure, a degraded performance, or an intermittent problem? We use built-in diagnostics, monitoring tools, and error logs to pinpoint the issue. For example, a sudden drop in signal strength might indicate an antenna problem or interference.
- Isolation: Once the problem area is identified, we isolate the faulty component. This might involve checking individual modules, signal paths, or software components. Think of it as tracing a faulty wire in a complex circuit.
- Hypothesis Testing: Based on the observed symptoms and diagnostic data, we formulate hypotheses about the root cause. We then design and execute tests to validate or refute these hypotheses. For example, if the hypothesis is a faulty power supply, we would substitute a known good power supply to test our theory.
- Repair or Replacement: Once the problem is identified and confirmed, the faulty component is repaired or replaced. This might involve board-level repair, component replacement, or even software updates.
- Verification and Validation: After the repair, a thorough verification process ensures that the system is functioning as expected. This includes running comprehensive tests and validating the system’s performance against established benchmarks.
During one mission, we experienced a sudden loss of jamming effectiveness. Through systematic troubleshooting, we isolated the issue to a faulty software module responsible for signal modulation. A quick software update restored full functionality, highlighting the importance of regular software maintenance and readily available backups.
Q 23. Describe your experience with different types of antennas and their applications in Electronic Warfare.
My experience encompasses a wide range of antennas used in EW, each with specific strengths and weaknesses. The choice of antenna is crucial, as it directly impacts the system’s performance.
- Dipole Antennas: Simple, versatile, and relatively inexpensive, dipole antennas are useful for receiving and transmitting signals across a broad frequency range. They are often used in surveillance systems, but their gain is limited.
- Yagi-Uda Antennas: These directional antennas offer higher gain and directivity compared to dipoles, making them ideal for both receiving and transmitting signals over longer distances. We often use these in direction-finding systems.
- Horn Antennas: Horn antennas provide high gain and well-defined beam patterns, making them suitable for applications requiring high directivity, like precise jamming or signal interception.
- Phased Array Antennas: This is a sophisticated antenna technology allowing for electronic beam steering without physically moving the antenna. This offers significant advantages in rapid target acquisition and tracking, crucial in modern EW. I’ve worked extensively with these on advanced EW platforms.
In a recent project, we upgraded our EW system with a phased array antenna. This allowed for real-time beamforming, enabling us to effectively neutralize multiple threats simultaneously – a significant improvement over our previous system that relied on mechanically steered antennas.
Q 24. How do you stay updated on the latest advancements in Electronic Warfare technology?
Staying current in the rapidly evolving field of EW requires a multi-pronged approach.
- Professional Journals and Publications: I regularly read publications such as IEEE Transactions on Aerospace and Electronic Systems, and other specialized EW journals.
- Conferences and Workshops: Attending conferences like the IEEE International Symposium on Phased Array Systems and Technology provides valuable insights into cutting-edge research and technological advancements. Networking with peers is an invaluable aspect of these events.
- Online Resources and Industry Newsletters: Many reputable online sources and industry newsletters keep me informed about the latest developments, new technologies, and emerging threats.
- Vendor Collaboration: Engaging with technology vendors, both directly and through industry groups, keeps me abreast of the newest commercially available technologies and their implications for EW systems.
For example, my awareness of advanced signal processing techniques has been greatly enhanced through attending industry conferences and actively engaging with leading researchers and manufacturers.
Q 25. Describe your experience working with diverse teams in Electronic Warfare operations.
Electronic Warfare operations necessitate collaborative teamwork, drawing on diverse skill sets and perspectives. I have extensive experience working with interdisciplinary teams comprising engineers, intelligence analysts, operators, and programmers.
In one operation, our team, comprising signal analysts, RF engineers, and software developers, was responsible for detecting and mitigating enemy electronic attacks against our assets. The success of the operation heavily relied on the effective communication and collaboration between each team member. Each brought unique expertise to the table, allowing us to devise an efficient and effective countermeasure strategy. Clear communication protocols, regular updates, and mutual respect for each others’ expertise were critical elements to our success.
Q 26. How do you manage time effectively during high-pressure Electronic Warfare situations?
High-pressure EW situations demand exceptional time management skills. Prioritization and clear communication are key.
- Prioritization: Identifying the most critical tasks and focusing resources accordingly is essential. Using a prioritized task list and adhering to a strict schedule helps ensure that the most urgent needs are met first.
- Delegation: Effectively delegating tasks to team members based on their expertise maximizes efficiency and minimizes response times.
- Clear Communication: Maintaining transparent communication with the team ensures everyone is aware of the situation, their responsibilities, and any changes in priorities.
- Adaptive Planning: In dynamic EW environments, plans must be flexible and adaptable to changing circumstances. Regular situation assessments and proactive adjustments to plans are crucial.
During a simulated cyber-attack scenario, our team’s ability to swiftly prioritize critical system defenses and effectively delegate tasks was instrumental in successfully mitigating the threat within the allotted timeframe.
Q 27. Explain your experience with Electronic Warfare system integration and testing.
System integration and testing in EW is a complex multi-stage process involving rigorous procedures to ensure system functionality, reliability, and interoperability.
- Requirements Definition: This initial phase lays out the system’s functional and performance requirements based on operational needs.
- System Design and Development: This stage focuses on selecting components, designing interfaces, and developing the system architecture.
- Integration: The different components are integrated and tested individually. This includes verification that all interfaces function correctly and that the system behaves as designed.
- System-Level Testing: Once fully integrated, the entire system undergoes rigorous testing to verify that it meets all the defined requirements. This involves various test scenarios, from simulated attacks to real-world operational conditions.
- Verification and Validation: After testing, a formal verification and validation process ensures that the system meets all operational needs and standards.
In a recent project, we integrated a new jammer into an existing EW platform. Rigorous testing, including simulated adversarial attacks, ensured seamless integration and validated the system’s performance, exceeding initial expectations.
Q 28. What are the key performance indicators for an effective Electronic Warfare system?
Key performance indicators (KPIs) for an effective EW system vary depending on the specific operational needs, but some common indicators include:
- Effectiveness of Jamming: This measures the system’s ability to disrupt or degrade enemy electronic systems. Metrics might include the percentage of signals successfully jammed or the level of signal degradation achieved.
- Probability of Detection: This indicator assesses the system’s ability to detect enemy emissions, crucial for situational awareness.
- False Alarm Rate: A low false alarm rate is essential to maintain operational efficiency and prevent wasted resources.
- Survivability: The system’s ability to withstand attacks and continue operating under duress is crucial.
- Response Time: Rapid response to threats is a critical factor, measuring the time it takes to detect, identify, and neutralize an electronic threat.
- System Availability: This measures the system’s uptime and its reliability, ensuring it’s operational when needed.
Analyzing these KPIs allows us to evaluate the system’s performance, identify areas for improvement, and make informed decisions about system upgrades or modifications.
Key Topics to Learn for Electronic Warfare Systems Operation Interview
- Electronic Support Measures (ESM): Understanding the principles of signal detection, identification, geolocation, and analysis. Practical application: Analyzing intercepted radar signals to identify the emitter type and location.
- Electronic Attack (EA): Knowledge of jamming techniques, deception strategies, and the capabilities of various EA systems. Practical application: Designing a jamming strategy to counter a specific threat radar.
- Electronic Protection (EP): Understanding methods for protecting friendly systems from electronic attack. Practical application: Implementing countermeasures to mitigate the effects of jamming on communication systems.
- Cyber Warfare Integration: Understanding the intersection of electronic warfare and cyber operations, including network-centric warfare and data exploitation. Practical application: Analyzing the vulnerabilities of electronic warfare systems to cyber attacks.
- System Operation and Maintenance: Hands-on experience with electronic warfare systems, including troubleshooting, diagnostics, and repair procedures. Practical application: Describing your experience maintaining and troubleshooting EW equipment in a field environment.
- Signal Processing Techniques: Familiarity with digital signal processing, filtering, and modulation/demodulation techniques relevant to EW systems. Practical application: Explaining how you would process a complex signal to extract relevant information.
- Threat Analysis and Modeling: Ability to assess potential threats, predict adversary actions, and develop effective countermeasures. Practical application: Developing a threat model for a specific operational scenario.
- EW System Architectures: Understanding the architecture and functionality of various EW systems, including their components and interoperability. Practical application: Describing the strengths and weaknesses of different EW system designs.
Next Steps
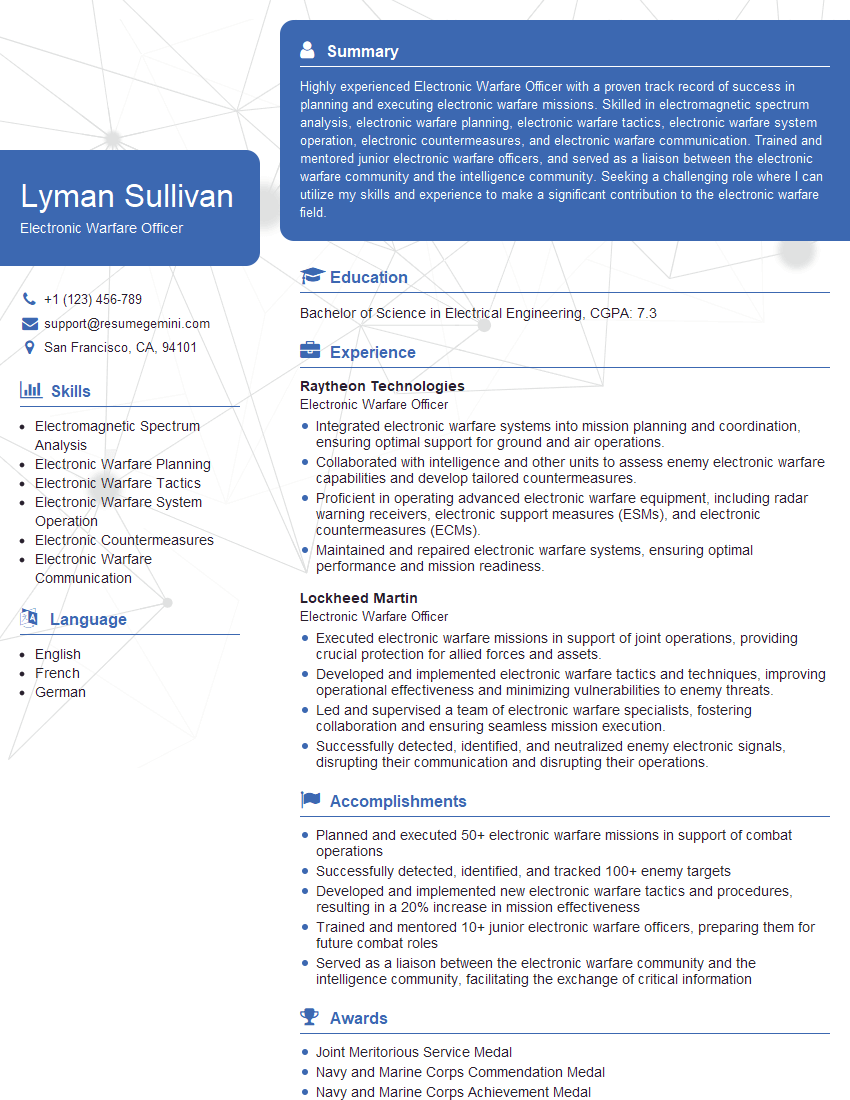
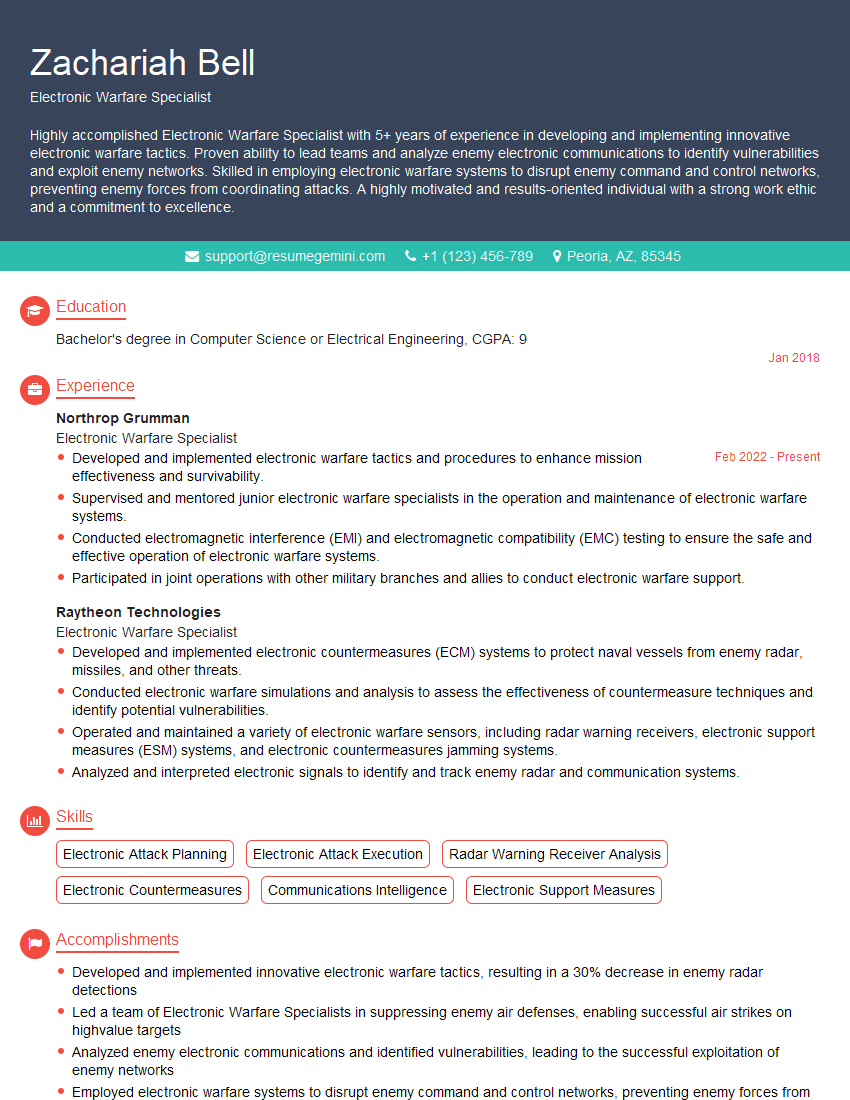
Mastering Electronic Warfare Systems Operation opens doors to exciting and impactful careers within the defense and intelligence sectors. To maximize your job prospects, it’s crucial to present your skills effectively. An ATS-friendly resume is essential for getting your application noticed by recruiters and hiring managers. We strongly recommend using ResumeGemini to create a professional and impactful resume that highlights your expertise in Electronic Warfare Systems Operation. ResumeGemini provides tools and examples to build a compelling resume; examples of resumes tailored to Electronic Warfare Systems Operation are available to guide you.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good