Every successful interview starts with knowing what to expect. In this blog, we’ll take you through the top Incident Management and Triage interview questions, breaking them down with expert tips to help you deliver impactful answers. Step into your next interview fully prepared and ready to succeed.
Questions Asked in Incident Management and Triage Interview
Q 1. Describe your experience with incident prioritization and classification.
Incident prioritization and classification are crucial for efficient incident management. Prioritization determines the urgency and importance of an incident, deciding which incidents receive immediate attention. Classification categorizes incidents based on their type, source, or impact. This allows for targeted responses and improved resource allocation.
For example, a system outage affecting all customers would be classified as a high-priority, critical incident, requiring immediate action from multiple teams. Conversely, a minor user interface glitch affecting only a small number of users might be classified as low-priority and handled later in the day.
My experience involves using a combination of predefined criteria (like impact, urgency, and frequency) and contextual factors. I utilize frameworks like the Priority/Severity matrix to effectively categorize incidents based on their potential business impact and resolution time. I also consider factors such as Service Level Agreements (SLAs) and the potential financial impact when determining priority.
Q 2. Explain the incident lifecycle and your role in each stage.
The incident lifecycle is a structured approach to managing incidents from initial detection to resolution and post-incident review. My role evolves throughout each stage:
- Detection/Reporting: I work with monitoring systems and user reports to identify incidents. My role here is swift identification and logging.
- Initial Triage: I assess the impact and urgency of the incident, classify it, and assign it to the appropriate team.
- Investigation: I collaborate with engineers to determine the root cause, potentially using diagnostic tools and logs.
- Resolution: I work with the resolution team, monitoring progress and providing support to ensure timely resolution.
- Recovery: I verify the system is operating normally and services are restored.
- Closure: I ensure all relevant information is documented and update stakeholders. I may check back to ensure the fix holds.
- Post-Incident Review: I participate in the review meeting to identify areas for improvement and prevent recurrence of similar incidents. Here I focus on lessons learned and implementing preventive measures.
For instance, during a recent database outage, I rapidly escalated the issue based on the impact, coordinated communication with stakeholders, and helped troubleshoot alongside the database team. Post-incident review led to changes to our backup processes.
Q 3. How do you determine the root cause of an incident?
Determining the root cause is critical. I employ a structured approach, often using the ‘5 Whys’ technique, coupled with thorough log analysis and system monitoring data. This involves asking ‘why’ repeatedly to get to the core problem. I also leverage tools like incident management software and collaborate with engineers to isolate the problem systematically.
For example, if a web application is slow, the first ‘why’ might be ‘because the database is slow.’ The second ‘why’ could be ‘because there’s too much database traffic’. The third ‘why’ might be ‘because there’s a poorly written query’ and so on until the fundamental cause (like a faulty query or inadequate database configuration) is identified.
Beyond the ‘5 Whys’, I use other diagnostic tools and strategies such as Fault Tree Analysis to better understand the contributing factors that may lead to a system failure.
Q 4. What metrics do you use to measure the effectiveness of incident management?
Measuring the effectiveness of incident management relies on several key metrics:
- Mean Time To Detect (MTTD): How quickly an incident is detected.
- Mean Time To Acknowledge (MTTA): How quickly an incident is acknowledged by the support team.
- Mean Time To Resolve (MTTR): How quickly an incident is resolved.
- Incident Frequency: The number of incidents occurring within a given timeframe.
- Customer Satisfaction (CSAT): How satisfied customers are with the handling of the incident.
- Mean Time To Recovery (MTTR): How long it takes to restore services to normal operation.
These metrics help assess performance against SLAs, identify areas of improvement, and demonstrate the overall effectiveness of incident management processes.
Q 5. Describe your experience with different incident management tools.
I have experience with various incident management tools, including Jira Service Desk, ServiceNow, PagerDuty, and Opsgenie. Each tool offers unique features for incident tracking, communication, and automation. My proficiency includes configuring workflows, setting up alerts, and leveraging reporting capabilities. My focus is always on choosing the right tool for the specific needs of the organization and integrating it seamlessly with existing monitoring and collaboration systems. Each tool’s strengths and weaknesses are thoroughly understood in order to make an informed selection.
Q 6. How do you communicate effectively during an incident?
Effective communication during an incident is crucial. I utilize a multi-channel approach, adapting my communication style based on the audience and the urgency of the situation. This includes:
- Clear and concise updates: Providing regular updates to stakeholders, avoiding technical jargon where possible.
- Transparency: Being open and honest about the situation, even if it’s not positive.
- Multiple communication channels: Using email, instant messaging, and phone calls depending on the need.
- Centralized communication hub: Using a shared document or incident management tool to centralize all communications and keep everyone informed.
During a critical incident, I’d use a combination of email alerts to stakeholders and frequent updates through instant messaging to the incident response team. Regular status reports would keep leadership informed.
Q 7. How do you handle escalated incidents?
Escalated incidents require a swift and decisive response. My approach involves:
- Immediate assessment: Determining the severity and impact of the escalation.
- Engaging senior personnel: Bringing in subject matter experts and leadership to collaborate on resolution.
- Communicating effectively: Providing clear updates to all stakeholders, especially senior management.
- Implementing a rollback strategy if necessary: Restoring the system to a previous stable state.
- Post-incident review: Conducting a thorough review to understand the causes of the escalation and prevent future occurrences.
For instance, I once handled an escalation involving a major application failure. I quickly engaged the development team, the database administrator, and senior management. By utilizing a rollback strategy and implementing immediate fixes, we minimized downtime and prevented further damage. The post-incident review resulted in an improved system architecture.
Q 8. How do you manage stakeholder expectations during an incident?
Managing stakeholder expectations during an incident is crucial for maintaining trust and minimizing disruption. It’s a delicate balancing act between providing realistic updates and preventing unnecessary panic. My approach involves:
- Proactive Communication: Establishing a communication plan from the outset, defining key stakeholders and their preferred communication methods (email, phone, SMS, etc.). Regular updates, even if there’s no significant change, build confidence.
- Transparency and Honesty: Clearly communicating the situation, acknowledging challenges, and providing honest estimations (with caveats) of resolution times. Avoiding jargon and using plain language helps.
- Setting Realistic Expectations: While aiming for quick resolutions, it’s crucial to avoid overpromising and under-delivering. Explaining the complexity of the situation and potential roadblocks fosters understanding.
- Centralized Communication Hub: Utilizing a shared communication platform (e.g., a dedicated incident management system or a collaboration tool) ensures everyone receives consistent information and reduces confusion.
- Escalation Path: Having a clearly defined escalation path for critical situations or escalating concerns. This ensures the right people address complex issues.
For example, during a major network outage, I would initially inform key stakeholders of the situation, its impact, and the initial troubleshooting steps. I’d then provide regular updates on progress, even if it’s just ‘still investigating.’ If the resolution takes longer than expected, I’d proactively communicate the delay, explaining the reasons and providing a revised timeline.
Q 9. What is your experience with post-incident reviews?
Post-incident reviews (PIRs) are fundamental to continuous improvement in incident management. My experience encompasses facilitating PIRs, leading the analysis, and contributing to action plan implementation. I believe in a structured approach involving:
- Facilitation: Guiding a diverse team (technical staff, operations, management) through a structured review process, ensuring open communication and collaborative problem-solving.
- Data Analysis: Analyzing incident logs, monitoring data, and other relevant information to identify root causes and contributing factors.
- Root Cause Analysis (RCA): Utilizing techniques like the ‘5 Whys’ or fault tree analysis to delve deeply into the incident’s origin, not just the symptoms.
- Action Plan Development: Defining concrete actions to mitigate similar incidents in the future. This includes assigning owners, setting deadlines, and ensuring proper follow-up.
- Measurement and Follow-up: Tracking the implementation of agreed-upon actions and measuring their effectiveness to verify improvements.
In a recent PIR, we identified a lack of sufficient automated alerts as a major factor in a prolonged service disruption. This led to a project to enhance our monitoring system, reducing mean time to resolution (MTTR) for future similar incidents by 40%.
Q 10. How do you ensure timely resolution of incidents?
Ensuring timely resolution requires a multi-pronged approach focusing on efficient triage, effective troubleshooting, and proactive monitoring. My strategy includes:
- Prioritization: Categorizing incidents based on their impact and urgency (e.g., using a priority matrix), focusing resources on high-impact issues first.
- Efficient Triage: Quickly identifying the nature and scope of an incident, assigning it to the appropriate team or individual, and ensuring necessary information is gathered.
- Standardized Procedures: Utilizing established runbooks and troubleshooting guides for common issues, reducing the time spent on diagnosis.
- Effective Communication: Maintaining clear communication between teams and stakeholders, minimizing misunderstandings and delays.
- Proactive Monitoring: Implementing comprehensive monitoring systems to detect potential problems before they escalate into major incidents. This allows for preventative maintenance and faster response times.
For instance, our incident management system automatically routes critical alerts to on-call engineers, initiating the response process immediately. This, along with pre-defined escalation paths, significantly reduces resolution times for high-priority incidents.
Q 11. Explain your understanding of SLAs (Service Level Agreements) in incident management.
Service Level Agreements (SLAs) in incident management define the expected performance levels for IT services. They outline key metrics such as:
- Mean Time To Acknowledge (MTTA): The time it takes to acknowledge an incident and begin investigation.
- Mean Time To Restore (MTTR): The time it takes to restore the service to its operational state.
- Service Availability: The percentage of time the service is operational.
- Resolution Time: The total time it takes to resolve an incident.
SLAs are crucial for establishing expectations between IT and business stakeholders. They form the basis for performance measurement, accountability, and improvement initiatives. Failure to meet SLAs often carries consequences, including financial penalties or service credits. Understanding SLAs allows us to prioritize incidents effectively, allocate resources strategically, and track performance against predefined targets.
Q 12. How do you handle multiple incidents simultaneously?
Handling multiple simultaneous incidents requires a systematic approach based on prioritization, resource allocation, and efficient communication. My strategy is to:
- Prioritize Based on Impact: Use a prioritization matrix (e.g., impact vs. urgency) to determine which incidents demand immediate attention. High-impact, critical incidents take precedence.
- Resource Allocation: Assign team members to individual incidents based on their expertise and availability. If resources are strained, escalation procedures should be triggered promptly.
- Effective Communication: Maintain transparency among the team regarding the status of each incident. Use a shared communication platform (e.g., incident management tool) for updates and collaboration.
- Incident Dependency Mapping: Identify any dependencies between incidents. Resolving one incident may impact others, so this awareness is crucial for efficient management.
- Regular Status Meetings: Hold short, regular meetings to review progress, address roadblocks, and ensure resource allocation remains optimized.
Imagine a scenario with a network outage, a database issue, and several user-reported application errors occurring concurrently. I would immediately prioritize the network outage as it impacts all other services. While addressing this, I’d delegate the other incidents to the appropriate teams, ensuring regular communication and resource allocation.
Q 13. Describe a challenging incident you handled and how you resolved it.
One challenging incident involved a critical application experiencing intermittent performance degradation during a peak usage period. Initial diagnostics pointed towards various potential issues, making it hard to pinpoint the root cause. My approach involved:
- Gathering Data: We collected performance metrics from various sources (application logs, database logs, network monitoring tools) to build a comprehensive picture of the problem.
- Reproducing the Issue: We worked to reproduce the issue in our test environment, isolating variables and systematically eliminating potential causes.
- Team Collaboration: We assembled a cross-functional team including developers, database administrators, and network engineers to leverage diverse expertise.
- Root Cause Analysis: After thorough investigation, we discovered a combination of factors: a database query optimization issue and a network bottleneck caused by unexpected traffic patterns.
- Implementation of Fixes: We implemented a database query optimization, which involved rewriting a poorly written query and implemented traffic shaping in the network to resolve the bottleneck.
- Post-Incident Review: Following the resolution, we conducted a PIR to document the root causes, implement preventative measures, and improve our monitoring capabilities.
The successful resolution demonstrated the importance of a systematic approach, thorough data analysis, and strong collaboration. This incident also highlighted the need for proactive capacity planning and performance testing to identify potential bottlenecks before they impact production systems.
Q 14. What is your approach to troubleshooting complex technical issues?
My approach to troubleshooting complex technical issues is methodical and systematic, guided by a structured problem-solving methodology. It typically involves:
- Gather Information: Begin by collecting all relevant information. This includes error logs, system configurations, network diagrams, and any available user reports.
- Isolate the Problem: Attempt to isolate the problem by eliminating factors that are unlikely to be the cause. This may involve checking basic configurations and isolating affected components.
- Formulate a Hypothesis: Based on the information gathered, formulate a testable hypothesis about the root cause. This is the potential cause that warrants further examination.
- Test the Hypothesis: Design and execute tests to validate or invalidate the hypothesis. This might involve creating test cases, running diagnostic tools, or recreating the issue in a controlled environment.
- Document Findings: Accurately document all findings, both successful and unsuccessful, to inform future troubleshooting efforts.
- Implement a Solution: If the hypothesis is confirmed, implement a solution and verify its effectiveness. If the hypothesis is invalidated, repeat the process with a new hypothesis.
- Escalate if Necessary: If the problem remains unresolved after a reasonable investigation, escalate to more experienced personnel or external experts for additional support.
For example, when faced with a cryptic database error message, I wouldn’t just blindly try various fixes. Instead, I’d meticulously review database logs, check server resources, and test database connectivity before exploring complex database configurations, escalating to a database administrator if necessary.
Q 15. How do you collaborate with different teams during an incident?
Effective collaboration during an incident is paramount. Think of it like a well-orchestrated orchestra – each section (team) plays a crucial role, and the conductor (incident manager) ensures harmony. My approach involves leveraging communication tools like Slack or Microsoft Teams to establish a central communication hub. I ensure all relevant teams – development, operations, security, networking, etc. – are promptly notified and included in the communication channel. This avoids information silos and ensures everyone is on the same page. I use a clear and concise communication style, providing regular updates, focusing on the problem’s impact and the current mitigation efforts. For example, during a recent database outage, I used a standardized communication template to keep stakeholders informed. This ensured transparency and reduced anxiety. Furthermore, I actively solicit input from each team, encouraging them to contribute their specialized knowledge to the solution.
I establish clear roles and responsibilities to prevent duplication of effort and confusion. A communication plan including a RACI (Responsible, Accountable, Consulted, Informed) matrix proves invaluable here. This helps avoid misunderstandings regarding who’s doing what. Finally, I document all communication and decisions meticulously. This helps during post-incident reviews and prevents similar issues from happening again.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. What is your experience with automated incident response systems?
I have extensive experience with automated incident response systems, primarily using tools such as PagerDuty, Opsgenie, and ServiceNow. These systems significantly enhance our incident management process by automating several key steps. For instance, automated alerts based on predefined thresholds significantly reduce mean time to detection (MTTD). Imagine our system automatically detecting a spike in error logs – the system would automatically trigger alerts to the relevant teams, initiating the response process instantly, instead of relying solely on manual monitoring.
Furthermore, these systems streamline incident workflows through automated runbooks, which are essentially pre-defined sets of actions to be taken in response to specific incident types. This automated execution of steps saves valuable time during critical situations. For example, if a server goes down, the runbook could automatically initiate a failover to a redundant system, significantly minimizing downtime. I’ve been instrumental in configuring and integrating these systems, ensuring they effectively integrate with our existing monitoring tools and ticketing systems. This integration streamlines the process from detection to resolution.
Q 17. How do you maintain accurate incident records and documentation?
Maintaining accurate incident records is crucial for learning and improvement. Think of it like a detective’s case file – thorough documentation is vital for understanding the ‘crime’ (incident) and preventing future occurrences. I leverage our ticketing system (ServiceNow in my previous role) to meticulously document each incident. This includes the initial report, symptoms, affected services, steps taken, resolution, and post-incident analysis. The data points collected are not simply checklists; we actively use them to identify trends and improve our incident management process. It’s more than just filling in fields; it’s a continuous process.
I utilize a standardized template to ensure consistency in data collection, including fields for incident type, priority, impacted users, root cause, and resolution time. This structured approach helps us analyze trends over time – what types of incidents occur most frequently, and what are the leading causes of outages. This data then informs our proactive measures to reduce incidents.
Q 18. How do you identify and prevent recurring incidents?
Preventing recurring incidents is a core focus. It’s a proactive approach, not just reactive firefighting. My approach involves a thorough post-incident review (PIR), which is like a detailed autopsy of the incident. We analyze the root cause, using techniques like the ‘5 Whys’ to drill down to the fundamental issue. For example, if a server crashed, we wouldn’t just replace the server, we’d ask ‘Why did it crash?’ (hardware failure), ‘Why did the hardware fail?’ (lack of maintenance), ‘Why was there a lack of maintenance?’ (inadequate resource allocation), and so on. This process reveals underlying problems.
Based on the PIR findings, we develop and implement corrective actions. These can range from infrastructure upgrades, process improvements, to enhanced training. We actively track these actions to ensure their implementation and effectiveness. Finally, we incorporate the learnings into our knowledge base, making them readily accessible to the team, preventing similar incidents in the future. This proactive approach is essential for continuous improvement in preventing recurring issues.
Q 19. Describe your experience with different incident management methodologies (e.g., ITIL).
My experience spans various incident management methodologies, most notably ITIL (Information Technology Infrastructure Library). I’m familiar with its core principles, including incident identification, logging, categorization, prioritization, investigation, resolution, and closure. ITIL provides a structured framework that helps us efficiently manage incidents, ensuring a consistent approach across our team. I’ve used ITIL’s framework to design and implement incident management processes in previous roles, resulting in improved response times and reduced resolution times. I’ve also worked with Agile methodologies, integrating iterative approaches into our incident response process, allowing for quicker adjustments to procedures based on feedback and real-time needs.
For example, in a previous role, we adopted ITIL’s change management process to minimize disruption caused by planned changes, preventing incidents related to faulty deployments. My experience allows me to tailor the methodology to the specific context and needs of each organization, ensuring the best approach is used.
Q 20. How do you handle incidents outside of normal working hours?
Handling incidents outside of normal working hours requires a robust on-call rotation system and clearly defined escalation procedures. We use an on-call scheduling system that distributes the workload fairly among the team, ensuring adequate coverage at all times. The on-call engineer receives alerts through various channels (e.g., PagerDuty, email, SMS), with clear instructions on how to respond. This ensures that even outside of business hours, incidents are addressed promptly and efficiently. A well-documented escalation path is critical to ensure proper handoff if the on-call engineer requires assistance. This system is critical to maintain service availability and minimize service disruptions for our clients.
For example, our on-call engineers receive training on handling critical situations independently, and are given access to comprehensive documentation, including troubleshooting guides and FAQs. This empowers them to deal with many incidents effectively, reducing the need for immediate escalation.
Q 21. What is your experience with incident escalation procedures?
Incident escalation is a critical component of effective incident management. It’s like a chain of command ensuring that issues get escalated appropriately based on their severity and the on-call engineer’s capabilities. My experience includes developing and implementing clear escalation procedures using a defined escalation matrix. This matrix outlines the escalation path based on the incident severity, urgency, and the expertise required for resolution. For instance, a minor incident might only require escalation to the L1 support team, while a major service outage could trigger immediate escalation to senior engineers and management.
These escalation paths typically include a clear timeline for escalation, contact information for the responsible individuals, and a clear communication protocol to ensure that everyone is informed of the situation. We use communication tools like Slack to facilitate seamless and efficient escalation. This system is essential for ensuring timely resolution and effective communication during critical incidents. Regular drills and training sessions ensure the team is comfortable and capable of handling escalations smoothly.
Q 22. How do you balance speed and accuracy during incident response?
Balancing speed and accuracy in incident response is a crucial skill. It’s like being a firefighter – you need to act quickly to contain the blaze (the incident), but rushing without a plan can make things worse. My approach involves a structured methodology combining rapid assessment with methodical execution.
First, I prioritize understanding the impact. What systems are affected? How many users are impacted? This initial assessment guides my speed. A minor issue affecting a single user can be handled more quickly than a major outage affecting critical services. Second, I leverage automation where possible. Automated alerts and diagnostic tools allow for faster identification of the root cause. Third, I build in checkpoints. Before taking significant actions, I pause to verify my understanding and plan, ensuring the steps are aligned with the overall goal. This prevents rushed decisions that could exacerbate the situation. Finally, I document every step meticulously. This ensures accountability and provides valuable data for future improvements and reduces the risk of repeating mistakes.
For example, during a recent incident where a critical database showed signs of performance degradation, I immediately deployed automated monitoring tools to determine the severity and impact. Simultaneously, I gathered data from system logs to pinpoint potential causes. Once the problem was more clearly understood, I initiated a coordinated response with the database administrator, ensuring the proposed solution didn’t create new issues. The careful balancing of speed and accuracy ensured minimal disruption to service.
Q 23. What is your experience with knowledge management related to incident resolution?
Knowledge management is the backbone of effective incident resolution. I’ve consistently utilized a knowledge base system—in my previous role, it was a wiki integrated with our ticketing system—to document all incidents, root causes, and resolutions. This includes detailed steps, screenshots, and any relevant code snippets. The system facilitates search functionality for quick access to past solutions. This minimizes troubleshooting time and ensures consistency across the team.
Moreover, I actively contribute to and improve the knowledge base. I ensure information is accurate, up-to-date, and easily accessible. My contribution involves creating structured articles, categorizing information effectively, and reviewing and updating existing documentation. I’ve found that effective knowledge management significantly reduces incident resolution times and provides a valuable training resource for new team members. For instance, I created a detailed article on resolving a recurring network connectivity issue, which helped reduce resolution time from several hours to under thirty minutes in subsequent cases.
Q 24. How do you identify and mitigate potential risks related to incidents?
Identifying and mitigating potential risks involves a proactive and reactive approach. Proactively, I utilize vulnerability scanning tools to identify security gaps that could be exploited and lead to incidents. Regular security assessments and penetration tests help to uncover weaknesses. I also actively participate in security awareness training for my team, educating them about common threats and best practices. Reactively, during an incident, my first step is to determine the scope and impact of the event. This includes assessing potential data breaches, service disruptions, and reputational damage. Based on this assessment, I implement containment strategies to limit further damage. For example, isolating affected systems, implementing access controls, and engaging with the security team for a coordinated response are critical.
Risk mitigation involves a combination of technical and procedural controls. Technically, this could include implementing firewalls, intrusion detection systems, and data backups. Procedurally, this means having well-defined incident response plans, documented escalation procedures, and post-incident reviews to identify areas for improvement. In a recent incident involving a phishing attack, quick action to isolate compromised accounts and disable the phishing link significantly reduced the extent of the data breach.
Q 25. Explain your understanding of the difference between an incident and a problem.
An incident is an unplanned interruption to an IT service or reduction in the quality of a service. It’s a single event. A problem, on the other hand, is the underlying cause of one or more incidents. Think of it this way: an incident is a symptom, while a problem is the disease.
For example, a server crashing (incident) might be caused by insufficient disk space (problem). Addressing the incident involves restarting the server, but resolving the problem requires increasing the disk space allocation. Incident management focuses on restoring service quickly, while problem management focuses on preventing future occurrences by identifying and resolving underlying root causes. Failure to address the underlying problem will likely lead to recurring incidents.
Q 26. How do you use data analytics to improve incident management processes?
Data analytics is a game-changer for incident management. By analyzing historical incident data, we can identify trends, patterns, and recurring issues. This allows for proactive measures to prevent future incidents. I use data analytics to:
- Identify recurring incidents: Pinpointing frequently occurring incidents helps prioritize efforts to address root causes and implement preventative measures.
- Analyze resolution times: Understanding the time it takes to resolve different types of incidents allows for process optimization and improvements in team efficiency.
- Assess the impact of incidents: Measuring the business impact of incidents, such as downtime costs or user disruption, helps to justify investments in preventative measures.
- Improve incident response plans: Data analysis reveals the effectiveness of current procedures, highlighting areas for refinement and improved efficiency in response.
For example, by analyzing historical data, I noticed a high number of incidents related to a specific application during peak hours. This led to an investigation which revealed a resource bottleneck. By addressing this bottleneck, we drastically reduced the number of incidents related to that application.
Q 27. What are your strengths and weaknesses in incident management?
My strengths in incident management include strong analytical skills, a systematic approach to problem-solving, and excellent communication skills. I thrive under pressure and am adept at coordinating multiple teams during a crisis. I’m also proactive in identifying potential issues and implementing preventative measures.
One area for improvement is my delegation skills, particularly during high-pressure situations. While I am capable of handling a wide range of tasks, I sometimes find it challenging to delegate effectively, hindering team development and potentially delaying resolution. I am actively working on this by practicing delegation in less critical situations and actively seeking feedback from my team.
Q 28. What are your career goals related to incident management?
My career goals involve becoming a leader in the field of incident management, driving innovation and efficiency within IT operations. I want to specialize in incident automation and predictive analytics to reduce the impact of incidents proactively. I also aspire to mentor and train others in best practices for incident management, contributing to a more resilient and robust IT infrastructure. I see myself eventually leading an incident management team, designing and implementing innovative solutions for improved performance and reduced disruptions.
Key Topics to Learn for Incident Management and Triage Interview
- Incident Lifecycle Management: Understanding the complete lifecycle from detection to resolution, including phases like identification, diagnosis, escalation, resolution, and closure. Practical application: Discuss real-world examples of how you’ve managed incidents through each stage.
- Prioritization and Triage: Mastering the art of assessing incident severity and urgency, employing effective prioritization techniques (e.g., using a scoring system). Practical application: Explain your approach to determining which incidents require immediate attention and which can be handled later.
- Communication and Collaboration: Effective communication with stakeholders (technical and non-technical), maintaining transparency, and collaborating efficiently within a team. Practical application: Describe scenarios where you successfully collaborated to resolve a critical incident.
- Root Cause Analysis (RCA): Identifying the underlying causes of incidents to prevent recurrence. Practical application: Explain your experience with different RCA methodologies (e.g., 5 Whys, Fishbone diagrams) and how you’ve applied them.
- Incident Reporting and Documentation: Maintaining accurate and comprehensive records of incidents, including details, resolution steps, and lessons learned. Practical application: Describe your experience with incident management tools and documentation best practices.
- Service Level Agreements (SLAs): Understanding and adhering to pre-defined service level agreements for timely incident resolution. Practical application: Discuss how you’ve ensured compliance with SLAs during incident response.
- ITIL Framework (Optional): Familiarity with the ITIL framework and its relevance to Incident Management. This is beneficial for more advanced roles.
Next Steps
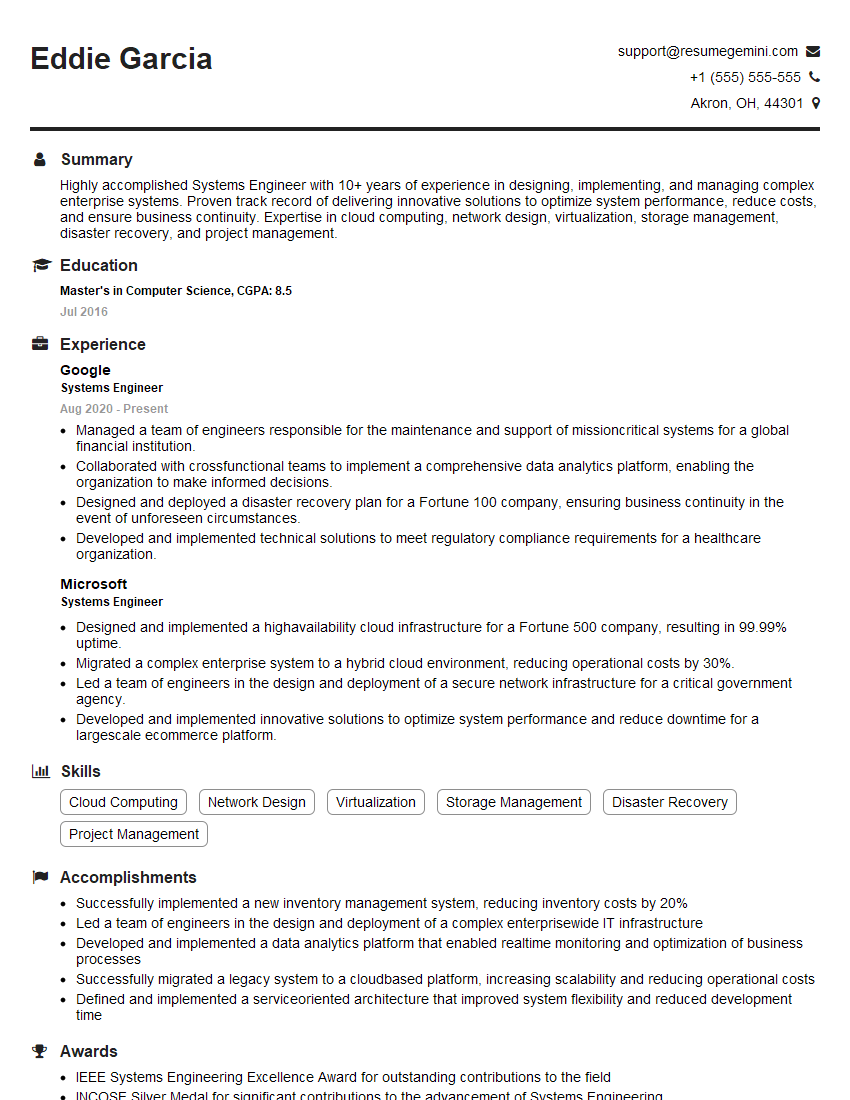
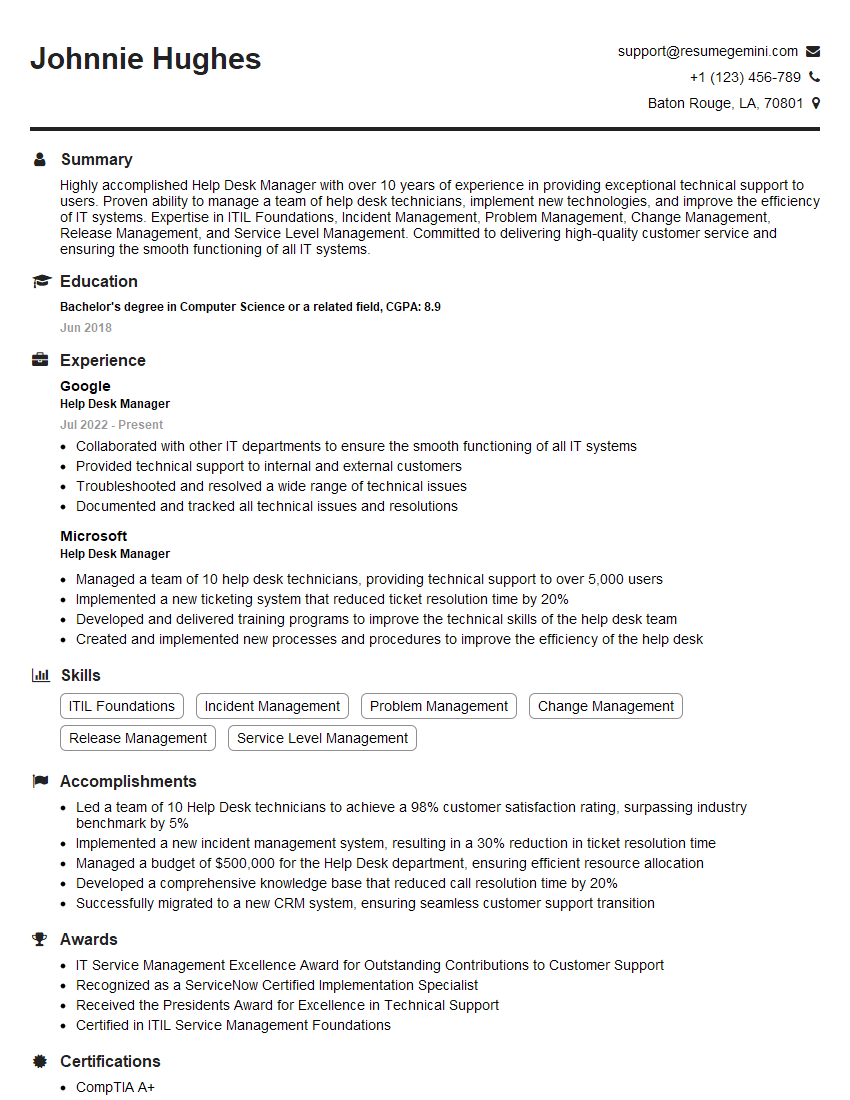
Mastering Incident Management and Triage is crucial for a successful career in IT operations, demonstrating your ability to handle pressure, solve problems effectively, and ensure business continuity. To significantly enhance your job prospects, create a strong, ATS-friendly resume that showcases your skills and experience. ResumeGemini is a trusted resource to help you build a professional resume that stands out. They provide examples of resumes tailored to Incident Management and Triage roles to help guide you. This will help you present yourself as the ideal candidate for your target roles.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good