Cracking a skill-specific interview, like one for Intelligence Cycle Management, requires understanding the nuances of the role. In this blog, we present the questions you’re most likely to encounter, along with insights into how to answer them effectively. Let’s ensure you’re ready to make a strong impression.
Questions Asked in Intelligence Cycle Management Interview
Q 1. Describe the five phases of the intelligence cycle.
The intelligence cycle is a fundamental framework for intelligence operations, encompassing five key phases: Planning & Direction, Collection, Processing & Exploitation, Analysis & Production, and Dissemination. Think of it as an assembly line for information, transforming raw data into actionable intelligence.
- Planning & Direction: This initial stage identifies intelligence needs, sets priorities, and allocates resources. It’s like deciding what recipe you’ll cook—you need to know what ingredients (information) you’ll need and how much time and effort you’ll invest.
- Collection: This involves gathering raw information from various sources, such as human intelligence (HUMINT), signals intelligence (SIGINT), open-source intelligence (OSINT), and more. This is where you gather your ingredients—going to the market, checking your pantry, etc.
- Processing & Exploitation: This phase involves converting raw data into usable intelligence. For example, deciphering intercepted communications (SIGINT), translating documents (HUMINT), or verifying information from the internet (OSINT). This is akin to preparing your ingredients—washing, chopping, etc.
- Analysis & Production: Analysts process the exploited information, interpret patterns, and develop assessments to inform decision-makers. This is where you cook your dish, combining the prepared ingredients to create a final product.
- Dissemination: This is the final stage where intelligence is shared with the appropriate consumers, who use the information for decision-making. This is like serving your dish to those who will enjoy it and benefit from it.
These phases are iterative; feedback loops exist between them, constantly refining the process and improving accuracy.
Q 2. Explain the concept of ‘all-source intelligence.’
All-source intelligence refers to the integration and analysis of information gathered from multiple sources to create a comprehensive and well-rounded intelligence picture. It’s about seeing the whole picture, not just individual pieces. Imagine trying to solve a puzzle—a single piece won’t give you the whole picture, but putting many pieces together will.
Instead of relying solely on one type of intelligence (like only using HUMINT or only using SIGINT), all-source intelligence leverages the strengths of various sources to compensate for their weaknesses. For instance, open-source information (news articles, social media) can provide context, while signals intelligence might reveal hidden communications. By combining these, analysts gain a far richer understanding of the situation.
The key is integrating different data types, methodologies, and perspectives to develop a more robust and reliable assessment. This holistic approach minimizes bias and enhances the accuracy of the final intelligence product.
Q 3. How do you prioritize intelligence requirements?
Prioritizing intelligence requirements is crucial for effective resource allocation. I employ a multi-faceted approach that considers several factors:
- Urgency and Time Sensitivity: Immediate threats or rapidly evolving situations take precedence. This is like prioritizing a burning house over a leaky faucet.
- Impact and Relevance to Missions: Requirements directly impacting key missions or objectives are prioritized over those with less direct relevance. This is focusing your resources on the most impactful work.
- Feasibility and Cost: Some intelligence requirements may be too costly, time-consuming, or impossible to fulfill with available resources. This is a reality check – some things simply aren’t feasible at the time.
- Value Added: Prioritization considers the potential impact of the intelligence. What will this intelligence achieve, and is the return on investment worth the effort?
I often utilize a matrix or scoring system to quantitatively assess these factors, ensuring objective prioritization. The process isn’t static; priorities are reassessed regularly as the situation evolves.
Q 4. What are the key challenges in intelligence collection?
Intelligence collection faces numerous challenges, including:
- Technological advancements: Adversaries are constantly developing new technologies to protect their communications and operations, making collection more difficult. Think about encryption – it’s a constant arms race.
- Accessibility and Legal Restrictions: Gathering intelligence requires careful consideration of legal and ethical implications. This means working within the bounds of the law and respecting privacy.
- Information Overload: The sheer volume of information available can be overwhelming, making it challenging to identify and analyze relevant data. This is like searching for a needle in a haystack.
- Source Reliability and Bias: Not all sources are equally reliable, and biases can affect the accuracy of information. Critical evaluation and cross-referencing are vital.
- Secrecy and Deception: Adversaries actively try to deceive intelligence agencies, making accurate assessment challenging. This necessitates developing methods for identifying deception.
Overcoming these challenges requires the use of cutting-edge technologies, robust analytical skills, and a commitment to ethical and legal compliance.
Q 5. Describe your experience with intelligence processing and analysis.
My experience in intelligence processing and analysis spans over [Number] years, involving extensive work with [mention specific types of intelligence, e.g., SIGINT, HUMINT, OSINT]. I’m proficient in various analytical techniques, including:
- All-Source Analysis: Integrating data from diverse sources to gain a comprehensive understanding.
- Link Analysis: Identifying relationships and connections between entities and events.
- Geospatial Analysis: Utilizing maps and geographic information systems (GIS) to analyze spatial patterns and relationships.
- Trend Analysis: Identifying patterns and predicting future trends.
I have a proven track record of successfully processing and analyzing complex data sets to produce timely and accurate intelligence assessments. I’ve contributed to [mention specific projects or accomplishments, ensuring they are anonymized if necessary for security reasons]. A recent example involved [anonymized description of a project demonstrating analytical skills and problem-solving abilities].
Q 6. How do you ensure the accuracy and validity of intelligence products?
Ensuring the accuracy and validity of intelligence products requires rigorous methods:
- Source Validation: Verifying the credibility and reliability of all sources used. This involves comparing information across multiple sources and looking for corroborating evidence.
- Data Triangulation: Comparing information from independent sources to confirm its accuracy. Think of it as checking the same story from three different news sources.
- Peer Review: Having other analysts review the intelligence assessment before dissemination. This helps to identify any potential biases or errors.
- Quality Control Measures: Establishing clear standards and procedures for data collection, analysis, and reporting. This includes regular audits and reviews of processes.
- Transparency and Documentation: Clearly documenting the sources and methodologies used, allowing for traceability and accountability. This is crucial for maintaining credibility.
Accuracy is paramount; misleading intelligence can have severe consequences. By adhering to these principles, we minimize the risk of error and ensure that the intelligence provided is reliable and trustworthy.
Q 7. Explain the importance of intelligence dissemination.
Intelligence dissemination is the critical final phase of the intelligence cycle, involving the timely and targeted distribution of intelligence products to decision-makers and consumers. Effective dissemination ensures that those who need the information receive it in a usable format, enabling informed decision-making.
Dissemination is important because:
- It enables informed decision-making: Providing decision-makers with accurate and timely intelligence allows them to make better, more strategic decisions.
- It facilitates coordination and collaboration: Sharing intelligence across agencies and departments fosters cooperation and prevents duplication of effort.
- It enhances situational awareness: Disseminating intelligence helps various stakeholders to maintain a shared understanding of the operational environment.
- It fosters trust and confidence: Regular, transparent, and accurate dissemination builds trust and confidence among the intelligence community and its consumers.
Methods of dissemination include briefings, reports, databases, and secure communication channels, tailored to the specific needs of each recipient. The goal is to ensure the right information reaches the right people at the right time.
Q 8. How do you handle conflicting intelligence information?
Conflicting intelligence is a common challenge. It’s rarely a case of simply choosing one piece of information over another; instead, it requires a systematic approach to analysis and reconciliation. Think of it like a puzzle with missing pieces and some pieces that seem contradictory. My approach involves several steps:
- Identify the conflict: Pinpoint the specific discrepancies between different intelligence sources or reports. This might involve comparing reporting on the same event from human intelligence (HUMINT), signals intelligence (SIGINT), or open-source intelligence (OSINT).
- Assess the credibility of each source: Determine the reliability and track record of each source. Consider factors like past accuracy, motivation, and potential biases. A source with a history of accurate reporting holds more weight than an unverified anonymous tip.
- Analyze the context: Understand the circumstances surrounding the conflicting information. Were there limitations in collection methods? Could there be intentional deception or misinformation involved?
- Corroborate with other intelligence: Search for additional intelligence that might support one version of events or shed light on the inconsistencies. This might involve reviewing supporting documents, conducting further research, or requesting additional data collection.
- Develop a comprehensive assessment: Synthesize all available information, weighing the credibility of each source and the supporting evidence. This might lead to a conclusion that one piece of information is more likely accurate, that the truth lies somewhere in between, or that the conflict remains unresolved, necessitating further investigation.
For example, if one source claims a political figure is planning a coup, while another claims the figure is planning a peaceful resignation, I would examine their respective track records, the methodologies they used to reach their conclusion, and whether corroborating evidence exists from other credible sources. I might investigate the political climate, the figure’s past actions, and statements made by their associates.
Q 9. What are the ethical considerations in intelligence work?
Ethical considerations are paramount in intelligence work. We operate under a strict code of conduct, balancing the need for national security with the rights and freedoms of individuals. Key considerations include:
- Legality: All intelligence activities must adhere to national and international laws. This includes respecting privacy rights, avoiding illegal surveillance, and ensuring proper authorization for all operations.
- Proportionality: The methods used to collect intelligence must be proportional to the threat faced. Intrusive techniques should only be employed when absolutely necessary and justified.
- Accountability: There must be clear lines of accountability for intelligence activities. This includes robust oversight mechanisms to prevent abuse and ensure transparency.
- Privacy: The privacy of individuals must be protected. Intelligence agencies must have clear legal authority and safeguards in place to prevent unwarranted intrusion into the private lives of individuals.
- Objectivity: Intelligence analysis must be objective and unbiased. Personal opinions or political agendas should never influence the assessment of information.
A real-world example might be the debate surrounding the use of drone strikes. While these can be effective in neutralizing terrorist threats, ethical concerns arise regarding civilian casualties and the potential for violating international humanitarian law. It’s our responsibility to ensure that such operations are conducted legally, proportionally, and with the utmost consideration for human life.
Q 10. Describe your experience with intelligence reporting and briefing.
My experience in intelligence reporting and briefing spans several years, encompassing a variety of formats and audiences. I’ve crafted detailed written reports for senior leadership, presenting complex information in a clear, concise, and actionable manner. I’ve also delivered numerous verbal briefings, adapting my presentation style to the audience’s level of expertise and time constraints.
I am adept at using different visualization techniques to highlight key trends and patterns in data. For instance, in briefing on potential geopolitical instability, I might utilize maps to illustrate areas of tension, charts to show the escalation of conflict, and timelines to outline key events leading up to the current situation. I prioritize clarity and accuracy to ensure that the audience gains a comprehensive understanding of the intelligence presented, facilitating effective decision-making. This often involves using both verbal and visual communication to make the information easily digestible and impactful.
Q 11. How do you assess the credibility of intelligence sources?
Assessing source credibility is crucial to the intelligence process. It’s a multi-faceted judgment that involves considering several factors:
- Track Record: Has this source provided accurate information in the past? A consistent history of reliable reporting significantly enhances credibility.
- Motivation: What are the source’s motivations for providing this information? Are they seeking personal gain, revenge, or are they genuinely concerned about the issue? A source with ulterior motives should be treated with caution.
- Methods of Collection: How did the source obtain this information? Was it firsthand observation, hearsay, or intercepted communication? Direct observation generally lends more weight to the information.
- Bias: Does the source have any known biases or affiliations that might influence their perspective? It’s crucial to understand any potential biases that might color the information.
- Corroboration: Does the information align with other credible sources and available evidence? Independent corroboration strengthens the credibility of the information significantly.
For example, if a source claims that a specific company is involved in illegal arms dealing, we would examine their past reporting, their potential motivations (e.g., rival company, whistleblower), and how they obtained the information. We would then cross-reference their claims with information from other reliable sources, open-source intelligence, and financial records before forming a conclusion.
Q 12. Explain the role of technology in modern intelligence analysis.
Technology plays a transformative role in modern intelligence analysis. It enhances our ability to collect, process, analyze, and disseminate information with unprecedented speed and efficiency. Key technological advancements include:
- Big Data Analytics: Tools and techniques for analyzing massive datasets from various sources to identify patterns and anomalies that might indicate threats.
- Artificial Intelligence (AI) and Machine Learning (ML): AI and ML algorithms can automate many aspects of intelligence analysis, such as identifying patterns in communication data, predicting future events, and detecting disinformation campaigns.
- Geospatial Intelligence (GEOINT): Satellite imagery, aerial photography, and mapping software provide critical insights into geographical locations, infrastructure, and military movements.
- Signals Intelligence (SIGINT): Advanced technologies are used to intercept and analyze communications, providing valuable insights into adversary plans and activities.
- Cyber Intelligence (CYINT): Tools and techniques for monitoring and analyzing cyber activities, detecting and responding to cyber threats.
For instance, AI can be used to sift through vast amounts of social media data to identify potential terrorist threats, while GEOINT can provide visual confirmation of troop movements. These technologies are crucial for maintaining situational awareness and making informed decisions.
Q 13. How do you manage competing priorities in an intelligence setting?
Managing competing priorities in intelligence is a constant balancing act. I employ a prioritization framework that combines urgency and importance. This involves:
- Prioritization Matrix: I use a matrix to categorize tasks based on their urgency and importance. High-urgency, high-importance tasks are addressed immediately, while low-urgency, low-importance tasks are delegated or postponed.
- Time Management Techniques: Employing techniques like time blocking, the Pomodoro Technique, and task delegation allows efficient allocation of time and resources.
- Communication and Collaboration: Open communication with stakeholders is crucial to ensure alignment on priorities. Collaborative work practices help to distribute the workload and share the burden of conflicting demands.
- Flexibility and Adaptability: Intelligence work is inherently unpredictable. Flexibility and the ability to adapt to changing circumstances are essential for managing competing priorities effectively. It’s important to be prepared to adjust priorities based on new information or changing circumstances.
For instance, if I’m working on a long-term strategic analysis while also needing to respond to an immediate, urgent threat, I will allocate my time and resources accordingly, prioritizing the immediate threat while ensuring that the long-term analysis continues to progress, even if at a slower pace.
Q 14. Describe your experience with using different intelligence databases and tools.
My experience includes extensive use of various intelligence databases and tools. I am proficient in using both classified and unclassified systems, ranging from open-source intelligence platforms like Google Earth and social media monitoring tools to specialized databases containing sensitive information. This includes familiarity with various data visualization tools to analyze and present data effectively.
Specific examples include experience with [mention specific tools or databases used, while avoiding classified information]. My expertise extends to utilizing these tools effectively to extract relevant information, cross-reference data from multiple sources, and identify key patterns and insights. This ensures a comprehensive and well-informed intelligence picture.
Q 15. How do you communicate complex intelligence information to non-technical audiences?
Communicating complex intelligence to non-technical audiences requires translating technical jargon into plain language and focusing on the key takeaways. Think of it like explaining a complicated recipe to someone who’s never cooked before – you need to break it down into simple steps and focus on the end result.
- Use analogies and metaphors: Instead of saying “The adversary employed a sophisticated network infiltration technique,” try “Imagine them using a master key to unlock a secure building.”
- Visual aids: Charts, graphs, and maps are invaluable for simplifying data. A picture really is worth a thousand words, especially when dealing with complex data sets.
- Prioritize key findings: Don’t overwhelm the audience with unnecessary detail. Start with the most important conclusions and only elaborate on the supporting information if needed.
- Tailor the message: Consider the audience’s background and knowledge level. A presentation to senior executives will differ significantly from one given to junior analysts.
- Practice active listening and feedback: After the presentation, make sure to answer questions and address any concerns to ensure your message is understood.
For instance, when explaining the likelihood of a terrorist attack, I would avoid technical terms like ‘probability density function’ and instead use simple statements like ‘there’s a high/medium/low chance’ coupled with supporting evidence presented visually. This ensures clarity and avoids confusion.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. What is your experience with intelligence community collaboration?
My experience with intelligence community collaboration spans several years and diverse projects. I’ve worked extensively with agencies like [mention relevant agencies without compromising security – e.g., ‘various national and international partners’], participating in joint analysis, data sharing, and collaborative investigations.
Successful collaboration hinges on clear communication, mutual trust, and a shared understanding of goals. We often use standardized formats for intelligence reporting to ensure consistency and interoperability. For example, we utilize a common intelligence format (CIF) for exchanging information efficiently across platforms and agencies.
One project involved working with a foreign partner on a transnational organized crime investigation. By using secure communication channels and standardized reporting, we successfully shared sensitive information, leading to a significant number of arrests. This required constant communication, understanding cultural nuances, and navigating differing legal frameworks, proving collaboration’s importance in intelligence gathering.
Q 17. Explain your understanding of intelligence oversight and accountability.
Intelligence oversight and accountability are crucial to ensure ethical conduct and prevent abuses of power. Oversight mechanisms, often involving legislative bodies and independent review boards, monitor intelligence agencies’ activities, ensuring they operate within legal boundaries and respect human rights. Accountability involves mechanisms for investigating and addressing any misconduct or failures. This typically involves internal reviews, external audits, and, in severe cases, legal action.
Examples include regular audits of intelligence agencies’ budgets and operations, rigorous review of targeting procedures to protect civilian lives, and the establishment of independent inspector general offices to investigate allegations of wrongdoing. These processes ensure transparency and promote public trust in intelligence agencies. Without these measures, there’s a risk of unchecked power and potential violations of privacy or international law.
Q 18. Describe a time you had to make a critical decision based on incomplete intelligence.
During a counter-terrorism operation, we received incomplete intelligence regarding a potential imminent attack. The information indicated a possible target and a timeframe, but lacked crucial details about the perpetrators’ capabilities and the method of attack. Making a decision to deploy resources was critical, despite this uncertainty.
To mitigate the risk of incomplete information, we followed a multi-step process:
- Risk Assessment: We weighed the potential consequences of inaction (allowing the attack to proceed) against the risks of acting on incomplete information (e.g., deploying resources unnecessarily).
- Scenario Planning: We developed several plausible scenarios based on the available intelligence, considering best-case, worst-case, and most likely outcomes.
- Consultations: We engaged with other intelligence agencies and subject matter experts to gain additional insights and perspectives.
- Decision Matrix: We used a decision matrix to weigh the different factors and help us make the most informed decision possible, taking into account likelihood and impact of various outcomes.
Ultimately, we decided to deploy a scaled-down response, focusing on surveillance and intelligence gathering before escalating. While the incomplete information made the situation challenging, this approach allowed us to act decisively while limiting unnecessary risks. Following the incident we reviewed the intelligence failure to improve future operational processes.
Q 19. How do you measure the effectiveness of intelligence operations?
Measuring the effectiveness of intelligence operations is complex and requires a multi-faceted approach. It’s not enough to just count the number of reports; we need to assess whether the intelligence provided was accurate, timely, relevant, and influenced decision-making.
- Impact on decision-making: Did the intelligence contribute to a positive outcome, such as preventing a terrorist attack, disrupting a criminal network, or providing strategic advantage?
- Accuracy and timeliness: Was the intelligence accurate and was it delivered in a timely manner? Late intelligence is often as useless as inaccurate intelligence.
- Relevance: Did the intelligence address the specific questions or issues it was intended to address? Was it actionable?
- Feedback mechanisms: Collecting feedback from consumers of intelligence – policymakers, military commanders, etc. – to understand its utility and identify areas for improvement.
- Quantitative metrics: Using quantitative metrics, such as the number of successful operations attributed to intelligence, is only one small piece of the puzzle.
For instance, we might track the number of successful counter-terrorism operations directly resulting from our intelligence. But just as importantly we would solicit feedback from the operational units on how useful our analysis was and whether it could have been better tailored to their needs. It’s about a holistic evaluation, not just counting numbers.
Q 20. How do you stay up-to-date on current intelligence trends and developments?
Staying current on intelligence trends requires a multi-pronged approach. It’s an ongoing process, not a one-time activity.
- Regular briefings and reports: I attend regular intelligence briefings and read reports from various agencies, think tanks, and open-source materials.
- Professional networks: I maintain professional contacts with colleagues and experts in the field to exchange information and perspectives. Conferences and professional organizations play an important part in this.
- Open-source intelligence (OSINT): I actively monitor news sources, social media, and other open-source channels for relevant information. This provides valuable context and early warning signs.
- Specialized publications and journals: Reading academic journals, specialized intelligence publications, and government reports provides in-depth analysis and insights.
- Advanced search techniques: Proficient use of online search engines and databases helps me track specific developments and trends.
For example, I regularly use advanced search operators on Google and other search engines to track specific keywords related to geopolitical events and emerging threats. By combining these methods, I ensure that I have a comprehensive and up-to-date understanding of the intelligence landscape.
Q 21. What are your strengths and weaknesses as an intelligence analyst?
My strengths as an intelligence analyst include strong analytical skills, a meticulous approach to data analysis, and excellent communication skills. I’m adept at identifying patterns, drawing inferences, and presenting complex information in a clear and concise manner. My experience with diverse data sources and methodologies allows me to approach problems from multiple angles.
One area I’m actively working to improve is my ability to handle large volumes of unstructured data. While I possess effective analytical techniques, enhancing my expertise in utilizing AI-powered tools for data processing would significantly improve efficiency and analytical scope. This is an area of active professional development for me, as advancements in technology are rapidly changing the intelligence landscape. I’m actively pursuing training and certifications to address this.
Q 22. What is your experience with using intelligence to inform decision-making?
My experience in using intelligence to inform decision-making spans over a decade, encompassing various roles within both government and private sectors. I’ve consistently focused on bridging the gap between raw intelligence data and actionable insights. This involves not only analyzing information but also understanding the context, limitations, and potential biases inherent in any intelligence product. For example, during my time at [Previous Company Name], I led a team that analyzed market intelligence to inform a major strategic investment decision. We meticulously gathered data from multiple sources, identified key trends, and assessed potential risks, ultimately guiding the company towards a highly successful venture. The key to success here was not simply presenting the data, but crafting a clear, concise, and persuasive narrative that communicated the implications for senior management, ultimately influencing their decision-making process. I believe that effective intelligence informs decision-making by reducing uncertainty, mitigating risks, and identifying opportunities.
Q 23. Describe your experience in risk assessment and mitigation related to intelligence.
Risk assessment and mitigation are integral to any sound intelligence operation. My approach involves a multi-stage process. Firstly, I identify potential threats and vulnerabilities through comprehensive analysis of available intelligence, considering both known and emerging risks. Secondly, I evaluate the likelihood and potential impact of each risk. This often involves using quantitative and qualitative methods, incorporating expert judgment and scenario planning. Thirdly, I develop and implement mitigation strategies, which might include developing contingency plans, enhancing information security measures, or implementing specific countermeasures. For example, while working on a project involving geopolitical analysis, we identified a high likelihood of a specific country enacting trade sanctions. We then mitigated this risk by developing alternative sourcing strategies and diversifying our supply chain, proactively minimizing potential negative impacts. The key here is to be proactive, identifying potential problems before they escalate into major crises. Regular review and adaptation of mitigation strategies are crucial as the risk landscape constantly evolves.
Q 24. Explain your understanding of different intelligence methodologies.
My understanding of intelligence methodologies encompasses a wide range, from traditional methods to cutting-edge techniques. I am proficient in employing both open-source intelligence (OSINT), utilizing publicly available data such as news reports, social media, and academic publications, and closed-source intelligence (HUMINT), which involves human sources and confidential information. I am also experienced in signals intelligence (SIGINT), analyzing communications data, and geospatial intelligence (GEOINT), drawing insights from satellite imagery and mapping. Moreover, I have experience with using advanced analytical techniques like data mining, predictive modeling, and network analysis to uncover patterns, trends and identify critical relationships within complex datasets. A successful intelligence operation often relies on a combination of these methods, employing each to complement the others and build a more holistic picture. For instance, in a recent project, we combined HUMINT insights with GEOINT data to verify the accuracy of information obtained from a sensitive human source, enhancing the credibility and reliability of our final assessment.
Q 25. How do you deal with ambiguity and uncertainty in intelligence analysis?
Ambiguity and uncertainty are inherent characteristics of intelligence analysis. I address this by employing several strategies: Firstly, I embrace a structured approach, utilizing established frameworks to analyze data systematically and reduce cognitive biases. Secondly, I focus on building robust scenarios, considering various possibilities and their associated probabilities. This allows for the development of contingency plans. Thirdly, I explicitly acknowledge and document areas of uncertainty, ensuring that decision-makers understand the limitations of the analysis. Fourthly, I use sensitivity analysis to evaluate how changes in key assumptions impact the conclusions. Finally, I remain open to revising my analysis as new information emerges. Think of it like a detective piecing together a puzzle with some missing pieces; you carefully consider the available evidence, acknowledge gaps, and construct plausible scenarios based on the available information, always leaving room for new discoveries.
Q 26. What are your views on the future of intelligence analysis?
The future of intelligence analysis will be profoundly shaped by technological advancements. I foresee a growing reliance on artificial intelligence (AI) and machine learning (ML) to process vast amounts of data, identifying patterns and anomalies that may elude human analysts. However, human expertise will remain crucial to interpret the results, contextualize findings, and make sound judgments. The increasing importance of cybersecurity will also require intelligence analysts to develop new skills and techniques to counter evolving threats. Furthermore, I believe that collaborative intelligence gathering and sharing, across both government and private sectors, will be essential to address complex, trans-national challenges. The analyst of tomorrow will need to be adept at integrating a wide variety of data sources, employing advanced analytical techniques, and working effectively within multidisciplinary teams to effectively anticipate and respond to emerging threats in a rapidly changing world.
Q 27. How do you contribute to a positive and collaborative team environment in intelligence work?
In my experience, a positive and collaborative team environment is essential for effective intelligence work. I contribute to this by fostering open communication, actively listening to colleagues’ perspectives, and valuing diverse viewpoints. I believe in actively seeking feedback, both giving and receiving constructive criticism, and promoting a culture of mutual respect and trust. I also actively contribute to team knowledge-sharing initiatives, organizing workshops or training sessions to help enhance the team’s collective skills. By valuing every team member’s contributions, fostering transparency and encouraging a free exchange of ideas, we build a more robust and successful intelligence function. The success of intelligence work depends heavily on strong team cohesion and effective collaboration.
Q 28. Describe your experience with intelligence budget management or resource allocation.
My experience with intelligence budget management and resource allocation has involved both strategic planning and operational oversight. I have been involved in the development of annual budgets, prioritizing projects based on their strategic importance and anticipated impact. This process involves careful consideration of resource constraints, optimizing the use of available funding to maximize effectiveness. I have also been responsible for monitoring expenditures, ensuring that resources are allocated efficiently and effectively, and that projects remain within budget. Moreover, I have experience in justifying resource requests to senior management, demonstrating the value and importance of proposed projects through comprehensive cost-benefit analyses. Effective resource allocation within the intelligence community is paramount, demanding meticulous planning, robust monitoring, and constant evaluation to ensure that scarce resources are used in the most effective manner to achieve strategic objectives.
Key Topics to Learn for Intelligence Cycle Management Interview
- Planning & Direction: Understanding the intelligence requirements process, identifying gaps in existing intelligence, and formulating effective collection strategies. Practical application: Developing a plan to address a specific intelligence need, considering resource limitations and potential risks.
- Collection: Mastering various intelligence collection methods (HUMINT, SIGINT, OSINT, etc.), understanding their strengths and weaknesses, and ethical considerations. Practical application: Evaluating the effectiveness of different collection methods for a given scenario and justifying choices.
- Processing & Exploitation: Techniques for analyzing raw intelligence data, converting it into usable information, and utilizing appropriate technologies. Practical application: Demonstrating proficiency in data analysis and interpretation, identifying key trends and patterns.
- Analysis & Production: Developing analytical tradecraft skills, including critical thinking, problem-solving, and hypothesis generation. Practical application: Constructing clear and concise intelligence reports, effectively communicating complex information to diverse audiences.
- Dissemination & Feedback: Understanding secure information sharing protocols, ensuring timely and accurate dissemination of intelligence products, and incorporating feedback into future cycles. Practical application: Describing strategies for disseminating intelligence effectively to decision-makers, while maintaining security and minimizing risk.
- Technology & Tools: Familiarity with relevant software and databases used in intelligence analysis and management. Practical application: Demonstrating competency with relevant technologies and explaining how they enhance the intelligence cycle.
- Ethical Considerations & Legal Frameworks: Understanding legal and ethical limitations, privacy concerns, and the importance of responsible intelligence gathering and dissemination. Practical application: Discussing ethical dilemmas and proposing solutions within the constraints of legal frameworks.
Next Steps
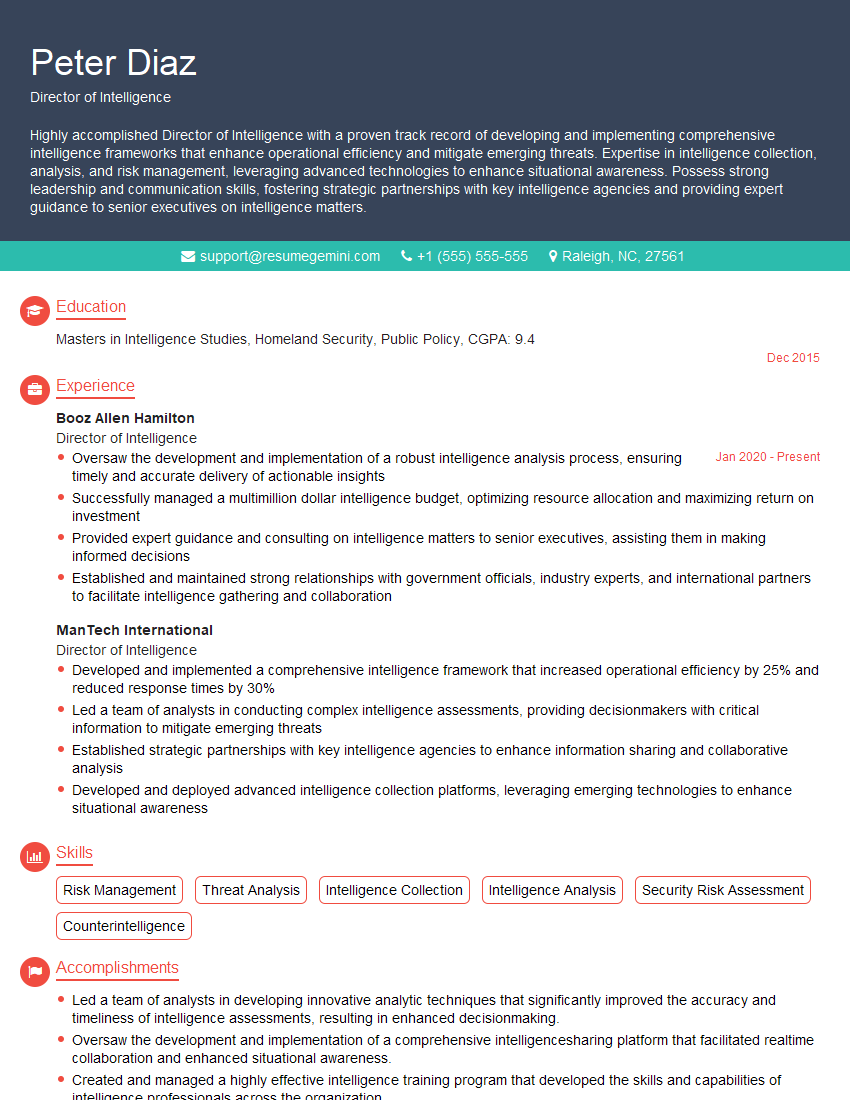
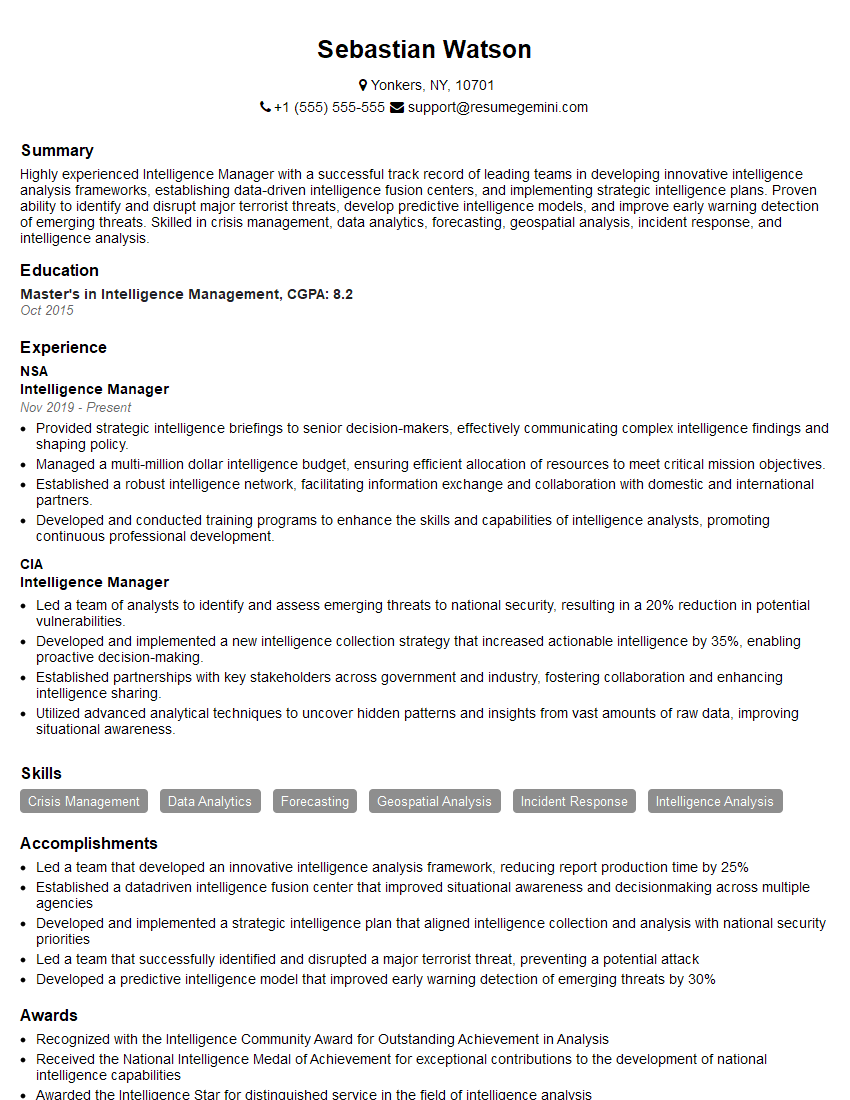
Mastering Intelligence Cycle Management is crucial for career advancement in this dynamic field. It demonstrates a comprehensive understanding of the intelligence process and positions you as a valuable asset to any organization. To significantly increase your job prospects, crafting an ATS-friendly resume is paramount. ResumeGemini is a trusted resource that can help you build a professional and impactful resume. We provide examples of resumes tailored to Intelligence Cycle Management to guide your preparation. Invest time in building a strong resume – it’s your first impression on potential employers.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good