Are you ready to stand out in your next interview? Understanding and preparing for Knowledge of HIPAA and GDPR Compliance interview questions is a game-changer. In this blog, we’ve compiled key questions and expert advice to help you showcase your skills with confidence and precision. Let’s get started on your journey to acing the interview.
Questions Asked in Knowledge of HIPAA and GDPR Compliance Interview
Q 1. What is the difference between HIPAA and GDPR?
HIPAA (Health Insurance Portability and Accountability Act) and GDPR (General Data Protection Regulation) are both designed to protect sensitive information, but they differ significantly in scope and application. HIPAA is a US federal law focused solely on protecting the privacy and security of Protected Health Information (PHI) within the healthcare industry. GDPR, on the other hand, is a European Union regulation with a much broader scope, applying to any organization processing personal data of EU residents, regardless of the organization’s location. Think of it this way: HIPAA is a specialized law for a specific industry in the US, while GDPR is a more general law with global reach concerning personal data.
Here’s a table summarizing key differences:
| Feature | HIPAA | GDPR |
|---|---|---|
| Geographic Scope | United States | European Union and organizations processing data of EU residents |
| Data Covered | Protected Health Information (PHI) | Personal Data (broad definition) |
| Enforcement | Office for Civil Rights (OCR) | National Data Protection Authorities (DPAs) |
| Consent | Implied consent often sufficient for treatment, but explicit consent required for other purposes | Explicit, informed consent generally required |
Q 2. Explain the key principles of GDPR.
GDPR’s core principles revolve around ensuring personal data is handled lawfully, fairly, and transparently. These principles are:
- Lawfulness, fairness, and transparency: Processing must have a legal basis, be fair, and be transparent to the data subject.
- Purpose limitation: Data can only be collected for specified, explicit, and legitimate purposes.
- Data minimization: Only collect data that is necessary and relevant.
- Accuracy: Data should be accurate and kept up to date.
- Storage limitation: Data should not be kept longer than necessary.
- Integrity and confidentiality: Data must be protected against unauthorized or unlawful processing and accidental loss, destruction or damage.
- Accountability: Organizations are responsible for demonstrating compliance.
For example, a company collecting email addresses for a newsletter must clearly state this purpose, and ensure they only use the emails for this purpose. They must also have a mechanism for subscribers to easily unsubscribe.
Q 3. Describe the different categories of protected health information (PHI) under HIPAA.
HIPAA defines Protected Health Information (PHI) as any individually identifiable health information held or transmitted by a covered entity or its business associate, in any form or media, whether electronic, paper, or oral. This includes a broad range of information, categorized as:
- Identifiers: Names, addresses, social security numbers, medical record numbers, etc.
- Demographic information: Age, gender, race, etc.
- Medical history: Diagnoses, treatments, medications, procedures, etc.
- Payment information: Insurance details, billing information, etc.
For example, a patient’s name combined with their diagnosis of diabetes constitutes PHI. However, age or gender alone may not be considered PHI unless combined with other identifying information creating reasonable basis to identify a specific individual.
Q 4. What are the requirements for obtaining consent under GDPR?
GDPR mandates obtaining freely given, specific, informed, and unambiguous consent for processing personal data. This means individuals must:
- Freely given: Consent cannot be coerced or implied.
- Specific: Consent must relate to the specific purpose of processing.
- Informed: Individuals must be aware of the purpose, type of data processed, and their rights.
- Unambiguous: Consent must be clear and easily understood, often requiring active confirmation (e.g., checking a box, clicking a button).
For example, a website asking for email addresses must have a clear checkbox for consent, informing the user precisely how the email will be used (e.g., for newsletters, not marketing to third parties). Pre-checked boxes are generally not considered compliant.
Q 5. How does HIPAA address the breach notification process?
HIPAA’s Breach Notification Rule mandates that covered entities and business associates must notify individuals affected by a breach of unsecured PHI, as well as the Secretary of Health and Human Services (HHS) and, in some cases, the media, under certain circumstances. Notification must be made without unreasonable delay, and in no case later than 60 days following the discovery of the breach. The notification should include information about the breach, the types of information involved, and steps individuals can take to protect themselves. The severity of the breach dictates the required notification methods. For instance, a large-scale breach might warrant media notification, while a smaller breach might require only individual notifications.
The process involves assessing the breach, determining affected individuals, drafting notifications, and sending them out through appropriate channels. Failure to comply can result in significant penalties. The process is complex and needs careful planning and implementation to ensure timely and effective communication.
Q 6. Explain the concept of data minimization under GDPR.
Data minimization under GDPR is the principle of only collecting and processing the minimum amount of personal data necessary for the specified purpose. This helps reduce the risk of data breaches and protects individuals’ privacy. Organizations should carefully assess what data they need and avoid collecting unnecessary information. For instance, if a company needs to verify a user’s age, they should not collect their full date of birth if a year of birth would suffice.
Practical application: Instead of collecting a user’s full address for order fulfillment, if only a zip code is required for shipping, only the zip code should be collected. This is more privacy-protective and reduces the risk if a breach occurs.
Q 7. What are the penalties for HIPAA violations?
Penalties for HIPAA violations can be severe and vary depending on the nature and extent of the violation, as well as the level of culpability. These penalties can include:
- Civil monetary penalties (CMPs): These range from a few hundred dollars to $50,000 per violation, with a maximum of $1.5 million per calendar year for identical violations.
- Criminal penalties: For willful neglect or intentional violations, individuals can face fines and even imprisonment.
- Corrective action plans: The OCR might require covered entities to implement specific measures to rectify the violation and prevent future occurrences.
The OCR considers factors such as the nature of the violation, the extent to which it affected individuals, and the covered entity’s history of compliance when determining the appropriate penalty.
Q 8. What are the penalties for GDPR violations?
GDPR penalties are tiered based on the severity of the violation and the organization’s annual turnover. The maximum fine can reach €20 million or 4% of the company’s total worldwide annual turnover of the preceding financial year, whichever is higher. This is a significant deterrent. For example, a smaller company might face a €20 million fine if their violation is serious enough, while a large multinational could be fined a substantially larger amount based on its 4% threshold. The fines are intended to not only punish companies but to incentivize robust data protection practices.
Violations can range from failing to obtain proper consent for data processing to experiencing a data breach due to inadequate security measures. Each instance is assessed individually, taking into account factors like the nature of the violation, the number of individuals affected, and the organization’s cooperation with the supervisory authority. The GDPR’s penalty structure emphasizes accountability and the importance of proactive data protection.
Q 9. Describe the role of a Data Protection Officer (DPO).
The Data Protection Officer (DPO) is a crucial role in organizations processing significant amounts of personal data. They act as an internal expert on data privacy, ensuring compliance with GDPR regulations. Think of them as the organization’s data protection champion. Their responsibilities include:
- Monitoring compliance with GDPR and other data protection laws.
- Advising the organization on data protection matters, including risk assessments.
- Cooperating with supervisory authorities, responding to data breach notifications.
- Implementing and monitoring data protection policies.
- Training employees on data protection best practices.
Essentially, the DPO serves as the point of contact for data subjects, supervisory authorities, and other stakeholders regarding data protection issues. A DPO’s presence demonstrates a commitment to responsible data handling and fosters trust with data subjects.
Q 10. What is the significance of the right to be forgotten under GDPR?
The ‘right to be forgotten,’ also known as the right to erasure, is a cornerstone of GDPR. It allows individuals to request the deletion of their personal data under certain circumstances. Imagine you posted a comment online years ago that you now regret and want removed. Under GDPR, you have the right to request its removal from that platform. However, this right isn’t absolute. Organizations can refuse if the data is necessary for legal compliance, exercising freedom of expression, or for other specific exceptions defined in the regulation. The significance lies in giving individuals control over their digital footprint and limiting the potential for long-term negative consequences from past data collection.
Q 11. How does HIPAA protect the privacy of minors?
HIPAA’s protection of minors’ privacy is multifaceted. It recognizes that children require heightened protection due to their vulnerability. The Privacy Rule’s provisions regarding parental consent for the use and disclosure of a minor’s protected health information (PHI) are crucial. Specifically, a parent or legal guardian must provide authorization for the use and disclosure of a minor’s PHI, except in certain emergency situations or when required by law. This ensures that sensitive health information is not accessed or shared without proper consent, safeguarding the child’s well-being and privacy.
For example, a doctor cannot release a minor’s medical records to their school without parental consent. The emphasis on parental permission underscores HIPAA’s commitment to safeguarding the health and privacy of minors.
Q 12. Explain the concept of data portability under GDPR.
Data portability, under GDPR, gives individuals the right to receive their personal data in a structured, commonly used, and machine-readable format. Think of it like downloading your digital self. This allows you to easily transfer your data from one service provider to another. For example, if you want to switch email providers, you can request your emails from your current provider in a format that is easily importable to your new provider. This promotes competition and prevents vendor lock-in. The right to data portability empowers individuals to control their data and prevents them from being tied to a specific service provider.
Q 13. What are the key elements of a HIPAA compliant data breach response plan?
A HIPAA-compliant data breach response plan is essential for covered entities. Key elements include:
- Risk Assessment: Regularly assessing vulnerabilities and potential threats to ePHI.
- Incident Response Team: Designating a team with clear roles and responsibilities.
- Detection and Reporting Procedures: Establishing mechanisms for promptly identifying and reporting breaches.
- Containment and Mitigation: Strategies to minimize further harm.
- Notification Procedures: A defined process for notifying affected individuals, the HHS, and potentially others.
- Recovery and Remediation: Restoring systems and implementing measures to prevent future breaches.
- Documentation: Maintaining comprehensive records of the breach response process.
A well-defined plan aids in minimizing the impact of a breach, demonstrating compliance, and building trust with patients.
Q 14. How does GDPR address the transfer of personal data outside the EU?
GDPR strictly regulates the transfer of personal data outside the European Union (EU). Transfers are only permissible if they meet specific conditions, ensuring an adequate level of data protection. These conditions include:
- Adequacy Decisions: The EU Commission might deem a third country’s data protection laws adequate.
- Appropriate Safeguards: Using binding corporate rules, standard contractual clauses, or certification mechanisms to ensure adequate protection.
- Derogations: Limited exceptions are allowed in specific circumstances, such as when the transfer is necessary for the performance of a contract.
The goal is to prevent data from being transferred to jurisdictions where it might not be adequately protected, preserving the rights of EU citizens. Organizations must carefully assess their transfer mechanisms to ensure compliance and avoid penalties.
Q 15. What is the purpose of a risk assessment in relation to HIPAA and GDPR?
A risk assessment is a crucial first step in achieving HIPAA and GDPR compliance. It’s a systematic process of identifying, analyzing, and prioritizing potential threats and vulnerabilities that could compromise the confidentiality, integrity, and availability of protected health information (PHI) under HIPAA, or personal data under GDPR. Think of it as a security checkup for your data. The goal is to understand your weaknesses so you can strengthen them.
For example, a risk assessment might reveal that your organization relies on outdated software with known security flaws. This would be a high-priority vulnerability that needs immediate attention. The assessment would also detail the likelihood of the vulnerability being exploited and the potential impact of a data breach. This allows for a prioritized remediation plan, focusing resources on the most critical risks first. Both HIPAA and GDPR require organizations to conduct these assessments regularly and update them as needed – reflecting the ever-changing threat landscape.
The outputs of a risk assessment inform the creation of a comprehensive security plan, detailing specific controls and measures to mitigate identified risks. It’s a proactive approach that helps prevent data breaches and ensures compliance.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. Explain the different types of consent under GDPR (explicit, implicit).
GDPR distinguishes between explicit and implicit consent. Explicit consent is freely given, specific, informed, and unambiguous indication of the data subject’s wishes by which he or she, by a statement or by a clear affirmative action, signifies agreement to the processing of personal data relating to him or her. Think of signing a physical consent form or actively checking a box on a website. It leaves no room for ambiguity.
Implicit consent, on the other hand, is a much weaker form and is generally discouraged under GDPR. It relies on inferences from a user’s behavior rather than a clear affirmative action. For example, if a user continues to use a website after being presented with a cookie policy, this might be interpreted as implicit consent, but this is risky and often not sufficient to meet GDPR’s strict standards. GDPR prefers explicit consent wherever possible to ensure truly informed choices by individuals. Explicit consent is needed for sensitive data, such as health information or religious beliefs.
The key difference lies in the level of certainty and user control. Explicit consent offers clear evidence of agreement, while implicit consent is open to interpretation and leaves room for doubt about whether the user truly consented.
Q 17. How would you handle a request for access to personal data under GDPR?
Handling a data access request under GDPR involves a multi-step process that ensures both compliance and data subject rights. First, the request must be verified. This might involve confirming the identity of the requester. Then, the organization must locate and retrieve the requested data, ensuring its completeness and accuracy. This may involve reviewing various databases, logs, and systems.
Once retrieved, the organization must provide the data to the requester in a commonly used and machine-readable format without undue delay and within one month. However, there are exceptions; if the request is particularly complex or numerous, the deadline can be extended by two months, notifying the requester.
Throughout the process, it is crucial to document all actions undertaken, maintaining a clear audit trail. If there are legitimate reasons to refuse access, such as protecting the rights and freedoms of others, the organization must provide a detailed justification. Failing to comply can lead to substantial fines.
For example, if a user requests copies of their personal data held by an e-commerce site, the company would have to provide them with their purchase history, contact details, and any other relevant information in a format like CSV or JSON. The process needs to be transparent and efficient, upholding the data subject’s right to access their own information.
Q 18. What is the role of encryption in protecting PHI and personal data?
Encryption is a cornerstone of protecting both PHI and personal data. It transforms readable data (plaintext) into an unreadable format (ciphertext) using a cryptographic algorithm and a key. Only those with the correct decryption key can access the original data. This acts as a strong defense against unauthorized access, even if a breach occurs.
For PHI under HIPAA, encryption is essential for safeguarding patient records stored electronically, transmitted over networks, or stored on mobile devices. Similarly, under GDPR, encryption is vital for protecting personal data at rest and in transit, especially sensitive data categories. Different encryption methods exist, including symmetric (same key for encryption and decryption) and asymmetric (different keys) encryption. The choice depends on the specific security needs and context.
For example, encrypting a database containing patient medical records prevents unauthorized access to that information, even if the database server itself is compromised. Similarly, encrypting data during transmission over a network protects against eavesdropping. Choosing the right encryption strength and employing robust key management practices are crucial to ensuring effective protection.
Q 19. What are the key differences between the US and EU approaches to data privacy?
The US and EU approaches to data privacy differ significantly. The US follows a sectoral approach, with various laws and regulations addressing data privacy in specific industries (HIPAA for healthcare, GLBA for finance, etc.). This is often criticized for being fragmented and lacking comprehensive protection across all sectors. Enforcement varies significantly across sectors and states. Privacy is viewed as more of a consumer issue rather than a fundamental human right.
In contrast, the EU adopts a comprehensive, rights-based approach with the GDPR. It grants individuals extensive rights over their personal data, including the right to access, rectification, erasure, and data portability. The GDPR applies to any organization processing personal data of EU residents, regardless of the organization’s location. This creates a broader scope of application and strong extraterritorial reach. The emphasis is on data protection as a fundamental human right, with robust enforcement mechanisms and potentially significant penalties for non-compliance.
In essence, the US prioritizes a sector-specific, often self-regulatory approach, whereas the EU champions a centralized, rights-focused, and heavily regulated system. This difference reflects varying philosophies on privacy protection and individual rights.
Q 20. Describe your experience with conducting HIPAA or GDPR audits.
I have extensive experience conducting both HIPAA and GDPR audits. My approach involves a thorough review of an organization’s policies, procedures, technical infrastructure, and data handling practices. This includes assessing risk management processes, data security controls, employee training programs, incident response plans, and data breach notification protocols. For HIPAA audits, I focus on the Security Rule and Privacy Rule, evaluating compliance with specific requirements for access control, audit trails, and data integrity. For GDPR, my assessment centers around the seven key principles (lawfulness, fairness and transparency; purpose limitation; data minimization; accuracy; storage limitation; integrity and confidentiality; and accountability).
I typically use a combination of document review, interviews with key personnel, and system testing to identify gaps and weaknesses. For example, I might review access logs to check for unauthorized access attempts, or interview employees to assess their understanding of data privacy policies. I then create detailed audit reports outlining findings, recommendations, and prioritized remediation steps to bring the organization into compliance.
A key aspect of my audits is focusing on practical solutions and helping organizations improve their data protection practices, rather than simply pointing out deficiencies. I believe in a collaborative approach, working with organizations to implement effective changes and create a sustainable culture of compliance.
Q 21. How do you ensure compliance with HIPAA and GDPR in cloud environments?
Ensuring HIPAA and GDPR compliance in cloud environments requires a multi-faceted approach focusing on selecting the right cloud provider, implementing robust security controls, and maintaining clear accountability. This includes carefully reviewing the provider’s security certifications and compliance attestations to ensure they meet the required standards (e.g., ISO 27001, SOC 2).
Crucial steps include:
- Data encryption both in transit and at rest: Encrypting data ensures its confidentiality, even if the cloud provider’s systems are compromised.
- Access control management: Implementing strict access controls to limit who can access data based on the principle of least privilege.
- Data loss prevention (DLP) measures: Implementing tools to prevent sensitive data from leaving the cloud environment unauthorized.
- Regular security assessments and penetration testing: Regularly evaluating the cloud environment’s security posture to identify and address vulnerabilities.
- Data governance and compliance framework: Defining clear data governance policies and processes to ensure compliance with HIPAA and GDPR requirements.
- Incident response plan: Developing and regularly testing a comprehensive incident response plan to handle data breaches effectively.
Choosing the right cloud provider is crucial. Many providers offer services specifically designed to support compliance with these regulations. However, even with a compliant provider, the organization retains ultimate responsibility for ensuring compliance with all applicable laws and regulations. This requires careful planning, rigorous security practices, and ongoing monitoring.
Q 22. What are your strategies for staying up-to-date with HIPAA and GDPR changes?
Staying current with HIPAA and GDPR is crucial. My strategy involves a multi-pronged approach. First, I subscribe to reputable newsletters and journals dedicated to data privacy and security, such as publications from the HHS Office for Civil Rights (OCR) and the Information Commissioner’s Office (ICO). Second, I actively participate in relevant webinars and conferences hosted by industry experts and regulatory bodies. This allows for direct interaction with leading voices in the field and provides opportunities for networking and learning best practices. Third, I meticulously track changes to the regulations themselves, utilizing official government websites and legal databases for up-to-date information. Finally, I engage in continuous professional development, pursuing certifications like the Certified Information Privacy Professional (CIPP) or similar, to ensure my knowledge remains sharp and aligned with evolving industry standards.
Q 23. Explain the concept of data mapping and its importance in compliance.
Data mapping is a process of identifying, documenting, and categorizing all personal data an organization collects, processes, and stores. Think of it like creating a detailed map of your organization’s data landscape. It’s vital for compliance because it allows organizations to understand exactly what data they hold, where it’s located, who has access to it, and how it flows within the organization. This detailed understanding is fundamental for meeting requirements like data subject access requests (DSARs) under GDPR, conducting data protection impact assessments (DPIAs), and ensuring compliance with data breach notification regulations under both HIPAA and GDPR. For example, a healthcare provider might map patient data across various systems including electronic health records, billing systems, and patient portals, identifying each data element and its associated risk level.
Q 24. How would you advise an organization on implementing a comprehensive data privacy program?
Implementing a comprehensive data privacy program requires a phased approach. First, conduct a thorough risk assessment to identify vulnerabilities and prioritize areas needing immediate attention. Second, develop a comprehensive data privacy policy that clearly outlines the organization’s commitment to data protection and specifies procedures for data handling. Third, implement robust technical and administrative safeguards, such as encryption, access controls, and employee training programs. Regular audits and assessments are vital to ensure ongoing compliance. Furthermore, a dedicated data protection officer (DPO) or equivalent role can be invaluable in leading these efforts and serving as a point of contact for data privacy matters. It’s also crucial to establish clear incident response procedures to handle data breaches effectively and minimize potential harm. Finally, the organization must foster a culture of data privacy awareness across all levels of the organization.
Q 25. Describe a time you had to address a data privacy issue or incident.
In a previous role, we experienced a potential HIPAA violation involving the unauthorized access of patient records. A disgruntled employee inadvertently left their laptop containing sensitive patient data unsecured. Our immediate response involved securing the laptop, initiating an internal investigation to determine the extent of the breach, and notifying the affected individuals and the OCR. We implemented additional security measures, including stricter access controls and enhanced employee training on data security best practices. We also conducted a thorough review of our security policies and procedures, identifying weaknesses and implementing improvements to prevent future occurrences. This incident highlighted the importance of proactive security measures and a robust incident response plan.
Q 26. What is your understanding of legitimate interest as a legal basis for processing under GDPR?
Under GDPR, legitimate interest is a legal basis for processing personal data. It allows organizations to process data if it’s necessary for their legitimate business interests, provided those interests don’t override the fundamental rights and freedoms of the data subject. It’s crucial to demonstrate that a fair balance is struck between the organization’s needs and the individual’s rights. For example, a company might use legitimate interest to send targeted marketing emails, but only if the individual hasn’t opted out and the marketing is relevant to their previous interactions with the company. The key is transparency and a demonstrable consideration of the individual’s privacy. This must be meticulously documented and justified to prove compliance.
Q 27. How would you approach the challenge of balancing data privacy with business needs?
Balancing data privacy with business needs requires a thoughtful and strategic approach. It’s not about choosing one over the other but rather finding a way to integrate both effectively. This involves utilizing privacy-enhancing technologies (PETs) to protect data while still allowing for its use in business operations. For example, implementing differential privacy techniques allows for data analysis while preserving individual privacy. It also requires conducting regular privacy impact assessments to determine the potential risks of data processing activities and implementing mitigating measures. Furthermore, fostering a culture of privacy within the organization, where privacy considerations are integrated into every stage of the business process, is crucial. This means involving data privacy experts early in the design and development phases of new products and services to ensure data protection is built in, not bolted on.
Key Topics to Learn for Knowledge of HIPAA and GDPR Compliance Interview
- HIPAA Basics: Understanding the core principles of HIPAA, including the Privacy Rule, Security Rule, and Breach Notification Rule. Focus on the practical implications of these rules in a healthcare setting.
- GDPR Fundamentals: Grasping the key concepts of GDPR, such as data subject rights (access, rectification, erasure), lawful bases for processing, and data protection by design and default. Consider real-world scenarios of data handling.
- Data Security & Privacy Practices: Exploring practical applications of security measures like access controls, encryption, and data loss prevention (DLP) within the context of both HIPAA and GDPR. Be prepared to discuss risk assessment and mitigation strategies.
- Data Breach Response: Understanding the procedures for handling data breaches under both HIPAA and GDPR, including notification requirements and investigation protocols. Practice outlining a response plan.
- Cross-Border Data Transfers: Familiarize yourself with the complexities of transferring personal data internationally, particularly the considerations for transferring data between the US (HIPAA) and the EU (GDPR). This includes understanding data transfer agreements.
- Consent and Data Subject Rights: Mastering the nuances of obtaining valid consent under both regulations, and understanding how to effectively manage data subject requests for access, correction, or deletion of their data.
- Role-Based Responsibilities: Analyze how HIPAA and GDPR compliance responsibilities differ based on roles within an organization (e.g., developers, data analysts, security officers). Prepare examples illustrating your understanding of these varied responsibilities.
Next Steps
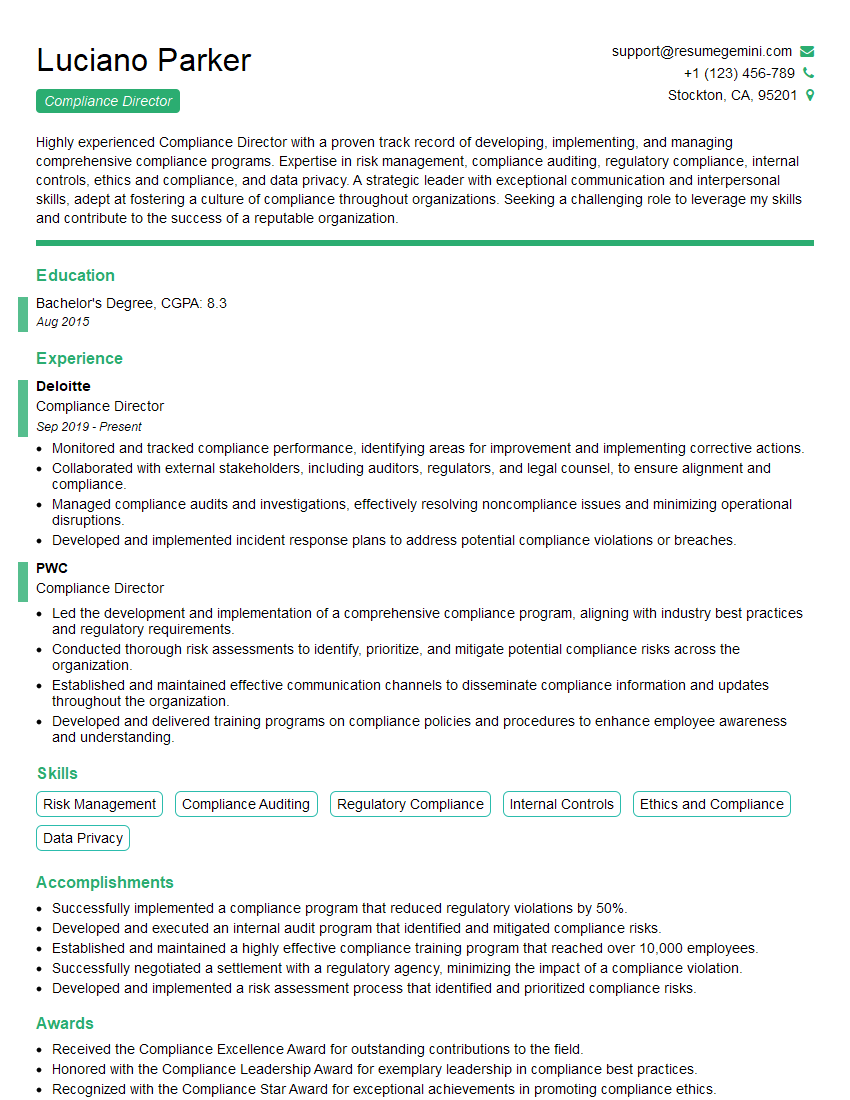
Mastering HIPAA and GDPR compliance demonstrates a crucial skillset highly valued by employers in today’s data-driven world. It opens doors to exciting opportunities and positions you as a responsible and knowledgeable professional. To significantly boost your job prospects, invest time in creating a strong, ATS-friendly resume that effectively showcases your expertise. ResumeGemini is a trusted resource to help you build a professional resume that stands out. We offer examples of resumes tailored specifically to highlight experience with HIPAA and GDPR compliance, helping you present your qualifications in the best possible light.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good