Cracking a skill-specific interview, like one for Lock Decoding, requires understanding the nuances of the role. In this blog, we present the questions you’re most likely to encounter, along with insights into how to answer them effectively. Let’s ensure you’re ready to make a strong impression.
Questions Asked in Lock Decoding Interview
Q 1. Explain the difference between a pin tumbler lock and a wafer lock.
The core difference between pin tumbler locks and wafer locks lies in their internal mechanisms. Pin tumbler locks, the most common type, utilize a series of pins that must be aligned precisely to allow the cylinder to turn. These pins are divided into two parts: key pins and driver pins. The key lifts the key pins to the correct height, allowing the driver pins to align with the cylinder’s shear line, enabling the lock to open. Wafer locks, on the other hand, use thinner, simpler wafers that are lifted by the key’s cuts to create a path for the cylinder to turn. Think of it like this: pin tumbler locks are more complex, offering better security, while wafer locks are simpler, offering less resistance to picking or manipulation.
In essence: Pin tumbler locks are more secure and complex with multiple interacting pins; wafer locks are simpler and less secure, using thin, flat wafers.
Q 2. Describe the process of picking a pin tumbler lock.
Picking a pin tumbler lock involves manipulating the pins to mimic the action of the correct key. It requires two tools: a tension wrench and a set of picks. The tension wrench applies slight torque to the cylinder, simulating the turning action of the key. The picks are used to carefully lift each pin to the shear line. This is done individually, one pin at a time. As you lift each pin to the correct height, you feel a slight ‘click’ indicating it’s set. Once all pins are set, the cylinder will turn, opening the lock. It’s a delicate process requiring patience and precision. Think of it like carefully playing a musical instrument—each note (pin) needs precise timing and pressure.
Steps:
- Apply slight tension to the cylinder with the tension wrench.
- Use the pick to carefully lift each pin to its shear line, feeling for each ‘click’.
- Once all pins are set, the cylinder will turn.
Q 3. What are the common types of lock bypass techniques?
Lock bypass techniques go beyond picking and often involve exploiting weaknesses in the lock’s design or installation. Some common methods include:
- Picking: As discussed earlier, this involves manipulating the internal mechanism to open the lock without a key.
- Raking: A faster, less precise technique than picking, where the pick is moved back and forth to quickly lift all pins simultaneously.
- Bumping: Using a specially made bump key to strike the lock, jarring the pins into place.
- Drilling: Directly drilling through the lock casing to bypass the internal mechanism. This is destructive.
- Shimming: Inserting a thin shim into the gap between the door and the frame to force the bolt back.
- Extraction: Removing the entire lock cylinder from the door. This often requires specialized tools.
Each technique has its own level of difficulty and risk, and the choice depends on the specific lock and the available tools and skills.
Q 4. How do you identify different types of locks based on their features?
Identifying lock types relies on observing key features: The keyway (the shape of the keyhole) is a primary indicator. Different manufacturers and lock types have distinct keyway designs. Look at the cylinder itself – is it a simple wafer cylinder, or does it appear more complex, hinting at a pin tumbler design? The presence of a visible keyway and/or the overall construction (size, material) can offer valuable clues. Consider the lock’s housing: is it a simple surface mount or integrated into the door itself? For instance, a small, simple cylinder with a single, straight keyway likely suggests a wafer lock, while a more robust cylinder with a complex keyway would indicate a pin tumbler or other high-security system. It’s often helpful to consult manufacturer markings or research online databases of lock designs if needed.
Q 5. Explain the principles of tension and picking in lock manipulation.
Tension and picking are inseparable in lock picking. Tension provides the necessary force to turn the cylinder, while picking manipulates the pins. The tension wrench applies gentle, consistent pressure to the plug (the rotating part of the cylinder). This pressure is crucial; too much tension will bind the pins, too little, and the pins will not properly align. The pick then interacts with the pins, lifting them one by one until they reach the shear line. The delicate balance between these two actions is what determines success. Imagine it like a tightrope walker—tension is the rope, and the picks are the walker’s careful steps.
Q 6. What tools are essential for lock decoding and what are their specific functions?
Essential tools for lock decoding vary depending on the lock type and technique used. However, some common tools include:
- Tension Wrenches: Apply controlled torque to the cylinder.
- Picks: Various shapes and sizes designed to lift individual pins.
- Rakes: Used for a faster, but less precise, picking method.
- Bump Keys: Used in bump keying, this requires specially made keys.
- Lock Picks Sets: Collections of various tension wrenches and picks.
- Drill Bits (for destructive entry): This would only be used in extreme situations and with appropriate authority.
- Extraction Tools: To remove the cylinder from the door. This requires specialized tools.
The specific function of each tool is to aid in manipulating the lock mechanism to open it without the original key.
Q 7. How do you handle a lock that’s jammed or damaged?
Handling a jammed or damaged lock requires careful assessment and appropriate action. First, try to identify the cause of the jam – is it due to debris, a broken component, or forced entry? For minor jams, lubricating the mechanism with graphite powder can sometimes help. If the lock is severely damaged, attempting to pick or bypass it might cause further harm. In such cases, professional assistance from a locksmith is recommended. Attempting to force a damaged lock open can cause further damage, potentially leading to increased repair costs or the need for a complete lock replacement. Always prioritize safety and professional help when dealing with potentially hazardous or irreparable damage.
Q 8. Describe your experience with different lock mechanisms (e.g., disc detainer, lever lock).
My experience encompasses a wide range of lock mechanisms, from the simpler lever locks to the more complex disc detainer systems. Lever locks operate using a series of levers that must be aligned precisely with the bitting of the key. Think of it like a combination puzzle where each lever represents a digit; only the correct sequence unlocks the mechanism. I’ve worked extensively with various lever lock designs, understanding their internal components and how to manipulate them effectively. Disc detainer locks, on the other hand, use rotating discs with cuts that need to be aligned. These are prevalent in many automotive applications and require a different set of techniques for decoding.
I’ve also worked with pin tumbler locks, which are the most common type found in residential and commercial settings. These locks utilize pins that need to be lifted to a specific height by the key’s bitting. My expertise extends to identifying the various types of pins, understanding their tolerances, and manipulating them during decoding. Beyond these, I have familiarity with wafer locks, tubular locks and even specialized high-security locks, each presenting unique challenges and requiring specific knowledge.
- Lever Locks: High degree of manipulation required, often involves understanding the specific lever positions and their interactions.
- Disc Detainer Locks: Requires precision and understanding of the disc rotations and their alignment.
- Pin Tumbler Locks: Most common type, involves understanding pin heights and manipulating them with tension and picking tools.
Q 9. How do you maintain the confidentiality and security of information related to lock decoding?
Maintaining confidentiality and security is paramount in this field. I adhere to strict professional ethics and legal frameworks. All client information, including lock details, locations, and methods used, is treated as strictly confidential and is never discussed outside of secure channels. I utilize encrypted communication methods and secure data storage solutions to protect sensitive information. Any records are kept only for a limited period as required by law and then securely destroyed.
Furthermore, I avoid public discussions or demonstrations of techniques that could compromise security. My work is always conducted with the utmost discretion and respect for client privacy. The ethical implications of my work are consistently at the forefront of my mind.
Q 10. What are the ethical considerations associated with lock decoding?
The ethical considerations surrounding lock decoding are significant. While my skills are valuable for legitimate purposes like locksmithing, security consulting, and law enforcement, they can also be misused. It’s crucial to use these skills responsibly and only for ethical and legal purposes. I strictly refuse any requests that involve illegal activities, such as unauthorized entry into premises or the theft of property. It is my personal and professional code to act with integrity and adhere to all applicable laws and regulations. Ethical considerations guide every decision I make.
Prioritizing ethical behavior ensures the responsible use of my expertise. It’s about protecting individuals, businesses, and communities from harm while contributing to a more secure environment.
Q 11. How do you prioritize tasks and manage time effectively when working on multiple lock decoding projects?
Managing multiple lock decoding projects efficiently requires a structured approach. I use a project management system that allows me to prioritize tasks based on urgency, complexity, and client deadlines. This system allows me to track progress, manage resources, and allocate time effectively. I break down complex projects into smaller, manageable tasks, making progress more easily measurable and allowing for better time management. I regularly review my schedule and adjust priorities as needed to ensure all deadlines are met.
For example, a high-priority project with a tight deadline would naturally take precedence over a less urgent task. I also communicate proactively with clients to manage expectations and prevent delays. Effective time management is crucial to avoid burnout and to maintain a high level of quality in my work.
Q 12. What are some common security vulnerabilities associated with locks and how can they be addressed?
Many security vulnerabilities exist with locks. Common issues include weak or easily guessable combinations, poorly installed locks, damaged or worn-out lock mechanisms, and easily picked lock designs. Improper use or lack of maintenance also contribute to vulnerabilities.
To address these vulnerabilities, regular inspection and maintenance of locks are crucial. This includes checking for damage, wear and tear, and ensuring proper installation. Upgrading to higher-security locks with advanced features can significantly improve security. Using strong, unique combinations and choosing locks that resist picking and other forms of manipulation are essential. Employee training on proper lock usage and security best practices is also vital. For example, regularly changing combinations or implementing key control systems significantly increases security.
Q 13. Explain your understanding of different key types (e.g., dimple keys, flat keys).
My understanding of key types includes a detailed knowledge of their design and how they interact with their corresponding lock mechanisms. Flat keys are the simplest type, with a series of cuts determining the interaction with the lock’s tumblers. Dimple keys, on the other hand, feature indentations or dimples that engage with a more complex pin configuration within the lock. This design usually offers a higher level of security against picking.
Beyond these, I’m familiar with various other key types, including tubular keys, which are often used in vending machines and other commercial applications, and laser-cut keys, known for their intricate cuts and higher security. Each key type presents different challenges and opportunities during decoding, requiring specialized knowledge and tools.
Q 14. Describe your experience with electronic locks and access control systems.
My experience with electronic locks and access control systems extends to understanding their operational principles, vulnerabilities, and decoding techniques. Electronic locks utilize electronic components, such as microprocessors and sensors, to control access. These locks often include features such as keypads, biometric readers, or proximity card readers. I have experience analyzing the vulnerabilities of various electronic access control systems, understanding how to bypass them while respecting the ethical and legal boundaries of my work.
I understand the different communication protocols used in electronic locks, as well as the underlying hardware and software configurations. This expertise allows me to assess their security level and identify potential weaknesses. I also have hands-on experience working with various types of access control systems, including those based on keypads, biometric readers, and proximity cards. This helps me understand the overall system design and how individual components interact.
Q 15. How do you troubleshoot and resolve problems with electronic locks?
Troubleshooting electronic locks involves a systematic approach. First, I’d assess the problem: Is the lock unresponsive, displaying an error code, or malfunctioning in a specific way? I’d then check the power source – are batteries low or is there a power outage affecting the electronic system? Next, I examine the lock’s internal components, looking for loose wires, damaged circuit boards, or other physical issues. I might use a multimeter to test voltage and continuity. If the problem lies within the software, I’d attempt a system reset or firmware update, following the manufacturer’s instructions. For complex issues, diagnostic tools specific to the lock’s brand and model are often necessary. Think of it like troubleshooting a computer – you need to identify the specific component failing and then address it accordingly.
For example, a common issue is a keypad malfunction. I would first visually inspect the keypad for any signs of damage or debris. If the keypad seems fine, I might test the connection between the keypad and the electronic control board using a multimeter. If there’s a break in the circuit, I would repair or replace the faulty component. In other cases, an improperly configured access code or a jammed mechanism could be the source of the problem.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. What are some common methods for non-destructive entry?
Non-destructive entry techniques prioritize preserving the integrity of the lock and the surrounding property. Methods vary based on the lock type. For pin tumbler locks, tools like tension wrenches and picks are used to manipulate the pins into the correct position, allowing the lock to open without damage. For lever locks, a similar approach is used but the tools and techniques differ slightly. Specialized tools may be needed for more complex mechanisms. In some cases, knowledge of the lock’s internal workings (e.g., understanding shear lines and binding) are crucial to successful opening.
For example, impressioning involves carefully creating a key from the existing keyway, using a specialized tool to determine the depth of each cut. This is a silent method that can be quite effective, but requires high levels of skill and practice. Another example would be using a bump key, a specifically modified key that is used to manipulate the pins in the lock, but this method can be more forceful and increase the chance of damage.
Q 17. What safety precautions do you take while performing lock decoding?
Safety is paramount during lock decoding. I always start by assessing the situation. If I’m entering a secured area, I’ll ensure I have proper authorization and that I am aware of any potential hazards. I wear appropriate personal protective equipment (PPE), including gloves to avoid leaving fingerprints and eye protection to guard against accidental injuries from tools or broken parts. I carefully handle tools to prevent damage to the lock or surroundings. I also maintain detailed records and photographic evidence of my work, documenting every step. This is critical for both legal reasons and for reconstructing the process if needed later. Every situation needs specific consideration, and safety protocols should be adapted accordingly.
Q 18. How do you handle situations involving complex or unusual lock mechanisms?
Complex or unusual lock mechanisms require a combination of knowledge, skill, and often, specialized tools. I start by thoroughly examining the lock’s construction and identifying its unique features. This might involve using magnification to scrutinize individual components. I consult technical resources, including manufacturer specifications, lockpicking forums, and specialized publications to gain insight into the mechanism’s operation. I might need to employ advanced techniques, such as using specialized tools or adapting existing tools to suit the specific lock’s design. It’s a process of methodical investigation, combining observation with practical experience.
For example, encountering a high-security lock with complex internal components would necessitate a more meticulous approach, potentially involving the use of advanced tools and techniques, perhaps even requiring the consultation of other experts in the field.
Q 19. Describe a challenging lock decoding experience and how you overcame it.
One particularly challenging experience involved a high-security Medeco Biaxial lock. These locks have a complex pin arrangement that made traditional lock picking methods extremely difficult. The unique keyway and the double-sided arrangement of the pins created a significant hurdle. I spent several hours meticulously analyzing the lock’s internal mechanism, using various tools and techniques. The key was understanding the interaction between the two sets of pins and how they engage differently depending on the key’s orientation. I eventually succeeded using a combination of careful manipulation and a specially adapted pick, focusing on one set of pins at a time before addressing the other. This experience reinforced the importance of patience, persistence, and a thorough understanding of the lock’s inner workings.
Q 20. How do you stay updated with the latest advancements in lock technology?
Staying updated in the field of lock technology is crucial. I regularly attend industry conferences and workshops, subscribe to relevant professional journals and publications, and actively engage with online communities and forums dedicated to locksmithing and security. I also keep up to date on new lock designs and security measures through manufacturer websites and technical documents. This ongoing professional development is crucial to ensure I have the knowledge and skills to effectively address increasingly sophisticated security challenges. Staying informed also allows me to anticipate emerging trends and technologies.
Q 21. What is your experience with forensic lock analysis?
My experience with forensic lock analysis involves examining locks to determine how they were opened, whether by legitimate means or through forced entry. This often involves analyzing marks and damage left on the lock, identifying the type of tools used, and determining the sequence of events leading to the opening of the lock. The process includes detailed documentation, photography, and often requires the use of specialized equipment, such as microscopes to analyze tool marks. This level of analysis is crucial in investigations to determine the intent and method of entry, and my expertise is based on practical training and experience in handling various lock types and potential forms of manipulation.
Q 22. Explain your understanding of relevant security regulations and standards.
My understanding of security regulations and standards regarding lock decoding is multifaceted and crucial to my work. It goes beyond simply knowing how to open a lock; it’s about ethical considerations, legal ramifications, and client confidentiality. I’m familiar with laws concerning access to property and data, which are paramount when dealing with locks securing sensitive information or valuable assets. For instance, I am well-versed in regulations surrounding the use of lock picking tools and the potential consequences of unauthorized entry. Furthermore, I adhere to strict professional codes of conduct, which often include confidentiality agreements ensuring client information remains protected. I’m also aware of industry best practices for safeguarding digital access systems, such as password management and encryption protocols. These regulations and standards are not just guidelines; they are the bedrock of ethical and responsible practice in the field of lock decoding.
Q 23. How do you document your work accurately and thoroughly?
Accurate and thorough documentation is fundamental to my work. I use a systematic approach, starting with a detailed description of the lock itself – its type, manufacturer, any visible damage, and unique identifying features. I meticulously document the steps involved in the decoding process, including the tools used, any attempts that were unsuccessful, and the precise techniques that ultimately proved effective. This is often accompanied by high-quality photographic or video evidence. For example, when working on a complex high-security lock, I might create a step-by-step visual guide showing the manipulations required to bypass the mechanisms. This documentation serves several crucial purposes: it allows for repeatability if necessary, assists in future troubleshooting, offers legal protection in case of disputes, and provides valuable training material for colleagues. All documentation is stored securely, following established client confidentiality protocols.
Q 24. What is your approach to identifying and mitigating security risks related to locks?
Identifying and mitigating security risks related to locks involves a thorough assessment of the entire system, not just the lock itself. I begin by evaluating the physical security of the environment – access points, potential vulnerabilities, and the overall level of protection. For example, a seemingly secure lock might be compromised by a weak door frame or easily accessible window. I also assess the type of lock, looking for known vulnerabilities or weaknesses. Older lock mechanisms are inherently more susceptible to certain picking techniques than newer, more advanced ones. Once potential vulnerabilities are identified, I propose mitigation strategies. These could involve upgrading to more secure locks, improving the overall physical security, implementing access control systems, or providing comprehensive lock maintenance and training to clients on security best practices. A risk mitigation plan might include recommendations for regular security audits and staff training on proper lock usage and security awareness.
Q 25. Describe your experience working independently and as part of a team.
I’m comfortable working both independently and collaboratively. When working independently, I thrive on the autonomy and focus it provides. My organizational skills and meticulous nature allow me to manage projects effectively without supervision. For instance, I’ve successfully completed numerous solo assignments involving complex lock decoding and security assessments. However, teamwork is equally important. I’ve been part of several successful teams, where my expertise in lock decoding has been valuable. In team environments, I actively participate in brainstorming sessions, contribute to problem-solving, and readily share my knowledge and skills to benefit the group. A recent project involving a large-scale security overhaul demonstrated the strength of collaborative efforts; by combining our individual strengths, we developed a more comprehensive and robust solution than would have been possible individually.
Q 26. How do you handle stressful situations and tight deadlines?
Handling stressful situations and tight deadlines is part and parcel of this profession. My approach is methodical and organized. First, I prioritize tasks based on urgency and importance. I focus on breaking down complex problems into smaller, manageable steps. For instance, facing a tight deadline on a critical security breach requires immediate action. My strategy focuses on identifying the most critical vulnerabilities first, addressing those swiftly, while planning a more thorough assessment for later. Clear communication with the team and client is also crucial. Keeping everyone informed of progress and any challenges proactively prevents misunderstandings and reduces overall stress. Time management techniques, such as utilizing project management software and prioritizing tasks, are crucial to staying on track under pressure. I’ve successfully navigated numerous high-pressure scenarios using this systematic approach, delivering results effectively and efficiently, even under extreme time constraints.
Q 27. What are your salary expectations?
My salary expectations are commensurate with my experience, skills, and the demands of the role. I am confident in my abilities and my contribution to any team. Considering my extensive expertise in lock decoding, my proven ability to handle high-pressure situations, and my commitment to ethical and responsible practices, I am seeking a competitive compensation package reflecting my value.
Key Topics to Learn for Lock Decoding Interview
- Understanding Lock Mechanisms: Explore the internal workings of various lock types (pin tumbler, wafer, disc detainer, etc.), including their strengths and vulnerabilities.
- Lock Picking Techniques: Learn about different picking methods, such as raking, single pin picking, and impressioning. Understand the tools and techniques involved in each method.
- Security Analysis and Vulnerability Assessment: Develop skills in identifying weaknesses in lock systems and suggesting improvements for enhanced security.
- Practical Application: Consider real-world scenarios like residential security, automotive security, and safe cracking. Understand how lock decoding principles apply to these contexts.
- Ethical Considerations: Discuss the ethical implications of lock decoding and the importance of responsible practices. This is crucial for demonstrating professionalism.
- Troubleshooting and Problem Solving: Develop your ability to diagnose and resolve lock-related issues, including jammed mechanisms or unusual lock behavior.
- Tool Selection and Maintenance: Learn to select appropriate tools for various lock types and understand proper tool maintenance to ensure longevity and performance.
Next Steps
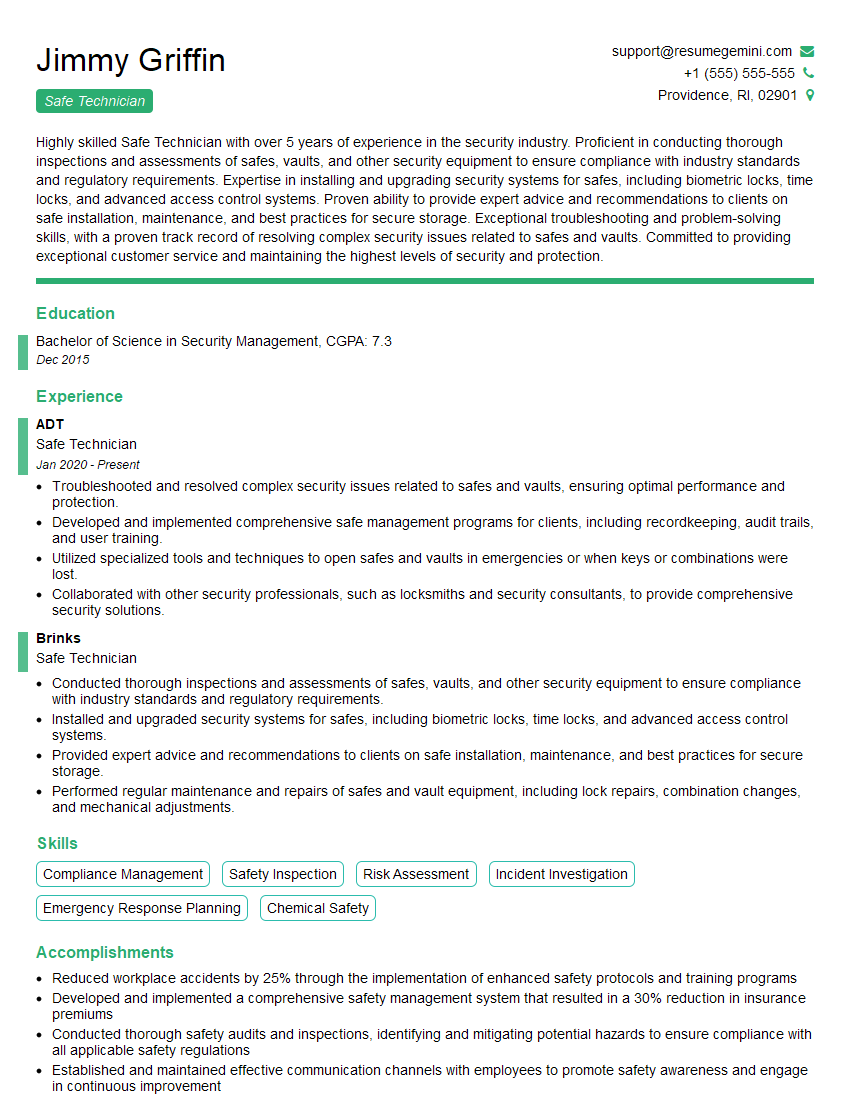
Mastering lock decoding opens doors to exciting career opportunities in security, law enforcement, and forensic science. A strong understanding of these principles demonstrates valuable problem-solving skills and technical expertise highly sought after by employers. To significantly boost your job prospects, it’s vital to create a compelling, ATS-friendly resume that effectively showcases your abilities. We highly recommend using ResumeGemini to build a professional and impactful resume tailored to the lock decoding field. Examples of resumes specifically designed for lock decoding professionals are available to help you get started.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good