The thought of an interview can be nerve-wracking, but the right preparation can make all the difference. Explore this comprehensive guide to Open Source Intelligence (OSINT) Management interview questions and gain the confidence you need to showcase your abilities and secure the role.
Questions Asked in Open Source Intelligence (OSINT) Management Interview
Q 1. Explain the difference between OSINT and HUMINT.
Open-Source Intelligence (OSINT) and Human Intelligence (HUMINT) are both crucial intelligence gathering methods, but they differ significantly in their sources and methodologies. OSINT relies exclusively on publicly available information, such as news articles, social media posts, government documents, and publicly accessible databases. Think of it like detective work using publicly available clues. HUMINT, on the other hand, involves collecting information from human sources, often through interviews, informants, or undercover operations. This is akin to interviewing witnesses or gaining intel through trusted contacts.
For example, imagine investigating a company’s potential market entry into a new region. OSINT might involve analyzing press releases, market research reports, and social media sentiment to gauge public opinion and competitor activity. HUMINT might involve interviewing industry experts or company insiders to gain confidential information.
Q 2. Describe your experience with various OSINT tools and techniques.
My OSINT toolkit is extensive and adapts to the specific investigation. I’m proficient in using tools like Maltego for link analysis, allowing me to visualize connections between individuals, organizations, and data points. I regularly utilize Shodan to discover exposed devices and services on the internet, valuable in identifying vulnerabilities or potential targets. For social media analysis, I leverage tools like TweetDeck and specialized social listening platforms for efficient data collection and filtering. I am also adept at using Google Dorking techniques, crafting specific search queries to uncover hidden or less readily available information on Google.
Beyond these, I’m comfortable using various web archives (like the Wayback Machine) to see past versions of websites, providing historical context. I also utilize open-source intelligence databases, such as those provided by governments or international organizations, to cross-reference and verify my findings. The choice of tools always depends on the specific investigative goal.
Q 3. How do you verify the credibility of information found through OSINT?
Verifying OSINT information is paramount. I employ a multi-layered approach, emphasizing triangulation and source corroboration. This means verifying information from at least three independent and credible sources. For example, finding the same fact mentioned in a reputable news outlet, a government report, and a scholarly article significantly increases confidence in its accuracy.
I also assess source bias and reputation. Is the source known for accuracy and objectivity? Are there any potential conflicts of interest? I cross-reference data with other known facts to check for consistency and internal contradictions. Reverse image searching is frequently used to identify the origin and context of images, helping to combat misinformation. Fact-checking websites and expert opinions can further strengthen the verification process.
Q 4. What are some ethical considerations when conducting OSINT investigations?
Ethical considerations are central to my OSINT practice. I strictly adhere to legal boundaries, ensuring all information gathered is publicly available and accessible. I avoid accessing private or restricted information, respecting individual privacy rights. I never engage in activities that could be construed as harassment, stalking, or doxing. Transparency is also crucial; when reporting findings, I clearly document my sources and methodology.
Moreover, I consider the potential impact of my work. For example, disseminating inaccurate or misleading information could have serious consequences. Hence, careful verification and responsible reporting are essential. Understanding and adhering to the laws and regulations of the relevant jurisdictions is a core part of my ethical framework. My guiding principle is always to act with integrity and respect for individuals’ rights and privacy.
Q 5. How do you handle large datasets of OSINT information?
Managing large OSINT datasets requires structured approaches. I employ data organization and analysis techniques, using tools like spreadsheets or dedicated data analysis software to effectively filter, sort, and visualize the information. Keyword searching, filtering by date, and using advanced search operators are crucial for refining massive datasets.
Data visualization is equally important. Transforming raw data into charts, graphs, or network maps allows for easier identification of patterns and relationships. Tools such as Gephi or even simple spreadsheet features are extremely helpful for this. Finally, regularly backing up data and employing a secure storage system prevents loss and ensures data integrity.
Q 6. Describe your experience using social media for OSINT purposes.
Social media is a treasure trove of OSINT. I use it to identify individuals, track their activities, and assess their affiliations. By analyzing profiles, posts, and connections, I can build a comprehensive picture of a person’s online persona. For instance, analyzing someone’s LinkedIn profile provides insights into their professional background and network. Their Twitter feed can reveal their opinions, interests, and even their location through geotagging.
However, social media data must be interpreted carefully. Information can be misleading, outdated, or deliberately fabricated. Always corroborate information from multiple sources. Tools like social listening platforms assist in tracking keywords, hashtags, and mentions related to a specific investigation, helping to organize and filter information across platforms. Understanding the platform’s algorithms and privacy settings is critical for effective social media OSINT.
Q 7. How do you prioritize information gathered during an OSINT investigation?
Prioritizing OSINT information is crucial for efficient investigations. I use a multi-faceted approach, prioritizing information based on its relevance, reliability, and time sensitivity. Information directly related to the investigation’s core questions receives top priority. Credibility, assessed through source verification and triangulation, is another key factor.
Time-sensitive information, such as breaking news or urgent developments, takes precedence over less immediate data. I utilize a tiered system, assigning different levels of priority based on these factors. This ensures that the most relevant and reliable information is analyzed first, allowing for a focused and efficient investigation. Regular reassessment of priorities might be needed based on the evolving nature of the investigation.
Q 8. What are some common pitfalls to avoid during OSINT investigations?
Common pitfalls in OSINT investigations often stem from a lack of planning, verification, and awareness of legal and ethical boundaries. One significant mistake is confirmation bias – seeking out only information that confirms pre-existing beliefs and ignoring contradictory evidence. This leads to skewed conclusions. Another is overreliance on a single source. A single source might be inaccurate or deliberately misleading. Always triangulate information from multiple, independent sources. Finally, neglecting to document the entire process meticulously can undermine credibility and reproducibility. This includes recording search terms, sources, and the reasoning behind each step. Think of it like a scientific experiment: your methodology must be transparent and repeatable.
- Example: Believing a social media post at face value without verifying its authenticity via other sources.
- Example: Using only one search engine or database for information gathering, thus missing crucial contextual data.
Q 9. Explain your experience with data analysis techniques used in OSINT.
My experience with OSINT data analysis involves a range of techniques, from simple keyword searches to advanced network analysis. I frequently employ data mining to extract relevant information from large datasets, often employing regular expressions (regex) to filter and refine results. For example, grep -i "keyword" file.txt would be used to find all instances of a keyword within a text file. Network analysis helps map relationships between individuals, organizations, and entities, revealing hidden connections and patterns. I use tools that allow for the visualization of these relationships, highlighting key players or clusters. Statistical analysis is also crucial in identifying trends and anomalies, such as unusual spikes in activity or communication patterns. For example, I might use Python libraries like Pandas and SciPy to perform quantitative analysis on extracted data, identifying correlations between various datasets. Finally, sentiment analysis helps understand the emotional context behind text data which adds a crucial layer of interpretation.
Q 10. How do you stay up-to-date with the constantly evolving OSINT landscape?
The OSINT landscape is dynamic, so continuous learning is paramount. I actively follow industry blogs, podcasts, and online forums dedicated to OSINT and digital forensics. Attending conferences and workshops, like those hosted by SANS Institute or OWASP, keeps me abreast of the latest tools, techniques, and emerging threats. I also regularly engage with online communities and actively participate in open-source projects, directly contributing to the evolution of OSINT methodologies. Furthermore, experimenting with new tools and techniques on controlled datasets is invaluable for staying ahead of the curve.
Q 11. Describe a time you faced a challenge during an OSINT investigation. How did you overcome it?
During an investigation involving a complex cybercrime case, I encountered a challenge when dealing with heavily obfuscated data. The perpetrators were using anonymization techniques to hide their online identities and communication trails. Initially, I struggled to trace their activities. To overcome this, I adopted a multi-pronged approach. First, I utilized advanced network analysis techniques to map the connections between various digital footprints, including IP addresses, domain names, and social media accounts. Second, I employed specialized tools for analyzing metadata embedded within digital artifacts, helping identify clues about their location and activities. Finally, I collaborated with colleagues with expertise in digital forensics to share and cross-reference information, enabling us to identify patterns and break through the obfuscation layers. This collaborative effort ultimately led to the successful identification of the perpetrators.
Q 12. What are some key legal and regulatory considerations in OSINT?
Legal and regulatory considerations are critical in OSINT. Key aspects include data privacy laws (like GDPR and CCPA), which govern the collection, processing, and storage of personal information. Copyright laws protect intellectual property, requiring proper attribution and permission when using copyrighted material. Terms of service for websites and platforms must be respected. Violation can lead to account suspension or legal repercussions. Finally, laws against computer fraud and abuse must be carefully considered to ensure compliance. It’s crucial to understand and adhere to these laws in every step of the investigation to avoid legal issues. When dealing with sensitive information, seeking legal counsel can be extremely helpful.
Q 13. How do you handle conflicting information found through OSINT?
Handling conflicting information is a routine aspect of OSINT. My approach centers around verification and triangulation. I examine the source credibility, looking for evidence of bias or manipulation. I cross-reference information with multiple, independent sources to identify patterns and inconsistencies. If discrepancies persist, I analyze the context and methodology of each source, considering factors like publication date, author expertise, and potential motivations. I document all conflicting information and my rationale for resolving it in my investigation report. A crucial element is transparently presenting conflicting information to show the thoroughness and accuracy of the investigation. This methodical approach allows me to reach informed conclusions despite the ambiguity inherent in some OSINT datasets.
Q 14. Describe your experience with mapping and visualizing OSINT data.
I’ve extensive experience with mapping and visualizing OSINT data to present findings effectively. Tools like Gephi and Maltego are frequently used to create visual representations of complex relationships within the data. Mapping can clearly illustrate connections between people, organizations, locations, and digital assets. I typically use different node shapes and sizes to represent different entities and their relative importance, while the links between nodes illustrate different types of relationships. Visualizing data is not only crucial for understanding complex relationships, but also helps to effectively communicate findings to non-technical audiences, particularly in presentations or reports. For example, a network map illustrating communication flows between suspected members of a criminal organization can clearly show their hierarchy and operational structure.
Q 15. How do you use OSINT to identify potential threats or risks?
Identifying potential threats and risks using OSINT involves systematically collecting and analyzing publicly available information to uncover vulnerabilities or malicious activities. Think of it like being a detective, but instead of relying on witnesses and crime scenes, you use readily available online data.
For example, we might monitor social media for disgruntled employees posting about company secrets or look for suspicious online activity linked to a competitor, such as unusually high traffic to a specific server or registration of domain names closely mimicking our brand. We might also analyze news articles or government reports to gauge geopolitical risks that could impact our operations. This process often involves keyword searches, network analysis, and the identification of patterns or anomalies that suggest potential threats.
- Example 1: Analyzing a competitor’s job postings might reveal their strategic focus and identify potential gaps in our own strategies.
- Example 2: Monitoring dark web forums can uncover potential data breaches or planned attacks against our organization.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. Explain the process of developing an OSINT research plan.
Developing a robust OSINT research plan is crucial for efficiency and accuracy. It’s like creating a blueprint before starting construction – it saves time and prevents costly mistakes. The process generally involves these steps:
- Define the objective: Clearly state what information you need and why. For example, ‘Identify potential cyber threats targeting our company’s infrastructure.’
- Identify relevant keywords and search terms: This is crucial for efficient searching. Think about synonyms, related concepts, and potential misspellings.
- Select appropriate data sources: Choose relevant databases, social media platforms, forums, and other resources that align with your objective. The type of data and its accessibility will help focus your choices.
- Develop a search strategy: Plan the order of your searches. Start with broad searches to get an overview, and then refine your search criteria to narrow down the results. Use Boolean operators (AND, OR, NOT) to enhance accuracy.
- Document your findings: Maintain a detailed log of your sources, search terms, and results. This is essential for traceability, reproducibility, and auditability.
- Analyze and interpret the data: Evaluate the information you’ve gathered, identify patterns, correlations, and draw conclusions.
Q 17. How do you use OSINT to support strategic decision-making?
OSINT significantly supports strategic decision-making by providing valuable insights into market trends, competitor activities, and emerging risks. It acts as a ‘situational awareness’ tool, enabling informed and proactive decisions.
For example, OSINT can be used to analyze market trends by monitoring social media conversations, online forums, and review sites to understand customer sentiment and emerging preferences. It can inform decisions on product development, marketing strategies, and resource allocation. Another application would be assessing a potential merger or acquisition by researching the target company’s operations, reputation, and potential legal issues. This intelligence can help mitigate risks and optimize the acquisition process.
Consider a scenario where a company wants to expand into a new market. OSINT can help them understand the local regulatory environment, assess the competitive landscape, and identify potential partnerships. This reduces uncertainty and increases the chances of a successful market entry.
Q 18. Describe your experience working with different types of OSINT data sources.
My experience encompasses a wide range of OSINT data sources, including:
- Social Media Platforms: Twitter, Facebook, LinkedIn, Instagram, Reddit – to analyze public profiles, posts, and interactions for sentiment analysis, identifying key influencers, and uncovering potential threats.
- Open-Source Databases: Data.gov, World Bank data, and other publicly available repositories – used to extract economic, demographic, and environmental data for market research, risk assessment, and trend analysis.
- News Articles and Blogs: Utilizing news aggregators and search engines to monitor media coverage and identify emerging trends or crises that might affect our operations.
- Government and Regulatory Websites: Accessing public records, permits, and licensing information to validate information and identify compliance issues.
- Forums and Online Communities: Monitoring discussions in relevant forums and online communities to gather insights into customer opinions, technical challenges, or emerging threats.
- Image and Video Analysis: Utilizing reverse image search and video analysis tools to identify sources, verify authenticity, and extract relevant details from visual media.
I’m proficient in using advanced search techniques and data mining tools to effectively extract and analyze information from these diverse sources.
Q 19. How do you protect your privacy and security while conducting OSINT investigations?
Protecting privacy and security during OSINT investigations is paramount. This requires a multi-layered approach:
- Using Virtual Private Networks (VPNs): Encrypting internet traffic to mask IP address and location.
- Employing Secure Browsers and Search Engines: Utilizing privacy-focused browsers and search engines to minimize tracking and data collection.
- Avoiding Personal Information Disclosure: Refraining from providing personal details on online platforms or interacting with suspicious individuals or websites.
- Adhering to Legal and Ethical Guidelines: Ensuring all activities comply with applicable laws and regulations regarding data privacy and access.
- Regularly Updating Software and Security Protocols: Keeping software and security protocols updated to protect against malware and vulnerabilities.
- Using Anonymized Accounts: Employing anonymous or pseudonymous accounts when engaging with online platforms to reduce personal exposure.
Essentially, it’s about minimizing your digital footprint and practicing good operational security to stay both safe and legal.
Q 20. How do you create effective reports based on OSINT findings?
Effective OSINT reports need to be clear, concise, and actionable. They should clearly state the objective, methodology, findings, and conclusions. The structure should follow a logical flow and utilize visual aids where appropriate.
A typical structure might include:
- Executive Summary: A brief overview of the findings and their implications.
- Methodology: A description of the data sources used, the search terms employed, and the analytical techniques applied.
- Findings: A detailed presentation of the information gathered, organized logically with supporting evidence.
- Analysis and Interpretation: An assessment of the findings, drawing conclusions, identifying patterns, and highlighting key insights.
- Recommendations: Actionable recommendations based on the findings and their implications.
- Appendices: Supporting documents, such as screenshots, links to sources, and detailed data tables.
Visual aids such as charts, graphs, and maps can significantly enhance understanding and engagement.
Q 21. What are some common techniques for identifying and extracting information from images and videos?
Extracting information from images and videos requires a multi-faceted approach. It’s often more than just ‘looking’ at the visual; it’s about employing specific techniques:
- Reverse Image Search: Using search engines like Google Images or TinEye to identify the origin and other occurrences of an image. This can help verify authenticity or find related information.
- Metadata Extraction: Examining image metadata (EXIF data) for details such as camera model, date and time of capture, GPS coordinates, and other potentially useful information. Software tools can easily extract this information.
- Facial Recognition Software: Utilizing facial recognition tools (with appropriate ethical considerations and legal compliance) to identify individuals within images or videos.
- Optical Character Recognition (OCR): Employing OCR software to extract text from images or videos. This can be valuable for identifying logos, license plates, or other text-based clues.
- Video Analysis Tools: Utilizing specialized video analysis tools to enhance quality, slow down footage, extract frames, and identify objects or anomalies within video content.
- Geospatial Analysis: Identifying locations within images or videos using landmarks, street signs, or GPS coordinates. This can help pinpoint the context and location of events.
These techniques, combined with careful observation and analytical skills, enable detailed information extraction from visual media.
Q 22. Describe your understanding of the legal framework related to data collection and use in OSINT.
The legal framework surrounding OSINT data collection and use is complex and varies significantly by jurisdiction. It’s crucial to understand that simply because information is publicly available doesn’t mean it’s free to use for any purpose. Key legal considerations include data privacy laws (like GDPR in Europe and CCPA in California), copyright laws, and laws prohibiting the dissemination of illegal or harmful content. For example, scraping personal data from social media profiles might violate privacy laws even if the profiles are publicly accessible. Similarly, using copyrighted material without permission, even if found online, is illegal. Ethical considerations are paramount, mirroring the legal ones. Responsible OSINT investigators always consider the potential impact of their actions and respect individual privacy. Before engaging in any OSINT activity, careful consideration of the applicable laws and ethical guidelines is essential. This often involves consulting legal counsel to ensure compliance and mitigate risk.
Think of it like this: finding a lost wallet on the street doesn’t give you the right to keep the money inside. Similarly, finding information online doesn’t give you carte blanche to use it however you wish. You need to respect the rules surrounding its use.
Q 23. What is the role of automation in OSINT analysis?
Automation plays a vital role in modern OSINT analysis, significantly enhancing efficiency and scale. Tools automate repetitive tasks like web scraping, data aggregation from multiple sources, and social media monitoring. This allows analysts to focus on higher-level analysis and interpretation, rather than manually sifting through vast amounts of data. For instance, a script can automate the process of searching for specific keywords across multiple search engines and social media platforms, saving countless hours of manual work. Moreover, automation facilitates real-time monitoring of data sources, enabling quicker responses to developing situations. However, it’s crucial to use automation responsibly. Over-aggressive scraping can overload websites and violate terms of service, leading to IP bans. Careful planning and ethical considerations must accompany any automation strategy.
Imagine trying to find a specific needle in a massive haystack. Manual searching would be incredibly time-consuming. Automation is like using a powerful magnet to quickly isolate the relevant pieces of hay for manual examination.
Q 24. How do you use OSINT to investigate cybercrime?
OSINT is an invaluable tool in cybercrime investigations. It can be used to identify perpetrators, uncover their methods, and gather evidence. For example, analyzing publicly available information about a suspected attacker might reveal their online aliases, forums they frequent, or even their real-world location. This information can then be used to corroborate evidence from other sources. In a ransomware attack, OSINT could be used to trace the origin of the malware, identify victims, or even find details about the attackers’ financial transactions through publicly available blockchain data. It’s important to remember that OSINT is often used as a first step, providing valuable leads for further, more intrusive investigation methods. OSINT provides context, enabling investigators to focus their efforts and resources more effectively.
Think of OSINT as the initial reconnaissance phase of a military operation – gathering information before launching a full-scale attack.
Q 25. Explain your understanding of various search engine techniques used in OSINT.
Effective OSINT relies heavily on advanced search engine techniques. Beyond simple keyword searches, advanced techniques include using Boolean operators (AND, OR, NOT) to refine results, utilizing wildcard characters (*) to find variations of keywords, and leveraging advanced search operators specific to each search engine (e.g., site: to limit results to a specific website, intitle: to search for keywords within the page title). Furthermore, using specialized search engines like Shodan (for internet-connected devices) or specialized databases adds another layer of sophistication. Understanding how different search engines index and rank results is also crucial for maximizing effectiveness. The more sophisticated the search query, the more targeted the information retrieved. This allows investigators to swiftly isolate crucial data from an immense amount of noise.
For example, searching for “malware” AND “download” site:example.com will only show results containing both keywords on the example.com domain. This targeted approach significantly improves the accuracy and efficiency of the search compared to a simple keyword search.
Q 26. Describe your experience with analyzing dark web data sources.
Analyzing dark web data sources requires specialized tools and skills, due to the encrypted nature of these networks and the often illegal activities taking place there. Accessing the dark web necessitates the use of anonymity tools such as Tor. Data analysis often involves searching hidden services, using specialized search engines like Ahmia, and understanding the various forums, marketplaces, and communication channels used by malicious actors. Identifying reliable sources and discerning credible information from disinformation is crucial. Moreover, ethical and legal considerations are paramount due to the high potential for encountering illegal content. Data analysis in the dark web must always follow strict protocols and comply with relevant laws and regulations. It is an environment that requires strong technical and analytical skills alongside a clear awareness of the potential dangers.
Analyzing dark web data is like entering a hidden city where the rules of engagement are different, and identifying reliable informants is key.
Q 27. How do you measure the success of an OSINT investigation?
Measuring the success of an OSINT investigation depends on its goals. A successful investigation might result in identifying a suspect, verifying a piece of information, or uncovering a previously unknown pattern of behavior. It’s not always about finding a ‘smoking gun’ but rather about accumulating sufficient evidence to support a hypothesis or provide valuable leads for further investigation. Metrics might include the number of credible sources identified, the accuracy of information gathered, and the effectiveness of this information in guiding further investigations. A well-documented investigation, including clear methodology, sources, and a comprehensive report, is also critical to demonstrating its success. Qualitative assessments, considering the impact and value of information obtained, are as important as quantitative measures. The outcome of the investigation should always be evaluated within the context of its objectives.
Think of it like a puzzle: success isn’t just about finding all the pieces; it’s about assembling them to create a coherent and accurate picture.
Key Topics to Learn for Open Source Intelligence (OSINT) Management Interview
- Data Acquisition and Collection Strategies: Understanding various OSINT sources (social media, forums, news sites, etc.), techniques for efficient data gathering, and legal and ethical considerations.
- Data Analysis and Interpretation: Mastering methods for analyzing large datasets, identifying patterns and anomalies, and drawing meaningful conclusions from diverse information sources. Practical application includes case studies demonstrating how to connect seemingly disparate pieces of information to build a comprehensive picture.
- Tool Selection and Utilization: Familiarity with common OSINT tools and platforms, understanding their strengths and weaknesses, and selecting the appropriate tools for specific investigative needs. This includes understanding the limitations of each tool and how to mitigate potential biases.
- Information Validation and Verification: Developing critical thinking skills to assess the credibility and reliability of OSINT data, techniques for verifying information from multiple sources, and mitigating the risk of misinformation.
- Reporting and Presentation of Findings: Effectively communicating OSINT findings through clear, concise, and visually appealing reports. This includes understanding how to tailor the presentation to different audiences.
- Risk Management and Security Best Practices: Understanding the potential risks associated with OSINT investigations, implementing security measures to protect sensitive data, and adhering to ethical guidelines.
- Legal and Ethical Frameworks: A strong understanding of the legal and ethical implications of OSINT investigations, including privacy concerns and data protection laws.
- Advanced OSINT Techniques: Explore areas like geolocation, network analysis, and social network analysis for more complex investigative scenarios.
Next Steps
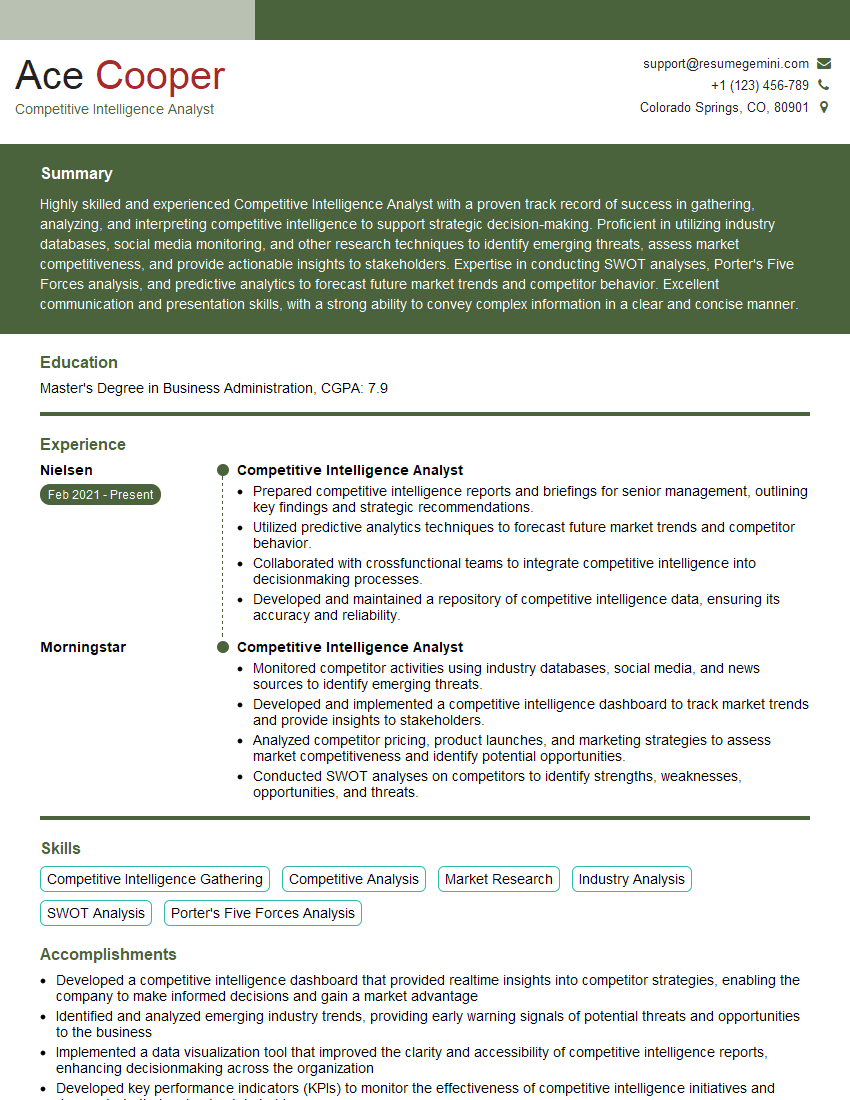
Mastering Open Source Intelligence (OSINT) Management is crucial for a successful and rewarding career in today’s data-driven world. It opens doors to exciting roles demanding critical thinking, problem-solving, and advanced analytical skills. To maximize your job prospects, crafting a compelling and ATS-friendly resume is essential. ResumeGemini can be a valuable partner in this process. It offers a user-friendly platform to create professional resumes that highlight your unique skills and experience. Take advantage of the provided examples of resumes tailored specifically to Open Source Intelligence (OSINT) Management roles to gain inspiration and structure your own document effectively. Investing time in building a strong resume is an investment in your career success.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good