Feeling uncertain about what to expect in your upcoming interview? We’ve got you covered! This blog highlights the most important Wireless Communication Standards interview questions and provides actionable advice to help you stand out as the ideal candidate. Let’s pave the way for your success.
Questions Asked in Wireless Communication Standards Interview
Q 1. Explain the differences between OFDM and OFDMA.
OFDM (Orthogonal Frequency Division Multiplexing) and OFDMA (Orthogonal Frequency Division Multiple Access) are closely related modulation techniques used in wireless communication to transmit data efficiently over a wide bandwidth. Think of it like sending many small packages (data) simultaneously on different trains (subcarriers) instead of one large package on a single train. The key difference lies in how they handle multiple users.
OFDM divides the available bandwidth into many orthogonal subcarriers, each carrying a portion of the data stream. All users share the same set of subcarriers. It’s like a highway with many lanes; each car (user) can choose any lane, but they all share the same road. OFDMA enhances OFDM by adding resource allocation features. It allows assigning different sets of subcarriers and time slots to individual users. This is like having separate highways for different groups of cars, leading to improved efficiency and fairness.
- OFDM: Single user, or all users sharing the same resource allocation.
- OFDMA: Multiple users, each with dedicated resource allocation (subcarriers and time slots).
In essence, OFDMA is a more sophisticated evolution of OFDM, especially beneficial in scenarios with multiple users demanding high data rates, like 5G cellular networks. The dynamic allocation in OFDMA enables better management of interference and improved overall network performance.
Q 2. Describe the concept of MIMO and its benefits in wireless communication.
MIMO (Multiple-Input Multiple-Output) technology uses multiple antennas at both the transmitter and receiver ends to enhance wireless communication. Imagine shouting to someone across a crowded room – it’s hard to hear clearly. MIMO is like having multiple people shouting the same message from different locations, making it easier for the receiver to understand.
The benefits are significant:
- Increased Data Rate: By sending multiple data streams simultaneously over different antennas, MIMO drastically increases the overall data transmission speed. This is spatial multiplexing.
- Improved Reliability: Multiple antennas allow for diversity reception, meaning even if one signal is weak or fades, others can compensate. This improves link reliability, reducing errors and dropouts.
- Extended Range: MIMO enhances signal strength by intelligently combining signals from multiple antennas, extending the coverage area of the wireless system.
MIMO is extensively used in modern wireless standards like Wi-Fi and 4G/5G cellular networks. It’s crucial for delivering high-speed, reliable wireless connectivity in diverse environments.
Q 3. What are the key features and improvements of 5G compared to 4G?
5G offers considerable advancements over 4G LTE, focusing on higher data rates, lower latency, and increased network capacity. Think of it as upgrading from a dial-up connection to fiber optic internet.
- Higher Data Rates: 5G leverages wider bandwidths, higher-order modulation schemes, and MIMO techniques to achieve significantly faster download and upload speeds compared to 4G. Peak data rates can be hundreds of times greater.
- Lower Latency: 5G significantly reduces latency (delay), crucial for real-time applications like autonomous vehicles and online gaming. This reduction is achieved through technologies like OFDMA and network slicing.
- Increased Network Capacity: 5G supports a substantially larger number of connected devices, accommodating the growing demand from the Internet of Things (IoT). This is partly due to denser network deployments and efficient spectrum utilization.
- Improved Reliability: 5G utilizes advanced error correction codes and diverse transmission techniques to enhance reliability and robustness even in challenging environments.
- New Frequency Bands: 5G uses higher frequency bands (millimeter wave) offering large bandwidths but with limited range. This means more cell towers, but also incredibly fast speeds within coverage.
These improvements collectively enable 5G to power new applications and services not possible with 4G, paving the way for a more connected and intelligent world.
Q 4. Explain the role of channel coding in wireless communication systems.
Channel coding plays a vital role in mitigating the effects of noise and interference in wireless communication. Imagine sending a message through a noisy room; some words might get lost or misinterpreted. Channel coding adds redundancy to the message to ensure reliable reception.
It works by adding extra bits to the original data, creating a codeword. These added bits allow the receiver to detect and correct errors introduced during transmission. Common techniques include convolutional codes, turbo codes, and low-density parity-check (LDPC) codes.
The process involves two steps:
- Encoding: Adding redundancy to the data at the transmitter.
- Decoding: Detecting and correcting errors in the received data at the receiver.
Effective channel coding ensures reliable data transmission despite impairments in the wireless channel, crucial for maintaining the integrity of information in unreliable wireless environments.
Q 5. Describe different multiple access techniques used in wireless networks (e.g., TDMA, FDMA, CDMA).
Multiple access techniques determine how multiple users share the available wireless resources. Think of it as managing traffic on a road – different methods ensure efficient and fair use.
- TDMA (Time Division Multiple Access): Users take turns accessing the channel. Each user is allocated a specific time slot. It’s like a traffic light, allowing one car to pass at a time.
- FDMA (Frequency Division Multiple Access): Users are allocated different frequency bands. It’s like having separate lanes on a highway, each for a different group of cars.
- CDMA (Code Division Multiple Access): Users are assigned unique codes, allowing them to transmit simultaneously on the same frequency. It’s like many conversations happening in a room simultaneously, but each person can filter out the other conversations to listen to their specific one.
These are fundamental techniques, and modern systems often combine them or use more sophisticated approaches like OFDMA to optimize resource allocation and improve network capacity. The choice of technique depends on factors like the application, the available bandwidth, and the number of users.
Q 6. What are the challenges in designing a reliable wireless communication system in a dense urban environment?
Designing reliable wireless communication systems in dense urban environments presents several unique challenges. Imagine trying to have a clear conversation in a bustling marketplace.
- Severe Signal Attenuation and Multipath Propagation: Tall buildings and other obstacles absorb and reflect signals, leading to signal attenuation and multipath fading. Signals arrive at the receiver at different times and with different strengths.
- High Levels of Interference: Dense urban areas are crammed with numerous wireless devices operating in close proximity, causing significant interference. It’s like many conversations happening at once.
- Rapid Channel Variations: The wireless channel conditions can change rapidly as users move around, leading to unpredictable signal quality. It’s like navigating a changing and crowded environment.
- High User Density: The sheer number of users demands high network capacity and efficient resource allocation to avoid congestion.
Addressing these challenges requires sophisticated techniques like MIMO, beamforming, adaptive modulation and coding, and careful frequency planning to ensure reliable and high-quality wireless connectivity.
Q 7. Explain the concept of beamforming and its applications in 5G.
Beamforming is a signal processing technique used to focus the transmitted signal in a specific direction. Instead of broadcasting a signal in all directions, like a lightbulb, beamforming is like using a flashlight to target a specific recipient. This improves signal strength and reduces interference.
In 5G, beamforming is crucial for:
- Improving spectral efficiency: By directing the signal towards the intended receiver, beamforming minimizes interference and improves overall network capacity.
- Increasing data rates: The focused signal results in higher signal-to-noise ratio, enabling higher data rates.
- Extending coverage: Beamforming helps reach users who would otherwise be in areas with weak signals.
- Enabling massive MIMO: Beamforming is essential for efficiently managing the large number of antennas used in massive MIMO systems.
Beamforming is implemented using phased antenna arrays and sophisticated signal processing algorithms to adjust the phase of signals transmitted from each antenna element. It’s a core technology in 5G, enabling the high data rates and improved performance needed for next-generation wireless applications.
Q 8. How does carrier aggregation work in LTE and 5G?
Carrier aggregation, a crucial feature in both LTE and 5G, allows a device to combine multiple frequency bands (bandwidths) to achieve higher data rates. Imagine downloading a file – using carrier aggregation is like using multiple download pipelines simultaneously to finish faster. In LTE, this is called Carrier Aggregation (CA), while in 5G, it’s often referred to as Frequency Aggregation (FA), though the underlying principle remains the same. The combined bandwidth is significantly greater than any single component carrier, boosting speeds and capacity.
How it works: The base station (eNodeB in LTE, gNodeB in 5G) and the user equipment (UE) negotiate which component carriers are available and suitable for aggregation. The UE then receives data from these carriers concurrently. This requires sophisticated synchronization and resource management within both the network and the device itself. Factors like signal strength, interference, and available spectrum influence which carriers are selected.
LTE Example: An LTE device might aggregate a 20 MHz carrier in the 1800 MHz band with a 10 MHz carrier in the 2600 MHz band, resulting in a 30 MHz total bandwidth.
5G Example: A 5G device might aggregate multiple carriers within the same frequency band (intra-band aggregation) or across different bands (inter-band aggregation), potentially leveraging mmWave spectrum for high-speed links along with lower-frequency bands for wider coverage.
Challenges: Implementing carrier aggregation effectively poses challenges such as increased complexity in radio resource management, synchronization between carriers, and efficient power management in the UE.
Q 9. Describe the different layers of the OSI model and their relevance in wireless communication.
The OSI model is a conceptual framework that divides network communication into seven distinct layers. Each layer performs specific functions, allowing for modularity and standardization. In wireless communication, this model is crucial for understanding the flow of data from a source device to a destination device.
- Physical Layer (Layer 1): Deals with the physical transmission of bits over a communication channel. This includes signal encoding, modulation, and physical interface specifications. Think of this as the actual wires or radio waves carrying the data.
- Data Link Layer (Layer 2): Provides error-free transmission of data frames between two directly connected nodes. Examples include MAC addressing (Media Access Control) and error detection/correction protocols. In wireless, technologies like Wi-Fi use this layer extensively for managing access to the wireless medium.
- Network Layer (Layer 3): Handles logical addressing and routing of data packets across networks. IP addressing (Internet Protocol) falls under this layer. This is essential for routing data between different wireless access points and across the wider internet.
- Transport Layer (Layer 4): Provides reliable end-to-end data transfer. TCP (Transmission Control Protocol) and UDP (User Datagram Protocol) are key protocols operating at this layer. TCP guarantees delivery, while UDP prioritizes speed over reliability.
- Session Layer (Layer 5): Manages sessions between applications, handling synchronization and checkpoints. Less critical in many wireless applications.
- Presentation Layer (Layer 6): Handles data formatting, encryption, and compression. Handles data representation ensuring applications can understand the data.
- Application Layer (Layer 7): Contains the applications that users interact with. Examples include HTTP (web browsing), SMTP (email), and FTP (file transfer).
Relevance in Wireless: Each layer plays a vital role in wireless communication. For example, the physical layer deals with radio frequency transmissions, while the data link layer handles access to the wireless channel and error correction. The network layer is critical for routing packets across different wireless cells. Understanding these layers allows for efficient troubleshooting and network optimization.
Q 10. What are the key performance indicators (KPIs) for evaluating a wireless network?
Key Performance Indicators (KPIs) for a wireless network are metrics used to evaluate its effectiveness and quality. These KPIs can be categorized into several groups:
- Coverage: Measures the geographical area where the network provides acceptable signal strength. This is often expressed as percentage coverage or signal strength maps.
- Capacity: Represents the maximum number of users the network can support while maintaining a satisfactory Quality of Service (QoS). This is measured in bits per second per Hz per user or similar metrics.
- Data Rate: Measures the speed at which data is transmitted over the network. Typically expressed in Mbps (Megabits per second) or Gbps (Gigabits per second).
- Latency: Measures the delay experienced between the transmission and reception of data. Low latency is crucial for real-time applications such as video conferencing and online gaming.
- Reliability: Reflects the consistency and stability of the network connection, often measured as packet loss rate or bit error rate.
- Availability: The percentage of time the network is operational and accessible to users.
- Mobility: For mobile networks, measures the effectiveness of handovers between different cells or base stations.
- Security: Measures the level of protection against unauthorized access and data breaches.
Practical Application: Network operators use these KPIs to monitor performance, identify areas needing improvement, and plan for network upgrades. For example, low data rates in a specific area might indicate a need for additional base stations or spectrum allocation.
Q 11. Explain the concept of handover and its significance in mobile networks.
Handover, also known as handoff, is the seamless transfer of a mobile device’s connection from one base station (cell tower) to another as the device moves around. Imagine you are talking on your phone and walking between different rooms. Handover ensures your call doesn’t drop.
Significance: Handover is essential for maintaining continuous connectivity in mobile networks, ensuring uninterrupted service as users move around. Without handover, calls would drop frequently and data sessions would be interrupted.
Types of Handover: There are various handover techniques, including:
- Hard Handover: The connection to the old base station is completely terminated before connecting to the new one. This may cause a brief interruption in service.
- Soft Handover: The device connects to the new base station before disconnecting from the old one, resulting in a smoother transition and uninterrupted service. This is used in many modern cellular systems.
- Intra-frequency Handover: Handover between base stations operating on the same frequency band.
- Inter-frequency Handover: Handover between base stations using different frequency bands.
Factors affecting handover: Several factors influence the efficiency of a handover, including signal strength, interference levels, network load, and the handover algorithm used by the network.
Q 12. What are the different types of wireless security protocols (e.g., WPA2, WPA3)?
Wireless security protocols are crucial for protecting data transmitted over wireless networks. Here are some key protocols:
- WPA2 (Wi-Fi Protected Access II): Was the widely adopted standard for Wi-Fi security for many years. It uses the AES (Advanced Encryption Standard) algorithm for encryption, providing strong security. However, vulnerabilities have been discovered, prompting its eventual replacement.
- WPA3 (Wi-Fi Protected Access III): The latest generation of Wi-Fi security. It offers improved security compared to WPA2, addressing vulnerabilities found in the older protocol. Key improvements include stronger encryption and simplified password management.
- WEP (Wired Equivalent Privacy): An older and less secure protocol that should no longer be used. It has significant vulnerabilities making it easy to crack.
- Other protocols: Beyond Wi-Fi, various security protocols exist for other wireless technologies like Bluetooth (e.g., Secure Simple Pairing), Zigbee (using AES encryption), and cellular networks (using various encryption techniques specific to each generation).
Choosing the right protocol: Selecting the appropriate security protocol depends on the specific wireless technology and the security requirements of the application. WPA3 is recommended for Wi-Fi networks whenever possible, ensuring the highest level of protection.
Q 13. Describe your experience with different wireless protocols (e.g., Bluetooth, Zigbee, Wi-Fi).
My experience with various wireless protocols spans several years and diverse applications. I have worked extensively with:
- Wi-Fi (IEEE 802.11): Extensive experience with various standards including 802.11a/b/g/n/ac/ax. My work involved designing, deploying and troubleshooting Wi-Fi networks in various settings, from small offices to large enterprise environments. This included optimizing network performance, addressing interference issues and securing networks using various protocols like WPA2/WPA3.
- Bluetooth (IEEE 802.15.1): I’ve worked with Bluetooth in low-power, short-range applications, including developing prototypes for sensor networks and integrating it into various IoT devices. Understanding its limitations in terms of range and bandwidth has been critical in these projects.
- Zigbee (IEEE 802.15.4): My experience with Zigbee focuses on low-power, low-data-rate applications. This is suitable for applications like home automation and sensor networks. I have expertise in mesh networking, an essential feature of Zigbee, which enhances coverage and robustness.
Cross-protocol Integration: A significant part of my work has involved integrating various wireless protocols. For instance, I have worked on projects involving using Zigbee sensors to collect data and then sending that data over a Wi-Fi network to a central server. This requires a deep understanding of each technology’s strengths and limitations, as well as the appropriate bridging techniques.
Q 14. Explain the principles of frequency planning and spectrum allocation.
Frequency planning and spectrum allocation are critical aspects of wireless communication, aiming to efficiently use the limited radio frequency spectrum. They involve deciding which frequencies will be assigned to different wireless systems to avoid interference and maximize capacity.
Principles of Frequency Planning:
- Avoidance of Interference: The primary goal is to assign frequencies to different systems in such a way that they don’t interfere with each other. This involves considering factors such as frequency reuse, adjacent channel interference, and co-channel interference.
- Efficient Spectrum Use: The goal is to use the available spectrum as efficiently as possible, maximizing the number of users and services that can be supported. Techniques such as frequency reuse and dynamic channel allocation help achieve this goal.
- Meeting Regulatory Requirements: Frequency planning must adhere to the regulatory rules and guidelines of the relevant governing bodies. This varies by country and region, specifying which frequencies can be used for various purposes.
- System Performance Optimization: The frequency plan should be designed to optimize the performance of wireless systems, considering factors such as signal propagation, path loss, and multipath fading.
Spectrum Allocation: This is the process of assigning specific frequency bands to different users or services. This is usually done by government regulatory agencies, ensuring fair and equitable access to the spectrum. Licensing and other regulatory processes govern the use of specific frequency bands.
Real-world Example: Cellular networks carefully plan their frequency usage to minimize interference between different cells and frequency bands. A specific frequency band might be reused in geographically distant cells, while avoiding adjacent channel reuse in nearby cells to prevent interference. This requires sophisticated modeling and simulation tools to predict and optimize frequency usage.
Q 15. What is the significance of path loss and fading in wireless communication?
Path loss and fading are fundamental challenges in wireless communication, significantly impacting signal strength and reliability. Path loss refers to the reduction in signal power as it travels from the transmitter to the receiver. This is primarily due to signal spreading over space and absorption by the environment. Think of it like a light bulb: the further you are, the dimmer it appears. Fading, on the other hand, is the random variation in signal strength caused by multipath propagation – the signal bouncing off multiple objects (buildings, trees, etc.) before reaching the receiver. These reflected signals can interfere constructively (boosting the signal) or destructively (weakening it), leading to rapid fluctuations in signal strength. Understanding and mitigating these effects is crucial for designing reliable wireless systems.
Example: Imagine a cell phone call in a city. Path loss will steadily decrease the signal strength as you move away from the cell tower. Additionally, buildings and other structures will cause fading, leading to moments of poor reception even at relatively close distances to the tower. Techniques like using multiple antennas (MIMO) help overcome these challenges.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. Explain different techniques used for channel estimation and equalization.
Channel estimation and equalization are crucial for compensating for the distorting effects of the wireless channel. Channel estimation involves determining the characteristics of the wireless channel, including path loss, fading, and delay spread. This information is then used to design an equalizer. Equalization is the process of compensating for the channel’s distortion to recover the original transmitted signal. Several techniques exist for both:
- Channel Estimation Techniques:
- Pilot-based estimation: Known symbols (pilots) are transmitted periodically, and the channel response is estimated based on the received pilot signals. This is commonly used in OFDM systems.
- Blind estimation: Channel characteristics are estimated without using known pilot symbols. This is more challenging but useful in scenarios where pilots are limited.
- Least Squares (LS) estimation: A simple and widely used method that minimizes the squared error between the received and expected signals.
- Equalization Techniques:
- Linear Equalization (Zero-Forcing and MMSE): Simple and computationally efficient, but may suffer from noise enhancement.
- Decision Feedback Equalization (DFE): Uses previously detected symbols to aid in the equalization of the current symbol, improving performance.
- Maximum Likelihood Sequence Estimation (MLSE): Optimal but computationally complex, offering the best performance in severe channel conditions.
The choice of technique depends on factors like complexity, computational resources, and channel characteristics.
Q 17. How do you troubleshoot common wireless network issues?
Troubleshooting wireless network issues involves a systematic approach. I typically follow these steps:
- Identify the problem: Determine the nature of the issue (slow speeds, dropped connections, limited range, etc.) and which devices or users are affected.
- Check the basics: Verify that the router is powered on, the Wi-Fi is enabled, and the correct SSID and password are used. Check for physical obstructions or interference sources (microwaves, cordless phones).
- Signal strength analysis: Use a Wi-Fi analyzer app or built-in tools to check the signal strength at different locations. Weak signals indicate path loss or interference.
- Check the router configuration: Examine the router’s settings, looking for issues like incorrect channel selection (overlapping channels), outdated firmware, or security misconfigurations.
- Examine network congestion: Many devices connected to the network can lead to congestion. Consider upgrading to a router with higher bandwidth or implementing QoS (Quality of Service) to prioritize traffic.
- Consider interference: Investigate potential sources of interference, such as other Wi-Fi networks, Bluetooth devices, or cordless phones. Try changing the Wi-Fi channel to avoid interference.
- Test the cabling and hardware: If using a wired connection, check the cables and network interface cards (NICs) for issues.
- Restart devices: A simple reboot of the router and other devices can often resolve temporary glitches.
- Advanced troubleshooting: For persistent issues, more advanced techniques like packet capture and analysis may be necessary.
Example: If users complain of slow speeds, I’d first check signal strength and network congestion. If signal strength is low, I’d investigate potential interference or relocate the router. If congestion is the problem, I might implement QoS or upgrade the router.
Q 18. What is the difference between time-division duplex (TDD) and frequency-division duplex (FDD)?
TDD (Time-Division Duplex) and FDD (Frequency-Division Duplex) are two different methods for enabling bidirectional communication in wireless systems. They differ fundamentally in how they allocate time and frequency resources for uplink (mobile to base station) and downlink (base station to mobile) transmissions:
- FDD: Uses separate frequency bands for uplink and downlink transmissions. This provides greater flexibility and capacity, particularly in scenarios with high asymmetry in uplink and downlink traffic (e.g., video streaming).
- TDD: Uses the same frequency band for both uplink and downlink transmissions, but switches between them over time. This simplifies frequency planning and offers the potential for dynamic resource allocation based on real-time traffic demands. However, careful synchronization and efficient time slot allocation are crucial.
Example: 4G LTE predominantly uses FDD, while 5G NR employs both FDD and TDD. The choice between TDD and FDD depends on factors such as spectrum availability, traffic characteristics, and system design goals.
Q 19. Explain the concept of network slicing in 5G.
Network slicing in 5G allows for the logical partitioning of a single physical network infrastructure into multiple virtual networks, each tailored to specific application requirements. Imagine a pizza: the physical network is the whole pizza, and slices are created for different needs, like one slice for high-speed video streaming, another for low-latency autonomous vehicle control, and another for massive IoT connectivity.
Each slice has its own dedicated resources (bandwidth, computational power, etc.), QoS parameters, and security policies. This enables operators to offer diverse services with different performance and reliability guarantees, catering to a wide range of applications. For example, a slice for autonomous driving requires ultra-low latency and high reliability, while a slice for massive IoT connectivity needs to support a large number of devices with minimal bandwidth per device.
Benefits: Improved resource utilization, increased efficiency, enhanced service quality, and support for diverse applications.
Q 20. Describe your experience with different wireless testing equipment and procedures.
Throughout my career, I’ve extensively utilized various wireless testing equipment and procedures. My experience encompasses:
- Signal analyzers: Used for measuring signal strength, spectrum occupancy, and signal quality. I’m proficient with instruments from Keysight, Rohde & Schwarz, and Anritsu.
- Channel emulators: These tools simulate real-world wireless channel conditions, allowing for testing of equipment under various scenarios. I’ve worked with channel emulators from Spirent and Anritsu.
- Network protocol analyzers (e.g., Wireshark): Used for capturing and analyzing network traffic to identify performance bottlenecks or errors.
- Drive testing: Conducting drive tests using specialized software and GPS devices to assess network coverage and performance in real-world environments. I am experienced in using tools like Nemo Outdoor.
- Over-the-air (OTA) testing chambers: For controlled testing of device performance in a shielded environment, minimizing external interference.
My testing procedures adhere to industry standards and best practices, ensuring accurate and repeatable results. I’m comfortable developing test plans, executing tests, analyzing results, and reporting findings. I’ve worked with both standardized and custom test procedures to suit specific project needs.
Q 21. How do you handle interference in wireless networks?
Interference in wireless networks significantly degrades performance and can lead to dropped connections and slow speeds. Managing interference requires a multi-faceted approach:
- Site surveys: Conducting site surveys to identify potential sources of interference and assess the current RF environment.
- Channel selection: Choosing appropriate Wi-Fi channels to minimize overlap with neighboring networks. Tools like Wi-Fi analyzers help identify less congested channels.
- Antenna placement and design: Optimizing antenna placement and design to improve signal quality and reduce interference. Directional antennas can help focus the signal and reduce interference from specific directions.
- Power control: Adjusting the transmit power of access points to optimize coverage and minimize interference.
- Filtering and shielding: Using filters to block unwanted frequencies and shielding to reduce electromagnetic interference from external sources.
- Co-channel interference mitigation techniques: Employing techniques like frequency hopping or spread spectrum to reduce the impact of co-channel interference.
- Adaptive modulation and coding: Adjusting the modulation scheme and coding rate based on channel conditions to improve robustness against interference.
Example: In a dense urban environment, many Wi-Fi networks might operate on the same channel, causing significant interference. By carefully selecting less congested channels and optimizing antenna placement, we can significantly improve network performance and reduce interference.
Q 22. What is your experience with wireless network simulations and modeling?
My experience with wireless network simulations and modeling is extensive. I’ve worked extensively with tools like NS-3, MATLAB, and OPNET Modeler to design, analyze, and optimize various wireless systems. For instance, I used NS-3 to model a 5G network, simulating different channel models and evaluating the performance of various resource allocation algorithms. This involved creating detailed network topologies, configuring different protocols, and running simulations to analyze key performance indicators (KPIs) like throughput, latency, and packet loss. In another project using MATLAB, I developed a ray-tracing model to predict signal propagation in urban environments, crucial for optimizing base station placement and antenna design. This required a deep understanding of signal propagation principles and the ability to translate theoretical models into practical simulations. The results from these simulations directly informed design decisions, leading to improved network efficiency and performance.
Q 23. Explain the concept of cognitive radio and its potential applications.
Cognitive radio is a paradigm shift in wireless communication where a secondary user (SU) dynamically accesses the spectrum allocated to a primary user (PU) without causing harmful interference. Think of it like a smart radio that ‘listens’ to the spectrum and opportunistically utilizes available frequencies. This is particularly important because the fixed allocation of spectrum often leads to underutilization. Cognitive radio employs spectrum sensing to detect unused channels, spectrum sharing techniques to coexist with PUs, and power control to manage interference levels. Potential applications include improving spectrum efficiency in crowded bands like Wi-Fi and cellular networks, enabling more efficient use of scarce spectrum resources in IoT devices, and facilitating dynamic spectrum access in emergency situations.
For example, a cognitive radio-enabled device could detect unused TV broadcast frequencies and use them for data transmission, dramatically increasing available bandwidth. The challenges lie in ensuring reliable spectrum sensing, preventing harmful interference to PUs, and developing efficient algorithms for spectrum allocation and management. This requires sophisticated signal processing and AI techniques to manage the complex interactions within the radio environment.
Q 24. Describe the differences between different wireless modulation schemes.
Different wireless modulation schemes determine how digital information is encoded onto a radio carrier wave. The choice of modulation impacts the bandwidth efficiency, power efficiency, and resistance to noise and interference. Let’s compare a few common schemes:
- Amplitude Shift Keying (ASK): Information is encoded by changing the amplitude of the carrier wave. It’s simple but susceptible to noise.
- Frequency Shift Keying (FSK): Information is encoded by shifting the frequency of the carrier wave. It’s more robust than ASK but less bandwidth efficient.
- Phase Shift Keying (PSK): Information is encoded by changing the phase of the carrier wave. Quadrature Phase Shift Keying (QPSK) and higher-order PSK schemes offer improved spectral efficiency.
- Quadrature Amplitude Modulation (QAM): Combines both amplitude and phase modulation, offering high spectral efficiency at the cost of increased complexity and susceptibility to noise.
For instance, Wi-Fi often uses orthogonal frequency-division multiplexing (OFDM) which combines multiple QAM signals, improving robustness and data rates. Choosing the right modulation scheme requires a trade-off between these factors based on the specific application and channel conditions.
Q 25. Explain the role of error correction codes in ensuring reliable data transmission.
Error correction codes (ECCs) are crucial for reliable data transmission over noisy wireless channels. They add redundancy to the data stream, allowing the receiver to detect and correct errors introduced during transmission. These codes work by introducing extra bits based on mathematical algorithms that contain information about the original data. When errors occur, the receiver uses these extra bits to identify and fix the corrupted data. Different ECCs offer varying levels of error correction capability and redundancy overhead. Common examples include:
- Hamming codes: Simple and efficient for correcting single-bit errors.
- Reed-Solomon codes: Powerful codes capable of correcting multiple-bit errors and burst errors, commonly used in CDs and DVDs.
- Turbo codes and Low-Density Parity-Check (LDPC) codes: Advanced codes achieving near-Shannon limit performance, used in modern communication systems like 5G.
For example, in a satellite communication system, where signal degradation is significant, powerful ECCs like LDPC codes are essential to ensure data integrity. Without them, the high error rates would make communication impossible.
Q 26. What is your understanding of the future trends in wireless communication technologies?
The future of wireless communication is marked by several exciting trends. We’re seeing a rapid shift towards higher frequencies (mmWave and beyond), enabling significantly increased data rates. This requires new antenna designs, advanced signal processing techniques, and overcoming propagation challenges at higher frequencies. The integration of artificial intelligence (AI) and machine learning (ML) will play a critical role in optimizing network performance, managing interference, and enabling self-organizing networks. The Internet of Things (IoT) is driving demand for low-power, wide-area networks (LPWANs), requiring energy-efficient communication protocols and optimized hardware. Network virtualization and software-defined networking (SDN) are revolutionizing network management and flexibility, enabling dynamic resource allocation and adaptation to changing conditions. Finally, the convergence of different wireless technologies, leading to integrated networks supporting multiple access methods and device types, is also expected. For instance, 6G promises to integrate terrestrial and satellite networks for seamless global connectivity and support a vast number of connected devices.
Q 27. Describe your experience with different wireless network topologies.
I have experience with a range of wireless network topologies. This includes:
- Infrastructure-based networks (e.g., Wi-Fi, cellular): These rely on a centralized access point (AP) or base station. I’ve worked on designing and optimizing these networks, considering factors such as AP placement, channel assignment, and interference management.
- Ad-hoc networks: These networks are formed dynamically without a central infrastructure, often seen in mobile ad-hoc networks (MANETs). I’ve worked on developing routing protocols and addressing the challenges of dynamic connectivity and limited bandwidth.
- Mesh networks: These networks utilize multiple nodes that relay data for each other, offering resilience and extended coverage. I have experience in simulating and analyzing performance in various mesh network topologies.
- Star networks: In this structure, all nodes connect to a central node, which acts as a hub. Understanding their limitations related to central point failures is key.
The selection of a suitable topology depends on factors such as coverage requirements, mobility, scalability, and security considerations. In a practical project, I chose a mesh topology for a rural area network to provide wide coverage and resilience against individual node failures.
Q 28. What are your preferred tools and technologies for wireless network design and analysis?
My preferred tools and technologies for wireless network design and analysis include:
- NS-3: A discrete-event network simulator providing detailed control and flexibility for modeling various wireless protocols and network scenarios.
- MATLAB: A powerful tool for signal processing, algorithm development, and performance analysis, invaluable for creating custom models and visualizing results.
- OPNET Modeler: A comprehensive network simulator useful for large-scale network simulations and performance evaluation.
- Wireshark: A network protocol analyzer used for capturing and analyzing network traffic, providing valuable insights into real-world network behavior.
- Python: A versatile programming language used for scripting, automation, and data processing tasks within the design and analysis process.
The choice of tools often depends on the specifics of the project, with NS-3 being preferred for detailed protocol-level simulations and MATLAB for signal processing and algorithm analysis. Combining multiple tools often leads to the most comprehensive and accurate results.
Key Topics to Learn for Wireless Communication Standards Interview
- Fundamental Concepts: Understanding the electromagnetic spectrum, signal propagation, modulation techniques (e.g., OFDM, QAM), channel coding, and error correction.
- Specific Standards: Deep dive into key standards like 4G LTE, 5G NR (including NR-NSA and NR-SA), Wi-Fi (802.11ax/be), Bluetooth (BLE, Classic), and their respective architectures, protocols, and performance characteristics. Consider exploring the evolution and differences between generations.
- Practical Applications: Analyze real-world applications of wireless communication standards in various sectors such as IoT, telecommunications, automotive, and healthcare. Be prepared to discuss use cases and associated challenges.
- Network Topologies and Protocols: Master different network architectures (e.g., cellular, ad-hoc, mesh) and related protocols (e.g., TCP/IP, UDP). Understand how these impact performance and scalability.
- Security Considerations: Familiarize yourself with security protocols and threats related to wireless communication. Discuss authentication, encryption, and data integrity measures.
- Performance Optimization: Understand techniques for optimizing throughput, latency, and power consumption in wireless systems. This includes concepts like resource allocation, interference management, and power control.
- Troubleshooting and Problem Solving: Develop your ability to diagnose and troubleshoot issues related to signal quality, connectivity, and network performance. Be prepared to discuss problem-solving methodologies.
- Emerging Trends: Stay updated on the latest advancements and future trends in wireless communication technologies, including 6G, satellite communication, and other cutting-edge developments.
Next Steps
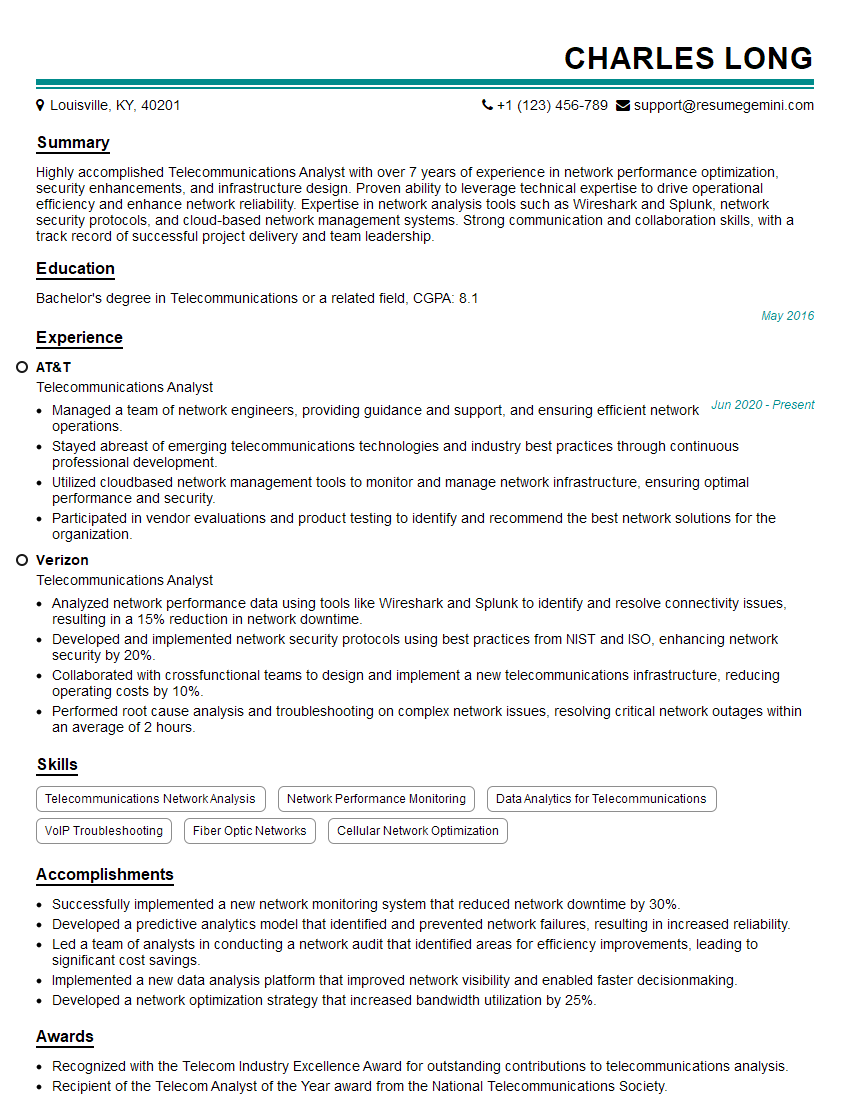
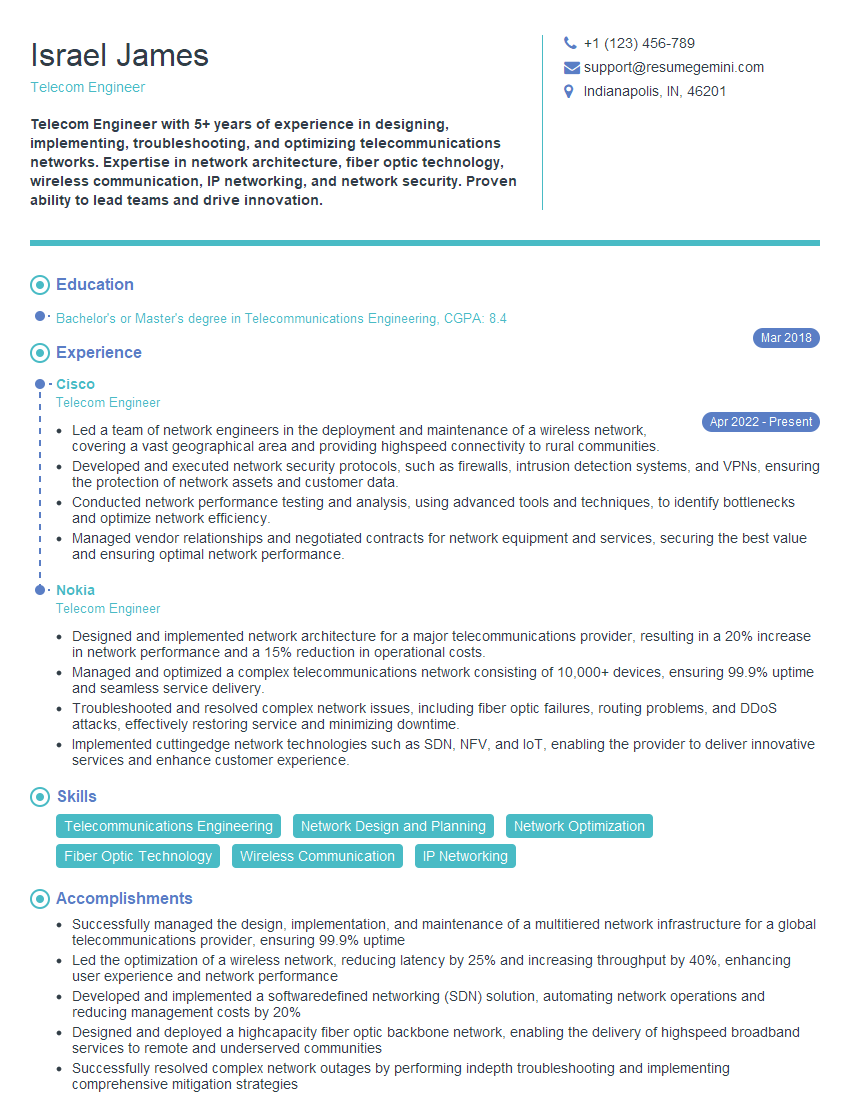
Mastering Wireless Communication Standards is crucial for career advancement in the dynamic field of telecommunications and related industries. A strong understanding of these concepts demonstrates technical expertise and opens doors to exciting opportunities. To maximize your job prospects, focus on creating an ATS-friendly resume that effectively highlights your skills and experience. ResumeGemini is a trusted resource to help you build a professional and impactful resume. Examples of resumes tailored to Wireless Communication Standards are available to guide you. Invest time in crafting a compelling resume that showcases your expertise – it’s a vital step in landing your dream role.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good