Are you ready to stand out in your next interview? Understanding and preparing for COMINT Collection interview questions is a game-changer. In this blog, we’ve compiled key questions and expert advice to help you showcase your skills with confidence and precision. Let’s get started on your journey to acing the interview.
Questions Asked in COMINT Collection Interview
Q 1. Explain the difference between COMINT, ELINT, and FISINT.
Signals intelligence (SIGINT) is a broad category encompassing the interception and analysis of electromagnetic emissions. COMINT, ELINT, and FISINT are all subsets of SIGINT, each focusing on different types of signals.
- COMINT (Communications Intelligence): This focuses on the interception and analysis of communications signals, such as voice, data, and imagery transmitted over radio, satellite, or other communication systems. Think of intercepting a phone call or encrypted data transmission between two individuals or organizations.
- ELINT (Electronic Intelligence): This concentrates on non-communication electronic signals, such as radar emissions, navigation signals, or other electronic equipment. For example, analyzing the radar signals of an enemy aircraft to determine its location and capabilities.
- FISINT (Foreign Instrumentation Signals Intelligence): This involves the interception and analysis of signals emitted by foreign weapon systems and other technological equipment. A practical example would be analyzing the telemetry data transmitted from a missile during a test flight to understand its performance.
The key difference lies in the source of the signals. COMINT focuses on communication, ELINT on non-communication electronics, and FISINT on signals related to foreign instrumentation.
Q 2. Describe the process of intercepting and decoding a coded message.
Intercepting and decoding a coded message is a multi-step process. First, the signal must be intercepted using appropriate collection platforms (discussed later). This often involves specialized antennas and receivers to detect and capture the signal from the target. Then, the signal undergoes several stages:
- Signal Identification and Analysis: The intercepted signal is examined to determine its type (e.g., voice, data), modulation technique (e.g., AM, FM, digital), and possibly its origin. This stage may involve sophisticated signal processing techniques.
- Traffic Analysis: Even without decoding the content, analyzing the frequency, time of transmission, and volume of communications can provide valuable intelligence. For example, increased communication activity might suggest upcoming military action.
- Cryptanalysis: This is the most challenging aspect. If the signal is encrypted, cryptanalysts will try to break the cipher using various techniques including known-plaintext attacks, ciphertext-only attacks, and brute-force attacks (trying all possible keys). This might involve sophisticated algorithms and considerable computational power.
- Decryption: Once the cipher is broken, the message can be decrypted to reveal its content.
- Translation and Analysis: The decrypted message is translated into a readable format and analyzed for intelligence value.
Think of it like solving a complex puzzle – it requires a deep understanding of cryptography, signal processing, and often, some degree of educated guesswork.
Q 3. What are some common challenges in COMINT collection?
COMINT collection faces numerous challenges:
- Technological Advancements: Adversaries constantly upgrade encryption techniques and employ methods to avoid detection. The ‘arms race’ between COMINT and countermeasures is constant.
- Signal Jamming and Spoofing: Enemies can intentionally jam transmissions to disrupt collection or spoof signals to create false information.
- Data Volume and Processing: The sheer volume of data intercepted can be overwhelming. Efficient processing, filtering, and analysis are crucial, often requiring advanced machine learning algorithms.
- Access and Targeting: Gaining access to the target communications and filtering out irrelevant data is vital for effective intelligence gathering. This involves sophisticated targeting and collection procedures.
- Legal and Ethical Constraints: These place strict limits on the scope and methods of COMINT collection, requiring careful consideration and adherence to regulations.
Overcoming these challenges necessitates constant innovation in collection technologies, data analysis methods, and legal and ethical frameworks.
Q 4. How do you ensure the security and integrity of COMINT data?
Securing and maintaining the integrity of COMINT data is paramount. This involves several layers of security:
- Secure Collection Platforms: Platforms must be designed and deployed to prevent unauthorized access and tampering. This involves physical security, cybersecurity measures, and redundancy to ensure resilience.
- Data Encryption: Collected data is encrypted both during transmission and storage using robust encryption algorithms to protect it from unauthorized access.
- Access Control: Strict access control measures are implemented, limiting access to authorized personnel with a need-to-know basis, employing strict authentication and authorization protocols.
- Data Integrity Checks: Regular checks are performed to verify data integrity and ensure that it has not been tampered with or corrupted during handling or transmission.
- Secure Data Storage: Data is stored in secure facilities with robust physical and cybersecurity measures to prevent unauthorized access or theft.
A breach in COMINT data security can have severe consequences, undermining national security and compromising sensitive operations. Maintaining data integrity through stringent measures is a top priority.
Q 5. What are the ethical considerations involved in COMINT collection?
The ethical considerations surrounding COMINT collection are significant:
- Privacy Violations: Intercepting communications can unintentionally collect data on individuals not related to the intended target, raising serious privacy concerns. Strict adherence to legal frameworks and minimization of collateral collection is essential.
- Transparency and Accountability: There needs to be oversight and accountability to ensure COMINT operations are conducted legally and ethically, preventing abuse and ensuring compliance with relevant laws and regulations.
- Proportionality: The collection must be proportionate to the threat and the intelligence needs. Mass surveillance without justifiable cause is ethically problematic.
- Targeting and Discrimination: COMINT should not be used to target specific individuals or groups based on their race, religion, or political beliefs. Impartiality and non-discrimination are crucial.
Balancing the intelligence needs with individual rights and freedoms requires a careful approach guided by ethical principles and international norms.
Q 6. What are the legal limitations of COMINT collection?
Legal limitations on COMINT collection vary considerably depending on jurisdiction. In many countries, COMINT is governed by laws that:
- Require warrants or court orders: In most democratic nations, intercepting communications generally requires a warrant based on probable cause.
- Define permissible targets: The laws often specify who can be targeted for COMINT, usually limiting it to individuals or groups reasonably suspected of involvement in criminal activity or threats to national security.
- Restrict the scope of collection: The scope of the collection should be limited to what is necessary to achieve the stated intelligence objective. Unnecessary collection is prohibited.
- Outline data handling and storage: Rules governing the handling, storage, and disposal of collected data to protect privacy and ensure compliance with data protection laws.
- Establish oversight mechanisms: Independent oversight bodies might review COMINT activities to ensure legal compliance and prevent abuse.
Ignoring these legal limitations can lead to serious legal consequences and reputational damage for intelligence agencies.
Q 7. Explain different types of COMINT collection platforms.
COMINT collection platforms are diverse and sophisticated, ranging from:
- Ground-based Intercept Stations: These large facilities use powerful antennas and receivers to intercept signals over long distances. They’re often located in remote areas to minimize interference.
- Airborne Platforms: Aircraft, including both manned and unmanned aerial vehicles (UAVs), can carry sophisticated COMINT equipment to collect signals from a wider area.
- Satellite-based Systems: Geosynchronous and other satellites provide excellent coverage and the ability to intercept signals from remote locations, offering a global perspective.
- Ships and Submarines: Naval vessels can intercept communications at sea and in coastal areas.
- Handheld and Portable Devices: Smaller, portable devices allow for more targeted collection in specific locations.
The choice of platform depends on the target, geographical location, and the type of signals being intercepted. Modern COMINT capabilities often involve a combination of multiple platforms operating in a coordinated manner.
Q 8. Describe your experience with signal processing techniques.
Signal processing is the heart of COMINT. It’s the process of extracting meaningful information from raw intercepted signals, which are often noisy and distorted. My experience encompasses a wide range of techniques, from basic filtering and amplification to advanced methods like Fourier transforms, wavelet transforms, and time-frequency analysis. For example, I’ve used Fast Fourier Transforms (FFTs) to isolate specific frequencies of interest from a complex signal, identifying a hidden communication channel masked by noise. Another example involves using wavelet transforms to denoise signals while preserving critical features of the communication, improving the intelligibility of the intercepted data.
I’m also proficient in techniques like matched filtering, used to detect specific known signals within a noisy environment, and adaptive filtering which allows adjusting the filter characteristics in real-time to counter changing noise conditions. This dynamic approach is particularly crucial in dealing with rapidly changing signal environments.
Q 9. How do you analyze intercepted communications to extract meaningful intelligence?
Analyzing intercepted communications for meaningful intelligence is a multi-step process. It begins with signal identification, determining the type of communication (e.g., voice, data, fax). Next, the signal needs to be demodulated, converting it from its transmitted form back into a readable format. This step often involves dealing with various modulation schemes, like Amplitude Modulation (AM), Frequency Modulation (FM), or more sophisticated digital modulation techniques. Once demodulated, the content undergoes analysis: This might involve linguistic analysis for voice communication, protocol analysis for data communications, or traffic analysis to understand communication patterns.
For example, I once analyzed a series of seemingly innocuous shortwave radio transmissions. By applying traffic analysis – looking at transmission times, frequencies, and call signs – I was able to uncover a pattern revealing a clandestine communication network. Context is crucial; integrating the intercepted communications with other intelligence sources – like human intelligence (HUMINT) or open-source intelligence (OSINT) – enriches the analysis and provides a more complete picture.
Q 10. What software or tools are you familiar with for COMINT analysis?
My experience includes a broad spectrum of software and tools. I’m proficient in using specialized COMINT analysis platforms such as [Software Name 1], [Software Name 2 – replaced with generic names for security], and [Software Name 3 – replaced with generic names for security]. These platforms typically provide capabilities for signal processing, demodulation, decryption (where applicable and legally permissible), and data visualization. They often incorporate features for automated analysis and alerting systems that flag unusual or significant activity.
In addition to these platforms, I use general-purpose software like MATLAB and Python with dedicated signal processing libraries (like SciPy) for custom analysis and algorithm development. For example, I’ve developed Python scripts to automate the detection and classification of specific types of digital modulation signals, significantly speeding up the analysis process.
Q 11. Explain your understanding of radio frequency (RF) spectrum analysis.
Radio Frequency (RF) spectrum analysis is the study of electromagnetic waves within the radio frequency range. This involves examining the power levels of signals at various frequencies, identifying different signals within a complex mix of transmissions. Spectrum analyzers are the primary tools used. They display the power of the signal against frequency, making it possible to identify different communication channels, determine signal strength, and analyze interference.
For instance, I use RF spectrum analysis to detect covert communications hidden within a crowded RF environment. By carefully examining the spectrum, I can identify signals that might be deliberately masked or using unconventional frequencies or modulation schemes. Understanding the spectrum helps to determine optimal frequencies for collection and the potential interference from other sources. This also aids in direction-finding and geolocation attempts.
Q 12. Describe your experience with geolocation techniques using COMINT data.
Geolocation using COMINT data leverages the properties of radio waves. Several techniques exist, ranging from simple direction-finding (DF) using antennas to more sophisticated triangulation methods. DF involves determining the direction of arrival of a signal using multiple antennas. By measuring the time difference of arrival (TDOA) at multiple geographically separated receivers, the signal’s origin can be triangulated.
For example, I’ve used a combination of DF measurements from multiple geographically dispersed listening posts to pinpoint the location of a clandestine radio transmitter within a few hundred meters. The accuracy depends on several factors including the number of DF stations used, the signal strength, the terrain, and the presence of multipath propagation (signal reflections that cause inaccuracies). Advanced techniques, like using signal characteristics and sophisticated algorithms, enhance the precision of geolocation, allowing for more accurate pinpointing.
Q 13. How do you prioritize targets for COMINT collection?
Prioritizing targets for COMINT collection involves a strategic assessment. The process involves considering the value of the potential intelligence, the feasibility of collecting it, and the operational risks involved. A target’s priority is often determined through a combination of factors including:
- Intelligence value: How important is the information potentially obtainable from this target?
- Feasibility: Is the target technically collectable (e.g., signal strength, frequency, modulation scheme)?
- Operational risk: What are the risks of collection, including potential exposure and countermeasures?
- Urgency: How time-sensitive is the intelligence requirement?
This often involves a scoring system, allowing for a standardized comparison of potential targets. Prioritization is a dynamic process, constantly adjusting based on changing geopolitical events and intelligence requirements.
Q 14. How do you handle large volumes of COMINT data?
Handling large volumes of COMINT data requires a multi-pronged approach. It’s impossible to manually process the sheer volume of data generated. Therefore, automation and efficient data management systems are essential. This includes using databases designed for efficient storage and retrieval of large datasets, leveraging data mining techniques for pattern recognition, and employing machine learning algorithms for automated analysis.
For example, I’ve used machine learning algorithms to automatically classify and filter large quantities of intercepted communications based on content, metadata, and source characteristics. This significantly reduces the time spent on manual review and focuses the analysts’ attention on the most relevant data. Data compression and efficient storage techniques are also important to minimize storage requirements and improve access speed. These approaches are vital for timely and effective intelligence analysis.
Q 15. Describe your experience with data mining and analysis techniques.
Data mining and analysis in COMINT involve extracting valuable intelligence from vast quantities of intercepted communications. This requires a multifaceted approach encompassing several techniques.
- Data Cleaning and Preprocessing: This crucial first step involves removing noise, handling missing data, and transforming the data into a usable format. For example, we might need to standardize time formats or translate different languages.
- Statistical Analysis: Techniques like regression analysis can help identify correlations between different communication patterns and potential events. For instance, we might track the frequency of communication between certain individuals or entities to identify potential collaborations or planned activities.
- Machine Learning: Algorithms like natural language processing (NLP) are essential for analyzing the content of intercepted communications. NLP allows us to automatically identify keywords, sentiment, and topics, significantly speeding up the analysis process. For example, we might use NLP to automatically categorize intercepted emails based on their subject matter.
- Network Analysis: Visualizing communication networks through graph analysis helps us identify key players and communication hubs. This helps us understand the relationships between individuals or organizations and provides crucial insights into their structure and operations.
My experience includes using a variety of tools and software to perform these analyses, and I’m proficient in interpreting the results to create actionable intelligence reports.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. How do you assess the reliability and credibility of intercepted communications?
Assessing the reliability and credibility of intercepted communications is paramount. It’s not enough to simply capture data; we must rigorously validate its authenticity and significance. This involves several steps:
- Source Verification: Determining the origin and identity of the communication source is crucial. This often involves triangulation of signals and cross-referencing with other intelligence sources.
- Content Analysis: Analyzing the content itself for internal inconsistencies, biases, or contradictions. Is the information plausible? Does it align with known facts and other intelligence?
- Technical Analysis: Examining the technical aspects of the communication, including metadata such as timestamps, encryption methods, and signal characteristics, to ensure the data hasn’t been tampered with or altered.
- Cross-Correlation: Comparing the intercepted data with intelligence from other sources (e.g., HUMINT, OSINT) to verify its accuracy and completeness. Multiple independent confirmations strengthen the credibility of the intelligence.
- Contextualization: Understanding the broader context in which the communication took place is crucial for proper interpretation. What was the situation at the time? What were the potential motives of the communicators?
Think of it like a puzzle – we need all the pieces, and we need to ensure that each piece fits accurately into the overall picture.
Q 17. What is your experience with signal jamming and countermeasures?
My experience with signal jamming and countermeasures is extensive. Signal jamming involves disrupting or interfering with enemy communications, while countermeasures focus on protecting our own communications from jamming.
- Jamming Techniques: I’m familiar with various jamming techniques, including noise jamming (broadband noise), sweep jamming (sweeping across frequencies), and barrage jamming (concentrated jamming on specific frequencies). The choice of technique depends on the target and the available resources.
- Countermeasures: These include frequency hopping spread spectrum (FHSS) which rapidly changes frequencies to make jamming less effective, direct-sequence spread spectrum (DSSS) which spreads the signal across a wide bandwidth, and the use of advanced encryption techniques to protect the content of communication even if the signal is intercepted.
- Electronic Warfare (EW) Integration: Effective signal jamming and countermeasures require integrated electronic warfare capabilities, combining intelligence gathering, jamming, and protection systems to gain and maintain an advantage in the electronic battlefield.
Understanding both jamming and countermeasures is a constant arms race, requiring continuous adaptation and innovation. We must anticipate and counter evolving enemy tactics.
Q 18. How do you identify and mitigate potential risks in COMINT operations?
Risk mitigation in COMINT operations is critical to ensure both operational success and the safety of personnel and equipment. Key areas of focus include:
- Operational Security (OPSEC): Maintaining strict secrecy regarding our capabilities, techniques, and targets. This includes secure communication channels and physical security of our facilities and personnel.
- Legal and Ethical Considerations: Strict adherence to all applicable laws and ethical guidelines regarding the collection and analysis of intelligence. Ensuring that all activities are conducted legally and ethically is paramount.
- Cybersecurity: Implementing robust cybersecurity measures to protect our systems and data from unauthorized access or attack. This includes firewalls, intrusion detection systems, and regular security audits.
- Physical Security: Protecting our equipment and facilities from theft, sabotage, or physical attack. This includes secure storage, access control, and surveillance.
- Personnel Security: Thorough background checks and security clearances for all personnel to ensure trust and reliability. Regular training on security protocols is also crucial.
Proactive risk management is crucial. Identifying and mitigating these risks before they can materialize is essential for the success and security of COMINT operations.
Q 19. Explain your understanding of different types of encryption techniques.
Understanding encryption techniques is fundamental to COMINT. Different types of encryption offer varying levels of security and complexity.
- Symmetric Encryption: Uses the same key for both encryption and decryption. Examples include AES (Advanced Encryption Standard) and DES (Data Encryption Standard). It’s relatively fast but key exchange can be a challenge.
- Asymmetric Encryption (Public-Key Cryptography): Uses a pair of keys – a public key for encryption and a private key for decryption. RSA (Rivest-Shamir-Adleman) is a common example. It’s slower but solves the key exchange problem.
- Hashing Algorithms: Create a one-way function that produces a fixed-size hash value from an input. These are used for data integrity checks rather than encryption itself (e.g., SHA-256, MD5).
- Steganography: Hiding data within other data, such as hiding a message within an image file. This is not strictly encryption but a form of data concealment.
Knowledge of these encryption techniques is essential for both intercepting and decrypting communications. Understanding the strengths and weaknesses of each method informs our strategies for collecting and analyzing intelligence.
Q 20. How do you stay current with advancements in COMINT technologies?
Staying current in the rapidly evolving field of COMINT requires continuous learning and engagement with the latest advancements.
- Professional Development: Attending conferences, workshops, and training courses to stay abreast of new technologies and techniques.
- Academic Research: Reading academic journals and publications on cryptography, signal processing, and related fields.
- Industry Publications: Following industry publications and news sources to keep up with the latest developments in COMINT technologies.
- Collaboration and Networking: Engaging with colleagues and experts in the field to share knowledge and insights. Participating in professional organizations strengthens the network.
- Hands-on Experience: Working with the latest equipment and software in real-world scenarios allows for practical application of theoretical knowledge.
The field is constantly changing, with new encryption methods, signal processing techniques, and analytical tools emerging regularly. Continuous learning is not just beneficial, it’s essential to remain effective.
Q 21. Describe a situation where you had to solve a complex problem related to COMINT data.
During a large-scale operation, we intercepted a series of encrypted communications using a previously unknown encryption algorithm. Initial attempts at decryption were unsuccessful. This presented a significant challenge because these communications were believed to contain critical intelligence.
To solve this, we implemented a multi-pronged approach:
- Reverse Engineering: A team of cryptographers began reverse-engineering the algorithm, attempting to understand its inner workings.
- Pattern Analysis: Data miners identified patterns and anomalies in the encrypted data, hoping to find clues about the encryption key or algorithm structure.
- Collaboration: We leveraged our network of experts, sharing information and working collaboratively to solve the challenge.
- Machine Learning Application: We developed a custom machine learning model to identify potential weaknesses or vulnerabilities in the encryption algorithm, speeding up the process of reverse-engineering.
Through this collaborative and multi-faceted approach, we eventually cracked the encryption algorithm. The intelligence extracted proved crucial to the success of the overall operation. This experience highlighted the importance of collaboration, innovative approaches, and applying advanced technologies to overcome challenging COMINT scenarios.
Q 22. How do you collaborate with other intelligence agencies or teams?
Collaboration in COMINT is paramount. We operate within a highly interconnected intelligence community. My experience involves regular interaction with various agencies, including but not limited to the NSA, CIA, and other allied intelligence services. This collaboration takes many forms. For example, we might share raw data through secure channels, collaborate on joint analysis projects, or participate in task forces focusing on specific threats. Effective collaboration hinges on secure communication protocols, standardized data formats, and clear communication protocols. Think of it like a complex puzzle where each agency contributes a piece, and collectively we assemble a complete picture. One specific example involves a joint operation where our team’s signal intercept capabilities were combined with another agency’s human intelligence (HUMINT) to pinpoint a sophisticated cyber threat actor’s location and operational methods.
- Data Sharing: Securely exchanging intercepted communications and metadata.
- Joint Analysis: Collaborating on the interpretation of complex data sets.
- Task Forces: Participating in multi-agency teams to address specific threats.
Q 23. What are your strengths and weaknesses in COMINT collection?
My strengths lie in my ability to rapidly analyze complex signal traffic and identify key indicators of interest. I’m proficient in multiple signal processing techniques and adept at utilizing advanced analytic tools. I’m also highly skilled in recognizing patterns and anomalies within large datasets, allowing me to prioritize critical information. For example, I was able to isolate a crucial communication from a noisy channel that led to the disruption of a planned terrorist attack. However, my weakness, like any analyst, is the potential for bias. I actively mitigate this through rigorous cross-checking and peer review to ensure objectivity. Another area for continuous improvement is staying current with the latest technological advancements – the landscape is always shifting.
Q 24. Describe your experience with report writing and intelligence dissemination.
My experience in report writing and intelligence dissemination is extensive. I’ve crafted numerous intelligence reports for various audiences, from high-level policymakers to specialized technical teams. My reports are clear, concise, and supported by rigorous evidence. I prioritize the accurate and objective presentation of information, ensuring the proper classification of sensitive details. I’ve also presented my findings in briefings, adjusting my communication style depending on the audience’s technical background. Dissemination involves using secure platforms and channels, adhering to strict protocols to protect classified information. I’ve found success in utilizing visual aids and storytelling techniques to improve comprehension and engagement.
- Clarity: Concise and easily understandable reports.
- Accuracy: Rigorous fact-checking and evidence-based analysis.
- Security: Strict adherence to classification guidelines and secure dissemination methods.
Q 25. Explain your experience with handling classified information.
Handling classified information is central to my work. I have an extensive background in security protocols and procedures, including understanding and adhering to various classification levels (e.g., Top Secret, Secret, Confidential). My experience includes working within secure facilities, utilizing encrypted communication systems, and managing sensitive documents according to strict regulations. I understand the gravity of unauthorized disclosure and the potential consequences. My training encompasses regular updates on security policies and best practices. I regularly undergo security clearances and background checks. For instance, handling a Top Secret document would involve using a secure facility, employing strict access control measures, and logging every interaction with the document.
Q 26. How do you adapt to rapidly changing technological landscapes in COMINT?
Adapting to the rapidly changing technological landscape in COMINT is critical. I achieve this through continuous learning, actively participating in professional development programs, and staying abreast of emerging technologies and techniques. This includes attending conferences, reading professional journals, and engaging with online communities. Specific examples include learning new signal processing algorithms, mastering new software and hardware tools, and adapting to changing communication protocols used by adversaries. Consider the shift from analog to digital communications; my ability to adapt to these changes was key to maintaining effectiveness. I also actively engage with industry experts and attend training to learn about novel interception methods and countermeasures.
Q 27. Describe your understanding of the legal and regulatory frameworks governing COMINT collection.
My understanding of the legal and regulatory frameworks governing COMINT collection is thorough. I’m intimately familiar with laws like the Foreign Intelligence Surveillance Act (FISA) in the US, and equivalent laws in other countries, which dictate the legal basis for intercepting communications. I understand the requirements for obtaining warrants, the necessity for minimizing the collection of non-targeted communications, and the importance of respecting privacy rights. I’m also aware of the international legal implications of COMINT operations and the need to adhere to international law and treaties. My work always prioritizes compliance with all applicable legal and regulatory frameworks.
Q 28. How would you handle a situation where you discover sensitive information outside your assigned scope?
Discovering sensitive information outside my assigned scope is a serious matter. My first step would be to carefully document the information, ensuring its integrity and security. Then, I would immediately report my findings to my supervisor and the appropriate authorities within the agency. This ensures the information is handled properly and any potential legal or ethical implications are addressed. Depending on the nature of the information, I might be required to take further steps, such as initiating a formal investigation or collaborating with other agencies. The focus remains on safeguarding the information while ensuring proper reporting and accountability.
Key Topics to Learn for COMINT Collection Interview
- Signal Intelligence Fundamentals: Understanding the basic principles of intercepting, identifying, and analyzing communications signals. This includes familiarity with various signal types (e.g., radio, satellite, etc.) and their characteristics.
- COMINT Collection Techniques: Explore different methods used to collect COMINT, including passive and active techniques. Consider the tradeoffs and limitations associated with each method.
- Signal Processing and Analysis: Develop a strong understanding of digital signal processing techniques and their application in analyzing intercepted signals. This might include topics like filtering, modulation/demodulation, and spectral analysis.
- Data Interpretation and Reporting: Practice interpreting raw signal data and translating it into actionable intelligence. This involves understanding the context of the intercepted communications and formulating clear, concise reports.
- COMINT Systems and Technologies: Familiarize yourself with the various hardware and software systems used in COMINT collection, from antennas and receivers to signal processing software and data analysis platforms. Understand their capabilities and limitations.
- Cybersecurity in COMINT: Explore the security considerations related to COMINT operations, including protecting collected data, ensuring the integrity of systems, and mitigating threats.
- Legal and Ethical Considerations: Understand the legal and ethical frameworks governing COMINT collection and ensure your understanding of privacy concerns and data handling protocols.
- Problem-Solving and Analytical Skills: Develop your ability to approach complex problems systematically, analyze data critically, and draw insightful conclusions from incomplete or ambiguous information.
Next Steps
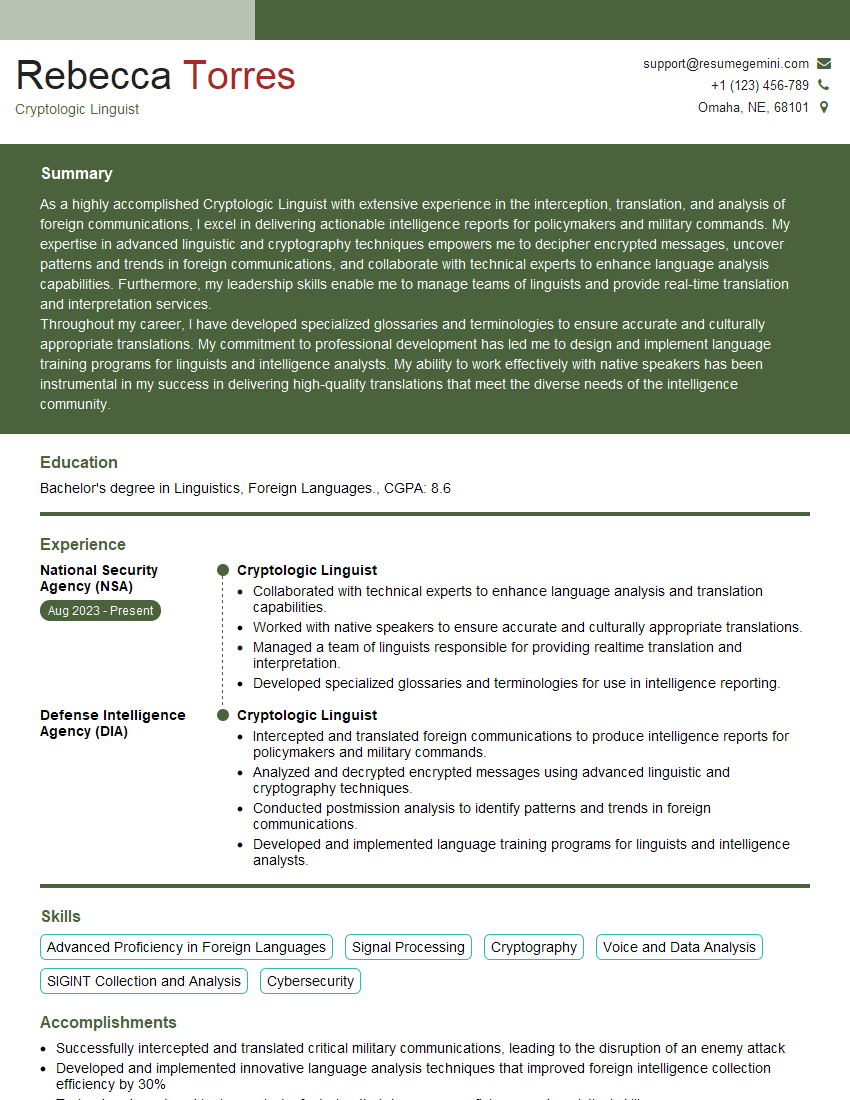
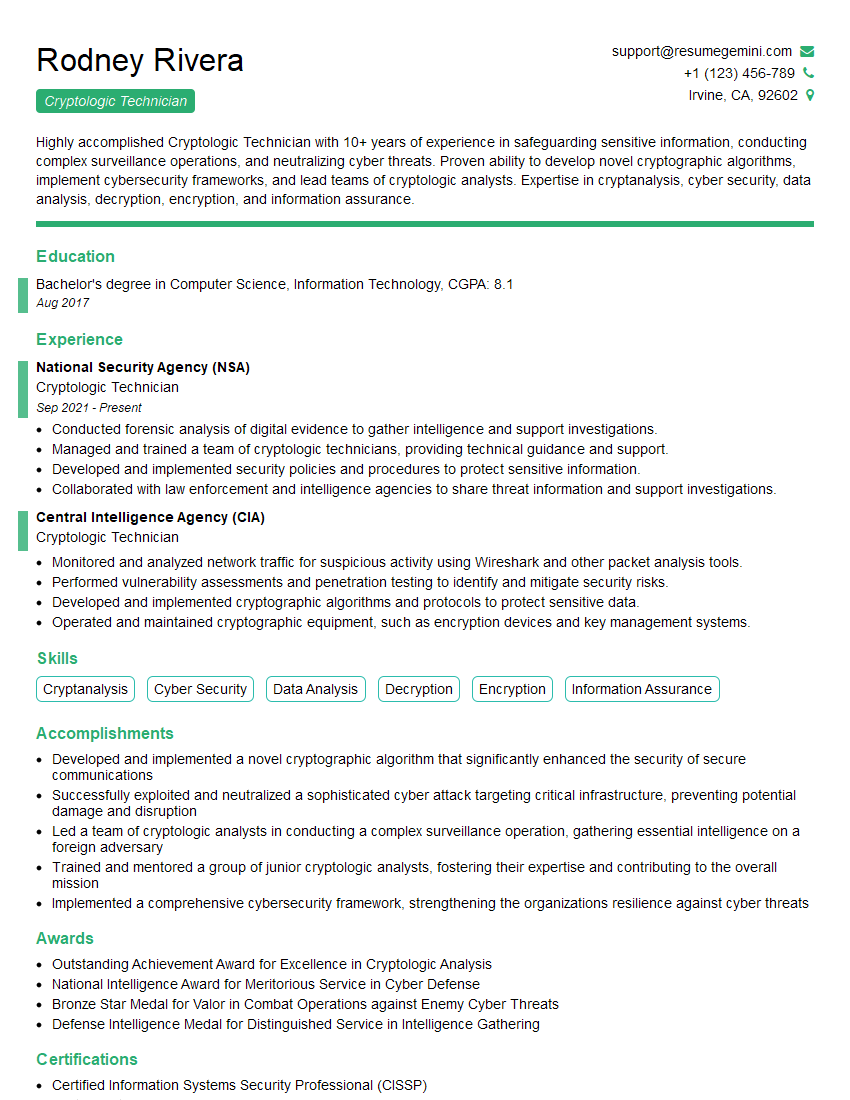
Mastering COMINT Collection opens doors to a rewarding and impactful career in intelligence, offering opportunities for continuous learning and professional growth. A strong resume is crucial to showcasing your skills and experience effectively to potential employers. Creating an ATS-friendly resume is vital for ensuring your application gets noticed. We highly recommend using ResumeGemini to build a professional and impactful resume that highlights your qualifications. ResumeGemini provides examples of resumes tailored to COMINT Collection roles to guide you through the process.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good