Every successful interview starts with knowing what to expect. In this blog, we’ll take you through the top Configuration Baseline Management interview questions, breaking them down with expert tips to help you deliver impactful answers. Step into your next interview fully prepared and ready to succeed.
Questions Asked in Configuration Baseline Management Interview
Q 1. Explain the concept of a Configuration Baseline.
A Configuration Baseline is a formally approved specification of a system or component at a specific point in time. Think of it as a snapshot of your system’s configuration that’s been officially signed off on. It serves as a reference point for future changes and ensures that modifications don’t destabilize the system’s functionality or integrity. It includes not only the software, hardware, and network configurations, but also documentation like design specs and test results. Establishing a baseline is crucial for managing complex systems and ensuring consistency, traceability, and accountability.
Q 2. What is a Configuration Item (CI) and how does it relate to baselines?
A Configuration Item (CI) is a single, identifiable component within a system. This could be anything from a piece of hardware (like a server), a software application, a database, or even a configuration file. Baselines are built from collections of CIs. Each CI within a baseline has its own version and attributes documented. For example, a baseline for a web application might include CIs such as the application code (version 1.0), the web server (Apache 2.4.5), and the database (MySQL 8.0). The relationships between these CIs are also defined within the baseline.
Q 3. Describe the process of establishing a Configuration Baseline.
Establishing a Configuration Baseline is a formal process. It typically involves these steps:
- Identify CIs: Determine all the components making up the system.
- Version Control: Assign version numbers to each CI. Use a version control system (like Git) for software components.
- Document Configuration: Create comprehensive documentation detailing the configuration of each CI, including settings, dependencies, and relationships.
- Testing and Verification: Rigorously test the system to ensure its stability and functionality at this baseline. This often includes unit, integration, and system tests.
- Formal Approval: Obtain formal approval from stakeholders, signifying the acceptance of the baseline.
- Baseline Identification and Storage: Assign a unique identifier to the baseline and store all documentation in a central repository. This could be a CMDB or a dedicated document management system.
Imagine building a house. The baseline would be the completed blueprint – the finalized design – before construction begins. Any changes after that require a formal review and update to the blueprint.
Q 4. How do you manage changes to a Configuration Baseline?
Managing changes to a Configuration Baseline requires a formal Change Management process. This usually involves:
- Change Request: A formal request for a change is submitted, detailing the proposed modification and its justification.
- Impact Assessment: Assessing the impact of the change on other CIs and the overall system.
- Risk Assessment: Identifying and mitigating potential risks associated with the change.
- Change Approval: The change request is reviewed and approved by the appropriate stakeholders.
- Implementation: The change is implemented, carefully following the approved plan.
- Verification: Thorough testing is performed to verify the change’s success and its impact on the system.
- Documentation Update: The baseline documentation is updated to reflect the changes.
- New Baseline Creation (Optional): Depending on the significance of the change, a new baseline might be created to represent the updated system.
Think of it like updating software: A patch is a small change, but a major upgrade might create an entirely new version, necessitating a new baseline.
Q 5. What is the role of a CMDB in Configuration Baseline Management?
A Configuration Management Database (CMDB) is a crucial tool for Configuration Baseline Management. It acts as a central repository for all CIs and their relationships, providing a single source of truth about the system’s configuration. The CMDB facilitates the tracking of versions, dependencies, and changes. It supports the documentation and management of baselines, simplifying the process of identifying impacted CIs when changes are proposed. A well-maintained CMDB is essential for effective Configuration Baseline Management and aids in problem diagnosis and risk mitigation.
Q 6. Explain the difference between a baseline and a snapshot.
While both baselines and snapshots capture the state of a system, they differ significantly in their formality and purpose. A snapshot is an informal record of the system’s state at a particular point in time. It’s typically used for quick reference or recovery purposes. A baseline, on the other hand, is a formally approved and documented configuration that serves as the foundation for future development and change. Think of a snapshot as a casual photo, while a baseline is a formal portrait – carefully posed and documented.
Q 7. How do you ensure the integrity of a Configuration Baseline?
Ensuring the integrity of a Configuration Baseline requires a multi-faceted approach:
- Version Control: Utilizing a robust version control system (e.g., Git) to track changes to all CIs.
- Access Control: Implementing strict access controls to prevent unauthorized modifications to the baseline.
- Regular Audits: Conducting regular audits to compare the actual configuration against the baseline documentation.
- Automated Checks: Employing automated tools to detect discrepancies between the documented and actual configurations.
- Configuration Monitoring: Continuously monitoring the system’s configuration for unexpected changes.
- Documented Change Management Process: Strictly adhering to a well-defined change management process for all modifications.
Maintaining baseline integrity is like carefully preserving a valuable artifact. Any damage or alteration must be documented and controlled.
Q 8. What are the key benefits of using Configuration Baselines?
Configuration Baselines are snapshots of a system’s configuration at a specific point in time. They serve as a trusted reference point for managing changes and ensuring system stability. Think of it like a blueprint for your system; it documents everything from hardware and software components to network settings and security configurations.
- Improved Traceability: Easily track changes and understand the impact of each modification. Imagine trying to troubleshoot a problem without knowing what changed when! Baselines make this a breeze.
- Reduced Risk: By establishing a baseline, you create a known good state. Reversions to this state become much easier and faster, significantly reducing the downtime due to errors.
- Enhanced Consistency: All systems can be brought to the same standard, enhancing performance and reducing variations across deployments.
- Simplified Audits and Compliance: Baselines simplify audits by providing clear documentation of the system’s configuration, crucial for meeting regulatory requirements.
- Better Collaboration: A clear and documented baseline allows development, operations, and security teams to work together more efficiently, reducing confusion and conflicts.
Q 9. Describe a situation where a Configuration Baseline was critical to success.
During a recent major software release for a financial institution, we established a Configuration Baseline before the deployment. This baseline included all server configurations, network settings, database schemas, and application code versions. After deployment, we encountered an unexpected performance bottleneck. By comparing the post-deployment configuration against the baseline, we quickly identified the specific changes that introduced the issue. A rollback to the baseline restored the system’s performance within minutes, minimizing disruption and financial losses. Without this baseline, identifying the root cause and restoring the system would have been significantly more time-consuming and disruptive.
Q 10. How do you handle conflicting changes to a Configuration Baseline?
Conflicting changes to a Configuration Baseline are a common challenge. Resolution requires a structured approach. We use a Change Control Board (CCB) to evaluate competing changes. This board comprises representatives from development, operations, and security. The CCB assesses the impact of each change request, considering factors like risk, urgency, and dependencies. They may employ several strategies:
- Prioritization: The CCB may prioritize changes based on business needs or urgency, selecting one change to be implemented and deferring others.
- Integration: If both changes are deemed necessary, the CCB might work to integrate them, ensuring compatibility.
- Negotiation and Compromise: Sometimes, compromises need to be made, perhaps altering the scope of one or both changes to resolve the conflict.
- Rejection: In cases where the conflict is unresolvable or the risks are too high, a change request might be rejected.
Throughout this process, detailed documentation is key, ensuring everyone is aware of the decisions made and the rationale behind them. The outcome is always documented and the baseline updated accordingly.
Q 11. What metrics do you use to track the effectiveness of Configuration Baseline Management?
Tracking the effectiveness of Configuration Baseline Management relies on several key metrics:
- Mean Time To Recovery (MTTR): Measures the time it takes to restore the system to a working state after an incident. A lower MTTR indicates improved efficiency and the effectiveness of the baseline in facilitating faster recovery.
- Change Failure Rate: Tracks the percentage of changes that result in incidents or require rollbacks. A lower rate reflects a more robust and well-managed baseline.
- Compliance Rate: Assesses adherence to established policies and regulations. This is particularly important for regulated industries.
- Number of Baseline Updates: Tracks the frequency of baseline updates. A high frequency might indicate an unstable system or insufficient planning, while extremely low frequency may indicate a lack of responsiveness to necessary changes.
- Time Spent on Incident Resolution: The time needed to resolve incidents. A decrease in this metric shows the positive effect of having well-defined baselines.
Q 12. How do you communicate changes to Configuration Baselines to stakeholders?
Communicating changes to Configuration Baselines effectively is crucial to minimize disruption and maintain trust among stakeholders. We employ a multi-faceted approach:
- Formal Change Notifications: Changes are formally documented and communicated through email or a dedicated change management system. These notifications include a summary of changes, their impact, and scheduled implementation times.
- Regular Reporting: Periodic reports are generated and distributed to stakeholders, providing an overview of baseline changes and their effects on system performance and stability.
- Dedicated Communication Channels: We use a combination of channels, such as email, instant messaging, and project management tools to ensure everyone stays informed.
- Change Management Meetings: Regular meetings can be scheduled with key stakeholders to discuss upcoming changes and address any concerns.
- Knowledge Base: A readily accessible knowledge base should document all configuration changes, providing clarity and historical context.
Q 13. What tools or technologies have you used for Configuration Baseline Management?
Over the years, I’ve used a variety of tools for Configuration Baseline Management. These include:
- Configuration Management Databases (CMDBs): Such as ServiceNow or BMC Remedy, to store and track configuration items.
- Version Control Systems (VCSs): Like Git, for managing code and configuration files.
- Infrastructure as Code (IaC) tools: Such as Terraform or Ansible, to automate infrastructure provisioning and configuration management, allowing us to easily create and manage baselines.
- Specialized Configuration Management Tools: These tools provide specific functionalities for managing configurations for particular technologies or platforms.
The choice of tool depends on the specific needs and the scale of the system. For example, a small-scale project might use Git, while a large enterprise would likely leverage a CMDB and IaC tools for greater efficiency and scalability.
Q 14. Explain the process of auditing a Configuration Baseline.
Auditing a Configuration Baseline involves a systematic review to verify its accuracy and completeness against the actual system configuration. This process typically involves:
- Defining the Scope: Clearly define what components are included in the audit.
- Developing an Audit Plan: This plan outlines the steps involved, tools to be used, and the expected timeframe.
- Gathering Evidence: Collect evidence from various sources, such as system logs, configuration files, and documentation.
- Comparing Baseline to Actual: Compare the documented baseline with the actual configuration of the system. Discrepancies should be noted.
- Investigating Discrepancies: Investigate the root causes of any discrepancies. Were changes not documented? Were they unauthorized?
- Reporting and Remediation: Document the findings and recommend any necessary corrective actions to address discrepancies. Update the baseline to reflect the actual configuration.
Regular auditing is crucial for maintaining the integrity of the Configuration Baseline and ensuring it accurately reflects the current state of the system. The frequency of audits depends on several factors, including the criticality of the system and regulatory requirements.
Q 15. How do you address deviations from a Configuration Baseline?
Addressing deviations from a Configuration Baseline is crucial for maintaining system stability and integrity. Think of a baseline as a blueprint for your system; any deviation is like an unauthorized alteration to that blueprint. When a deviation occurs, a rigorous process must be followed.
First, the deviation needs to be identified and documented. This often involves change management systems and regular audits. Once identified, the deviation is assessed for its impact. Is it a minor tweak with negligible risk or a major change that could cause system instability? This assessment dictates the next steps.
- Minor Deviations: These might be addressed through a simple change request, documented and approved within the existing change management framework. For instance, a minor update to a configuration file on a non-critical server.
- Major Deviations: Significant deviations require a more thorough investigation. This might involve a formal change request with a comprehensive risk assessment, impact analysis, and testing before implementation. Let’s say a key security patch was not applied as part of a planned update – this needs careful review and remediation.
Finally, after the deviation is addressed, the baseline needs to be updated to reflect the changes. This ensures the configuration documentation accurately represents the current state of the system. Without this update, the baseline becomes useless – a stale reflection of the past.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. How do you ensure that Configuration Baselines are up-to-date and accurate?
Maintaining up-to-date and accurate Configuration Baselines is an ongoing process requiring a combination of automated tools and disciplined procedures. Imagine a living document that continuously evolves with your system.
- Automated Monitoring: Employing automated tools to continuously monitor the system’s configuration is key. These tools can compare the actual configuration against the baseline, alerting you to any discrepancies. Think of it as a vigilant watchdog, constantly comparing the ‘as-is’ state to the ‘should-be’ state.
- Regular Audits: Scheduled audits, both manual and automated, are vital to verify the baseline’s accuracy. These audits should cover all aspects of the configuration, ensuring no gaps or inconsistencies exist.
- Configuration Management Database (CMDB): A CMDB serves as a central repository for all configuration items (CIs). This database should be integrated with your change management system to automatically update the baseline after approved changes. This provides a single source of truth about your system’s configuration.
- Version Control: Implementing a robust version control system for all configuration files allows you to track changes, revert to previous versions if necessary, and maintain a clear audit trail. Git, for example, is an excellent choice for this purpose.
By combining these methods, you can ensure that your Configuration Baselines remain a reliable representation of your system’s actual configuration.
Q 17. Describe your experience with different Configuration Baseline Management methodologies.
My experience encompasses various Configuration Baseline Management methodologies, each with its own strengths and weaknesses. I’ve worked with ITIL, COBIT, and agile frameworks, adapting my approach to the specific context of each project.
- ITIL (Information Technology Infrastructure Library): ITIL provides a comprehensive framework for IT service management, including change management and configuration management processes. I’ve used ITIL’s change control processes to manage changes to baselines effectively, ensuring thorough testing and approvals before implementation.
- COBIT (Control Objectives for Information and related Technologies): COBIT provides a framework for IT governance and management, emphasizing risk management and compliance. In projects requiring strict regulatory compliance, I’ve integrated COBIT principles into our Configuration Baseline Management, ensuring adherence to relevant standards and controls.
- Agile Methodologies: In agile environments, the baseline is often more fluid and iterative. My experience involves using agile principles such as continuous integration and continuous delivery (CI/CD) to manage changes to the baseline more frequently and with greater agility. This requires a more dynamic approach to change management and baseline updates.
The choice of methodology depends on the organization’s size, complexity, and regulatory requirements. I always tailor my approach to best suit the specific environment and project needs.
Q 18. How do you integrate Configuration Baseline Management with other IT processes?
Configuration Baseline Management doesn’t exist in isolation. It’s tightly integrated with various other IT processes to ensure a holistic approach to system management.
- Change Management: This is arguably the most critical integration. Changes to the baseline are managed through a formal change management process, ensuring proper approvals, testing, and documentation.
- Incident Management: When incidents occur, investigating the root cause often involves comparing the current configuration to the baseline to identify any deviations that might have contributed to the problem.
- Problem Management: Problem management aims at preventing future incidents. Analysis of incidents frequently highlights areas where the baseline needs improvement or updates to prevent recurrence.
- Release Management: New releases often necessitate updates to the baseline. Close collaboration between Configuration Management and Release Management is essential to ensure that baselines are updated to reflect the changes introduced by new releases.
- Security Management: Baseline management plays a critical role in security, ensuring that the system is configured according to security policies and standards. Regular audits and comparisons against security baselines are fundamental.
Effective integration across these processes is achieved through robust communication, collaboration, and the use of shared tools and databases, such as a CMDB.
Q 19. What are the challenges of managing Configuration Baselines in a large, complex environment?
Managing Configuration Baselines in large, complex environments presents several challenges. Think of trying to manage the blueprint for a massive skyscraper versus a small house – the scale and complexity drastically increase the difficulty.
- Scale and Complexity: The sheer number of CIs and their interdependencies make it difficult to maintain a completely accurate and up-to-date baseline. The risk of human error increases proportionally.
- Data Silos: Information about configuration items might be scattered across different departments or systems, making it challenging to get a holistic view of the entire environment.
- Integration Challenges: Integrating Configuration Baseline Management with other IT processes can be complex, requiring careful planning and coordination.
- Maintaining Accuracy: In dynamic environments, constantly updating the baseline to reflect changes can be a significant undertaking. Keeping up with the speed of changes is a constant battle.
- Automation Limitations: While automation helps, it can’t entirely replace human oversight. Manual intervention and expert judgment are still required for complex scenarios.
Addressing these challenges requires a well-defined process, robust tooling, and a strong emphasis on automation, collaboration, and continuous improvement.
Q 20. How do you prioritize changes to a Configuration Baseline?
Prioritizing changes to a Configuration Baseline involves a careful evaluation of several factors. It’s about recognizing the urgency and impact of each change.
- Urgency: How quickly does this change need to be implemented? Critical security patches or urgent bug fixes require immediate attention.
- Impact: What will be the impact of the change on the system and its users? High-impact changes require more thorough testing and review before implementation.
- Risk: What are the potential risks associated with the change? High-risk changes might require more rigorous testing and approvals.
- Business Value: Does the change align with business priorities? Changes that align with strategic goals and improve business operations should be prioritized.
A common approach is to use a prioritization matrix that combines urgency and impact to rank changes. A simple example would be a 2×2 matrix with high/low urgency and high/low impact, allowing for a straightforward categorization of each change request.
Q 21. What is your experience with version control systems in the context of Configuration Baselines?
Version control systems (VCS) are indispensable for effective Configuration Baseline Management. They provide a mechanism to track changes, revert to previous versions, and maintain a complete audit trail.
- Tracking Changes: VCS, such as Git or Subversion, allow you to meticulously track every change made to the baseline. This helps identify who made the change, when it was made, and why it was made. Think of it as a comprehensive historical log for your configuration.
- Rollback Capability: If a change introduces errors, a VCS allows you to easily revert to a previous, stable version of the baseline. This minimizes downtime and reduces the impact of errors.
- Collaboration and Branching: VCS supports collaborative efforts, allowing multiple individuals to work on changes simultaneously using branching. This promotes efficiency and allows for parallel development and testing of changes.
- Auditing: The complete audit trail provided by a VCS ensures compliance with regulatory requirements and provides valuable insights into configuration history.
In my experience, integrating a VCS into Configuration Baseline Management is crucial for maintaining the integrity, traceability, and overall effectiveness of the configuration process. This facilitates audits, problem solving, and the continuous improvement of the configuration management processes.
Q 22. Explain the importance of Configuration Identification in establishing a baseline.
Configuration Identification is the cornerstone of establishing a robust baseline. It’s the process of uniquely identifying all the components – hardware, software, documentation, even processes – that make up a system or service. Think of it as creating a detailed inventory of everything that needs to be managed. Without accurate identification, you can’t track changes, assess risks, or ensure consistency.
For example, a server might be identified by its serial number, IP address, operating system version, and installed applications. Each item is given a unique identifier, and its attributes are meticulously documented. This detailed identification allows us to track the specific version of software running on a particular server, crucial for troubleshooting and ensuring consistent functionality across multiple systems.
A strong Configuration Identification process is vital for establishing a baseline because it provides the foundation for comparison. Later, when changes occur, we can precisely compare the current state with the baseline, easily identifying deviations and ensuring that only approved changes are implemented.
Q 23. How do you handle the retirement or decommissioning of Configuration Items?
Retiring or decommissioning Configuration Items (CIs) requires a structured approach to maintain data integrity and prevent future issues. This process typically involves several steps. First, a thorough assessment is carried out to understand the impact of the decommissioning. This includes identifying any dependencies on the CI – for example, if other systems rely on this server for data storage or application access. Next, a plan is developed to safely remove the CI, which may involve data migration, backup, and testing.
Once the CI is decommissioned, its status must be updated in the CMDB (Configuration Management Database) – marking it as retired or decommissioned. This prevents accidental reuse or misidentification. Importantly, all related documentation is archived, preserving a record of its existence and lifecycle. This archival ensures traceability and aids in future audits or troubleshooting. Failing to properly retire a CI can lead to confusion, security vulnerabilities, or difficulty in understanding the current system configuration.
In one project, we decommissioned a legacy application server. Before decommissioning, we migrated all relevant data to a new server, documented the process meticulously, and then formally marked the legacy server as decommissioned in our CMDB. This ensured a smooth transition and maintained the accuracy of our configuration records.
Q 24. Describe your experience with Configuration Management Databases (CMDBs).
I have extensive experience working with CMDBs, using them as the central repository for all configuration information. I’ve worked with both commercial CMDB solutions like ServiceNow and Remedy, as well as custom-built solutions. My experience spans the entire CMDB lifecycle, from initial design and implementation to ongoing maintenance and improvement.
My responsibilities have included defining the CI attributes, establishing relationships between CIs, ensuring data accuracy, implementing reporting and analytics capabilities, and integrating the CMDB with other IT tools. A key aspect of my work has involved ensuring the CMDB’s data reflects the actual configuration of the system – this requires robust processes for data synchronization and validation.
For instance, in a recent project, we used a ServiceNow CMDB to track the configurations of hundreds of servers and applications. We used the CMDB to automate change management processes, generate reports for compliance audits, and improve incident resolution times. The structured information within the CMDB proved invaluable in maintaining consistency and ensuring we always had an accurate view of our infrastructure.
Q 25. How do you ensure compliance with regulatory requirements related to Configuration Baselines?
Ensuring compliance with regulatory requirements related to Configuration Baselines is critical. This involves a multi-faceted approach. First, we need to thoroughly understand the specific regulations that apply – this could include HIPAA for healthcare, PCI DSS for payment card processing, or industry-specific standards. Once understood, we map those requirements to our configuration items and define baseline controls to ensure adherence.
This process involves regularly auditing the configuration baseline to verify compliance and implementing corrective actions when deviations are detected. Documentation plays a crucial role, proving that the baseline is regularly audited and that all changes are properly authorized and tracked. Effective reporting is essential to demonstrate compliance to auditors.
For example, when dealing with PCI DSS, we would meticulously track all changes related to payment processing systems, documenting access controls, software versions, and security patches. This ensures that our systems meet the stringent requirements of the standard and that we can provide verifiable proof of compliance during audits.
Q 26. What is your experience with automated Configuration Baseline Management tools?
I have significant experience with automated Configuration Baseline Management tools. These tools streamline many aspects of the process, increasing efficiency and reducing the risk of human error. I’ve used tools that automate discovery, CI identification, change tracking, and reporting.
For example, I have experience with tools that automatically scan networks to identify hardware and software components, reducing the manual effort required for inventory management. Other tools I’ve used automatically compare the current configuration with the baseline, highlighting any deviations and facilitating prompt remediation. This automation helps us quickly identify potential security risks or compliance issues.
One specific tool I am familiar with integrates with our CMDB, providing real-time updates and automated alerts for critical changes. This allows for proactive management and reduces the risk of configuration drift – where the actual system configuration diverges from the documented baseline.
Q 27. How do you handle emergency changes that impact a Configuration Baseline?
Emergency changes, while necessary, require a controlled process to minimize disruption and maintain configuration integrity. A formal emergency change process, often defined within an incident management framework, is implemented. This process typically involves a rapid assessment of the impact, a quick approval by authorized personnel, and immediate implementation.
Crucially, all emergency changes must be documented, including the reason for the change, the steps taken, and the verification that the change resolved the issue. Following the emergency change, a post-incident review assesses what went wrong and how to prevent a similar situation in the future. This review might suggest changes to the baseline configuration to prevent recurrence.
For instance, if a server fails, an emergency change might involve quickly bringing up a redundant server. Following this, the event would be documented, a post-incident review completed, and potential baseline changes (like added monitoring) would be considered to improve system resilience.
Q 28. Describe your process for documenting and approving changes to a Configuration Baseline.
The process for documenting and approving changes to a configuration baseline is crucial for maintaining control and traceability. This typically involves a formal change management process. This process usually starts with a change request, detailing the proposed modification to the baseline. This request is then reviewed and approved or rejected according to pre-defined criteria. This ensures that only authorized changes are made.
Once approved, the change is implemented, and thorough testing is conducted to ensure that it doesn’t introduce new issues. The implementation is then documented, and the baseline is updated to reflect the changes. This updated baseline then undergoes a review to ensure its accuracy and consistency. The entire process is traceable through a change management system, which provides a complete audit trail of all modifications.
For example, suppose we want to upgrade the operating system on a server. A change request would be submitted, reviewed, and approved. After the upgrade, we’d document the process, test the server, update the baseline in the CMDB, and archive the change record for auditing purposes. This ensures a transparent and auditable change process, keeping the configuration baseline accurate and compliant.
Key Topics to Learn for Configuration Baseline Management Interview
- Defining Configuration Baselines: Understand the different types of baselines (functional, allocated, product) and their purpose within the software development lifecycle (SDLC).
- Baseline Establishment and Change Management: Learn the processes involved in creating, approving, and managing changes to established baselines. Discuss the importance of formal change control boards and processes.
- Configuration Item (CI) Identification and Control: Explore methods for identifying and tracking CIs throughout their lifecycle. Understand version control systems and their role in managing CI versions.
- Version Control and Branching Strategies: Discuss various branching strategies (e.g., Gitflow) and their impact on baseline management. Explain how to manage concurrent development efforts within a baseline framework.
- Baseline Verification and Validation: Understand the processes involved in verifying that a baseline meets its requirements and validating its suitability for its intended purpose. Discuss techniques for auditing baselines.
- Tools and Technologies: Familiarize yourself with common tools used for configuration baseline management, such as CMDBs (Configuration Management Databases) and related software.
- Risk Management in Configuration Baseline Management: Understand how to identify and mitigate risks associated with baseline changes and deviations.
- Practical Application: Prepare examples of how you’ve applied these concepts in previous roles, highlighting your problem-solving skills and ability to manage complex configurations.
- Problem-Solving Approach: Practice describing your approach to resolving conflicts and managing unexpected changes to baselines. Showcase your ability to think critically and proactively.
Next Steps
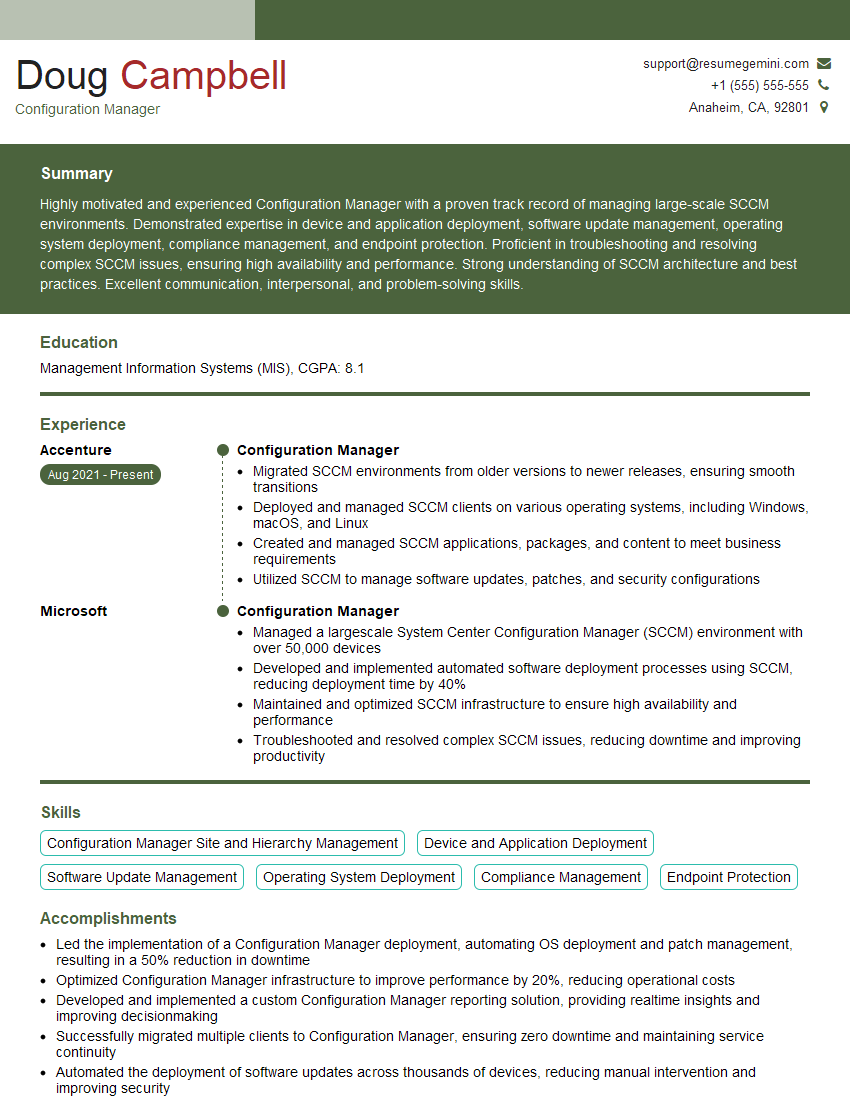
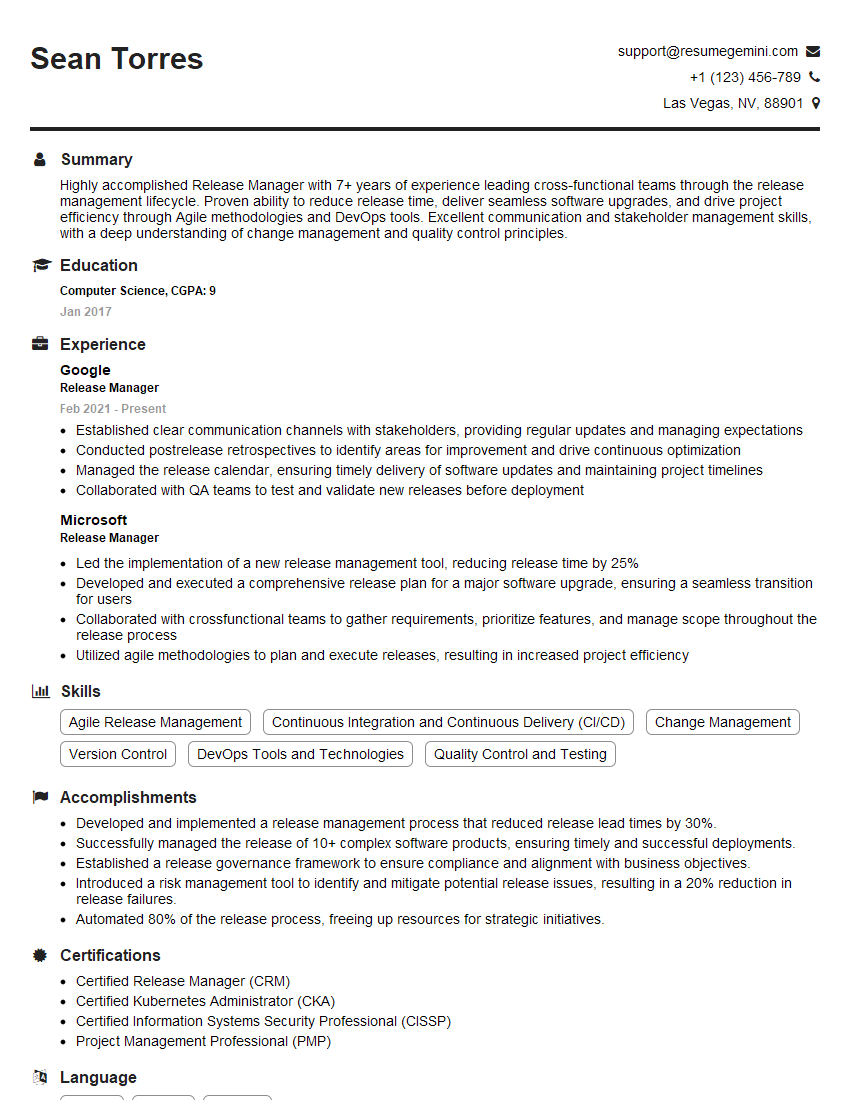
Mastering Configuration Baseline Management is crucial for advancing your career in IT and demonstrates your expertise in managing complex systems. A strong understanding of these principles significantly increases your value to potential employers. To maximize your job prospects, it’s vital to create an ATS-friendly resume that effectively showcases your skills and experience. ResumeGemini is a trusted resource that can help you build a professional and impactful resume tailored to the specific requirements of Configuration Baseline Management roles. Examples of resumes tailored to this field are available through ResumeGemini to guide you in creating a compelling application.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good