Feeling uncertain about what to expect in your upcoming interview? We’ve got you covered! This blog highlights the most important Cryptography Fundamentals interview questions and provides actionable advice to help you stand out as the ideal candidate. Let’s pave the way for your success.
Questions Asked in Cryptography Fundamentals Interview
Q 1. Explain the difference between symmetric and asymmetric encryption.
Symmetric and asymmetric encryption are two fundamental approaches to securing data. The core difference lies in the number of keys used.
Symmetric Encryption: Uses a single, secret key to both encrypt and decrypt data. Think of it like a secret codebook – both the sender and receiver need the same book to encode and decode messages. Examples include AES and DES. This method is fast and efficient but poses a key distribution challenge: how do you securely share that single secret key with the intended recipient?
Asymmetric Encryption: Employs two keys: a public key (freely shared) and a private key (kept secret). The public key is used to encrypt data, while only the corresponding private key can decrypt it. This elegantly solves the key distribution problem. RSA is a prime example of this type of encryption.
- Analogy: Imagine a mailbox with a public slot (public key) where anyone can drop a letter (encrypted message). Only the recipient who holds the key to the private compartment (private key) can retrieve the letter (decrypt the message).
In summary, symmetric encryption is faster but requires secure key exchange, while asymmetric encryption is slower but offers inherent key management advantages.
Q 2. Describe the RSA algorithm and its key components.
The RSA algorithm, named after its inventors Rivest, Shamir, and Adleman, is a widely used public-key cryptosystem. Its security relies on the computational difficulty of factoring large numbers.
- Key Generation: The process begins by selecting two large prime numbers, p and q. Their product, n = p * q, forms the modulus, a crucial component of both the public and private keys. Other calculations, involving Euler’s totient function, determine the public exponent (e) and the private exponent (d).
- Public Key: The pair (n, e) constitutes the public key and can be distributed freely.
- Private Key: The pair (n, d) is the private key and must be kept secret.
- Encryption: To encrypt a message M, it’s raised to the power of the public exponent e, modulo n:
C = Me mod n, where C is the ciphertext. - Decryption: The ciphertext C is raised to the power of the private exponent d, modulo n, to recover the original message:
M = Cd mod n.
The security relies on the fact that while it’s easy to compute n from p and q, it’s computationally infeasible to factor n back into p and q for sufficiently large primes. This difficulty is the foundation of RSA’s security.
Q 3. What are the advantages and disadvantages of AES and DES?
AES (Advanced Encryption Standard) and DES (Data Encryption Standard) are both symmetric block ciphers, meaning they encrypt data in fixed-size blocks. However, they differ significantly in their key sizes, block sizes, and overall security.
AES Advantages:
- Stronger Security: AES has larger key sizes (128, 192, or 256 bits) compared to DES’s 56 bits, making it far more resistant to brute-force attacks.
- Higher Efficiency: Modern hardware and software implementations of AES are highly optimized for speed and performance.
- Wider Adoption: AES is the current standard and is widely adopted globally.
AES Disadvantages:
- Complexity: The implementation can be more complex than DES.
DES Advantages:
- Simplicity: DES is relatively simple to understand and implement.
DES Disadvantages:
- Weak Security: The 56-bit key size makes DES highly vulnerable to brute-force attacks. It is considered insecure for modern applications.
- Obsolete: DES has been largely superseded by AES.
In essence, AES is a modern, secure, and efficient replacement for the outdated and insecure DES.
Q 4. Explain the concept of a digital signature and its applications.
A digital signature is a cryptographic technique used to verify the authenticity and integrity of a digital message or document. It’s analogous to a handwritten signature, but with much stronger security guarantees.
How it Works: The sender uses their private key to create a digital signature of the message. This signature is then attached to the message. The recipient uses the sender’s public key to verify the signature. If the verification succeeds, it confirms that the message originated from the claimed sender and hasn’t been tampered with.
Applications:
- Secure Email: Verifying the sender’s identity and preventing message forgery.
- Software Distribution: Ensuring that downloaded software hasn’t been modified maliciously.
- Digital Certificates: Used in SSL/TLS for secure web browsing.
- Transaction Security: Verifying the authenticity of financial transactions.
In essence, digital signatures provide non-repudiation (the sender cannot deny sending the message), authentication (verifying the sender’s identity), and data integrity (ensuring the message hasn’t been altered).
Q 5. How does a hash function work, and what are its properties?
A hash function is a one-way cryptographic function that takes an input of arbitrary size (the message) and produces a fixed-size output called a hash value or digest. This process is deterministic; the same input will always produce the same output.
How it Works: The function applies a series of complex mathematical operations to the input, creating a unique and seemingly random hash value. Even a tiny change in the input results in a significantly different hash value.
Properties of a Good Hash Function:
- Collision resistance: It’s computationally infeasible to find two different inputs that produce the same hash value.
- Pre-image resistance: Given a hash value, it’s computationally infeasible to find the original input that produced it.
- Second pre-image resistance: Given an input and its hash value, it’s computationally infeasible to find a different input that produces the same hash value.
- Deterministic: The same input always produces the same output.
Applications:
- Password storage: Storing password hashes instead of plain text passwords.
- Data integrity: Verifying that data hasn’t been altered.
- Digital signatures: Used as part of the signing process.
- Blockchain technology: Used to link blocks together securely.
Q 6. What is a collision in cryptography, and why is it important?
In cryptography, a collision refers to the scenario where two different inputs produce the same hash value. This is a critical concern because it can compromise the security of systems that rely on hash functions.
Why it’s Important: A collision weakens the security of a hash function because it makes it easier to forge data or create malicious inputs that produce the same hash as a legitimate input. For example, if a collision is found in a system used for digital signatures, an attacker could potentially create a fraudulent document with the same hash value as a genuine document, thereby bypassing the verification process.
Significance: The strength of a hash function is largely determined by its resistance to collisions. Good hash functions should make it computationally infeasible to find collisions, even with significant computational resources.
Q 7. Explain the concept of public key infrastructure (PKI).
Public Key Infrastructure (PKI) is a system for creating, managing, distributing, using, storing, and revoking digital certificates and managing public-key cryptography. It’s a crucial component of securing online communications and transactions.
Key Components:
- Certificate Authority (CA): A trusted third party that issues digital certificates, essentially vouching for the authenticity of public keys.
- Registration Authority (RA): An optional intermediary that verifies the identity of certificate applicants before the CA issues a certificate.
- Certificate Revocation List (CRL): A list of certificates that have been revoked (e.g., due to compromise).
- Digital Certificates: These contain the public key, identity information of the owner, and the CA’s digital signature. They are the fundamental building blocks of PKI.
How it Works: A user (or device) requests a certificate from a CA. The CA verifies the user’s identity and issues a certificate containing their public key. This certificate can then be used to verify the user’s identity in various applications, such as secure email, website authentication (HTTPS), and software distribution. The CRL helps ensure that only valid certificates are used.
In essence, PKI provides a trusted framework for managing and verifying digital identities and public keys, enabling secure online interactions.
Q 8. Describe the different types of cryptographic attacks.
Cryptographic attacks aim to break the security of a cryptographic system. They can be broadly categorized into several types, often targeting different aspects of the system’s design or implementation.
- Ciphertext-only attacks: The attacker only has access to the encrypted message (ciphertext). They try to deduce the plaintext or the key by analyzing patterns and frequencies in the ciphertext. Think of someone intercepting a coded message without knowing anything about the code itself.
- Known-plaintext attacks: The attacker has access to both the ciphertext and the corresponding plaintext. This allows them to analyze the relationship between the two and potentially derive the key. Imagine intercepting a coded message and also having access to a decoded version of a similar message.
- Chosen-plaintext attacks: The attacker can choose the plaintext and obtain its corresponding ciphertext. This is a more powerful attack than a known-plaintext attack, allowing for more targeted analysis. This is like submitting your own test message into the encrypted system and seeing how it gets encrypted.
- Chosen-ciphertext attacks: The attacker can choose the ciphertext and obtain its corresponding plaintext. This allows them to analyze the decryption process and find weaknesses. An analogy would be choosing a decrypted message and seeing what happens when you try to decrypt it a second time.
- Side-channel attacks: These attacks exploit information leaked during the cryptographic operations, such as timing, power consumption, or electromagnetic emissions. These aren’t direct attacks on the algorithm itself but rather on the implementation. Think of inferring data from how long a computer takes to process encrypted information.
- Brute-force attacks: The attacker tries every possible key until the correct one is found. This is computationally intensive and its effectiveness depends on the key size. This is like trying every possible combination to a lock.
Understanding these attack types is crucial for designing and implementing secure cryptographic systems.
Q 9. What are the security implications of using weak random number generators?
Weak random number generators (RNGs) have serious security implications because they produce predictable or easily guessable sequences of numbers. Cryptography heavily relies on randomness for key generation, nonce generation, and other critical operations. If the randomness is compromised, the entire security of the system can be at risk.
- Predictable Keys: If keys are generated using a weak RNG, an attacker might be able to predict the keys, compromising the confidentiality and integrity of the data. This is akin to using the same combination for every lock.
- Vulnerable Nonces: Nonces (numbers used once) are essential for many cryptographic protocols. A weak RNG can lead to nonce reuse, allowing an attacker to exploit vulnerabilities in cryptographic algorithms, like in some versions of TLS/SSL protocols.
- Easily Guessable Numbers: The predictability of the numbers generated by a weak RNG can lead to various attacks, including those that leverage patterns or biases in the sequence.
Therefore, it’s imperative to use cryptographically secure random number generators (CSPRNGs) in any security-sensitive application. CSPRNGs are designed to produce sequences that are statistically random and unpredictable, even given some knowledge of previous outputs.
Q 10. Explain the concept of key exchange and describe the Diffie-Hellman key exchange.
Key exchange is the process by which two parties securely establish a shared secret key over an insecure channel. This shared key can then be used for symmetric encryption, which is generally much faster than asymmetric encryption. The Diffie-Hellman key exchange is a widely used method for achieving this.
Diffie-Hellman Key Exchange: It’s based on the mathematical properties of modular arithmetic. Let’s break it down:
- Public Parameters: Two large prime numbers,
p(a prime modulus) andg(a generator) which is a primitive root modulop, are publicly known. - Private Keys: Each party (Alice and Bob) secretly chooses a private key: Alice chooses
aand Bob choosesb. - Public Keys: Each party computes their public key: Alice computes
A = ga mod pand Bob computesB = gb mod p. They then exchange these public keys over an insecure channel. - Shared Secret: Both Alice and Bob can now compute the same shared secret: Alice computes
s = Ba mod pand Bob computess = Ab mod p. Mathematically, these calculations are equivalent tos = gab mod p.
The security of Diffie-Hellman relies on the computational difficulty of the discrete logarithm problem. Even if an attacker intercepts the exchanged public keys A and B, it’s computationally infeasible to determine the shared secret s without knowing the private keys a and b.
In practice, Diffie-Hellman is often used in conjunction with other cryptographic protocols, such as TLS/SSL, to establish secure connections over the internet.
Q 11. What is a digital certificate, and how does it work?
A digital certificate is an electronic document that verifies the identity of a website or an individual. Think of it as an online passport or driver’s license. It contains information like the owner’s name (website or individual), public key, and validity period. Certificates are issued by Certificate Authorities (CAs), trusted third parties.
How it Works:
- Certificate Generation: A website or individual requests a certificate from a CA. The CA verifies the identity of the applicant.
- Public Key Inclusion: The applicant’s public key is embedded within the certificate.
- Digital Signature: The CA digitally signs the certificate using its private key. This signature confirms the certificate’s authenticity.
- Certificate Distribution: The signed certificate is then provided to the applicant.
- Verification: When a user connects to a website, the user’s browser retrieves the website’s certificate. The browser then verifies the certificate’s signature using the CA’s public key. If the signature is valid and the certificate’s other details check out, the user trusts the website’s identity and its public key.
Real-world application: Every time you access a website with HTTPS, you’re implicitly relying on digital certificates to authenticate the website’s identity and to securely exchange information.
Q 12. How does HTTPS secure web communication?
HTTPS (Hypertext Transfer Protocol Secure) secures web communication by using TLS/SSL (Transport Layer Security/Secure Sockets Layer) protocol. This protocol leverages several cryptographic techniques to protect data integrity and confidentiality.
- TLS Handshake: The initial connection involves a handshake where the server presents its digital certificate to the client (your browser). This certificate verifies the server’s identity.
- Symmetric Encryption: Once the server’s identity is verified, both the client and the server establish a shared secret key using a key exchange mechanism, such as Diffie-Hellman. This shared key is then used for symmetric encryption of the actual web traffic (data exchange).
- Data Integrity: Message Authentication Codes (MACs) or digital signatures are used to ensure data integrity, preventing unauthorized modification of the exchanged data. This confirms that the data received is exactly what was sent.
- Confidentiality: Symmetric encryption ensures that only the client and server can decipher the exchanged data, protecting it from eavesdropping.
In essence, HTTPS prevents eavesdropping, tampering, and forgery of web communication by using a combination of digital certificates, key exchange, symmetric encryption, and message authentication.
Q 13. Explain the concept of elliptic curve cryptography (ECC).
Elliptic Curve Cryptography (ECC) is a public-key cryptography system based on the algebraic structure of elliptic curves over finite fields. It offers similar functionality to RSA but with significantly smaller key sizes for the same level of security. This makes it particularly attractive for resource-constrained devices like smartphones and embedded systems.
Concept: ECC relies on the difficulty of solving the Elliptic Curve Discrete Logarithm Problem (ECDLP). Given two points P and Q on an elliptic curve, where Q = kP (k is a scalar multiplier), finding k given P and Q is computationally hard. This hardness forms the basis of ECC security.
Key Generation: A private key is a random integer k. The corresponding public key is calculated as Q = kP, where P is a generator point on the elliptic curve.
Advantages over RSA: For comparable security levels, ECC requires much smaller key sizes than RSA, leading to faster computations and reduced storage requirements. This makes it more efficient for applications with limited processing power and memory.
Applications: ECC is widely used in various applications including TLS/SSL, digital signatures, and cryptocurrencies like Bitcoin and Ethereum (although Bitcoin uses a different, older form of elliptic curve cryptography).
Q 14. What is a nonce, and why is it important in cryptography?
A nonce is a random number used only once in a cryptographic operation. Imagine it as a unique, one-time password. Its primary purpose is to prevent replay attacks.
Importance: Nonces enhance security by ensuring that even if an attacker intercepts a message and the same message is sent later, the cryptographic process won’t produce the same output. This prevents replay attacks, where an attacker intercepts a message and retransmits it to achieve malicious goals.
Examples: Nonces are used in various protocols like TLS/SSL handshakes, to prevent attackers from replaying captured requests. They are also frequently used in digital signatures and other cryptographic constructions to introduce randomness and enhance security.
Without nonces, an attacker could potentially replay a previously captured encrypted message or signature, undermining the security and integrity of the system.
Q 15. Describe the concept of message authentication codes (MACs).
Message Authentication Codes (MACs) are cryptographic checksums used to verify both the integrity and authenticity of data. Think of it like a digital fingerprint for your message. A MAC ensures that the message hasn’t been tampered with during transmission and that it actually originated from the claimed sender. Unlike digital signatures, MACs don’t require public key cryptography; they use a shared secret key known only to the sender and receiver.
Here’s how it works: The sender calculates a MAC using a secret key and the message. This MAC is then appended to the message and sent to the receiver. The receiver, using the same secret key, independently calculates the MAC for the received message. If the calculated MAC matches the received MAC, the message is deemed authentic and unaltered. If they don’t match, it indicates either tampering or a transmission error.
Example: Imagine sending a financial transaction over a network. Using a MAC ensures that the amount, recipient, and other details haven’t been modified during transit, protecting against fraud. Popular MAC algorithms include HMAC (Hash-based Message Authentication Code), which uses a cryptographic hash function like SHA-256 along with a secret key.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. What are the differences between confidentiality, integrity, and authentication?
Confidentiality, integrity, and authentication are three fundamental pillars of information security, each addressing a different aspect of data protection:
- Confidentiality: This ensures that only authorized parties can access sensitive information. Think of it like a locked safe – only those with the key can open it. Encryption is the primary mechanism for achieving confidentiality, preventing unauthorized individuals from reading the data.
- Integrity: This guarantees that data remains unchanged and accurate during transmission and storage. It ensures that no unauthorized modifications, deletions, or insertions have occurred. Hashing and digital signatures are common techniques to ensure data integrity.
- Authentication: This verifies the identity of the sender or the source of information. It assures you that the message truly came from the claimed sender and wasn’t forged. Techniques like passwords, digital certificates, and biometrics are used for authentication.
Illustrative Example: Consider an online banking transaction. Confidentiality protects the account details from being intercepted. Integrity ensures that the transaction amount hasn’t been altered. Authentication verifies that you are indeed the legitimate account holder initiating the transaction.
Q 17. Explain the principles of Kerberos authentication.
Kerberos is a network authentication protocol that uses symmetric key cryptography to provide strong authentication for client-server applications. Imagine it as a trusted third-party ticket granting service that acts as a secure intermediary between clients and servers.
The process involves:
- Ticket-Granting Ticket (TGT): The client initially authenticates with the Kerberos Key Distribution Center (KDC) using a password or other credentials. The KDC verifies the client’s identity and issues a TGT, which is an encrypted ticket that grants the client access to other services.
- Service Ticket: When the client wants to access a specific server, it presents its TGT to the KDC. The KDC then issues a service ticket, which is an encrypted ticket granting access to that specific service. This ticket contains a session key that the client and server will use for secure communication.
- Mutual Authentication: The client presents the service ticket to the server. The server decrypts the ticket using a secret key it shares with the KDC and verifies the client’s identity. The server and client then use the session key for secure communication.
Benefits of Kerberos: Strong mutual authentication, single sign-on capability (allowing access to multiple services with a single login), and protection against replay attacks.
Q 18. What are some common vulnerabilities in cryptographic systems?
Cryptographic systems, despite their strength, are susceptible to several vulnerabilities:
- Weak or compromised keys: Insufficient key length, poorly generated keys, or keys exposed through vulnerabilities are major risks. Reusing keys is a critical error.
- Implementation flaws: Bugs in the code implementing the cryptographic algorithm can create exploitable weaknesses.
- Side-channel attacks: These attacks exploit information leaked during cryptographic operations, such as timing, power consumption, or electromagnetic emissions.
- Cryptographic algorithm weaknesses: Advances in cryptanalysis can reveal weaknesses in algorithms, rendering them vulnerable.
- Social engineering: Tricking users into revealing their passwords or other sensitive information remains a significant threat.
Example: The Heartbleed bug in OpenSSL was a critical implementation flaw that allowed attackers to steal sensitive data from servers.
Q 19. How can you protect against side-channel attacks?
Side-channel attacks exploit information leaked during cryptographic operations. Protecting against them requires a multi-layered approach:
- Constant-time algorithms: Designing algorithms that take the same amount of time to execute regardless of the input data prevents timing attacks.
- Power analysis countermeasures: Techniques like masking and shielding can reduce the information leaked through power consumption.
- Electromagnetic shielding: Protecting hardware from electromagnetic emissions can mitigate electromagnetic attacks.
- Secure hardware implementations: Using hardware specifically designed for cryptographic operations can offer additional protection against side-channel attacks.
- Regular security audits and code reviews: Identifying and fixing potential vulnerabilities in code is crucial.
Example: A constant-time implementation of an encryption algorithm ensures that the execution time is independent of the secret key, preventing attackers from inferring key information from timing differences.
Q 20. Explain the concept of homomorphic encryption.
Homomorphic encryption allows computations to be performed on encrypted data without decryption. Imagine having a locked box where you can perform calculations directly on the contents without ever opening the box. This has enormous implications for privacy-preserving computation.
There are different types of homomorphic encryption, including:
- Partially homomorphic encryption: Supports only a limited set of operations (e.g., only addition or only multiplication).
- Somewhat homomorphic encryption: Supports a limited number of operations before the ciphertext becomes too large or noisy.
- Fully homomorphic encryption (FHE): Supports arbitrary computations on encrypted data.
Applications: Secure cloud computing, privacy-preserving data analysis, and secure multi-party computation.
Challenges: Fully homomorphic encryption is computationally expensive and still under active research. Partially homomorphic schemes are more practical but have limitations on the type of computations they can support.
Q 21. Describe the challenges of implementing secure key management.
Secure key management is crucial for the overall security of any cryptographic system. The challenges include:
- Key generation and storage: Generating strong, random keys and securely storing them without compromising confidentiality is vital. Poor key generation practices can lead to weak keys susceptible to brute-force attacks.
- Key distribution: Safely distributing keys between parties without interception or modification requires secure channels and protocols.
- Key rotation: Regular key rotation is essential to mitigate the risk of key compromise. Outdated keys should be retired and securely destroyed.
- Key revocation: A mechanism to quickly invalidate compromised keys is needed to prevent further misuse. This often involves updating key distribution lists or employing certificate revocation lists.
- Key lifecycle management: The entire process, from generation and distribution to revocation and destruction, needs to be carefully managed and audited.
Example: Failure to properly rotate keys can lead to the long-term exposure of sensitive data if a key is compromised.
Q 22. What are the security considerations for cloud-based cryptography?
Cloud-based cryptography introduces unique security challenges compared to on-premise systems. The primary concern revolves around data security while it’s both in transit and at rest. Think of it like this: you’re entrusting your valuable jewels (data) to a highly secure vault (cloud provider), but you need to ensure the vault itself is impenetrable and the transport to and from the vault is secure.
Data breaches: A compromise of the cloud provider’s infrastructure can expose your encrypted data. Robust access controls, multi-factor authentication, and strong encryption are essential. Imagine a burglar gaining access to the entire vault – your jewels are still at risk even if individually locked.
Key management: Securely managing encryption keys is paramount. Losing or compromising keys renders your data useless, essentially losing the combination to your vault. Key management solutions, such as Hardware Security Modules (HSMs), are crucial to mitigate this risk.
Data residency and compliance: Depending on your industry and location, regulations may dictate where your data must reside. Cloud providers need to be compliant with those regulations. This is like making sure the vault is located in a permitted zone according to the law.
Vendor lock-in: Choosing a cloud provider means relying on their security practices. Changing providers can be complex and potentially risky. You need to ensure you can easily move your encrypted data to a different vault if necessary.
Insider threats: Malicious insiders within the cloud provider or your own organization could compromise your data. Strong auditing and monitoring are essential, much like having security cameras in and around your vault to deter and detect theft.
Q 23. Explain the concept of zero-knowledge proofs.
Zero-knowledge proofs (ZKPs) allow one party (the prover) to prove to another party (the verifier) that a statement is true, without revealing any information beyond the truth of the statement itself. Imagine trying to prove you know the solution to a complex puzzle without actually showing the solution. That’s the essence of a ZKP.
For example, imagine you need to prove you possess a specific digital signature without revealing the private key. A ZKP allows you to prove ownership without disclosing the private key, making it highly secure. This is crucial for things like blockchain transactions where the privacy of the involved parties is needed.
ZKPs are built upon cryptographic techniques that leverage mathematical properties to construct a verifiable proof. There are various types of ZKPs, including:
Interactive ZKPs: Require multiple rounds of interaction between the prover and verifier.
Non-interactive ZKPs: Only require a single interaction, making them more practical in many applications.
ZKPs find applications in various areas such as anonymous authentication, blockchain privacy, and secure multi-party computation.
Q 24. How can you evaluate the security of a cryptographic algorithm?
Evaluating the security of a cryptographic algorithm is a complex process involving both theoretical analysis and practical testing. It’s not a simple pass/fail assessment, but rather a continuous evaluation and improvement process.
Cryptanalysis: Researchers attempt to break the algorithm by finding vulnerabilities or weaknesses. This involves analyzing the algorithm’s mathematical structure and searching for patterns or exploitable flaws. This is like trying to crack a safe by studying its construction and mechanisms.
Peer review: The algorithm’s design and analysis are subjected to scrutiny by experts in the field. This is crucial to identify any overlooked weaknesses before deployment. Think of this as a panel of expert locksmiths reviewing the safe’s design.
Implementation analysis: The way the algorithm is implemented in software or hardware can introduce vulnerabilities. Secure coding practices and careful implementation are crucial. A perfectly designed safe can be useless if it’s installed improperly or has weak surrounding security.
Practical testing: The algorithm is tested against various attacks and scenarios, often involving large datasets and considerable computational resources. This involves simulating real-world attack scenarios.
Standardization: Algorithms that undergo rigorous evaluation and achieve widespread adoption through standardization bodies (like NIST) are generally considered more secure. This adds a layer of trust and community validation, like a safe that has been certified by a reputable testing organization.
It’s important to note that even widely used algorithms can be vulnerable to new attacks as computing power and cryptanalytic techniques advance. Constant vigilance and updates are necessary.
Q 25. What is a block cipher, and how does it differ from a stream cipher?
Both block ciphers and stream ciphers are fundamental building blocks in cryptography used for encryption, but they operate differently.
Block cipher: Encrypts data in fixed-size blocks. Imagine having a series of small safes, each holding a fixed amount of jewels. The same key is used to lock/unlock each safe.
Stream cipher: Encrypts data one bit or byte at a time, using a keystream generated from a secret key. Imagine a continuous conveyor belt of jewels moving past a machine that continuously changes its encryption method based on a secret code.
Key Differences:
Block size: Block ciphers operate on fixed-size blocks (e.g., 64 bits, 128 bits), while stream ciphers process data bit by bit or byte by byte.
Modes of operation: Block ciphers require various modes of operation (e.g., CBC, CTR) to handle data larger than the block size, introducing complexities. Stream ciphers usually don’t need such modes.
Error propagation: Errors in block cipher encryption affect only a single block. In stream ciphers, an error can propagate.
Efficiency: Stream ciphers are generally faster for encrypting large amounts of data due to their simpler architecture.
Examples of block ciphers include AES and DES, while examples of stream ciphers include RC4 (now considered insecure) and ChaCha20.
Q 26. Explain the concept of digital rights management (DRM).
Digital Rights Management (DRM) is a set of technologies, processes, and business models that are used to control access to digital content and restrict its usage. Think of DRM as a sophisticated system of locks and keys designed to protect copyrighted material in the digital world.
DRM mechanisms aim to prevent unauthorized copying, distribution, and use of digital content like music, movies, ebooks, and software. Methods used include:
Encryption: The content is encrypted, and only authorized users with decryption keys can access it.
Watermarking: Identifying information is embedded into the content to trace unauthorized copies.
Access control: Various mechanisms restrict access based on user permissions, device limitations, or time-based constraints.
Licensing: Users agree to terms and conditions that govern how they can use the content.
However, DRM is a complex and often controversial topic. While it aims to protect intellectual property, it can also restrict legitimate use and create user inconvenience. Finding the balance between protecting content creators and ensuring fair use for consumers is a continuing challenge.
Q 27. Describe the role of cryptography in blockchain technology.
Cryptography plays a crucial role in securing the integrity and trust of blockchain technology. It’s the foundation upon which the entire system is built; essentially, it’s the locks and keys that keep the entire digital ledger secure.
Hashing: Cryptographic hash functions create unique fingerprints (hashes) of data blocks. Changes to the data, however small, result in entirely different hashes, ensuring data integrity. This prevents tampering with the blockchain.
Digital signatures: Used to verify the authenticity and integrity of transactions. Each transaction is digitally signed by the sender, proving ownership and preventing unauthorized alterations. This assures the parties involved that the transactions are genuinely theirs and haven’t been modified.
Encryption: Can be used to protect sensitive information within transactions, ensuring privacy. While some blockchains operate transparently, encryption allows for confidential transactions.
Consensus mechanisms: Cryptographic protocols (like Proof-of-Work or Proof-of-Stake) are used to ensure agreement among participants on the state of the blockchain, preventing fraudulent entries. These algorithms help verify the validity of new blocks of data.
Without cryptography, blockchain would not be secure or trustworthy. The tamper-proof nature of the blockchain relies entirely on the strength and security of the cryptographic algorithms used.
Q 28. Discuss the implications of quantum computing on existing cryptographic algorithms.
Quantum computing poses a significant threat to many widely used cryptographic algorithms. Quantum computers, with their vastly superior computational power, could potentially break widely used public-key cryptography, like RSA and ECC, upon which much of our online security relies.
Shor’s algorithm, a quantum algorithm, can factor large numbers exponentially faster than classical algorithms. This directly threatens RSA, which relies on the difficulty of factoring large numbers. Similarly, algorithms like ECC that rely on the difficulty of the discrete logarithm problem are vulnerable to quantum attacks.
The implications are severe: online banking, secure communications, digital signatures, and many other security measures could be compromised. The cryptographic community is actively researching and developing post-quantum cryptography (PQC) algorithms that are resistant to attacks from quantum computers. These algorithms are designed to be secure even against the computing power of future quantum computers.
Transitioning to PQC is a major undertaking and requires careful planning and implementation. It is not a quick fix, but rather a long-term process involving standardizing new algorithms, updating existing systems, and developing secure implementations.
Key Topics to Learn for Cryptography Fundamentals Interview
- Symmetric-key Cryptography: Understand algorithms like AES and DES, including their strengths, weaknesses, and modes of operation. Consider practical applications in data-at-rest and in-transit protection.
- Asymmetric-key Cryptography: Grasp the principles behind RSA and ECC, focusing on key generation, encryption/decryption, and digital signatures. Explore their roles in secure communication and authentication.
- Hashing Algorithms: Learn about SHA-256, SHA-3, and other hashing functions, their collision resistance properties, and applications in data integrity verification and digital signatures.
- Digital Certificates and Public Key Infrastructure (PKI): Understand the concepts of certificate authorities, certificate chains, and how PKI secures online communication and transactions.
- Message Authentication Codes (MACs): Explore HMAC and other MAC algorithms and their role in ensuring data authenticity and integrity.
- Cryptographic Protocols: Familiarize yourself with TLS/SSL, SSH, and other protocols used to secure network communication. Understand their underlying cryptographic mechanisms.
- Number Theory and Algebra: Develop a solid understanding of modular arithmetic, prime numbers, and other mathematical foundations crucial for cryptography.
- Cryptanalysis and Attacks: Learn about common attacks on cryptographic systems, such as brute-force attacks, known-plaintext attacks, and side-channel attacks. This will enhance your understanding of security vulnerabilities.
- Security Models and Frameworks: Explore various security models (e.g., Bell-LaPadula) and frameworks (e.g., NIST Cybersecurity Framework) to understand the broader context of cryptographic applications.
Next Steps
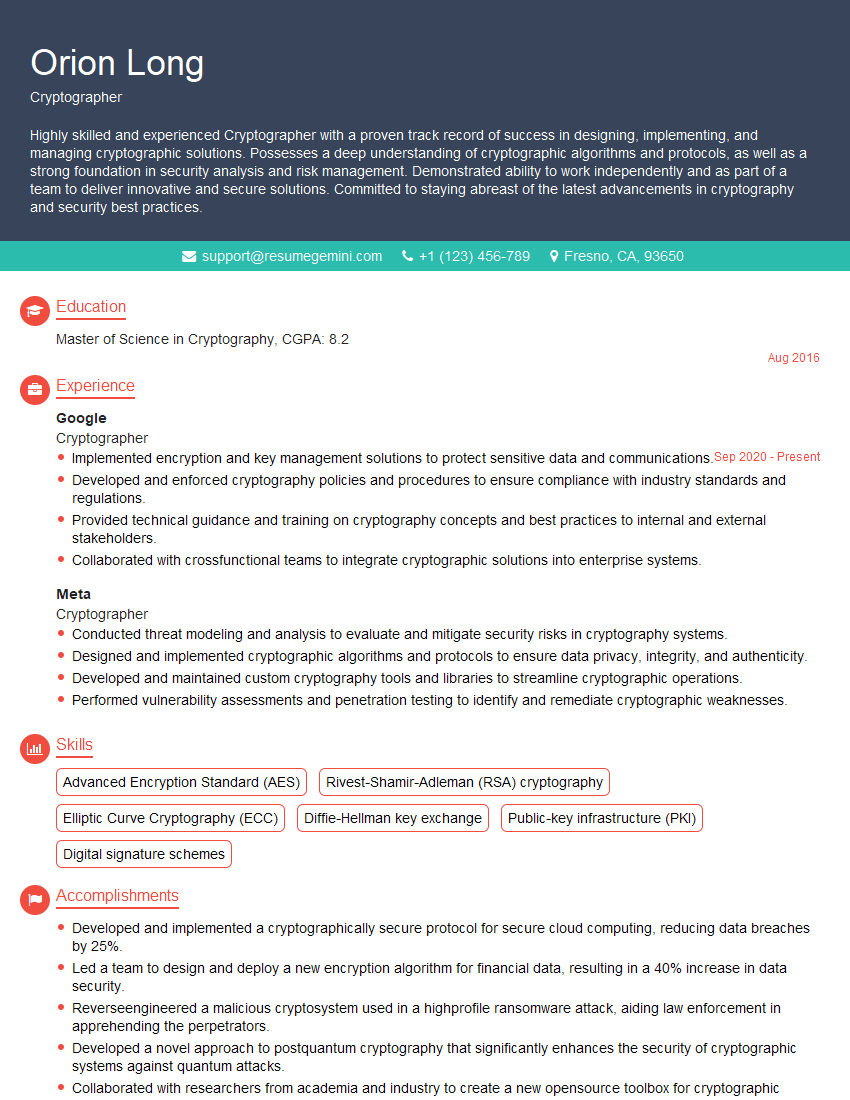
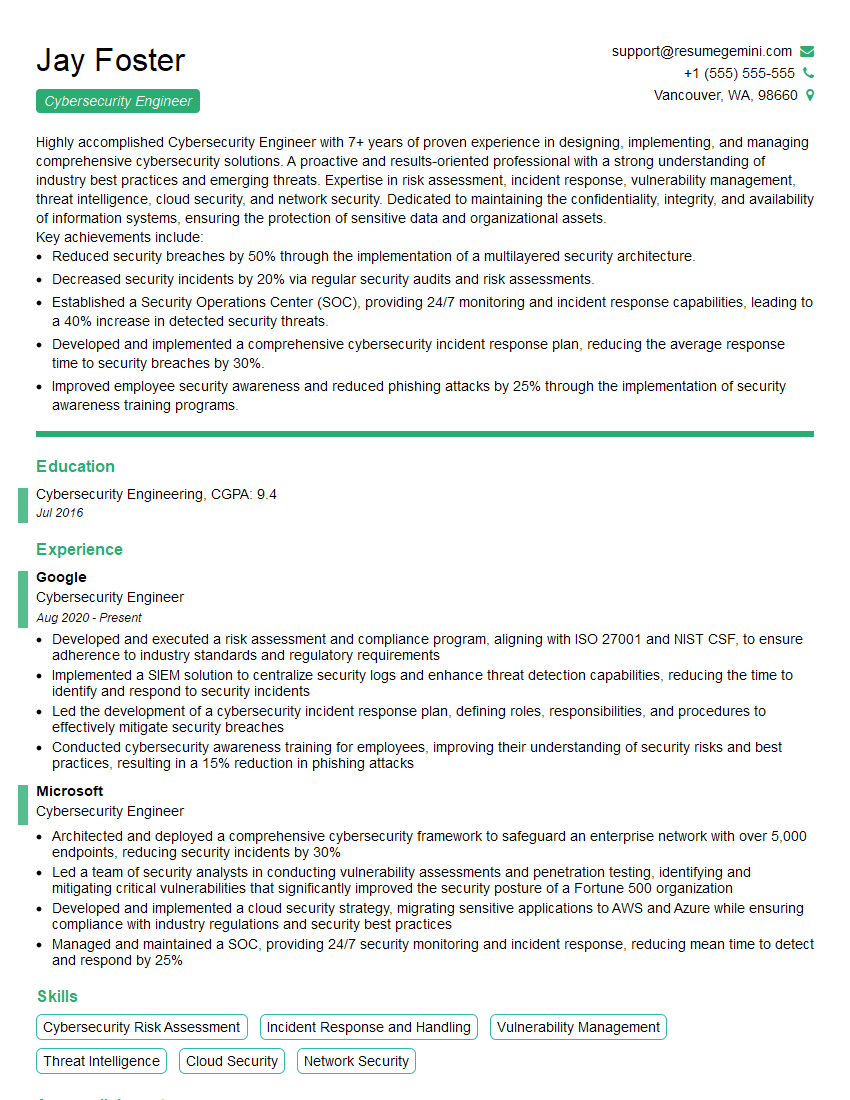
Mastering Cryptography Fundamentals is crucial for a successful career in cybersecurity, blockchain technology, and other related fields. A strong understanding of these concepts will significantly enhance your job prospects and open doors to exciting opportunities. To maximize your chances, create a compelling and ATS-friendly resume that highlights your skills and experience. ResumeGemini is a trusted resource that can help you build a professional and effective resume, ensuring your application stands out. Examples of resumes tailored to Cryptography Fundamentals are available to guide you.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good