The right preparation can turn an interview into an opportunity to showcase your expertise. This guide to Cryptology interview questions is your ultimate resource, providing key insights and tips to help you ace your responses and stand out as a top candidate.
Questions Asked in Cryptology Interview
Q 1. Explain the difference between symmetric and asymmetric encryption.
Symmetric and asymmetric encryption are two fundamental approaches to securing data, differing primarily in how they handle encryption and decryption keys.
Symmetric encryption uses the same secret key for both encrypting and decrypting data. Imagine a locked box; you need the same key to lock it (encrypt) and unlock it (decrypt). This is efficient and fast but presents a key distribution challenge – securely sharing the secret key between parties becomes a crucial vulnerability. Examples include AES (Advanced Encryption Standard) and DES (Data Encryption Standard).
Asymmetric encryption, also known as public-key cryptography, employs two distinct keys: a public key for encryption and a private key for decryption. Think of a mailbox with a slot (public key) where anyone can drop a letter (encrypted data). Only the recipient possessing the key to the mailbox (private key) can open it and read the letter (decrypt). This solves the key distribution problem as the public key can be openly shared, but it’s computationally more intensive than symmetric encryption. RSA (Rivest–Shamir–Adleman) and ECC (Elliptic Curve Cryptography) are prime examples.
In practice, often a hybrid approach is used, leveraging the speed of symmetric encryption for bulk data and the security of asymmetric encryption for key exchange.
Q 2. Describe the RSA algorithm and its security implications.
The RSA algorithm is a cornerstone of modern public-key cryptography. Its security rests on the difficulty of factoring large numbers. Specifically, it relies on the mathematical relationship between two large prime numbers.
- Key Generation: Two large prime numbers, p and q, are randomly selected. Their product, n = p * q, forms the modulus. Euler’s totient function, φ(n) = (p – 1)(q – 1), is calculated. A public exponent, e, is chosen such that 1 < e < φ(n) and e is coprime to φ(n). The private exponent, d, is then calculated such that e * d ≡ 1 (mod φ(n)).
- Encryption: The plaintext message, M, is encrypted as a ciphertext, C, using the public key (n, e):
C ≡ Me (mod n) - Decryption: The ciphertext, C, is decrypted back to the plaintext message, M, using the private key (n, d):
M ≡ Cd (mod n)
Security Implications: RSA’s security is directly tied to the difficulty of factoring the modulus n. If n can be factored efficiently, the private key d can be computed, compromising the system. Advances in quantum computing pose a significant threat to RSA’s long-term security as Shor’s algorithm can factor large numbers exponentially faster than classical algorithms. Therefore, key sizes need to be carefully chosen and regularly updated to maintain security.
Q 3. What are the strengths and weaknesses of AES encryption?
AES (Advanced Encryption Standard) is a widely used symmetric block cipher known for its robustness and performance.
Strengths:
- Security: AES has withstood extensive cryptanalysis and is considered highly secure for appropriately sized keys (128, 192, or 256 bits).
- Speed and Efficiency: It’s relatively fast and efficient, making it suitable for encrypting large amounts of data.
- Standardization: Its widespread adoption as a standard provides a consistent and well-understood encryption mechanism.
Weaknesses:
- Key Management: Like all symmetric algorithms, secure key distribution remains a challenge. Compromising the key compromises the entire encryption.
- Side-Channel Attacks: While the algorithm itself is strong, implementation vulnerabilities can lead to side-channel attacks, such as timing or power analysis attacks, revealing information about the key.
- Future Threats: Although currently secure, advancements in cryptanalysis or computing power could potentially weaken AES in the distant future.
The choice of key size is crucial. While 128-bit AES is sufficient for most applications, 256-bit AES offers greater security against future threats and is recommended for applications requiring long-term confidentiality.
Q 4. Explain the concept of a digital signature and its applications.
A digital signature is a cryptographic technique used to verify the authenticity and integrity of digital data. It’s analogous to a handwritten signature on a physical document.
How it Works: A digital signature uses a private key to create a unique ‘signature’ for a message. Anyone with the corresponding public key can verify the signature’s validity. The signature is not directly attached to the message, it is a result of applying a hash function on the message and then encrypting it using the private key.
Applications:
- Authentication: Verifying the identity of the sender.
- Non-repudiation: Preventing the sender from denying they sent the message.
- Integrity: Ensuring the message hasn’t been tampered with.
- Software Distribution: Verifying the authenticity of software downloads.
- Secure Email: Ensuring email messages haven’t been altered during transit.
- Digital Certificates: Used to verify the identity of websites and online services.
Digital signatures are essential for building trust and security in digital communication and transactions.
Q 5. How does a hash function work, and what are its properties?
A hash function is a one-way cryptographic function that takes an input of any size (e.g., a message, file, or password) and produces a fixed-size output called a hash value or digest.
How it Works: The function processes the input through a series of mathematical operations, resulting in a seemingly random hash value. Even a small change in the input will dramatically alter the hash value. This property is crucial for its various applications.
Properties of a Good Hash Function:
- Deterministic: The same input always produces the same output.
- One-way: It’s computationally infeasible to reverse the process and determine the input from the hash value.
- Collision-resistant: It’s extremely difficult to find two different inputs that produce the same hash value (collisions).
- Pre-image resistant: Given a hash value, it’s hard to find an input that produces that hash.
- Second pre-image resistant: Given an input and its hash, it’s hard to find a different input with the same hash.
Examples include SHA-256, SHA-3, and MD5 (although MD5 is now considered cryptographically broken due to discovered collisions).
Q 6. What is a collision in cryptography, and why is it significant?
In cryptography, a collision is when two different inputs produce the same hash value using a hash function. This is a significant concern because it compromises the integrity of the system.
Significance:
- Data Integrity: If collisions are found, it means that different data can have the same hash, making it impossible to reliably verify the integrity of data based on its hash. An attacker could potentially create a malicious file with the same hash as a legitimate file, allowing it to be passed as authentic.
- Digital Signatures: Collisions can be exploited to forge digital signatures. An attacker might create a different message with the same hash as a legitimate message, and then sign the malicious message with the victim’s private key.
The goal of designing a good hash function is to make finding collisions computationally infeasible. However, no hash function is perfectly collision-resistant; the security depends on the difficulty of finding collisions, which is influenced by the hash function’s design and the available computational power.
Q 7. Explain the concept of Diffie-Hellman key exchange.
The Diffie-Hellman key exchange is a revolutionary method for establishing a shared secret key between two parties over an insecure channel without ever explicitly transmitting the secret.
How it Works:
- Public Parameters: Two parties, Alice and Bob, agree on a public prime number, p, and a generator, g (a number that generates many different numbers when repeatedly multiplied modulo p).
- Private Key Generation: Alice chooses a secret integer, a, and Bob chooses a secret integer, b. These are their private keys.
- Public Key Calculation: Alice calculates her public key, A = ga (mod p), and Bob calculates his public key, B = gb (mod p).
- Public Key Exchange: Alice and Bob exchange their public keys (A and B) over the insecure channel.
- Shared Secret Calculation: Alice computes the shared secret as s = Ba (mod p), and Bob computes the shared secret as s = Ab (mod p). Both calculations result in the same value, s, which is their shared secret key.
Security: The security of Diffie-Hellman relies on the discrete logarithm problem – the difficulty of computing a from ga (mod p). Although computationally intensive, the complexity increases significantly with larger values of p, making it extremely difficult to crack with current technology. This key exchange provides a secure way for two parties to share a symmetric encryption key, which is then used for secure communication.
Q 8. What are elliptic curve cryptosystems, and what are their advantages?
Elliptic curve cryptosystems (ECC) are public-key cryptosystems based on the algebraic structure of elliptic curves over finite fields. Instead of relying on the difficulty of factoring large numbers (like RSA), ECC leverages the difficulty of the elliptic curve discrete logarithm problem (ECDLP). This problem involves finding a scalar k given a point P on the curve and the point Q = kP (where kP represents adding the point P to itself k times using the elliptic curve group operation).
Advantages of ECC:
- Stronger Security with Smaller Key Sizes: ECC offers comparable security to RSA with significantly smaller key sizes. A 256-bit ECC key provides roughly the same security as a 3072-bit RSA key, resulting in faster computation and reduced storage requirements.
- Improved Efficiency: The smaller key sizes lead to faster encryption, decryption, signing, and verification processes.
- Suitable for Resource-Constrained Devices: ECC’s efficiency makes it ideal for devices with limited processing power and memory, such as smartphones and embedded systems.
- Wide Adoption: ECC is widely adopted in various security standards and protocols, including TLS/SSL, digital signatures, and blockchain technologies.
Example: Bitcoin utilizes ECC for its digital signatures, enabling secure transactions and ownership verification.
Q 9. Describe the process of public key infrastructure (PKI).
Public Key Infrastructure (PKI) is a system for creating, managing, distributing, using, storing, and revoking digital certificates and managing public-key cryptography. It’s like a digital identity management system, ensuring the authenticity and integrity of online communications. Think of it as a digital notary public, vouching for the identity of websites and individuals.
The PKI process typically involves these steps:
- Certificate Authority (CA): A trusted third party that issues and manages digital certificates. They verify the identity of certificate applicants.
- Registration Authority (RA): An optional intermediary that assists the CA in verifying identities and handling certificate requests. Think of them as assistants to the CA.
- Certificate Request: An entity (individual or organization) requests a digital certificate from the CA or RA, providing necessary identity verification.
- Certificate Issuance: Upon successful verification, the CA issues a digital certificate containing the entity’s public key and other identifying information.
- Certificate Revocation: If a certificate is compromised, the CA revokes it, preventing its further use. This information is typically published in a Certificate Revocation List (CRL).
- Certificate Validation: When a user interacts with a secure website, their browser verifies the website’s certificate by checking its validity and the CA’s trustworthiness.
Q 10. Explain the concept of a digital certificate.
A digital certificate is an electronic document that verifies the identity of a person or organization. It’s like a digital passport or driver’s license. It contains the entity’s public key and other identifying information, digitally signed by a trusted Certificate Authority (CA).
Key components of a digital certificate:
- Public Key: The entity’s public key, used for encryption and verification.
- Subject Information: Details about the entity (e.g., name, organization, email address).
- Issuer Information: Details about the CA that issued the certificate.
- Validity Period: The time period during which the certificate is valid.
- Digital Signature: The CA’s digital signature, verifying the certificate’s authenticity.
Example: When you visit a secure website (HTTPS), your browser checks the website’s digital certificate to verify its identity before establishing a secure connection. If the certificate is invalid or untrusted, your browser will issue a warning.
Q 11. What are the different types of cryptographic attacks?
Cryptographic attacks aim to compromise the security of cryptographic systems. They can be broadly categorized as:
- Ciphertext-only attacks: The attacker only has access to the ciphertext.
- Known-plaintext attacks: The attacker has access to both the plaintext and the corresponding ciphertext.
- Chosen-plaintext attacks: The attacker can choose plaintexts and obtain their corresponding ciphertexts.
- Chosen-ciphertext attacks: The attacker can choose ciphertexts and obtain their corresponding plaintexts (or partial information).
- Side-channel attacks: Attacks that exploit information leaked through side channels (e.g., power consumption, timing, electromagnetic emissions).
- Brute-force attacks: Trying all possible keys until the correct one is found.
Example: A known-plaintext attack might involve an attacker intercepting an encrypted message and knowing part of the message’s content (e.g., a standard header). They can then use this information to try to decipher the rest of the message.
Q 12. How does a man-in-the-middle attack work?
A man-in-the-middle (MITM) attack occurs when an attacker secretly relays and possibly alters the communication between two parties who believe they are directly communicating with each other. It’s like eavesdropping on a phone call and impersonating both parties involved.
How it works:
- Interception: The attacker intercepts communication between two parties (e.g., Alice and Bob).
- Impersonation: The attacker establishes separate connections with Alice and Bob, pretending to be each other.
- Relaying: The attacker relays messages between Alice and Bob, potentially modifying or inserting messages.
Example: A malicious Wi-Fi hotspot can be used to launch a MITM attack. Users connecting to the hotspot unknowingly have their communication intercepted by the attacker.
Q 13. What are some countermeasures against side-channel attacks?
Side-channel attacks exploit information leaked through physical channels, not directly from the cryptographic algorithm itself. Countermeasures aim to reduce or eliminate these information leaks.
Countermeasures:
- Power analysis countermeasures: Techniques like masking, blinding, and dual-rail logic aim to prevent power consumption from revealing sensitive information.
- Timing attack countermeasures: Constant-time algorithms ensure that execution time doesn’t depend on sensitive data.
- Electromagnetic emissions countermeasures: Shielding and careful circuit design minimize electromagnetic emanations.
- Software countermeasures: Randomization techniques, code obfuscation, and secure coding practices help reduce vulnerabilities.
Example: Using constant-time algorithms for cryptographic operations prevents timing differences from revealing information about the key.
Q 14. Explain the concept of perfect secrecy.
Perfect secrecy, as defined by Claude Shannon, means that the ciphertext reveals absolutely no information about the plaintext beyond the length of the message. In other words, even with unlimited computational power, an attacker can’t learn anything about the plaintext from the ciphertext.
Conditions for perfect secrecy:
- The key must be at least as long as the message.
- Each key must be used only once (one-time pad).
One-time pad (OTP): is a cryptosystem that achieves perfect secrecy. It involves using a truly random key (as long as the message) to encrypt the plaintext by performing a bitwise XOR operation. Decryption involves performing the same XOR operation with the same key.
Limitations: Perfect secrecy is practically difficult to achieve due to the need for very long, truly random keys that need to be securely shared between communicating parties. It’s more of a theoretical ideal than a widely used practical solution.
Q 15. What are some common vulnerabilities in cryptographic systems?
Cryptographic systems, while incredibly powerful, are susceptible to various vulnerabilities. These vulnerabilities can stem from flaws in the algorithm design itself, implementation errors, or weaknesses in key management practices. Let’s explore some common ones:
- Side-Channel Attacks: These attacks exploit information leaked during computation, such as timing variations, power consumption, or electromagnetic emissions. For instance, an attacker might observe the time taken to decrypt a ciphertext; variations in timing can reveal information about the key.
- Implementation Errors: Bugs in the code implementing a cryptographic algorithm can create security holes. A simple coding error could allow an attacker to bypass security measures or even gain access to the secret key.
- Weak or Compromised Keys: The strength of any cryptographic system rests on the secrecy and randomness of its keys. Poor key generation, reuse of keys, or inadequate key storage can compromise the entire system. Imagine using the same key to lock your front door and your car – compromising one compromises both.
- Algorithm Vulnerabilities: Advances in cryptanalysis can reveal weaknesses in established cryptographic algorithms. Algorithms once considered secure can become vulnerable as computing power increases or new mathematical techniques are developed. The recent shift away from SHA-1 is a prime example of this.
- Social Engineering Attacks: These attacks exploit human psychology to trick individuals into revealing sensitive information, such as passwords or cryptographic keys. Phishing emails, for instance, can lead to a breach of security, even if the underlying cryptographic system is perfectly secure.
Understanding these vulnerabilities is crucial for designing and implementing robust cryptographic systems. It requires a multi-layered approach, combining strong algorithms, secure implementation, and effective key management practices.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. Describe the role of cryptography in blockchain technology.
Cryptography is the backbone of blockchain technology, providing the security and trust necessary for its operation. It ensures the integrity and confidentiality of transactions. Here’s how:
- Hashing: Cryptographic hash functions, like SHA-256, are used to generate unique fingerprints (hashes) of blocks of transactions. These hashes are crucial for linking blocks together in the chain, making it tamper-proof. Changing even a single bit in a transaction would drastically alter its hash, making the tampering immediately detectable.
- Digital Signatures: These provide authentication and non-repudiation. Users sign transactions using their private keys, proving ownership and preventing fraudulent transactions. Anyone can verify the signature using the corresponding public key, ensuring the transaction’s authenticity.
- Public Key Cryptography: This is foundational to blockchain’s secure operation. Each user has a public and a private key pair. The public key is shared, allowing others to send transactions to the user. The private key remains secret and is used to sign transactions, proving the user’s authorization.
- Encryption (Optional): While not always a core component of all blockchains, encryption can further enhance security by protecting sensitive transaction data. This ensures only authorized parties can access the data.
In essence, cryptography underpins the entire concept of a decentralized, secure, and transparent ledger system. Without it, blockchain technology would be fundamentally insecure and untrustworthy.
Q 17. Explain how zero-knowledge proofs work.
Zero-knowledge proofs (ZKPs) allow one party (the prover) to prove to another party (the verifier) that a statement is true, without revealing any information beyond the truth of the statement itself. Imagine proving you know a password without revealing the password itself – that’s the essence of a ZKP.
There are various types of ZKPs, but a common approach involves cryptographic techniques to demonstrate knowledge without disclosing the underlying information. The prover engages in an interactive protocol with the verifier, performing computations that convince the verifier of the statement’s validity without leaking any additional data.
Example: Imagine a scenario where you need to prove you know the solution to a Sudoku puzzle without revealing the solution. A ZKP could allow you to demonstrate that your solution is correct through a series of interactive steps, without showing the verifier your actual completed grid. The verifier would be convinced of the solution’s correctness without ever seeing it.
ZKPs are used in various applications, including anonymous authentication, secure voting systems, and blockchain privacy enhancements. They play a vital role in protecting sensitive information while proving the validity of claims.
Q 18. What is homomorphic encryption, and what are its applications?
Homomorphic encryption allows computations to be performed on encrypted data without decryption. This means you can process information while it’s still encrypted, preserving confidentiality. Think of it as performing arithmetic on locked boxes—you can add or multiply the boxes without opening them to see their contents.
There are different types of homomorphic encryption, including:
- Fully Homomorphic Encryption (FHE): Supports arbitrary computations on encrypted data.
- Partially Homomorphic Encryption: Supports only specific types of computations (e.g., only addition or only multiplication).
Applications:
- Cloud Computing: Process sensitive data in the cloud without compromising confidentiality.
- Secure Multi-Party Computation: Enable collaboration on sensitive data without revealing individual inputs.
- Privacy-Preserving Data Analysis: Analyze data without accessing the underlying raw data, protecting individual privacy.
Homomorphic encryption is a relatively new and complex field, but its potential applications are vast, holding immense promise for enhancing data privacy and security in various domains.
Q 19. How do you choose an appropriate cryptographic algorithm for a specific application?
Choosing the right cryptographic algorithm depends heavily on the specific application’s security requirements and constraints. There’s no one-size-fits-all solution. Here’s a framework:
- Identify Security Goals: Define what needs to be protected (confidentiality, integrity, authenticity, non-repudiation) and the level of security required (e.g., protecting financial transactions versus protecting casual online communication).
- Assess Constraints: Consider factors like computational resources (processing power, memory), communication bandwidth, and latency requirements. A complex algorithm might be overkill for a low-power device.
- Algorithm Selection: Based on the goals and constraints, choose appropriate algorithms. For example, AES (Advanced Encryption Standard) is commonly used for symmetric encryption, while RSA or ECC (Elliptic Curve Cryptography) are used for asymmetric encryption. Consider established standards and vetted algorithms whenever possible.
- Key Length: Choose appropriate key lengths to match the desired security level. Longer keys provide stronger security but require more computational resources.
- Implementation and Testing: Implement the chosen algorithm carefully, following security best practices. Thoroughly test the implementation to identify any vulnerabilities before deploying it.
Example: A secure banking application requires robust encryption and strong digital signatures. AES-256 for data encryption and RSA with a sufficiently long key length for digital signatures might be suitable. In contrast, a simple password protection system might only need a strong hashing algorithm like bcrypt.
Q 20. Discuss the importance of key management in cryptography.
Key management is the cornerstone of cryptographic security. It encompasses all aspects of handling cryptographic keys, from their generation and storage to their use and destruction. Neglecting key management is like leaving the keys to your valuables lying around.
Key management practices must address:
- Key Generation: Keys must be generated using cryptographically secure random number generators (CSPRNGs) to ensure unpredictability.
- Key Storage: Keys must be stored securely, using hardware security modules (HSMs) or other secure methods to protect them from unauthorized access. Protecting keys is even more critical than protecting algorithms.
- Key Distribution: Secure methods are needed to distribute keys between parties, preventing interception or modification.
- Key Rotation: Periodically changing keys reduces the risk of long-term compromise. Like changing passwords regularly.
- Key Revocation: Mechanisms for quickly invalidating compromised keys are essential.
- Key Destruction: Securely erasing keys when they are no longer needed.
Robust key management procedures are essential to ensure the overall security and reliability of any cryptographic system.
Q 21. Explain the concept of key escrow.
Key escrow refers to a system where cryptographic keys are entrusted to a third party (the escrow agent). This agent can access the keys under specific circumstances, typically in the case of emergencies, such as legal investigations or when a user loses access to their key. Think of it as having a spare set of keys kept by a trusted friend.
Advantages:
- Data recovery: Allows access to encrypted data if a user loses their key.
- Law enforcement access: Can facilitate access to encrypted data for legal purposes.
Disadvantages:
- Security risks: Introduces a single point of failure. If the escrow agent is compromised, all the keys are at risk.
- Privacy concerns: Raises privacy issues as a third party has access to sensitive keys.
- Trust issues: Requires absolute trust in the escrow agent’s integrity and security measures.
Key escrow is a complex issue with significant security and privacy implications. The potential benefits must be carefully weighed against the substantial risks involved before implementing such a system.
Q 22. What are the security considerations for implementing encryption in a cloud environment?
Implementing encryption in a cloud environment introduces unique security challenges. The shared responsibility model, where both the cloud provider and the client share security duties, is crucial to understand. Key considerations include:
- Data at Rest: Encryption of data stored on cloud servers is vital. This often involves using techniques like disk encryption (e.g., full disk encryption or file-level encryption) and database encryption. We need to choose strong encryption algorithms (like AES-256) and manage keys securely using techniques such as Hardware Security Modules (HSMs).
- Data in Transit: Securing data as it travels between the client and the cloud server is paramount. This relies on using Transport Layer Security (TLS) or Secure Sockets Layer (SSL) protocols. We must ensure the certificates are properly managed and updated.
- Key Management: Secure key management is the cornerstone of encryption. Losing access to keys renders data unusable. Robust key management systems, including key rotation policies and secure key storage, are essential. HSMs are often used to minimize the risk of key compromise.
- Cloud Provider Security: Selecting a reputable cloud provider with strong security certifications and practices is crucial. Regularly auditing the provider’s security measures and compliance with relevant standards (like ISO 27001) is needed.
- Access Control: Implementing robust access control mechanisms is vital to prevent unauthorized access to encrypted data. This involves using role-based access control (RBAC) and granular permission settings. Principle of least privilege should always be applied.
- Data Loss Prevention (DLP): Implementing DLP measures helps prevent sensitive data from leaving the cloud environment without authorization, even if encrypted.
For example, if a company stores sensitive customer data in a cloud database, it must ensure the database is encrypted at rest, that the connection between the application and the database uses TLS, and that only authorized personnel have access to the encryption keys.
Q 23. How do you assess the security of a cryptographic system?
Assessing the security of a cryptographic system is a multifaceted process involving several stages. It’s not a single test, but rather a continuous evaluation process. We generally follow a structured approach:
- Algorithm Analysis: This involves scrutinizing the underlying mathematical principles of the cryptographic algorithm. We look for weaknesses or vulnerabilities that could be exploited by attackers. This often involves reviewing published cryptanalysis papers and exploring the algorithm’s resilience against known attacks (e.g., brute-force, side-channel, differential cryptanalysis).
- Implementation Review: Even a strong algorithm can be rendered weak by poor implementation. We examine the code for potential vulnerabilities like buffer overflows, memory leaks, or improper key handling. Secure coding practices and rigorous code reviews are essential.
- Key Management Assessment: The security of any cryptosystem is highly dependent on the security of its keys. We evaluate the key generation process, storage mechanisms (HSMs are preferred for high security), and key distribution methods. Key rotation policies and procedures for key recovery are critical elements.
- Security Testing: Penetration testing and vulnerability assessments play a vital role. Simulating real-world attacks helps uncover weaknesses in the system’s overall security. This could involve testing for vulnerabilities like injection flaws, cross-site scripting (XSS), and insecure direct object references.
- Compliance and Standards: We check whether the system meets relevant security standards and regulations (e.g., NIST, FIPS). This demonstrates the system’s adherence to established best practices.
For instance, assessing the security of a TLS implementation requires analyzing the chosen cipher suites, validating the certificate chain, and testing the system’s resistance to known TLS vulnerabilities like POODLE or BEAST.
Q 24. Describe your experience with different cryptographic libraries or tools.
Throughout my career, I’ve worked extensively with several cryptographic libraries and tools. My experience encompasses both open-source and commercial solutions. Some notable examples include:
- OpenSSL: A widely used, open-source library providing a comprehensive set of cryptographic functionalities, including TLS/SSL, digital signatures, and various encryption algorithms. I have leveraged OpenSSL for implementing secure communication channels in numerous projects.
- Libsodium: A modern, easy-to-use, and well-designed cryptographic library focusing on ease of use and security. It’s particularly useful for applications requiring simpler integration but with robust security.
- Bouncy Castle (Java): A highly versatile Java cryptographic library providing a broad range of algorithms and functionalities, suitable for diverse applications. I’ve employed it in numerous Java-based projects requiring strong cryptography.
- Hardware Security Modules (HSMs): I have experience integrating HSMs (such as those from Thales and SafeNet) into security-sensitive applications. HSMs offer a secure hardware environment for key generation, storage, and cryptographic operations, crucial for protecting sensitive keys and cryptographic material.
My experience allows me to select the appropriate library or tool based on the specific security requirements, performance considerations, and development environment of the project.
Q 25. Explain your understanding of post-quantum cryptography.
Post-quantum cryptography (PQC) refers to cryptographic algorithms designed to be secure against attacks from both classical computers and quantum computers. Current widely used algorithms, like RSA and ECC, are vulnerable to attacks by sufficiently powerful quantum computers. PQC aims to address this threat.
Several promising PQC approaches exist, including:
- Lattice-based cryptography: Relies on the hardness of problems related to lattices in high-dimensional spaces. Examples include CRYSTALS-Kyber (for key encapsulation) and CRYSTALS-Dilithium (for digital signatures).
- Code-based cryptography: Based on the difficulty of decoding linear codes. McEliece is a prominent example.
- Multivariate cryptography: Utilizes the difficulty of solving systems of multivariate polynomial equations. Rainbow is a representative algorithm.
- Hash-based cryptography: Uses cryptographic hash functions to build digital signature schemes. SPHINCS+ is an example of a hash-based signature algorithm.
The NIST (National Institute of Standards and Technology) has recently standardized several PQC algorithms, marking a significant step towards their widespread adoption. Transitioning to PQC will require a considerable effort, involving updating existing systems and developing new implementations. This is a crucial step in ensuring long-term security in a post-quantum world.
Q 26. What are the ethical considerations in the field of cryptography?
Ethical considerations in cryptography are paramount. The power of cryptography to protect privacy and confidentiality also gives it the potential for misuse. Key ethical concerns include:
- Privacy vs. Security: Balancing the need for strong security with the preservation of individual privacy is a constant challenge. Overly strong encryption can hinder law enforcement, while weak encryption leaves data vulnerable.
- Export Controls: Restrictions on the export of strong cryptographic technologies have historically hampered global security. The ethical implications of such controls need careful consideration.
- Widespread Access: Cryptography should be accessible to everyone, not just governments or large corporations. Ensuring equitable access to secure technologies is an important ethical goal.
- Transparency and Openness: Open-source cryptographic implementations are preferred as they allow independent review and analysis, enhancing trust and security. Proprietary, closed-source systems can harbor hidden vulnerabilities.
- Responsible Disclosure: Researchers discovering vulnerabilities in cryptographic systems should disclose them responsibly, following established processes to minimize the risk of exploitation before a patch is available.
For example, the debate around backdoors in encryption systems highlights the tension between security and privacy. The potential benefits for law enforcement are balanced against the risk of these backdoors being exploited by malicious actors. Ethical considerations guide the development and deployment of cryptographic systems, ensuring that the benefits outweigh the risks.
Q 27. How do you stay up-to-date with the latest advancements in cryptography?
Staying current in the rapidly evolving field of cryptography requires a multi-pronged approach:
- Academic Publications: Regularly reviewing publications from leading cryptography conferences (CRYPTO, EUROCRYPT, ASIACRYPT) and journals keeps me abreast of the latest research and advancements.
- Industry Blogs and Newsletters: Following reputable blogs and newsletters from security companies and researchers provides updates on practical applications and emerging threats.
- Open-Source Projects: Contributing to and monitoring activity in open-source cryptographic libraries allows for firsthand experience with the latest implementations and development techniques.
- Conferences and Workshops: Attending conferences and workshops allows for networking with experts and learning from presentations and discussions.
- Online Courses and Tutorials: Utilizing online resources from platforms like Coursera and edX allows continuous learning and skill development.
- NIST Publications: Following updates and publications from NIST, especially concerning PQC standardization, is essential.
This combination of active engagement with the academic and practical sides of the field ensures I maintain a deep and current understanding of cryptography’s landscape.
Q 28. Describe a time you had to solve a complex cryptographic problem.
In a previous role, we faced a complex challenge involving securing legacy systems that used outdated encryption algorithms. These systems lacked proper key management and were vulnerable to various attacks. Our approach involved a phased transition to stronger encryption.
Phase 1: Assessment: We started by thoroughly assessing the existing systems, identifying the vulnerabilities, and classifying the data sensitivity. This involved analyzing the algorithms in use, determining the key management procedures, and evaluating the potential impact of a security breach.
Phase 2: Mitigation: To address immediate risks, we implemented stronger access controls and improved logging mechanisms to enhance detection capabilities. We also started educating users about security best practices.
Phase 3: Migration: We developed a phased migration strategy, migrating different systems to updated encryption algorithms and key management procedures in stages. This ensured a controlled transition while minimizing disruption to ongoing operations. We chose to gradually move to AES-256 for encryption, implementing robust key management practices involving HSMs.
Phase 4: Monitoring and Maintenance: Post-migration, ongoing monitoring and maintenance are crucial to ensure the security of the upgraded systems. Regular security audits and penetration testing were essential to maintain a high level of security.
This multi-phased approach allowed us to successfully address the security weaknesses of the legacy systems while minimizing disruptions and ensuring the confidentiality and integrity of the data.
Key Topics to Learn for Cryptology Interview
- Symmetric-key Cryptography: Understanding algorithms like AES and DES, their strengths, weaknesses, and modes of operation. Practical application: Secure communication channels within a network.
- Asymmetric-key Cryptography: Mastering RSA, ECC, and their roles in digital signatures and key exchange. Practical application: Secure online transactions and authentication.
- Hash Functions: Exploring SHA-256, SHA-3, and their use in data integrity and digital signatures. Practical application: Ensuring data hasn’t been tampered with.
- Number Theory and Algebra: Developing a strong foundation in modular arithmetic, prime numbers, and group theory. This is crucial for understanding the underlying mathematics of many cryptographic algorithms.
- Cryptography Protocols: Familiarizing yourself with TLS/SSL, SSH, and their functionalities. Practical application: Understanding secure web browsing and remote access.
- Cryptanalysis: Understanding common attack vectors like brute-force attacks, known-plaintext attacks, and chosen-plaintext attacks. This helps in designing more robust and secure systems.
- Digital Signatures and Certificates: Understanding how digital signatures ensure authenticity and non-repudiation. Practical application: Verifying the identity of websites and software.
- Blockchain Technology and Cryptocurrencies: Understanding the cryptographic principles underlying blockchain technology and various cryptocurrencies. Practical application: Developing secure and transparent systems.
Next Steps
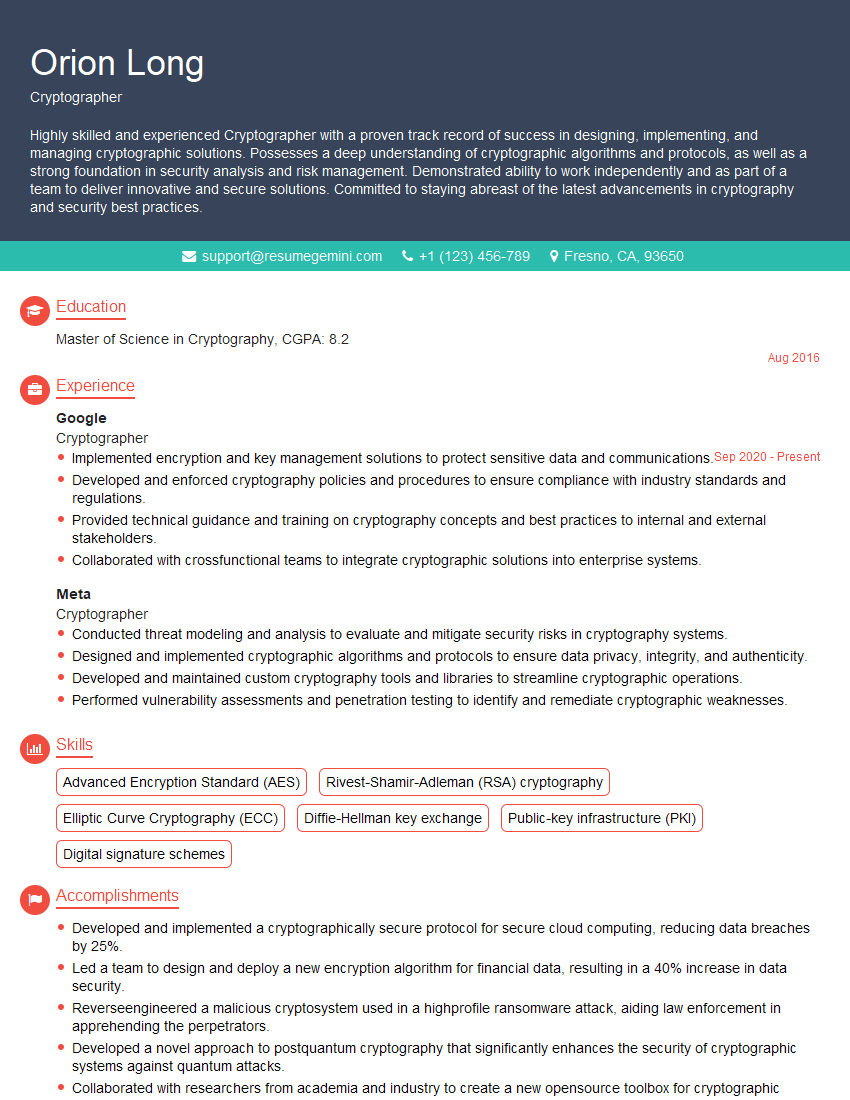
Mastering Cryptology opens doors to exciting and impactful careers in cybersecurity, blockchain development, and research. To maximize your job prospects, it’s crucial to present your skills effectively. Creating an ATS-friendly resume is paramount for getting your application noticed by recruiters. ResumeGemini is a trusted resource that can help you build a professional and impactful resume tailored to the Cryptology field. Examples of Cryptology-focused resumes are available to guide you in crafting a compelling document that highlights your expertise.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Attention music lovers!
Wow, All the best Sax Summer music !!!
Spotify: https://open.spotify.com/artist/6ShcdIT7rPVVaFEpgZQbUk
Apple Music: https://music.apple.com/fr/artist/jimmy-sax-black/1530501936
YouTube: https://music.youtube.com/browse/VLOLAK5uy_noClmC7abM6YpZsnySxRqt3LoalPf88No
Other Platforms and Free Downloads : https://fanlink.tv/jimmysaxblack
on google : https://www.google.com/search?q=22+AND+22+AND+22
on ChatGPT : https://chat.openai.com?q=who20jlJimmy20Black20Sax20Producer
Get back into the groove with Jimmy sax Black
Best regards,
Jimmy sax Black
www.jimmysaxblack.com
Hi I am a troller at The aquatic interview center and I suddenly went so fast in Roblox and it was gone when I reset.
Hi,
Business owners spend hours every week worrying about their website—or avoiding it because it feels overwhelming.
We’d like to take that off your plate:
$69/month. Everything handled.
Our team will:
Design a custom website—or completely overhaul your current one
Take care of hosting as an option
Handle edits and improvements—up to 60 minutes of work included every month
No setup fees, no annual commitments. Just a site that makes a strong first impression.
Find out if it’s right for you:
https://websolutionsgenius.com/awardwinningwebsites
Hello,
we currently offer a complimentary backlink and URL indexing test for search engine optimization professionals.
You can get complimentary indexing credits to test how link discovery works in practice.
No credit card is required and there is no recurring fee.
You can find details here:
https://wikipedia-backlinks.com/indexing/
Regards
NICE RESPONSE TO Q & A
hi
The aim of this message is regarding an unclaimed deposit of a deceased nationale that bears the same name as you. You are not relate to him as there are millions of people answering the names across around the world. But i will use my position to influence the release of the deposit to you for our mutual benefit.
Respond for full details and how to claim the deposit. This is 100% risk free. Send hello to my email id: lukachachibaialuka@gmail.com
Luka Chachibaialuka
Hey interviewgemini.com, just wanted to follow up on my last email.
We just launched Call the Monster, an parenting app that lets you summon friendly ‘monsters’ kids actually listen to.
We’re also running a giveaway for everyone who downloads the app. Since it’s brand new, there aren’t many users yet, which means you’ve got a much better chance of winning some great prizes.
You can check it out here: https://bit.ly/callamonsterapp
Or follow us on Instagram: https://www.instagram.com/callamonsterapp
Thanks,
Ryan
CEO – Call the Monster App
Hey interviewgemini.com, I saw your website and love your approach.
I just want this to look like spam email, but want to share something important to you. We just launched Call the Monster, a parenting app that lets you summon friendly ‘monsters’ kids actually listen to.
Parents are loving it for calming chaos before bedtime. Thought you might want to try it: https://bit.ly/callamonsterapp or just follow our fun monster lore on Instagram: https://www.instagram.com/callamonsterapp
Thanks,
Ryan
CEO – Call A Monster APP
To the interviewgemini.com Owner.
Dear interviewgemini.com Webmaster!
Hi interviewgemini.com Webmaster!
Dear interviewgemini.com Webmaster!
excellent
Hello,
We found issues with your domain’s email setup that may be sending your messages to spam or blocking them completely. InboxShield Mini shows you how to fix it in minutes — no tech skills required.
Scan your domain now for details: https://inboxshield-mini.com/
— Adam @ InboxShield Mini
support@inboxshield-mini.com
Reply STOP to unsubscribe
Hi, are you owner of interviewgemini.com? What if I told you I could help you find extra time in your schedule, reconnect with leads you didn’t even realize you missed, and bring in more “I want to work with you” conversations, without increasing your ad spend or hiring a full-time employee?
All with a flexible, budget-friendly service that could easily pay for itself. Sounds good?
Would it be nice to jump on a quick 10-minute call so I can show you exactly how we make this work?
Best,
Hapei
Marketing Director
Hey, I know you’re the owner of interviewgemini.com. I’ll be quick.
Fundraising for your business is tough and time-consuming. We make it easier by guaranteeing two private investor meetings each month, for six months. No demos, no pitch events – just direct introductions to active investors matched to your startup.
If youR17;re raising, this could help you build real momentum. Want me to send more info?
Hi, I represent an SEO company that specialises in getting you AI citations and higher rankings on Google. I’d like to offer you a 100% free SEO audit for your website. Would you be interested?
Hi, I represent an SEO company that specialises in getting you AI citations and higher rankings on Google. I’d like to offer you a 100% free SEO audit for your website. Would you be interested?