Cracking a skill-specific interview, like one for Deception Techniques, requires understanding the nuances of the role. In this blog, we present the questions you’re most likely to encounter, along with insights into how to answer them effectively. Let’s ensure you’re ready to make a strong impression.
Questions Asked in Deception Techniques Interview
Q 1. Explain the difference between active and passive deception techniques.
The core difference between active and passive deception techniques lies in their level of interaction with the attacker. Passive deception involves deploying decoys that simply sit and wait to be discovered. Think of it like a dummy camera – it looks real, but doesn’t actively do anything unless interacted with. Active deception, on the other hand, engages the attacker. It’s like a motion sensor alarm; it detects interaction and responds, potentially providing valuable intelligence on the attacker’s methods and goals.
An example of passive deception is a fake file containing seemingly sensitive data; an example of active deception is a honeypot server that simulates a valuable system and logs all attempted access.
Q 2. Describe three common deception technologies used in cybersecurity.
Three common deception technologies are:
- Honeypots: These are decoy systems designed to lure attackers. They mimic valuable assets, such as servers or databases, to attract malicious activity. There are low-interaction honeypots (offering limited functionality) and high-interaction honeypots (offering a more realistic environment). The latter are riskier as they could be compromised, but they offer richer data.
- Honeytokens: These are deceptively tempting pieces of data, such as fake credentials or files, placed within a network to identify and track malicious activity. They’re simpler than honeypots and easier to deploy, acting as breadcrumbs to trace an attacker’s path.
- Deception platforms: These are sophisticated systems that manage and orchestrate multiple deception techniques, including honeypots and honeytokens, providing centralized monitoring and analysis of attacker behavior. They offer automation and scalability, vital for larger networks.
Q 3. How do you assess the effectiveness of a deception deployment?
Assessing the effectiveness of a deception deployment involves several key metrics:
- Number of engagements: How often are decoys being accessed or interacted with? This highlights the presence of active threats and the attractiveness of your deception.
- Attacker behavior analysis: What techniques are attackers using? What are their targets? This informs threat intelligence and improves security posture.
- Time to detection: How quickly is the deception system detecting and alerting on malicious activity? A faster response reduces the impact of a successful attack.
- False positive rate: The number of false alarms generated by the system. A high rate reduces the credibility of alerts and needs investigation. Fine-tuning and adjusting deception deployment is crucial to keep this low.
- Integration with existing security systems: How well does the deception data integrate with other security tools (SIEM, SOAR) to improve the overall security response? Effective integration automates the process of handling alerts and enables a broader security overview.
Regularly reviewing these metrics and adapting your deployment based on findings is essential to maximize the effectiveness of your deception strategy.
Q 4. What are the ethical considerations of using deception techniques?
Ethical considerations are paramount when using deception techniques. The primary concern is legality and adherence to privacy laws. Deception should never be used to intentionally mislead or harm individuals or organizations that aren’t actively attempting malicious activities. It’s crucial to establish clear legal and ethical guidelines, such as obtaining appropriate consent where applicable, before implementing such systems.
Furthermore, deception systems should be transparent and clearly documented. You need to clearly state the purposes and intentions of the system, ideally providing a clear opt-out for those that wish to avoid it. Transparency fosters trust and aligns your security practices with ethical best practices.
Q 5. How do you handle false positives generated by deception systems?
False positives, while unavoidable, can significantly reduce the credibility of your deception system. Effective handling involves a multi-pronged approach:
- Refinement of detection rules: Analyzing the characteristics of false positives to refine and adjust detection thresholds and filters. This helps to distinguish between legitimate and malicious activity more accurately.
- Improved data analysis: Using advanced analytics and machine learning to distinguish between normal user activity and malicious behavior. This helps to filter out noise and prioritize high-probability alerts.
- Security information and event management (SIEM) integration: Correlating alerts generated by the deception system with data from other security tools to verify and validate alerts. This provides context and reduces false positive rates.
- Regular system reviews and updates: Continuously evaluate and update your deception deployment to adapt to evolving attack methods and user behavior. This proactive approach keeps your defenses sharp.
Ultimately, a balanced approach of carefully setting up your deception system to minimize false positives, combined with a robust process to triage and investigate alerts, is crucial for maximizing effectiveness.
Q 6. Explain the concept of a ‘honeytoken’ and its purpose.
A honeytoken is a seemingly valuable piece of data designed to attract and trap attackers. It can be a fake file name, a decoy username and password, or even a URL that looks like a legitimate link. Think of it as a digital ‘trap’. The main purpose is to detect malicious activity and gain insights into attacker behavior. If an attacker interacts with a honeytoken, it provides immediate evidence of their presence and intentions. By analyzing this interaction, you can track their progress and learn more about their tactics, techniques, and procedures (TTPs).
For example, placing a honeytoken file named ‘Confidential_Financial_Data.xlsx’ in a shared folder is likely to attract an attacker.
Q 7. Describe a situation where you had to analyze deceptive activity.
In a recent engagement, a client’s network experienced suspicious activity. Initial logs indicated unauthorized access attempts to several servers. We deployed a deception platform with both honeypots and honeytokens strategically placed within the network. Within 24 hours, the platform detected several attacks targeting specific honeypots simulating database servers. The attackers tried several different exploits before eventually being logged. Analysis of the attacker’s behavior revealed they were using a known exploit kit to gain initial access. We used this information to update the client’s security controls, patched vulnerabilities, and improved their overall security posture based on the attack information gleaned from the deception platform. This allowed us to prevent a potentially devastating data breach, demonstrating the value of deception techniques in proactive security.
Q 8. What are some common indicators of deception in network traffic?
Identifying deception in network traffic requires a keen eye for anomalies. Think of it like a detective looking for clues – instead of searching for explicitly malicious activity, we look for behaviors that deviate from the established norm. Common indicators include:
Unusual login attempts from unexpected locations or times: A user logging in from a country they’ve never accessed the network from, or at 3 AM, could signal a compromised account or reconnaissance activity.
Unexpected high volumes of data transfer: A sudden spike in traffic from a usually quiet server might indicate data exfiltration by an attacker.
Suspicious communication patterns: Connections to known malicious IP addresses or domains, or unusual communication protocols used by a specific host, are red flags.
Scanning activity: Repeated port scans or attempts to access non-standard ports hint at an attacker attempting to discover vulnerabilities.
Failed login attempts with unusual credentials: Brute-force attacks or attempts using weak passwords are clear signs of malicious intent.
Analyzing these anomalies using Security Information and Event Management (SIEM) systems and network traffic analysis tools is key to uncovering deception attempts. For example, a SIEM might alert on a large number of failed login attempts from a single IP address, prompting further investigation.
Q 9. How do you integrate deception techniques into a broader security strategy?
Integrating deception techniques into a broader security strategy is crucial for enhancing overall effectiveness. It’s not a standalone solution but rather a powerful addition to your existing defenses. Think of it as a layered approach, much like a castle with multiple lines of defense. Here’s how it integrates:
Defense in Depth: Deception sits alongside other security controls like firewalls, intrusion detection/prevention systems (IDS/IPS), and endpoint detection and response (EDR) solutions. It acts as a lure, distracting attackers while other systems monitor and respond to threats.
Threat Intelligence Enrichment: Deception platforms gather valuable intelligence about attacker tactics, techniques, and procedures (TTPs). This information can improve the accuracy of threat hunting and security operations.
Vulnerability Management: While not directly patching vulnerabilities, deception can highlight weaknesses in your defenses by attracting attackers to specific lures. This allows you to prioritize remediation efforts.
Incident Response: Deception provides crucial insights into attacker behavior during an active attack, allowing for a more effective response.
A successful integration requires close collaboration between security teams. It’s essential to have a clear strategy, well-defined goals, and a plan for handling alerts generated by the deception platform.
Q 10. Explain the role of deception in a layered security architecture.
In a layered security architecture, deception plays a vital role in providing an additional layer of defense that complements existing security controls. Imagine it as a honey pot within a fortress. It doesn’t replace the walls or guards (traditional security measures), but it acts as a trap, drawing attackers away from critical assets.
Early Warning System: Deception lures can detect reconnaissance and initial attack phases, providing early warnings about potential threats.
Attacker Profiling: By analyzing attacker behavior on deception assets, organizations can gain valuable insights into their tactics, enabling more effective threat hunting and prevention.
Resource Protection: Deception diverts attacker attention, reducing the risk to critical assets and systems. It essentially buys time and allows for a more measured response.
Improved Security Posture: Analyzing deception data can help identify blind spots and vulnerabilities in the overall security architecture, leading to improvements and a stronger defense.
The key is to strategically place deception assets throughout the network to maximize their effectiveness and integrate them seamlessly with other security layers.
Q 11. What are the key performance indicators (KPIs) for a deception program?
Key Performance Indicators (KPIs) for a deception program should focus on both effectiveness and efficiency. Some crucial metrics include:
Number of attacks detected: This shows the program’s ability to identify and capture malicious activities.
Attacker dwell time: A shorter dwell time indicates faster detection and response capabilities.
Number of unique attackers identified: Provides insights into the diversity and sophistication of threats encountered.
False positive rate: A low false positive rate demonstrates the accuracy of the deception system.
Time to detect and respond: Measures the efficiency of the security operations center (SOC) in handling alerts from the deception platform.
Coverage of deception assets: Indicates the extent to which the deception program protects the organization’s assets.
Regular monitoring and analysis of these KPIs are essential to optimize the deception program’s performance and ensure it aligns with the organization’s overall security objectives.
Q 12. How do you measure the return on investment (ROI) of a deception program?
Measuring the Return on Investment (ROI) of a deception program requires a comprehensive approach. It’s not solely about the cost of the platform but also the value derived from preventing data breaches, reducing downtime, and improving incident response time. Consider these factors:
Cost of the deception platform and implementation: This includes software licenses, hardware, professional services, and staff training.
Cost avoided by preventing breaches: This is a difficult-to-quantify aspect but crucial. Estimate the potential financial and reputational damage avoided by detecting and responding to attacks earlier.
Reduced downtime: Quantify the cost savings from quicker incident response and reduced system outages.
Improved incident response efficiency: Measure the reduction in time and resources spent on investigating security incidents.
Enhanced security posture: While difficult to directly quantify, a stronger security posture leads to a lower overall risk profile and potential cost savings in the long run.
By comparing the costs with the avoided costs and the benefits, you can create a robust ROI calculation demonstrating the value of the deception program. Remember that ROI should be measured over time and reevaluated regularly.
Q 13. Describe your experience with different types of deception platforms.
My experience encompasses a range of deception platforms, from small-scale, open-source solutions to large-scale enterprise deployments. I’ve worked with both network-based and endpoint-based deception technologies. Some examples include:
Network-based deception platforms: These create virtualized assets and services within the network to lure attackers. I’ve used platforms that deploy virtual machines, servers, and network devices to mimic real systems but act as traps.
Endpoint-based deception: These platforms embed decoys directly on endpoints to detect malicious activity at the host level. These often use techniques like file system monitoring and process analysis to identify suspicious behaviors.
Hybrid solutions: Many modern deception platforms offer a combination of network and endpoint capabilities, providing comprehensive coverage across the IT infrastructure.
My experience also includes integrating these platforms with existing SIEM and SOAR systems, creating a unified security ecosystem. Each platform has its own strengths and weaknesses, and the best choice depends on the organization’s specific needs and security architecture.
Q 14. How do you stay up-to-date on the latest deception techniques and technologies?
Staying current in the rapidly evolving field of deception techniques and technologies requires a multifaceted approach:
Industry conferences and webinars: Attending industry conferences, like RSA Conference or Black Hat, and participating in webinars provides valuable insights into the latest research and innovations.
Professional certifications: Pursuing certifications relevant to cybersecurity, incident response, and deception technologies keeps my knowledge base updated with industry best practices.
Research papers and publications: Regularly reviewing academic research papers and industry publications keeps me abreast of new techniques and approaches.
Online communities and forums: Engaging in online communities and forums provides access to discussions and insights from other experts in the field.
Vendor briefings and product demonstrations: Participating in vendor briefings and product demonstrations provides a hands-on understanding of the latest deception technologies available.
This continuous learning ensures I remain proficient in the latest deception strategies and techniques, enabling me to provide effective and up-to-date solutions to address emerging threats.
Q 15. What are the limitations of deception techniques?
Deception techniques, while powerful in cybersecurity, aren’t without limitations. One major constraint is the risk of false positives. A seemingly malicious action might be triggered by legitimate user behavior, leading to unnecessary investigations and alerts. Think of it like a smoke alarm – sometimes it goes off due to burnt toast instead of a fire.
Another limitation is the potential for adversary adaptation. Sophisticated attackers can detect and circumvent deception techniques, rendering them ineffective. This requires constant evolution of the deception strategies.
Finally, there’s the resource intensity. Implementing and managing deception systems requires significant technical expertise, infrastructure, and ongoing maintenance. It’s not a ‘set it and forget it’ solution.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. How do you mitigate the risks associated with using deception techniques?
Mitigating the risks of deception techniques involves a multi-layered approach. Careful planning and design are paramount. This includes identifying the specific threats you’re targeting, selecting appropriate deception technologies, and meticulously configuring them to avoid triggering false positives.
Regular monitoring and analysis are crucial. You need to constantly assess the effectiveness of your deception strategy, analyzing alerts to distinguish genuine threats from false positives. This involves examining the context of each alert, correlating it with other security data, and fine-tuning the system accordingly.
Finally, continuous improvement is vital. The threat landscape constantly evolves, so your deception strategy must adapt. This means regularly updating your deception techniques, expanding the scope of your decoys, and incorporating new technologies and intelligence.
Q 17. Explain the concept of ‘adversarial modeling’ in the context of deception.
Adversarial modeling in the context of deception involves building models that simulate the behavior of attackers. This allows you to anticipate their actions and proactively deploy deception techniques to trap them. Think of it like setting a trap based on how you anticipate a predator would behave.
For example, an adversarial model might predict that an attacker will attempt to exploit a specific vulnerability in your system. You could then deploy a decoy system with that vulnerability exposed, capturing the attacker’s actions and gathering valuable intelligence. This can include creating fake accounts with seemingly valuable data, or deploying honeypots mimicking crucial infrastructure components. The model helps to predict attack vectors, allowing for targeted deception deployment.
Q 18. Describe how you would respond to a successful deception detection event.
Responding to a successful deception detection event is a critical process. The first step is to contain the breach – isolate the affected system or network segment to prevent further damage. Then, we start to analyze the attacker’s behavior. This includes examining the techniques they used, the data they accessed (if any), and their overall goals. The information gathered provides insights into their tactics, techniques, and procedures (TTPs).
Next, incident response teams swing into action. This could involve forensic analysis, threat hunting to identify other compromised systems, and patching vulnerabilities. We also use this incident to improve our deception strategy, identifying weaknesses that the adversary exploited and refining our models and decoys accordingly. Finally, we thoroughly document the entire process – from detection to remediation – for future analysis and improvement.
Q 19. How do you identify and prioritize deception targets within an organization?
Identifying and prioritizing deception targets requires a risk-based approach. We start by assessing the organization’s critical assets and systems. This includes identifying systems holding sensitive data, those critical to business operations, and those frequently targeted by attackers. For instance, financial systems, customer databases, and servers containing intellectual property are high-value targets.
Then, we prioritize targets based on their value, likelihood of attack, and the potential impact of a successful breach. This often involves using a risk matrix that weighs these factors to assign a risk score to each target. A system with high value and high likelihood of attack receives a higher priority for deception deployment. This allows for efficient resource allocation and focusing on the areas most vulnerable to attack.
Q 20. What are the legal and regulatory considerations of using deception techniques?
The legal and regulatory considerations of using deception techniques are significant and vary by jurisdiction. It is crucial to ensure that your use of deception techniques complies with all applicable laws and regulations. This includes data protection laws like GDPR and CCPA, which require consent for the processing of personal data. Employing deception techniques involving personal data without explicit consent can lead to serious legal ramifications.
Moreover, laws regarding computer fraud and abuse must be considered. It is important to avoid actions that could be construed as illegal activity, such as setting traps that inadvertently capture legitimate users’ actions. Legal counsel should be consulted to ensure full compliance before deploying deception technologies.
Q 21. How do you communicate the value of deception techniques to non-technical stakeholders?
Communicating the value of deception techniques to non-technical stakeholders requires a clear and concise approach, focusing on the business impact. Instead of technical jargon, we use relatable analogies and examples. For example, we can explain it as a sophisticated security camera system that identifies and traps intruders before they can access valuable assets.
We highlight the cost savings associated with preventing breaches, minimizing downtime, and avoiding the hefty fines associated with data breaches and regulatory non-compliance. We present data showing the return on investment (ROI) of deception technology, and the reduction in risk exposure. This helps stakeholders understand the practical benefits of deception, linking it directly to business objectives and strengthening the overall security posture.
Q 22. What are some common challenges in implementing deception techniques?
Implementing deception techniques presents several significant challenges. One major hurdle is the complexity of managing and maintaining a deception environment. These environments often involve numerous decoys, honeypots, and other deceptive assets, requiring constant monitoring and updating to maintain their effectiveness. A poorly managed environment can lead to false positives, overwhelming security teams, and ultimately, a failure to detect real threats.
Another challenge is balancing deception with operational risk. Poorly designed or deployed decoys could inadvertently expose sensitive systems or data. It’s crucial to carefully segment and protect the deception environment to prevent attackers from inadvertently gaining access to critical assets.
Furthermore, achieving appropriate scale and integration can be difficult. Organizations may struggle to deploy and manage deception technology across their entire infrastructure, especially in large or complex environments. Integration with existing security tools and workflows also requires careful planning and execution.
Finally, measuring the effectiveness of deception operations is often complex. While detecting an attack against a decoy proves a breach attempt, understanding the full scope and implications of that attempt necessitates thorough analysis and correlation with other security data.
Q 23. How do you train your team to effectively utilize deception techniques?
Training a team to effectively utilize deception techniques requires a multi-faceted approach that combines theoretical knowledge with hands-on practice. We begin with a comprehensive understanding of deception principles, including the various types of decoys, their strengths and weaknesses, and the ethical considerations surrounding their use. We emphasize the importance of understanding attacker behavior and motivations to better design and deploy deceptive assets.
Next, we move into practical training using a combination of simulated environments and real-world case studies. This allows them to gain experience in deploying and managing decoys, analyzing attack traffic, and interpreting alerts generated by the deception system. We also incorporate capture-the-flag (CTF) exercises, mirroring real-world attack scenarios, to sharpen their skills.
Crucially, ongoing training and development are vital. The threat landscape constantly evolves, so regular updates on new techniques, attack vectors, and deception technologies are essential to keep the team ahead of the curve. We encourage continuous learning and collaboration to share best practices and lessons learned.
Q 24. Describe your experience with automating deception operations.
My experience with automating deception operations centers around leveraging Deception-as-a-Service (DaaS) platforms and integrating them with Security Information and Event Management (SIEM) systems. This allows us to scale our deception efforts efficiently and effectively. Automation plays a vital role in several key areas:
- Deployment and Management: Automating the deployment of decoys simplifies the process and allows for rapid scaling as the organization’s infrastructure expands. This includes automatically configuring and updating decoys, ensuring consistent security across the entire network.
- Alerting and Response: Automated alerts and response systems help prioritize and manage security alerts generated by deception activities, minimizing the risk of human error and reducing response time to critical threats.
- Analysis and Reporting: Automated analysis tools provide valuable insights into attacker behavior, including their tools, techniques, and procedures (TTPs), and enable generation of customized reports on the effectiveness of our deception strategy.
For example, we use scripting to automatically provision and configure new decoys based on detected vulnerabilities or changes in the network architecture. python script to automate decoy deployment (placeholder for a potential script snippet, would be provided in a real-world scenario). This ensures we’re constantly adapting our deception strategy to the evolving threat landscape.
Q 25. How do you integrate deception techniques with threat intelligence?
Integrating deception techniques with threat intelligence is crucial for maximizing their effectiveness. Threat intelligence provides context and insights into current and emerging threats, enabling more targeted and effective deception deployments. We leverage threat intelligence in several ways:
- Identifying high-value targets: Threat intelligence helps identify critical assets most likely to be targeted by attackers, guiding the placement and configuration of decoys to prioritize protection of sensitive data.
- Tailoring decoys: Threat intelligence helps in designing decoys that mimic real systems and data, making them more attractive to attackers and better suited to specific attack techniques.
- Enhancing alert prioritization: Threat intelligence helps filter alerts generated by the deception system, allowing analysts to focus on high-priority threats based on known attack patterns and TTPs.
- Improving response strategies: By understanding the attacker’s goals and techniques, we can design more effective response strategies once a decoy is compromised, minimizing the impact of an attack.
For instance, if threat intelligence indicates an increase in ransomware attacks targeting a specific type of database server, we would deploy decoys mimicking that server configuration, enhancing the likelihood of detecting and disrupting these attacks. This proactive approach maximizes the impact of our deception strategy.
Q 26. What are some innovative deception techniques you have encountered or developed?
I’ve been involved in the development and implementation of several innovative deception techniques. One example is the use of behavioral decoys. These decoys go beyond simply mimicking a system’s structure; they also emulate its behavior. Instead of simply presenting a fake login page, we simulate realistic application activity, such as generating log files and network traffic, making the decoy more convincing and increasing the likelihood of attracting attackers.
Another innovative technique I’ve encountered involves the use of dynamically generated decoys. These decoys are created and configured on-demand based on real-time threat intelligence and network activity. This allows us to create decoys specifically targeted at the observed attack patterns, enhancing the effectiveness and reducing the risk of detection.
Finally, the incorporation of artificial intelligence (AI) and machine learning (ML) into deception operations is proving revolutionary. AI/ML can be used to analyze attacker behavior in real-time, automatically adjust the behavior of decoys to enhance their effectiveness, and prioritize alerts based on the risk level of the detected activity.
Q 27. Explain how you would design a deception strategy for a specific industry (e.g., finance, healthcare).
Designing a deception strategy for the finance industry requires a focus on protecting highly sensitive data and systems. The strategy would need to address several key considerations:
- Protection of customer data: Deception techniques should be deployed to protect databases containing personally identifiable information (PII) and financial records. This would involve deploying decoys mimicking databases and other systems storing this sensitive data.
- Securing financial transactions: Deception techniques should be used to protect online banking systems and payment gateways. This may involve deploying decoys mimicking these systems to detect and disrupt fraudulent activities.
- Protecting internal systems: Deception techniques should also protect internal systems involved in financial operations, such as trading platforms and internal networks.
The specific implementation would involve a layered approach, including the use of various deception techniques such as honeypots, decoy servers, and deceptive user accounts, carefully integrated with existing security systems and workflows. Regular updates and adjustments based on threat intelligence would be crucial to maintain the effectiveness of the deception strategy. The focus would be on creating a complex, dynamic environment that makes it difficult for attackers to distinguish between real and fake assets, forcing them to reveal their intentions and tactics.
Q 28. How do you handle the potential for deception techniques to be bypassed?
The possibility of deception techniques being bypassed is a real concern. However, we address this through a multi-pronged approach focused on adaptability and continuous improvement. First, we implement a robust monitoring and analysis system to detect when a decoy is successfully compromised or a deception technique is being bypassed. This involves actively analyzing logs, network traffic, and other data to identify anomalies and patterns that indicate a successful attack.
Second, we utilize a layered defense approach, combining deception with other security measures. By combining deception techniques with firewalls, intrusion detection systems, and other security measures, we create a multi-layered defense, reducing the likelihood of a successful attack, even if one layer is bypassed.
Third, continuous adaptation and improvement are crucial. When a deception technique is bypassed, we analyze the attack to understand the methods used. This analysis informs the design and implementation of improved and more robust deception techniques, closing any vulnerabilities revealed by the attack.
Essentially, we view deception as a dynamic and evolving defense mechanism. Our approach emphasizes continuous improvement, allowing us to adapt to new and evolving attack methods, ensuring that our deception strategies remain effective even as attacker tactics improve.
Key Topics to Learn for Deception Techniques Interview
- Nonverbal Communication Analysis: Understanding microexpressions, body language, and vocal cues to detect deception.
- Statement Analysis: Identifying inconsistencies, contradictions, and evasiveness in verbal statements to assess truthfulness.
- Cognitive Interviewing Techniques: Employing specific questioning strategies to elicit truthful information and uncover concealed details.
- Deception Detection Technologies: Familiarizing yourself with the principles and limitations of polygraph testing and other technological approaches.
- Contextual Factors in Deception: Recognizing how situational pressures, cultural influences, and individual differences can impact the detection process.
- Ethical Considerations in Deception Detection: Understanding the ethical implications and legal boundaries related to deception detection practices.
- Case Studies and Practical Applications: Analyzing real-world scenarios to apply learned techniques and improve problem-solving skills. Consider various professional contexts, from law enforcement to corporate security.
- Developing Critical Thinking Skills: Honing your ability to analyze information objectively, identify biases, and form well-reasoned conclusions.
Next Steps
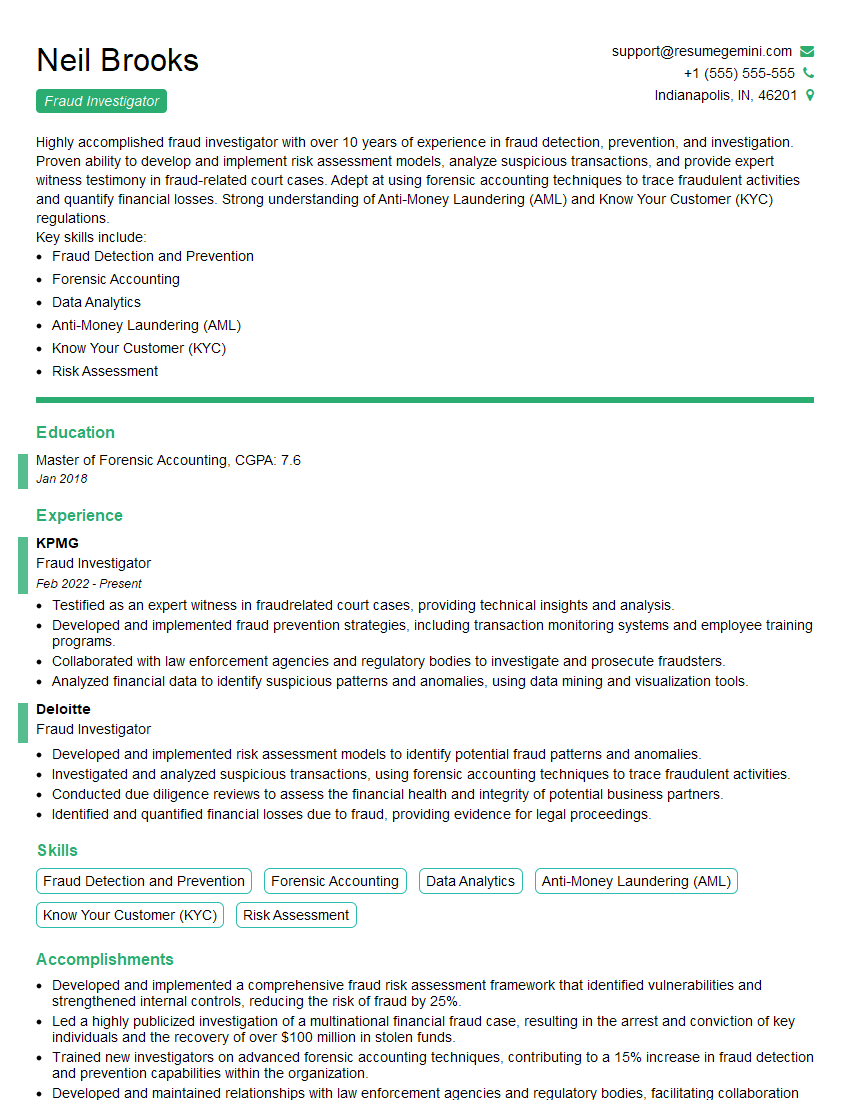
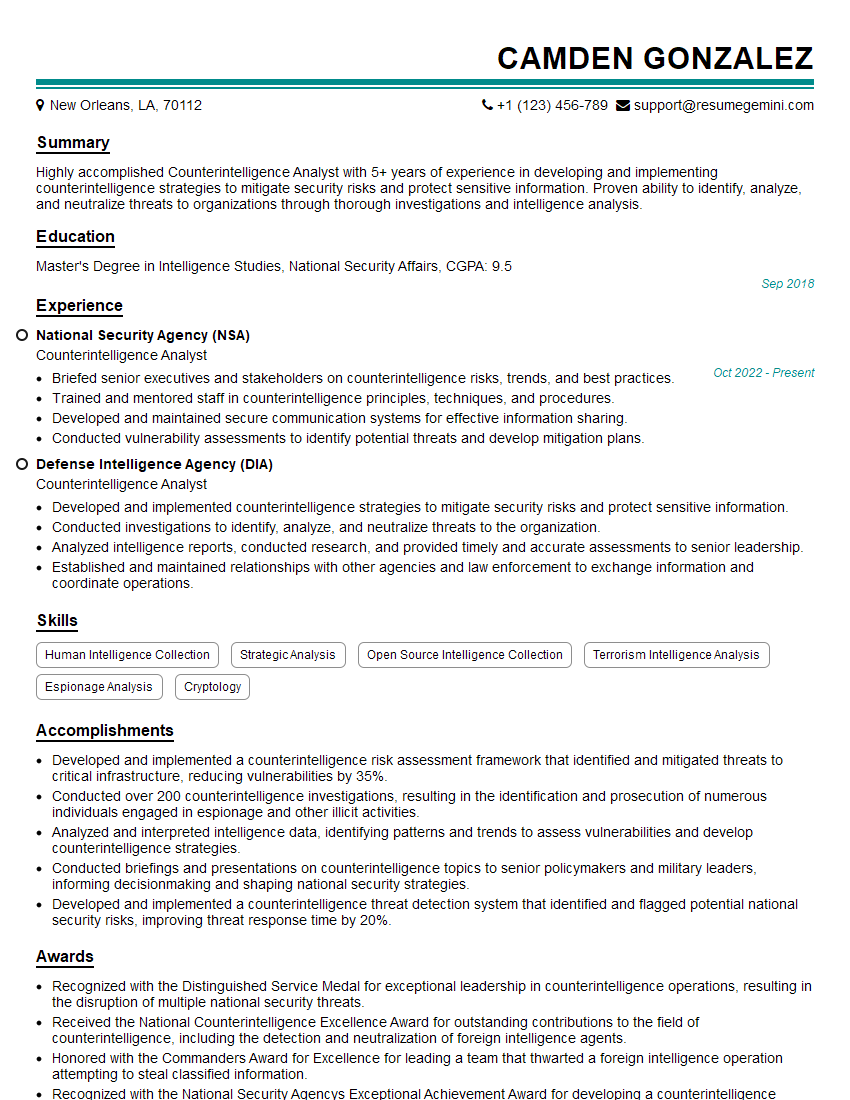
Mastering deception techniques significantly enhances your career prospects in fields requiring acute observational and analytical skills. Whether in law enforcement, intelligence, security, or even investigative journalism, the ability to accurately assess truthfulness is highly valued. To maximize your job search success, it’s crucial to have a resume that is both impactful and optimized for Applicant Tracking Systems (ATS). ResumeGemini is a trusted resource that can help you craft a compelling and ATS-friendly resume tailored to highlight your skills in deception techniques. We provide examples of resumes specifically designed for this field to give you a head start. Invest in your future – build a resume that reflects your expertise and secures your dream role.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good