Feeling uncertain about what to expect in your upcoming interview? We’ve got you covered! This blog highlights the most important Defense Acquisition interview questions and provides actionable advice to help you stand out as the ideal candidate. Let’s pave the way for your success.
Questions Asked in Defense Acquisition Interview
Q 1. Explain the Defense Acquisition System lifecycle phases.
The Defense Acquisition System lifecycle is a structured process for developing and procuring defense systems. It’s designed to manage complexity, risk, and cost effectively. While specific names and phases might vary slightly across different nations and branches of service, a common framework includes these major phases:
- Materiel Solution Analysis (MSA): This initial phase focuses on defining the need, exploring potential solutions, and conducting preliminary analyses to determine feasibility and affordability. Think of it as laying the groundwork – defining the ‘what’ and ‘why’ before jumping into ‘how’.
- Technology Development (TD): This phase involves researching and developing technologies required for the system. It often includes prototyping and testing of critical components. This is where we address the technological challenges, ensuring that the solution is technically feasible.
- Engineering and Manufacturing Development (EMD): Here, a complete prototype is built and rigorously tested to verify performance and identify any remaining design flaws. This is essentially a final test drive before mass production.
- Production and Deployment (P&D): This phase involves mass production, delivery, and integration of the system into operational use. It includes training for personnel and establishing logistical support.
- Operations and Support (O&S): This post-production phase encompasses the system’s life cycle after deployment, including maintenance, upgrades, and eventual disposal. This phase is crucial for ensuring the system remains effective and reliable throughout its service life.
Each phase involves rigorous reviews and approvals to ensure the program stays on track and meets its objectives. Think of it like building a house – each phase represents a vital stage, from initial planning to final occupancy and ongoing maintenance.
Q 2. Describe your experience with Cost-Plus-Fixed-Fee contracts.
Cost-Plus-Fixed-Fee (CPFF) contracts are a type of cost-reimbursement contract where the contractor is reimbursed for all allowable costs up to a predetermined ceiling, plus a fixed fee that is established at the outset and is not subject to change regardless of the actual costs incurred.
In my experience, CPFF contracts are best suited for projects with a high degree of uncertainty or technical complexity, where the scope of work is not fully defined at the contract initiation. For example, I worked on a program developing a new advanced radar system. The specific technical challenges were not fully understood at the start, making a CPFF contract suitable because it allowed for flexibility in addressing unforeseen technical issues without jeopardizing the project’s completion.
However, a significant challenge with CPFF contracts is the potential for cost growth due to a lack of sufficient incentive for cost control by the contractor. Therefore, strong oversight, robust cost control mechanisms, and a clearly defined set of allowable costs are crucial for successful execution. I’ve found effective cost control requires detailed cost baselines, regular performance reviews, and close collaboration with the contractor. Transparency is key to managing this type of contract successfully.
Q 3. What is your experience with Earned Value Management (EVM)?
Earned Value Management (EVM) is a project management technique that integrates scope, schedule, and cost to provide a comprehensive assessment of project performance. It measures progress based on the value of the work completed, rather than just the time spent or resources consumed.
My experience with EVM has been extensive. I’ve used it across multiple defense acquisition programs to track performance against cost and schedule baselines. I’ve managed the development of EVM plans, established cost and schedule baselines, monitored performance indicators (like the Cost Performance Index (CPI) and Schedule Performance Index (SPI)), and reported performance to senior management.
For instance, on a recent program, we used EVM to identify a schedule slip early on. Through analysis of the earned value data, we pinpointed the source of the delay, which was due to unforeseen integration issues. This early detection allowed us to implement corrective actions, like bringing in additional resources, and ultimately mitigated further schedule slippage and cost overruns.
EVM is not just a tool for tracking; it is a critical instrument for proactive risk management. By continuously monitoring the CPI and SPI, we could anticipate potential problems and proactively mitigate them, rather than simply reacting to problems after they arise. Effective use of EVM relies on accurate data collection, proper reporting, and a willingness to address potential issues transparently.
Q 4. How do you manage risks in a defense acquisition program?
Risk management in defense acquisition is crucial because of the high cost, complexity, and potential consequences of failure. My approach involves a systematic process:
- Risk Identification: This involves brainstorming and systematically identifying potential risks across all aspects of the program – technical, cost, schedule, regulatory, and operational. Techniques like SWOT analysis and expert panels are helpful.
- Risk Assessment: Once identified, risks are assessed using a qualitative or quantitative approach, considering their likelihood and potential impact. A risk matrix helps visualize this.
- Risk Response Planning: Based on the assessment, a response plan is developed for each risk. This may include risk mitigation (reducing the likelihood or impact), risk avoidance (eliminating the risk entirely), risk transfer (shifting the risk to another party through insurance or contractual arrangements), or risk acceptance (accepting the risk and allocating resources to handle it if it occurs).
- Risk Monitoring and Control: Finally, risks are monitored throughout the program lifecycle. This requires regular review of risk registers, updated risk assessments, and adjustments to response plans as needed. This cyclical nature allows for flexibility and adjustment based on new developments.
I’ve successfully used this framework on numerous occasions, proactively identifying and mitigating potential problems that could have significantly impacted programs. A key element is fostering a culture of open communication and collaboration, encouraging individuals to openly identify and report potential risks early on.
Q 5. What are some common challenges in Defense Acquisition, and how have you addressed them?
Defense acquisition programs often face numerous challenges. Some of the most common include:
- Requirements Volatility: Changing operational needs, technological advancements, and evolving threat landscapes can lead to shifting requirements, adding complexity and cost.
- Technological Risk: Developing cutting-edge technologies often involves high uncertainty and potential for delays or failures.
- Cost Growth: Unforeseen technical issues, scope creep, and inflation can drive significant cost overruns.
- Schedule Slips: Delays due to technical challenges, supply chain disruptions, or bureaucratic hurdles are common.
I’ve addressed these challenges by employing several strategies: For requirements volatility, I advocate for robust requirements management processes and collaborative engagement with stakeholders. For technological risk, I emphasize thorough prototyping and testing, and employing incremental development approaches. For cost growth and schedule slips, I implement rigorous cost and schedule control, using tools like EVM and employing risk management techniques to identify and mitigate potential problems early on. Open communication and strong stakeholder engagement are vital throughout all stages.
Q 6. Describe your experience with source selection and proposal evaluation.
Source selection and proposal evaluation are critical steps in defense acquisition, ensuring the government selects the best contractor for the job. My experience spans the entire process, from developing evaluation criteria to conducting detailed proposal reviews and making source selection recommendations.
I’ve been involved in various source selection efforts, including competitive procurements where multiple vendors submitted proposals. A typical process includes defining clear and measurable evaluation criteria, developing a detailed evaluation plan, assembling an independent evaluation team, conducting thorough proposal reviews, and documenting the evaluation results. We often utilize weighted scoring systems to fairly compare proposals across multiple dimensions such as technical approach, management plan, past performance, and cost.
A crucial aspect is ensuring the evaluation process is fair, transparent, and objective. This requires careful adherence to government regulations and best practices. In one notable instance, I discovered a discrepancy in a proposal’s cost breakdown during our review. This was initially overlooked and could have led to a flawed selection. Thorough due diligence and a rigorous evaluation process allowed us to identify and address this concern before it compromised the outcome.
Q 7. Explain the importance of requirements management in Defense Acquisition.
Requirements management is fundamental to successful defense acquisition. Clearly defined, well-documented, and consistently managed requirements are the foundation upon which the entire acquisition process is built. Poor requirements management is a major contributor to cost overruns, schedule delays, and ultimately, system failure.
Effective requirements management ensures that the system being acquired meets the operational needs and addresses the intended threats. It involves several key activities: defining user needs, translating those needs into technical requirements, managing those requirements throughout the acquisition lifecycle, verifying that the delivered system meets the requirements, and ensuring traceability throughout the process.
Without clear and concise requirements, the program risks building the wrong system. Think of building a house without blueprints; the result may be structurally unsound and entirely unusable. My experience underscores the importance of actively engaging with stakeholders to understand their needs, leveraging requirements tracing tools to ensure complete traceability and using formal reviews and verification processes to ensure requirements are met throughout the system’s development.
Q 8. What is your experience with Integrated Product Teams (IPTs)?
Integrated Product Teams (IPTs) are cross-functional teams that bring together individuals from various disciplines – engineering, logistics, contracting, program management, and the end-user – to collaboratively work on a single product or system. My experience with IPTs spans over a decade, working on multiple major defense acquisition programs. I’ve found that a well-functioning IPT is crucial for effective communication, streamlined decision-making, and a shared sense of responsibility. In my previous role, I led an IPT responsible for the development of a new communication system. We faced challenges in integrating legacy systems, which we overcame through rigorous testing and collaborative problem-solving within the IPT. A key success factor was establishing clear roles, responsibilities, and communication protocols at the outset, which fostered a culture of shared ownership and accountability. We also utilized collaborative software tools that allowed team members to track progress, share documentation, and communicate in real time, even across different geographic locations.
One specific example involved resolving a critical software integration issue. Instead of assigning the problem to a single department, we leveraged the expertise within the IPT. The software engineers, systems integrators, and testers worked together, identifying the root cause and implementing a solution far more efficiently than a traditional departmental approach would have allowed. This highlights the value of diverse perspectives and collaborative problem-solving within an IPT environment.
Q 9. How do you ensure compliance with relevant regulations and laws in Defense Acquisition?
Compliance with regulations and laws in Defense Acquisition is paramount. It’s not just about avoiding penalties; it’s about ensuring the integrity of the process and maintaining public trust. My approach involves a multi-layered strategy. First, I familiarize myself with the relevant regulations from the outset, including the Federal Acquisition Regulation (FAR), Defense Federal Acquisition Regulation Supplement (DFARS), and any specific statutes applicable to the project. I also leverage the expertise of legal counsel to ensure all contractual agreements, procurement methods, and project execution comply with these regulations.
I implement a robust compliance program that includes regular audits and reviews of project documentation, ensuring all processes are documented and traceable. We also incorporate compliance considerations into every stage of the acquisition lifecycle, from initial planning to contract closeout. For example, we thoroughly vet potential vendors to ensure they meet the necessary security and ethical standards, and we regularly review the project’s progress to ensure it remains compliant with all relevant regulations. A proactive approach is key, rather than reacting to non-compliance after it has occurred. Finally, training and education for all team members on relevant regulations and best practices is also a critical component of my compliance strategy.
Q 10. Describe your experience with different acquisition strategies (e.g., sole source, competitive).
I have extensive experience with various acquisition strategies, including sole-source, competitive, and best-value procurements. The choice of strategy depends critically on the specific needs of the program and the available market conditions. Sole-source acquisitions are used when only one vendor can provide the required capability, often due to proprietary technology or national security concerns. This approach requires robust justification and documentation to ensure transparency and fairness.
Competitive procurements, on the other hand, leverage competition to drive innovation and cost savings. This involves issuing a Request for Proposal (RFP) to multiple vendors and rigorously evaluating their proposals based on pre-defined criteria. Best-value procurements balance cost and technical factors, providing flexibility in weighing different aspects of a proposal. I have managed both large-scale competitive bids involving multiple international companies, as well as smaller, more focused sole-source contracts where a particular vendor possessed essential expertise. In both scenarios, a clear understanding of the requirements, a well-defined evaluation process, and diligent contract management are key to success. Each acquisition strategy comes with its own set of challenges and requires a tailored approach to ensure effective outcomes.
Q 11. How do you manage stakeholder expectations in a complex acquisition program?
Managing stakeholder expectations in complex acquisition programs requires proactive communication, transparency, and a well-defined communication plan. Stakeholders can range from senior leadership and government officials to contractors, end-users, and even the public. Each group has unique interests and priorities. I begin by identifying all key stakeholders and understanding their specific concerns and expectations. Regular communication is critical, which I facilitate through various channels, including formal briefings, progress reports, and informal meetings. I strive to maintain open communication channels and ensure that information is accurate, timely, and consistent across all stakeholders.
When expectations are unrealistic or conflicting, I facilitate open dialogue to identify potential solutions. This can involve negotiating priorities, adjusting timelines, or modifying requirements. Transparency is vital in managing expectations; when challenges arise, I communicate them honestly and proactively, offering potential mitigation strategies. Building trust and credibility is key to effectively managing stakeholder expectations. Using data-driven analysis to support decisions and transparently communicating both successes and challenges earns credibility and fosters understanding, which is critical for navigating complex situations. Finally, regularly soliciting feedback from stakeholders is essential to adapt strategies as the program evolves.
Q 12. What is your experience with configuration management?
Configuration management (CM) is a crucial aspect of defense acquisition, ensuring that all aspects of a system – hardware, software, documentation – remain consistent and traceable throughout its lifecycle. My experience with CM involves implementing and managing CM plans and procedures, adhering to standards such as MIL-STD-480. I’ve worked extensively with CM tools to track changes, manage baselines, and control modifications. This involves establishing a baseline configuration, tracking changes through a formal change control process, and maintaining comprehensive documentation.
A key aspect of my CM approach is fostering a culture of CM awareness within the project team. This involves training team members on CM procedures and ensuring they understand the importance of properly documenting changes. Effective CM minimizes errors, reduces rework, and helps ensure that the system meets its intended requirements. For instance, in a previous project, we encountered a significant software bug late in the development cycle. Our rigorous CM processes allowed us to quickly identify the source of the error, isolate the affected components, and implement a solution with minimal disruption to the overall schedule. This underscores the importance of CM in preventing costly delays and ensuring the delivery of a quality product.
Q 13. Explain your understanding of life-cycle cost estimation.
Life-cycle cost estimation is the process of predicting all costs associated with a system or program throughout its entire lifespan, from research and development to disposal. It’s a critical aspect of decision-making in defense acquisition, as it informs resource allocation and helps evaluate the overall value of a program. My approach to life-cycle cost estimation involves a structured process: First, we define the scope and boundaries of the cost estimation, clearly identifying the system’s components and lifecycle phases. Then, we develop detailed cost breakdowns for each phase, using various estimation techniques –parametric modeling, analogous estimating, and bottom-up costing.
Uncertainty analysis is a crucial element; we employ statistical methods to quantify the uncertainty associated with the estimates, providing a range of possible costs rather than a single point estimate. This allows stakeholders to understand the risks involved and make informed decisions. We also incorporate contingency reserves to account for unforeseen events. Finally, the estimates are regularly reviewed and updated as the program progresses to reflect the latest information and lessons learned. I have consistently used this multi-faceted approach to deliver accurate and reliable cost estimates, guiding strategic decisions and ensuring effective resource allocation for numerous defense acquisition programs. An example includes estimating the total ownership cost for a fleet of vehicles including operational costs, maintenance, fuel consumption and disposal costs.
Q 14. How do you handle schedule delays and cost overruns in a defense acquisition project?
Schedule delays and cost overruns are common challenges in defense acquisition projects. My approach to handling these involves a proactive and systematic strategy. First, I establish a robust project management framework with clearly defined milestones, deliverables, and responsibilities. Regular monitoring and tracking of progress against the baseline plan are essential. When delays or cost overruns occur, I immediately initiate a thorough investigation to identify the root causes. This often involves analyzing the project’s performance, identifying areas of inefficiency, and assessing the impact of external factors.
Once the root causes are understood, I develop a recovery plan that includes corrective actions and mitigation strategies. This may involve adjusting the project schedule, renegotiating contracts, or reallocating resources. Stakeholder communication is crucial; I keep all stakeholders informed of the situation and the proposed recovery plan, ensuring transparency and collaboration. For example, in a past project, we encountered a significant delay due to supplier issues. We immediately engaged with the supplier, renegotiated the contract to include incentives for expedited delivery, and implemented stricter quality control measures to prevent future delays. This proactive approach allowed us to mitigate the impact of the delay and ultimately deliver the project on time and within budget. Continuous monitoring and adaptive planning are critical for preventing further issues and ensuring project success.
Q 15. Describe your experience with technical performance measurement.
Technical performance measurement in Defense Acquisition is crucial for ensuring programs stay on track, within budget, and deliver the promised capabilities. It involves establishing clear metrics, consistently monitoring progress against those metrics, and making data-driven adjustments as needed. This isn’t simply about tracking numbers; it’s about understanding the why behind those numbers and identifying potential problems early.
In my experience, I’ve utilized various methods, including Earned Value Management (EVM) which integrates scope, schedule, and cost performance. For example, on a recent missile defense system program, we used EVM to track the completion of critical design reviews, subsystem testing milestones, and integration events. Any variance from the planned schedule or budget was immediately investigated to determine root causes and implement corrective actions. Beyond EVM, we also used Key Performance Indicators (KPIs) focused on specific technical achievements, such as achieving a certain level of software maturity or meeting specific performance requirements in testing. Regular reporting and analysis of these KPIs enabled us to proactively identify and address potential risks.
Effective technical performance measurement requires a collaborative effort. It necessitates clear communication between program managers, engineers, contractors, and other stakeholders. Regular review sessions and progress reports help ensure everyone is aligned and informed. Further, I’ve found that data visualization tools are invaluable in presenting complex information in a clear and concise manner, facilitating better decision-making.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. What is your familiarity with the Defense Federal Acquisition Regulation Supplement (DFARS)?
My familiarity with the Defense Federal Acquisition Regulation Supplement (DFARS) is extensive. I’ve worked extensively with it throughout my career, focusing on its impact on various aspects of the acquisition process, from contract writing and administration to cybersecurity and data rights. The DFARS is the cornerstone of defense acquisition, providing the legal framework for all aspects of acquiring goods and services for the Department of Defense (DoD).
I understand the intricacies of clauses related to cost accounting standards, cybersecurity requirements (like NIST SP 800-171), and the complexities of intellectual property rights. For example, I’ve been directly involved in negotiating contract clauses related to data security, ensuring compliance with DFARS 252.204-7012. This often involves working with contractors to develop and implement robust cybersecurity plans that meet DoD standards. Understanding the DFARS is vital for ensuring legal and regulatory compliance throughout the acquisition lifecycle, minimizing risks, and protecting taxpayer dollars.
My experience extends to staying current with updates and changes to the DFARS. The regulatory environment is constantly evolving, and staying abreast of these changes is paramount for effective acquisition management. I actively participate in professional development opportunities to maintain my knowledge of the DFARS and its implications for defense acquisition programs.
Q 17. How do you ensure the quality of deliverables in Defense Acquisition?
Ensuring the quality of deliverables in Defense Acquisition requires a multi-faceted approach that begins long before the final product is delivered. It’s about building quality into the process from the start. This involves a strong emphasis on requirements definition, rigorous testing and evaluation, and continuous monitoring throughout the acquisition lifecycle.
- Robust Requirements Definition: Clearly defined and validated requirements are the foundation of quality. Ambiguous or incomplete requirements lead to costly rework and potential performance shortfalls. We use techniques like Model-Based Systems Engineering (MBSE) to ensure requirements are comprehensive and consistent.
- Independent Verification and Validation (IV&V): Independent assessment by a separate team is crucial for identifying defects that might be missed by the developing organization. This ensures an objective evaluation of the system’s performance and adherence to requirements.
- Rigorous Testing and Evaluation: A comprehensive testing strategy, encompassing unit, integration, and system-level testing, is essential to identify and resolve defects early in the development process. This includes both laboratory and field testing to validate the system’s performance in real-world conditions.
- Continuous Monitoring and Improvement: Continuous monitoring of the development process, through regular reviews and audits, helps identify and address potential quality issues proactively. We utilize tools and techniques like statistical process control to track performance and identify trends.
For example, on a recent project, implementing rigorous test procedures uncovered a critical software flaw during integration testing, preventing it from impacting the final product. This highlights the importance of building quality throughout the acquisition process, and not simply relying on end-of-process inspections.
Q 18. What is your experience with contract negotiations?
Contract negotiations in Defense Acquisition are complex and often involve high-stakes decisions. My experience encompasses all phases, from initial proposal review to final contract award and subsequent modifications. It’s about more than just price; it’s about achieving a balanced agreement that protects the government’s interests while fostering a productive relationship with the contractor.
I utilize a collaborative, yet firm, approach. This includes thorough preparation, understanding the contractor’s capabilities and motivations, and clearly articulating the government’s needs and expectations. I leverage my expertise in cost and schedule analysis to identify potential risks and develop strategies for mitigation. I’ve successfully negotiated contracts involving complex technical requirements, incentivized performance-based contracts, and cost-plus contracts, adapting my approach depending on the specific circumstances of each acquisition.
One specific example involved negotiating a contract for a new communication system. Through rigorous analysis of the contractor’s proposal, we identified inconsistencies and potential cost overruns. This led to a renegotiation resulting in a more cost-effective agreement while ensuring the system met all critical performance requirements. Effective contract negotiation is not about confrontation, but about creating a mutually beneficial agreement that secures the best value for the government.
Q 19. How do you manage international cooperation in Defense Acquisition?
Managing international cooperation in Defense Acquisition requires a nuanced understanding of differing national priorities, regulations, and security concerns. It often involves navigating complex legal frameworks and cultural sensitivities. My experience involves collaborating with international partners on joint acquisition programs, requiring strong communication, diplomacy, and a deep awareness of international relations.
Effective international cooperation starts with clearly defined roles and responsibilities. We use formal agreements to outline each partner’s contribution and establish mechanisms for resolving disputes. This often includes establishing joint program offices, staffed by representatives from all participating nations. Transparent communication and regular meetings are essential to maintain alignment and address emerging issues proactively. It’s also critical to consider intellectual property rights, technology transfer agreements, and export control regulations.
For instance, I was part of a team that collaborated with a European ally on the development of a new radar system. Successfully navigating the differences in procurement regulations, export control requirements, and technological standards required careful planning, diplomatic engagement, and a deep understanding of each country’s regulations. Successful collaboration resulted in a system that met both our countries’ requirements, strengthening our defense relationship in the process.
Q 20. Explain your experience with technology insertion and obsolescence management.
Technology insertion and obsolescence management are critical aspects of maintaining the operational effectiveness and longevity of defense systems. Obsolescence, the process by which a technology becomes outdated or unsupported, presents a significant challenge. My experience involves developing strategies to mitigate these risks and integrate new technologies to enhance capabilities.
Technology insertion requires careful planning and execution. We use a phased approach, evaluating new technologies for compatibility and performance before integrating them into existing systems. Rigorous testing and analysis are critical to ensure the new technology meets the required performance standards and doesn’t introduce new vulnerabilities. Obsolescence management involves proactively identifying components nearing end-of-life, developing replacement plans, and managing the transition process to minimize disruption to operational capabilities.
A prime example from my experience involves upgrading the avionics systems on a fleet of fighter aircraft. By proactively identifying at-risk components and collaborating with industry partners, we successfully implemented a phased upgrade program that minimized downtime and ensured the aircraft remained operationally effective. This included not only hardware but also software updates and integration of new capabilities.
Q 21. Describe your experience with independent program assessments.
Independent program assessments provide an objective evaluation of a defense acquisition program’s progress, performance, and risks. These assessments, often conducted by external experts, provide valuable insights that can inform decision-making and help identify areas for improvement. My experience includes both participating in and managing independent program assessments.
My role has involved coordinating with assessment teams, providing necessary data and documentation, and addressing questions and concerns raised during the assessment. This requires transparency and a willingness to address potential shortcomings. The results of these assessments often highlight areas where the program can be improved, either through process adjustments or technological improvements. I’ve found that these assessments, while sometimes challenging, are crucial for enhancing program success.
A recent example involved an independent assessment of a new communication satellite program. The assessment identified potential integration challenges and recommended changes to the testing plan. By addressing these issues proactively, we were able to avoid potential delays and cost overruns, demonstrating the value of independent assessments in identifying and mitigating program risks.
Q 22. How do you ensure cybersecurity in a defense acquisition program?
Cybersecurity in defense acquisition is paramount. It’s not just about protecting the final product; it’s about securing the entire lifecycle, from initial design and development through deployment and disposal. We must consider threats at every stage.
- Early Integration: Cybersecurity should be baked into the system from the very beginning, not bolted on as an afterthought. This involves incorporating secure coding practices, vulnerability assessments throughout development, and using secure hardware components.
- Supply Chain Security: A significant vulnerability lies within the supply chain. We need rigorous vetting of all vendors and suppliers, ensuring they adhere to stringent security standards and have robust security practices in place. This includes regular audits and monitoring for suspicious activities.
- Threat Modeling: Proactive threat modeling helps anticipate potential cyberattacks. By identifying vulnerabilities early, we can design more resilient systems. This involves simulating attacks to identify weaknesses.
- Continuous Monitoring: Post-deployment, continuous monitoring and threat intelligence are vital. This requires robust intrusion detection and prevention systems, as well as mechanisms for timely response to security incidents. Regular penetration testing is crucial.
- Compliance: Adhering to relevant cybersecurity standards and regulations, such as NIST Cybersecurity Framework, is non-negotiable. This ensures consistent security practices across the acquisition program.
For example, in a recent project involving the acquisition of a new communication system, we integrated secure boot processes, implemented regular vulnerability scans, and included a robust intrusion detection system from the earliest stages of development. This proactive approach significantly reduced the risk of cyber breaches.
Q 23. What is your experience with working with government oversight agencies?
I’ve worked extensively with various government oversight agencies, including the Defense Contract Audit Agency (DCAA), the Defense Contract Management Agency (DCMA), and the Government Accountability Office (GAO). My experience spans numerous programs and involves navigating diverse regulatory landscapes.
- DCAA Audits: I’ve successfully managed multiple DCAA audits, ensuring compliance with cost accounting standards and providing transparent documentation of all financial transactions. This involved proactive preparation and diligent record-keeping.
- DCMA Oversight: I’ve collaborated effectively with DCMA representatives, providing regular progress reports and addressing any concerns promptly and professionally. This included ensuring compliance with contractual obligations and providing access to necessary information.
- GAO Reviews: I’ve participated in GAO reviews, offering clear explanations of program decisions and justifying resource allocations. This required demonstrating a clear understanding of program goals and how resources contribute to achieving those goals.
These interactions have honed my ability to understand and anticipate government requirements, manage expectations, and maintain effective working relationships with oversight bodies. It’s crucial to be transparent, responsive, and meticulously document every aspect of the acquisition process.
Q 24. How do you foster collaboration and communication among diverse teams in Defense Acquisition?
Fostering collaboration in defense acquisition, with its inherently diverse teams (contractors, government personnel, subcontractors, etc.), requires deliberate effort. It’s about establishing a shared vision, promoting open communication, and creating a culture of trust.
- Clear Communication Channels: Establishing clear and consistent communication channels, utilizing tools like project management software and regular meetings, is critical. This ensures everyone is informed and aligned.
- Shared Goals and Objectives: A well-defined project charter and clear articulation of program goals and objectives are crucial for aligning diverse teams around a shared purpose.
- Regular Meetings and Collaboration Tools: Utilizing collaborative platforms and conducting regular meetings, including those involving all stakeholders, keeps teams informed and facilitates quick problem-solving.
- Conflict Resolution Mechanisms: Establishing clear processes for addressing conflicts and disagreements is crucial to maintaining a healthy working environment. This involves promoting open dialogue and finding mutually acceptable solutions.
- Team Building Activities: Engaging team building exercises can improve communication and collaboration among team members, fostering better working relationships.
For instance, on a recent program, we implemented a weekly all-hands meeting that included representatives from all stakeholder groups. This facilitated early identification and resolution of potential issues, preventing costly delays.
Q 25. Describe your experience with developing and implementing acquisition strategies.
Developing and implementing acquisition strategies involves a thorough understanding of program requirements, available resources, and potential risks. It’s a systematic process that balances cost, schedule, and performance.
- Needs Analysis: A comprehensive needs analysis is the cornerstone of any effective acquisition strategy. This identifies the specific capabilities required, translating operational needs into technical specifications.
- Market Research: Thorough market research identifies potential vendors, assesses their capabilities, and evaluates various acquisition approaches (e.g., sole-source, competitive bidding).
- Risk Assessment and Mitigation: Identifying and mitigating potential risks (technical, cost, schedule) is critical. Developing contingency plans for unforeseen challenges ensures program success.
- Acquisition Strategy Selection: Choosing the right acquisition approach (e.g., fixed-price, cost-plus) depends on program specifics and risk tolerance. This involves careful consideration of trade-offs.
- Contract Negotiation: Negotiating fair and equitable contracts with vendors is a crucial element, ensuring compliance with legal and regulatory requirements.
In a recent project, we opted for a phased acquisition approach, allowing for incremental development and testing, reducing overall program risk and allowing for adjustments based on evolving requirements.
Q 26. Explain your approach to identifying and mitigating risks in the supply chain.
Supply chain risk management is critical in defense acquisition. It’s about identifying and mitigating potential disruptions to the flow of materials, components, and services that can impact program cost, schedule, and performance.
- Vendor Risk Assessment: Rigorous assessment of vendors includes evaluating their financial stability, technical capabilities, and security practices. This may involve on-site audits and background checks.
- Diversification: Reducing reliance on single sources for critical components helps mitigate the impact of potential disruptions. This involves identifying alternative suppliers and developing backup plans.
- Contractual Safeguards: Contracts should include clauses addressing potential supply chain disruptions, including provisions for timely delivery and penalties for non-compliance.
- Monitoring and Surveillance: Continuous monitoring of the supply chain helps identify potential issues early. This may involve tracking key metrics and actively engaging with suppliers.
- Cybersecurity Considerations: Protecting the supply chain from cyber threats is crucial. This involves securing vendor systems and communications, and implementing robust cybersecurity protocols.
In one instance, we identified a potential risk of a single-source supplier for a critical component. We proactively engaged with alternative vendors, successfully diversifying our supply chain and mitigating the risk of delays.
Q 27. How do you utilize data analytics to inform decision-making in Defense Acquisition?
Data analytics plays a crucial role in informing decision-making in defense acquisition. It provides insights into program performance, cost trends, and potential risks, allowing for data-driven decision-making.
- Cost Estimation: Data analytics helps refine cost estimates, improving accuracy and reducing uncertainty. This involves analyzing historical data, market trends, and other relevant factors.
- Schedule Management: Analyzing project timelines and identifying potential delays helps optimize schedules and improve project execution.
- Risk Management: Data analytics can identify potential risks and vulnerabilities early on, allowing for proactive mitigation strategies.
- Performance Monitoring: Tracking key performance indicators (KPIs) provides insights into program performance and helps identify areas for improvement.
- Predictive Modeling: Using predictive models can forecast potential outcomes, assisting in strategic planning and resource allocation.
For example, by analyzing historical data on similar projects, we were able to more accurately predict cost and schedule overruns, allowing for proactive mitigation measures.
Q 28. Describe your experience with the transition from development to production in a defense acquisition project.
The transition from development to production in a defense acquisition project is a critical phase requiring careful planning and execution. It’s about ensuring a smooth transfer of technology and processes, with minimal disruption.
- Production Readiness Review: A thorough Production Readiness Review (PRR) assesses the readiness of the system for production. This involves verifying that all design and development aspects are complete and meet requirements.
- Manufacturing Process Validation: Validating the manufacturing processes ensures consistent production quality and reliability. This may involve pilot runs and quality control inspections.
- Testing and Verification: Rigorous testing and verification of production units confirm that they meet the required specifications and performance standards.
- Supply Chain Management: Establishing a robust supply chain for production is crucial to ensure timely delivery of materials and components.
- Documentation and Training: Comprehensive documentation and training for production personnel are essential for a smooth transition.
During a recent program, we conducted rigorous testing and established a comprehensive quality control system before transitioning to production. This resulted in a smooth transition with minimal defects and delays.
Key Topics to Learn for Defense Acquisition Interview
- Acquisition Life Cycle Management: Understand the phases (materiel solution analysis, technology development, production and deployment, operations and sustainment, and disposal) and their interdependencies. Consider how each phase contributes to overall program success and risk mitigation.
- Cost Estimation and Budgeting: Explore various cost estimation techniques and their applications in Defense Acquisition. Practice analyzing cost proposals and identifying potential cost overruns or savings opportunities. Develop an understanding of budget constraints and their impact on program decisions.
- Source Selection and Contract Management: Familiarize yourself with different contract types (e.g., firm-fixed-price, cost-plus-fixed-fee) and their implications for risk allocation and program execution. Practice evaluating proposals and selecting the most suitable contractor based on predefined criteria.
- Risk Management in Defense Acquisition: Learn to identify, assess, and mitigate risks throughout the acquisition life cycle. Understand the importance of proactive risk management in ensuring program success and cost control. Develop strategies for communicating and responding to identified risks.
- Program Planning and Scheduling: Master the techniques involved in creating and managing program schedules, including critical path analysis and Earned Value Management (EVM). Practice analyzing schedules for potential delays and developing mitigation plans.
- Technology Development and Transition: Understand the processes involved in transitioning new technologies from research and development into operational systems. This includes considerations for technology maturation, testing, and integration into existing systems.
- Defense Acquisition Regulations (DAR): Gain a working knowledge of relevant acquisition regulations and policies to demonstrate compliance and ethical conduct. Focus on understanding how these regulations impact decision-making and program execution.
Next Steps
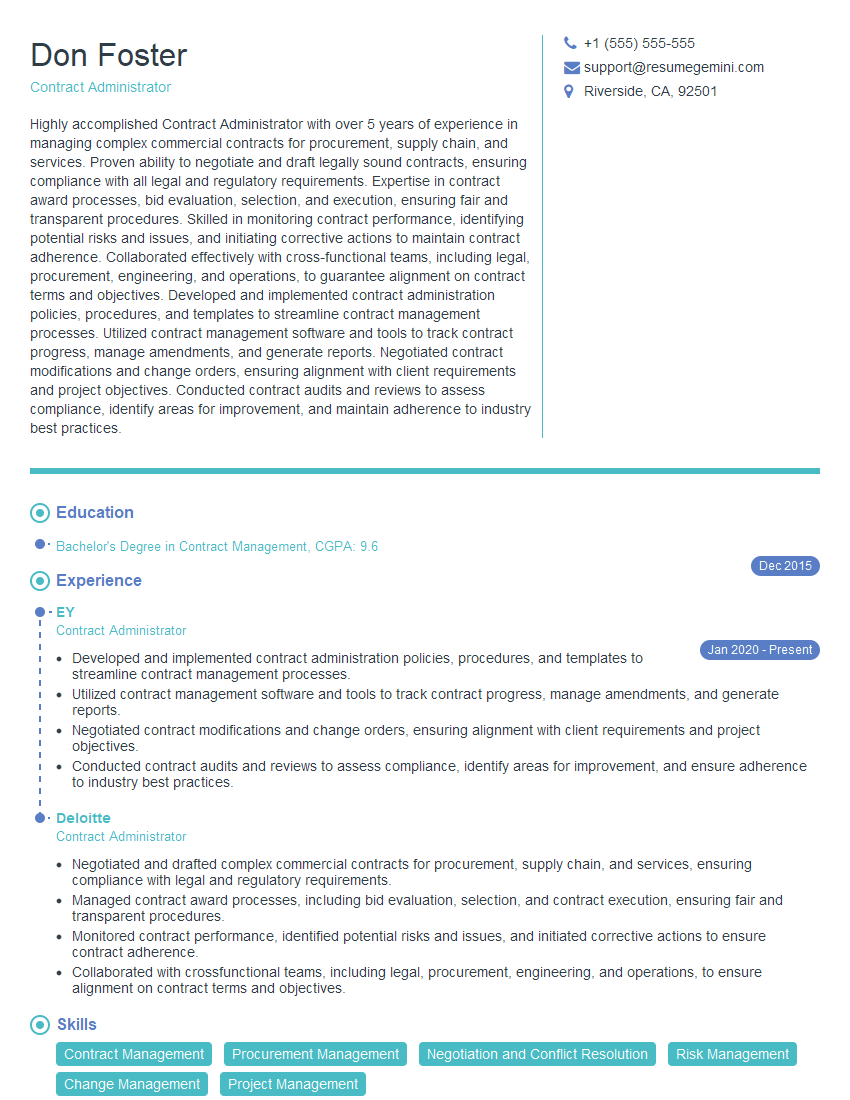
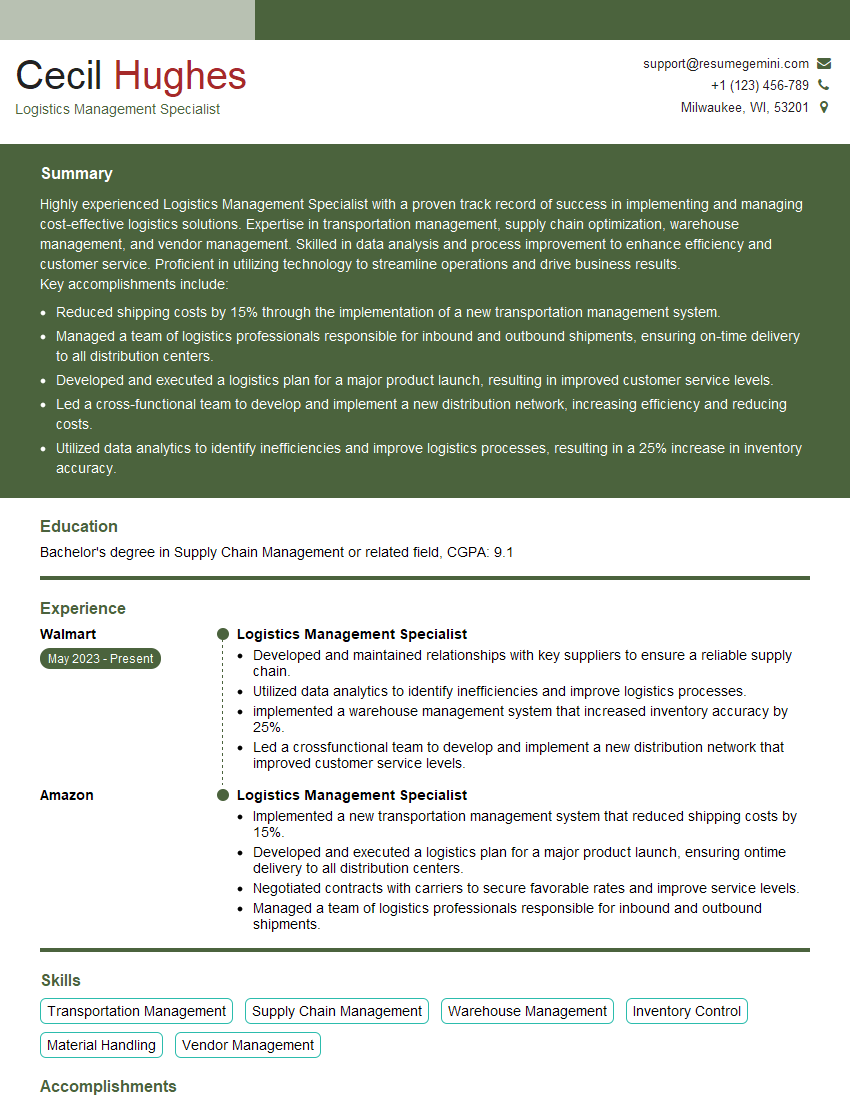
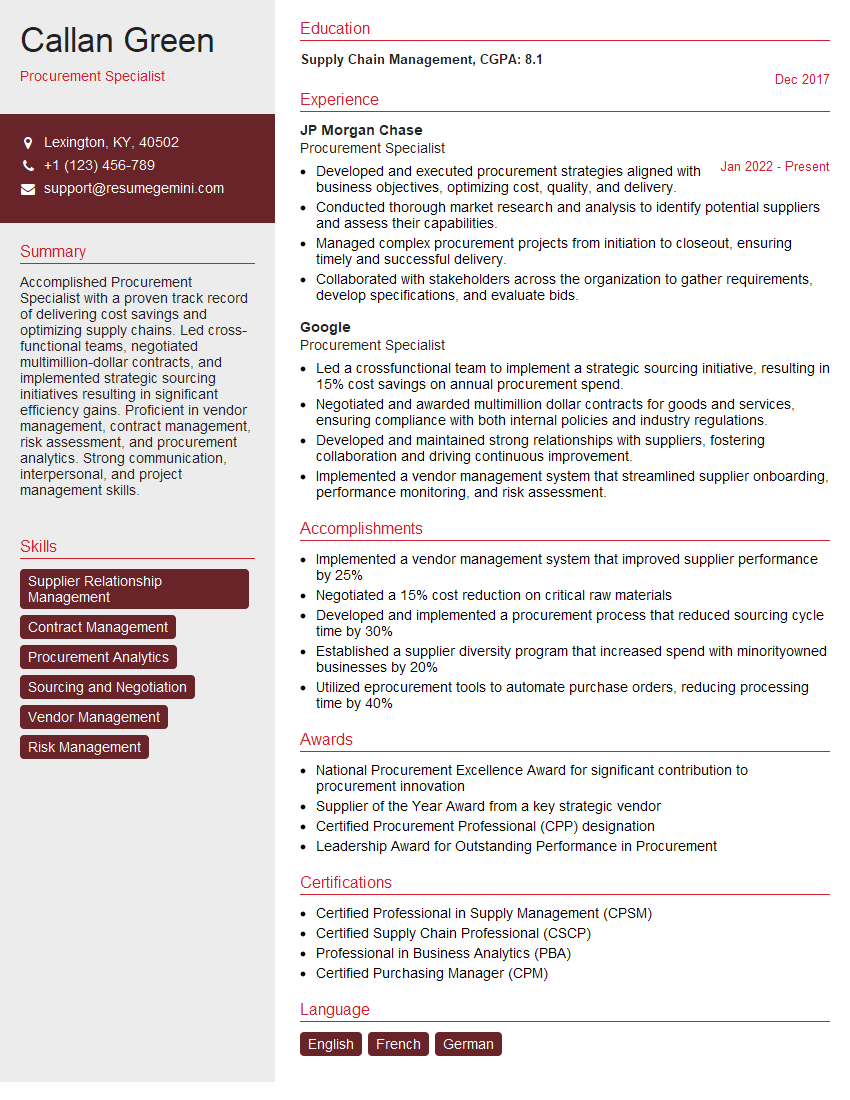
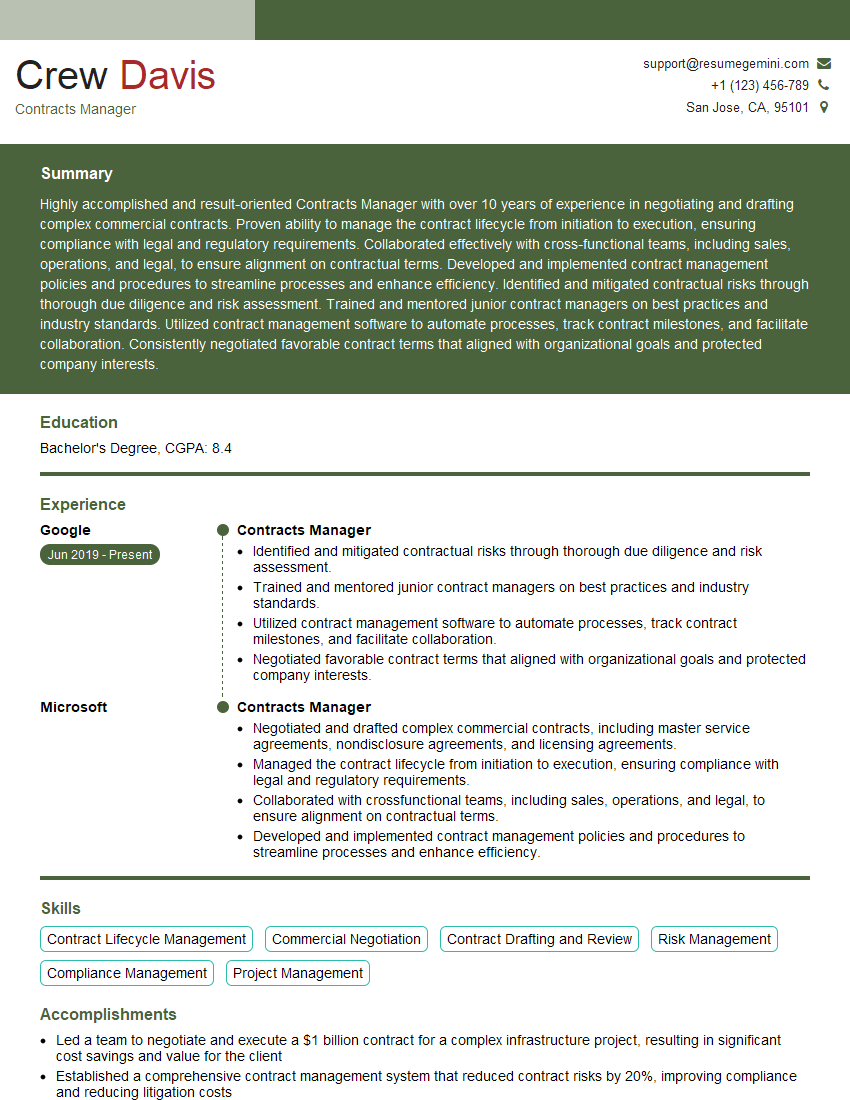
Mastering Defense Acquisition principles significantly enhances your career prospects, opening doors to challenging and rewarding roles within the defense industry and government. A strong, ATS-friendly resume is crucial for showcasing your skills and experience to potential employers. To create a truly impactful resume that highlights your qualifications for Defense Acquisition positions, leverage the power of ResumeGemini. ResumeGemini provides a user-friendly platform to craft professional resumes, and we offer examples of resumes specifically tailored to the Defense Acquisition field to guide you. Take the next step towards your dream career – build your best resume with ResumeGemini.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good