Feeling uncertain about what to expect in your upcoming interview? We’ve got you covered! This blog highlights the most important Incident Triage and Escalation Procedures interview questions and provides actionable advice to help you stand out as the ideal candidate. Let’s pave the way for your success.
Questions Asked in Incident Triage and Escalation Procedures Interview
Q 1. Describe your experience with incident triage methodologies.
Incident triage methodologies are the processes used to quickly assess and categorize incoming incidents to determine their urgency and impact. Think of it as a first responder’s initial assessment at an accident scene – they need to quickly determine the severity before deciding how to proceed. My experience encompasses several approaches, including:
- Prioritization Matrices: Using a matrix that plots severity against urgency to prioritize incidents. For example, a high-severity, low-urgency issue might be a planned system outage, while a low-severity, high-urgency issue could be a minor performance degradation impacting many users.
- Categorization and Routing: Sorting incidents based on their type (e.g., network, application, security) and routing them to the appropriate teams. This might involve using keywords in incident tickets or automated routing based on pre-defined rules.
- Root Cause Analysis (RCA) during Triage: In some cases, initial triage can include a preliminary RCA to get a clearer picture of the problem and aid faster resolution. This is particularly useful when the problem is readily identifiable.
For example, in my previous role, we implemented a prioritization matrix that classified incidents based on impact (number of users affected) and urgency (time to resolution). This allowed us to focus resources on the most critical issues first, ensuring efficient resolution of high-impact outages before addressing less critical ones.
Q 2. Explain the process of escalating an incident.
Escalating an incident means moving it to a higher level of support or to a more senior team member when the initial team lacks the resources or expertise to resolve it effectively. This is crucial to ensure that critical incidents receive the attention they need.
The escalation process typically involves:
- Identifying the need for escalation: This happens when the incident is beyond the capabilities of the first-response team, the incident’s impact is severe, or the initial troubleshooting steps have failed.
- Notifying the appropriate team or individual: This often involves using a communication tool like Slack, email, or a dedicated incident management system.
- Providing context and relevant information: The escalation should include detailed information about the incident, including symptoms, steps already taken, and any relevant logs or error messages. The more information provided upfront, the better the higher team can understand and address the issue.
- Following up: After escalation, it is important to follow up with the receiving team to ensure they are working on the issue and to receive regular updates.
A real-world example would be a major network outage. The first-line support team may identify the problem but lack the authority or expertise to resolve a complex routing issue. They would then escalate the incident to the network engineering team, providing them with detailed network logs and topology diagrams.
Q 3. What criteria do you use to prioritize incidents?
Incident prioritization relies on several key criteria, aiming to focus resources on the most impactful issues first. I typically use a combination of:
- Impact: How many users are affected? A widespread outage impacting thousands of users is obviously higher priority than a problem impacting a single user.
- Urgency: How quickly does the issue need to be resolved? A critical system failure requiring immediate attention takes precedence over a minor bug with a low impact.
- Business Criticality: Does the incident affect a core business function? An outage to the payment processing system is far more critical than a problem with a non-essential internal tool.
- Severity: How severe is the impact of the incident on the system or data? Data loss or corruption would have a higher priority than a minor performance issue.
We often use a prioritization matrix, as mentioned before. This helps ensure a standardized and objective approach across the team. For example, a system outage that stops all sales transactions (high impact, high urgency) would be assigned a much higher priority than a slow login screen (low impact, low urgency), even if the latter might affect many users.
Q 4. How do you determine the severity of an incident?
Determining the severity of an incident requires careful consideration of its potential consequences. I generally use a scale that considers:
- Data Loss or Corruption: The potential for data loss or corruption is a significant severity factor. The more data at risk, the higher the severity.
- System Downtime: How long is the system unavailable? Extended downtime significantly impacts severity.
- Financial Impact: What is the potential cost of the downtime or data loss? This is especially important for businesses that rely on their systems for revenue generation.
- Reputational Risk: Does the incident risk damaging the company’s reputation? Public-facing outages can lead to significant reputational harm.
- Regulatory Compliance: Does the incident violate any regulatory requirements or industry standards?
For example, a security breach resulting in customer data exposure would be considered extremely high severity due to the potential for financial loss, reputational damage, and legal ramifications. A minor application bug impacting only a few users, with no data loss, would be categorized as low severity.
Q 5. What tools or systems have you used for incident management?
Throughout my career, I’ve used a variety of tools and systems for incident management. Some examples include:
- ServiceNow: A comprehensive IT Service Management (ITSM) platform offering robust incident management capabilities, including ticketing, escalation workflows, and reporting.
- Jira Service Desk: A popular issue tracking and service desk solution that is frequently used for incident management, especially in software development environments.
- PagerDuty: An on-call management and incident response platform that excels at notifying and coordinating response teams during critical events.
- Opsgenie: Similar to PagerDuty, a powerful platform for on-call scheduling and alerting.
- Datadog: A monitoring and analytics platform that can be integrated with incident management systems to provide real-time visibility into system performance and facilitate faster incident identification and resolution.
The specific tools used depend heavily on the organization’s size and the complexity of its IT infrastructure.
Q 6. Describe your experience with incident ticketing systems.
Incident ticketing systems are the backbone of efficient incident management. They provide a structured way to track and manage incidents from initial report to resolution. My experience with these systems includes:
- Ticket creation and assignment: Creating clear and concise tickets with all relevant details, and assigning tickets to the appropriate teams or individuals.
- Tracking progress and updates: Using the system to monitor the progress of incidents, recording updates, and ensuring timely resolution.
- Escalation management: Leveraging the ticketing system’s workflow capabilities to automatically escalate incidents to higher levels of support as needed.
- Reporting and analysis: Using data from the ticketing system to identify trends, improve processes, and measure the effectiveness of incident response.
For example, I’ve used Jira Service Desk extensively to manage tickets, automate workflows, and generate reports on incident resolution times and types. A well-maintained ticketing system ensures accurate tracking, improves communication, and facilitates post-incident analysis.
Q 7. How do you communicate updates to stakeholders during an incident?
Effective communication with stakeholders during an incident is critical. I employ a multi-pronged approach:
- Regular updates: Provide regular updates on the status of the incident, including the problem, the steps being taken, and the estimated time to resolution. Frequency depends on the severity of the incident—more frequent updates for high-severity incidents.
- Multiple communication channels: Depending on the audience and the nature of the update, I use email, Slack, SMS messaging, and potentially even a dedicated communication portal for large-scale events.
- Transparent communication: Be upfront about what is known and unknown, and avoid providing misleading or overly optimistic information. Honesty builds trust and helps manage expectations.
- Targeted communication: Tailor communications to the specific needs and technical understanding of each audience. Technical details are important for engineers, while non-technical summaries are best suited for business stakeholders.
- Post-incident report: After the incident is resolved, publish a comprehensive report summarizing the incident, its cause, the steps taken to resolve it, and any lessons learned. This helps improve future response and prevent recurrence.
Imagine a website outage. I’d provide regular updates to customers via a status page, detailed technical updates to the development team through Slack, and concise summaries to senior management via email. This targeted approach ensures everyone receives the necessary information in a timely and appropriate manner.
Q 8. How do you handle multiple incidents simultaneously?
Handling multiple incidents simultaneously requires a systematic approach prioritizing urgency and impact. Think of it like a triage nurse in a busy emergency room – you need to assess the severity of each case and allocate resources effectively.
- Prioritization: I use a matrix that considers the impact of the incident (business criticality) and the urgency (time to resolution). This allows me to quickly identify which incidents require immediate attention and which can be handled later.
- Delegation: If possible, I delegate less critical incidents to other qualified team members. This ensures that no single person becomes overwhelmed and maintains overall team efficiency.
- Communication: Open and frequent communication with stakeholders is crucial. Keeping everyone informed about the status of each incident prevents duplicated efforts and minimizes confusion.
- Tools: I leverage incident management tools that allow for efficient tracking and assignment of tasks, providing a clear overview of all active incidents. These tools often incorporate features such as automated alerts and escalation pathways.
For example, if we have a critical outage affecting a major customer application alongside several minor performance issues, I would focus my immediate efforts on resolving the critical outage first, while assigning the smaller incidents to other team members. Regular status updates would keep everyone aligned.
Q 9. How do you ensure accurate incident documentation?
Accurate incident documentation is the cornerstone of effective incident management. It’s not just about recording what happened; it’s about creating a clear, concise, and actionable record that can be used for future analysis and prevention.
- Standardized Templates: We use pre-defined templates to ensure consistency and completeness. These templates usually include fields for the incident summary, impact, affected systems, resolution steps, root cause analysis, and lessons learned.
- Detailed Steps: Every step taken during the incident resolution process is documented, including timestamps and the individuals involved. This helps in recreating the sequence of events and identifying potential bottlenecks.
- Objective Language: Documentation should avoid subjective opinions and focus on factual information. It should be easy to understand, even by someone unfamiliar with the incident.
- Version Control: Using a system with version control ensures that changes are tracked and the history of the incident is preserved. This prevents confusion and ensures accuracy.
Imagine a situation where an incident involved multiple teams and occurred over several hours. A well-documented incident report will be invaluable in identifying the sequence of events and determining the root cause, preventing similar issues in the future.
Q 10. Explain your approach to root cause analysis after an incident.
My approach to root cause analysis (RCA) is systematic and data-driven, using the '5 Whys' technique along with other analytical methods.
- Gather Data: The first step involves collecting all relevant data from the incident logs, monitoring tools, and affected teams. This helps to build a comprehensive understanding of what happened.
- 5 Whys: This iterative technique involves asking 'why' repeatedly until the root cause is identified. For example: Why did the server crash? (Lack of memory) Why did it lack memory? (Memory leak in application X) Why was there a memory leak? (Faulty code) Why was the faulty code deployed? (Insufficient testing).
- Fishbone Diagram (Ishikawa): This visual tool helps to brainstorm potential root causes and their contributing factors. It organizes causes by category (people, methods, materials, machines, environment, measurement).
- Documentation: The findings of the RCA should be meticulously documented, including the root cause, contributing factors, and recommended corrective actions.
A recent incident involving a database outage highlighted the value of a thorough RCA. By repeatedly asking ‘why,’ we uncovered a configuration error in the database replication setup, not just the immediate symptom of the outage. This led to revised procedures and improved monitoring, preventing future occurrences.
Q 11. What metrics do you track to measure incident management effectiveness?
Several key metrics help measure incident management effectiveness. These metrics provide insights into our performance and highlight areas for improvement.
- Mean Time To Acknowledge (MTTA): How quickly incidents are acknowledged.
- Mean Time To Resolution (MTTR): The average time taken to resolve an incident.
- Incident Frequency: The number of incidents occurring over a given period.
- Mean Time Between Failures (MTBF): The average time between system failures.
- Customer Satisfaction: Gauging customer impact and satisfaction with the resolution process. (e.g., through surveys).
- Number of escalated incidents: Indicates potential systemic issues requiring attention.
Tracking these metrics allows us to monitor trends, identify areas needing improvement and demonstrate the effectiveness of our incident management process over time. For instance, a consistently high MTTR could indicate a need for additional training or improved tools.
Q 12. Describe a challenging incident you resolved. What was your role?
One particularly challenging incident involved a cascading failure across multiple services during a major product launch. My role was the lead incident manager, coordinating the response of different teams (engineering, network, database).
The initial problem appeared to be a database overload, but as we investigated, we discovered this was a symptom of a network bottleneck caused by an unforeseen surge in traffic. This caused a ripple effect impacting other dependent services.
My approach involved:
- Rapid Assessment: I quickly identified the critical path and prioritized addressing the network bottleneck. This involved working closely with the network team.
- Communication: Maintaining transparent communication with stakeholders (including marketing and leadership) was crucial. Regular updates kept everyone informed about the progress, managing expectations amidst the crisis.
- Escalation: While I coordinated the response, I escalated certain aspects to senior engineers with specialized expertise. This ensured optimal resolution times.
- Post-Incident Review: Following the incident, we conducted a thorough RCA, which highlighted the need for better capacity planning and more robust network monitoring.
The successful resolution, while stressful, demonstrated the importance of collaborative problem-solving and proactive planning in mitigating large-scale incidents.
Q 13. How do you collaborate with other teams during an incident?
Collaboration is essential during incidents. I leverage several strategies to ensure effective teamwork.
- Unified Communication Channels: We use collaborative platforms (e.g., Slack, Microsoft Teams) to facilitate real-time communication among involved teams.
- Shared Documentation: Using a central repository (e.g., a shared document or incident management system) for all incident-related information ensures everyone has access to the latest updates.
- Regular Updates: I ensure regular updates to all involved teams, keeping them informed about the incident’s status, progress, and next steps.
- Clearly Defined Roles: Each team member has a clearly defined role and responsibility, minimizing confusion and maximizing efficiency.
- Post-Incident Debrief: After resolution, a post-incident debrief meeting ensures everyone reflects on the collaborative process and identifies opportunities for improvement.
Effective collaboration, especially during high-pressure situations, relies heavily on clear communication and well-defined roles. It’s like a well-orchestrated symphony; each section (team) plays its part, creating a harmonious resolution.
Q 14. How do you handle incidents outside of your area of expertise?
When faced with incidents outside my area of expertise, my approach focuses on identifying the right experts and facilitating effective communication.
- Escalation and Delegation: I immediately escalate the incident to the appropriate team or individual with the necessary expertise.
- Knowledge Transfer: I facilitate the knowledge transfer by gathering relevant information and providing context to the responsible team.
- Coordination: I act as a liaison between the affected team and other stakeholders, ensuring transparent communication and keeping everyone informed.
- Documentation: I ensure that the incident is properly documented, including the actions taken and the individuals involved.
This approach ensures the incident receives the appropriate attention and is resolved efficiently, even if it falls outside my direct area of responsibility. It’s about knowing your limits and leveraging the expertise of others to achieve the best outcome.
Q 15. What are some common causes of incidents in your experience?
In my experience, incidents stem from a variety of sources, often interconnected. They can be broadly categorized into:
- Hardware Failures: Server crashes, network device malfunctions (routers, switches), storage array issues, and failing power supplies are common culprits. For example, a failing hard drive in a database server can lead to application downtime.
- Software Bugs: Unexpected behavior in applications, operating systems, or third-party software can trigger incidents. A poorly written code update that introduces a security vulnerability or a performance bottleneck is a classic example.
- Human Error: Misconfigurations, accidental deletions, incorrect access control settings, and even simple typos can lead to significant disruptions. For instance, accidentally deleting a critical database table could cause an immediate service outage.
- Network Issues: Connectivity problems, bandwidth limitations, or routing failures can impact application availability and performance. A fiber cut affecting a major network link is a prime example of a network-related incident.
- Security Breaches: Unauthorized access, malware infections, denial-of-service attacks, and data breaches are serious incidents that require swift action. A successful ransomware attack encrypting critical data is a severe example.
- Third-Party Dependencies: Issues with services provided by external vendors can cascade and affect internal systems. For example, a failure in a cloud provider’s infrastructure could impact your cloud-based applications.
Understanding these root causes allows for a more targeted approach to incident prevention and resolution.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. How do you prevent future incidents from recurring?
Preventing future incidents requires a proactive, multi-faceted approach. Key strategies include:
- Root Cause Analysis (RCA): After each incident, conducting a thorough RCA to pinpoint the underlying cause is crucial. This involves gathering logs, interviewing involved personnel, and analyzing system data. A simple example would be tracing a network outage back to a faulty cable.
- Proactive Monitoring: Implementing robust monitoring systems that track key metrics and trigger alerts for anomalies can help detect potential issues before they escalate into major incidents. Think of it as having a ‘check-engine’ light for your IT infrastructure.
- Automation: Automating repetitive tasks like backups, patching, and security updates minimizes human error and improves operational efficiency. Automated patching prevents vulnerabilities from being exploited.
- Regular Testing and Drills: Performing regular tests (e.g., disaster recovery drills, failover tests) ensures that your systems can withstand failures and that recovery plans are effective. These tests identify weaknesses before they become critical issues.
- Change Management Process: Implementing a formal change management process ensures that all changes to the IT infrastructure are carefully planned, tested, and documented, minimizing the risk of introducing new problems.
- Training and Awareness: Educating staff on best practices, security awareness, and incident response procedures is critical. This helps prevent human error that could lead to incidents.
By combining these methods, organizations can significantly reduce the frequency and severity of future incidents.
Q 17. What is your understanding of SLAs (Service Level Agreements)?
Service Level Agreements (SLAs) are formal contracts between a service provider and its customers (internal or external) that define the expected level of service. They typically include metrics like:
- Availability: The percentage of time a service is operational (e.g., 99.9% uptime).
- Response Time: The time it takes for the service provider to acknowledge an incident and begin working on a resolution.
- Resolution Time: The time it takes for the service provider to fully resolve the incident.
- Performance: Metrics related to the speed and efficiency of the service.
SLAs are essential for managing expectations, holding service providers accountable, and ensuring that services meet customer needs. A breach of an SLA may have financial or other contractual implications.
Q 18. How do you manage expectations with stakeholders during an outage?
Managing stakeholder expectations during an outage requires clear, consistent, and empathetic communication. My approach includes:
- Immediate Acknowledgement: Acknowledge the incident promptly and provide a brief overview of the situation. This assures stakeholders that you are aware of the problem and working on a solution.
- Regular Updates: Provide regular updates on the progress of the investigation and resolution. Be transparent, even if you don’t have all the answers. Avoid providing false reassurances.
- Realistic Timelines: Provide realistic estimates for resolution, avoiding overly optimistic projections that can lead to further frustration.
- Clear Communication Channels: Utilize appropriate communication channels (e.g., email, phone, SMS, status pages) to reach all stakeholders effectively. Consider setting up a dedicated communication channel for the incident.
- Empathy and Apology: Show empathy for the disruption the outage is causing. A sincere apology can go a long way in managing frustration.
- Post-Incident Report: After the outage is resolved, provide a post-incident report summarizing the incident, root cause, remediation steps, and preventative measures.
By following these steps, you can build and maintain trust with stakeholders even during challenging situations.
Q 19. Describe your experience with incident communication plans.
I have extensive experience developing and implementing incident communication plans. These plans outline:
- Communication Channels: Defining the best channels to reach different stakeholder groups (e.g., email for broad announcements, phone for urgent updates, SMS for critical alerts).
- Communication Roles: Assigning roles and responsibilities for communication during incidents (e.g., communication lead, technical lead, spokesperson).
- Message Templates: Creating pre-written messages for various stages of an incident (initial notification, progress updates, resolution announcement).
- Escalation Procedures: Outlining when and how to escalate communications to senior management or other stakeholders.
- Communication Frequency: Determining the frequency of updates based on the severity of the incident and stakeholder expectations.
- Approval Process: Establishing an approval process for messages to ensure accuracy and consistency.
Effective communication plans ensure that stakeholders receive timely, accurate, and consistent information during incidents, minimizing disruption and maintaining trust.
Q 20. How familiar are you with ITIL frameworks?
I am very familiar with the ITIL (Information Technology Infrastructure Library) framework, specifically its incident management processes. ITIL provides a comprehensive set of best practices for managing IT services, including incident identification, logging, classification, prioritization, investigation, resolution, and closure. My experience includes applying ITIL principles to:
- Incident Lifecycle Management: Managing the entire lifecycle of an incident from detection to closure, using the ITIL framework as a guide.
- Incident Recording and Categorization: Using standardized categories and descriptions to ensure accurate tracking and reporting of incidents.
- Incident Prioritization: Utilizing ITIL’s guidance on prioritizing incidents based on impact and urgency.
- Knowledge Management: Contributing to a knowledge base to prevent future incidents and share lessons learned from past events.
ITIL provides a structured approach to incident management, helping to improve efficiency and effectiveness.
Q 21. What is your experience with different incident prioritization models?
I have experience with various incident prioritization models, including:
- Urgency/Impact Matrix: This is a common model that classifies incidents based on their urgency (how quickly they need to be resolved) and impact (how severe the consequences are). This matrix typically results in four priority levels (high, medium, low, critical).
- Severity Levels: This model assigns severity levels based on the impact of the incident on business operations. Higher severity levels translate to higher priority.
- Predefined Prioritization Rules: Some organizations have predefined rules for prioritizing incidents based on specific criteria. For example, security breaches might automatically get high priority regardless of impact or urgency.
The choice of prioritization model depends on the organization’s specific needs and priorities. My expertise lies in selecting and applying the most appropriate model given the context of the incidents and organizational goals. It’s important to maintain consistent application of the chosen model to avoid bias and ensure fair treatment of all incidents.
Q 22. How do you ensure the accuracy and completeness of incident reports?
Ensuring accurate and complete incident reports is paramount for effective incident management. Think of an incident report as a detective’s case file – it needs to be thorough and unbiased to facilitate a successful resolution. We achieve this through a multi-pronged approach:
- Structured Reporting Forms: We use standardized forms that guide reporters through essential fields, such as date/time, affected systems, user impact, initial symptoms, and steps taken. This minimizes omissions and ensures consistency across incidents.
- Clear Definitions and Terminology: A common lexicon is crucial. We define key terms (e.g., ‘outage,’ ‘latency,’ ‘error code’) to prevent ambiguity and misinterpretations. This ensures everyone is on the same page, regardless of their technical expertise.
- Verification and Validation: Once an initial report is filed, I often cross-check details with other sources, like system logs or affected users. This helps uncover discrepancies or hidden context. For example, a user might report a website is down, but log files might reveal a specific error code that points to the actual problem.
- Follow-up Questions: If information is missing or unclear, I proactively contact the reporter to seek clarification. Open-ended questions like, ‘Can you describe the error message in more detail?’, can unearth crucial information.
- Regular Training: We conduct regular training for all staff on the proper procedure for incident reporting, emphasizing the importance of accuracy and completeness. This ensures everyone understands their role in maintaining data integrity.
By implementing these methods, we build a reliable foundation for incident analysis, resolution, and ultimately, preventing future occurrences.
Q 23. How do you handle conflicting priorities during an incident?
Handling conflicting priorities during an incident requires a structured approach focused on prioritization and communication. Imagine a battlefield where resources are limited – you need a clear strategy. We use a framework based on impact and urgency:
- Impact Assessment: We first assess the impact of each issue on the business and users. A critical system outage affecting thousands of customers clearly takes precedence over a minor bug impacting a single user.
- Urgency Assessment: We evaluate how quickly each issue needs to be resolved. A security breach requires immediate attention, while a minor performance issue might have a longer resolution timeframe.
- Prioritization Matrix: We use a matrix combining impact and urgency (high/medium/low for both) to categorize incidents. High impact/high urgency issues are tackled first, using a ‘triage’ meeting to quickly allocate resources.
- Communication is Key: Open communication with stakeholders is essential. We keep them updated on our progress and rationale behind prioritization choices. Transparency builds trust and prevents frustration.
- Escalation Procedures: If resources are insufficient to handle all high-priority issues concurrently, clear escalation procedures are in place to involve more senior personnel or external resources.
By focusing on impact and urgency, using a matrix for prioritization, and maintaining open communication, we ensure critical incidents receive the attention they deserve, while also managing less urgent issues effectively.
Q 24. Explain the importance of post-incident reviews.
Post-incident reviews (PIRs) are crucial for continuous improvement in incident management. They’re like a post-game analysis in sports – identifying what went well, what went wrong, and how to do better next time. The key benefits include:
- Identifying Root Causes: PIRs delve deeper than just resolving the immediate problem. They aim to understand the underlying causes that contributed to the incident, preventing recurrence.
- Improving Response Times: By analyzing the time it took to detect, respond to, and resolve the incident, we identify bottlenecks and areas for optimization.
- Enhancing Procedures and Processes: PIRs highlight weaknesses in existing processes, allowing for improvements to documentation, escalation paths, or communication protocols. For example, a PIR might reveal a lack of clear communication between teams, leading to delays.
- Team Training and Development: PIRs provide valuable learning opportunities for all involved. They facilitate knowledge sharing and help improve individual and team skills.
- Reducing Risk: By addressing root causes and strengthening processes, PIRs contribute to reducing the likelihood and impact of future incidents.
A well-conducted PIR involves a structured review of the incident timeline, a detailed analysis of root causes, and the development of concrete action items to prevent similar occurrences. It’s a proactive step towards a more resilient and efficient IT infrastructure.
Q 25. Describe your experience using a knowledge base for incident resolution.
A well-maintained knowledge base is invaluable for efficient incident resolution. Think of it as a comprehensive library of solutions – readily available to guide technicians and reduce resolution time. My experience encompasses:
- Contributing to the Knowledge Base: I actively contribute to our knowledge base by documenting solutions to incidents I’ve resolved. This includes detailed steps, error messages, relevant logs, and screenshots. This ensures others can benefit from my experience.
- Searching and Utilizing Existing Knowledge: Before starting any troubleshooting, I always search our knowledge base for relevant articles or solutions. This often allows me to quickly identify and resolve common issues.
- Improving Search Functionality: I’ve been involved in improving our knowledge base’s search functionality through better keyword tagging and categorization. This ensures that information is easily accessible and relevant to the issue at hand.
- Identifying Knowledge Gaps: I’ve also identified gaps in our knowledge base – areas where information is missing or outdated. I then propose improvements and documentation to close these gaps proactively.
By actively participating in building and utilizing our knowledge base, we collectively build an institutional memory of solutions that benefits everyone and makes incident resolution faster and more efficient.
Q 26. How do you stay up-to-date on the latest security threats and vulnerabilities?
Staying current on security threats and vulnerabilities is crucial in incident management. It’s like being a vigilant security guard – always aware of potential threats. My approach combines several strategies:
- Subscription to Security Newsletters and Alerts: I subscribe to reputable sources like security blogs, mailing lists, and vulnerability databases (e.g., NIST NVD) to receive timely updates.
- Following Security Researchers and Experts: I follow industry experts and researchers on social media and other platforms to stay aware of emerging trends and new attack vectors.
- Participating in Security Communities: I actively participate in online forums and communities to discuss latest threats and share insights with other security professionals.
- Attending Webinars and Conferences: I attend relevant webinars and security conferences to learn about the latest attack techniques and mitigation strategies from leading experts.
- Utilizing Security Tools and Platforms: I utilize vulnerability scanners and security information and event management (SIEM) systems to monitor our systems for potential threats. This allows for proactive identification of vulnerabilities before they can be exploited.
By combining these strategies, I stay informed about the evolving threat landscape, enabling us to proactively address vulnerabilities and better respond to security incidents.
Q 27. How do you handle pressure and stress during a critical incident?
Handling pressure and stress during critical incidents requires a calm and methodical approach. It’s like being a captain navigating a storm – maintaining composure and strategic thinking is crucial. My strategies include:
- Deep Breathing and Mindfulness Techniques: I use deep breathing exercises and mindfulness techniques to manage stress and maintain focus amidst chaos.
- Prioritization and Delegation: I focus on prioritizing tasks and delegating responsibilities to others as appropriate to prevent feeling overwhelmed.
- Clear Communication: I maintain clear and concise communication with the team and stakeholders, providing updates and ensuring everyone understands their roles.
- Time Management and Breaks: I use effective time management techniques and take short breaks to prevent burnout. Short breaks for fresh air and a change of pace can be very effective.
- Post-Incident Debrief: After a critical incident, I take time to debrief and reflect on my performance, identifying areas for improvement and strategies for handling future incidents more effectively.
These strategies help me maintain a clear head and effective decision-making even under immense pressure, crucial for navigating challenging situations.
Q 28. What is your experience with automation in incident management?
Automation plays a vital role in modern incident management, enhancing speed, efficiency, and accuracy. Think of it as having an automated assistant that handles routine tasks. My experience includes:
- Automated Alerting and Notification Systems: We use automated systems that trigger alerts based on predefined thresholds or events. This allows for faster detection and notification of incidents.
- Automated Incident Ticket Creation: Many incidents can be automatically detected and tickets created without manual intervention, saving significant time.
- Automated Diagnostics and Troubleshooting: We utilize tools that automatically diagnose common issues and suggest solutions, speeding up resolution time. For example, a script might automatically check server logs for common errors and provide relevant fixes.
- Automated Remediation: In some cases, automation can even execute automated remediation steps, like restarting a service or applying a patch, without human intervention (though always with careful oversight).
- Integration with Monitoring Tools: We integrate incident management tools with monitoring systems for seamless data flow and improved visibility into system health.
Through automation, we’ve significantly reduced manual effort, improved response times, and enhanced the overall efficiency of our incident management process.
Key Topics to Learn for Incident Triage and Escalation Procedures Interview
- Incident Classification and Prioritization: Understanding different incident severity levels (critical, major, minor), impact analysis, and effective prioritization based on business impact and urgency. Practical application: Developing a prioritization matrix and applying it to real-world scenarios.
- Communication and Collaboration: Mastering effective communication techniques for keeping stakeholders informed during incidents, collaborating with different teams (engineering, support, management), and documenting all actions taken. Practical application: Practicing clear and concise communication during simulated incident response scenarios.
- Root Cause Analysis (RCA): Learning various RCA methodologies (e.g., 5 Whys, Fishbone diagram) to identify the underlying causes of incidents, preventing recurrence, and improving system reliability. Practical application: Analyzing case studies of past incidents and identifying root causes.
- Escalation Procedures: Understanding when and how to escalate incidents to the appropriate teams or individuals based on predefined criteria and established communication channels. Practical application: Creating a detailed escalation plan for a hypothetical system outage.
- Incident Management Tools and Technologies: Familiarity with common incident management systems and ticketing platforms, including their functionalities and best practices for their use. Practical application: Researching and comparing different incident management tools.
- Service Level Agreements (SLAs): Understanding the role of SLAs in incident management, and how they influence incident response timelines and escalation procedures. Practical application: Analyzing SLAs and their implications for incident resolution.
- Post-Incident Reviews (PIRs): Understanding the importance of conducting thorough PIRs to identify areas for improvement in incident response processes, communication, and system resilience. Practical application: Developing a template for a comprehensive PIR report.
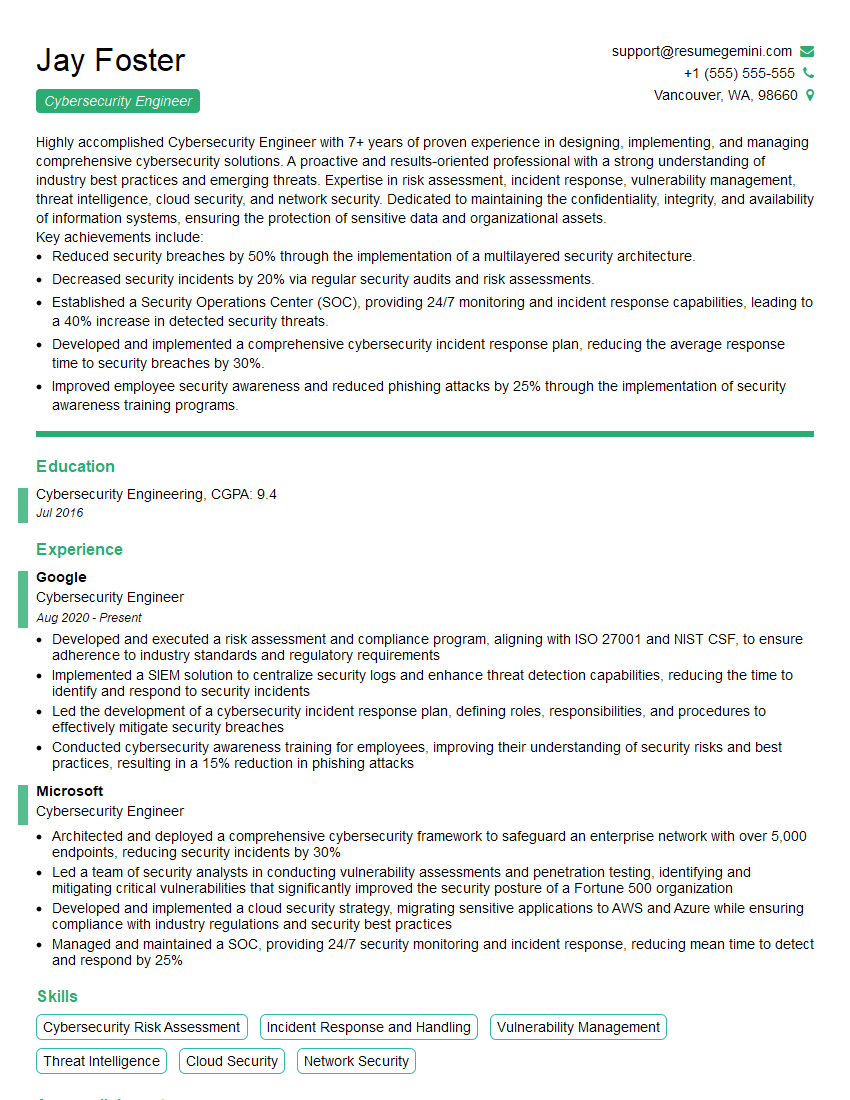
Next Steps
Mastering Incident Triage and Escalation Procedures is crucial for career advancement in IT and related fields. It demonstrates your ability to handle pressure, solve complex problems, and collaborate effectively within a team. To significantly improve your job prospects, focus on building an ATS-friendly resume that highlights your relevant skills and experience. ResumeGemini is a trusted resource to help you create a compelling and effective resume. We provide examples of resumes tailored specifically to Incident Triage and Escalation Procedures to guide you in showcasing your expertise. Take the next step towards your dream job today!
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good