Interviews are more than just a Q&A session—they’re a chance to prove your worth. This blog dives into essential Intelligence Analysis and Fusion interview questions and expert tips to help you align your answers with what hiring managers are looking for. Start preparing to shine!
Questions Asked in Intelligence Analysis and Fusion Interview
Q 1. Explain the difference between strategic and tactical intelligence analysis.
Strategic and tactical intelligence analysis differ primarily in their scope and timeframe. Strategic intelligence focuses on long-term trends, threats, and opportunities, informing high-level decision-making. Think of it as the big picture – understanding geopolitical shifts, the rise of new technologies, or long-term economic forecasts. Tactical intelligence, on the other hand, is short-term and action-oriented. It addresses immediate needs, supporting specific operations or responses to immediate threats. For example, identifying the location of an imminent terrorist attack or tracking a specific criminal’s movements falls under tactical intelligence.
Analogy: Imagine planning a military campaign. Strategic intelligence would involve assessing the enemy’s overall capabilities, their political alliances, and their likely long-term objectives. Tactical intelligence would involve determining the best route for an immediate advance, identifying enemy troop positions, and selecting optimal targets for a specific battle.
Q 2. Describe the intelligence cycle and your role within it.
The intelligence cycle is a continuous process that encompasses planning and direction, collection, processing, analysis, and dissemination of intelligence information. It’s a cyclical process, meaning the output of one stage informs the next.
- Planning & Direction: Identifying intelligence requirements based on policymaker’s needs.
- Collection: Gathering raw information from various sources (HUMINT, SIGINT, OSINT, etc.).
- Processing: Transforming raw data into usable intelligence. This involves translating languages, verifying information, and organizing data.
- Analysis: Interpreting processed data to produce actionable intelligence assessments.
- Dissemination: Sharing intelligence products with relevant decision-makers.
My role typically falls within the analysis and sometimes dissemination stages. I’m responsible for transforming raw data into meaningful insights, preparing intelligence reports and briefings, and presenting findings to policymakers and operational teams. This requires not just technical expertise, but also strong communication and presentation skills.
Q 3. What are the key steps in the intelligence fusion process?
Intelligence fusion is the process of integrating information from multiple sources to create a more complete and accurate understanding of a situation. It’s about going beyond simply aggregating data and synthesizing it into a coherent narrative.
- Data Collection & Integration: Gathering information from diverse sources, including HUMINT, SIGINT, OSINT, IMINT, and MASINT.
- Data Analysis & Interpretation: Applying analytical techniques to identify patterns, trends, and relationships within the data.
- Correlation & Synthesis: Combining seemingly disparate pieces of information to form a cohesive picture.
- Validation & Verification: Assessing the credibility and reliability of sources and information.
- Dissemination & Feedback: Sharing the fused intelligence product with relevant stakeholders and incorporating feedback.
Example: Imagine investigating a potential cyberattack. Fusion would involve combining network logs (SIGINT), social media posts (OSINT), and insider information (HUMINT) to paint a complete picture of the attack’s origin, objectives, and potential impact.
Q 4. How do you assess the credibility and reliability of intelligence sources?
Assessing source credibility and reliability is crucial for producing accurate intelligence. This involves a multi-faceted approach.
- Source Track Record: Evaluating the source’s past performance and accuracy.
- Motivation & Bias: Understanding the source’s potential biases and motivations for providing information.
- Information Corroboration: Comparing information from multiple sources to verify its accuracy.
- Data Consistency & Plausibility: Checking for internal consistency and assessing the plausibility of the information within the context of existing knowledge.
- Method of Acquisition: Considering how the information was obtained – a direct observation will generally be considered more reliable than hearsay.
Example: If one source claims an imminent attack, but several others report nothing unusual and lack evidence, the credibility of the first source is diminished. Always seek multiple, independent sources to confirm information and apply critical thinking in the process.
Q 5. Explain the concept of ‘all-source intelligence’ and its importance.
All-source intelligence refers to the practice of integrating information from all available sources, regardless of their type or origin. This contrasts with relying on a single type of intelligence, such as solely HUMINT or SIGINT. Its importance stems from the synergistic effect of combining various perspectives and data points. This leads to a richer, more comprehensive understanding and minimizes bias associated with relying on a single source or method.
Example: Investigating a transnational crime syndicate would benefit greatly from all-source intelligence: financial records (OSINT), intercepted communications (SIGINT), human informants (HUMINT), and satellite imagery (IMINT) would be combined to build a complete picture of the group’s operations, finances, and leadership.
Q 6. What are some common challenges in intelligence fusion and how do you overcome them?
Challenges in intelligence fusion are numerous. Some common ones include:
- Data Overload: The sheer volume of data from diverse sources can be overwhelming.
- Data Inconsistencies: Conflicting or contradictory information from different sources is a major hurdle.
- Data Silos: Information may be fragmented across different agencies or departments, hindering integration.
- Technological Limitations: The ability to effectively process and analyze diverse datasets depends on appropriate technology and skilled analysts.
Overcoming these challenges requires:
- Robust data management systems: Effective tools for organizing, filtering, and analyzing large datasets.
- Standardized data formats: Facilitates integration of data from diverse sources.
- Inter-agency collaboration: Breaking down information silos requires cooperation and trust between different organizations.
- Advanced analytical techniques: Employing methods like machine learning for pattern recognition and predictive analytics.
- Highly skilled analysts: Experts capable of critical thinking, problem-solving, and effective communication.
Q 7. Describe your experience with various intelligence gathering methods (OSINT, HUMINT, SIGINT, etc.).
My experience encompasses a range of intelligence gathering methods.
- OSINT (Open-Source Intelligence): I have extensive experience using publicly available information – news articles, social media, academic papers, and government reports – to identify trends, assess threats, and build situational awareness. For instance, I used OSINT to track the movements of a particular activist group during a period of civil unrest.
- HUMINT (Human Intelligence): While not directly involved in the recruitment and handling of human sources, I regularly analyze and assess HUMINT reports, employing rigorous methods to evaluate their reliability and veracity.
- SIGINT (Signals Intelligence): I have worked with SIGINT data, primarily in an analytical capacity, interpreting intercepted communications to understand communication patterns, identify key players, and assess intentions. This includes experience with analyzing metadata from various communication channels.
- IMINT (Imagery Intelligence): I can effectively interpret satellite imagery and aerial photographs, and incorporate this data within fused intelligence products. I’ve utilized IMINT to monitor infrastructural changes in a region of geopolitical interest.
- MASINT (Measurement and Signature Intelligence): My experience with MASINT is more limited, but I understand its role and importance, particularly in technical intelligence assessments. I have participated in projects utilizing MASINT data in conjunction with other intelligence sources.
Q 8. How do you analyze conflicting or contradictory intelligence information?
Analyzing conflicting intelligence is a core skill in intelligence analysis. It’s not about dismissing contradictory information but about understanding its sources, biases, and potential explanations. I approach this using a structured process:
- Source Evaluation: First, I meticulously assess the credibility and reliability of each source. This includes considering their track record, motivations, and potential biases. For instance, an open-source news report might offer different insights than a classified HUMINT (Human Intelligence) report.
- Data Triangulation: I look for corroborating evidence from multiple independent sources. If multiple reliable sources support a particular piece of information, it strengthens its validity. Conversely, if only one source claims something, I treat it with greater scrutiny.
- Contextual Analysis: I consider the context in which the information was gathered. A report from a hostile actor might intentionally misrepresent facts. Understanding the geopolitical environment and the motivations of the sources is critical.
- Hypothesis Generation & Testing: Based on the available information, I develop competing hypotheses to explain the contradictions. I then systematically test these hypotheses against additional data and information. For example, if two reports give different casualty numbers in a conflict, I might investigate possible explanations: differing reporting methodologies, intentional obfuscation, or the use of different datasets.
- Developing a Weighted Assessment: Ultimately, I arrive at a weighted assessment, recognizing that some information might be more reliable than others. This isn’t about finding a single ‘truth’ but a well-supported conclusion given the available, often imperfect, data. I explicitly document my reasoning and any remaining uncertainties.
For example, during an investigation into a suspected terrorist cell, one source may claim the cell is planning a large-scale attack, while another suggests they’re merely engaged in fundraising. By comparing the sourcing, assessing the reliability, and analyzing the supporting evidence, I can weigh the credibility of both accounts and create a more accurate picture of the threat.
Q 9. What analytical techniques do you employ to identify trends and patterns in data?
Identifying trends and patterns requires a combination of analytical techniques. I utilize several approaches:
- Data Mining and Statistical Analysis: I leverage statistical software and data mining techniques to identify correlations, clusters, and outliers in large datasets. This might involve using regression analysis to predict future events based on historical trends or clustering algorithms to group similar incidents.
- Network Analysis: This technique is particularly useful for understanding relationships between entities (individuals, organizations, etc.). I might use network visualization tools to map connections and identify key players within a network. For example, in analyzing a drug trafficking network, network analysis helps identify leaders and key logistical nodes.
- Time Series Analysis: When dealing with data collected over time, time series analysis helps identify cyclical patterns, trends, and seasonality. For instance, analyzing crime statistics over several years might reveal a seasonal increase in certain types of crime.
- Comparative Case Studies: I often use comparative case studies to identify common themes and causal factors across different events or situations. Comparing past terrorist attacks, for example, might help identify common planning phases or operational strategies.
- Visualization: Transforming data into visual representations, such as charts, graphs, and maps, is crucial for identifying patterns and trends that might not be apparent in raw data. Geographic Information Systems (GIS) are particularly valuable here.
Often, I use a combination of these techniques to achieve a more comprehensive understanding of the data.
Q 10. How do you prioritize intelligence requirements based on urgency and impact?
Prioritizing intelligence requirements is crucial due to resource constraints and the need to focus on the most critical issues. I use a framework that considers both urgency and impact:
- Urgency Assessment: This involves estimating the immediacy of the threat or opportunity. How quickly must action be taken? Imminent threats require immediate attention.
- Impact Assessment: This involves assessing the potential consequences of various scenarios. How significant would the impact be if the intelligence requirement remains unaddressed? This might involve considering the potential loss of life, financial damage, or reputational harm.
- Prioritization Matrix: I often use a prioritization matrix that plots intelligence requirements based on both urgency and impact. This allows for a clear visual representation of which requirements are most critical and should receive priority attention. High urgency, high impact issues receive top priority.
- Resource Allocation: Once the priorities have been established, resources—personnel, tools, and time—are allocated accordingly.
- Regular Review: The priorities are regularly reviewed and updated, reflecting evolving circumstances. The situation on the ground can change quickly, requiring dynamic adaptation of priorities.
For example, intelligence indicating an imminent terrorist attack would take precedence over intelligence related to a long-term geopolitical trend, even if the long-term trend carries greater potential overall impact.
Q 11. How familiar are you with various intelligence databases and analytical tools?
I’m highly familiar with a range of intelligence databases and analytical tools. My experience includes working with:
- Commercial Databases: LexisNexis, Factiva, and similar platforms provide access to a wealth of open-source information, including news articles, company records, and legal documents.
- Government Databases: I have experience accessing secure government databases containing classified information relevant to my areas of expertise. (Specific database names omitted for security reasons.)
- Geospatial Intelligence (GEOINT) Systems: I’m proficient in using GIS software such as ArcGIS and QGIS to analyze geospatial data, integrating it with other intelligence sources.
- Data Analysis Software: I utilize statistical software packages such as R and SPSS, as well as data visualization tools like Tableau, for data analysis and reporting.
- Link Analysis Software: Tools designed for network analysis, allowing me to visualize and analyze relationships between individuals, organizations, and events.
My proficiency in these tools allows me to effectively collect, analyze, and fuse data from diverse sources to produce comprehensive intelligence assessments.
Q 12. Describe your experience using geospatial intelligence (GEOINT) in your analysis.
Geospatial intelligence (GEOINT) plays a vital role in my analysis. I regularly integrate GEOINT into my work to provide context, identify patterns, and support decision-making. Examples of my GEOINT usage include:
- Mapping Conflict Zones: Using satellite imagery and other geospatial data to track troop movements, identify infrastructure damage, and assess the impact of conflict on civilian populations.
- Analyzing Infrastructure: Identifying and assessing critical infrastructure, such as power plants, communication networks, and transportation hubs, to understand vulnerabilities and potential targets.
- Tracking Movement Patterns: Analyzing the movement of individuals or vehicles through geospatial data to identify potential patterns and connections.
- Corroborating Other Intelligence: Using GEOINT to verify or refute information obtained from other sources. For example, satellite imagery can confirm or deny the presence of certain types of weaponry at a specific location.
- Creating Visualizations: Developing maps and other visualizations to effectively communicate findings to both technical and non-technical audiences.
GEOINT isn’t just about maps; it’s about integrating location information with other intelligence disciplines to achieve a holistic understanding of a situation.
Q 13. How do you present your intelligence findings to different audiences (technical vs. non-technical)?
Tailoring the presentation of intelligence findings to the audience is crucial for effective communication. I use different approaches for technical and non-technical audiences:
- Technical Audiences: When presenting to technical audiences, I use detailed reports that include methodologies, data sources, and supporting evidence. I use technical terminology appropriately, ensuring clarity and precision. I might also include detailed statistical analysis or advanced visualizations.
- Non-Technical Audiences: For non-technical audiences, I use simpler language, avoiding jargon. I focus on communicating the key findings and their implications in a concise and easily understandable manner. Visual aids like charts, graphs, and maps are critical for conveying complex information effectively. I aim to emphasize the ‘so what?’ – the relevance and actionability of the intelligence.
Regardless of the audience, I always ensure that my presentation is clear, concise, and well-supported by evidence. A good intelligence briefing is both informative and persuasive.
Q 14. Explain your understanding of risk assessment and its role in intelligence analysis.
Risk assessment is an integral part of intelligence analysis. It helps to understand the likelihood and potential impact of various threats and opportunities. It allows for informed decision-making by providing a framework for evaluating potential risks and allocating resources accordingly.
My approach to risk assessment involves:
- Identifying Potential Risks: This involves systematically identifying all potential risks relevant to the issue under consideration. This might involve brainstorming, reviewing past incidents, and consulting with subject-matter experts.
- Assessing Likelihood: Determining the probability of each identified risk occurring. This often involves qualitative judgment, but quantitative data can also be used where available.
- Assessing Impact: Determining the potential consequences if the risk occurs. This can be measured in various ways—financial losses, reputational damage, loss of life, etc.
- Risk Prioritization: Combining likelihood and impact to prioritize risks. High-likelihood, high-impact risks require immediate attention.
- Mitigation Strategies: Developing strategies to mitigate or reduce the likelihood and impact of identified risks. This might involve implementing security measures, developing contingency plans, or improving information sharing.
- Monitoring and Review: Regularly monitoring and reviewing the identified risks, updating the assessment as circumstances change.
Risk assessment is a dynamic process that should be continuously updated as new information becomes available and circumstances evolve. It helps transform raw intelligence into actionable insights by providing a structured framework for evaluating threats and opportunities.
Q 15. How do you ensure the accuracy and objectivity of your intelligence reports?
Ensuring accuracy and objectivity in intelligence reports is paramount. It’s not just about getting the facts right; it’s about presenting them in a way that avoids bias and allows decision-makers to form their own conclusions. This involves a multi-faceted approach.
Source Verification: We rigorously check the credibility of every source. This includes assessing their past performance, motivations, and potential biases. For example, if we’re relying on information from a foreign government, we’d consider their geopolitical interests and history of truthfulness.
Cross-Referencing: We never rely on a single source. Instead, we corroborate information from multiple independent sources. If several credible sources report the same event, our confidence in the accuracy of the intelligence increases significantly. Discrepancies, however, require further investigation.
Data Triangulation: We employ data triangulation to verify information. This involves comparing information from different sources and methodologies (e.g., human intelligence, signals intelligence, open-source intelligence) to check consistency and identify potential errors or manipulation.
Analytical Rigor: We use structured analytical techniques (SATs), which I’ll elaborate on later, to minimize cognitive biases and ensure a systematic approach to analysis. Techniques like analysis of competing hypotheses (ACH) help us objectively assess various interpretations of the evidence.
Transparency and Documentation: We meticulously document our sources and methodology. This allows for independent review and verification, contributing to transparency and accountability. This is particularly crucial when dealing with sensitive information.
Ultimately, striving for objectivity is an ongoing process. We acknowledge the inherent limitations of intelligence analysis and aim for continuous improvement in our methods and practices.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. Describe your experience with intelligence briefings and presentations.
I have extensive experience delivering intelligence briefings and presentations to diverse audiences, including senior government officials, military commanders, and interagency partners. My approach is tailored to the audience’s knowledge and needs.
Audience Tailoring: I begin by understanding the audience’s background and specific information requirements. A briefing for a military commander will differ substantially from one for a policymaker.
Clear and Concise Communication: I prioritize clear and concise communication, avoiding technical jargon where possible. I use visual aids such as maps, charts, and timelines to enhance understanding.
Data Visualization: I focus on presenting data in visually compelling ways. For example, if analyzing terrorist group activity, I might use a network graph to illustrate relationships between individuals and groups.
Storytelling: I utilize storytelling techniques to engage the audience and make the information more memorable. A narrative structure can help contextualize complex information and make it more accessible.
Handling Questions: I am adept at handling questions and providing thoughtful, well-informed responses, even when the information is incomplete or uncertain.
I’ve regularly presented at high-stakes briefings, where accuracy and clarity are essential for effective decision-making. In one instance, I presented a critical assessment of a potential foreign policy intervention, where my clear communication helped inform a crucial decision.
Q 17. How do you stay updated on current events and emerging intelligence threats?
Staying updated on current events and emerging intelligence threats is crucial in this field. My approach involves a multi-layered strategy:
Open Source Intelligence (OSINT): I regularly monitor reputable news organizations, academic journals, social media, and other open sources to gain insights into current events and emerging trends. This provides a broad overview of the global security landscape.
Specialized Publications and Databases: I subscribe to and regularly consult specialized intelligence publications, databases, and analytical reports, such as those produced by government agencies and think tanks. These provide detailed, in-depth analyses of specific threats.
Professional Networking: I actively participate in professional conferences and maintain relationships with colleagues and experts in the field. This facilitates the exchange of knowledge and allows me to stay ahead of emerging challenges.
Threat Modeling and Forecasting: I use various analytical methods including trend analysis, scenario planning, and other forecasting techniques to identify potential future threats and vulnerabilities.
For example, by combining OSINT analysis of social media trends with data from specialized databases, I recently identified an emerging pattern of disinformation campaigns aimed at undermining public trust in democratic institutions.
Q 18. What is your experience with using analytic methodologies like structured analytic techniques (SAT)?
I have significant experience using structured analytic techniques (SATs) to improve the rigor and objectivity of my analyses. SATs provide a framework for systematically addressing complex problems and minimizing cognitive biases.
Analysis of Competing Hypotheses (ACH): I frequently use ACH to systematically evaluate multiple plausible explanations for an event or phenomenon, ensuring that we consider alternative perspectives and avoid premature conclusions.
Key Assumptions Check (KAC): KAC helps identify and examine underlying assumptions driving our analysis. By challenging these assumptions, we can uncover potential flaws in our reasoning and strengthen our conclusions.
Premortem Analysis: This technique involves imagining that a project has already failed and then working backward to identify potential causes of failure. This allows us to proactively address potential problems and improve our planning.
Structured Brainstorming: Structured brainstorming encourages group participation and helps avoid groupthink by providing a systematic way to generate ideas and explore diverse perspectives.
In a recent case involving an escalating regional conflict, employing ACH allowed us to identify a previously overlooked factor that significantly altered our understanding of the situation and our recommendations for policymakers.
Q 19. How familiar are you with the concept of link analysis and its application in intelligence analysis?
Link analysis is a crucial tool in intelligence analysis, particularly for understanding relationships between individuals, organizations, and events. It involves mapping connections to reveal patterns, identify key players, and uncover hidden relationships.
Network Mapping: I use various software tools to create network maps illustrating connections between individuals, groups, or entities. This visually represents relationships and allows us to identify central figures or key organizational structures.
Identifying Clusters: By analyzing the network, we can identify clusters of individuals or organizations that share common characteristics or connections, providing insights into potential collaborations or conspiracies.
Path Analysis: Link analysis enables us to trace information flow or resource movements through a network, identifying pathways for illicit activities or communication channels.
Predictive Modeling: In some cases, link analysis can be used to build predictive models, forecasting potential future connections or activities based on observed patterns.
For example, in analyzing a transnational criminal organization, link analysis allowed us to identify key financial facilitators and communication networks, leading to successful disruptions of their operations.
Q 20. Describe your experience working with classified information and handling security protocols.
I have extensive experience working with classified information and adhering to strict security protocols. My experience encompasses handling information at various classification levels, including Top Secret.
Security Clearances: I possess the necessary security clearances and undergo regular background checks to maintain access to classified information.
Data Handling Procedures: I am thoroughly familiar with and strictly adhere to all relevant data handling procedures, including proper storage, access control, and dissemination protocols. This includes the use of secure communication channels and systems.
Compartmentalization: I understand and respect the principle of compartmentalization, accessing only the information necessary for my specific tasks and responsibilities.
Security Awareness Training: I regularly participate in security awareness training to remain up-to-date on the latest threats and best practices for protecting classified information.
Maintaining the security of classified information is not merely a procedural matter but a critical responsibility that requires constant vigilance and attention to detail. I treat it with the utmost seriousness.
Q 21. How do you manage competing priorities and deadlines in a fast-paced intelligence environment?
The intelligence environment is inherently fast-paced and demanding. Managing competing priorities and deadlines requires a structured approach.
Prioritization: I use a prioritization matrix to rank tasks based on urgency and importance. This ensures that the most critical tasks receive the necessary attention first.
Time Management Techniques: I employ various time management techniques, including time blocking, task lists, and the Pomodoro Technique, to optimize my productivity and meet deadlines.
Delegation: Where appropriate, I delegate tasks to team members, ensuring that their skills and expertise are utilized effectively.
Communication and Collaboration: I maintain open and clear communication with my colleagues and stakeholders, ensuring that everyone is aware of priorities and potential conflicts.
Flexibility and Adaptability: I am flexible and adaptable, recognizing that priorities can change rapidly in a dynamic environment. I am prepared to adjust my plans as needed.
For example, during a crisis situation, I was able to effectively prioritize tasks, delegate responsibilities, and maintain clear communication, ensuring that critical intelligence was delivered to decision-makers in a timely manner.
Q 22. Explain your understanding of the ethical considerations in intelligence analysis.
Ethical considerations in intelligence analysis are paramount. They govern how we collect, analyze, and disseminate information, ensuring we operate within legal and moral boundaries. This involves a complex interplay of factors, including:
- Privacy and Confidentiality: Protecting the privacy of individuals whose data is collected is crucial. We must adhere strictly to legal frameworks like the Privacy Act and ensure data is handled responsibly and only used for legitimate intelligence purposes.
- Accuracy and Objectivity: We must strive for unbiased analysis, presenting information fairly and avoiding manipulation or distortion to support pre-conceived notions. Any biases must be explicitly acknowledged and addressed.
- Legality and Accountability: All actions must be legal and comply with national and international laws. This includes ensuring proper authorization for surveillance and data collection. Transparency and accountability for actions are key.
- Proportionality: The intrusive nature of intelligence gathering needs careful consideration. We must balance the potential benefits of intelligence against the potential harm caused by intrusive methods. The means must be proportionate to the ends.
- Minimizing Harm: Intelligence operations can have unintended consequences. Analysts have a responsibility to anticipate and mitigate potential harm to individuals, groups, or even national security through our actions or the dissemination of our analysis.
For example, during an investigation involving a suspected terrorist cell, ethical considerations dictate that we only collect information relevant to the investigation, minimizing unnecessary intrusion on the privacy of individuals not directly linked to the threat.
Q 23. Describe a situation where you had to make a critical decision based on incomplete intelligence.
During a counter-narcotics operation, we received fragmented intelligence suggesting a large shipment of cocaine was leaving a specific port, but the exact vessel, route, and destination were uncertain. Satellite imagery showed unusual activity, but we lacked clear confirmation of the cargo. Human intelligence was limited and unreliable.
This required a critical decision: allocate limited resources to monitor the port intensively, potentially diverting resources from other operations, or defer action, risking the successful transit of the shipment. We opted for a risk assessment matrix, weighting the probability of the shipment’s departure versus the potential consequences of a false positive and the opportunity costs of diverting resources. This, coupled with a review of past success rates of such operations, allowed us to make an informed judgment to increase surveillance in that area. The increased surveillance eventually confirmed the smuggling operation and facilitated its disruption.
Q 24. How do you handle pressure and uncertainty in your work as an intelligence analyst?
Working under pressure and uncertainty is inherent to intelligence analysis. Managing this requires a structured approach:
- Prioritization and Time Management: I use techniques like Eisenhower Matrix (urgent/important) to prioritize tasks and allocate time effectively.
- Stress Management Techniques: Regular exercise, mindfulness, and sufficient sleep help maintain mental resilience.
- Structured Analysis: Applying rigorous analytical methodologies, like the Structured Analytic Techniques (SATs) helps to mitigate uncertainty through systematic evaluation of information, even when incomplete.
- Teamwork and Collaboration: Open communication and collaboration with colleagues provide support and different perspectives which help to manage stress and enhance decision-making.
- Seeking Mentorship: Experienced colleagues provide valuable guidance and help in navigating complex situations.
Think of it like navigating a fog. You don’t have perfect visibility, but you use your instruments (analytical methods), maps (existing intelligence), and your crew (colleagues) to make your way through safely.
Q 25. How do you incorporate feedback into your intelligence analysis process?
Feedback is essential for continuous improvement. I actively seek and incorporate feedback throughout the intelligence cycle. This involves:
- Regular Debriefings: After significant events or operations, I engage in debriefings to identify areas where analysis was accurate or inaccurate, and what lessons learned could improve future analyses.
- Peer Reviews: My work is regularly reviewed by colleagues with varied expertise. This helps identify biases, logical fallacies, and alternative interpretations.
- Client Feedback: Seeking feedback from policymakers or operational users on the usefulness and impact of my analysis allows me to tailor future analyses to their needs and gain valuable insights on applicability.
- Self-Reflection: Regular introspection is crucial. I review my own work to identify recurring strengths and weaknesses in my approach.
Imagine building a house. Feedback from architects, engineers, and the clients helps refine the blueprint and the final product. Similarly, feedback improves the quality and relevance of intelligence analysis.
Q 26. What are your strengths and weaknesses as an intelligence analyst?
My strengths include strong analytical skills, a methodical approach to problem-solving, and a proven ability to synthesize complex information from diverse sources. I excel at identifying patterns and drawing inferences from incomplete data, and I am adept at communicating my findings clearly and concisely. I also work effectively both independently and collaboratively.
My area for development is enhancing my knowledge of specific technological advancements in data analysis and visualization. While proficient in traditional methods, I am actively working to improve my proficiency in using these modern tools to further enhance my analysis.
Q 27. Where do you see yourself in five years in the field of intelligence analysis?
In five years, I see myself in a leadership role, mentoring junior analysts and contributing to the development of innovative analytical techniques. I am interested in specializing in the application of advanced technologies to intelligence analysis, perhaps focusing on predictive modeling or using AI/ML techniques for threat forecasting. I also hope to expand my knowledge and contribute to the development of robust ethical guidelines for the use of AI in intelligence analysis.
Key Topics to Learn for Intelligence Analysis and Fusion Interview
- Intelligence Cycle: Understand the phases (planning & direction, collection, processing, analysis & production, dissemination) and how they interact. Consider practical applications like prioritizing collection efforts based on analytical needs.
- All-Source Intelligence: Explore the integration of information from various sources (human intelligence, signals intelligence, open-source intelligence, etc.). Practice analyzing conflicting information and identifying biases.
- Analytical Tradecraft: Master techniques like hypothesis generation, evidence evaluation, and argument construction. Consider how to present complex analyses clearly and concisely for different audiences.
- Data Analysis & Visualization: Develop skills in using data analysis tools and techniques to identify patterns and trends in large datasets. Practice creating compelling visualizations to communicate insights effectively.
- Geopolitical Understanding: Demonstrate a solid grasp of current geopolitical events and their potential implications. Practice analyzing regional conflicts and their impact on national security.
- Risk Assessment & Prediction: Learn to assess potential threats and develop predictive models based on available intelligence. Consider scenarios and their potential consequences.
- Communication & Collaboration: Highlight your abilities to clearly and effectively communicate complex information to diverse audiences, both verbally and in writing, and to work collaboratively in a team environment.
- Ethical Considerations: Demonstrate understanding of the ethical implications of intelligence work, including privacy, security, and the responsible use of information.
Next Steps
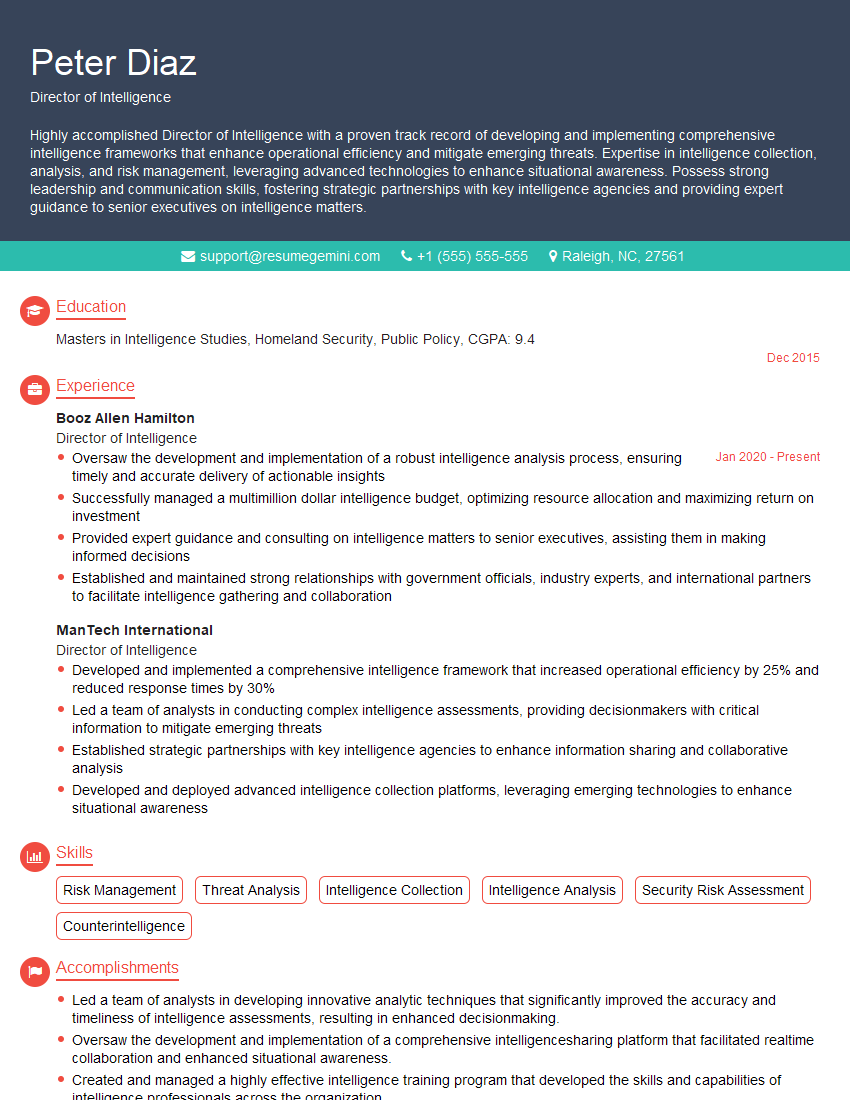
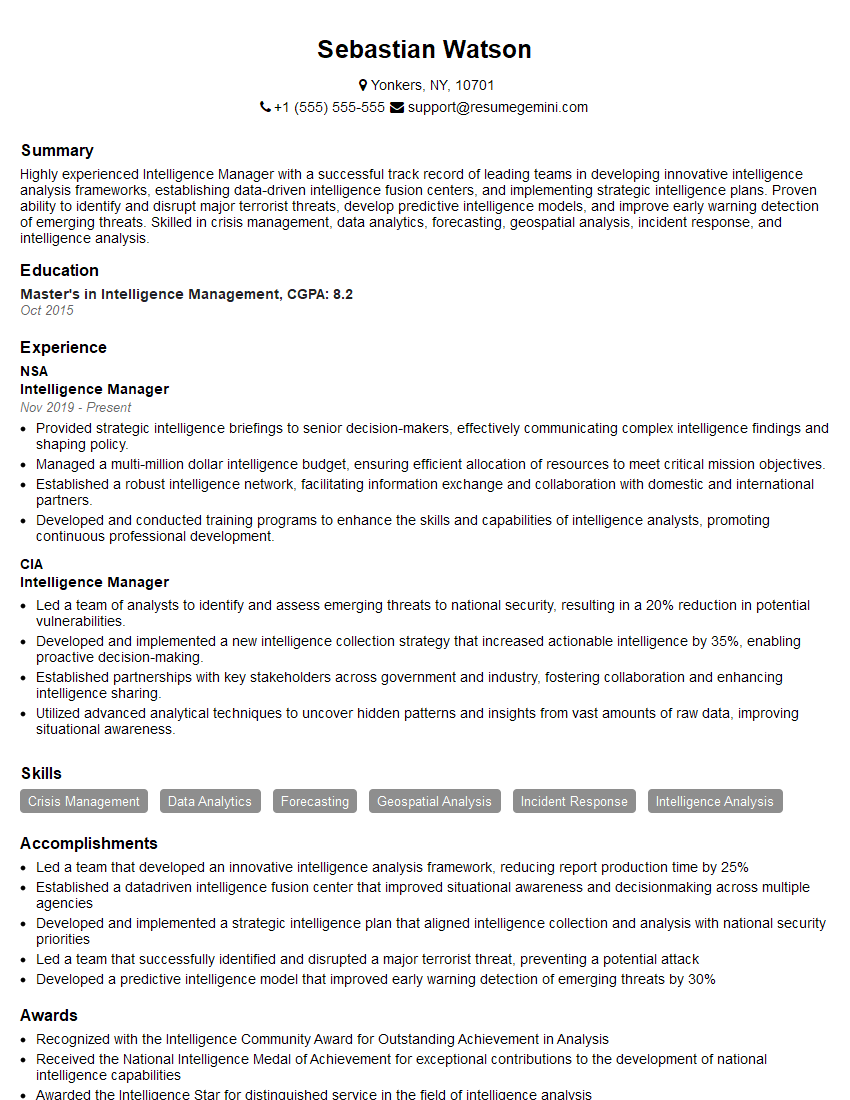
Mastering Intelligence Analysis and Fusion opens doors to exciting and impactful careers, offering opportunities for continuous learning and professional growth within national security and related fields. A strong resume is crucial for showcasing your skills and experience to potential employers. To maximize your job prospects, focus on creating an ATS-friendly resume that highlights your relevant accomplishments and keywords. ResumeGemini can significantly help you in this process by providing tools and examples to build a professional and effective resume tailored to the Intelligence Analysis and Fusion field. Examples of resumes tailored to this field are available within ResumeGemini.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good