Feeling uncertain about what to expect in your upcoming interview? We’ve got you covered! This blog highlights the most important Pin Extraction interview questions and provides actionable advice to help you stand out as the ideal candidate. Let’s pave the way for your success.
Questions Asked in Pin Extraction Interview
Q 1. Explain the process of power analysis side-channel attacks in pin extraction.
Power analysis side-channel attacks exploit the relationship between the power consumption of a cryptographic device (like a smart card) and the secret data it processes, in this case, a PIN. The underlying principle is that different cryptographic operations consume different amounts of power. By carefully measuring the power consumption during PIN verification, attackers can deduce information about the PIN itself.
The process generally involves:
- Data Acquisition: Precisely measuring the power consumption of the smart card during multiple PIN verification attempts. This often requires specialized equipment.
- Pre-processing: Cleaning and aligning the power traces to minimize noise and improve signal quality.
- Analysis: Applying statistical techniques, like correlation power analysis (CPA) or template attacks, to identify correlations between power consumption patterns and specific bits or parts of the PIN. This often requires sophisticated signal processing and statistical expertise.
- PIN Reconstruction: Using the extracted information to reconstruct the full PIN.
Example: Imagine a smart card comparing a user’s entered PIN digit to a stored digit. The comparison operation might consume significantly more power if the digits match than if they don’t. By analyzing many power traces, an attacker could identify this power difference and deduce the correct digit.
Q 2. Describe different methods for extracting PINs from smart cards.
Extracting PINs from smart cards is a challenging task, often requiring specialized expertise and sophisticated tools. Methods include:
- Power Analysis Attacks (as described above): Differential Power Analysis (DPA) and Correlation Power Analysis (CPA) are powerful techniques.
- Fault Injection Attacks: These attacks involve introducing faults (e.g., glitches in power supply or clock signals) during PIN verification to disrupt the cryptographic process and extract information about the PIN. This can lead to revealing the PIN or parts of the cryptographic key.
- Electromagnetic Analysis (EMA): Similar to power analysis, but uses electromagnetic emissions instead of power consumption as a side channel. This can reveal information about the internal state of the smart card.
- Physical Attacks: This could involve physically tampering with the card, such as using microscopes to find out how the PIN is stored, or even using highly sophisticated techniques to extract the data.
- Software-based Attacks: Exploiting vulnerabilities in the smart card’s software or its interaction with a reader device.
The effectiveness of each method depends on factors like the smart card’s security features, the attacker’s resources, and the specific implementation of the PIN verification process.
Q 3. What are the ethical considerations surrounding PIN extraction?
The ethical considerations surrounding PIN extraction are paramount. It’s crucial to remember that PINs are sensitive personal information that protects financial accounts and other vital data. Extracting PINs without authorization is illegal and can lead to severe consequences, including:
- Identity theft: Unauthorized access to financial accounts can lead to significant financial loss and damage to an individual’s credit rating.
- Fraud: Stolen PINs can be used to make fraudulent purchases or transfers.
Ethical considerations also extend to the development of security measures. Researchers working on PIN extraction techniques have a responsibility to use their knowledge responsibly and ethically, for example by disclosing vulnerabilities to manufacturers so they can be addressed, rather than exploiting them for malicious purposes.
Q 4. How does fault injection work in the context of PIN extraction?
Fault injection attacks manipulate the normal operation of a smart card during PIN verification to extract information. By introducing a temporary fault (e.g., a brief power glitch, a clock pulse alteration, or radiation pulse), the attacker can cause errors in the cryptographic calculations. These errors can leak information about the PIN or cryptographic key used.
Several techniques exist, including:
- Power Glitching: Briefly disrupting the power supply to cause a malfunction.
- Clock Glitching: Manipulating the clock signal to interfere with the timing of cryptographic operations.
- Laser Fault Injection: Targeting specific components with a laser pulse.
The goal is often to cause a predictable error that reveals information about the internal state, thereby assisting in PIN reconstruction. For example, a fault might cause the smart card to return an unexpected response, or it might reveal intermediate results of the cryptographic calculation. It’s a highly specialized attack, usually requiring considerable expertise and equipment.
Q 5. Compare and contrast invasive and non-invasive PIN extraction techniques.
The key difference lies in the level of physical interaction with the smart card.
- Non-invasive techniques analyze the card’s side channels (power consumption, electromagnetic emissions) without physically altering it. Examples include DPA, CPA, and EMA. These are often preferred due to lower risk of detection and card damage, though they can be harder to execute successfully.
- Invasive techniques directly manipulate or damage the card. These might involve de-packaging the card to access its internal components, using probes to modify its circuitry, or using destructive methods. Examples include techniques that physically probe the integrated circuit or use laser fault injection to alter its behavior. Invasive techniques tend to be more effective, but they risk destroying the card and are far easier to detect.
Both types have their advantages and disadvantages. Non-invasive attacks are subtler, while invasive ones can be far more effective but risk more significant detection. The choice depends on the attacker’s goals, resources, and risk tolerance.
Q 6. What are some common countermeasures against PIN extraction attacks?
Many countermeasures exist to protect against PIN extraction attacks. They often involve a multi-layered approach:
- Hardware countermeasures: These include using tamper-resistant packaging, incorporating physical security features, and designing secure hardware architectures to resist power analysis and fault injection attacks. This could include shielding, power regulation, and clock stabilization.
- Software countermeasures: This could include randomizing the timing of cryptographic operations, adding noise to power consumption, implementing masking techniques that hide intermediate values from attackers, and using secure random number generators for key generation.
- Algorithm selection: Choosing cryptographic algorithms that are inherently resistant to side-channel attacks is vital.
- Regular software updates: Patching software vulnerabilities promptly is essential.
- PIN entry limitations: Limiting the number of incorrect PIN attempts helps mitigate brute-force attacks.
- Smart card design: Implementing physical protection mechanisms that make tampering difficult or detectable, such as embedded sensors.
A combination of these techniques is generally necessary to provide robust protection.
Q 7. Explain the concept of differential power analysis (DPA).
Differential Power Analysis (DPA) is a powerful side-channel attack that exploits the correlation between power consumption and the intermediate values processed during cryptographic operations. It’s particularly effective against cryptographic algorithms that use iterative processes.
The basic idea is this:
- Hypothesize a PIN value (or part of it).
- Predict the power consumption pattern based on the hypothesized PIN and the algorithm’s implementation. This uses statistical modelling and information on how the algorithm operates.
- Compare the prediction to the actual power traces. If the hypothesized PIN is correct, a strong correlation between predicted and measured power consumption will be observed.
- Iterate and refine. The attacker refines the hypothesis until a high correlation is achieved, indicating the correct value.
DPA is especially effective because it doesn’t require the attacker to understand the exact details of the algorithm’s implementation; it only needs to understand the general flow and which parts of the calculations are sensitive to the data being processed. It’s a sophisticated attack requiring specialized knowledge and tools.
Q 8. Describe the challenges in extracting PINs from tamper-resistant devices.
Extracting PINs from tamper-resistant devices presents significant challenges due to the security measures implemented to protect the sensitive data. These measures aim to make physical manipulation or data extraction extremely difficult.
- Physical Security: Devices often incorporate robust casings, making physical access and manipulation challenging. Specialized tools and expertise are required to bypass these physical barriers.
- Cryptographic Protection: PINs are rarely stored in plain text. Instead, they’re typically encrypted or hashed using strong cryptographic algorithms. Breaking these algorithms requires significant computational power and advanced techniques.
- Tamper Evidence: Many devices are designed to detect attempts at tampering. This might involve triggering alarms, erasing data, or self-destructing the PIN storage area.
- Power Management: Precise power control is essential for many attack methods, and unexpected power fluctuations can disrupt the process.
Imagine trying to open a high-security safe – it requires specialized tools and a deep understanding of its mechanisms. PIN extraction from tamper-resistant devices is similarly complex and requires advanced skills and technology.
Q 9. What are the legal implications of performing PIN extraction?
The legal implications of performing PIN extraction are severe and vary depending on jurisdiction. Generally, unauthorized access to and extraction of PINs is illegal and carries significant consequences.
- Violation of Privacy: PINs are personal and confidential data. Their extraction infringes upon an individual’s right to privacy.
- Fraud and Theft: Extracted PINs are commonly used for fraudulent activities, such as unauthorized access to bank accounts, credit cards, or other financial assets. This can lead to serious financial losses and legal repercussions for the perpetrator.
- Computer Crime Laws: Many jurisdictions have laws specifically targeting unauthorized access to computer systems and data, including PINs. These laws often carry substantial penalties, including hefty fines and imprisonment.
- Civil Liability: Victims of PIN extraction can pursue civil lawsuits against perpetrators for damages incurred as a result of the fraudulent activities.
Attempting PIN extraction without authorization is akin to breaking into someone’s home and stealing their valuables – it’s a serious crime with serious consequences. Ethical considerations are paramount in this field. Only authorized professionals with legal justification should be involved in any PIN extraction procedures.
Q 10. How does electromagnetic analysis (EMA) work for PIN extraction?
Electromagnetic Analysis (EMA) is a powerful side-channel attack used for PIN extraction. It works by measuring the electromagnetic emanations emitted by a device during its operation. These emanations contain information that can reveal secrets such as PINs, even if the device’s physical access is secure.
During a cryptographic operation (like PIN verification), the device’s internal components generate electromagnetic signals. These signals are subtle, but they leak information about the internal processes. Specialized probes are used to capture these emanations. By analyzing these signals, an attacker can potentially identify patterns correlated with the PIN being processed.
For example, the power consumption of a chip can change slightly depending on the bits being processed. These subtle power variations can leak data related to the PIN. Advanced techniques involving signal processing and machine learning are employed to analyze the captured data and extract the PIN.
EMA is a complex technique requiring specialized equipment and deep expertise in signal processing and cryptography.
Q 11. Explain the role of glitching in PIN extraction.
Glitching, also known as power glitching, is a fault injection attack used in PIN extraction. It involves disrupting the normal operation of a target device by introducing brief glitches in its power supply. These glitches can cause the device to malfunction temporarily, potentially revealing sensitive information.
By carefully timing and controlling these power glitches, attackers can force the device into an unexpected state where security checks might be bypassed, allowing access to sensitive information, including the PIN. The idea is to cause a temporary fault that disrupts the normal execution flow of the software, causing it to reveal or behave in an unintended manner which can then be exploited.
Imagine briefly interrupting the power supply to a computer during a critical operation; this might cause the system to crash or freeze, possibly revealing data in memory that would normally be protected. The precision of the glitch is critical to avoid permanently damaging the device while successfully extracting data.
Q 12. What are some common tools used for PIN extraction?
Several tools are used for PIN extraction, ranging from specialized hardware to sophisticated software. The choice of tools depends on the target device and the chosen attack method.
- Logic Analyzers: These capture the digital signals within a device, allowing analysis of data flows and timing patterns.
- Oscilloscope: Used to visually analyze analog signals, including electromagnetic emanations.
- Electromagnetic Probes: These capture the electromagnetic emissions from a device during operation.
- Power Glitching Equipment: Devices capable of precisely controlling and injecting power glitches into the target.
- Software Defined Radios (SDRs): Can be used for advanced side-channel attacks, such as electromagnetic analysis.
- Specialized Software: Software is often used to process the captured data, analyze the signals, and attempt to extract the PIN.
The specific tools used are highly dependent on the target device and the attack vector employed. Many of these tools are sophisticated and require significant expertise to operate effectively.
Q 13. Describe the process of extracting PINs from a specific device (e.g., ATM card).
Extracting a PIN from an ATM card typically involves advanced techniques, often leveraging side-channel attacks like EMA or glitching. The process is complex and requires specialized equipment and skills.
Hypothetical scenario using EMA: The attacker might use an electromagnetic probe to capture the electromagnetic emanations from the ATM card reader as a card is inserted and the PIN is entered. The captured data will be analyzed using sophisticated signal processing techniques. By correlating the electromagnetic emissions with the timing of key presses or specific operations in the card reader, the attacker can potentially identify patterns that reveal the PIN.
Hypothetical scenario using glitching: The attacker could use a power glitching device to introduce precisely timed voltage drops to the card reader during PIN entry. This could momentarily disrupt the chip’s normal operation and potentially reveal the PIN in its temporary memory or cause it to behave unpredictably, revealing information about the PIN.
Important Note: These are highly simplified hypothetical scenarios. Actual PIN extraction from an ATM card is significantly more complex, requiring a deep understanding of the card reader’s hardware and software, sophisticated tools, and extensive expertise.
Q 14. How does software-based PIN extraction differ from hardware-based methods?
Software-based PIN extraction and hardware-based methods differ fundamentally in their approach and capabilities.
- Software-based methods typically involve exploiting vulnerabilities in the software running on a device, such as buffer overflows or logical flaws. These methods rely on weaknesses in the software’s code to gain unauthorized access to the PIN or to manipulate the system’s behavior to reveal the PIN.
- Hardware-based methods focus on directly interacting with the physical hardware of the device. This includes side-channel attacks like EMA and glitching, which analyze the device’s physical emissions or manipulate its power supply to extract information.
Software-based attacks are often easier to implement if vulnerabilities exist but are highly dependent on the target software’s weaknesses and can be mitigated by software updates. Hardware-based attacks are more difficult to implement, requiring specialized tools and expertise, but they can often bypass software-level security measures.
Imagine a house with a weak lock (software vulnerability) versus a house with extremely strong walls (hardware security). A software attack is like picking the lock, whereas a hardware attack is like breaking through the walls. Both approaches have their strengths and weaknesses.
Q 15. Explain the concept of clock glitches and how they are used in pin extraction.
Clock glitches, in the context of pin extraction, are carefully timed disruptions to a device’s clock signal. These disruptions are intentionally introduced to force the device into unpredictable states, revealing sensitive information like cryptographic keys or PINs. Imagine a perfectly timed stumble in a dancer’s routine – the stumble itself isn’t the goal, but the resulting unexpected pose might reveal something hidden. Similarly, a clock glitch forces the device to momentarily behave erratically, potentially leaking its secrets.
During pin extraction, attackers utilize these glitches to manipulate the timing of cryptographic operations, causing the device to reveal intermediate values or bypass security checks. A well-timed glitch might cause a conditional branch in the algorithm to be taken or skipped, leading to the exposure of sensitive data. This is often combined with other techniques like power analysis or fault injection to maximize the chances of success.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. What are the limitations of using optical methods for pin extraction?
Optical methods for pin extraction, while offering a non-invasive approach, suffer from several limitations. Primarily, the resolution and depth of penetration are often insufficient to directly observe the internal workings of a modern chip. Think of trying to examine the intricate gears of a watch from a distance – you can see some parts, but the finer details escape your view. Similarly, optical methods may struggle to resolve small features or pinpoint the precise location of data within the device’s memory.
Another limitation is the sensitivity to surface reflections and scattering, which can obscure the data being observed. This is especially problematic when trying to capture the fleeting signals related to the cryptographic operations. Furthermore, the need for specialized equipment and expertise makes this method expensive and not readily accessible.
Q 17. Discuss the role of signal processing in analyzing data obtained during pin extraction.
Signal processing plays a critical role in analyzing the data acquired during pin extraction. The raw data often contains a mixture of noise and the signal of interest. It’s like trying to hear someone’s voice in a crowded room – the signal (the voice) is weak, and the noise (the chatter) is overwhelming. Signal processing techniques like filtering, averaging, and correlation are used to isolate and amplify the relevant signals, enhancing the chances of extracting the desired information.
For instance, power analysis techniques produce data containing subtle fluctuations in power consumption, related to specific cryptographic operations. Signal processing helps to identify and interpret these fluctuations, allowing researchers to draw inferences about the secret key or PIN. Specifically, techniques like wavelet transforms and Fourier analysis can be applied to remove noise and highlight patterns within the signals.
Q 18. How can you protect against attacks targeting the communication protocol of a device during pin extraction?
Protecting against attacks targeting the communication protocol during pin extraction involves a multi-layered approach focused on securing the communication channel itself. Think of it like protecting your home – you wouldn’t just lock the front door; you would also use security cameras, alarms, and strong locks on all windows. Similarly, strong encryption is essential, ideally employing a robust protocol like TLS or IPsec to encrypt all communications. Regular security audits and penetration testing are crucial to identify and address vulnerabilities in the communication protocol.
Authentication mechanisms such as mutual authentication (both the device and the extraction system verifying each other’s identity) provide another layer of security. Implementing access control mechanisms, restricting access based on user roles and privileges, prevents unauthorized access. Finally, regularly updating firmware and software can patch known vulnerabilities, minimizing risks.
Q 19. Describe different types of fault injection techniques used in PIN extraction.
Several fault injection techniques are employed in PIN extraction. These techniques aim to induce temporary malfunctions in the target device to reveal information. Imagine accidentally hitting a few keys on a keyboard – you might introduce errors in the text, and similarly, fault injection introduces errors in a device’s computation.
- Power Glitches: Brief interruptions in the power supply disrupt the device’s operation.
- Clock Glitches (as discussed above): Disrupting the timing signal.
- Electromagnetic Fault Injection (EMFI): Using electromagnetic pulses to manipulate internal states.
- Laser Fault Injection: Using precisely targeted laser pulses to alter memory or logic circuits.
The choice of technique depends on factors like the target device’s architecture and the attacker’s resources. Each method requires specialized equipment and expertise, and the effectiveness varies depending on factors like the device’s shielding and the specific implementation of its security measures.
Q 20. What are the advantages and disadvantages of using laser fault injection?
Laser fault injection offers high precision and spatial control, allowing attackers to target specific memory locations or logic circuits with minimal collateral damage. It’s like using a scalpel instead of a hammer to perform a delicate operation – accuracy is paramount. This precision can increase the chances of success and reduce the risk of unintended consequences that might render the device unusable.
However, laser fault injection also has disadvantages. The equipment is expensive and requires specialized expertise to operate. The technique is sensitive to the target device’s physical properties (packaging material, shielding). Finally, it may not be effective against devices with robust countermeasures against fault injection.
Q 21. How can you identify and mitigate the risks associated with power analysis attacks?
Power analysis attacks exploit the relationship between a device’s power consumption and its internal computations. By observing the power traces, attackers can deduce information about the secret key or PIN. It’s like observing the flicker of a light bulb to infer the activities within a room – the subtle changes in the power consumption can reveal a great deal of information.
Mitigating power analysis attacks requires a multi-pronged approach. Techniques like masking, which adds random noise to the power consumption, make it difficult to distinguish the meaningful signals from the noise. Furthermore, using constant-time algorithms ensures that the execution time and power consumption are independent of the secret data. Regular security audits and penetration testing identify potential vulnerabilities.
Q 22. Explain the concept of template attacks in the context of pin extraction.
Template attacks exploit the side-channel information leaked during cryptographic operations, such as power consumption or execution time, to indirectly reveal the secret PIN. Imagine a thief trying to guess a combination lock by observing how much force is needed to turn the dials – they aren’t directly seeing the combination, but they’re gathering clues about each digit. Similarly, a template attack builds a ‘template’ representing the power consumption pattern for each possible PIN. By comparing the power consumption of a target device during PIN entry to these templates, the attacker can identify the most likely PIN.
For example, if a smart card uses a specific power consumption pattern for the PIN ‘1234’, an attacker might have already profiled that pattern. If the device shows a similar pattern during a transaction, ‘1234’ becomes the strongest candidate. The success of these attacks heavily relies on having a sufficiently large number of samples to build the templates and accurately model the noise present in the measurements.
Q 23. Discuss the use of machine learning in enhancing the effectiveness of pin extraction.
Machine learning algorithms, particularly those suited for pattern recognition and anomaly detection, significantly boost PIN extraction effectiveness. They can analyze complex and noisy side-channel data, far exceeding human capabilities. For instance, Support Vector Machines (SVMs) and Artificial Neural Networks (ANNs) can identify subtle correlations between PIN digits and various side-channel characteristics like electromagnetic emissions or timing variations, enhancing accuracy and efficiency.
These algorithms learn from a dataset of measured side-channel information associated with known PINs. Once trained, they can predict the PIN corresponding to new side-channel measurements from an untrusted device. Moreover, machine learning can adapt to different device models and variations in side-channel leakage patterns, improving the robustness of PIN extraction attacks.
Q 24. Describe the role of physical access in pin extraction.
Physical access is often a prerequisite for many PIN extraction techniques. Think of it as the key to the lock – you can’t pick a lock if you don’t have access to it. With physical access, an attacker can employ various methods like:
- Direct hardware manipulation: This could involve using specialized equipment like a logic analyzer to directly intercept PIN information as it travels on the device’s internal buses.
- Software-based attacks: After gaining physical access, malicious software can be installed to record keystrokes or capture screen data.
- Side-channel attacks: Physical access allows the attacker to be positioned near the device to capture electromagnetic emissions or measure subtle timing variations, using specialized equipment.
The level of physical access required varies depending on the attack method, ranging from simply being able to observe the device’s operation to having the ability to physically disassemble and probe the device.
Q 25. What are the differences between contactless and contact-based pin extraction techniques?
Contactless PIN extraction, typically targeting NFC-enabled devices, relies on capturing radio frequency signals transmitted during communication. These signals might reveal parts of the PIN or allow for relay attacks where the attacker intercepts the communication between the device and a reader. Contact-based techniques, in contrast, require direct physical interaction. This could include direct hardware probing, manipulating the device’s software, or capturing side-channel data (power consumption, timing) through physical proximity.
The fundamental difference lies in the proximity and interaction level. Contactless attacks aim to capture data remotely via RF signals, while contact-based attacks require direct physical access and can employ more intrusive techniques.
Q 26. How does the complexity of the cryptographic algorithm influence the difficulty of pin extraction?
The complexity of the cryptographic algorithm used to protect the PIN significantly impacts the difficulty of extraction. A robust algorithm, like a well-implemented AES (Advanced Encryption Standard) with a long key, makes direct extraction of the PIN extremely challenging. Brute-forcing such an algorithm would be computationally infeasible. However, even strong encryption doesn’t eliminate all vulnerabilities. Side-channel attacks, for example, can still exploit subtle information leaked during the cryptographic process, bypassing the algorithm’s inherent strength.
Simpler or poorly implemented algorithms, on the other hand, are much more vulnerable. Weak algorithms or those with known vulnerabilities increase the likelihood of successful attacks.
Q 27. Describe the challenges in extracting PINs from devices with advanced security features (e.g., encryption, hashing).
Modern devices employ various advanced security features to thwart PIN extraction attempts. Encryption protects the PIN in transit and at rest; hashing creates one-way functions that make retrieving the original PIN impossible; tamper-resistant hardware detects and prevents unauthorized access or modification. These measures make direct extraction extremely difficult. Attackers may need to resort to more sophisticated techniques, such as:
- Fault injection attacks: These involve temporarily disrupting the device’s operation to induce errors in the cryptographic process, revealing information about the PIN.
- Advanced side-channel analysis: Combining multiple side-channel measurements and advanced signal processing techniques to improve the accuracy of template attacks.
- Exploiting software vulnerabilities: Finding and exploiting weaknesses in the device’s software to bypass security controls.
Overcoming these advanced security features requires significant expertise and resources, making PIN extraction a complex and challenging endeavor.
Q 28. What are some emerging trends in the field of PIN extraction?
The field of PIN extraction is constantly evolving, driven by advancements in both attack and defense techniques. Some key emerging trends include:
- AI-driven attacks: More sophisticated machine learning algorithms are being developed to improve the accuracy and efficiency of side-channel analysis.
- Quantum computing’s potential threat: Future quantum computers could potentially break many currently used cryptographic algorithms, posing a significant threat to PIN security.
- Enhanced hardware security: Researchers are exploring new hardware security solutions, such as physically unclonable functions (PUFs) and trusted execution environments (TEEs), to protect sensitive data like PINs more effectively.
- Biometric authentication: The growing adoption of biometric authentication is expected to reduce the reliance on traditional PIN-based systems, mitigating the impact of PIN extraction attacks.
The arms race between attackers and defenders will continue to shape this field, driving innovation in both attack and defense methods.
Key Topics to Learn for Pin Extraction Interview
- Fundamentals of Pin Extraction: Understanding the core principles and methodologies behind various pin extraction techniques.
- Data Acquisition and Preprocessing: Exploring methods for obtaining relevant data and preparing it for analysis, including data cleaning and transformation.
- Algorithm Selection and Implementation: Evaluating different algorithms suitable for pin extraction and understanding their strengths and weaknesses. Practical experience implementing these algorithms is crucial.
- Accuracy and Precision: Analyzing the accuracy and precision of different pin extraction methods and understanding the factors that influence them. This includes error analysis and mitigation strategies.
- Ethical Considerations: Understanding the ethical implications of pin extraction and adhering to best practices and legal regulations.
- Advanced Techniques: Exploring advanced topics such as image processing techniques for pin extraction, handling noisy data, and optimizing for speed and efficiency.
- Problem-Solving and Debugging: Developing strong problem-solving skills to identify and resolve issues encountered during the pin extraction process.
- Case Studies and Real-world Applications: Reviewing real-world examples of pin extraction applications and how different techniques were implemented and optimized.
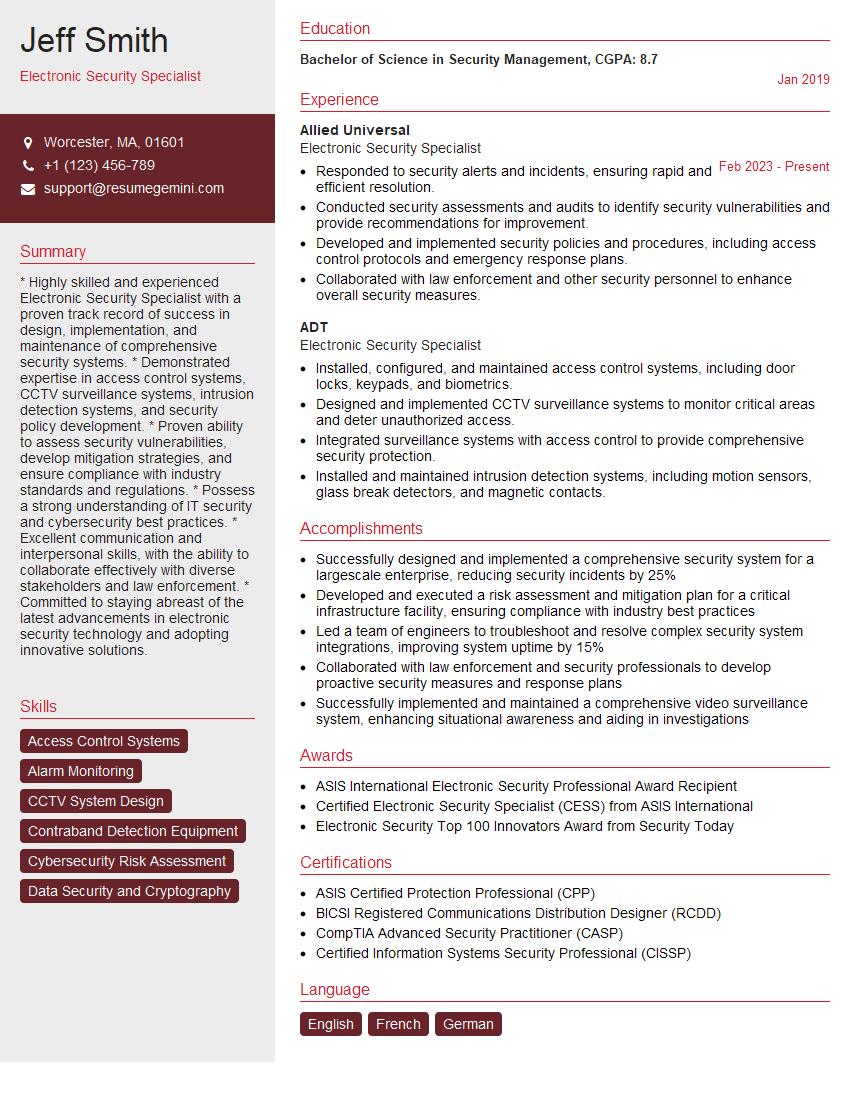
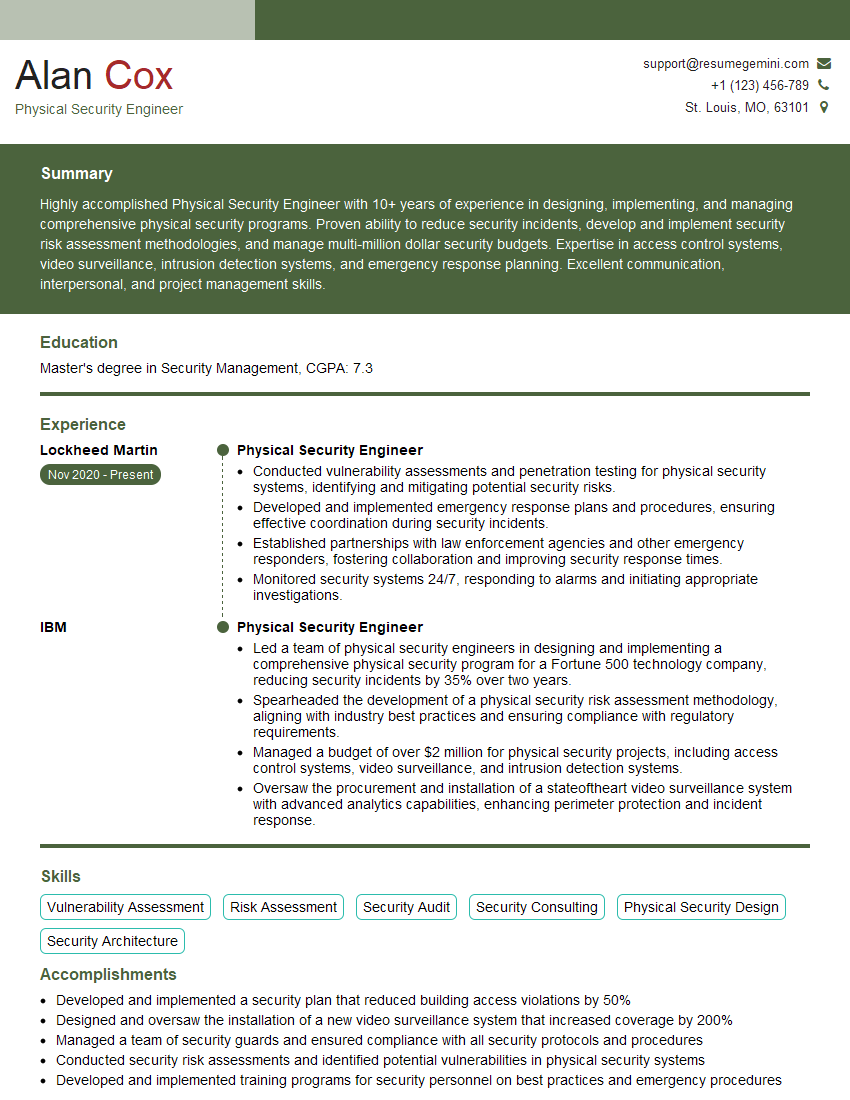
Next Steps
Mastering Pin Extraction opens doors to exciting career opportunities in fields demanding high accuracy and precision. A strong understanding of these techniques significantly enhances your value to potential employers. To maximize your job prospects, invest time in creating an ATS-friendly resume that highlights your skills and experience effectively. ResumeGemini is a trusted resource that can help you build a professional and impactful resume tailored to the specific demands of Pin Extraction roles. Examples of resumes tailored to Pin Extraction are available to help guide you.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good