Every successful interview starts with knowing what to expect. In this blog, we’ll take you through the top Situational Awareness and Risk Management interview questions, breaking them down with expert tips to help you deliver impactful answers. Step into your next interview fully prepared and ready to succeed.
Questions Asked in Situational Awareness and Risk Management Interview
Q 1. Describe your process for conducting a risk assessment.
My risk assessment process follows a structured approach, ensuring comprehensive coverage and actionable insights. It begins with identification, where I systematically brainstorm potential hazards through techniques like brainstorming sessions, checklists, HAZOP (Hazard and Operability) studies, and reviewing historical data. This phase critically involves understanding the context – the system, its environment, and potential interactions. Next comes analysis, where I evaluate the likelihood and potential impact of each identified risk. This can be qualitative (high, medium, low) or quantitative (using statistical models and data). The evaluation stage involves prioritizing risks based on a risk matrix (likelihood vs. impact). Finally, I develop control measures (mitigation strategies) and document the entire process in a risk register. This register is then regularly reviewed and updated.
For example, in assessing risks for a new software launch, I’d identify risks like coding errors leading to system crashes, insufficient user training leading to low adoption, or competitor actions impacting market share. Each risk would be analyzed for likelihood and potential impact, prioritized, and appropriate mitigation strategies (e.g., rigorous testing, comprehensive training materials, competitive market analysis) would be developed.
Q 2. Explain the difference between qualitative and quantitative risk analysis.
Qualitative and quantitative risk analysis differ primarily in their approach to assessing risk. Qualitative analysis uses subjective judgment and descriptive scales (e.g., high, medium, low) to estimate likelihood and impact. It’s often quicker and less data-intensive but less precise. Quantitative analysis, on the other hand, uses numerical data and statistical methods to assign probabilities and potential financial losses to risks. It provides a more precise estimate but demands more data and resources.
Imagine assessing the risk of a product recall. A qualitative approach might describe the likelihood of a defect as ‘high’ and the impact as ‘severe,’ based on expert opinions and past experience. A quantitative approach might use historical data on defect rates and cost of recall to assign a specific probability (e.g., 15% chance of recall) and a financial loss estimate (e.g., $5 million).
Q 3. How do you prioritize risks based on likelihood and impact?
Risk prioritization is crucial for effective risk management. I commonly use a risk matrix, a visual tool plotting likelihood against impact. Each risk is placed on the matrix based on its assessed likelihood and impact scores. Risks in the high-likelihood, high-impact quadrant are prioritized first. Various scoring methods can be employed; for instance, a simple scale of 1-5 for both likelihood and impact, with scores multiplied to get a risk score. Higher risk scores indicate higher priority.
For instance, a risk with high likelihood (4) and high impact (5) would have a risk score of 20, taking precedence over a risk with low likelihood (2) and medium impact (3), having a score of 6. Beyond the matrix, we may consider factors such as urgency, regulatory requirements, and organizational tolerance for risk when fine-tuning prioritization.
Q 4. What are some common risk mitigation strategies?
Common risk mitigation strategies include:
- Avoidance: Eliminating the risk entirely by not undertaking the activity. For example, not launching a product in a volatile market.
- Reduction: Implementing controls to lessen the likelihood or impact of the risk. For example, implementing stricter quality control measures to reduce the likelihood of product defects.
- Transfer: Shifting the risk to a third party, such as through insurance or outsourcing. For example, purchasing insurance to cover potential liabilities.
- Acceptance: Acknowledging the risk and accepting the potential consequences. This is often used for low-likelihood, low-impact risks. For example, accepting the minor risk of equipment malfunction due to its low likelihood and minimal impact.
The choice of strategy depends on the specific risk, its characteristics, and the organization’s risk appetite.
Q 5. Describe a time you identified a potential risk before it became a problem.
During a large-scale software implementation project, I noticed a lack of communication protocols between different development teams. While everyone was individually performing well, the potential for integration issues and delays was significant. This was a latent risk – not immediately apparent as a problem. I proactively proposed establishing clear communication channels, regular progress meetings, and a shared documentation system. This prevented significant delays and integration challenges later in the project, saving time and resources.
Q 6. How do you communicate risk effectively to different audiences?
Effective risk communication is crucial. My approach is tailored to the audience. For executives, I focus on the high-level summary, highlighting key risks and their potential financial impacts. For technical teams, I provide detailed risk assessments, including mitigation strategies and technical specifications. For stakeholders, I use clear, concise language, avoiding technical jargon. I often use visual aids like risk matrices, charts, and graphs to improve understanding.
For example, when presenting risks to senior management, I’d use a dashboard showing the top 3-5 risks with their likelihood, impact, and proposed mitigation strategies, highlighting potential financial losses. When discussing with engineers, I’d present a detailed risk register and technical documents, allowing for a deep dive into specific issues.
Q 7. What is your experience with risk registers and reporting?
I have extensive experience with risk registers and reporting. I use risk registers to document all identified risks, their likelihood and impact, mitigation strategies, responsible parties, and timelines. The register is a dynamic document, updated regularly to reflect changes and new information. My reporting focuses on key risk indicators (KRIs), tracking progress on mitigation efforts and identifying emerging risks. Reports are tailored to audience needs, ranging from high-level summaries for executive dashboards to detailed reports for risk management committees. I also leverage software tools to automate risk register management and reporting.
For example, I might use a spreadsheet or dedicated risk management software to manage the risk register. Regular reports might include a summary of open risks, their status, and progress towards mitigation, as well as any new risks identified and their potential impact.
Q 8. How do you stay current with emerging risks in your field?
Staying current with emerging risks in situational awareness and risk management requires a multi-faceted approach. It’s not just about reading reports; it’s about actively participating in the evolving landscape.
- Industry Publications and Conferences: I regularly subscribe to leading journals and attend industry conferences to learn about the latest threats and vulnerabilities. For example, attending the annual RSA Conference provides invaluable insights into cybersecurity risks, a critical aspect of situational awareness.
- Threat Intelligence Platforms: I utilize various threat intelligence platforms that aggregate data from numerous sources, providing early warnings of emerging risks. These platforms often offer threat modeling tools and vulnerability databases that are critical for proactive risk management.
- Networking and Collaboration: Maintaining a strong professional network is essential. Discussions with peers and experts from diverse backgrounds offer unique perspectives and insights into emerging threats that might not be publicly available.
- Scenario Planning and War Games: Regularly engaging in scenario planning and war games allows us to proactively identify potential risks and test our mitigation strategies before they become real-world problems. This ensures our plans remain relevant and effective.
- Government and Regulatory Updates: Staying informed on changes in regulations and governmental advisories is vital, as these often highlight newly identified risks and provide guidance on best practices.
This holistic approach ensures I remain ahead of the curve and can effectively address emerging risks in a timely and informed manner.
Q 9. Describe your experience with implementing a risk management framework.
In a previous role, I was instrumental in implementing a comprehensive risk management framework based on the NIST Cybersecurity Framework. This involved a collaborative effort across multiple departments.
- Risk Identification: We began by conducting thorough risk assessments, utilizing both qualitative and quantitative methods. This included brainstorming sessions with stakeholders from various departments to identify potential threats and vulnerabilities. We used a combination of surveys, interviews, and document reviews to gather comprehensive data.
- Risk Analysis and Prioritization: We analyzed each identified risk, considering its likelihood and potential impact. This enabled us to prioritize risks based on their severity, focusing resources on the most critical threats. We used a risk matrix to visually represent the likelihood and impact of each risk.
- Risk Response Planning: For each prioritized risk, we developed tailored mitigation strategies, leveraging a combination of avoidance, reduction, transfer, and acceptance strategies. For example, for a cybersecurity risk, we implemented multi-factor authentication and strengthened our firewall.
- Monitoring and Review: The framework included a robust monitoring and review process, with regular assessments to evaluate the effectiveness of our mitigation strategies and to identify any new or emerging risks. Key Risk Indicators (KRIs) were established to track the success of our risk management program.
This structured approach ensured a consistent and effective risk management process across the organization, significantly reducing our exposure to various threats.
Q 10. How do you measure the effectiveness of risk mitigation strategies?
Measuring the effectiveness of risk mitigation strategies is crucial for continuous improvement. This is done through a combination of quantitative and qualitative methods.
- Key Risk Indicators (KRIs): We track KRIs to monitor the success of our mitigation strategies. For instance, if our mitigation strategy aims to reduce phishing attacks, a KRI could be the number of successful phishing attempts per month. A decrease in this KRI would indicate the strategy’s effectiveness.
- Regular Audits and Assessments: We conduct regular internal and external audits to independently verify the effectiveness of our controls and identify any gaps in our risk management program. These audits provide objective evidence of our success.
- Incident Response Data: Analyzing incident response data helps us evaluate the effectiveness of our mitigation strategies in real-world scenarios. For instance, if a security incident occurs, we analyze the response and determine if our mitigation strategies effectively contained the damage.
- Post-Incident Reviews: After significant incidents, we conduct thorough post-incident reviews to identify areas of improvement and refine our strategies for future events. This process is crucial for learning from mistakes and continuously improving our preparedness.
- Stakeholder Feedback: Gathering feedback from stakeholders across the organization allows us to assess the overall effectiveness of our risk management program and identify areas for enhancement. This often leads to important insights that might not be captured through quantitative methods alone.
By employing these methods, we can objectively evaluate the success of our risk mitigation efforts, making necessary adjustments to optimize our program and minimize our overall risk profile.
Q 11. Explain your understanding of key risk indicators (KRIs).
Key Risk Indicators (KRIs) are measurable metrics used to monitor the likelihood and potential impact of identified risks. They serve as early warning signals, providing insights into the effectiveness of risk mitigation strategies and indicating potential problems before they escalate into major incidents.
Think of KRIs as the vital signs of your organization’s health in terms of risk. Just as a doctor monitors a patient’s blood pressure and heart rate, we monitor KRIs to gauge the health of our risk profile.
- Examples: A KRI for cybersecurity might be the number of successful login attempts from unauthorized IP addresses. For operational risk, it might be the number of customer complaints or production downtime hours. For financial risk, it might be the debt-to-equity ratio or the rate of customer churn.
- Purpose: KRIs help us proactively identify potential issues, allocate resources effectively, and demonstrate the effectiveness of our risk management program to stakeholders.
- Selection: Choosing the right KRIs is crucial. They should be relevant to the specific risks faced by the organization, measurable, and readily available.
KRIs are an essential part of a proactive risk management approach, enabling us to anticipate and mitigate threats before they become significant problems.
Q 12. How do you handle conflicting priorities in risk management?
Conflicting priorities in risk management are common. Prioritization requires a structured approach that balances competing interests and maximizes resource allocation.
- Risk Assessment and Scoring: A robust risk assessment process is critical. This involves assigning a score to each risk based on its likelihood and impact. This score helps objectively compare different risks.
- Stakeholder Alignment: Open communication and collaboration with stakeholders are crucial to understand competing priorities and build consensus. This may involve presenting a clear and concise risk profile to decision-makers, highlighting the potential consequences of inaction.
- Resource Allocation Strategy: Based on the risk scoring and stakeholder input, we develop a resource allocation strategy that prioritizes the most critical risks. This may involve deploying resources to mitigate the highest-scoring risks first while accepting or transferring less critical risks.
- Scenario Planning: Scenario planning helps explore the consequences of different prioritization decisions, allowing for a more informed and strategic approach. This can help manage expectations and build support for the chosen approach.
- Regular Review and Adjustment: The risk landscape is constantly changing. Regularly reviewing and adjusting priorities based on new information and emerging risks is essential to maintain an effective risk management program.
By using these methods, we can resolve conflicting priorities in a systematic and transparent manner, ensuring that resources are allocated efficiently to mitigate the most critical risks.
Q 13. Describe a situation where you had to make a difficult decision under pressure.
During a major security incident, we experienced a significant data breach. The pressure was immense, requiring immediate and decisive action. The situation demanded a rapid response involving multiple teams across the organization.
My first step was to activate our incident response plan. This involved immediately notifying relevant stakeholders, isolating the affected systems, and launching a forensic investigation to identify the source and extent of the breach. We also focused on containing the breach and preventing further data loss.
The most difficult decision involved balancing the need for transparency with the need to protect the organization’s reputation and prevent further damage. We decided on a phased communication strategy, starting with internal stakeholders and then gradually informing external parties as more information became available. This required careful consideration of legal and regulatory requirements.
The situation demanded strategic thinking, quick decision-making under immense pressure, and effective collaboration with various teams. It underscored the importance of meticulous planning and regular testing of our incident response plan. Ultimately, we managed to contain the breach, mitigate the damage, and learn valuable lessons for future incidents.
Q 14. What are the key elements of a robust business continuity plan?
A robust business continuity plan (BCP) is crucial for ensuring organizational resilience. It outlines strategies for maintaining essential business functions during and after disruptive events.
- Risk Assessment: A thorough risk assessment identifies potential threats and vulnerabilities that could disrupt business operations. This includes natural disasters, cyberattacks, pandemics, and other unforeseen circumstances.
- Business Impact Analysis (BIA): The BIA determines the potential impact of disruptions on critical business functions. This helps prioritize which functions to recover first in the event of an incident.
- Recovery Strategies: The BCP details specific recovery strategies for each critical business function. This could involve utilizing backup systems, relocating operations, or leveraging cloud-based solutions.
- Communication Plan: A clear communication plan outlines how the organization will communicate with employees, customers, and other stakeholders during and after a disruption. This is crucial for maintaining trust and confidence.
- Testing and Training: Regular testing and training are essential to ensure that the BCP is effective and that employees know their roles and responsibilities. This can involve simulations and tabletop exercises.
- Recovery Metrics: The BCP should include key metrics to monitor the recovery process and measure the effectiveness of the plan. This could include recovery time objectives (RTOs) and recovery point objectives (RPOs).
A well-defined BCP is not just a document; it’s a living, breathing plan that undergoes regular review and updates to remain relevant and effective in the face of ever-evolving threats. It’s an investment in the long-term health and sustainability of the organization.
Q 15. How do you involve stakeholders in the risk management process?
Effective risk management isn’t a solo act; it thrives on collaboration. Stakeholder involvement is crucial from the initial risk identification phase through to mitigation and monitoring. I employ a multi-pronged approach.
- Workshops and Meetings: I facilitate interactive sessions involving all relevant stakeholders – from executives to frontline staff – to identify potential risks specific to their roles and responsibilities. This ensures a comprehensive understanding of the risk landscape from various perspectives.
- Surveys and Questionnaires: For larger groups or when gathering diverse perspectives, I use structured surveys and questionnaires to gather input efficiently and anonymously. This allows for frank feedback, particularly on sensitive issues.
- Regular Communication and Reporting: Transparent and consistent communication is paramount. I establish a clear communication plan to keep stakeholders informed of the risk assessment process, emerging risks, and the effectiveness of mitigation strategies. Regular reports, dashboards, and visual aids enhance understanding and engagement.
- Risk Registers and Collaboration Platforms: I leverage collaborative tools like shared risk registers to ensure stakeholders have access to current information, can contribute comments, and track the progress of risk mitigation efforts. This enhances transparency and accountability.
For instance, in a recent project involving the launch of a new product, I organized a series of workshops with the marketing, sales, development, and legal teams. This collaborative approach unearthed previously unidentified risks related to product liability and marketing compliance, allowing us to proactively implement mitigation strategies.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. What software or tools do you use for risk management?
The tools I use for risk management depend heavily on the context and scale of the project. I prefer a mix of qualitative and quantitative methods, supported by appropriate software.
- Spreadsheet Software (e.g., Excel, Google Sheets): For smaller projects, I use spreadsheets for basic risk registers, documenting identified risks, likelihood, impact, mitigation strategies, and owners.
- Risk Management Software (e.g., Archer, MetricStream): For larger, more complex projects, dedicated risk management software provides features for risk identification, analysis, assessment, tracking, reporting, and collaboration. These tools often integrate with other enterprise systems.
- Project Management Software (e.g., Jira, Asana): These platforms can be integrated with risk management processes, allowing risks to be tracked alongside project tasks and deadlines. This promotes a holistic view of the project’s progress and challenges.
- Data Analytics Tools (e.g., Tableau, Power BI): These are useful for visualizing risk data, identifying trends, and creating reports for management. Data visualization improves stakeholder understanding and promotes data-driven decision making.
Choosing the right tools is crucial and depends on factors such as project size, budget, existing infrastructure, and stakeholder needs. The key is to select tools that facilitate seamless collaboration and effective communication.
Q 17. How do you handle unexpected events or incidents?
Handling unexpected events requires a swift and structured response. My approach is based on a well-defined incident management plan and a proactive mindset.
- Immediate Response: The first priority is to ensure the safety and security of personnel and assets. This often involves activating emergency response protocols and communicating effectively with stakeholders.
- Assessment and Containment: Once the immediate threat is addressed, we assess the situation to understand the nature and extent of the incident, identifying its root cause and the potential impact. Containment measures are implemented to prevent further escalation.
- Investigation and Analysis: A thorough investigation is carried out to understand what happened, why it happened, and how to prevent recurrence. This might involve collecting data, interviewing witnesses, and reviewing logs.
- Corrective Actions: Based on the findings of the investigation, corrective actions are implemented to address the root causes of the incident. This could involve changes to procedures, training, or technology.
- Lessons Learned: A formal lessons-learned process is vital to improve future responses. We document the key takeaways from the incident and integrate them into our training programs and risk management processes.
For example, in a previous role, a sudden power outage disrupted our primary data center. Our incident response plan enabled us to swiftly switch to our backup system, minimizing downtime and data loss. The subsequent investigation led to upgrades to our power backup systems and improved disaster recovery procedures.
Q 18. Describe your experience with crisis management.
My crisis management experience includes several instances of navigating unexpected and high-pressure situations. I’ve found that successful crisis management hinges on effective communication, decisive leadership, and a proactive approach to risk mitigation.
In one instance, a major security breach threatened the confidentiality of sensitive customer data. My role involved leading the incident response team, coordinating with law enforcement, and communicating transparently with affected customers. We immediately implemented containment measures, launched a forensic investigation, and established a dedicated communication channel to keep stakeholders informed. The crisis highlighted the importance of robust security protocols, regular security audits, and a clear communication plan during such incidents.
My experiences emphasize the importance of:
- Pre-planning: Developing detailed crisis management plans, including communication protocols, escalation procedures, and roles and responsibilities.
- Teamwork: Building a strong, well-trained crisis management team capable of responding effectively under pressure.
- Communication: Establishing clear and consistent communication channels to keep stakeholders informed and minimize misinformation.
- Transparency: Being honest and transparent with stakeholders about the situation and the actions being taken.
- Post-incident review: Conducting a thorough review of the crisis response to identify areas for improvement and to enhance future preparedness.
Q 19. What is your understanding of situational awareness and how does it relate to risk management?
Situational awareness is the ability to understand the current state of your environment, including the relevant factors that influence your objectives, and to anticipate how that environment might change in the future. It’s a crucial component of effective risk management.
In risk management, situational awareness provides the foundation for identifying and assessing potential risks. By understanding the current context and anticipating potential changes, we can proactively identify emerging risks and develop appropriate mitigation strategies. For example, if we’re aware of a potential economic downturn, we can assess its impact on our operations and adjust our plans accordingly.
The relationship is symbiotic: strong situational awareness enhances risk management, and effective risk management contributes to improved situational awareness by prompting a deeper understanding of the environment and its potential vulnerabilities.
Q 20. How do you cultivate situational awareness in yourself and your team?
Cultivating situational awareness is an ongoing process that requires continuous effort and self-reflection. I use several techniques to enhance my own awareness and that of my team:
- Information Gathering: I actively seek out relevant information from multiple sources, including news articles, industry reports, competitor analysis, and internal reports.
- Active Listening: I prioritize active listening during meetings, discussions, and informal conversations. This helps in picking up subtle cues and early warning signals.
- Regular Reviews: I conduct regular reviews of project progress, operational data, and key performance indicators (KPIs) to identify potential issues and trends.
- Team Collaboration: I encourage open communication and collaboration among team members, enabling us to share observations, insights, and potential concerns.
- Training and Simulation: I provide training on situational awareness principles and conduct simulations to practice responses to various scenarios. These exercises enhance awareness and build team cohesion.
- Debriefing Sessions: After significant events, both successful and unsuccessful, I lead debriefing sessions to analyze the situation, identify lessons learned, and enhance our collective awareness.
For example, I recently introduced a daily “huddle” for my team where we briefly discuss current projects, potential roadblocks, and any emerging concerns. This simple practice has significantly improved our collective situational awareness and our ability to respond proactively to potential challenges.
Q 21. Describe a time you failed to anticipate a risk. What did you learn?
In a past project involving the launch of a new software application, I underestimated the potential impact of user adoption challenges. While we had conducted thorough testing, we failed to anticipate the resistance from users accustomed to the older system. This resulted in slower-than-expected adoption rates and a negative impact on project goals.
The key lesson learned was the importance of comprehensive user engagement from the initial stages of project planning. Now, I ensure that user acceptance testing (UAT) is more extensive and incorporates feedback mechanisms at multiple stages of development. We also prioritize communication and training programs to address user concerns and ensure smooth transition. This experience reinforced the need to consider the human factor and incorporate user perspectives into risk assessments – a critical element often overlooked.
Q 22. What are the ethical considerations in risk management?
Ethical considerations in risk management are paramount. It’s not just about mitigating losses; it’s about ensuring fairness, transparency, and accountability in how we identify, assess, and respond to risks. This includes:
- Transparency and Disclosure: Openly communicating risks and the rationale behind risk management decisions to stakeholders. Hiding risks or downplaying their severity is unethical and can have disastrous consequences.
- Fairness and Equity: Ensuring that risk management strategies don’t disproportionately impact certain groups or individuals. For example, a security system that inadvertently disadvantages people with disabilities would be ethically problematic.
- Confidentiality and Privacy: Protecting sensitive information related to risks and risk management activities. This is especially crucial when dealing with personal data or trade secrets.
- Due Diligence: Thoroughly investigating and assessing risks before making decisions. Negligence in this area can be both ethically and legally problematic.
- Conflicts of Interest: Avoiding situations where personal interests could compromise objective risk assessment and management. For example, an employee benefiting financially from a particular vendor could bias their risk assessment of that vendor’s product.
For example, imagine a pharmaceutical company discovering a potential side effect of a drug. Ethically, they must immediately report it, even if it impacts profits. Failing to do so could have devastating consequences and be a clear breach of ethical responsibility.
Q 23. How do you balance risk and opportunity?
Balancing risk and opportunity is a core principle of effective risk management. It’s about making informed decisions that maximize potential gains while minimizing potential losses. This isn’t about avoiding all risk – that’s impossible and often counterproductive. Instead, it’s about understanding the risk appetite (the level of risk an organization is willing to accept) and making strategic choices.
This often involves a cost-benefit analysis. We weigh the potential rewards of a particular opportunity against the potential costs (financial, reputational, etc.) of the associated risks. Techniques like decision trees and risk matrices can help visualize and analyze these trade-offs.
For instance, a startup might take on higher risks – launching a novel product with limited market research – because the potential rewards (significant market share) outweigh the potential costs (product failure). In contrast, a well-established company might favor lower-risk ventures, focusing on incremental innovation to maintain stability.
Q 24. How do you manage information security risks?
Managing information security risks requires a multi-layered approach. It starts with a thorough risk assessment, identifying vulnerabilities and potential threats to your data and systems. This involves considering:
- Threats: What are the potential sources of harm? (e.g., malicious hackers, malware, insider threats, natural disasters)
- Vulnerabilities: What weaknesses in your systems could be exploited? (e.g., outdated software, weak passwords, lack of encryption)
- Impact: What are the potential consequences of a security breach? (e.g., data loss, financial losses, reputational damage)
Based on this assessment, we implement security controls to mitigate risks. These include technical controls (firewalls, intrusion detection systems, encryption), administrative controls (access control policies, security awareness training), and physical controls (secure facilities, access badges).
Regular security audits and penetration testing are crucial to validate the effectiveness of these controls and identify any remaining vulnerabilities. Incident response planning is also essential – having a clear plan in place for handling security breaches minimizes damage and ensures a swift recovery.
For example, a bank uses multi-factor authentication, encryption of customer data, and regular security audits to mitigate the risk of data breaches and financial fraud.
Q 25. What are your experiences with regulatory compliance related to risk management?
My experience with regulatory compliance in risk management is extensive. I’ve worked with organizations across various sectors navigating diverse regulatory landscapes, including:
- GDPR (General Data Protection Regulation): Implementing data protection measures to comply with EU regulations on personal data processing.
- HIPAA (Health Insurance Portability and Accountability Act): Ensuring compliance with US regulations regarding the privacy and security of protected health information.
- SOX (Sarbanes-Oxley Act): Implementing internal controls over financial reporting to meet US requirements for public companies.
- PCI DSS (Payment Card Industry Data Security Standard): Protecting credit card information by adhering to industry standards for payment processing security.
Compliance isn’t merely about checking boxes; it’s about integrating regulatory requirements into the overall risk management framework. This includes developing robust policies, procedures, and controls, conducting regular audits, and documenting all activities. I’ve led teams in developing these compliance programs, training staff, and conducting internal audits to ensure ongoing compliance.
For instance, in one project, I helped a healthcare provider implement robust data encryption and access controls to meet HIPAA compliance requirements, reducing their risk of hefty fines and reputational damage.
Q 26. Explain your understanding of the concept of residual risk.
Residual risk is the risk that remains after implementing risk responses. Even with the best risk management strategies, it’s impossible to eliminate all risks entirely. Some level of risk will always persist. Understanding and accepting this residual risk is a crucial part of the process.
Think of it like this: you’ve installed a security system in your house (a risk response), but there’s still a chance of a break-in (residual risk). The goal isn’t to achieve zero risk, but to reduce it to an acceptable level – a level that the organization is comfortable with, considering its risk appetite and tolerance.
Managing residual risk involves ongoing monitoring, reviewing controls, and adapting strategies as needed. It’s not a static endpoint but a dynamic process of continuous improvement. Regularly reassessing residual risks helps organizations stay ahead of potential problems and adjust their risk management plans accordingly.
Q 27. How do you ensure that risk management is integrated into daily operations?
Integrating risk management into daily operations is vital for its effectiveness. It shouldn’t be a separate, siloed activity but a continuous, embedded process. Here’s how to achieve this:
- Embed risk assessment into decision-making: Every major decision – from project launches to new hires – should involve an assessment of potential risks and how they’ll be addressed.
- Develop clear risk management policies and procedures: These should be easily accessible and understood by all employees.
- Provide regular risk management training: Employees at all levels should understand their roles and responsibilities in risk management.
- Use technology to support risk management: Tools for risk assessment, monitoring, and reporting can streamline the process and enhance efficiency.
- Foster a culture of risk awareness: Encourage employees to identify and report potential risks proactively.
- Regularly review and update risk management plans: The risk landscape is constantly changing, so plans must be adaptable.
For example, a manufacturing company might integrate risk assessments into its daily production meetings, discussing potential hazards and safety protocols before each shift begins. This ensures that safety isn’t an afterthought but a fundamental part of the daily workflow.
Q 28. How do you adapt your risk management approach to different contexts and industries?
Adapting risk management approaches across different contexts and industries requires flexibility and a deep understanding of the specific risks involved. While the core principles remain consistent, the application varies significantly.
For example, the risks faced by a financial institution (e.g., fraud, market volatility) differ substantially from those of a healthcare provider (e.g., patient safety, data breaches) or a manufacturing company (e.g., workplace accidents, supply chain disruptions).
My approach involves:
- Industry-specific knowledge: I stay updated on industry best practices, regulations, and emerging risks.
- Tailored risk assessments: I customize risk assessments to reflect the unique challenges of each industry and organization.
- Contextualized risk responses: I select risk mitigation strategies appropriate for the specific context, considering factors such as budget, resources, and organizational culture.
- Collaboration and communication: I work closely with stakeholders to ensure that risk management strategies align with organizational goals and objectives.
For instance, when working with a tech startup, I might focus on agile risk management approaches, adapting quickly to changing circumstances. In contrast, a highly regulated industry might require more formal and structured risk management processes with extensive documentation.
Key Topics to Learn for Situational Awareness and Risk Management Interview
- Defining Situational Awareness: Understanding the components of SA (perception, comprehension, projection) and its application in diverse contexts.
- Risk Identification & Assessment: Methods for identifying potential risks (SWOT analysis, HAZOP, etc.), assessing their likelihood and impact, and prioritizing mitigation efforts.
- Risk Mitigation Strategies: Developing and implementing effective risk mitigation plans, including preventative measures, contingency planning, and crisis management.
- Communication & Collaboration in Risk Management: The importance of clear, concise communication in conveying risk information and collaborating with teams to address potential threats.
- Decision-Making Under Pressure: Practical application of SA and risk assessment in making timely and informed decisions in high-pressure or ambiguous situations.
- Ethical Considerations in Risk Management: Understanding the ethical implications of decisions and actions related to risk management, including transparency and accountability.
- Practical Application Examples: Analyzing case studies to demonstrate understanding of SA and risk management principles in real-world scenarios (e.g., project management, security, healthcare).
- Continuous Improvement & Learning from Mistakes: The importance of post-incident analysis and incorporating lessons learned to improve future risk management strategies.
Next Steps
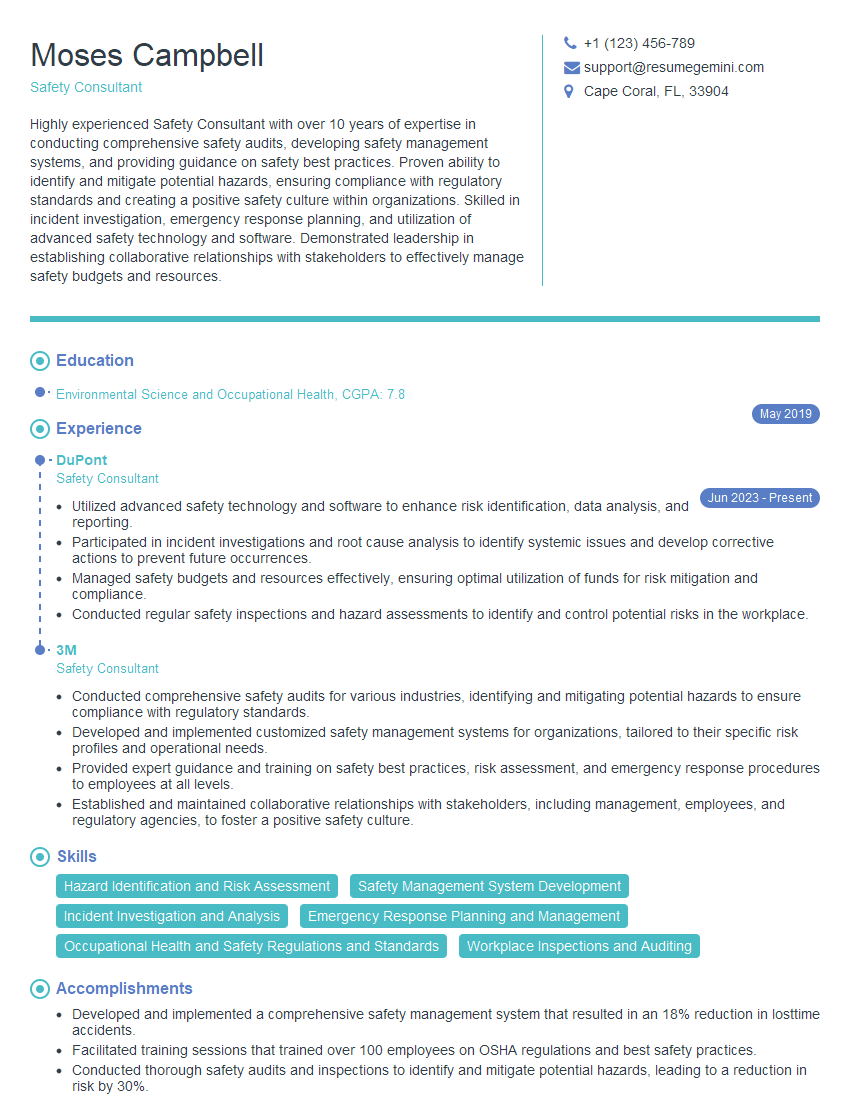
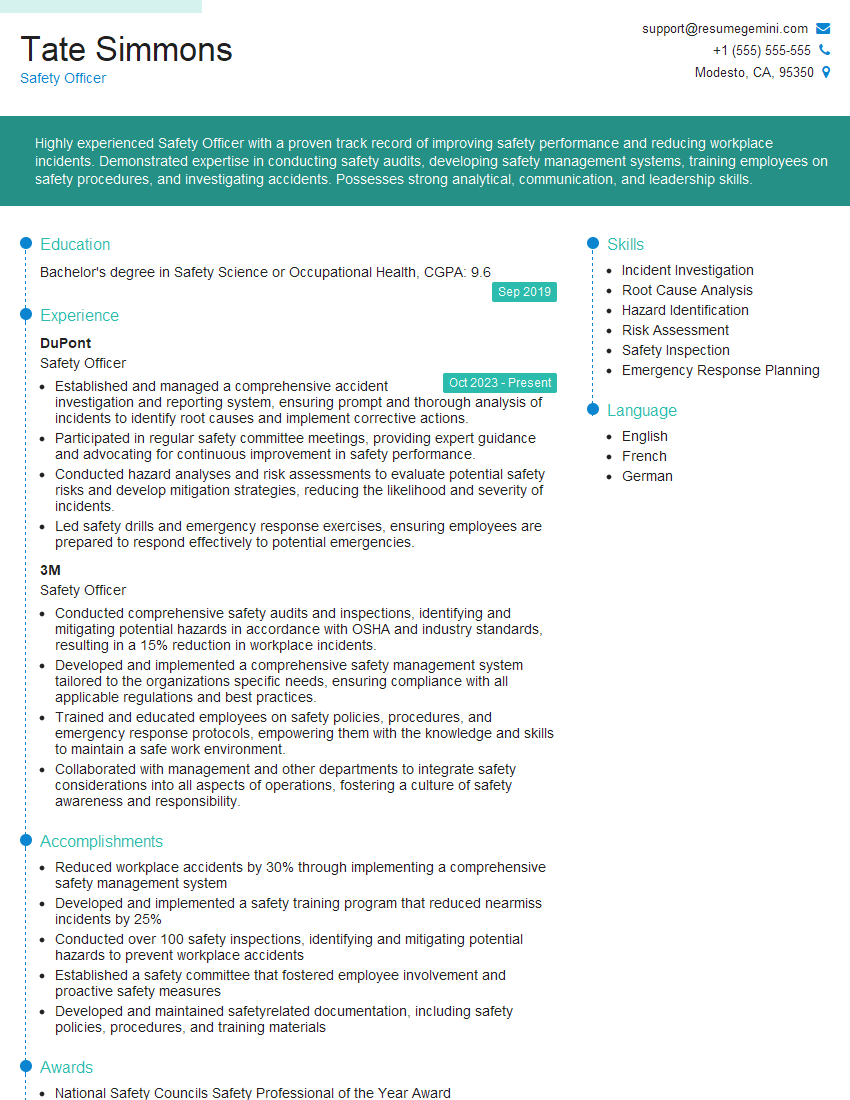
Mastering Situational Awareness and Risk Management is crucial for career advancement in many fields, demonstrating your ability to proactively identify and mitigate challenges, leading to improved decision-making and enhanced performance. To maximize your job prospects, creating a strong, ATS-friendly resume is essential. ResumeGemini can help you build a professional and impactful resume tailored to highlight your skills and experience in Situational Awareness and Risk Management. Examples of resumes specifically designed for this field are available to guide you. Take the next step in your career journey today!
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good