The right preparation can turn an interview into an opportunity to showcase your expertise. This guide to Special Reconnaissance and Surveillance interview questions is your ultimate resource, providing key insights and tips to help you ace your responses and stand out as a top candidate.
Questions Asked in Special Reconnaissance and Surveillance Interview
Q 1. Describe your experience with various surveillance techniques.
My experience encompasses a wide range of surveillance techniques, from traditional methods to cutting-edge technologies. I’m proficient in both overt and covert surveillance, adapting my approach based on the specific operational requirements and the target’s characteristics. This includes:
- Visual Surveillance: This involves direct observation, often employing concealment and blending techniques to remain undetected. I’ve conducted numerous stakeouts, utilizing both static and mobile observation points, meticulously documenting activities and maintaining operational security.
- Audio Surveillance: I’m experienced in deploying and managing various audio recording devices, including covert microphones and ambient recording systems. Data analysis and interpretation are crucial aspects of this, and I’m adept at filtering out noise and isolating relevant audio.
- Technical Surveillance: This involves exploiting vulnerabilities in technology to gather intelligence. I have extensive experience with utilizing software and hardware to intercept and analyze communications, including network traffic analysis and data extraction from mobile devices. This often requires a deep understanding of cryptography and security protocols.
- Electronic Surveillance: This often overlaps with technical surveillance, but places a greater emphasis on electronic signals. My experience includes the use of radio frequency (RF) detectors, to locate and identify hidden devices, as well as analyzing communication signals for intelligence gathering.
For example, during one operation, we used a combination of visual surveillance, utilizing a concealed observation post, alongside technical surveillance to monitor communications traffic near a suspected smuggling operation. The combined data gave us a complete picture of the target’s activities, leading to a successful operation.
Q 2. Explain your understanding of different types of reconnaissance (e.g., visual, technical, electronic).
Reconnaissance is the process of gathering information about a target. Different types of reconnaissance cater to specific information needs.
- Visual Reconnaissance: This is the most basic form, involving direct observation of the target area or object. This can range from simple observation through binoculars to using drones for aerial reconnaissance, providing detailed images and videos.
- Technical Reconnaissance: This focuses on gathering information about a target’s technological infrastructure. This could involve analyzing a target’s communication systems, identifying vulnerabilities in their network security, or identifying the type and capabilities of their equipment.
- Electronic Reconnaissance: This involves intercepting and analyzing electronic signals emitted by a target. This can include radio communications, radar signals, or even analyzing electromagnetic emissions from electronic devices. This often requires specialized equipment and expertise in signal processing.
For instance, during a pre-operation briefing, we might conduct visual reconnaissance using satellite imagery to identify potential access points and obstacles. Then, we would follow up with technical reconnaissance to assess the target’s security systems, before finally utilizing electronic reconnaissance to monitor communication patterns.
Q 3. How proficient are you in utilizing geospatial intelligence tools?
I am highly proficient in utilizing geospatial intelligence (GEOINT) tools. My expertise extends across various software and platforms, including ArcGIS, QGIS, Google Earth Pro, and specialized intelligence analysis applications. I can effectively process, analyze, and interpret data from diverse sources, such as satellite imagery, aerial photography, and geographic databases, to create accurate and informative maps, models, and reports.
I’m comfortable with georeferencing, creating 3D models, and performing spatial analysis to identify patterns and trends. For example, in a recent operation, I used GEOINT tools to analyze high-resolution satellite imagery to identify subtle changes in a target’s infrastructure, providing valuable insight into their operations.
Q 4. What experience do you have with interpreting aerial imagery?
Interpreting aerial imagery is a core skill in my professional background. I can analyze various types of aerial imagery, including satellite imagery, aerial photographs, and drone footage, to extract valuable information. This includes identifying objects, assessing terrain, and determining potential threats or opportunities. My experience encompasses different resolutions and image types, from panchromatic to multispectral.
For example, I’ve utilized aerial imagery to identify potential ambush locations during route planning or to track the movement of vehicles and personnel during an operation. Understanding photogrammetry and image processing techniques is crucial for accurate interpretation, and this is something I have extensive knowledge and practical experience in.
Q 5. Describe your experience with counter-surveillance techniques.
Counter-surveillance is crucial for operational security and involves detecting and mitigating any attempts to surveil our activities. This is an area I have significant experience in. My approach is multifaceted and incorporates:
- Physical Detection: This involves using observation skills and equipment to identify potential surveillance devices like hidden cameras or microphones. We also employ techniques such as sweep techniques to detect bugs in a target environment.
- Electronic Detection: This employs specialized equipment to detect radio frequency signals, electromagnetic emissions, and other electronic indicators of surveillance activity.
- Behavioral Detection: This involves noticing unusual patterns or behavior suggesting someone might be following or observing us. Understanding surveillance techniques allows me to anticipate and counteract those tactics.
During one operation, we used a combination of electronic sweeps and behavioral observations to identify and neutralize a suspected counter-surveillance team, ensuring the success of our primary objective.
Q 6. How familiar are you with different types of surveillance equipment?
My familiarity with surveillance equipment is comprehensive. I have hands-on experience with a broad range of tools, including:
- Cameras and Lenses: From high-powered long-range lenses to covert cameras disguised as everyday objects.
- Audio Recording Devices: Parabolic microphones, covert microphones, and digital audio recorders.
- Electronic Surveillance Equipment: RF detectors, signal analyzers, and GPS tracking devices.
- Data Analysis Software: Specialized software for analyzing audio, video, and other types of surveillance data.
- Drones and UAS: Experience with deploying and operating unmanned aerial systems (UAS) for aerial surveillance.
I understand the capabilities and limitations of each piece of equipment and can choose the most appropriate technology for any given scenario. I also understand the importance of proper maintenance and calibration of this equipment.
Q 7. How would you handle a compromised surveillance operation?
Handling a compromised surveillance operation requires a swift and decisive response. The priority is to minimize damage and prevent further compromise. My approach involves these steps:
- Immediate Assessment: Identify the extent of the compromise – what information was exposed, and how? Determine if the compromise originated from technical failure, human error, or deliberate attack.
- Damage Control: Secure all remaining equipment and data. Implement countermeasures to prevent further data leakage. This may involve changing passwords, disabling systems, or even recalling operatives.
- Investigation: Conduct a thorough investigation to identify the cause of the compromise. This may involve reviewing logs, interviewing personnel, or engaging specialized cybersecurity teams.
- Reporting and Remediation: Prepare a comprehensive report detailing the incident, its impact, and recommendations for preventing future occurrences. Implement corrective actions to address the vulnerabilities identified during the investigation.
- Debriefing: Conduct thorough debriefings with all involved personnel to understand the circumstances surrounding the compromise and to refine procedures to avoid similar occurrences in the future.
A compromised operation can be highly damaging, but a prompt and effective response can minimize the impact and help maintain operational integrity.
Q 8. Explain your understanding of the legal and ethical implications of surveillance.
Surveillance, while crucial for national security and law enforcement, treads a delicate line between necessity and infringement on fundamental rights. Legally, operations must adhere strictly to warrants, probable cause requirements, and the limitations imposed by laws like the Fourth Amendment (in the US) or equivalent legislation in other jurisdictions. Ethical considerations are paramount; we must always balance the potential benefits of intelligence gathering against the potential harms to individual privacy and civil liberties. This includes minimizing intrusion, ensuring proportionality (the level of surveillance must be proportionate to the threat), and maintaining transparency and accountability wherever possible. For instance, the use of facial recognition technology raises serious ethical concerns regarding bias and potential misuse, requiring careful oversight and stringent guidelines.
In practice, this means meticulous planning and execution. We must ensure that all surveillance activities are fully compliant with the law and authorized by the appropriate authorities. This includes obtaining necessary legal authorizations, carefully defining the scope of surveillance, and implementing robust oversight mechanisms to prevent abuse. Regular internal reviews and audits are critical to ensuring ethical conduct and compliance. We must constantly consider the potential consequences of our actions and strive to minimize any negative impact on innocent individuals.
Q 9. How do you ensure the security and integrity of collected intelligence?
Securing and maintaining the integrity of collected intelligence is paramount. It involves a multi-layered approach starting with secure collection methods. This means utilizing encrypted communication channels, employing robust data encryption techniques during transmission and storage, and implementing strict access control measures. We use specialized software and hardware to minimize vulnerabilities and protect sensitive information. Data is often compartmentalized, meaning access is granted only on a need-to-know basis, further limiting potential breaches.
Furthermore, regular security audits and penetration testing identify weaknesses in our systems. We employ rigorous authentication and authorization protocols, including multi-factor authentication, to ensure only authorized personnel can access sensitive information. Any potential compromises are immediately investigated, and appropriate remedial actions are taken. Regular training for personnel on cybersecurity best practices is crucial to maintaining the integrity of our intelligence. We also employ robust data destruction protocols to securely erase information when it’s no longer needed, preventing leaks or unauthorized access. Think of it as a digital fortress, with multiple layers of defense designed to keep the information safe.
Q 10. Describe your experience working within a team environment on surveillance operations.
Teamwork is fundamental in Special Reconnaissance and Surveillance. In my experience, successful operations rely on seamless collaboration, clear communication, and mutual trust. I’ve been part of numerous teams, each with specialized roles (e.g., surveillance technicians, analysts, communications specialists). For instance, during a complex operation involving multiple targets, we relied heavily on constant communication via encrypted channels. Each member had specific tasks and responsibilities, yet we maintained a collaborative approach to address challenges effectively. A clear chain of command and a shared understanding of objectives ensured coordinated efforts, even under pressure. We used regular briefings and debriefings to share information, evaluate progress, and adapt to evolving circumstances. Success required each team member to have not only technical expertise but also strong interpersonal skills and the ability to function effectively under stress.
Q 11. How would you prioritize multiple surveillance targets?
Prioritizing surveillance targets depends on a thorough risk assessment. We use a structured approach, considering factors like the immediacy of the threat, the potential impact of the target’s actions, the feasibility of surveillance, and the availability of resources. A matrix or scoring system can be employed to objectively compare targets. For example, a high-value target with imminent plans for a terrorist attack would obviously take precedence over a target with lower-level, less immediate threats. We might use a threat matrix ranking targets based on likelihood and impact, and then factor in resource constraints (personnel, equipment, time) to determine a feasible order of operations. Continuous monitoring and reassessment are crucial as intelligence develops and circumstances change.
Q 12. What are your skills in report writing and intelligence analysis?
My report writing emphasizes clarity, conciseness, and accuracy. Reports are structured logically, providing a clear summary of findings, followed by detailed supporting evidence and analysis. I employ standard intelligence formats to ensure consistency and facilitate efficient information sharing. My analysis skills involve interpreting raw data, identifying patterns and trends, and drawing actionable conclusions. I utilize various analytical techniques, including trend analysis, link analysis, and geospatial analysis, to make sense of complex datasets. I am proficient in using various software tools for data analysis and report generation, ensuring the reports are easily understandable and readily accessible to decision-makers.
Q 13. How experienced are you with data analysis and visualization related to reconnaissance data?
I am highly proficient in data analysis and visualization related to reconnaissance data. I utilize various software packages (e.g., ArcGIS, QGIS, specialized intelligence analysis platforms) to process, analyze, and visualize geospatial and temporal data. I can create maps, charts, and graphs to illustrate key findings and communicate complex information effectively. For example, I’ve used geospatial analysis to track the movements of targets, identify patterns in their activities, and predict future actions. Data visualization is key to transforming raw data into actionable intelligence that is readily understandable by both technical and non-technical audiences. My skills ensure I can effectively transform complex datasets into concise, meaningful representations that support effective decision-making.
Q 14. Explain your understanding of SIGINT and HUMINT collection methods.
SIGINT (Signals Intelligence) and HUMINT (Human Intelligence) are two critical intelligence collection methods. SIGINT involves intercepting and analyzing electronic communications (radio, satellite, internet traffic) to gather intelligence. This includes various techniques like electronic surveillance, radio frequency analysis, and traffic analysis. It provides valuable insights into communications and activities, potentially revealing planned events or hidden agendas. HUMINT focuses on gathering intelligence from human sources. This could involve cultivating relationships with informants, conducting interviews, or using deception to elicit information. HUMINT often provides crucial context and insight that SIGINT alone cannot offer. Think of SIGINT as listening to the conversation, and HUMINT as understanding the context of that conversation, who is speaking, and what their intentions might be. Both SIGINT and HUMINT are frequently used in conjunction to provide a comprehensive intelligence picture, often complementing each other.
Q 15. Describe your experience with OSINT gathering and analysis.
Open-Source Intelligence (OSINT) gathering and analysis is crucial for Special Reconnaissance. It involves collecting information from publicly available sources to build a comprehensive picture of a target, location, or event. My experience encompasses a wide range of techniques, from passively monitoring social media and news articles to actively searching online databases and forums. I’m proficient in using advanced search operators and tools to refine my searches and filter out irrelevant information. For example, during a recent operation, we needed to establish the daily routines of a high-value target. Through meticulously analyzing their social media activity, publicly available flight records, and news reports about their public appearances, we successfully mapped out their schedule with remarkable accuracy. This allowed our team to plan effective surveillance without unnecessary risk.
- Techniques: Advanced search operators (Google Dorking, Boolean logic), social media monitoring, news aggregation, database searches.
- Tools: Maltego, Google Earth, various social media monitoring tools, and specialized OSINT databases.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. How familiar are you with risk assessment and mitigation in surveillance operations?
Risk assessment and mitigation are paramount in surveillance operations. It’s a continuous process, beginning with the initial planning stages and continuing throughout the mission’s execution. I utilize a structured approach, considering factors like the target’s profile, the operational environment, potential threats (physical, technological, legal), and the available resources. For example, I meticulously assess the risks associated with using specific surveillance technologies, weighing their benefits against the potential for detection or compromise. If a risk is deemed unacceptable, I develop mitigation strategies, such as employing alternative methods or adjusting the operational plan. This might involve changing surveillance locations, adjusting the timing of operations, or deploying counter-surveillance measures. The goal is always to minimize risks while maximizing the mission’s effectiveness.
- Methods: SWOT analysis, threat modeling, risk matrices.
- Mitigation: Alternative surveillance techniques, counter-surveillance measures, operational plan adjustments.
Q 17. How do you maintain operational security during a surveillance operation?
Maintaining operational security (OPSEC) is critical; a compromised operation can have severe consequences. My approach to OPSEC is multi-layered. It starts with meticulous planning, ensuring all communication and movement are carefully considered and planned in advance. I employ techniques like using encrypted communication channels, employing plausible cover stories, and adhering strictly to established communication protocols. During operations, I maintain a low profile, avoid unnecessary attention, and continuously assess potential compromises. For example, during a surveillance operation in a densely populated area, I meticulously avoided drawing attention to myself by blending into the environment and avoiding repetitive patterns in my movements. Regular debriefings and operational reviews are crucial to identify and rectify potential OPSEC weaknesses.
- Techniques: Secure communication, plausible cover stories, counter-surveillance, compartmentalization of information.
- Tools: Encrypted communication devices, secure data storage, and techniques like traffic analysis avoidance.
Q 18. What is your experience with mission planning and execution in a reconnaissance context?
Mission planning and execution in reconnaissance are methodical processes. I begin by clearly defining the mission’s objectives, identifying the necessary intelligence, and assessing potential risks. This involves creating detailed timelines, assigning roles and responsibilities, and selecting appropriate equipment and technologies. The plan always includes contingencies for unexpected challenges. During execution, I continuously monitor the situation, adapting the plan as needed and ensuring effective communication within the team. For example, during a recent mission requiring the assessment of a potential threat, the initial plan was disrupted by unexpected road closures. My team quickly adapted, utilizing alternative routes and communication methods, ensuring the mission objectives were still met within the timeframe.
- Phases: Planning, briefing, execution, debriefing.
- Tools: Mapping software, mission planning software, communication systems.
Q 19. Describe your experience with using various communication systems during surveillance.
Proficiency in various communication systems is essential for effective surveillance. My experience includes secure voice communication (encrypted radios, satellite phones), data transmission (secure messaging apps, encrypted email), and real-time video streaming. Choosing the appropriate communication system depends on the operational context, considering factors like range, security, and bandwidth requirements. For example, in a high-risk environment, I would opt for encrypted satellite communication to ensure secure and reliable transmission, even in areas with limited cell service. I always have backup communication methods to ensure redundancy and maintain communication during emergencies.
- Systems: Encrypted radios, satellite phones, secure messaging apps, encrypted email, video streaming systems.
- Security: Encryption protocols, authentication methods, communication security protocols.
Q 20. How do you handle unexpected challenges or complications during a surveillance mission?
Handling unexpected challenges is an integral part of surveillance. My approach is based on adaptability and resourcefulness. When faced with unexpected complications, I first assess the situation calmly, identifying the nature and severity of the problem. Then, I develop and implement a solution using available resources and adjusting the operational plan as needed. For example, during a surveillance operation, the target unexpectedly changed their route. I immediately assessed the situation and, through swift communication with my team and by utilizing real-time traffic data, successfully adapted our position and continued observation without losing sight of the target.
- Strategies: Adaptability, problem-solving, quick thinking, teamwork.
- Contingency planning: Pre-planning alternative routes, communication methods, and observation points.
Q 21. What is your experience with different types of surveillance platforms (e.g., UAVs, ground vehicles)?
My experience encompasses diverse surveillance platforms, including Unmanned Aerial Vehicles (UAVs) or drones, ground vehicles (both covert and overt), and stationary observation points. UAVs offer advantages in terms of aerial perspective and maneuverability, but their use requires meticulous planning and consideration of airspace regulations. Ground vehicles provide flexibility and discretion, allowing for close-range observation while maintaining a low profile. Choosing the right platform depends on the specific mission requirements and the operational environment. For example, in a densely populated urban area, a covert ground vehicle would be ideal, while for a large open area, a UAV would offer significant advantages.
- UAVs: Operation, maintenance, image processing, data analysis.
- Ground Vehicles: Covert driving techniques, surveillance equipment integration, driver training.
- Stationary Observation: Camouflage, concealment, observation techniques.
Q 22. Describe your experience with target identification and tracking.
Target identification and tracking are fundamental to special reconnaissance. It involves systematically identifying, locating, and monitoring a specific individual, group, or asset of interest. This process starts with intelligence gathering to establish a target’s characteristics – physical description, vehicles used, known associates, routines, etc. Then, using a combination of techniques like visual observation (often enhanced by optics), electronic surveillance (e.g., tracking devices, cell phone triangulation), and open-source intelligence (OSINT), we build a comprehensive profile.
Tracking involves maintaining constant awareness of the target’s movements and activities. This can range from stationary observation to mobile surveillance, often requiring meticulous planning and coordination, sometimes utilizing multiple teams and assets. Effective tracking relies on anticipating the target’s behaviour and adapting the surveillance strategy accordingly. For example, if a target unexpectedly changes their transportation, we must quickly re-assess the situation and adjust our approach to maintain visual or electronic contact.
One case involved tracking a high-value target suspected of involvement in arms trafficking. We initially used long-range visual surveillance, but due to the target’s frequent changes in location and use of heavily trafficked areas, we transitioned to employing a combination of discreet mobile surveillance and electronic tracking devices. This multi-faceted approach allowed us to maintain continuous observation while minimizing the risk of detection.
Q 23. How would you assess the reliability and validity of collected intelligence?
Assessing the reliability and validity of intelligence is crucial. It’s a multi-step process that involves evaluating the source, method, and content of the intelligence. We utilize a framework that considers the source’s credibility – their past accuracy, motivations, and potential biases. We also examine the method of collection – was it direct observation, intercepted communication, or open-source information? Each method has inherent strengths and weaknesses that must be considered.
For example, information from a known unreliable source requires corroboration with other, more credible sources. If the information conflicts with known facts or established intelligence, further investigation is necessary. Data triangulation – comparing and contrasting information from multiple independent sources – is essential for building confidence in the intelligence. We also examine the context of the information, considering factors like timeliness and relevance to the current operational picture.
Furthermore, rigorous analysis of the information’s consistency and logical coherence is critical. In essence, we are constructing a puzzle, carefully examining each piece for its fit and consistency within the overall picture. The final assessment reflects the overall confidence level in the collected intelligence – ranging from high confidence, based on multiple verified sources, to low confidence, where information lacks corroboration or is from a dubious source.
Q 24. What is your understanding of the intelligence cycle?
The intelligence cycle is a continuous process involving planning and direction, collection, processing, analysis and production, dissemination, and evaluation. It’s a cyclical process, constantly refining the intelligence picture.
- Planning and Direction: Identifying intelligence needs and defining the objectives of the intelligence effort.
- Collection: Gathering raw intelligence data using various methods (human intelligence, signals intelligence, imagery intelligence, open-source intelligence).
- Processing: Transforming raw data into a usable format (e.g., translating, transcribing, geo-referencing).
- Analysis and Production: Interpreting processed intelligence to produce an assessment of the situation.
- Dissemination: Sharing the intelligence with relevant decision-makers.
- Evaluation: Assessing the accuracy and effectiveness of the intelligence.
Think of it as a feedback loop; the evaluation phase informs the next planning cycle, ensuring the intelligence remains relevant and accurate. Each stage is interdependent, and a weakness in one area can compromise the entire process. Effective management of the intelligence cycle requires careful coordination and communication among all involved parties.
Q 25. Explain your experience with data encryption and secure communication protocols.
Secure communication and data encryption are paramount in special reconnaissance. We use a variety of encryption methods, from simple symmetric encryption (like AES) for secure communication over shorter distances, to more complex public-key cryptography (like RSA) for secure exchange of sensitive information. The choice depends on the security requirements and the level of risk involved. We also employ secure communication protocols like HTTPS and VPNs for secure data transfer and communication over networks.
For example, when transmitting sensitive imagery, we utilize end-to-end encryption, ensuring only authorized personnel can access the data. Secure communication channels often involve using encrypted satellite links or hardened communication systems. We also adhere strictly to operational security (OPSEC) principles, limiting the amount of data transferred and using secure methods to destroy any sensitive material when no longer required.
The importance of this cannot be overstated. A breach in security can compromise an operation, endanger personnel, and potentially reveal sensitive sources and methods. Therefore, continuous training and updating our knowledge of the latest encryption and communication technologies are crucial.
Q 26. How do you stay current with advancements in surveillance technology?
Staying current with advancements in surveillance technology is an ongoing process. I regularly attend industry conferences, read specialized journals and publications, and network with colleagues and experts in the field. I also actively participate in training courses offered by manufacturers and government agencies. This includes both theoretical knowledge and hands-on experience with the newest technologies.
Furthermore, I keep abreast of developments through open-source intelligence gathering, scrutinizing the latest research papers and industry news reports on emerging surveillance technologies. Understanding the capabilities and limitations of these technologies allows me to assess their potential applications and to anticipate future trends in surveillance capabilities. This ensures that our operations remain at the cutting edge of technology and effectiveness.
Q 27. How do you manage stress and maintain focus during long or demanding surveillance operations?
Long and demanding surveillance operations can be incredibly stressful. Maintaining focus requires a combination of physical and mental preparation. This includes rigorous physical fitness training to enhance stamina and endurance, and mental discipline to manage stress and fatigue.
I also employ various stress management techniques, including mindfulness and meditation practices. Teamwork and communication are crucial; open communication within the team helps alleviate stress and maintains morale. Regular breaks, proper hydration, and healthy nutrition are vital for sustaining physical and mental performance during prolonged operations. A key factor is adherence to a well-defined operational plan, that minimises risk and enhances predictability, reducing uncertainty and potential stressors.
Q 28. Describe a situation where you had to adapt your surveillance strategy due to unforeseen circumstances.
During a surveillance operation targeting a suspected money-laundering ring, the primary target unexpectedly changed his transportation method from a private car to a crowded public bus. Our initial surveillance strategy, which relied on discreet vehicle tracking, became ineffective. To maintain surveillance, we immediately adapted our strategy.
We utilized a combination of operatives blending into the crowd on the bus (while maintaining visual contact) and additional observers monitoring the bus’s route from strategic locations. This involved quick coordination and re-assignment of personnel, and the utilization of portable surveillance equipment that permitted discreet monitoring in public areas. This adaptive approach allowed us to maintain surveillance without compromising operational security or alerting the target, ultimately leading to the successful collection of key intelligence.
Key Topics to Learn for Special Reconnaissance and Surveillance Interview
- Intelligence Gathering Techniques: Understanding various methods for collecting information, including human intelligence (HUMINT), signals intelligence (SIGINT), and open-source intelligence (OSINT). Consider the ethical and legal implications of each.
- Surveillance Planning and Execution: Developing comprehensive surveillance plans, encompassing target identification, resource allocation, risk assessment, and contingency planning. Practical application includes understanding different surveillance methods and their limitations (e.g., static vs. mobile surveillance).
- Data Analysis and Interpretation: Processing and analyzing collected intelligence to identify patterns, trends, and actionable insights. This involves critical thinking skills and the ability to synthesize information from multiple sources.
- Technical Surveillance Countermeasures (TSCM): Understanding techniques used to detect and defeat surveillance technologies. This includes familiarity with various electronic surveillance devices and countermeasures.
- Risk Management and Security Protocols: Developing and implementing security protocols to mitigate risks associated with reconnaissance and surveillance operations. This includes personal safety, operational security (OPSEC), and communication security (COMSEC).
- Report Writing and Briefing: Clearly and concisely communicating intelligence findings through concise reports and effective briefings. Consider the audience and the importance of concise, accurate information.
- Legal and Ethical Considerations: Understanding the legal framework governing intelligence gathering and surveillance activities. Maintaining ethical standards throughout the entire process is crucial.
- Teamwork and Collaboration: Special Reconnaissance and Surveillance often involves working in teams. Demonstrate understanding of effective teamwork and communication within a team environment.
Next Steps
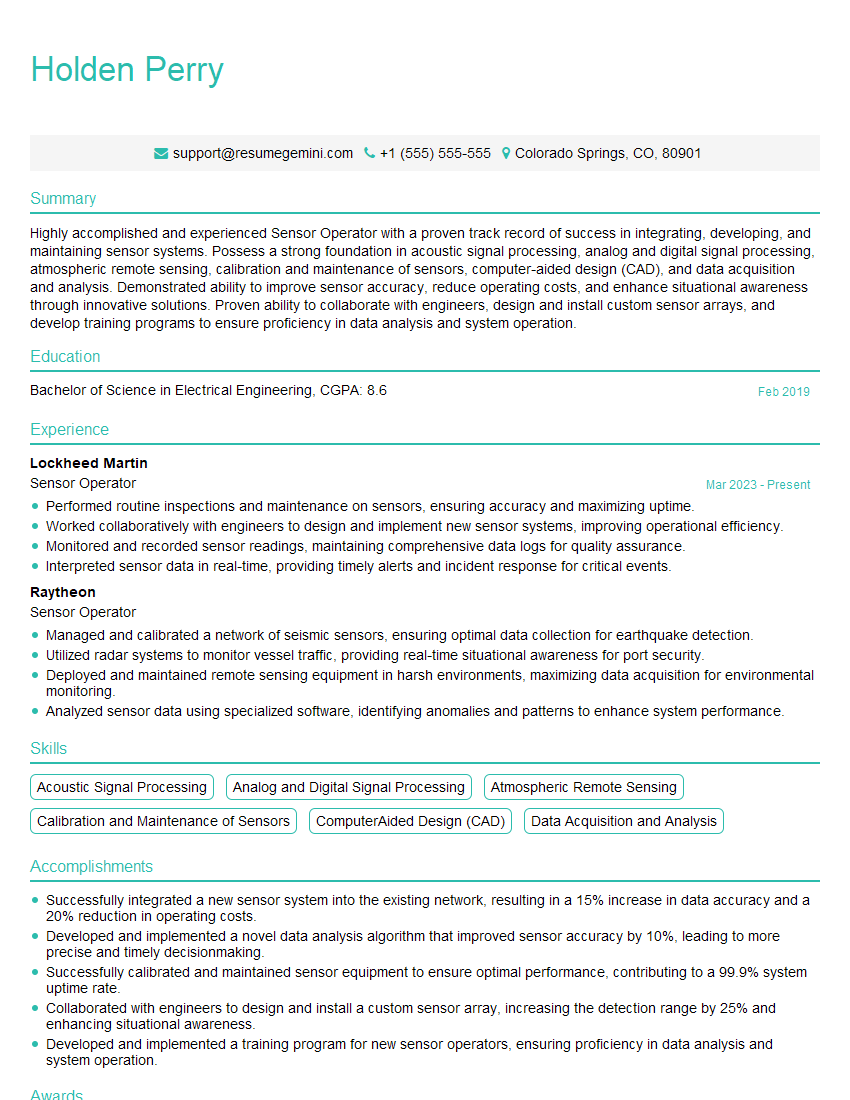
Mastering Special Reconnaissance and Surveillance opens doors to a rewarding and impactful career, offering opportunities for professional growth and contributing to national security. To significantly enhance your job prospects, crafting an ATS-friendly resume is essential. A well-structured resume highlights your key skills and experience effectively, increasing your chances of securing an interview. ResumeGemini is a trusted resource to help you build a professional and impactful resume. We provide examples of resumes tailored to Special Reconnaissance and Surveillance to guide you through the process. Take advantage of these resources and present your qualifications in the best possible light.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good