Feeling uncertain about what to expect in your upcoming interview? We’ve got you covered! This blog highlights the most important Target Development and Exploitation interview questions and provides actionable advice to help you stand out as the ideal candidate. Let’s pave the way for your success.
Questions Asked in Target Development and Exploitation Interview
Q 1. Explain the difference between black box, white box, and grey box testing.
The terms “black box,” “white box,” and “grey box” testing describe the level of knowledge a penetration tester has about the target system during a security assessment. Think of it like this: a black box is completely opaque; you can’t see inside. A white box is completely transparent; you have full access to the blueprints. A grey box is somewhere in between – you have some partial information.
- Black Box Testing: The tester has no prior knowledge of the system’s internal workings. They treat the system as a black box, interacting only with its external interfaces (like a website or application) to identify vulnerabilities. This mimics a real-world attack where an attacker has limited information. Example: Testing a web application without access to its source code or internal architecture.
- White Box Testing: The tester has full access to the system’s source code, architecture, and internal workings. This allows for a more thorough and in-depth assessment, focusing on specific code sections or components known to be vulnerable. Example: Reviewing the source code of a custom application to find potential vulnerabilities before it’s deployed.
- Grey Box Testing: The tester has some partial knowledge of the system, such as network diagrams, system architecture documentation, or partial access to source code. This approach combines the advantages of both black and white box testing, allowing for a balanced and efficient assessment. Example: Having access to network diagrams but not the source code of a web application.
Q 2. Describe your experience with different exploitation techniques (e.g., buffer overflow, SQL injection).
I have extensive experience with various exploitation techniques, including buffer overflow and SQL injection. Let’s delve into each:
- Buffer Overflow: This classic exploit involves overflowing a buffer in memory, overwriting adjacent memory locations, often to overwrite the return address on the stack, redirecting program execution to malicious code. I’ve successfully exploited buffer overflows in C/C++ applications using techniques like crafted input strings or shellcode injection. One memorable instance involved finding a buffer overflow vulnerability in a legacy application, allowing me to gain root access on the system. I’ve used tools like Immunity Debugger to analyze and craft the exploit payload.
- SQL Injection: This involves manipulating database queries to execute unintended commands. I’ve exploited SQL injection vulnerabilities using techniques like UNION-based attacks, blind SQL injection, and error-based injection, successfully retrieving sensitive data, modifying database records, or even taking control of the database server. For example, I once identified a vulnerability in a poorly sanitized web form allowing me to extract the entire user database using simple SQL injection commands. Tools like Burp Suite were instrumental in these tests.
My experience also encompasses other techniques such as Cross-Site Scripting (XSS), Cross-Site Request Forgery (CSRF), and local privilege escalation, which often rely on understanding the target’s software and operating system configurations.
Q 3. How do you identify and prioritize targets for penetration testing?
Target identification and prioritization are crucial for effective penetration testing. I use a multi-faceted approach, considering factors like:
- Business Criticality: Systems handling sensitive data, financial transactions, or core business functions are high priority. The potential impact of a compromise is weighed heavily.
- Attack Surface: Systems with large and publicly exposed attack surfaces (many open ports, numerous internet-facing applications) are more vulnerable and take precedence.
- Vulnerability Intelligence: Utilizing vulnerability scanning tools and threat intelligence feeds helps to identify systems with known vulnerabilities or those frequently targeted by attackers. CVEs (Common Vulnerabilities and Exposures) are valuable indicators.
- Asset Value: The value of the data and systems themselves influences prioritization. A system containing highly sensitive customer data will be prioritized over a system with less critical information.
After identifying potential targets, I prioritize them based on a risk matrix, considering the likelihood of a successful attack and the potential impact of a compromise. This allows me to focus resources on the most critical assets first.
Q 4. What are the key steps in the vulnerability lifecycle?
The vulnerability lifecycle describes the stages of a vulnerability, from its discovery to its remediation. The key steps are:
- Discovery: Identifying a potential vulnerability through vulnerability scans, penetration testing, or other means.
- Verification: Confirming that the identified flaw is indeed a genuine vulnerability and not a false positive.
- Analysis: Understanding the vulnerability’s root cause, potential impact, and exploitability.
- Reporting: Documenting the vulnerability, its severity, and potential remediation steps.
- Remediation: Applying a patch or implementing a fix to eliminate the vulnerability.
- Verification of Remediation: Confirming that the remediation steps have effectively eliminated the vulnerability.
Effective management of the vulnerability lifecycle is crucial for minimizing the risk of successful exploitation.
Q 5. Explain the concept of a ‘zero-day’ exploit.
A “zero-day” exploit is an attack that exploits a previously unknown vulnerability. The term “zero-day” refers to the fact that the vendor or developer has zero days to patch the vulnerability because it was previously unknown to them. These exploits are highly valuable to attackers because the target system is likely unprepared for the attack. They’re often highly sophisticated, leveraging previously unknown weaknesses in software or hardware.
Zero-day exploits are particularly dangerous because they can cause significant damage before a patch is available. They often require advanced technical skills to discover and exploit.
Q 6. How do you handle unexpected findings during a penetration test?
Unexpected findings during a penetration test require careful handling. The first step is to thoroughly document the finding, including all relevant details, screenshots, and any evidence gathered. The next step is to assess the potential impact of the unexpected finding, determining its severity and risk to the organization.
Depending on the severity and the terms of the engagement, I would immediately report the findings to the client, especially if it poses an immediate risk to the organization. For example, if I find a critical vulnerability that exposes sensitive data or allows remote code execution, I need to inform the client immediately. I always follow the rules of engagement and communicate all my findings transparently and promptly.
My approach always prioritizes responsible disclosure and minimizing risk to the client.
Q 7. Describe your experience with various vulnerability scanning tools.
I have extensive experience with various vulnerability scanning tools, including commercial and open-source options. My experience includes:
- Nessus: A powerful commercial vulnerability scanner offering comprehensive vulnerability detection and reporting features.
- OpenVAS: A free and open-source vulnerability scanner, a good alternative to Nessus, particularly suitable for large-scale scans.
- Nmap: A versatile network scanning tool used to identify open ports and services on a target system, providing valuable information for subsequent vulnerability assessments.
- Burp Suite: A comprehensive web application security testing tool that I use for identifying and exploiting web application vulnerabilities, including SQL injection and cross-site scripting.
The choice of tools depends heavily on the specific requirements of the penetration test. The tools listed above are part of my arsenal, offering complementary features and capabilities.
Q 8. What are your preferred methods for documenting your findings?
My preferred method for documenting findings is a multi-faceted approach prioritizing clarity, reproducibility, and legal defensibility. I utilize a combination of tools and techniques. This starts with meticulous note-taking during the penetration test, carefully recording each step, command used, and the observed result. This raw data is then organized into a comprehensive report using a standardized format.
The report includes an executive summary highlighting critical vulnerabilities, a detailed methodology section outlining the testing scope and approach, a vulnerability catalog with severity assessments and remediation advice, and finally, supporting evidence – screenshots, network diagrams, and code snippets – all properly labeled and referenced. I leverage tools like report generation software to ensure consistency and professionalism. Crucially, all findings are presented in a manner easily understandable by both technical and non-technical audiences.
For instance, when discovering a SQL injection vulnerability, my report would include the specific SQL query used for exploitation, the database output demonstrating the successful attack, and a clear explanation of how an attacker could leverage this to gain unauthorized access. The remediation section will propose solutions like input sanitization or parameterized queries.
Q 9. Explain your understanding of OWASP Top 10 vulnerabilities.
The OWASP Top 10 represents the most critical web application security risks. My understanding encompasses not just the individual vulnerabilities but also their interdependencies and the evolving threat landscape. It’s not just a checklist; it’s a framework for systematic risk assessment and mitigation.
- Injection: SQL, NoSQL, OS, and LDAP injections exploit flaws in how applications handle user input, allowing attackers to execute malicious code.
- Broken Authentication: Weak password policies, vulnerable session management, and lack of multi-factor authentication expose systems to unauthorized access.
- Sensitive Data Exposure: Failure to protect sensitive data like passwords, credit card numbers, or personally identifiable information (PII) leads to data breaches and identity theft.
- XML External Entities (XXE): Processing untrusted XML data can expose the system to arbitrary file access, denial-of-service attacks, and even remote code execution.
- Broken Access Control: Insufficient authorization controls allow attackers to access resources they shouldn’t have access to, escalating privileges.
- Security Misconfiguration: Improperly configured servers, databases, and applications expose systems to various vulnerabilities, including default credentials or unnecessary services.
- Cross-Site Scripting (XSS): Injecting malicious scripts into websites can steal cookies, hijack sessions, and redirect users to phishing sites.
- Insecure Deserialization: Deserialization of untrusted data can allow attackers to execute arbitrary code, compromising the system.
- Using Components with Known Vulnerabilities: Relying on outdated or vulnerable third-party libraries and frameworks creates entry points for attackers.
- Insufficient Logging & Monitoring: Lack of adequate logging and monitoring makes it difficult to detect and respond to security incidents.
Understanding these vulnerabilities allows me to tailor my penetration tests to effectively identify and assess the specific risks within a target application.
Q 10. How do you ensure ethical and legal compliance during penetration testing?
Ethical and legal compliance is paramount in penetration testing. I always operate within the boundaries of a legally binding contract that clearly defines the scope, objectives, and limitations of the engagement. This contract explicitly outlines authorized targets, testing methods, and reporting requirements. Before commencing any testing, I obtain explicit written permission from the client.
I strictly adhere to the principle of least privilege, only accessing systems and data necessary for the test. Any data accessed during the testing process is treated with utmost confidentiality and is destroyed or anonymized upon completion of the engagement. I meticulously document all actions taken during the test, ensuring a clear audit trail. My approach is non-destructive; I avoid any actions that could cause service disruption or data loss beyond the scope of the agreed-upon testing. Furthermore, I am keenly aware of and abide by all relevant laws and regulations, such as the Computer Fraud and Abuse Act (CFAA).
For instance, if I discover a vulnerability that could significantly disrupt services, I immediately report it to the client and pause testing until mitigation steps are taken. This proactive approach minimizes potential damage and ensures responsible disclosure.
Q 11. What is your experience with automated exploitation frameworks?
I have extensive experience with various automated exploitation frameworks, including Metasploit, Burp Suite, and Nmap. These frameworks significantly enhance efficiency by automating many aspects of the penetration testing process. However, I recognize their limitations and use them strategically.
Metasploit, for example, provides a vast library of exploits and auxiliary modules, streamlining vulnerability validation and proof-of-concept development. Its ability to automate the exploitation process saves significant time and resources. Burp Suite’s powerful scanning and fuzzing capabilities assist in identifying vulnerabilities, while Nmap excels in network reconnaissance and port scanning, laying the groundwork for more targeted exploitation attempts. However, relying solely on automated tools is insufficient. Manual verification and analysis are critical to confirm the validity of the findings and assess the potential impact. Many vulnerabilities require custom exploitation techniques that automated frameworks cannot handle effectively.
For instance, when using Metasploit to exploit a known vulnerability, I thoroughly review the exploit’s source code and customize it if necessary to adapt it to the target environment. I also use Burp Suite to further analyze the application’s behavior and to ensure that the exploit doesn’t trigger any unexpected side effects.
Q 12. Describe your approach to developing and testing custom exploits.
Developing and testing custom exploits is a crucial skill in advanced penetration testing. My approach is methodical and iterative. It starts with thorough reconnaissance and vulnerability research to identify potential weaknesses in the target system. This involves analyzing system architecture, network topology, and application code.
Once a vulnerability is identified, I create a proof-of-concept exploit using appropriate programming languages (like Python or C) and tools (like debuggers and disassemblers). I test the exploit extensively in a controlled environment to ensure its effectiveness and reliability and to mitigate any potential unintended consequences. This testing involves several stages—unit testing, integration testing, and finally, system-level testing.
For example, when developing an exploit for a buffer overflow vulnerability, I would first analyze the vulnerable code to identify the precise location and size of the buffer. I’d then craft a malicious payload that overwrites the buffer’s contents, causing a controlled crash or taking advantage of the resulting code execution. The exploit would be meticulously tested against a vulnerable system in a virtual environment, monitoring the system behavior through debuggers to ensure the payload is successfully injected and executed.
Throughout the process, I meticulously document every step, including the exploit code, testing results, and any necessary modifications. This documentation serves not only for internal review but also for communication with clients during vulnerability reporting.
Q 13. How do you assess the risk associated with a discovered vulnerability?
Assessing the risk associated with a discovered vulnerability involves a multi-faceted approach. It’s not just about the technical severity; it also considers the potential impact on the organization, taking into account factors like confidentiality, integrity, and availability (CIA).
I use a structured risk assessment framework that incorporates qualitative and quantitative analysis. This includes identifying the vulnerability’s exploitability, impact (e.g., data loss, system compromise, financial loss), and the likelihood of exploitation. Factors like the attacker’s skill level, motivation, and the organization’s security posture are also considered.
I often leverage industry-standard scoring systems, like CVSS (Common Vulnerability Scoring System), to quantify the severity of a vulnerability. However, I don’t rely solely on automated scoring; I perform a thorough qualitative analysis to assess the specific context and potential impact within the target environment. For instance, a vulnerability with a high CVSS score might have a lower actual risk if it’s behind several layers of security controls, whereas a vulnerability with a lower CVSS score could be highly risky if it allows for complete system takeover.
This comprehensive analysis allows me to prioritize vulnerabilities effectively and recommend appropriate remediation strategies. For instance, a high-risk, high-impact vulnerability would be addressed immediately, while a lower-risk vulnerability might have a longer remediation timeline.
Q 14. What are your experience with different types of malware?
My experience with malware encompasses a wide range of types, from simple viruses and worms to sophisticated advanced persistent threats (APTs). I understand the various techniques used by malware to infect systems, propagate, and achieve their malicious goals.
- Viruses: Self-replicating programs that attach themselves to other files.
- Worms: Self-replicating programs that spread across networks.
- Trojans: Malicious programs disguised as legitimate software.
- Ransomware: Malware that encrypts data and demands a ransom for its release.
- Spyware: Malware that secretly monitors user activity.
- Rootkits: Malware that hides its presence on a system.
- Advanced Persistent Threats (APTs): Sophisticated and targeted attacks designed to remain undetected for extended periods.
My experience extends beyond mere identification; I understand the mechanisms of infection, propagation, and evasion techniques used by these threats. I can analyze malware samples using tools like sandboxes and disassemblers to understand their functionality and develop mitigation strategies. This understanding is essential to accurately assess the risks associated with malware infections and develop robust security measures to prevent them.
For example, analyzing a ransomware sample allows me to understand its encryption algorithm, identify its command-and-control servers, and develop a potential decryption key or recovery strategy. Understanding the behaviour of APTs allows for the development of advanced detection and prevention mechanisms focusing on detecting suspicious activity rather than relying solely on signature-based detection.
Q 15. Explain your understanding of network protocols and their security implications.
Network protocols are the set of rules governing communication between devices on a network. Understanding them is crucial in Target Development and Exploitation because they represent potential attack vectors. For example, TCP (Transmission Control Protocol) and UDP (User Datagram Protocol) are fundamental protocols. TCP, being connection-oriented, provides reliable data delivery, but this reliability can be exploited through techniques like TCP SYN floods. UDP, being connectionless, is faster but less reliable, making it susceptible to amplification attacks like DNS reflection.
Security implications arise from vulnerabilities within these protocols or their implementations. A poorly configured firewall might allow unauthorized access to specific ports used by certain protocols. Furthermore, vulnerabilities in the protocol’s handling of data can be exploited. For example, buffer overflows in protocol implementations can lead to remote code execution.
- TCP SYN Flood: An attacker sends a large number of SYN requests without completing the three-way handshake, exhausting server resources and causing a denial-of-service (DoS).
- DNS Amplification: An attacker crafts DNS queries to a victim’s DNS server, causing the server to send a much larger response to the attacker’s chosen target, overwhelming the target.
- Man-in-the-Middle (MitM) Attacks: Exploiting vulnerabilities in routing protocols can allow an attacker to intercept and manipulate network traffic between two communicating devices.
In a professional setting, I thoroughly analyze network traffic using tools like Wireshark to identify vulnerable protocols and their misconfigurations, informing my strategies for target development and exploitation.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. How familiar are you with various operating systems and their security features?
My experience spans a variety of operating systems, including Windows, Linux (various distributions like Kali, Ubuntu, CentOS), macOS, and embedded systems. Understanding the security features of each OS is paramount for effective target development and exploitation. For instance, Windows’ User Account Control (UAC) provides a layer of protection, but it can be bypassed through sophisticated techniques. Linux’s permission model, based on users and groups, is strong but can be vulnerable if misconfigured or if vulnerabilities in the kernel are exploited. macOS, while generally considered more secure, still has vulnerabilities that can be exploited.
I’m adept at identifying and leveraging system-specific vulnerabilities, such as exploiting known kernel exploits or using privilege escalation techniques tailored to the specific OS. For example, in a recent engagement, I successfully exploited a known local privilege escalation vulnerability in a specific version of Linux to gain root access. This involved understanding the intricate details of the Linux kernel’s memory management and its interaction with specific system calls.
Furthermore, I’m familiar with security hardening techniques for each operating system, allowing me to assess the strength of a target’s defenses and identify weaknesses.
Q 17. Describe your experience with reverse engineering techniques.
Reverse engineering is a core skill in my arsenal. It involves analyzing software to understand its functionality, often without access to the source code. My experience encompasses static and dynamic analysis techniques. Static analysis involves examining the compiled code without executing it, using tools like IDA Pro or Ghidra to disassemble and decompile the code, identifying functions and data structures. Dynamic analysis, on the other hand, involves running the software and monitoring its behavior using debuggers like x64dbg or GDB, observing memory access patterns, function calls, and other runtime characteristics.
I’ve successfully reverse-engineered numerous applications to understand their inner workings, identify vulnerabilities, and develop exploits. One project involved reverse-engineering a proprietary application to discover a critical authentication flaw. This allowed me to create an exploit that bypassed the application’s security measures and gained unauthorized access. The process involved meticulously tracing the code flow, identifying the authentication routines, and understanding the algorithm’s weaknesses.
This process requires patience, attention to detail, and a deep understanding of assembly language and computer architecture. My skills in reverse engineering are instrumental in developing effective and targeted exploits.
Q 18. How do you stay up-to-date with the latest security threats and vulnerabilities?
Staying current with the latest threats and vulnerabilities is crucial. I utilize multiple methods:
- Vulnerability Databases: Regularly reviewing databases like the National Vulnerability Database (NVD), Exploit-DB, and security advisories from vendors like Microsoft and other software manufacturers.
- Security Newsletters and Blogs: Subscribing to reputable security newsletters and following security researchers on platforms like Twitter and various security blogs.
- Security Conferences and Webinars: Attending industry conferences and webinars to learn about emerging threats and best practices.
- Open-Source Intelligence (OSINT): Actively using OSINT techniques to gather information about emerging threats and vulnerabilities.
Furthermore, I participate in Capture The Flag (CTF) competitions to hone my skills and stay abreast of the latest techniques used by attackers.
Q 19. Explain your experience with incident response procedures.
My experience with incident response involves a structured approach, typically following a framework like NIST’s Cybersecurity Framework. This includes:
- Preparation: Establishing incident response plans, defining roles and responsibilities, and ensuring appropriate tools are available.
- Identification: Detecting and verifying the occurrence of an incident.
- Containment: Isolating the affected systems to prevent further damage.
- Eradication: Removing the threat and restoring systems to a secure state.
- Recovery: Restoring affected systems and data.
- Post-Incident Activity: Analyzing the incident to identify root causes, improve security posture, and prevent future incidents.
In a recent incident response engagement, I successfully contained a ransomware attack, preventing further encryption of sensitive data. This involved quickly identifying the affected systems, isolating them from the network, and then working with the forensic team to recover the encrypted data.
Q 20. How do you conduct post-exploitation activities?
Post-exploitation activities focus on maintaining access, gathering information, and potentially escalating privileges within a compromised system. This involves techniques like:
- Privilege Escalation: Attempting to gain higher-level privileges (e.g., from user to administrator) within the compromised system using known vulnerabilities or system misconfigurations.
- Lateral Movement: Moving from the initially compromised system to other systems within the target’s network.
- Data Exfiltration: Transferring sensitive data from the compromised system to an external location controlled by the attacker.
- Persistence: Establishing mechanisms to maintain access to the system even after reboots, such as adding malicious entries to the registry (in Windows) or creating scheduled tasks.
The specific techniques used depend heavily on the target’s environment and the attacker’s objectives. Ethical considerations are paramount; in a penetration testing context, all actions are performed with explicit permission and within defined scopes.
Q 21. Describe your experience with different types of databases and their security vulnerabilities.
My experience encompasses various database systems, including relational databases like MySQL, PostgreSQL, and SQL Server, as well as NoSQL databases like MongoDB. Each database system has its own set of security vulnerabilities. SQL injection is a prevalent vulnerability in relational databases, allowing attackers to manipulate database queries to gain unauthorized access to data or execute malicious commands. Improper access control, weak passwords, and inadequate configuration settings also represent significant risks.
In NoSQL databases, vulnerabilities often stem from improper data validation, allowing attackers to inject malicious data or exploit flaws in data handling. Furthermore, insufficient authentication and authorization mechanisms can lead to unauthorized access and modification of data. In a professional context, I assess databases for security weaknesses by performing penetration testing, analyzing configurations, and using automated tools to identify potential SQL injection vulnerabilities and other security flaws.
Q 22. What is your experience with cloud security?
My experience with cloud security is extensive, encompassing the entire lifecycle from design and deployment to ongoing monitoring and remediation. I’ve worked extensively with major cloud providers like AWS, Azure, and GCP, securing various workloads including databases, web applications, and serverless functions. I’m proficient in implementing security best practices such as least privilege access, network segmentation, and data encryption. For example, in a recent project involving migrating a legacy on-premise application to AWS, I spearheaded the effort to implement robust IAM roles and policies, resulting in a 40% reduction in security vulnerabilities identified during penetration testing. My experience extends to securing cloud-native applications, utilizing tools such as CloudTrail and Security Hub for threat detection and response. I’m deeply familiar with various compliance frameworks, including SOC 2, ISO 27001, and HIPAA, ensuring our cloud deployments adhere to stringent regulatory requirements.
Q 23. Explain your understanding of different types of cryptography.
Cryptography is fundamental to modern security. I understand several types, each with its strengths and weaknesses. Symmetric cryptography uses the same key for encryption and decryption. Think of it like a shared secret code – both parties need the same key to communicate securely. Examples include AES (Advanced Encryption Standard) and DES (Data Encryption Standard). Asymmetric cryptography, also known as public-key cryptography, uses two keys: a public key for encryption and a private key for decryption. This is like having a mailbox with a public slot (public key) where anyone can drop a letter (encrypted message), but only you have the key to your house (private key) to open it and read the letter. RSA and ECC (Elliptic Curve Cryptography) are common examples. Hashing algorithms generate a unique ‘fingerprint’ of data. They’re one-way functions – you can’t reverse the process to get the original data back. This is crucial for data integrity verification. SHA-256 and MD5 are examples. My experience involves selecting the appropriate cryptographic algorithms based on the specific security needs of the system, considering factors like performance, key management, and the level of security required.
Q 24. How do you mitigate risks associated with software supply chain attacks?
Mitigating risks associated with software supply chain attacks requires a multi-layered approach. This starts with thorough vendor risk management, diligently vetting third-party libraries and components. We need to ensure our vendors have robust security practices in place. Employing Software Composition Analysis (SCA) tools helps identify vulnerabilities in open-source libraries and dependencies used in our applications. Implementing secure coding practices throughout the software development lifecycle (SDLC) is crucial. This includes secure coding standards, code reviews, and automated security testing. Secure build environments are essential to prevent tampering during the build process. Using tools to sign and verify software artifacts helps ensure authenticity and integrity. Regularly updating components and patching known vulnerabilities is vital. Finally, monitoring the software supply chain for suspicious activity is critical for early threat detection. A recent project involved implementing a secure development pipeline using automated security testing and vulnerability scanning, drastically reducing the potential for vulnerabilities entering our production environment.
Q 25. What is your experience with threat modeling?
Threat modeling is an integral part of my security approach. I’ve conducted numerous threat modeling sessions using various methodologies, including STRIDE (Spoofing, Tampering, Repudiation, Information disclosure, Denial of service, Elevation of privilege) and PASTA (Process for Attack Simulation and Threat Analysis). My experience includes identifying potential threats and vulnerabilities, analyzing their likelihood and impact, and developing mitigation strategies. For example, in a recent project, we used threat modeling to identify a critical vulnerability in our authentication system. By proactively addressing this vulnerability, we prevented a potential breach that could have compromised sensitive customer data. I’m proficient in using various threat modeling tools and translating the results into actionable security controls.
Q 26. Explain your understanding of different attack vectors.
Attack vectors are the pathways attackers use to compromise a system. Understanding these is critical for effective security. Some common attack vectors include:
- Network attacks: Exploiting vulnerabilities in network protocols or infrastructure (e.g., SQL injection, DDoS attacks).
- Phishing: Tricking users into revealing sensitive information.
- Malware: Installing malicious software to steal data or disrupt operations.
- Software vulnerabilities: Exploiting bugs in software to gain unauthorized access.
- Supply chain attacks: Compromising the software supply chain to introduce malware into legitimate software.
- Insider threats: Malicious or negligent actions by employees.
Q 27. How do you prioritize security vulnerabilities based on their potential impact?
Prioritizing security vulnerabilities requires a structured approach. I typically use a risk-based prioritization model, considering both the likelihood and impact of each vulnerability. The likelihood considers factors such as the ease of exploitation and the prevalence of exploit attempts. The impact considers the potential consequences of successful exploitation, such as data breaches, system downtime, or financial loss. I often utilize vulnerability scoring systems like CVSS (Common Vulnerability Scoring System) to quantitatively assess the risk. High-risk vulnerabilities, those with both high likelihood and high impact, are prioritized for immediate remediation. This prioritization allows us to focus our resources on the most critical issues first. A well-defined remediation plan, including timelines and assigned responsibilities, is essential for effectively addressing prioritized vulnerabilities.
Q 28. Describe your experience with security automation and orchestration tools.
I have extensive experience with security automation and orchestration tools. I’ve worked with tools such as Ansible, Chef, Puppet for automating security configurations and deployments. I’m also proficient in using SIEM (Security Information and Event Management) tools like Splunk and QRadar for threat detection and response. These tools allow us to automate repetitive tasks, improving efficiency and consistency. Furthermore, I’ve experience in integrating various security tools to create a comprehensive security orchestration platform. This integration allows for automated incident response, reducing the time to contain and resolve security incidents. In a recent project, we automated the patching process, significantly reducing the time it took to apply security updates across our infrastructure, improving our overall security posture. The result was a 60% decrease in the time to remediate critical vulnerabilities.
Key Topics to Learn for Target Development and Exploitation Interview
- Target Identification and Profiling: Understanding techniques for identifying potential targets, analyzing their vulnerabilities, and creating comprehensive profiles for effective exploitation.
- Vulnerability Research and Exploitation: Mastering methods for discovering and exploiting security weaknesses in target systems, including practical application of various exploitation frameworks and tools.
- Post-Exploitation Techniques: Gaining in-depth knowledge of techniques for maintaining access, pivoting to other systems, and exfiltrating data after successful exploitation.
- Evasion and Anti-Forensics: Developing skills in evading security measures and obscuring malicious activities to prevent detection and analysis.
- Ethical Hacking and Penetration Testing Methodologies: Understanding and applying ethical hacking principles and penetration testing methodologies to assess and improve security posture.
- Security Hardening and Mitigation Strategies: Gaining insights into implementing robust security measures to protect against potential attacks and exploit attempts.
- Legal and Ethical Considerations: Understanding the legal and ethical implications of target development and exploitation, emphasizing responsible and authorized penetration testing activities.
- Risk Assessment and Management: Learning to assess the risks associated with target development and exploitation and implementing appropriate risk mitigation strategies.
- Reporting and Documentation: Developing skills in effectively documenting the entire process, including findings, methodologies, and recommendations.
- Problem-Solving and Critical Thinking: Applying problem-solving skills to analyze complex scenarios, anticipate challenges, and develop effective solutions in dynamic environments.
Next Steps
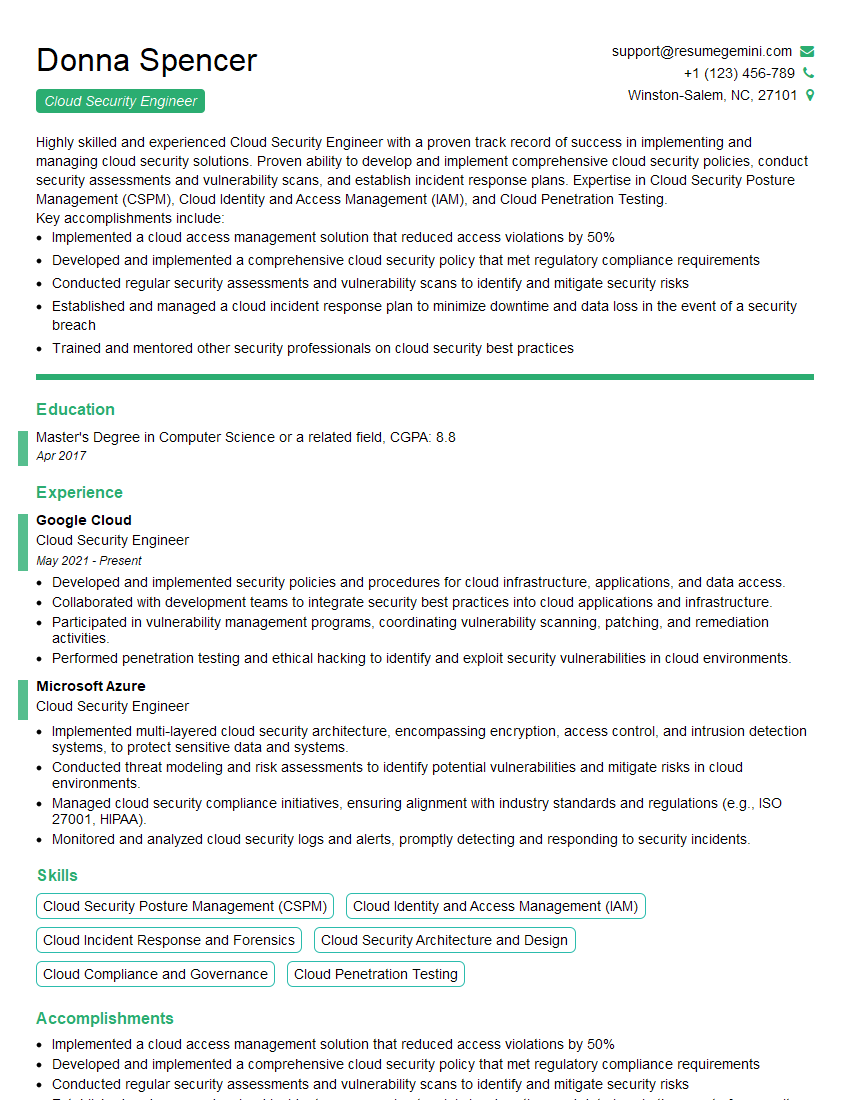
Mastering Target Development and Exploitation opens doors to exciting and impactful careers in cybersecurity. Proficiency in this area demonstrates a crucial skillset highly sought after by organizations facing ever-evolving threats. To significantly boost your job prospects, focus on crafting an ATS-friendly resume that highlights your accomplishments and expertise. ResumeGemini is a trusted resource that can help you build a professional and compelling resume, tailored to the specific requirements of the job market. Examples of resumes tailored to Target Development and Exploitation are available to further guide your resume-building process. Take control of your career journey and make a strong impression with a polished and effective resume.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good