Feeling uncertain about what to expect in your upcoming interview? We’ve got you covered! This blog highlights the most important AllSource Intelligence interview questions and provides actionable advice to help you stand out as the ideal candidate. Let’s pave the way for your success.
Questions Asked in AllSource Intelligence Interview
Q 1. Define All-Source Intelligence and its core components.
All-Source Intelligence (ASI) is the integration and analysis of information gathered from all available sources to create a comprehensive and objective understanding of a situation or issue. It moves beyond relying on a single intelligence discipline and instead leverages the strengths of multiple sources to compensate for their individual weaknesses. The core components include:
- Human Intelligence (HUMINT): Information gathered from human sources, such as informants or spies.
- Signals Intelligence (SIGINT): Information gathered from intercepted communications, such as radio, satellite, or internet traffic.
- Imagery Intelligence (IMINT): Information gathered from visual imagery, such as satellite photos or aerial reconnaissance.
- Measurement and Signature Intelligence (MASINT): Information gathered from measuring physical phenomena, such as electromagnetic emissions or acoustic signals.
- Open-Source Intelligence (OSINT): Information gathered from publicly available sources, such as news reports, social media, and academic papers.
- Geospatial Intelligence (GEOINT): Information derived from imagery, mapping, and geospatial data.
Think of it like building a puzzle: each intelligence discipline provides a piece, and ASI is the process of assembling those pieces to reveal the complete picture.
Q 2. Explain the process of fusing information from diverse intelligence sources.
Fusing information from diverse sources requires a systematic approach. It’s not just about combining data; it’s about critically evaluating, comparing, and integrating it to form a coherent narrative. The process typically involves:
- Data Collection: Gathering information from various sources, ensuring accuracy and reliability.
- Data Validation: Verifying the authenticity and accuracy of the collected data through cross-referencing and corroboration with other sources.
- Data Fusion: Combining data from multiple sources using appropriate techniques, such as data aggregation, correlation, and probabilistic reasoning.
- Analysis: Interpreting the fused data to identify patterns, trends, and insights.
- Dissemination: Sharing the analysis with relevant stakeholders in a clear and concise manner.
For example, if we are investigating a potential terrorist threat, we might combine HUMINT from an informant with SIGINT from intercepted communications and IMINT from satellite imagery. The fusion of these data sources would provide a more complete and reliable picture than relying on any single source alone.
Q 3. Describe your experience with open-source intelligence (OSINT) tools and techniques.
My experience with OSINT tools and techniques is extensive. I’m proficient in using various tools for data collection, analysis, and visualization. This includes using search engines like Google and specialized search engines designed for OSINT, such as Shodan (for discovering internet-connected devices) and Maltego (for link analysis). I also utilize social media monitoring tools to track online discussions and identify key influencers. My techniques involve keyword searches, Boolean operators, advanced search syntax, and utilizing social network analysis to identify connections and patterns within large datasets. For example, I successfully used OSINT to track down the origin of a disinformation campaign by identifying the initial source of a false narrative and tracing its spread across different online platforms.
Q 4. How do you assess the credibility and reliability of intelligence sources?
Assessing the credibility and reliability of intelligence sources is crucial. I employ a multi-faceted approach that includes:
- Source Evaluation: Assessing the source’s track record, motivations, and potential biases. Is this source known to be reliable? Do they have a history of accuracy?
- Data Corroboration: Verifying information from multiple independent sources to increase confidence in its accuracy. Do other sources confirm this information?
- Contextual Analysis: Examining the information within its broader context to identify inconsistencies or potential manipulation. Does this information fit with what we already know?
- Methodology Assessment: Evaluating the methods used to collect the information. How was this information gathered? Are the methods reliable?
For example, I would treat information from a known hostile source with more skepticism than information from a long-standing, reliable partner.
Q 5. Explain your understanding of the intelligence cycle.
The intelligence cycle is a continuous process that involves planning and directing intelligence activities. The stages are typically:
- Planning and Direction: Identifying intelligence requirements and establishing priorities.
- Collection: Gathering information from various sources.
- Processing: Transforming raw data into usable intelligence.
- Analysis and Production: Interpreting the processed data and producing intelligence assessments.
- Dissemination: Sharing the intelligence assessments with relevant stakeholders.
- Feedback: Evaluating the effectiveness of the intelligence and making necessary adjustments.
Think of it as a feedback loop constantly refining our understanding.
Q 6. How do you handle conflicting information from different sources?
Handling conflicting information requires a careful and methodical approach. I would first:
- Identify the discrepancies: Pinpoint the specific points of conflict between the different sources.
- Evaluate the sources: Assess the credibility and reliability of each source, considering factors like past performance, potential biases, and methodology.
- Seek additional information: Look for further evidence to resolve the conflict, potentially involving new sources or investigative techniques.
- Analyze the context: Consider the broader context in which the information was generated to identify potential reasons for the discrepancies.
- Develop a hypothesis: Formulate a hypothesis that explains the conflicting information, acknowledging the uncertainties involved.
In some cases, the conflict might remain unresolved, and I would communicate this uncertainty transparently in the final intelligence assessment, highlighting the limitations of the available evidence.
Q 7. Describe your experience with data analysis and visualization techniques relevant to intelligence analysis.
My experience with data analysis and visualization is crucial to my work. I use various statistical methods such as regression analysis and cluster analysis to identify patterns and relationships within large datasets. I’m proficient in using data visualization tools like Tableau and Power BI to create interactive dashboards and charts that effectively communicate complex intelligence findings. For example, I might use network graphs to visualize the relationships between individuals in a criminal organization or geographical maps to depict the spread of a disease outbreak. These visualizations are crucial for conveying insights to both technical and non-technical audiences.
Q 8. How do you prioritize intelligence requirements and tasks?
Prioritizing intelligence requirements and tasks involves a structured approach that balances urgency, importance, and available resources. I typically use a combination of methods, starting with a clear understanding of the overarching intelligence objective. This could be, for example, assessing the capabilities of a competitor’s new product line or understanding the potential for social unrest in a specific region.
- Prioritization Matrix: I often employ a matrix that plots requirements based on their urgency (high, medium, low) and importance (high, medium, low). This helps visualize which tasks demand immediate attention versus those that can be scheduled.
- Stakeholder Consultation: I actively engage with stakeholders to understand their needs and priorities. This ensures alignment between intelligence efforts and strategic goals. Their input helps refine the prioritization process.
- Resource Allocation: Once prioritized, tasks are assigned resources – personnel, technology, and time – based on their complexity and urgency. This ensures efficient use of resources.
- Regular Review: The prioritization process isn’t static. I regularly review and adjust the prioritization based on new information or changes in the operational environment. This dynamic approach allows for flexibility and responsiveness.
For instance, if we’re tracking a fast-evolving geopolitical situation, intelligence requirements related to immediate threats would naturally take precedence over long-term strategic assessments.
Q 9. Explain your approach to identifying and mitigating biases in intelligence analysis.
Mitigating bias in intelligence analysis is crucial for producing objective and reliable assessments. My approach involves a multi-layered strategy focused on awareness, methodology, and review.
- Self-Awareness: I actively acknowledge my own biases – cognitive, cultural, or personal – and strive to understand how they might influence my analysis. This includes regular reflection on my assumptions and interpretations.
- Diverse Data Sources: I actively seek diverse data sources, ensuring I’m not relying solely on information that confirms pre-existing beliefs. This includes using open-source intelligence (OSINT), human intelligence (HUMINT), and signals intelligence (SIGINT) in a balanced way.
- Structured Analytical Techniques: I employ structured analytical techniques like analysis of competing hypotheses (ACH) to systematically evaluate different possibilities and challenge my assumptions. This reduces the impact of personal biases.
- Peer Review: I routinely share my analysis with colleagues for review and feedback. A fresh perspective can highlight biases I might have missed.
- Red Teaming: Sometimes, I use red teaming – a deliberate attempt to challenge my conclusions and identify vulnerabilities – to uncover potential biases before they affect decision-making.
For example, if analyzing a competitor’s market strategy, I would actively seek data from multiple sources – not only their public statements but also independent market research and consumer feedback – to avoid being influenced by overly positive or negative viewpoints.
Q 10. Describe your experience working with geospatial intelligence (GEOINT) tools and data.
I have extensive experience working with geospatial intelligence (GEOINT) tools and data. This involves using various software and platforms to analyze imagery, maps, and geographic information. My experience encompasses:
- Imagery Analysis: Using satellite imagery, aerial photography, and other visual data to identify objects, patterns, and changes over time. This includes using software to enhance images, perform measurements, and create detailed maps.
- GIS Software: Proficiency in using Geographic Information Systems (GIS) software such as ArcGIS or QGIS to manage, analyze, and visualize geospatial data. This allows for the creation of thematic maps, spatial analysis, and integration of diverse data sets.
- Data Fusion: Combining GEOINT data with other intelligence sources (e.g., HUMINT, SIGINT) to create a more comprehensive understanding of a situation. This involves integrating data from different sources and formats to create a cohesive intelligence picture.
- 3D Modeling: Utilizing 3D modeling software to create visualizations of geographic areas and structures. This helps to understand the physical environment and plan operations.
For example, in a recent project, we used satellite imagery to track the movement of military equipment and correlate that with SIGINT data to understand troop deployments in a region experiencing political instability. The integration of these data sets gave us a significantly clearer and more reliable picture than relying on a single source.
Q 11. How do you conduct effective research and information gathering for intelligence analysis?
Effective research and information gathering for intelligence analysis requires a methodical and multi-faceted approach. It’s not simply about collecting data; it’s about identifying the most relevant information and validating its credibility.
- Defining the Research Question: Clearly defining the intelligence requirement guides the research process. This helps focus efforts and avoid unnecessary data collection.
- Source Selection: Identifying and utilizing appropriate sources, considering their credibility, bias, and potential limitations. This involves using a mix of open-source, closed-source, and human intelligence channels.
- Data Collection Techniques: Employing a range of data collection techniques, such as online searches, database searches, interviews, and document analysis, tailored to the specific research needs.
- Data Validation and Verification: Critically assessing the accuracy, reliability, and completeness of collected information by comparing data from multiple sources and utilizing corroboration techniques.
- Data Organization and Management: Systematically organizing and managing collected data using databases or other tools to ensure efficient access and analysis.
For example, when investigating the financial activities of a suspected criminal organization, I would use a combination of online searches to identify publicly available company records, database searches to cross-reference information from various government and financial institutions, and potentially even interviews with individuals who might have relevant knowledge – always ensuring I properly verify the information’s accuracy and source.
Q 12. Explain your understanding of different intelligence methodologies (e.g., competitive, strategic).
Different intelligence methodologies serve distinct purposes within the intelligence cycle. My understanding of various methodologies includes:
- Competitive Intelligence: Focuses on understanding competitors’ strengths, weaknesses, strategies, and capabilities to gain a competitive advantage. This might involve analyzing market trends, competitor products, and business strategies.
- Strategic Intelligence: Provides long-term insights into broad geopolitical trends, technological advancements, and potential future threats and opportunities. It supports high-level decision-making by examining the long-term implications of various factors.
- Tactical Intelligence: Provides timely information relevant to immediate operational needs. This may include real-time situational awareness during a crisis or supporting specific military operations.
- Open Source Intelligence (OSINT): Gathering and analyzing information from publicly available sources, including the internet, news media, and social media. It’s a crucial component of many intelligence operations due to its accessibility and often overlooked insights.
- Human Intelligence (HUMINT): Gathering information through human contact, including spies, informants, and other sources. This requires a high level of trust and careful management of sources.
Understanding these methodologies allows for a tailored approach to intelligence gathering, ensuring that the appropriate methods are used to address specific needs. For example, a business might prioritize competitive intelligence, while a national security agency would focus more on strategic and tactical intelligence.
Q 13. How do you maintain confidentiality and security when handling sensitive intelligence information?
Maintaining confidentiality and security when handling sensitive intelligence information is paramount. My approach involves adhering to strict protocols and best practices:
- Need-to-Know Basis: I only share information with individuals who have a legitimate need to know, adhering to strict security clearances and access controls.
- Secure Communication Channels: I use secure communication channels, such as encrypted email and secure networks, to transmit sensitive information.
- Data Encryption: I ensure that all sensitive data is encrypted both in transit and at rest, minimizing the risk of unauthorized access.
- Physical Security: I maintain appropriate physical security measures to protect sensitive documents and materials, such as secure storage facilities and access controls.
- Compliance with Regulations: I adhere to all relevant laws, regulations, and organizational policies related to the handling of sensitive intelligence information.
- Regular Security Training: I participate in regular security awareness training to stay updated on best practices and emerging threats.
For example, I would never discuss classified information in public spaces or over unsecured communication channels. My adherence to these protocols ensures that sensitive data remains protected.
Q 14. Describe your experience with intelligence reporting and briefing techniques.
My experience with intelligence reporting and briefing techniques focuses on clarity, accuracy, and effectiveness in conveying complex information to diverse audiences. This involves adapting my communication style and format to the specific needs of the recipient.
- Clear and Concise Writing: I produce well-written reports that are clear, concise, and free of jargon, tailored to the audience’s understanding. I use precise language and avoid ambiguity.
- Data Visualization: I effectively utilize charts, graphs, and maps to present data visually, enhancing understanding and impact. Visual aids are crucial for complex data sets.
- Tailored Briefings: I prepare and deliver briefings tailored to the audience, adjusting the level of detail and technical language to their expertise. A briefing for senior leadership will differ greatly from a briefing for field operatives.
- Structured Reports: I produce reports using a standardized format to ensure consistency and readability. A well-structured report includes executive summaries, key findings, supporting evidence, and conclusions.
- Feedback Incorporation: I actively seek and incorporate feedback from recipients to improve future reports and briefings. Iterative feedback improves the effectiveness of communication.
For instance, when briefing senior leaders on a complex geopolitical situation, I would focus on the high-level strategic implications, using clear visuals and concise language. However, when briefing operational teams, I would provide more detailed tactical information relevant to their immediate responsibilities.
Q 15. How do you communicate complex intelligence information effectively to diverse audiences?
Communicating complex intelligence information effectively to diverse audiences requires tailoring the message to the audience’s understanding and needs. This involves understanding their background knowledge, their level of technical expertise, and their primary concerns. I employ a multi-faceted approach:
- Visual Aids: Charts, graphs, and maps are crucial for simplifying complex data relationships. For example, a network graph can illustrate connections between individuals or organizations involved in a specific threat.
- Layered Briefings: I deliver information in layers, starting with a high-level overview and progressively adding detail based on the audience’s engagement and questions. This ensures everyone receives the core message, while experts can delve into more nuanced aspects.
- Analogies and Storytelling: I use relatable analogies and real-world examples to explain abstract concepts. For instance, explaining a sophisticated cyberattack using the analogy of a physical burglary helps non-technical audiences grasp the threat.
- Interactive Sessions: Facilitating discussions and Q&A sessions allows for immediate clarification and fosters a more engaging learning experience. This ensures that I can adapt my communication to address specific questions and address any misunderstandings.
- Tailored Reports: Written reports are crafted with the intended audience in mind. Executive summaries provide concise information for high-level decision-makers, whereas detailed reports offer granular analysis for specialized teams.
For example, when briefing a group of military strategists on a potential terrorist threat, I would focus on military capabilities, operational timelines, and strategic implications. In contrast, briefing a group of financial analysts on the same threat, I would highlight financial vulnerabilities and economic impacts. The core information remains the same, but the presentation and emphasis differ greatly.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. How do you stay updated on current events and intelligence trends?
Staying updated on current events and intelligence trends requires a multi-pronged strategy. I leverage a combination of resources to ensure I’m always informed:
- Open-Source Intelligence (OSINT) Monitoring: I regularly scan reputable news sources, academic journals, social media platforms, and government publications for relevant information. I employ automated tools to monitor key terms and entities related to my areas of expertise.
- Closed-Source Intelligence Monitoring: I have access to classified information through appropriate channels, which is critical for understanding the full scope of intelligence trends.
- Intelligence Community Networks: I actively participate in professional networks and conferences to engage with other experts and learn about new developments in the field. This includes attending webinars, conferences, and workshops organized by relevant institutions.
- Specialized Databases and Platforms: I utilize intelligence analysis platforms (examples I can’t specify due to confidentiality) and databases containing information about geopolitical events, economic trends, and technological advancements. These are essential for deeper analysis.
- Continuous Learning: I dedicate time to reading industry reports, books, and scholarly articles to enhance my knowledge and skills. Staying abreast of emerging technologies and analytical methods is paramount in this dynamic field.
In essence, it is not just about passively absorbing information but actively seeking out multiple perspectives and critically analyzing the data from various sources to identify patterns and trends.
Q 17. Describe your experience using specific intelligence analysis software or platforms.
My experience with intelligence analysis software and platforms is extensive, though I’m constrained by confidentiality agreements from naming specific tools. However, I can broadly describe my experience. I’m proficient in using platforms that facilitate:
- Data Collection and Integration: I am skilled at using tools that collect data from various sources, including open-source intelligence, social media, and closed-source databases. These platforms often offer robust capabilities for data cleansing, normalization, and integration.
- Data Visualization and Mapping: I regularly use tools that allow for interactive visualization of complex data sets, including mapping capabilities that allow me to visualize geographic relationships between events and actors.
- Network Analysis: I utilize specialized software to analyze relationships between entities, identifying key players and influencers within a network. This is crucial for understanding the structure and dynamics of criminal organizations or terrorist networks.
- Predictive Modeling: Some platforms provide capabilities for predictive modeling, which allows us to forecast potential threats or future events based on existing data and trends. This requires careful consideration of model limitations and potential biases.
- Collaboration and Knowledge Sharing: My experience includes working with collaborative platforms that facilitate secure sharing of intelligence analysis and information among team members and other stakeholders.
These platforms significantly enhance my analytical capabilities and ensure the efficiency and accuracy of my work. My proficiency extends to learning and adapting to new platforms and technologies as they emerge.
Q 18. Explain your understanding of risk assessment and threat analysis.
Risk assessment and threat analysis are integral parts of the intelligence process. Risk assessment involves identifying, analyzing, and evaluating potential hazards, while threat analysis focuses on specific entities or actors posing a danger. These processes are intertwined.
Risk Assessment: This involves defining the scope of potential threats, identifying vulnerabilities, assessing the likelihood and impact of various risks, and developing mitigation strategies. For example, assessing the risk of a cyberattack on a critical infrastructure would involve identifying vulnerabilities in the system, the potential impact of a successful attack (financial losses, operational disruption, etc.), and the likelihood of such an attack based on past incidents and threat actor activity.
Threat Analysis: This involves identifying specific actors (individuals, groups, states) that pose a credible threat, understanding their capabilities, intentions, and potential targets. For instance, analyzing the threat posed by a specific cybercrime group would involve understanding their past activities, their technical capabilities, their financial motivations, and their likely targets. This analysis would be supplemented by technical analysis of malware and attack vectors.
Both processes involve using qualitative and quantitative data, evaluating various sources of information, and applying analytical frameworks to reach informed conclusions. The output informs the development of preventative measures and response plans.
Q 19. How do you use analytical frameworks or methodologies to structure your intelligence analysis?
Several analytical frameworks and methodologies guide my intelligence analysis. The choice depends on the specific challenge and the type of intelligence being analyzed.
- Structured Analytic Techniques (SATs): These include tools like analysis of competing hypotheses (ACH), key assumptions check (KAC), and red teaming. ACH helps me systematically evaluate multiple plausible explanations for an event, while KAC challenges my underlying assumptions, preventing biases. Red teaming involves simulating adversary actions to identify vulnerabilities and test my assumptions.
- Intelligence Cycle: I use the intelligence cycle (planning & direction, collection, processing, analysis, and dissemination) as a framework to guide the entire intelligence process from identifying intelligence needs to disseminating findings to decision-makers. Each stage involves distinct methods and rigorous quality checks.
- Diamond Model of Intrusion Analysis: When analyzing cyberattacks, I often use this model to structure my analysis around four key elements: adversary, infrastructure, capability, and victim. This structured approach helps ensure a thorough and comprehensive understanding of the attack.
- Indicators of Compromise (IOCs): For cybersecurity analysis, I rely on IOCs (e.g., IP addresses, domain names, malware hashes) to identify and track malicious activities. These are critical for proactively detecting and responding to threats.
By employing these frameworks and methodologies, I ensure a systematic, rigorous, and objective approach to intelligence analysis, minimizing biases and maximizing accuracy.
Q 20. Describe your experience working in a team environment to conduct intelligence analysis.
Teamwork is fundamental to successful intelligence analysis. I have extensive experience collaborating in diverse teams, leveraging individual expertise to achieve shared objectives. My role in a team often involves:
- Information Sharing: Actively sharing data, insights, and findings with team members. I ensure transparency and facilitate open communication to avoid information silos.
- Cross-Checking and Validation: Collaborating with colleagues to cross-check information, validate sources, and ensure the accuracy and reliability of our analysis. Diverse perspectives enhance quality control.
- Specialized Roles: Working with analysts specializing in different areas (e.g., cyber security, geopolitical analysis, open-source intelligence) to leverage their unique skills and knowledge, contributing to a more comprehensive understanding of a threat.
- Conflict Resolution: Facilitating constructive discussions to resolve disagreements and reach consensus on findings. This involves respecting diverse opinions while adhering to established analytical standards.
- Dissemination Strategy: Collaborating with team members to develop and implement effective strategies for disseminating intelligence information to stakeholders. This often involves coordinating messaging to ensure consistency and clarity.
For instance, in a recent project involving a complex financial fraud, I worked with colleagues specializing in financial data analysis, cyber forensics, and open-source intelligence gathering. Our combined expertise allowed us to uncover a sophisticated money laundering scheme that would have been difficult to detect using a single analytical approach.
Q 21. How do you manage time effectively when working on multiple intelligence projects?
Effective time management is crucial when juggling multiple intelligence projects. I employ several strategies to ensure efficiency and productivity:
- Prioritization: I prioritize tasks based on urgency and importance, focusing on high-impact projects first. This often involves considering the potential consequences of delays and assigning projects accordingly.
- Project Planning: I create detailed project plans with clear timelines, milestones, and deliverables. This provides a roadmap for each project, allowing me to track progress and identify potential bottlenecks early on.
- Time Blocking: I dedicate specific time blocks to focused work on particular projects, minimizing distractions and maximizing concentration. This structured approach helps me manage my time effectively, avoiding multitasking and maximizing efficiency.
- Delegation: When appropriate, I delegate tasks to team members based on their skills and expertise. This frees up my time to focus on more complex or higher-priority tasks.
- Regular Reviews: I regularly review my progress against project plans, adjusting timelines and priorities as needed. This ensures that I remain on track and effectively address unforeseen challenges.
For instance, if I’m working on a high-priority counter-terrorism investigation alongside a long-term analysis of a geopolitical trend, I would prioritize the immediate threat, allocating more time and resources to that project while still ensuring progress is made on the geopolitical analysis. This balanced approach optimizes my resource allocation while maintaining awareness of all critical projects.
Q 22. Explain your experience with qualitative and quantitative data analysis in intelligence work.
In All-Source Intelligence, both qualitative and quantitative data analysis are crucial for a complete understanding. Qualitative analysis focuses on understanding the ‘why’ behind events, drawing insights from textual sources like news articles, social media posts, or interviews. This involves techniques like thematic analysis, content analysis, and discourse analysis to identify patterns, sentiments, and narratives. Quantitative analysis, on the other hand, deals with numerical data, focusing on the ‘what’ and ‘how many’. This might involve statistical modeling, trend analysis, and data visualization to identify correlations, frequencies, and probabilities. For example, analyzing social media posts to understand public sentiment towards a political event is qualitative, while analyzing the number of mentions and the distribution of sentiment scores across different demographics would be quantitative. I have extensive experience in both, often using them in conjunction. A typical project might involve analyzing qualitative data to identify key themes and then quantitatively measuring the frequency and intensity of those themes over time to track trends.
Q 23. Describe a challenging intelligence analysis project you worked on and your approach to solving it.
One particularly challenging project involved assessing the potential for civil unrest in a volatile region. The challenge stemmed from the fragmented and contradictory nature of the available intelligence. We had limited access to official government sources, and open-source information was often unreliable or manipulated. My approach involved a multi-phased strategy: First, we conducted a comprehensive data collection effort, pulling together open-source intelligence from various sources (news, social media, blogs) as well as limited human intelligence. Second, we used a combination of qualitative and quantitative techniques. Qualitative analysis helped us identify key grievances and underlying tensions among different groups. Quantitative analysis – examining the frequency of protests, social media mentions of key grievances, and the spread of misinformation online – helped us assess the intensity and potential for escalation. Finally, we developed a risk assessment model, combining both qualitative and quantitative insights to create a probability matrix outlining various scenarios and their likelihoods. This allowed us to present a nuanced assessment, highlighting both the potential risks and the uncertainties involved. The result was a more comprehensive and accurate prediction, leading to proactive measures that mitigated the risk of significant unrest.
Q 24. How do you ensure the accuracy and validity of your intelligence findings?
Ensuring accuracy and validity is paramount in intelligence analysis. My approach relies on several key strategies: Source triangulation – verifying information from multiple independent sources to minimize bias and ensure accuracy. Data validation – scrutinizing data for inconsistencies, errors, or signs of manipulation. This might involve cross-referencing information with other databases or using fact-checking tools. Methodological rigor – applying rigorous analytical techniques and documenting the entire process, making it transparent and auditable. Peer review – presenting findings to colleagues for review and critique, ensuring a diverse perspective and identifying potential flaws in my analysis. By employing these techniques, I aim to produce findings that are not only accurate but also robust and defensible. Think of it like a detective building a case; it’s not enough to have one witness; you need multiple corroborating sources and evidence to establish the truth.
Q 25. Explain your understanding of ethical considerations in intelligence analysis.
Ethical considerations are central to All-Source Intelligence. This includes respecting privacy, avoiding bias, protecting sources and methods, and ensuring the responsible use of information. My work is guided by a strong ethical framework, prioritizing transparency and accountability. I adhere strictly to all relevant laws and regulations, mindful of the potential consequences of misinformation or the misuse of intelligence. I always strive for objectivity, acknowledging the limits of my analysis and avoiding any form of manipulation or misrepresentation. For example, in a situation involving sensitive personal information, I would strictly adhere to data protection protocols, ensuring anonymization and appropriate access controls. Furthermore, I would be very cautious about the use of information gathered through deception or unethical means. Ethical practice is not just a matter of compliance, but a cornerstone of responsible intelligence work.
Q 26. Describe your experience with the use of social media and online platforms for intelligence gathering.
Social media and online platforms are invaluable sources of open-source intelligence. I have extensive experience using these platforms to gather information, identify trends, and monitor public sentiment. My methods include keyword searches, network analysis, sentiment analysis, and the use of specialized social media intelligence tools. For instance, during a crisis situation, I would monitor social media for real-time updates, identifying potential threats or misinformation campaigns. I am proficient in identifying and assessing the credibility of sources, differentiating between legitimate information and disinformation. I also utilize advanced search techniques to uncover hidden or less visible data and use visualizations to map social networks and information flows. It is crucial to be mindful of the biases and limitations of this data type, and I always cross-reference it with other sources to ensure accuracy.
Q 27. How do you utilize different types of data (text, imagery, signals) to build a complete intelligence picture?
Building a complete intelligence picture requires integrating diverse data types. Textual data (news reports, documents) provides context and narratives. Imagery (satellite imagery, photographs) offers visual evidence and situational awareness. Signals intelligence (SIGINT) – intercepted communications – provides direct insight into intentions and plans. I utilize a systematic approach, combining these data types through data fusion techniques. This often involves creating a common operating picture, integrating various data sources onto a single platform to identify patterns and relationships. For example, satellite imagery might reveal troop movements, textual analysis of intercepted communications may reveal the intended target, and social media chatter may show public reactions to the unfolding situation. This integrative approach allows for a deeper and more nuanced understanding than using any single data type in isolation.
Q 28. Explain your proficiency in using specific data analysis tools or languages (e.g., Python, R).
I am proficient in using several data analysis tools and programming languages relevant to All-Source Intelligence. My expertise includes Python, which I use for data cleaning, analysis, and visualization using libraries such as Pandas, NumPy, and Matplotlib. import pandas as pd # Example of Python code for data manipulation I also use R for statistical modeling and advanced data analysis, leveraging its powerful statistical packages. Beyond programming, I am skilled in using various Geographic Information Systems (GIS) software for mapping and spatial analysis, and I am familiar with several commercial intelligence platforms, facilitating efficient data collection, integration, and visualization. My programming skills allow me to automate tasks, build custom tools, and conduct advanced analyses not readily available through standard software packages, thus contributing to a more efficient and impactful intelligence process.
Key Topics to Learn for AllSource Intelligence Interview
- Data Analysis & Interpretation: Understanding how to extract meaningful insights from large datasets, focusing on relevant metrics and identifying trends.
- Intelligence Gathering Techniques: Familiarize yourself with various methods used to collect and analyze information, including open-source intelligence (OSINT) techniques.
- Risk Assessment & Mitigation: Learn how to evaluate potential risks and develop strategies to mitigate them based on analyzed intelligence.
- Report Writing & Presentation: Practice crafting concise, clear, and impactful reports that effectively communicate complex information to diverse audiences.
- Data Visualization & Communication: Mastering the art of visually representing data to enhance understanding and facilitate decision-making.
- Technological Proficiency: Demonstrate familiarity with relevant software and tools used in intelligence analysis (mention specific tools if known, but avoid specifics to encourage independent research).
- Problem-Solving & Critical Thinking: Develop your ability to analyze complex situations, identify key issues, and propose effective solutions.
- Ethical Considerations in Intelligence: Understanding the ethical implications and responsibilities associated with intelligence gathering and analysis.
Next Steps
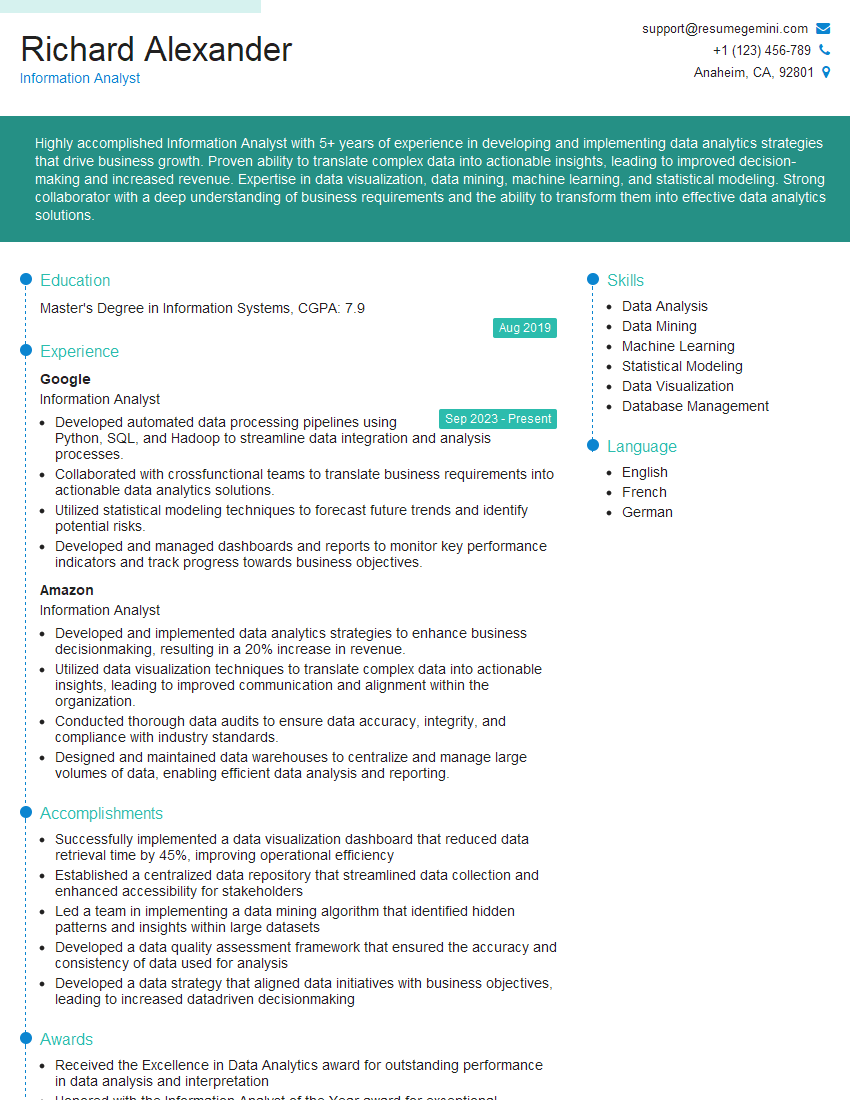
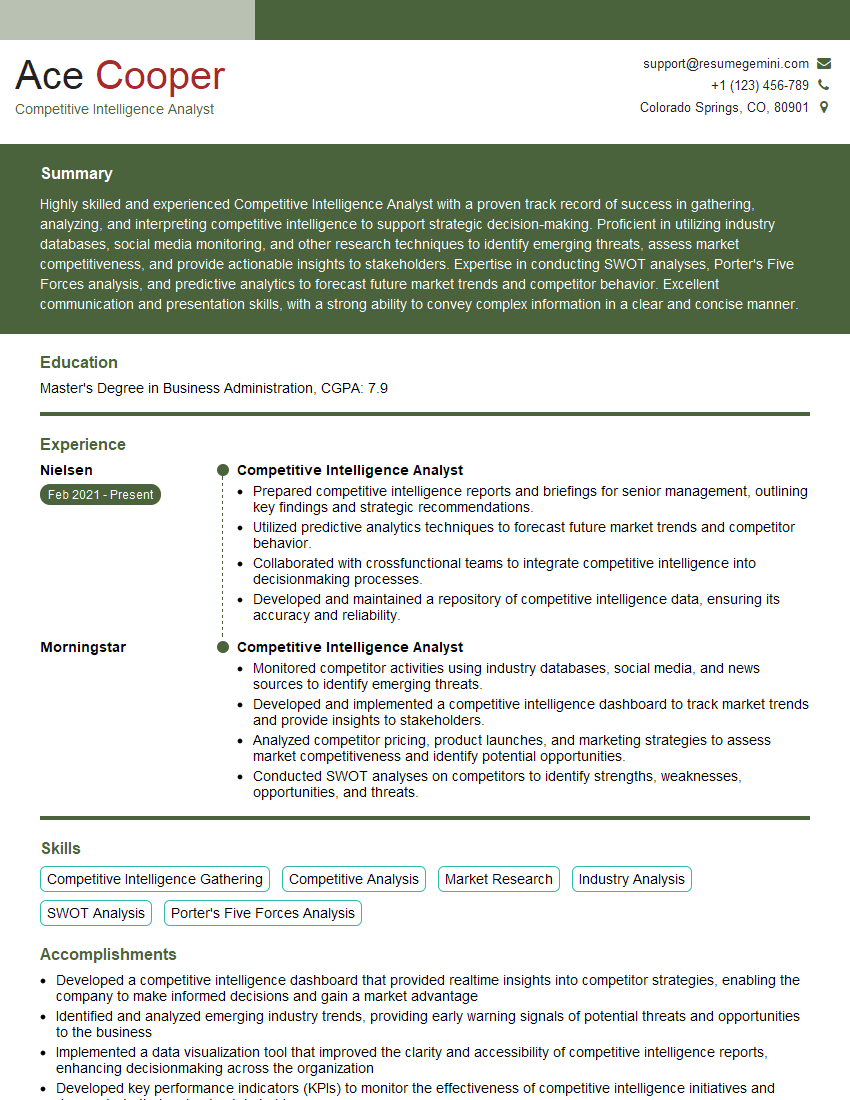
Mastering AllSource Intelligence principles significantly enhances your career prospects in the competitive intelligence field, opening doors to diverse and impactful roles. A strong, ATS-friendly resume is crucial for showcasing your skills and experience effectively. To build a compelling resume that highlights your capabilities and catches the attention of recruiters, we highly recommend using ResumeGemini. ResumeGemini offers a powerful and user-friendly platform to craft a professional document tailored to your specific career goals. Examples of resumes tailored to AllSource Intelligence are available to help guide your efforts.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good