The right preparation can turn an interview into an opportunity to showcase your expertise. This guide to Counterterrorism and Counterinsurgency Operations interview questions is your ultimate resource, providing key insights and tips to help you ace your responses and stand out as a top candidate.
Questions Asked in Counterterrorism and Counterinsurgency Operations Interview
Q 1. Explain the difference between counterterrorism and counterinsurgency.
While both counterterrorism (CT) and counterinsurgency (COIN) aim to defeat violence, they differ significantly in their targets and approaches. Counterterrorism focuses on disrupting specific terrorist groups and networks through targeted operations, often involving law enforcement and intelligence agencies. It’s a reactive approach, responding to threats as they emerge. Counterinsurgency, however, is a broader, more comprehensive strategy aimed at defeating an insurgency – a protracted armed rebellion seeking to overthrow a government or occupy territory. COIN involves military, political, economic, and social dimensions, striving to win the hearts and minds of the population and undermine the insurgents’ legitimacy and support. Think of it this way: CT is like surgical strikes against specific tumors, while COIN is like treating the entire body to prevent the cancer’s spread.
For example, the US response to the 9/11 attacks was primarily CT-focused, targeting Al-Qaeda’s leadership and infrastructure. In contrast, the US involvement in Afghanistan and Iraq encompassed major COIN operations, addressing not just the insurgent groups but also governance, development, and societal issues.
Q 2. Describe your understanding of asymmetric warfare.
Asymmetric warfare refers to conflict between belligerents with vastly different capabilities and strategies. One side, typically a weaker actor like an insurgency or terrorist group, employs unconventional tactics, such as guerrilla warfare, bombings, and hostage-taking, to offset the superior conventional strength of its opponent. The weaker party aims to exploit the opponent’s vulnerabilities and create a disproportionate impact. It’s like a David versus Goliath scenario, where David uses unconventional methods to overcome Goliath’s superior strength.
Examples of asymmetric warfare abound throughout history. The Viet Cong’s tactics during the Vietnam War, employing guerilla warfare and booby traps against a technologically superior US military, are a prime example. Similarly, terrorist organizations frequently use suicide bombings and other acts of terror to inflict maximum damage despite their limited resources and manpower.
Q 3. What are the key elements of a successful counterterrorism strategy?
A successful counterterrorism strategy requires a multifaceted approach that integrates several key elements:
- Intelligence Gathering and Analysis: Accurate and timely intelligence is crucial for identifying threats, tracking terrorist networks, and disrupting plots before they are executed.
- Law Enforcement: Effective investigation and prosecution of terrorist suspects within the legal framework are essential to hold individuals accountable and dismantle networks.
- Military Operations: Targeted strikes and other military actions may be necessary to eliminate key operatives and disrupt terrorist capabilities.
- International Cooperation: Terrorism is a global threat requiring collaborative efforts between countries to share intelligence, coordinate operations, and develop joint strategies.
- Counter-Ideology Efforts: Addressing the underlying ideologies that fuel terrorism is vital for preventing recruitment and building resilience to extremist narratives.
- Border Security and Transportation Security: Strengthening border security and improving transportation security measures are crucial to prevent terrorists from moving freely and carrying out attacks.
- Financial Disruption: Cutting off terrorist financing through sanctions, asset freezes, and other measures weakens their capacity to operate.
Ignoring any of these elements can significantly weaken the overall effectiveness of a counterterrorism strategy. It’s like trying to build a house with missing bricks – the whole structure is compromised.
Q 4. How would you assess the effectiveness of a counterinsurgency campaign?
Assessing the effectiveness of a counterinsurgency campaign requires a holistic approach beyond simply counting casualties. Key indicators include:
- Reduction in insurgent violence: A decline in attacks and casualties is a crucial, but not sufficient, indicator.
- Increased government control: Expanding the government’s authority and influence over territory and populations demonstrates effectiveness.
- Improved governance and public services: Providing essential services like healthcare, education, and infrastructure fosters support for the government and undermines the insurgents’ appeal.
- Strengthened security forces: The capability and capacity of the host nation’s security forces are vital for long-term stability.
- Increased popular support for the government: This is often measured through opinion polls, surveys, and observations of public behavior.
- Reduced insurgent recruitment and support: A decline in the flow of recruits and resources to the insurgency indicates diminishing legitimacy.
These factors should be assessed qualitatively and quantitatively using various metrics, reports, and analysis techniques. No single measure is sufficient. The goal isn’t just military victory; it’s lasting peace and stability that reduces the likelihood of future insurgency.
Q 5. What are some common indicators of terrorist activity?
Indicators of terrorist activity are diverse and can be subtle or overt. Some common indicators include:
- Intelligence reports: Intercepted communications, human intelligence, and signals intelligence.
- Surveillance activities: Unusual reconnaissance of potential targets like government buildings or infrastructure.
- Acquisition of weapons and explosives: Attempts to purchase or illicitly obtain weapons, explosives, or other materials relevant to attacks.
- Suspicious financial transactions: Large, unusual transfers of money that could be used to fund terrorist activities.
- Recruitment efforts: Attempts to recruit new members or spread extremist propaganda.
- Increased extremist rhetoric: A rise in online or offline propaganda and hateful messages.
- Travel patterns: Individuals traveling to known terrorist training camps or areas of conflict.
- Cyber activity: Hacking attempts and other online actions aimed at disrupting critical infrastructure or spreading propaganda.
It’s crucial to note that many of these indicators, in isolation, may be innocent. It’s the pattern of behavior and convergence of multiple indicators that suggest potential terrorist activity. Effective intelligence analysis is key to distinguishing legitimate activities from suspicious ones.
Q 6. Explain the concept of ‘hearts and minds’ in counterinsurgency.
The ‘hearts and minds’ approach in counterinsurgency refers to the strategy of winning the loyalty and support of the civilian population. It’s the recognition that military victory alone is insufficient; enduring stability requires the active cooperation and support of the people. Insurgents often rely on popular support, even tacitly, to survive and operate. By winning the hearts and minds, the government undermines the insurgency’s base of support and makes it more difficult for them to recruit, operate, and gain legitimacy.
This involves providing essential services like healthcare, education, and infrastructure, addressing grievances, and promoting good governance. It also requires demonstrating respect for human rights, avoiding excessive force, and fostering a sense of security and trust among the population. It’s a long-term endeavor requiring patience, understanding, and a deep commitment to improving the lives of civilians.
Q 7. Discuss the role of intelligence gathering in counterterrorism operations.
Intelligence gathering plays a vital, often decisive, role in counterterrorism operations. It involves the collection, analysis, and dissemination of information to identify and neutralize terrorist threats. Sources of intelligence include:
- Human intelligence (HUMINT): Information obtained from human sources, such as informants, defectors, and undercover agents.
- Signals intelligence (SIGINT): Intercepting and analyzing communications such as phone calls, emails, and radio transmissions.
- Imagery intelligence (IMINT): Satellite imagery, aerial photography, and other visual sources providing valuable information.
- Open-source intelligence (OSINT): Publicly available information from the internet, news reports, and other sources.
- Financial intelligence: Tracking financial flows to identify funding sources and money laundering activities.
Effective intelligence gathering is not merely about collecting data; it is about analyzing it effectively to identify patterns, predict future actions, and develop actionable intelligence that can disrupt plots and prevent attacks. It requires skilled analysts, robust technology, and strong collaboration across different agencies and countries. Think of it as the detective work necessary to solve a complex crime, but on a much larger and more dangerous scale.
Q 8. How do you evaluate the credibility of intelligence sources?
Evaluating the credibility of intelligence sources is paramount in counterterrorism and counterinsurgency. It’s a multi-faceted process that relies on a combination of technical analysis and human judgment. We use a rigorous system that assesses several key factors:
- Source Reliability: This involves examining the source’s past performance, their motivation (are they seeking reward, revenge, or are they truly providing unbiased information?), and their access to the information. A source with a consistent track record of accurate information is more credible than one with a history of misinformation.
- Information Corroboration: We rarely rely on a single source. Information needs to be corroborated from multiple independent sources. The convergence of information from different channels significantly increases the credibility of the intelligence. Think of it like a legal case: multiple witnesses testifying to the same event strengthens the case’s veracity.
- Method of Acquisition: How was the information obtained? Was it through human intelligence (HUMINT), signals intelligence (SIGINT), or open-source intelligence (OSINT)? Each method has its strengths and weaknesses, and understanding the limitations of the collection method is crucial. SIGINT, for example, might provide a broad overview but may lack context, requiring human analysis for meaningful interpretation.
- Bias Detection: We always consider potential biases in the information. A source’s cultural background, political affiliations, or personal experiences can influence their perspective and the information they provide. Understanding and accounting for these biases is vital in creating a more accurate intelligence picture.
For example, during my time in the field, we received information from a suspected insurgent informant. While the information provided was initially promising, cross-referencing with other intelligence sources revealed inconsistencies. Further investigation uncovered the informant’s ulterior motive – he was trying to manipulate us to target a rival faction. By diligently applying this multi-layered assessment process, we were able to avoid a potentially disastrous operation.
Q 9. Describe different methods of information dissemination in counterinsurgency.
Information dissemination in counterinsurgency is crucial for achieving the mission’s objectives. It’s not just about delivering information; it’s about tailoring the message to the target audience and the context. We employ several methods:
- Public Information Campaigns: These campaigns use a variety of media, including radio, television, print, and social media, to reach a wide audience with messages aimed at countering extremist narratives and promoting government initiatives.
- Community Engagement Programs: These involve directly engaging with local communities through town hall meetings, workshops, and other events. This allows for a two-way dialogue and facilitates the collection of local perspectives and concerns.
- Targeted Communications: This approach focuses on disseminating information to specific individuals or groups. For instance, we might use leaflets or personal contacts to reach out to potential defectors or to provide early warnings about impending attacks.
- Intermediaries: Working with community leaders, religious figures, and influential individuals is often crucial for disseminating information effectively. These individuals enjoy high credibility and trust within their communities, making their endorsement critical.
- Psychological Operations (PSYOPS): PSYOPS aims to influence the attitudes and behaviors of individuals and groups by using messaging and propaganda strategies. These need to be carefully planned and executed to avoid generating negative reactions.
For instance, in one counterinsurgency operation, we successfully utilized a combination of public information campaigns and targeted communications to promote a civilian disarmament program. This resulted in a significant reduction in the availability of weapons to insurgent groups.
Q 10. What are the ethical considerations in counterterrorism operations?
Ethical considerations in counterterrorism are paramount. The actions taken must always be justified, proportionate, and compliant with both national and international law. Key ethical concerns include:
- Proportionality: The response to a terrorist threat should be proportional to the threat itself. Excessive force or collateral damage are unacceptable. The potential harm caused by military action should always be weighed against the potential harm of inaction.
- Distinction: We must distinguish between combatants and non-combatants. Targeting civilians or civilian infrastructure is a war crime and morally reprehensible. This requires precise intelligence and meticulous planning to avoid causing harm to innocent people.
- Human Rights: Counterterrorism operations must uphold human rights standards. The use of torture, arbitrary detention, and extrajudicial killings is strictly prohibited. Accountability for abuses is essential for maintaining public trust and legitimacy.
- Transparency and Accountability: The actions taken in counterterrorism operations must be transparent and accountable. Independent oversight and investigation mechanisms are necessary to prevent abuses and ensure compliance with ethical standards.
- Due Process: Individuals suspected of terrorism-related offences must be afforded due process of law. This includes the right to a fair trial, legal representation, and the presumption of innocence.
One of the most challenging ethical dilemmas is dealing with the potential for collateral damage. We spend significant time in risk assessments before any operation to minimize such damage. Sometimes, the best option is to take no action; inaction can be more ethically sound than risking the lives of non-combatants.
Q 11. How do you manage risk in high-threat environments?
Risk management in high-threat environments requires a proactive and multi-layered approach. It’s not just about physical safety; it also encompasses operational security, information security, and personnel welfare. The process involves:
- Threat Assessment: Thoroughly evaluating the potential threats, considering the specific context, including the local environment, potential adversaries, and the mission’s objectives. This includes identifying potential vulnerabilities and prioritizing them.
- Risk Mitigation: Developing and implementing strategies to reduce or eliminate identified risks. This may involve modifying operational plans, implementing security measures, or providing personnel with specialized training.
- Contingency Planning: Developing detailed plans for responding to unexpected events or emergencies. This includes pre-planning evacuation routes, establishing communication protocols, and setting up emergency response teams.
- Security Protocols: Enforcing strict security protocols, such as access control, surveillance, and secure communications, to limit the risk of compromise.
- Force Protection: Implementing measures to protect personnel from harm. This may include providing armed security escorts, utilizing armored vehicles, and employing advanced surveillance technologies.
For example, before deploying to a high-risk area, we conducted a thorough risk assessment, identifying potential threats like IEDs, ambushes, and kidnappings. Based on this assessment, we implemented security measures, including route planning that avoided known high-risk areas, vehicle patrols, and the use of advanced communication systems.
Q 12. Explain the importance of cultural awareness in counterinsurgency.
Cultural awareness is critical for success in counterinsurgency. Ignoring local customs, traditions, and beliefs can severely undermine operations and even be counterproductive. Understanding the local culture allows us to:
- Build Trust and Rapport: Demonstrating respect for local customs and values helps build trust and rapport with the local population. This allows for more effective information gathering and cooperation.
- Adapt Operational Strategies: Tailoring operational strategies to fit the local cultural context ensures they are more effective and less likely to cause offense or alienation.
- Avoid Unintended Consequences: Understanding cultural nuances helps avoid actions that may have unintended negative consequences. What might be viewed as appropriate in one culture can be deeply offensive in another.
- Enhance Communication: Effective communication requires cultural sensitivity. Understanding non-verbal cues, social norms, and communication styles can significantly improve interactions with local communities.
- Identify Influencers: Understanding the social structure and identifying key influential figures in a community helps ensure the effective dissemination of information and cooperation in achieving mission objectives.
I’ve personally witnessed situations where operations failed because of a lack of cultural awareness. For example, inadvertently insulting a local leader by ignoring a seemingly minor customary practice led to the loss of crucial intelligence and valuable cooperation. Cultural training is thus essential, involving extensive study and interaction with the target community, ideally in advance of deployment.
Q 13. Describe your experience with crisis management protocols.
My experience with crisis management protocols involves a structured and highly coordinated approach. It begins with a rapid and accurate assessment of the situation, followed by a series of actions that often happen simultaneously:
- Situation Assessment: Quickly and accurately assessing the nature, scale, and severity of the crisis using all available information. Establishing clear communication channels is vital here.
- Activation of Protocols: Following pre-established crisis management protocols, including activation of relevant teams and personnel. Protocols should clearly define roles, responsibilities, and decision-making processes.
- Resource Allocation: Effectively allocating resources to support response efforts, such as personnel, equipment, and financial resources. This often means prioritizing needs and making difficult choices.
- Communication and Coordination: Maintaining clear and consistent communication with all stakeholders, including government agencies, international organizations, and the affected population. This requires clear, concise, and consistent messaging.
- Damage Control and Recovery: Implementing measures to mitigate the impact of the crisis, such as providing aid to victims, restoring essential services, and communicating with the public.
During one particular incident involving a hostage situation, the swift activation of our crisis response protocol, with clear communication and coordinated efforts among various agencies, was critical in achieving a positive resolution. Regular drills and training scenarios are vital to ensure effectiveness during a real crisis.
Q 14. What are the challenges of working in interagency environments?
Working in interagency environments presents unique challenges due to the diverse organizational cultures, priorities, and bureaucratic processes of different agencies. These challenges include:
- Communication Barriers: Differences in terminology, communication styles, and information-sharing practices can create barriers to effective communication and coordination.
- Conflicting Priorities: Agencies may have conflicting priorities, leading to disagreements on strategies and resource allocation. A unified strategic vision needs to be well-defined and understood by all participating entities.
- Bureaucratic Hurdles: Navigating bureaucratic processes and regulations can be time-consuming and frustrating, hindering rapid response times and decision-making.
- Data Silos: Agencies may have different data systems and information sharing practices, leading to data silos and an incomplete understanding of the situation.
- Personality Conflicts: Personality clashes and differing working styles can also hinder collaboration. Establishing a positive and cooperative working atmosphere is very important.
Overcoming these challenges requires strong leadership, clearly defined roles and responsibilities, effective communication strategies, and a commitment to collaboration. In my experience, successful interagency cooperation hinges on building trust, establishing common goals, and developing mechanisms for efficient information sharing and conflict resolution. Open and respectful communication, coupled with well-defined decision-making processes, is critical to success.
Q 15. How do you develop and maintain effective communication within a team?
Effective communication in a counterterrorism/counterinsurgency team is paramount. It’s not just about information exchange; it’s about building trust, fostering collaboration, and ensuring everyone is on the same page, especially under immense pressure. We achieve this through a multi-pronged approach.
Clear and Concise Communication Protocols: Establishing standardized reporting procedures, using clear and concise language, avoiding jargon, and utilizing various communication channels (secure messaging, briefings, debriefings) are crucial. For example, we use a structured reporting format for intelligence updates, ensuring consistent information flow and minimizing misunderstandings.
Active Listening and Feedback Mechanisms: Active listening is key to understanding team members’ perspectives and concerns. Regular feedback sessions, both formal and informal, allow for addressing challenges proactively and fostering a culture of open dialogue. In one operation, a team member’s concern about a potential ambush route, voiced during a casual conversation, led to a successful route adjustment, preventing casualties.
Building Trust and Rapport: Trust is the foundation of any effective team. This requires building strong interpersonal relationships based on mutual respect and confidence in each other’s abilities. Team-building exercises, informal interactions, and consistent, dependable behavior contribute to this crucial element.
Utilizing Technology Effectively: Secure communication platforms, collaborative workspaces, and data-sharing systems are vital for efficient communication, especially in geographically dispersed teams.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. How do you prioritize competing tasks in a high-pressure situation?
Prioritizing tasks in high-pressure situations requires a structured approach that balances urgency and importance. The Eisenhower Matrix (urgent/important) is a helpful tool, but in counterterrorism, we often adapt it for real-time decision-making.
Threat Assessment: The first step is a rapid threat assessment. We prioritize tasks based on their potential impact on human life, critical infrastructure, and mission objectives. For instance, an imminent terrorist attack takes precedence over a long-term intelligence gathering initiative.
Resource Allocation: We consider available resources (personnel, equipment, time) when assigning priorities. We avoid spreading resources too thinly, focusing on the most critical tasks first.
Time Management: We employ time management techniques like time blocking and prioritization matrices to allocate resources effectively. A common strategy is to delegate tasks to specialized teams.
Flexibility and Adaptability: The situation is dynamic. Prioritization is not static; reassessment and adjustment are essential as new information emerges or the situation evolves. For example, a sudden shift in enemy activity requires immediate reallocation of resources.
Q 17. Discuss your experience with data analysis and threat assessment.
Data analysis and threat assessment are integral to counterterrorism. It’s a continuous cycle of information gathering, analysis, and dissemination.
Data Sources: We gather data from various sources—open-source intelligence (OSINT), human intelligence (HUMINT), signals intelligence (SIGINT), geospatial intelligence (GEOINT), and more. Each source is rigorously evaluated for its reliability and validity.
Analytical Techniques: We employ a range of analytical techniques, including link analysis, pattern recognition, predictive modeling, and risk assessment methodologies. For instance, link analysis helps identify connections between individuals, groups, and events, revealing potential terrorist networks. Predictive modeling helps anticipate future threats based on historical data and trends.
Threat Assessment Frameworks: We use established frameworks to systematically assess threats, considering factors such as the actor’s capabilities, intentions, and the vulnerability of potential targets. This allows us to quantify and prioritize the most likely threats.
Technology’s Role: Technology plays a vital role in data analysis, from advanced data mining techniques to sophisticated visualization tools that help us identify patterns and trends that might otherwise be missed.
Q 18. Describe your understanding of the legal framework surrounding counterterrorism.
The legal framework surrounding counterterrorism is complex and varies across jurisdictions, but several core principles apply universally. It’s crucial to operate within the bounds of the law while effectively combating terrorism.
International Law: International humanitarian law (IHL), international human rights law (IHRL), and international criminal law (ICL) all play a significant role. Actions must be proportionate, discriminate between combatants and civilians, and respect fundamental human rights.
National Law: Each country has its own counterterrorism legislation, defining offenses, outlining investigative powers, and regulating the use of force. This legislation is often updated to reflect evolving terrorist tactics and threats.
Due Process and Human Rights: The legal framework protects individual rights, ensuring due process and the prevention of arbitrary detention or torture. Even in the context of counterterrorism, legal procedures must be followed rigorously.
Challenges and Balancing Acts: Balancing national security concerns with individual rights and legal obligations presents significant challenges. The effectiveness of counterterrorism strategies often depends on navigating this delicate balance.
Q 19. How do you identify and mitigate potential vulnerabilities to terrorist attacks?
Identifying and mitigating vulnerabilities to terrorist attacks requires a multi-layered approach that incorporates physical security, intelligence gathering, and community engagement.
Vulnerability Assessments: We conduct thorough vulnerability assessments of critical infrastructure, public spaces, and potential targets. This involves identifying weaknesses in physical security, personnel procedures, and emergency response plans.
Intelligence Gathering: Intelligence gathering helps us anticipate potential attacks. We utilize various intelligence sources to identify threats, track terrorist activities, and pinpoint vulnerabilities.
Security Enhancements: Based on vulnerability assessments and intelligence, we implement security enhancements, such as improved surveillance systems, access control measures, and physical barriers. This might include enhanced perimeter security at airports or increased police presence in high-risk areas.
Community Engagement: Engaging with communities is crucial. Building trust and fostering cooperation with local populations provides valuable intelligence and enhances community resilience against terrorist threats. Local knowledge can be incredibly useful in identifying potential vulnerabilities that might otherwise be overlooked.
Emergency Response Planning: Developing and regularly exercising comprehensive emergency response plans is vital. This ensures effective response in the event of an attack, minimizing casualties and damage.
Q 20. Explain the role of technology in counterterrorism and counterinsurgency.
Technology plays a transformative role in counterterrorism and counterinsurgency. It provides tools for intelligence gathering, analysis, communication, and response.
Intelligence Gathering and Analysis: Signal intelligence (SIGINT), geospatial intelligence (GEOINT), and data mining techniques are crucial for identifying potential threats and analyzing terrorist networks. Advanced analytics tools help identify patterns and connections in vast datasets.
Communication and Collaboration: Secure communication systems and collaborative platforms allow for effective information sharing and coordination among different agencies and teams, even across geographical boundaries.
Surveillance and Monitoring: Advanced surveillance technologies, including drones, satellite imagery, and facial recognition software, play a critical role in monitoring potential threats and tracking terrorist activities. However, ethical and legal considerations are paramount.
Cybersecurity: Protecting critical infrastructure and countering cyberterrorism are increasingly important. This includes protecting critical systems from cyberattacks and countering online propaganda and recruitment efforts.
Challenges and Ethical Considerations: While technology offers powerful tools, it also raises important ethical and legal considerations, such as privacy concerns and the potential for bias in algorithms. These must be carefully addressed.
Q 21. How do you assess the effectiveness of different counterterrorism tactics?
Assessing the effectiveness of counterterrorism tactics requires a multi-faceted approach, moving beyond simple metrics like arrests and casualties to encompass long-term outcomes and unintended consequences.
Quantitative Metrics: While crucial, simple metrics such as the number of terrorists apprehended, attacks prevented, or casualties inflicted, only offer a partial picture. These need to be contextualized.
Qualitative Metrics: Analyzing the long-term impact on terrorist networks, community attitudes, and political stability is equally important. Did the tactics weaken the terrorist group or merely displace it? Did they improve or erode public trust? Did they have unintended consequences, such as radicalization or civilian casualties?
Comparative Analysis: Comparing the effectiveness of different tactics across different contexts is crucial. What worked in one setting might not work in another. Understanding the factors that contribute to success or failure in specific situations is key.
Long-Term Impact Assessment: A true assessment requires considering the long-term effects of tactics, evaluating their sustainability and unintended consequences. Short-term successes might mask long-term failures if the underlying issues that lead to terrorism are not addressed.
Continuous Monitoring and Evaluation: The effectiveness of counterterrorism tactics should be continuously monitored and evaluated, adapting strategies based on evolving threats and circumstances.
Q 22. Discuss the importance of building trust with local populations in counterinsurgency.
Building trust with local populations is paramount in counterinsurgency (COIN) operations. Without it, even the most sophisticated military tactics will fail. Insurgents thrive on exploiting grievances and manipulating perceptions; winning hearts and minds directly counters this.
Trust is built through consistent, positive actions demonstrating respect for the local culture and community. This involves:
- Protecting civilians: Prioritizing civilian safety and minimizing collateral damage is crucial. This includes robust rules of engagement and thorough investigation of civilian casualties.
- Providing essential services: Assisting with infrastructure development, healthcare, education, and economic opportunities demonstrates tangible benefits and improves the quality of life.
- Engaging in respectful dialogue: Actively listening to local concerns, addressing grievances, and acting upon legitimate complaints shows a genuine commitment to their well-being. This requires cultural sensitivity training for personnel.
- Transparency and accountability: Openly communicating actions and intentions fosters confidence. Acknowledging mistakes and taking corrective action builds credibility.
- Empowering local leaders: Collaborating with and supporting legitimate local authorities strengthens governance and weakens the insurgent’s influence.
For example, during the US-led COIN effort in Iraq, projects focused on restoring essential services such as electricity and water were as critical as military operations in achieving stability. Similarly, the success of COIN operations in parts of Afghanistan was directly linked to the development of local governance structures.
Q 23. How do you address misinformation and propaganda during a conflict?
Combating misinformation and propaganda is a crucial aspect of COIN and counterterrorism. Insurgents often utilize propaganda to manipulate public opinion, recruit fighters, and undermine government legitimacy. Addressing this requires a multi-pronged approach.
- Identifying and understanding the narratives: Thorough intelligence gathering is essential to identify the main themes and sources of misinformation. This involves analyzing social media, local news, and direct community engagement.
- Developing counter-narratives: Creating compelling and credible messages that directly challenge the insurgents’ propaganda is crucial. These messages should be tailored to the specific audience and delivered through trusted channels.
- Leveraging local media: Partnering with credible local media outlets to disseminate accurate information and counter false narratives is essential. This requires building relationships with journalists and media organizations.
- Utilizing social media platforms: Effectively countering propaganda on social media requires a dedicated and agile team capable of monitoring, identifying and quickly refuting false claims. This needs a strategy that understands the nuances of specific platforms.
- Promoting media literacy: Educating the population on how to critically evaluate information and identify disinformation is vital in the long term.
Think of it like a vaccination program against an ideological disease; it’s not just about treating the symptoms (combatting the insurgents), but also about building immunity (media literacy) against future outbreaks of propaganda.
Q 24. What are the long-term implications of counterterrorism and counterinsurgency operations?
The long-term implications of counterterrorism and counterinsurgency operations are multifaceted and far-reaching. They extend beyond the immediate cessation of violence and can significantly impact political stability, economic development, and human rights for years or even decades after the conflict ends.
- Political instability: Prolonged conflicts can weaken state institutions, leading to political instability and the potential for future violence. The vacuum left by a collapsed state can be filled by other violent extremist groups.
- Economic hardship: Conflicts disrupt economic activity, destroying infrastructure and leading to job losses and widespread poverty. This can fuel resentment and create fertile ground for future insurgencies.
- Human rights abuses: Counterterrorism measures, if not carefully implemented and monitored, can lead to human rights abuses, including arbitrary detention, torture, and extrajudicial killings. These violations can erode trust in the government and fuel further radicalization.
- Social trauma and displacement: Communities impacted by violence may experience lasting social and psychological trauma. Displacement and migration patterns can destabilize neighboring regions.
- The rise of new extremist groups: Counterterrorism measures may inadvertently create space for the emergence of new extremist groups that feel marginalized or ignored. These groups will often adopt new tactics and ideologies.
Post-conflict reconstruction and reconciliation efforts are crucial to address these long-term implications. These initiatives should focus on strengthening governance, promoting economic development, and addressing human rights concerns in a holistic manner.
Q 25. Describe your understanding of the impact of counterterrorism on human rights.
The impact of counterterrorism on human rights is a complex and often controversial issue. While counterterrorism is essential to protect national security, it can inadvertently lead to human rights violations if not carefully managed. Striking a balance between security and human rights is a constant challenge.
- Due process violations: In the urgency to apprehend terrorists, governments may resort to measures that violate due process rights, such as indefinite detention without trial or torture to extract information.
- Profiling and discrimination: Counterterrorism measures may lead to profiling and discrimination against particular ethnic or religious groups, fueling resentment and alienation. This can inadvertently provide recruits for terrorist organizations.
- Surveillance and privacy concerns: The use of mass surveillance technologies raises significant privacy concerns. Balancing the need for security with the right to privacy is a delicate task.
- Collateral damage: Military operations and counterterrorism tactics may inadvertently harm civilians, violating the principle of distinction in warfare. This loss of life damages trust and fuels negative perceptions.
- Restrictions on freedom of expression: Governments might restrict freedom of expression under the guise of counterterrorism, silencing dissent and limiting open debate.
International human rights law and standards provide a framework for conducting counterterrorism operations while respecting human rights. Transparency, accountability, and independent oversight mechanisms are vital to ensure that counterterrorism measures do not undermine the rule of law and human rights.
Q 26. How do you ensure accountability and transparency in counterterrorism operations?
Ensuring accountability and transparency in counterterrorism operations is critical for maintaining public trust, upholding the rule of law, and preventing abuses of power. This requires a multi-layered approach.
- Independent oversight mechanisms: Establishing independent bodies to investigate allegations of misconduct and human rights violations is essential. These bodies need broad authority and access to information.
- Clear legal frameworks: Counterterrorism laws and policies should be clear, precise, and comply with international human rights standards. The use of force should be subject to strict legal constraints.
- Transparency in operations: Governments should be transparent about their counterterrorism strategies, operations, and the legal basis for their actions. This needs careful balance to protect national security.
- Mechanisms for redress: Victims of human rights abuses related to counterterrorism operations should have access to effective mechanisms for redress, including judicial remedies and compensation.
- International cooperation and standards: Collaboration among countries to share best practices and establish common standards for counterterrorism operations is necessary. International organizations can play a crucial role in monitoring and providing recommendations.
Accountability is not simply about punishing wrongdoing but also about preventing future abuses. It requires a culture of compliance with the rule of law and a commitment to transparency within security services. A failure to provide accountability can result in a loss of public confidence and create space for extremist narratives to thrive.
Q 27. Explain your experience with using different intelligence platforms.
My experience encompasses a wide range of intelligence platforms, both human and technical. I am proficient in:
- Human intelligence (HUMINT): This includes managing human sources, conducting interviews, and analyzing information obtained from confidential informants. This requires building rapport and trust with individuals who provide crucial information.
- Signals intelligence (SIGINT): I have experience in analyzing intercepted communications, including telephone calls, emails, and internet traffic. This requires technical expertise in signal processing and data analysis.
- Open-source intelligence (OSINT): I am skilled in gathering information from publicly available sources such as the internet, social media, news reports, and academic publications. OSINT is crucial in understanding the context and narrative used by terrorist groups.
- Geospatial intelligence (GEOINT): I have worked with satellite imagery, aerial photography, and maps to analyze terrain, infrastructure, and patterns of activity. This is important for planning operations and assessing risk.
- Measurement and Signature Intelligence (MASINT): My experience includes using various sensors to detect and analyze physical and electromagnetic signals, which are useful for detecting and tracking the movement of individuals and equipment.
I’m adept at integrating information from multiple sources to create a comprehensive intelligence picture. The effectiveness of intelligence analysis depends heavily on the ability to synthesize disparate data, identify patterns and make informed assessments.
Q 28. Describe your proficiency in risk assessment and mitigation.
Risk assessment and mitigation are fundamental to successful counterterrorism and counterinsurgency operations. My approach is systematic and involves:
- Identifying potential threats: This includes analyzing potential terrorist targets, assessing the capabilities of terrorist groups, and identifying vulnerabilities in security systems. This often involves threat modeling and scenario planning.
- Assessing the likelihood and impact of threats: A qualitative and quantitative assessment of the probability of an attack occurring and the potential consequences is crucial. This often involves the development of risk matrices.
- Developing mitigation strategies: This involves designing and implementing measures to reduce the likelihood and impact of threats. These strategies may include enhancing physical security, improving intelligence gathering, and strengthening community engagement.
- Implementing and monitoring mitigation measures: Effective implementation and regular monitoring of mitigation measures are essential to ensure their effectiveness. Regular reviews and updates are necessary to adapt to evolving threats.
- Continuous improvement: Regularly reviewing past incidents and near misses to identify areas for improvement in the risk assessment and mitigation process is vital. This helps refine procedures and improve outcomes.
For example, in assessing the risk of a terrorist attack on a public gathering, I would consider factors such as the target’s vulnerability, the terrorist group’s capabilities, and the local security environment. Mitigation strategies might involve enhanced security measures, increased surveillance, and improved community awareness campaigns.
Key Topics to Learn for Counterterrorism and Counterinsurgency Operations Interview
- Understanding the Threat Landscape: Analyzing terrorist and insurgent ideologies, motivations, and organizational structures. Developing strategies for identifying and assessing threats.
- Intelligence Gathering and Analysis: Utilizing various intelligence sources and methods (HUMINT, SIGINT, OSINT) to inform operational decisions. Practicing critical thinking and analytical skills to interpret complex data.
- Counterterrorism Strategies and Tactics: Exploring preemptive, preventative, and responsive counterterrorism measures. Understanding the ethical and legal considerations in counterterrorism operations.
- Counterinsurgency Doctrine and Principles: Applying COIN principles, such as population-centric approaches, legitimacy building, and the importance of hearts and minds. Understanding the role of civil-military cooperation.
- Operational Planning and Execution: Developing and implementing effective operational plans, considering risk assessment, resource allocation, and contingency planning. Understanding mission command and collaborative decision-making.
- Conflict Resolution and Peacebuilding: Exploring strategies for post-conflict stabilization and reconstruction. Understanding the role of reconciliation and transitional justice.
- Technological Applications: Utilizing technology in intelligence gathering, surveillance, and communication. Understanding the ethical implications of technological advancements in counterterrorism and counterinsurgency.
- Legal and Ethical Considerations: Navigating the complex legal and ethical frameworks governing counterterrorism and counterinsurgency operations. Understanding human rights and the rule of law.
Next Steps
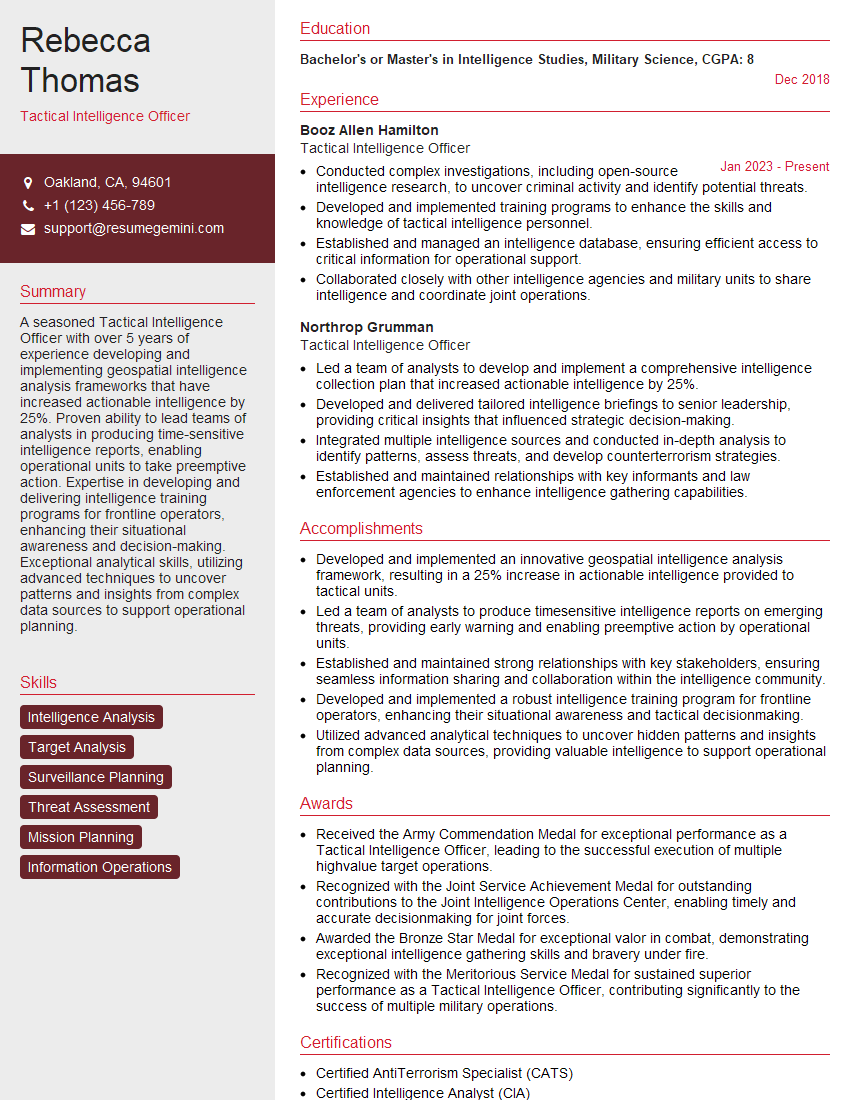
Mastering Counterterrorism and Counterinsurgency Operations opens doors to impactful and rewarding careers in national security and international affairs. A strong understanding of these crucial topics significantly enhances your candidacy and demonstrates your commitment to a challenging and vital field. To maximize your job prospects, it’s essential to create a compelling and ATS-friendly resume that showcases your skills and experience effectively. ResumeGemini is a trusted resource that can help you build a professional resume tailored to your unique qualifications. We provide examples of resumes specifically designed for Counterterrorism and Counterinsurgency Operations roles to guide you through the process. Invest time in crafting a standout resume – it’s your first impression and a critical step towards securing your desired position.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good