Interviews are opportunities to demonstrate your expertise, and this guide is here to help you shine. Explore the essential Intelligence Gathering and Assessment interview questions that employers frequently ask, paired with strategies for crafting responses that set you apart from the competition.
Questions Asked in Intelligence Gathering and Assessment Interview
Q 1. Explain the difference between OSINT, HUMINT, SIGINT, GEOINT, and MASINT.
Intelligence gathering relies on various sources and methods. The acronyms represent distinct disciplines:
- OSINT (Open-Source Intelligence): This involves collecting information from publicly available sources like news articles, social media, academic papers, and government websites. Think of it like a detective piecing together clues from a crime scene – except the ‘crime scene’ is the public domain. It’s about finding the relevant needles in the enormous haystack of publicly available data.
- HUMINT (Human Intelligence): This is the classic spycraft approach, relying on information gathered from human contacts. This could range from informants and spies providing classified information to casual conversations yielding valuable insights. Building trust and establishing rapport are crucial elements.
- SIGINT (Signals Intelligence): This focuses on intercepting and analyzing electronic signals, like communications, radar transmissions, and satellite signals. Think about intercepting encrypted messages, deciphering codes, or analyzing patterns in radio transmissions – a highly technical area needing specialized equipment and skills.
- GEOINT (Geospatial Intelligence): This uses imagery, maps, and geographic information systems (GIS) to analyze locations, terrain, and infrastructure. Satellite imagery, aerial photography, and even Google Maps can be powerful tools in identifying patterns, tracking movements, and understanding the context of events.
- MASINT (Measurement and Signature Intelligence): This is a more diverse category encompassing a broad range of intelligence gathered through technical means beyond SIGINT. Examples include analyzing acoustic signatures (sounds), electromagnetic signatures (EM emissions), nuclear radiation, or chemical traces. Often, this type of intelligence is used to confirm or refute information obtained from other sources.
In essence, each type of intelligence provides a unique perspective, and combining them (intelligence fusion) creates a more complete and accurate picture.
Q 2. Describe your experience with open-source intelligence gathering techniques.
My experience with OSINT is extensive. I’ve utilized a variety of techniques, including:
- Keyword Searches and Boolean Operators: I’m proficient in using advanced search operators (like AND, OR, NOT) to refine searches across multiple databases and websites, filtering out irrelevant results and focusing on precise information.
- Social Media Monitoring: I regularly analyze social media platforms like Twitter, Facebook, and LinkedIn to identify trends, sentiment, and potential threats. This includes tracking hashtags, monitoring specific accounts, and using social listening tools to gather insights.
- Web Scraping and Data Mining: I have experience using tools and programming languages (like Python with libraries like Beautiful Soup and Scrapy) to extract relevant data from websites and analyze large datasets to identify patterns and correlations.
- Deep Web and Dark Web Exploration (with appropriate ethical considerations): I understand the risks and regulations involved in accessing these areas and employ safe and ethical practices when exploring them for relevant information (with proper authorization).
- Open-Source Intelligence Aggregators: I utilize various platforms and tools that aggregate information from diverse sources, providing a consolidated view of relevant data.
For example, during a recent project, I used OSINT techniques to identify key personnel within a target organization by analyzing their LinkedIn profiles and news articles, which ultimately aided in forming a more complete understanding of their operations.
Q 3. How do you verify the credibility and reliability of intelligence sources?
Verifying the credibility and reliability of intelligence sources is paramount. I employ a multi-faceted approach:
- Source Triangulation: I always seek corroboration from multiple independent sources. If three different, unrelated sources confirm the same information, it’s more likely to be accurate.
- Source Evaluation: I assess the source’s reputation, expertise, potential biases, and track record. A known disinformation agent would carry less weight than an established journalist.
- Methodology Assessment: I examine how the information was gathered. Was it collected through firsthand observation, secondhand reporting, or inference? This allows for better understanding of its potential reliability.
- Contextual Analysis: I assess the information in the context of other known facts and intelligence. Does it fit with the broader picture or does it seem out of place?
- Fact-Checking and Verification: I utilize fact-checking websites, databases, and other resources to verify specific details and claims.
Think of it like a jury deliberating: multiple witnesses, different perspectives, and scrutiny of evidence are all required before reaching a verdict. Similarly, a robust verification process is essential for assessing the reliability of intelligence.
Q 4. Explain the process of intelligence fusion and analysis.
Intelligence fusion and analysis is the process of combining information from various sources and disciplines to develop a coherent understanding of a situation. It’s more than just compiling data; it’s about synthesizing it.
The process typically involves:
- Data Collection: Gathering information from all relevant sources (OSINT, HUMINT, SIGINT, etc.).
- Data Cleaning and Preprocessing: This involves standardizing formats, resolving inconsistencies, and eliminating duplicates.
- Data Integration: Combining data from disparate sources into a unified view.
- Analysis and Interpretation: Identifying patterns, trends, and anomalies in the integrated data.
- Assessment and Conclusion: Formulating an informed assessment and providing actionable intelligence.
- Visualization: Using charts, graphs, and maps to present findings clearly and effectively.
For instance, combining satellite imagery showing troop movements (GEOINT) with intercepted communications revealing operational plans (SIGINT) and reports from human sources (HUMINT) paints a far richer picture than any single data source could offer.
Q 5. How do you identify and assess potential threats or risks?
Identifying and assessing potential threats and risks is an iterative process that leverages various techniques:
- Threat Modeling: This involves systematically identifying potential threats, analyzing their likelihood and impact, and developing mitigation strategies. This often involves brainstorming sessions and ‘what-if’ scenarios.
- Risk Assessment: Quantifying the likelihood and potential impact of identified threats to determine the level of risk. This frequently uses a matrix to categorize risk based on severity.
- Vulnerability Analysis: Identifying weaknesses or vulnerabilities that could be exploited by adversaries. This often involves penetration testing or cybersecurity assessments.
- Scenario Planning: Developing multiple possible future scenarios to anticipate potential outcomes and prepare for various contingencies.
- Early Warning Systems: Establishing systems to detect emerging threats and provide timely warnings.
For example, analyzing OSINT regarding cyber activity, combined with vulnerability assessments of our systems, allows us to proactively identify potential cyber threats before they escalate into incidents.
Q 6. Describe your experience with data analysis and visualization techniques relevant to intelligence.
My experience with data analysis and visualization is extensive. I’m proficient in using various tools and techniques, including:
- Statistical Analysis: Employing statistical methods to identify patterns, trends, and correlations within datasets.
- Data Mining and Machine Learning: Using algorithms to identify anomalies and predict future events based on historical data (with appropriate ethical considerations).
- Data Visualization Tools: Proficient in using tools like Tableau, Power BI, and Python libraries like Matplotlib and Seaborn to create informative and compelling visualizations.
- Geographic Information Systems (GIS): Using GIS software to map and analyze geospatial data, facilitating the identification of spatial patterns and relationships.
- Network Analysis: Using network graphs to visualize relationships between entities, helping identify key players and information flows.
For instance, in one project, I used network analysis to visualize communication patterns within a suspected criminal organization, revealing key individuals and their relationships. This visualization helped prioritize investigation efforts.
Q 7. How do you handle conflicting or contradictory intelligence information?
Handling conflicting or contradictory intelligence information requires a meticulous and systematic approach:
- Identify and Document Discrepancies: Carefully note all inconsistencies and contradictions between different sources.
- Re-evaluate Sources: Reassess the credibility and reliability of each source in light of the discrepancies. Consider potential biases or motivations.
- Seek Additional Information: Gather more information to help resolve the conflicts. This may involve collecting additional data from other sources or revisiting existing sources to clarify ambiguities.
- Contextual Analysis: Analyze the information within its broader context. Which piece of information aligns better with the overall picture?
- Develop Multiple Hypotheses: Formulate competing hypotheses based on the contradictory information to explore various possibilities.
- Qualitative Assessment: Incorporate qualitative judgments based on experience and expertise to weigh the conflicting evidence.
Sometimes, the solution lies not in choosing one piece of information over another, but in recognizing that the truth might be more nuanced than initially presented. Accepting ambiguity is a crucial aspect of intelligence analysis.
Q 8. Explain your understanding of the intelligence cycle.
The intelligence cycle is a fundamental framework for how intelligence is gathered, processed, and disseminated. It’s a continuous loop, not a linear process, and typically consists of five key phases: Planning & Direction, where intelligence needs are identified and prioritized; Collection, where raw data is gathered from various sources (human intelligence, signals intelligence, etc.); Processing, where collected data is organized, analyzed, and evaluated for relevance; Analysis & Production, where information is interpreted and turned into actionable intelligence; and finally, Dissemination, where intelligence products are shared with relevant decision-makers.
Imagine it like baking a cake: Planning is deciding what kind of cake to make; Collection is gathering the ingredients; Processing is preparing those ingredients; Analysis is the actual baking; and Dissemination is serving the cake.
- Planning & Direction: Defining the intelligence requirements (IRs) based on policy needs.
- Collection: Utilizing HUMINT (Human Intelligence), SIGINT (Signals Intelligence), IMINT (Imagery Intelligence), OSINT (Open-Source Intelligence), MASINT (Measurement and Signature Intelligence), etc.
- Processing: Cleaning, organizing, and storing the collected data.
- Analysis & Production: Transforming raw data into meaningful intelligence assessments.
- Dissemination: Delivering the finished intelligence product to the end-user (policymakers, military commanders etc.).
Q 9. How would you prioritize intelligence requirements in a high-pressure situation?
Prioritizing intelligence requirements in a high-pressure situation demands a structured approach. I’d utilize a method combining urgency and importance. A simple matrix would help: plotting each requirement’s urgency (how quickly it’s needed) against its importance (its impact on the overall mission or objective). High-urgency, high-importance requirements get immediate attention; high-urgency, low-importance may need quick assessments to ensure they don’t distract from higher priorities; low-urgency, high-importance can be scheduled for later, with contingency plans in place. This helps ensure crucial intelligence needs are addressed first.
For example, during a potential terrorist attack, identifying the suspect’s location and immediate plans would be high-urgency, high-importance; while gathering detailed biographical information on the suspect might be high-importance but less urgent and therefore tackled after the immediate threat is addressed. Constant reassessment is vital as the situation evolves.
Q 10. Describe your experience with using intelligence analysis tools and technologies.
My experience includes proficiency in various intelligence analysis tools and technologies. I’m comfortable using geospatial intelligence (GEOINT) software for analyzing satellite imagery and mapping, link analysis tools to identify connections between individuals or organizations, and data mining software to sift through large datasets for patterns and anomalies. I’ve also used various databases and information retrieval systems to locate and access relevant information. In a previous role, I utilized Palantir Gotham for visualizing complex datasets and identifying relationships between seemingly disparate pieces of information. The software’s ability to integrate data from multiple sources and facilitate collaborative analysis was incredibly valuable.
Q 11. How do you maintain the confidentiality and security of sensitive intelligence information?
Maintaining confidentiality and security of sensitive intelligence information is paramount. My approach involves strict adherence to established security protocols, including access control measures (need-to-know basis), secure data storage and transmission methods (encryption), and regular security awareness training. I’m meticulous in handling classified information, using secure communication channels, and ensuring all physical and digital materials are appropriately protected. Regular audits and vulnerability assessments help identify and address potential weaknesses.
Think of it like handling highly sensitive financial documents – using secure vaults, strong passwords, and regular review to prevent access by unauthorized individuals.
Q 12. Explain your understanding of different intelligence methodologies and frameworks.
My understanding encompasses a range of intelligence methodologies and frameworks. These include the use of structured analytical techniques (like hypothesis generation, competitor analysis, and red teaming), all source intelligence fusion (combining different intelligence types for a more complete picture), and the application of various analytical models, depending on the context and the information available. I’m familiar with frameworks such as the Diamond Model of intrusion analysis which helps visualize attack phases. I also incorporate geopolitical theories and historical analysis to create more accurate predictions and assessments.
For example, understanding the strengths and weaknesses of different methodologies helps avoid biases when analyzing data. One approach might be better suited for a specific scenario than others. Using only one methodology and overlooking others can lead to inaccurate conclusions.
Q 13. How do you communicate complex intelligence findings to a non-technical audience?
Communicating complex intelligence findings to a non-technical audience requires a clear, concise, and accessible approach. I avoid jargon and technical terms, using plain language and visuals (charts, graphs, maps) to illustrate key points. I tailor my communication style to the audience, focusing on the ‘so what?’ – the implications and significance of the findings for their specific needs. I use analogies and real-world examples to make the information relatable and understandable. The objective is to provide actionable intelligence that is easy to grasp and apply.
For example, instead of saying “the adversary’s cyber infrastructure exhibits high levels of resilience due to obfuscation techniques and distributed network architecture,” I’d explain “their online defenses are very strong and spread out, making them hard to attack.”
Q 14. Describe a situation where you had to make a critical decision based on incomplete intelligence.
In a previous assignment, we were tasked with assessing the imminent threat level posed by an armed group in a volatile region. We had limited intelligence due to constraints in human sources and restricted access to certain areas. Using the available information – fragmented reports from unreliable sources, intercepted communications, and some open-source material – we generated several possible scenarios, each with assigned probabilities based on available evidence. We also identified key intelligence gaps that required further investigation. Based on this incomplete but structured analysis, we recommended a cautious approach that prioritized risk mitigation while simultaneously working to gather more intelligence. The cautious response proved to be correct, while the additional intelligence gathering efforts subsequently corroborated our initial assessment. Although the intelligence was incomplete, the process of structured analysis and acknowledging uncertainties allowed for a responsible and successful decision-making process.
Q 15. How do you identify and mitigate biases in intelligence analysis?
Identifying and mitigating bias in intelligence analysis is crucial for producing objective and reliable assessments. Bias, stemming from personal beliefs, cultural background, or even the information sources themselves, can significantly distort our understanding of events. We combat this through a multi-pronged approach.
- Structured Analytical Techniques: Techniques like the Analysis of Competing Hypotheses (ACH) force analysts to systematically consider multiple explanations for an event, rather than prematurely settling on a single, potentially biased, interpretation. This involves listing all plausible hypotheses, identifying evidence supporting and contradicting each, and then evaluating the relative likelihood of each hypothesis.
- Cross-referencing and Triangulation: We rely heavily on corroborating information from multiple independent sources. If three unrelated sources point to the same conclusion, it increases the confidence in the assessment. Contradictory information necessitates further investigation to understand the discrepancies.
- Devil’s Advocacy: This involves assigning someone the role of challenging the prevailing analysis, actively searching for weaknesses and alternative interpretations. This process helps unearth potential biases and hidden assumptions.
- Awareness and Self-Reflection: Analysts must be acutely aware of their own biases and how they might influence their analysis. Regular self-reflection and training programs focusing on cognitive biases are essential.
For example, during an analysis of a potential political uprising, I might consciously challenge my own preconceived notions about the motivations of the involved groups. By systematically considering diverse viewpoints and seeking evidence that contradicts my initial assumptions, I ensure a more balanced and unbiased assessment.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. What are some ethical considerations in intelligence gathering and assessment?
Ethical considerations are paramount in intelligence gathering and assessment. We operate within a strict ethical framework, guided by principles of legality, proportionality, and necessity.
- Legality: All intelligence activities must comply with national and international laws. This includes respecting privacy rights, avoiding illegal surveillance, and adhering to proper procedures for data collection and handling.
- Proportionality: The means used to gather intelligence should be proportional to the threat or objective. Intrusive methods should only be employed when absolutely necessary and justified.
- Necessity: Intelligence gathering must be necessary to protect national security or other legitimate interests. It shouldn’t be conducted out of mere curiosity or for improper purposes.
- Privacy and Data Protection: The privacy of individuals must be respected. Data collected should be handled responsibly, securely stored, and used only for authorized purposes. Compliance with data protection regulations is crucial.
- Transparency and Accountability: Intelligence agencies should be transparent (where security permits) and accountable for their actions. Effective oversight mechanisms are needed to prevent abuse.
A real-world example involves balancing the need to gather intelligence on terrorist threats against the right to privacy. We must carefully consider the potential impact on innocent individuals and ensure that our methods are both effective and ethically justifiable.
Q 17. Describe your experience with report writing and intelligence briefings.
I have extensive experience in writing intelligence reports and delivering briefings. My reports are structured to be clear, concise, and easily digestible, even for non-experts. They typically follow a standard format, including an executive summary, background information, analysis, conclusions, and recommendations. I am proficient in tailoring my writing style and level of detail based on the intended audience.
In briefings, I emphasize clear communication and visual aids to support my findings. I practice active listening to ensure the audience understands the information and can ask questions. I’ve found that effective visual communication through maps, charts, and graphs enhances comprehension and memorability. I also emphasize anticipating potential questions and preparing answers in advance. One particular briefing I remember involved presenting complex financial data related to a potential sanctions evasion scheme in a clear and accessible way to senior policymakers who might not have a strong financial background. Using illustrative charts and avoiding technical jargon, I was able to effectively communicate the findings.
Q 18. How do you stay up-to-date on current events and intelligence trends?
Staying abreast of current events and intelligence trends is a critical aspect of my work. I employ a multifaceted approach:
- News Monitoring: I regularly consume news from diverse reputable sources, both domestic and international, to maintain a broad understanding of the global landscape. This includes reputable news agencies, academic journals, and think tanks.
- Open-Source Intelligence (OSINT) tools: I utilize various OSINT platforms and tools to monitor social media, online forums, and other publicly available information. This provides valuable insights into public opinion, emerging trends, and potential threats.
- Intelligence Community Publications: I closely follow reports and publications from official intelligence agencies and relevant governmental bodies, providing insights into their assessments and priorities.
- Professional Networking: Engaging in professional development activities, attending conferences, and participating in relevant online communities allows me to learn from colleagues and experts in the field.
- Specialized Databases and Journals: Access to specialized databases containing academic papers, industry reports, and geopolitical analyses keeps me informed about cutting-edge research and emerging trends.
For example, during a recent analysis of cybersecurity threats, I monitored online forums frequented by hackers and leveraged OSINT tools to identify potential vulnerabilities in critical infrastructure. Combining this information with official cybersecurity advisories gave me a comprehensive picture of the threat landscape.
Q 19. What are the key characteristics of a successful intelligence analyst?
A successful intelligence analyst possesses a unique blend of skills and characteristics:
- Analytical Skills: Ability to critically evaluate information, identify patterns, draw inferences, and develop sound conclusions. This includes strong critical thinking and problem-solving skills.
- Research Skills: Proficiency in gathering, evaluating, and synthesizing information from diverse sources. This includes using both open-source and classified information.
- Writing and Communication Skills: Ability to clearly and concisely communicate complex information to a diverse audience through both written reports and oral briefings.
- Adaptability and Flexibility: Ability to adjust analytical approaches and work effectively in dynamic and rapidly evolving situations.
- Attention to Detail: Meticulous attention to detail in data collection, analysis, and reporting is critical to avoid errors.
- Objectivity and Impartiality: Ability to analyze information objectively, minimizing personal biases and preconceived notions.
- Intellectual Curiosity: A strong desire to understand complex issues and a willingness to explore new perspectives.
A successful analyst is also a lifelong learner, continuously updating their knowledge and skillset to keep pace with the ever-changing world of intelligence.
Q 20. How do you adapt your intelligence gathering approach to different contexts and situations?
Adapting my intelligence gathering approach depends heavily on the context and situation. The techniques used for assessing a transnational criminal organization will differ significantly from analyzing a potential political coup in a foreign country.
- Identifying Key Variables: I begin by clearly defining the objective of the intelligence gathering and identifying the key variables and factors influencing the situation. This helps to focus the analysis and avoid getting bogged down in irrelevant details.
- Selecting Appropriate Sources: The choice of sources is critical. For example, in assessing a domestic political climate, surveys, social media analysis, and news reports might be crucial; whereas in investigating a cross-border smuggling operation, confidential informants and law enforcement databases may be more pertinent.
- Employing Diverse Methods: A flexible approach might involve combining open-source intelligence, human intelligence, signals intelligence, and geospatial intelligence, depending on the specific requirements.
- Risk Assessment: A critical component involves a careful assessment of risks and potential threats associated with each method of intelligence gathering. Security protocols must be followed to protect sources and information.
For instance, when analyzing a natural disaster’s impact, I might utilize satellite imagery (geospatial intelligence), social media posts (OSINT), and reports from relief agencies (human intelligence) to understand the extent of the damage and humanitarian needs.
Q 21. Explain your experience with using geospatial intelligence tools and technologies.
I have considerable experience utilizing geospatial intelligence (GEOINT) tools and technologies. GEOINT provides a crucial visual context for understanding events and situations. My experience spans various software and platforms.
- Software Proficiency: I am proficient in using Geographic Information Systems (GIS) software such as ArcGIS and QGIS to analyze satellite imagery, maps, and other geospatial data. This includes creating thematic maps, conducting spatial analysis, and integrating data from multiple sources.
- Data Analysis: I can effectively interpret and analyze geospatial data, including satellite imagery, aerial photographs, and digital elevation models (DEMs). This allows for identifying patterns, trends, and anomalies.
- Imagery Interpretation: I possess skills in analyzing imagery to identify infrastructure, terrain features, movement patterns, and other relevant details. This involves using various image enhancement and analysis techniques.
- Data Integration: I can effectively integrate geospatial data with other intelligence sources, such as human intelligence (HUMINT) or signals intelligence (SIGINT), to build a more comprehensive understanding of a situation. For instance, by combining satellite imagery showing troop movements with HUMINT reports from informants, I can build a more detailed picture of the situation and potential future actions.
In a recent case, the use of high-resolution satellite imagery helped to confirm the location of a suspected weapons cache, thereby supporting a law enforcement operation. By layering imagery with intelligence from other sources, we were able to pinpoint the exact location and plan a successful raid.
Q 22. Describe your understanding of network analysis techniques in intelligence gathering.
Network analysis, in the context of intelligence gathering, is the systematic examination of relationships between individuals, groups, organizations, or entities to understand their interactions and structures. It’s like mapping out a complex social web to identify key players, patterns, and potential threats or vulnerabilities. We use various techniques to visualize and analyze these networks, uncovering hidden connections that might otherwise be missed.
Common methods include:
- Social Network Analysis (SNA): This involves mapping relationships between individuals, identifying central figures (hubs), clusters (communities), and the flow of information or resources.
- Link Analysis: This focuses on identifying the connections between different pieces of information, such as websites, documents, or individuals, to uncover patterns and associations. For example, we might trace the digital footprint of a suspected terrorist cell by analyzing their online communications and connections.
- Graph Databases: These are specialized databases designed to store and query network data efficiently, allowing us to perform complex analysis on large datasets.
For example, imagine investigating a drug trafficking ring. Network analysis would allow us to map the connections between drug dealers, suppliers, money launderers, and other involved parties. By visualizing the network, we can identify key figures, understand the flow of drugs and money, and develop effective strategies to disrupt the operation.
Q 23. How do you evaluate the effectiveness of intelligence gathering operations?
Evaluating the effectiveness of intelligence gathering operations requires a multifaceted approach that considers both the quality of the intelligence produced and the impact it has on decision-making. We need to ensure the information is accurate, timely, relevant, and complete. This evaluation can be done both quantitatively and qualitatively.
- Quantitative Measures: These include things like the number of actionable intelligence reports produced, the accuracy of predictions, and the number of successful operations based on the intelligence provided. For example, we can track the number of times our intel led to successful arrests or the prevention of a criminal act.
- Qualitative Measures: These are more subjective and focus on assessing the impact of the intelligence on policy decisions, operational success, and resource allocation. This would include things like reviewing post-operation reports to determine how well intelligence guided the mission.
- Feedback Loops: Establishing feedback mechanisms with intelligence consumers (analysts, policymakers, etc.) is crucial to understanding how our intelligence is used and improving future operations.
A key aspect is comparing the intelligence we gather with the actual events. Did our predictions hold true? If not, why not? This analysis allows us to improve our methods and techniques for future intelligence gathering missions.
Q 24. Explain your experience in using social media for intelligence gathering.
Social media platforms have become indispensable tools for intelligence gathering. They provide a vast, readily available source of information about individuals, groups, and events. However, it requires careful and ethical use.
My experience involves using social media to:
- Monitor public sentiment and opinion: Understanding public attitudes towards certain events or issues is vital in many scenarios. For example, monitoring social media posts related to a political event can provide insights into public reaction and potential threats.
- Identify and track individuals and groups: Social media profiles can provide a wealth of information on individuals, including their affiliations, beliefs, and activities. This data can be helpful in investigating potential threats.
- Open-source intelligence (OSINT) gathering: Social media is a rich source of open-source intelligence, providing data that can be corroborated with other sources.
- Identify disinformation campaigns: Recognizing and analyzing the spread of misinformation and propaganda through social media is crucial.
However, it’s crucial to remember that social media data is often incomplete, biased, and can be easily manipulated. Verification and triangulation with other sources are essential to avoid drawing inaccurate conclusions. Additionally, ethical considerations and legal frameworks surrounding data privacy and collection must be strictly adhered to.
Q 25. Describe your understanding of the legal and regulatory frameworks governing intelligence gathering.
The legal and regulatory frameworks governing intelligence gathering are complex and vary significantly across jurisdictions. These frameworks balance the need for national security with the protection of individual rights and freedoms. Key considerations include:
- Constitutional Rights: The Fourth Amendment (in the US) protects against unreasonable searches and seizures, and similar rights exist in other countries. Intelligence gathering must comply with these fundamental rights.
- Privacy Laws: Laws such as the Privacy Act (in the US) and the GDPR (in Europe) regulate the collection, use, and storage of personal data. Intelligence agencies must comply with these laws while collecting information.
- Surveillance Laws: Specific laws govern the use of surveillance technologies, such as wiretapping and electronic monitoring. These laws often require warrants or other legal authorizations.
- Foreign Intelligence Surveillance Act (FISA) (US): This law establishes procedures for the electronic surveillance of foreign powers and their agents within the United States.
My understanding of these frameworks is critical to ensuring all intelligence activities are conducted legally and ethically, upholding the rule of law while fulfilling our intelligence mission.
Q 26. How would you approach an intelligence requirement with limited resources?
Approaching an intelligence requirement with limited resources necessitates a prioritization strategy focused on efficiency and effectiveness. The key is to focus our efforts on the most critical information and use innovative, cost-effective methods.
- Prioritize Intelligence Requirements: Clearly define the most crucial questions that need to be answered and focus resources on those. The Pareto principle (80/20 rule) can be a useful guide here.
- Leverage Open-Source Intelligence (OSINT): OSINT is freely available information and can drastically reduce the need for expensive covert operations. Social media, news articles, government reports, and academic publications can provide valuable insights.
- Collaboration and Partnerships: Working with other organizations or agencies can provide access to resources and expertise that we might lack. This approach increases efficiency and cost-effectiveness.
- Employ cost-effective methodologies: Prioritize methods that are inexpensive and efficient, like thorough analysis of publicly available information.
- Focus on Human Intelligence (HUMINT): Although riskier, well-placed HUMINT sources can often provide vital intelligence without heavy financial investment, but this should be carefully assessed for risk and legal compliance.
For example, if investigating a suspected arms smuggling operation with limited funds, we might initially focus on OSINT to identify potential suspects and routes. This would be followed by prioritizing HUMINT sources with proven reliability to fill in the gaps.
Q 27. How do you manage competing priorities and deadlines in an intelligence gathering role?
Managing competing priorities and deadlines in intelligence gathering requires a structured and organized approach. Effective time management and prioritization skills are paramount.
- Prioritization Matrix: Use a prioritization matrix (like Eisenhower Matrix: Urgent/Important) to categorize tasks based on urgency and importance. Focus on high-impact, high-priority tasks first.
- Project Management Techniques: Employing project management tools and techniques like Gantt charts or Kanban boards can help visualize progress, manage timelines, and track dependencies.
- Effective Communication: Open and transparent communication with stakeholders about priorities and potential delays is essential to avoid conflicts and maintain trust.
- Delegation: When possible, delegate tasks to team members with appropriate expertise to free up time for more critical responsibilities.
- Regular Review and Adjustment: Continuously monitor progress, adjust plans as needed, and remain flexible to adapt to changing circumstances.
Think of it like conducting an orchestra—every instrument (task) has its own part, but the conductor (intelligence manager) must ensure harmony and synchronization. This often means making difficult choices, prioritizing tasks based on their impact, and adjusting the tempo as needed.
Q 28. Describe your understanding of predictive policing and its implications.
Predictive policing uses data analysis and statistical modeling to anticipate crime hotspots and potential criminal activity. It leverages historical crime data, demographic information, and other relevant factors to predict where and when crime is likely to occur. This can help allocate police resources more effectively.
Implications:
- Improved Resource Allocation: Predictive policing can help law enforcement agencies allocate resources (officers, patrols) more effectively to areas with a higher predicted crime risk.
- Potential for Bias: If the data used to train predictive models reflects existing biases in policing (e.g., disproportionate targeting of certain communities), the models can perpetuate and amplify these biases.
- Privacy Concerns: The use of large datasets containing personal information raises significant privacy concerns. Ensuring data security and minimizing the risk of data breaches is critical.
- Ethical Considerations: The potential for preemptive policing and the targeting of individuals based on predictions raises ethical questions about fairness, due process, and potential for self-fulfilling prophecies.
It’s important to remember that predictive policing is a tool, not a solution. Its effectiveness depends heavily on the quality and representativeness of the data used, as well as ethical implementation and ongoing evaluation to minimize biases and safeguard privacy. It should be used responsibly and transparently, with appropriate oversight and community engagement.
Key Topics to Learn for Intelligence Gathering and Assessment Interview
- Intelligence Cycle: Understand the complete intelligence cycle – from planning and collection to analysis, dissemination, and feedback. Consider its practical application in various scenarios.
- Collection Methods: Explore diverse intelligence gathering methods, including open-source intelligence (OSINT), human intelligence (HUMINT), signals intelligence (SIGINT), and geospatial intelligence (GEOINT). Practice analyzing the strengths and weaknesses of each method and how to integrate them effectively.
- Source Evaluation and Credibility Assessment: Develop a strong understanding of techniques for evaluating the reliability and credibility of intelligence sources. Be prepared to discuss how you would assess biases and potential misinformation.
- Analytical Techniques: Familiarize yourself with various analytical methods such as structured analytic techniques (SATs), hypothesis generation and testing, and developing competing hypotheses. Practice applying these techniques to hypothetical scenarios.
- Report Writing and Presentation: Master the art of concise, clear, and persuasive intelligence reporting. Practice structuring your reports logically and presenting your findings effectively – both verbally and in writing.
- Ethical Considerations: Demonstrate awareness of the ethical implications of intelligence gathering and assessment. Understand the legal and moral boundaries of the profession and the importance of responsible data handling.
- Technological Tools and Applications: Explore the role of technology in modern intelligence gathering and assessment. Familiarize yourself with relevant software and tools used for data analysis and visualization.
Next Steps
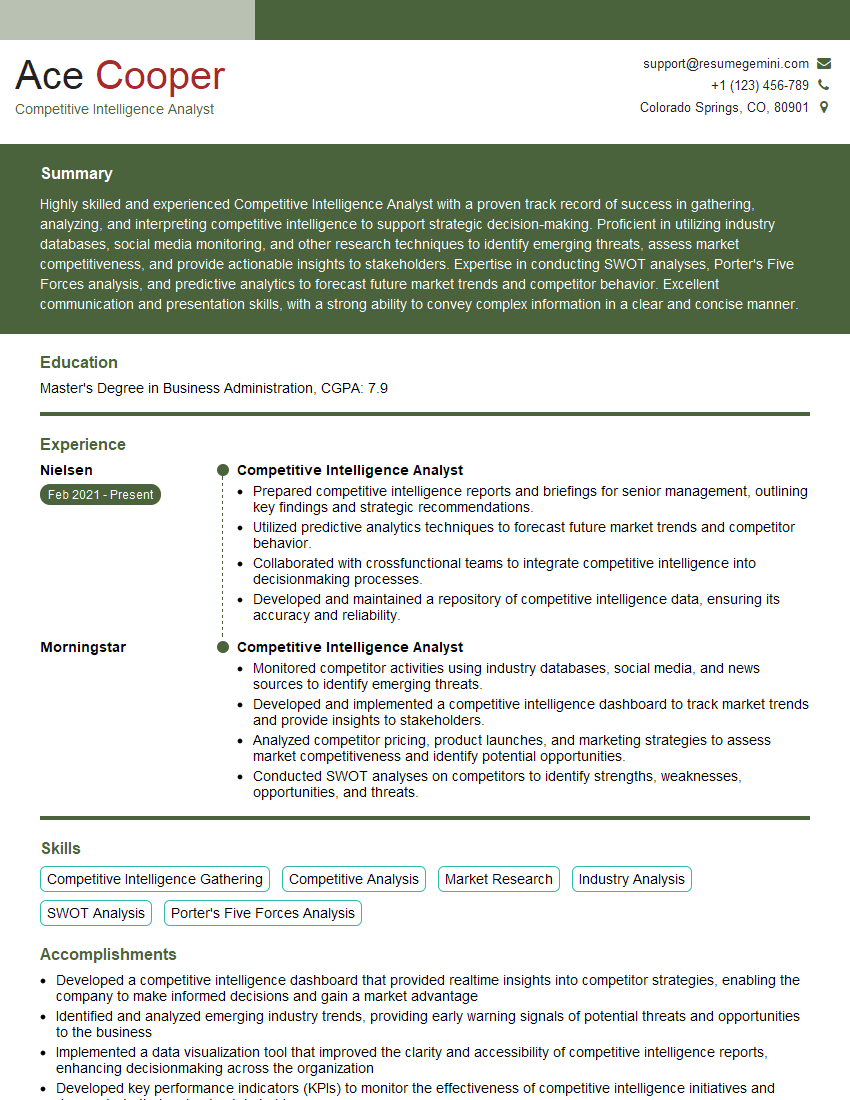
Mastering Intelligence Gathering and Assessment opens doors to exciting and impactful careers, offering opportunities for growth and significant contributions. To stand out in a competitive job market, a well-crafted, ATS-friendly resume is crucial. ResumeGemini is a trusted resource that can help you build a professional resume that highlights your skills and experience effectively. Examples of resumes tailored to Intelligence Gathering and Assessment are available to guide you through the process. Invest time in crafting a compelling resume; it’s your first impression on potential employers.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good