Are you ready to stand out in your next interview? Understanding and preparing for Product Safety Databases interview questions is a game-changer. In this blog, we’ve compiled key questions and expert advice to help you showcase your skills with confidence and precision. Let’s get started on your journey to acing the interview.
Questions Asked in Product Safety Databases Interview
Q 1. Explain your experience with different types of Product Safety Databases (e.g., relational, NoSQL).
My experience spans both relational and NoSQL databases in the context of product safety. Relational databases, like PostgreSQL or MySQL, are excellent for structured data with well-defined relationships between different product attributes (e.g., product ID, manufacturer, reported incidents). Their strength lies in data integrity and ACID properties (Atomicity, Consistency, Isolation, Durability), crucial for maintaining accurate safety records. I’ve used them extensively to build systems managing product recalls, incident reports, and compliance certifications. On the other hand, NoSQL databases, such as MongoDB or Cassandra, are valuable for handling semi-structured or unstructured data, like free-text incident reports or sensor data from connected products. Their scalability and flexibility make them suitable for handling large volumes of diverse data, especially when dealing with real-time monitoring or IoT-generated information. In one project, we used a hybrid approach: a relational database for core product information and a NoSQL database for handling the massive influx of sensor data associated with potential safety issues. This allowed for efficient querying of structured data while also accommodating the flexibility needed for unstructured sensor streams.
Q 2. Describe your proficiency in SQL and its application in querying and manipulating product safety data.
My SQL proficiency is quite advanced. I’m adept at writing complex queries to extract, analyze, and manipulate product safety data. For example, I can use SELECT, JOIN, WHERE, GROUP BY, and HAVING clauses to identify trends in reported incidents, pinpoint faulty batches, or track the effectiveness of recall campaigns. I frequently employ window functions for tasks such as ranking products based on incident severity or calculating moving averages of defect rates. Furthermore, I’m comfortable with stored procedures for automating data processing tasks and ensuring data consistency. For instance, I’ve developed stored procedures to automatically update product safety status based on incoming incident reports and trigger alerts when specific thresholds are breached. My expertise also extends to data optimization techniques like indexing and query planning to ensure efficient data retrieval, even with very large datasets.
SELECT COUNT(*) FROM Incidents WHERE ProductID = 1234 AND IncidentSeverity = 'Critical';This simple query, for instance, allows me to quickly count the number of critical incidents associated with a specific product ID.
Q 3. How do you ensure data integrity and accuracy within a Product Safety Database?
Data integrity and accuracy are paramount in product safety databases. I employ several strategies to ensure this. Firstly, I implement strict data validation rules at the application level and within the database itself, using constraints like NOT NULL, UNIQUE, CHECK, and foreign key constraints in relational databases. Secondly, regular data audits and quality checks are performed using both automated scripts and manual reviews. These processes involve comparing data against external sources (e.g., regulatory databases) and verifying the consistency of information across different tables. Finally, version control and change tracking are essential. Every data modification is logged, allowing us to trace changes and revert to previous versions if necessary. Think of it like a meticulous audit trail for every piece of safety-critical information. This meticulous approach ensures the highest level of confidence in the data’s accuracy and reliability.
Q 4. What methods do you use to identify and resolve data inconsistencies or errors?
Identifying and resolving data inconsistencies is a multi-faceted process. I often start by using SQL queries to detect anomalies, such as duplicate entries, missing values, or inconsistencies across related tables. For example, I might use queries to find products with conflicting information in different data sources or identify reports with missing critical fields. Automated data profiling tools can significantly streamline this process. After identification, I use a combination of techniques to correct inconsistencies. For duplicates, I may consolidate records, resolving conflicts using predefined business rules or manual review. For missing values, I might employ data imputation techniques based on statistical analysis or domain expertise. Data cleansing processes often involve scripting and potentially custom-built tools to automate repetitive tasks.
Q 5. Explain your understanding of data validation techniques in the context of product safety.
Data validation in product safety is crucial for preventing inaccuracies that could lead to serious consequences. It involves several steps. Firstly, defining clear data standards and validation rules before data entry. This might include range checks (e.g., ensuring a weight value falls within a reasonable range), format checks (e.g., validating date formats), and data type checks (e.g., verifying that a field is indeed numerical). Secondly, implementing input validation at the application level to prevent invalid data from entering the database. This is done via form validation and data sanitization. Thirdly, employing database constraints to enforce data integrity at the database level. This ensures data consistency, even if validation at the application level is bypassed. Finally, regular validation checks (automated or manual) are crucial to identify and correct any anomalies that might arise over time.
Q 6. How do you handle data security and compliance within a Product Safety Database?
Data security and compliance are paramount in product safety databases. We employ a multi-layered approach to ensure the confidentiality, integrity, and availability of sensitive data. This includes access control mechanisms using role-based permissions, encrypting data both in transit and at rest, regular security audits and penetration testing to identify vulnerabilities, and implementing robust backup and disaster recovery plans. We strictly adhere to relevant regulations like GDPR, CCPA, and industry-specific standards. Data anonymization techniques are used where appropriate to protect sensitive personal information. Regular security awareness training for all personnel involved in handling the data is also an essential component. A robust incident response plan is in place to manage and mitigate any security breaches that might occur.
Q 7. Describe your experience with data migration and integration within Product Safety Databases.
I have extensive experience with data migration and integration within product safety databases. This typically involves migrating data from legacy systems to modern platforms, consolidating data from multiple sources, or integrating new data streams. The process begins with a thorough assessment of the source and target systems, defining a clear migration plan with well-defined data mapping and transformation rules. I employ ETL (Extract, Transform, Load) tools and processes to perform the data migration. Data quality checks and validation are done at each stage to ensure data integrity. During integration with other systems, I utilize APIs and middleware solutions to ensure seamless data exchange and maintain data consistency across different platforms. Thorough testing, including unit and integration testing, is conducted before deploying any changes to the production environment. Change management processes are also in place to document all migrations and integrations.
Q 8. What are your preferred methods for data backup and recovery in a Product Safety Database environment?
Data backup and recovery in a Product Safety Database is paramount. We employ a multi-layered approach, mirroring the principle of redundancy for maximum protection. Think of it like having multiple copies of your most important documents stored in different, safe locations.
Regular Backups: We perform automated, incremental backups daily, with full backups weekly, using a robust backup solution. This ensures that we can quickly restore data to a specific point in time.
Offsite Storage: Backups are stored offsite, in a geographically separate location, protecting against local disasters like fires or power outages. Cloud storage or a dedicated disaster recovery site are common choices.
Version Control: We implement version control to track changes to the database, allowing us to revert to previous versions if needed. This is akin to having different versions of a document saved, enabling you to retrieve earlier drafts.
Testing and Validation: Regular testing of the backup and recovery procedures is crucial. We conduct simulated disaster recovery exercises to validate the entire process and ensure our recovery time objectives (RTO) and recovery point objectives (RPO) are met. This ensures our preparedness for real-world events.
Q 9. How do you ensure data accessibility and usability for various stakeholders?
Data accessibility and usability are achieved through a combination of strategies, carefully designed to cater to the needs of diverse stakeholders, including engineers, regulatory compliance officers, and legal teams. Think of it as building a well-organized library with different sections for different users.
Role-Based Access Control (RBAC): We use RBAC to restrict access to sensitive data based on user roles. This ensures that only authorized personnel can access specific information. This is like having different access levels to a building – some people have keys to all floors, while others are restricted to specific areas.
User-Friendly Interface: The database interface is designed to be intuitive and user-friendly, making it easy for various stakeholders to access and analyze data, regardless of their technical expertise. This aims to avoid ‘information overload’ and ensures information is presented in an accessible manner.
Data Export Capabilities: We provide options for exporting data in various formats (CSV, Excel, PDF) allowing stakeholders to use their preferred tools for analysis and reporting. This grants flexibility depending on the stakeholder’s technical preferences.
Secure Data Sharing: Secure methods for sharing data with external partners or regulatory bodies are implemented, adhering to strict data privacy and security guidelines. This involves secure file transfer protocols and adherence to all relevant regulations.
Q 10. Explain your experience with report generation and data visualization from Product Safety Databases.
Report generation and data visualization are essential aspects of effectively communicating product safety insights. Think of this as translating raw data into meaningful stories that reveal trends and patterns.
Customizable Reports: We utilize reporting tools to create customizable reports on various safety metrics, including incident rates, defect analysis, and recall effectiveness. This gives stakeholders the ability to generate reports specific to their needs.
Data Visualization: Interactive dashboards and charts are used to visualize data, making it easier to understand complex patterns and trends. For instance, a geographical map showing the distribution of incidents can quickly highlight potential regional problems.
Automated Reporting: Automated report generation simplifies routine tasks, freeing up time for more in-depth analysis. Scheduled reports help track key metrics continuously, which helps maintain a proactive approach to safety management.
Data Export Options: Ability to export reports in various formats (PDF, Excel, PowerPoint) enhances communication with various stakeholders, depending on their preferred methods of receiving data.
Q 11. Describe your experience with different data analysis techniques used in product safety.
Various data analysis techniques are employed in product safety, ranging from descriptive statistics to advanced predictive modeling. This allows us to move beyond simple summaries to develop proactive strategies to mitigate potential risks.
Descriptive Statistics: We utilize descriptive statistics (means, medians, standard deviations) to summarize key safety metrics and identify potential areas of concern. This helps establish a baseline for various safety measurements.
Regression Analysis: Regression analysis helps to identify relationships between different variables (e.g., product design features and incident rates). This allows us to pinpoint design elements potentially contributing to safety incidents.
Survival Analysis: This technique helps us to understand the lifespan of products and predict failure rates, enabling proactive interventions. This is essential for products with a complex life cycle or elements subject to wear and tear.
Machine Learning: Machine learning algorithms can be used to identify patterns and predict potential safety issues based on historical data. This helps us anticipate and prevent future incidents by analysing past failures.
Q 12. How do you use product safety data to identify trends and potential risks?
Identifying trends and potential risks involves a systematic approach to analyzing product safety data. We use a blend of analytical techniques and a deep understanding of the product lifecycle to anticipate future issues.
Trend Analysis: We track key metrics over time to identify emerging trends, such as increases in specific types of incidents or failures. This gives us insight into the performance of products over time.
Root Cause Analysis: Investigating incidents thoroughly to determine their root cause is crucial. We use techniques like the ‘5 Whys’ to understand the underlying factors and avoid repeating past mistakes.
Risk Assessment: Formal risk assessments are conducted to identify and evaluate potential hazards associated with products. This is crucial for determining which potential risks require the most attention and immediate mitigation.
Predictive Modeling: Using predictive modeling, we can forecast potential future safety issues based on historical data and trends. This allows for proactive measures to mitigate risks before they occur.
Q 13. What is your experience with regulatory compliance regarding data storage and reporting for product safety?
Regulatory compliance is a cornerstone of our data management strategy. We meticulously adhere to all relevant regulations regarding data storage, retention, and reporting for product safety. This is a critical element of protecting the brand’s reputation and avoiding legal ramifications.
Data Privacy Regulations (GDPR, CCPA): We ensure compliance with data privacy regulations, protecting the confidentiality of personal information related to incidents or customer reports. This is essential to avoid potential legal penalties and maintain customer trust.
Industry-Specific Regulations: We comply with all industry-specific regulations, such as those governing medical devices or automotive safety. This requires a detailed understanding of the legal requirements for different product categories.
Data Retention Policies: We have clear data retention policies that comply with legal and regulatory requirements. We need to ensure that we keep relevant data for the required period of time, and that we dispose of data safely and securely once it is no longer needed.
Auditing and Reporting: Regular audits are conducted to ensure ongoing compliance. We maintain detailed records of our compliance efforts for regulatory review.
Q 14. Describe your experience with implementing and maintaining data governance policies for product safety data.
Data governance policies are critical for ensuring the quality, integrity, and security of product safety data. These policies provide a framework for managing data throughout its lifecycle, from collection to disposal. This is the bedrock of maintaining data quality and ensuring the reliability of analysis.
Data Quality Management: Policies are in place to ensure the accuracy, completeness, and consistency of data collected. This includes defining data standards and implementing data validation processes.
Data Security Policies: Robust security policies and procedures are implemented to protect data from unauthorized access, use, disclosure, disruption, modification, or destruction. This includes defining user access permissions, encryption techniques, and regular security audits.
Data Retention and Disposal: Policies outline the retention periods for different types of data and the procedures for secure disposal of data when it is no longer needed. This is crucial for maintaining data privacy and security.
Data Governance Committee: A dedicated data governance committee oversees the implementation and enforcement of these policies, ensuring accountability and continuous improvement. This ensures all involved stakeholders understand and agree with the policies in place.
Q 15. How do you ensure the scalability and performance of a Product Safety Database?
Ensuring scalability and performance in a Product Safety Database is paramount. Think of it like building a highway: you need enough lanes (resources) to handle peak traffic (data volume and queries) without causing congestion (slowdowns). We achieve this through a multi-pronged approach.
- Database Choice: Selecting a database system designed for high-volume transactional data is crucial. Relational databases like PostgreSQL or Oracle, or NoSQL solutions like MongoDB, each offer strengths depending on the data structure and query patterns. For example, PostgreSQL’s robust features and ACID properties (Atomicity, Consistency, Isolation, Durability) are vital for maintaining data integrity in a safety-critical system.
- Database Design: Proper indexing is vital. Indexes are like the exit ramps on our highway, enabling quick access to specific data. We need to carefully analyze query patterns and create indexes on frequently queried columns to minimize search time. Database normalization (organizing data to reduce redundancy) further enhances performance and data integrity.
- Hardware and Infrastructure: Sufficient server resources (CPU, RAM, storage) are essential. Cloud-based solutions offer scalability advantages, allowing us to dynamically increase resources as needed. Using solid-state drives (SSDs) instead of traditional hard drives significantly improves read/write speeds.
- Caching: Caching frequently accessed data in memory significantly reduces database load. This is akin to having a local gas station near the highway, preventing many drivers from having to travel far for fuel.
- Query Optimization: Regularly reviewing and optimizing SQL queries is crucial. Inefficient queries can significantly impact performance. Tools and techniques like query analysis, explain plans, and database tuning help identify and rectify bottlenecks.
- Load Testing and Monitoring: Regular load testing simulates high-traffic scenarios to identify performance bottlenecks *before* they become problems in production. Continuous monitoring tools track key metrics like query execution time, database connection pool usage, and disk I/O to proactively address performance degradation.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. Explain your experience with database performance monitoring and optimization techniques.
Database performance monitoring and optimization are integral to my approach. I’ve used a variety of tools and techniques to identify and resolve performance issues. Imagine a doctor monitoring a patient’s vital signs – that’s what database monitoring is like. We need to constantly observe the system’s health.
- Tools: I’ve extensive experience with tools like pgAdmin (for PostgreSQL), Oracle Enterprise Manager, and various monitoring solutions offered by cloud providers (e.g., AWS CloudWatch, Azure Monitor). These provide insights into query performance, resource usage, and error rates.
- Techniques: I use a combination of proactive and reactive measures. Proactive measures include regular analysis of slow queries, optimizing indexes, and tuning database parameters. Reactive measures involve using the monitoring tools to identify performance issues, analyzing query plans (
EXPLAIN PLANin SQL), and implementing solutions like adding indexes, caching, or re-writing inefficient queries. - Example: In a previous role, I identified a performance bottleneck caused by a poorly written query that was performing full table scans instead of using indexes. Rewriting the query with appropriate index usage resulted in a 90% improvement in query execution time.
Q 17. Describe your experience with different database technologies and platforms.
My experience spans various database technologies, each with its strengths and weaknesses. The choice depends on the specific needs of the application. Think of it like choosing the right tool for the job – a hammer is great for nails, but not so much for screws.
- Relational Databases (RDBMS): I’m proficient with PostgreSQL, MySQL, Oracle, and SQL Server. These are suitable for structured data and complex relationships, ideal for scenarios where data integrity and ACID properties are crucial (like product safety data).
- NoSQL Databases: I have experience with MongoDB and Cassandra. These are better suited for large volumes of unstructured or semi-structured data where scalability and high write throughput are priorities. For instance, if we were dealing with a vast number of sensor readings from various devices reporting on product performance, a NoSQL database would be advantageous.
- Cloud-Based Databases: I’m also experienced with cloud-based database services like Amazon RDS, Azure SQL Database, and Google Cloud SQL. These offer scalability, high availability, and managed services, reducing the burden of infrastructure management.
In the context of a product safety database, the choice often leans towards a robust RDBMS due to the need for strong data integrity and ACID properties. However, NoSQL databases might be used for supplementary data, like sensor logs or user feedback.
Q 18. What experience do you have with data modeling and database design for product safety applications?
Data modeling and database design are fundamental to building effective product safety databases. A well-designed database ensures data integrity, efficient querying, and scalability. It’s like creating a blueprint for a house – careful planning ensures a strong and functional structure.
- Entity-Relationship Diagrams (ERDs): I use ERDs to visually represent the relationships between different data entities (e.g., products, incidents, components, suppliers). This helps in defining tables, columns, and relationships within the database.
- Normalization: I apply database normalization techniques to reduce data redundancy and improve data integrity. This minimizes data inconsistencies and simplifies data updates.
- Data Types: Careful selection of appropriate data types (e.g., integers, dates, strings, booleans) is critical for optimizing storage and query performance. For example, using an appropriate date type for manufacturing dates ensures accurate reporting and analysis.
- Indexing: Strategic placement of indexes greatly enhances query performance by optimizing data retrieval.
- Example: In a previous project, I designed a database schema to track product recalls. The schema included tables for products, recall events, affected batches, customer reports, and corrective actions. The relationships between these tables were carefully defined to facilitate efficient reporting and analysis of recall events.
Q 19. How would you handle a situation where a critical data element is missing in the Product Safety Database?
Missing critical data in a product safety database is a serious issue. It’s like a missing piece in a puzzle – it compromises the completeness and accuracy of the overall picture. Our response must be swift and thorough.
- Identify the Source: First, we pinpoint why the data is missing. Is there a problem with data entry, integration with external systems, or a flaw in the data collection process?
- Data Recovery: We explore all avenues to recover the missing data. This might involve checking backups, reviewing archived data, contacting relevant stakeholders (suppliers, manufacturers), or analyzing related data sources to infer missing information.
- Data Imputation (with caution): If recovery is impossible, we might consider data imputation – estimating the missing value based on statistical methods or other available data. However, this must be done cautiously, carefully documenting the imputation method and its potential impact on analysis. We must prioritize transparency and avoid introducing bias.
- Prevent Future Occurrences: The most important step is to prevent this from happening again. This could involve improving data entry procedures, strengthening data validation rules, or enhancing data integration processes. Regular data quality checks are vital.
- Impact Assessment: A thorough assessment of the impact of the missing data on analysis and reporting is crucial. If the missing data significantly affects key reports, we need to clearly communicate these limitations to stakeholders.
Q 20. Explain your understanding of different data types and their application in a Product Safety Database.
Understanding data types is essential for building a robust and efficient Product Safety Database. Different data types serve different purposes, and choosing the right ones is crucial for accuracy, efficiency, and data integrity. Think of it like using the correct tools in a workshop – using a screwdriver when you need a hammer will only lead to frustration.
- Numeric Types (INTEGER, FLOAT, DOUBLE): Used for quantitative data like product IDs, quantities, measurements, or test results.
- Text Types (VARCHAR, TEXT): Used for descriptive data like product names, descriptions, incident reports, or comments.
VARCHARis preferable for shorter text strings to optimize storage. - Date and Time Types (DATE, TIMESTAMP): Used for tracking dates of manufacture, incidents, or updates.
TIMESTAMPoften includes time zone information for accurate recording of events across different locations. - Boolean Types (BOOLEAN): Used for representing true/false values, such as whether a product passed a safety test or whether an incident was reported.
- Binary Data Types (BLOB): Used for storing large binary objects like images or documents, such as product schematics or test reports.
- ENUMs: Custom types representing a finite set of values, like product status (e.g., ‘in production’, ‘shipped’, ‘recalled’). These improve data consistency.
Choosing the correct data type minimizes storage space, improves query performance, and ensures data integrity. For instance, storing a product’s weight as an integer instead of a text string prevents errors and makes calculations easier.
Q 21. How do you manage and resolve conflicts between different data sources used in a Product Safety Database?
Managing conflicts between different data sources is a common challenge in building a Product Safety Database. This is like merging information from multiple witnesses in a crime investigation – each account might have slightly different details, and we need to resolve inconsistencies to get a clear picture.
- Data Profiling: We begin by thoroughly profiling each data source to understand its structure, data quality, and potential inconsistencies. This helps identify areas of potential conflict before integration.
- Data Transformation: Data transformation is often necessary to ensure consistency between sources. This may involve cleaning, standardizing, or converting data formats. For instance, we might need to convert different date formats to a consistent standard.
- Conflict Resolution Strategies: Several strategies exist to address conflicts. We might prioritize data from a more reliable source, use a weighted average if multiple values exist, or flag conflicts for manual review by subject matter experts. The choice depends on the nature of the data and the risk associated with inconsistencies.
- Data Governance and Validation Rules: Establishing clear data governance procedures, including data validation rules and quality checks, helps prevent conflicts from occurring in the first place. This promotes data consistency across all sources.
- Automated Conflict Detection: Implementing automated systems to detect and flag potential data conflicts helps ensure timely resolution. Tools can compare data across different sources and highlight inconsistencies.
The goal is to ensure the Product Safety Database contains accurate and consistent information despite the diverse origins of its data. Careful planning and execution of these steps is essential to maintain data integrity and reliability.
Q 22. Describe your experience with version control and change management in a Product Safety Database.
Version control and change management are crucial for maintaining the integrity and traceability of a Product Safety Database. Think of it like a meticulously kept logbook for a ship – every entry is important, and you need to know exactly who made what change and when. We use a robust system, typically Git or a similar platform, to track every modification to the database schema, data entries, and even configuration files. This allows us to easily revert to previous versions if needed, understand the evolution of the data, and ensure accountability.
For instance, if a recall is issued, we can pinpoint precisely when the faulty product information was entered and trace its journey through the database. This is critical for investigations and helps prevent similar incidents in the future. Our change management process includes a formal approval workflow, where changes are reviewed and authorized before deployment to the production environment. This minimizes errors and ensures data quality. We also implement thorough testing before any update goes live.
- Versioning schema changes: Every alteration to the database structure is logged, allowing us to roll back to a previous state if a new version introduces unexpected problems.
- Auditing data modifications: We track who made a change, when it was made, and what was changed. This ensures data integrity and accountability.
- Rollback capabilities: The version control system provides mechanisms to easily revert to previous database states in the event of errors or unintended changes.
Q 23. What is your familiarity with different data security protocols and encryption methods?
Data security is paramount in a Product Safety Database. We employ a multi-layered approach, combining various security protocols and encryption methods to protect sensitive information. This includes:
- Access Control: Role-based access control (RBAC) ensures that only authorized personnel can access specific data and perform certain actions. For example, a data entry clerk might only have permission to add new records, while a safety officer would have broader access.
- Encryption: Data at rest (on the database server) and data in transit (between client applications and the database) are encrypted using robust algorithms like AES-256. This ensures confidentiality even if the data is intercepted.
- Network Security: We employ firewalls, intrusion detection systems, and VPNs to protect the database server from unauthorized access.
- Data Loss Prevention (DLP): DLP tools monitor data movement and prevent sensitive information from being copied or exported without authorization.
- Regular Security Audits: We conduct regular security audits and penetration testing to identify and mitigate vulnerabilities.
We also stay current on the latest security best practices and emerging threats to proactively defend against evolving cyber security risks. Thinking about it like a high-security vault; multiple layers of protection are critical to keeping the contents safe.
Q 24. How do you ensure data privacy and compliance with relevant regulations like GDPR or CCPA?
Data privacy and compliance are integral parts of our operations. We adhere strictly to regulations like GDPR and CCPA, implementing procedures to ensure user rights are protected and data is handled responsibly. Key aspects of our approach include:
- Data Minimization: We only collect and store the minimum necessary data required for product safety purposes.
- Purpose Limitation: Data is collected and used solely for the specified purpose, with appropriate consent obtained where necessary.
- Data Security: We maintain stringent security measures to protect against unauthorized access, use, disclosure, alteration, or destruction of personal data, as detailed in the previous response.
- Data Subject Rights: We provide individuals with the ability to access, correct, or delete their personal data upon request, in line with GDPR and CCPA regulations.
- Data Breach Notification: We have procedures in place to promptly detect, respond to, and notify authorities of any data breaches, as mandated by relevant regulations.
- Privacy Impact Assessments: We regularly conduct privacy impact assessments to proactively identify and address potential privacy risks.
We treat data privacy with the utmost seriousness, recognizing the potential impact of non-compliance.
Q 25. Describe your experience in working with cross-functional teams to improve data quality and management.
Collaborating with cross-functional teams is essential for maintaining a high-quality Product Safety Database. I’ve worked extensively with engineering, quality assurance, legal, and regulatory affairs teams to improve data quality and management. Effective communication and shared goals are key to success.
For example, in one project we worked closely with the engineering team to standardize product identification codes, which significantly improved data accuracy and reduced inconsistencies. With the quality assurance team, we developed a comprehensive data validation process to catch errors before they reach the database. We also partnered with the legal team to ensure that data handling practices aligned with relevant regulations. These collaborative efforts led to a more robust and reliable database that supported better decision-making across the organization. Open communication and clearly defined roles are paramount for efficient teamwork. Regular meetings and shared documentation are also vital to keep everyone aligned on goals and progress.
Q 26. How do you prioritize competing demands and tasks related to maintaining a Product Safety Database?
Prioritizing competing demands in managing a Product Safety Database requires a structured approach. I typically use a combination of techniques to effectively manage tasks:
- Risk Assessment: I assess the potential impact of each task on product safety and regulatory compliance. Higher-risk tasks, such as addressing critical vulnerabilities or implementing urgent recall information, receive priority.
- Urgency and Importance Matrix: Categorizing tasks based on their urgency and importance helps to prioritize the most critical items. High-urgency, high-importance tasks are addressed immediately.
- Project Management Tools: I utilize project management software (e.g., Jira, Asana) to track progress, manage deadlines, and assign responsibilities. This enhances visibility and accountability.
- Regular Review and Adjustment: I regularly review the task list and adjust priorities based on evolving circumstances and new information.
Think of it like a triage system in a hospital—the most critical cases are dealt with first, ensuring efficient allocation of resources.
Q 27. Describe your experience with troubleshooting and resolving database-related issues.
Troubleshooting and resolving database issues is a regular part of the job. My experience encompasses a wide range of issues, from simple data entry errors to complex performance problems. My approach involves a systematic process:
- Identify the problem: Clearly define the nature and scope of the issue. Is it a performance bottleneck, a data corruption issue, or a security vulnerability?
- Gather information: Collect relevant data, such as error logs, performance metrics, and user reports.
- Analyze the cause: Investigate the root cause of the problem using SQL queries, database monitoring tools, and other diagnostic methods.
- Develop a solution: Based on the analysis, develop a plan to fix the problem. This might involve writing SQL scripts, modifying database configurations, or implementing new security measures.
- Implement the solution: Carefully implement the solution, testing thoroughly before deploying it to the production environment.
- Monitor and prevent recurrence: Monitor the database to ensure the solution is effective and take steps to prevent the problem from happening again. This might involve improving data validation procedures, implementing automated alerts, or upgrading database software.
For example, I once resolved a performance issue by optimizing database queries, resulting in a significant improvement in response times. Systematic investigation and thorough testing are essential to ensure the effectiveness of the solution.
Q 28. Explain your experience with implementing and utilizing data analytics tools for product safety.
Data analytics play a crucial role in improving product safety. We use a variety of tools to analyze data from the Product Safety Database to identify trends, predict potential issues, and support proactive decision-making. These tools range from basic SQL querying and reporting tools to advanced business intelligence (BI) platforms.
For example, we use data analytics to:
- Track incident rates: Identifying patterns in product failures and relating them to specific product characteristics.
- Analyze recall effectiveness: Evaluating the impact of recall campaigns and identifying areas for improvement.
- Predict potential safety issues: Using predictive modeling to identify products or components that may be prone to failure.
- Monitor regulatory compliance: Ensuring that product safety data meets all relevant regulations.
- Support product design improvements: Using data analysis to inform product design changes that enhance safety and reliability.
By leveraging data analytics, we can move from reactive to proactive safety management, preventing potential incidents before they occur.
Key Topics to Learn for Product Safety Databases Interview
- Data Structure and Management: Understanding relational databases, data modeling techniques relevant to product safety information (e.g., incident reports, test results, regulatory compliance data), and efficient data retrieval methods.
- Data Integrity and Validation: Practical application of data validation rules and techniques to ensure accuracy and reliability of product safety data. This includes handling missing data and addressing inconsistencies.
- Regulatory Compliance and Standards: Familiarity with relevant international and regional regulations (e.g., ISO, FDA, etc.) and how they impact the structure and content of product safety databases. Understanding data requirements for compliance reporting.
- Data Analysis and Reporting: Practical experience with querying and analyzing data to identify trends, potential safety hazards, and areas for improvement. Creating insightful reports from database information.
- Database Security and Access Control: Implementing robust security measures to protect sensitive product safety data. Understanding different user roles and access privileges within a database system.
- Troubleshooting and Problem Solving: Identifying and resolving database errors, performance issues, and data inconsistencies. Developing strategies for proactive data maintenance and error prevention.
- System Integration: Understanding how product safety databases integrate with other systems (e.g., CRM, ERP, incident reporting systems) and the importance of data exchange and standardization.
Next Steps
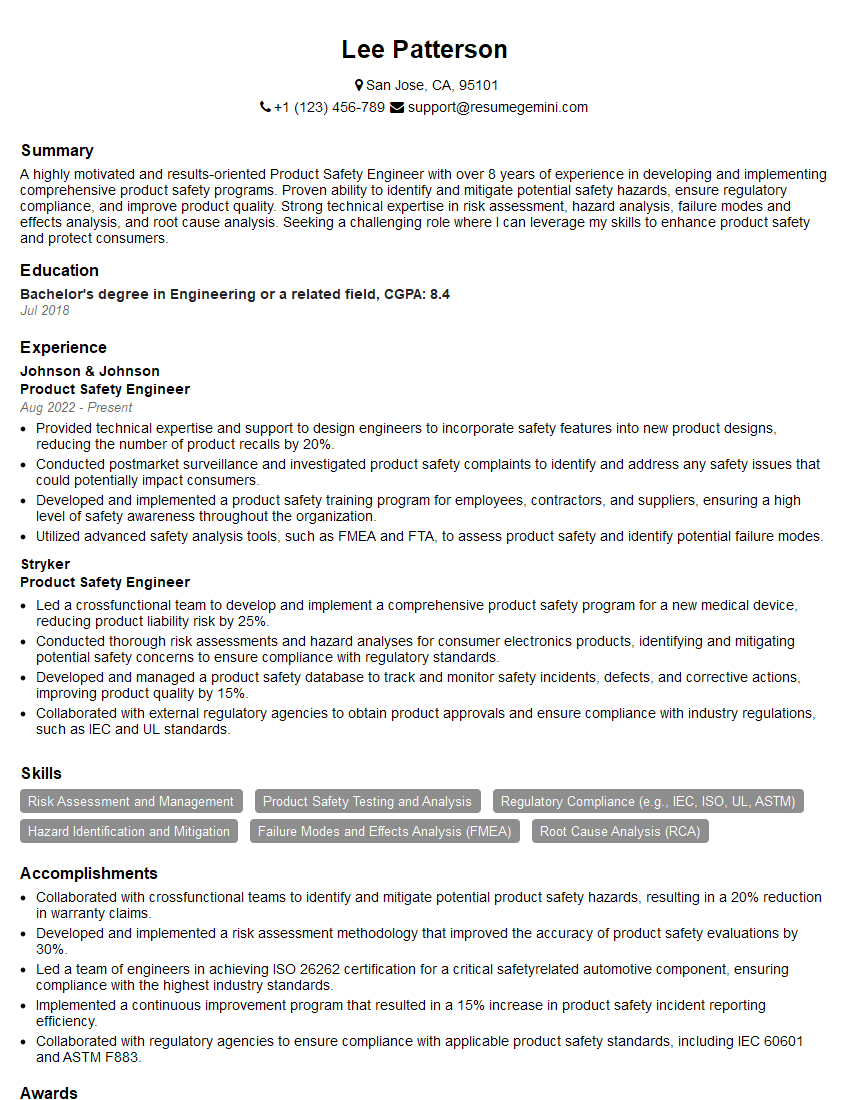
Mastering Product Safety Databases is crucial for career advancement in today’s data-driven regulatory environment. A strong understanding of these systems demonstrates valuable technical skills and a commitment to product safety. To significantly boost your job prospects, focus on crafting an ATS-friendly resume that highlights your expertise. ResumeGemini is a trusted resource that can help you create a professional and impactful resume, ensuring your qualifications shine. We provide examples of resumes tailored to Product Safety Databases to guide you through the process.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good