Are you ready to stand out in your next interview? Understanding and preparing for Risk and Vulnerability Assessment interview questions is a game-changer. In this blog, we’ve compiled key questions and expert advice to help you showcase your skills with confidence and precision. Let’s get started on your journey to acing the interview.
Questions Asked in Risk and Vulnerability Assessment Interview
Q 1. Explain the difference between a vulnerability and a threat.
Think of it like this: a vulnerability is a weakness in your security system – a crack in your wall, if you will. A threat is someone (or something) actively trying to exploit that weakness – a burglar trying to get through that crack. A vulnerability is a *passive* characteristic, while a threat is an *active* agent.
For example, an outdated operating system (vulnerability) might leave your computer susceptible to malware (threat). The vulnerability exists regardless of whether malware tries to attack; the threat only materializes when an attempt to exploit that vulnerability is made. Another example: A weak password (vulnerability) combined with a brute force attack (threat) could lead to unauthorized access.
Q 2. Describe the OWASP Top 10 vulnerabilities and their mitigation strategies.
The OWASP Top 10 represent the most critical web application security risks. Mitigation strategies are crucial to reducing the likelihood of successful exploitation.
- Injection (SQL, XSS, etc.): Use parameterized queries or prepared statements to prevent malicious code injection. Validate and sanitize all user inputs rigorously. Example: Sanitize user-supplied data before displaying it on a webpage to prevent Cross-Site Scripting (XSS).
- Broken Authentication: Implement strong password policies, multi-factor authentication (MFA), and regularly audit user accounts. Employ secure session management techniques.
- Sensitive Data Exposure: Encrypt sensitive data both in transit and at rest. Implement access control lists (ACLs) to restrict access to authorized personnel only.
- XML External Entities (XXE): Disable XML external entity processing in your applications. Use well-vetted XML libraries that have addressed the XXE vulnerability.
- Broken Access Control: Implement least privilege principle – grant users only the necessary access rights. Regularly audit access control configurations.
- Security Misconfiguration: Follow security best practices during deployment. Ensure proper configuration of all software components and regularly update them.
- Cross-Site Scripting (XSS): Sanitize user inputs, use output encoding, and employ a web application firewall (WAF).
- Insecure Deserialization: Validate and restrict untrusted data before deserialization. Avoid using deserialization for sensitive data.
- Using Components with Known Vulnerabilities: Regularly update software components, use vulnerability scanners, and perform dependency checks.
- Insufficient Logging & Monitoring: Implement comprehensive logging and monitoring solutions to detect and respond to security incidents promptly.
Q 3. What are the key components of a vulnerability assessment program?
A robust vulnerability assessment program has several key components:
- Policy and Procedures: A clearly defined policy outlining the scope, frequency, and responsibilities related to vulnerability assessments.
- Asset Inventory: A comprehensive list of all assets (servers, applications, network devices) within the organization’s scope.
- Vulnerability Scanning Tools: Utilizing automated tools to scan for known vulnerabilities.
- Penetration Testing: Conducting simulated attacks to assess the effectiveness of security controls.
- Vulnerability Prioritization and Remediation: A process for prioritizing identified vulnerabilities based on risk and developing a remediation plan.
- Reporting and Metrics: Regular reports to track progress and measure the effectiveness of the program.
- Vulnerability Management System: Utilizing a centralized system to track, manage, and remediate vulnerabilities.
- Training and Awareness: Educating personnel on security best practices and their role in the vulnerability management process.
Q 4. How do you prioritize vulnerabilities discovered during a scan?
Prioritization involves a combination of factors. The most common framework uses a risk-based approach, considering:
- Severity: How serious is the vulnerability (e.g., critical, high, medium, low)? This is often based on CVSS scores (Common Vulnerability Scoring System).
- Likelihood: How likely is the vulnerability to be exploited? This considers factors like the vulnerability’s exploitability and the attacker’s skill level.
- Impact: What’s the potential damage if the vulnerability is exploited? This could involve data breaches, system downtime, or financial loss.
A vulnerability with high severity, high likelihood, and high impact should be prioritized over one with low severity, low likelihood, and low impact. Many vulnerability management systems incorporate risk scoring algorithms to assist in this process. A simple example is assigning a score: Severity (1-5) x Likelihood (1-5) x Impact (1-5) = Risk Score. Higher scores get prioritized first.
Q 5. Explain the difference between a vulnerability scan and a penetration test.
A vulnerability scan is like a quick health check. Automated tools scan systems for known vulnerabilities based on a database of known weaknesses. It’s like using a metal detector to find possible metal objects. It identifies *potential* problems but doesn’t actually try to exploit them.
A penetration test is a more thorough investigation, simulating real-world attacks to assess how effectively your security defenses work. It’s like an intruder actually trying to break into your house. It goes beyond just identifying vulnerabilities and assesses their exploitability.
In short: Scanning identifies *what* vulnerabilities exist; penetration testing determines *how* they can be exploited and the effectiveness of existing security controls.
Q 6. What are the different types of vulnerability scanners?
There are several types of vulnerability scanners, each with its strengths and weaknesses:
- Network Scanners: These scan network devices for vulnerabilities like open ports, misconfigurations, and known weaknesses in specific services (e.g., Nessus, OpenVAS).
- Host-Based Scanners: These scan individual systems (servers, workstations) for vulnerabilities in the operating system, applications, and configurations (e.g., QualysGuard).
- Web Application Scanners: These are specialized scanners that focus on identifying vulnerabilities in web applications (e.g., Acunetix, Burp Suite).
- Database Scanners: These scan database systems (e.g., SQL Server, Oracle) for weaknesses in their configurations and code.
- Mobile Application Scanners: These specialized scanners help find vulnerabilities in mobile applications.
The choice of scanner depends on the specific needs and the type of assets being assessed.
Q 7. How do you handle false positives in vulnerability scanning?
False positives are a common occurrence in vulnerability scanning. They indicate a potential vulnerability that doesn’t actually exist. Handling them requires a careful and systematic approach:
- Review the Scan Results: Carefully examine the details of the reported vulnerability, including the affected asset, the vulnerability description, and any supporting evidence.
- Verify the Vulnerability: Manually check the affected system to confirm the vulnerability’s presence. This might involve reviewing configurations, checking logs, or running manual tests.
- Consult Documentation: Refer to the documentation for the affected software or system to determine if the reported vulnerability is a known issue, a false positive, or requires a specific configuration.
- Use Multiple Scanners: Running scans with different tools can help reduce false positives, as different scanners use different methodologies.
- Tune the Scanner Settings: Fine-tuning the scanner settings, such as adjusting the scan’s aggressiveness or specifying exclusion criteria, can help reduce false positives.
- Maintain a False Positive Database: Keep a record of previously identified false positives to avoid repetitive investigations.
It’s crucial to prioritize true positives, but dismissing false positives without proper investigation can be risky.
Q 8. Describe your experience with various vulnerability scanning tools (e.g., Nessus, OpenVAS).
Throughout my career, I’ve extensively utilized various vulnerability scanning tools, including Nessus and OpenVAS, to identify and assess security weaknesses in systems and networks. Nessus, with its comprehensive plugin library, excels at discovering a wide range of vulnerabilities, from outdated software to misconfigurations. I’ve used its reporting features to generate detailed vulnerability reports, prioritizing critical issues for remediation. OpenVAS, an open-source alternative, offers similar functionality, allowing for customization and integration into existing security infrastructures. My experience encompasses configuring these tools, scheduling scans, analyzing results, and collaborating with development and operations teams to address identified vulnerabilities. For example, in a recent project for a financial institution, I leveraged Nessus to identify a critical SQL injection vulnerability in their web application. This was promptly remediated, preventing potential data breaches. I also have experience using other tools like QualysGuard and Nexpose, each with its own strengths and weaknesses depending on the specific requirements of the assessment.
Q 9. Explain the concept of risk assessment and its methodology.
Risk assessment is a systematic process to identify, analyze, and evaluate potential threats and vulnerabilities that could negatively impact an organization’s objectives. It’s like a thorough health check for your security posture. The methodology generally follows these steps:
- Asset Identification: Identifying all valuable assets (data, systems, infrastructure).
- Threat Identification: Determining potential threats (malware, hackers, natural disasters).
- Vulnerability Identification: Pinpointing weaknesses that could be exploited (unpatched software, weak passwords).
- Risk Analysis: Assessing the likelihood and impact of each threat exploiting a vulnerability.
- Risk Response: Developing strategies to mitigate, transfer, accept, or avoid the risk.
- Monitoring and Review: Regularly reviewing and updating the assessment to reflect changes.
Think of it like this: you wouldn’t go on a long journey without checking your car’s tires and brakes – risk assessment is that crucial pre-journey check for your organization’s security.
Q 10. How do you calculate risk (e.g., using quantitative or qualitative methods)?
Risk calculation can be either quantitative or qualitative, depending on the available data and the desired level of precision.
Quantitative Risk Analysis involves assigning numerical values to the likelihood and impact of risks. A common formula is:
Risk = Likelihood x ImpactFor example, if the likelihood of a specific vulnerability being exploited is rated as 0.7 (high) and the impact is rated as 10 (catastrophic data loss), the risk score would be 7. This allows for a prioritized approach, addressing the highest-risk vulnerabilities first. This often requires specific data and can be quite complex to implement effectively.
Qualitative Risk Analysis relies on descriptive scales (e.g., low, medium, high) to assess likelihood and impact. This is useful when precise numerical data is unavailable. For instance, you might rate the likelihood of a social engineering attack as ‘medium’ and the impact as ‘high’, resulting in a ‘high’ overall risk. While less precise, it provides a valuable overview for decision-making.
Both methods are valuable, and often used in conjunction. For instance a qualitative assessment might be initially used to identify critical areas and then followed by a more detailed quantitative analysis to prioritize within that critical area.
Q 11. What are the key elements of a risk register?
A risk register is a central repository for documenting identified risks. Key elements include:
- Risk ID: A unique identifier for each risk.
- Risk Description: A clear and concise description of the risk.
- Likelihood: The probability of the risk occurring (often using qualitative or quantitative scales).
- Impact: The potential consequences if the risk occurs (e.g., financial loss, data breach).
- Risk Owner: The individual or team responsible for managing the risk.
- Risk Response: The plan to mitigate or address the risk (e.g., implement security controls, transfer risk through insurance).
- Status: The current status of the risk (e.g., open, in progress, closed).
- Due Date: The deadline for completing the risk response.
A well-maintained risk register is essential for tracking progress, ensuring accountability, and demonstrating proactive risk management.
Q 12. How do you communicate risk findings to both technical and non-technical audiences?
Communicating risk findings effectively requires tailoring the message to the audience. For technical audiences, I provide detailed reports with technical jargon and specific vulnerability details, including CVSS scores and remediation steps. I might include detailed scan results and exploitability analysis.
For non-technical audiences, I use clear, concise language, focusing on the business impact of each risk. Instead of technical terms, I use analogies and visualizations (e.g., charts, graphs) to illustrate the potential consequences. For example, instead of saying “SQL injection vulnerability,” I might say, “a weakness in our system that could allow hackers to steal customer data.” I prioritize clear communication of the overall risk level and proposed mitigation strategies, focusing on the cost/benefit analysis of implementing solutions.
In both cases, the goal is to ensure the audience understands the risks and the recommended actions, fostering collaboration and informed decision-making.
Q 13. Describe your experience with various risk management frameworks (e.g., NIST, ISO 27001).
I have practical experience working with several risk management frameworks, most notably NIST Cybersecurity Framework and ISO 27001. The NIST framework offers a flexible approach, allowing organizations to tailor their security practices to their specific needs and risk profile. I’ve used it to guide risk assessments, develop security controls, and measure the effectiveness of our security posture. My work with ISO 27001 has involved implementing and maintaining an Information Security Management System (ISMS). This includes conducting regular risk assessments, establishing security policies and procedures, and ensuring compliance with the standard’s requirements. Both frameworks offer valuable guidance, but they differ in their approach; NIST being more flexible, while ISO 27001 provides a more prescriptive, certification-oriented framework.
Q 14. What is the difference between qualitative and quantitative risk analysis?
The key difference lies in the approach to measuring risk. Qualitative risk analysis uses subjective judgment and descriptive scales (low, medium, high) to assess likelihood and impact. It’s simpler and faster, suitable when data is limited. Think of it like using color-coded labels – red for high risk, yellow for medium, green for low.
Quantitative risk analysis uses numerical data and mathematical models to assign precise values to likelihood and impact. This provides a more precise measurement of risk, allowing for better prioritization of resources. Think of it like using a precise measuring scale to determine weight – the more precise, the better your understanding.
The choice between qualitative and quantitative depends on factors such as available data, resources, time constraints, and the desired level of precision. Often, a combination of both approaches provides the most comprehensive risk assessment.
Q 15. How do you conduct a business impact analysis (BIA)?
A Business Impact Analysis (BIA) is a crucial process that identifies the potential consequences of disruptions to an organization’s operations. It helps prioritize resources for risk mitigation and business continuity planning. We conduct a BIA through a structured process involving several key steps:
- Identify Critical Business Functions: This involves determining the essential functions that must continue operating to ensure the organization’s survival and success. For example, in a hospital, emergency care would be a critical function.
- Identify Potential Disruptions: We brainstorm potential threats that could interrupt these critical functions. This includes natural disasters (earthquakes, floods), cyberattacks, pandemics, and even human error.
- Analyze the Impact of Disruptions: For each identified disruption and critical function, we assess the potential impact. This is often quantified using metrics like financial loss, reputational damage, legal liabilities, and downtime. We might use a matrix to rate impact severity (e.g., low, medium, high) and likelihood (e.g., unlikely, possible, probable).
- Determine Recovery Time Objectives (RTO) and Recovery Point Objectives (RPO): RTO is the maximum acceptable downtime for a critical function after a disruption, while RPO defines the maximum acceptable data loss. For instance, an online banking system would have very low RTO and RPO requirements compared to a marketing department.
- Develop Recovery Strategies: Based on the BIA findings, we develop strategies for recovering from disruptions, including backup and recovery plans, disaster recovery plans, and alternative work arrangements.
- Document and Review: The entire BIA process is meticulously documented, regularly reviewed, and updated to reflect changes in the organization’s operations and risk environment.
A well-executed BIA provides a clear picture of an organization’s vulnerabilities and helps make informed decisions about risk management and resource allocation. It’s not a one-time exercise; it requires continuous monitoring and updates.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. Explain the concept of a threat model and how you create one.
A threat model is a systematic process to identify and analyze potential threats to a system or application. It’s like creating a detailed map of potential vulnerabilities, helping us proactively address them before they are exploited. We typically create a threat model using a structured approach, such as the STRIDE methodology:
- Spoofing: Identity or session hijacking. Example: A phisher mimicking a legitimate website.
- Tampering: Unauthorized modification of data. Example: Changing prices on an e-commerce site.
- Repudiation: Denial of actions. Example: An employee denying they sent an unauthorized email.
- Information Disclosure: Unauthorized access to sensitive information. Example: Leaking customer credit card data.
- Denial of Service (DoS): Disrupting availability. Example: Flooding a web server with requests.
- Elevation of Privilege: Gaining unauthorized access to higher-level functionalities. Example: A user gaining admin access.
Creating a threat model involves identifying assets, threats, vulnerabilities, and potential impacts. Then, we evaluate the likelihood and severity of each threat and prioritize mitigation strategies. Tools like threat modeling software can assist in this process, but the core is a collaborative exercise involving developers, security engineers, and business stakeholders. We often use diagrams (like Data Flow Diagrams) to visualize the system and identify attack paths. After analyzing the threats, we develop mitigation strategies that can be implemented throughout the software development lifecycle.
Q 17. What are the common types of security controls?
Security controls are safeguards or countermeasures implemented to reduce or mitigate risks to information systems. They can be categorized into several types:
- Administrative Controls: Policies, procedures, and guidelines. Examples include security awareness training, access control policies, and incident response plans.
- Technical Controls: Hardware and software mechanisms. Examples include firewalls, intrusion detection systems (IDS), antivirus software, and encryption.
- Physical Controls: Physical measures to protect assets. Examples include security cameras, access badges, locked doors, and fences.
These controls work in concert to provide layered security. A strong security posture relies on a robust implementation of all three types of controls. The specific controls implemented will depend on the risk assessment and the sensitivity of the data being protected.
Q 18. Describe your experience with security control implementation and testing.
I have extensive experience implementing and testing various security controls across diverse environments. For instance, I led the implementation of a multi-factor authentication (MFA) system for a large financial institution, significantly reducing the risk of unauthorized access. This involved configuring the MFA system, integrating it with existing authentication infrastructure, and conducting thorough user training. Post-implementation, we performed penetration testing to validate the effectiveness of the MFA controls and identify any residual vulnerabilities. In another project, I oversaw the deployment and testing of a next-generation firewall (NGFW), configuring rules and policies to manage network traffic securely and efficiently. We rigorously tested the firewall’s ability to block malicious traffic using various penetration testing techniques. Regular security audits and vulnerability scans are integral parts of my process, ensuring the continuous effectiveness of implemented security controls.
Q 19. What is the purpose of a security audit?
The purpose of a security audit is to systematically evaluate an organization’s security posture and identify weaknesses. It provides an independent assessment of an organization’s compliance with security policies, standards, and regulations, and its effectiveness in mitigating risks. A security audit typically involves reviewing security policies and procedures, assessing the effectiveness of security controls, and examining vulnerabilities in systems and networks. The findings of a security audit are used to improve the organization’s overall security posture, minimize risks, and ensure compliance. Think of it as a comprehensive health check for your organization’s security system, uncovering potential issues before they are exploited.
Q 20. How do you ensure the confidentiality, integrity, and availability (CIA triad) of data?
Ensuring the confidentiality, integrity, and availability (CIA triad) of data is paramount in any secure system. We achieve this through a combination of technical, administrative, and physical controls:
- Confidentiality: Protecting data from unauthorized access. This is achieved through access control mechanisms (like role-based access control), encryption (both in transit and at rest), and data loss prevention (DLP) tools.
- Integrity: Ensuring data accuracy and reliability. This is ensured through access controls, data validation, version control, hashing and digital signatures, and regular backups.
- Availability: Guaranteeing timely and reliable access to data. This involves redundancy (like failover systems), disaster recovery planning, load balancing, and regular system maintenance.
These three principles are interconnected. For example, strong encryption (confidentiality) is crucial for maintaining data integrity. Similarly, redundancy enhances both availability and the ability to recover from data loss, protecting both confidentiality and integrity. A holistic approach, encompassing all three elements of the CIA triad, is essential for building a robust security posture.
Q 21. What experience do you have with incident response procedures?
I have extensive experience with incident response procedures, having participated in numerous incident response efforts. My experience includes handling security breaches, malware infections, and denial-of-service attacks. My approach aligns with the widely accepted NIST Cybersecurity Framework, which outlines a response process including:
- Preparation: Developing incident response plans, establishing communication protocols, and training personnel.
- Identification: Detecting and confirming the occurrence of a security incident.
- Containment: Isolating the affected systems to prevent further damage.
- Eradication: Removing the root cause of the incident.
- Recovery: Restoring systems and data to their pre-incident state.
- Lessons Learned: Analyzing the incident to identify weaknesses and improve security practices.
During incident response, I prioritize communication, collaboration, and timeliness. Maintaining accurate documentation throughout the entire process is also crucial for post-incident analysis and reporting. I have effectively employed various forensic techniques to investigate the root cause of incidents, providing valuable insights for enhancing our security posture.
Q 22. Describe your experience with remediation of security vulnerabilities.
Remediating security vulnerabilities involves a systematic process of identifying, analyzing, and fixing weaknesses in an organization’s systems and applications. It’s not just about patching software; it’s about understanding the root cause and implementing a lasting solution. My approach typically follows these steps:
- Assessment and Prioritization: I begin by thoroughly assessing the identified vulnerability, considering its severity (critical, high, medium, low), potential impact, and exploitability. This involves reviewing vulnerability scan reports, penetration testing results, and threat intelligence to determine the risk level.
- Root Cause Analysis: Once the vulnerability is identified, a root cause analysis is performed to understand *why* the vulnerability exists. This might involve reviewing code, configurations, or network architecture.
- Remediation Planning: Based on the root cause, I develop a remediation plan. This plan includes the specific actions needed to fix the vulnerability, the resources required (personnel, tools, budget), and timelines for completion. This is critical to ensure efficient and effective patching.
- Implementation: I implement the remediation plan, which may involve patching software, updating configurations, deploying security controls, or modifying code. This phase is often carefully controlled and tested to avoid unintended consequences.
- Verification and Validation: After implementation, I thoroughly verify that the vulnerability has been successfully mitigated. This might involve rescanning the system, re-running penetration tests, or manually testing the affected component. Crucially, I validate that the solution doesn’t introduce new vulnerabilities.
- Documentation: Thorough documentation of the entire process, including the vulnerability details, remediation steps, and validation results, is essential for auditing and future reference.
For example, I once remediated a critical SQL injection vulnerability in a web application. This involved not only patching the application but also reviewing the application’s database access logic to prevent similar vulnerabilities from occurring in the future. This involved collaborating with developers to implement parameterized queries and input validation.
Q 23. How do you stay up-to-date with the latest cybersecurity threats and vulnerabilities?
Staying current in cybersecurity is paramount. I utilize a multi-faceted approach:
- Subscription to threat intelligence feeds: I subscribe to reputable threat intelligence platforms that provide real-time alerts on emerging threats and vulnerabilities. These often include detailed analysis, indicators of compromise (IOCs), and suggested mitigations.
- Following industry news and blogs: I regularly read industry publications, blogs, and security news websites to stay informed about the latest attacks, trends, and vulnerabilities.
- Participating in online communities and forums: Engaging with other security professionals in online forums and communities allows me to learn from shared experiences and discussions about emerging threats.
- Attending conferences and webinars: Industry conferences and webinars provide valuable insights into the latest research, tools, and techniques.
- Certifications and professional development: Maintaining relevant security certifications (e.g., CISSP, CEH) ensures my knowledge base is updated regularly through continuous learning requirements.
- Vulnerability scanning and penetration testing: I regularly conduct vulnerability scans and penetration tests on systems and applications to proactively identify and address weaknesses. This is a hands-on approach that helps me understand real-world vulnerabilities.
This continuous learning approach allows me to effectively identify and respond to emerging threats and stay ahead of the curve.
Q 24. Explain your understanding of compliance regulations (e.g., HIPAA, GDPR, PCI DSS).
Compliance regulations like HIPAA, GDPR, and PCI DSS are crucial for ensuring data protection and privacy. My understanding encompasses their core principles and practical implications:
- HIPAA (Health Insurance Portability and Accountability Act): This US law protects the privacy and security of Protected Health Information (PHI). Compliance requires implementing robust security measures to safeguard patient data, including access controls, encryption, and audit trails.
- GDPR (General Data Protection Regulation): This EU regulation mandates stringent data protection rules, focusing on individual rights and data processing controls. Compliance requires obtaining consent, providing transparency, implementing data breach notification procedures, and ensuring data security.
- PCI DSS (Payment Card Industry Data Security Standard): This standard protects credit card data. Compliance requires implementing stringent security controls around payment processing systems, including strong encryption, secure coding practices, and regular vulnerability scanning.
In practice, understanding these regulations means being able to map their requirements to specific security controls and technical implementations. For example, ensuring data encryption at rest and in transit meets requirements across all three standards. Furthermore, regular audits and risk assessments are essential for maintaining compliance.
Q 25. What is your experience with automating security tasks?
Automating security tasks is crucial for efficiency and scalability. My experience includes:
- Vulnerability scanning automation: Utilizing tools like Nessus, OpenVAS, or QualysGuard to schedule and automate regular vulnerability scans across the organization’s IT infrastructure.
- Security Information and Event Management (SIEM) integration: Using SIEM systems (e.g., Splunk, QRadar) to automate log collection, analysis, and threat detection.
- Incident response automation: Developing and implementing automated playbooks for incident response using tools like SOAR (Security Orchestration, Automation, and Response) platforms.
- Configuration management automation: Using tools like Ansible, Chef, or Puppet to automate the configuration and hardening of servers and network devices.
- Penetration testing automation: Leveraging automated penetration testing tools to quickly identify common vulnerabilities.
Automation drastically reduces manual effort, improves consistency, and enables quicker responses to threats. For instance, automated vulnerability scans allow for rapid identification and remediation of critical security issues, significantly reducing the attack surface.
Q 26. Describe your experience with scripting or programming languages relevant to security.
I am proficient in several scripting and programming languages relevant to security:
- Python: I use Python extensively for automating security tasks, such as vulnerability scanning, log analysis, and penetration testing.
#Example: Simple port scanner in Python import socket sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM) for port in range(1, 1025): result = sock.connect_ex(('127.0.0.1', port)) if result == 0: print('Port {}: Open'.format(port)) sock.close() - Bash/Shell scripting: I use Bash scripting for automating tasks on Linux/Unix systems, such as system hardening, log management, and security audits.
- PowerShell: I utilize PowerShell for automating security tasks on Windows systems, including system administration, security auditing, and incident response.
These scripting skills are invaluable for developing custom security tools, automating repetitive tasks, and enhancing the overall efficiency of security operations.
Q 27. How do you handle pressure and tight deadlines in a security environment?
The security field often demands working under pressure and tight deadlines. I manage this by:
- Prioritization: I focus on addressing the most critical risks first, using a risk-based approach to prioritize tasks. This ensures that the most impactful vulnerabilities are addressed immediately.
- Time management: I use project management techniques (e.g., Agile methodologies) to break down complex tasks into smaller, manageable components and track progress effectively.
- Teamwork and communication: I collaborate effectively with other team members to share workloads and ensure efficient communication. Clear communication is key to coordinating efforts and resolving issues promptly.
- Stress management techniques: I utilize stress management techniques such as time-blocking, delegating effectively, and taking short breaks to maintain focus and productivity under pressure.
A calm and methodical approach is crucial when dealing with security incidents, which often involve high-pressure situations. Effective delegation and collaboration are critical for managing the complexities of a security breach response.
Q 28. Describe a time you had to troubleshoot a complex security issue.
During a recent incident, our web application experienced unusual spikes in database activity, suggesting potential unauthorized access. Initially, the logs didn’t provide enough information to pinpoint the root cause. My troubleshooting process involved these steps:
- Data Collection: I started by gathering detailed logs from the web server, database server, and network devices. This included reviewing access logs, error logs, and system events.
- Pattern Analysis: I analyzed the logs for patterns, looking for unusual activity or anomalies. This revealed a recurring pattern of connections originating from a specific IP address.
- Network Analysis: I then examined network traffic logs to identify the source of the connections. This helped me confirm the suspicious IP address and trace its location.
- Vulnerability Assessment: I re-ran vulnerability scans on the web application, focusing on potential SQL injection vulnerabilities, as the database activity was suspicious. This discovered a previously unknown vulnerability in a specific section of the code.
- Remediation: Once the vulnerability was identified, I implemented a temporary mitigation strategy, blocking the malicious IP address, while simultaneously developing a permanent fix for the vulnerability. The fix involved adding appropriate input validation checks to the code and further hardening database access configurations.
- Validation: After implementing the fix, I validated that the issue was resolved by re-running vulnerability scans, monitoring database activity, and verifying that the system was operating normally.
This systematic approach, combining log analysis, network analysis, and vulnerability assessments, allowed us to quickly identify the root cause, implement a solution, and prevent further exploitation. This also highlighted the importance of comprehensive logging and ongoing vulnerability management.
Key Topics to Learn for Risk and Vulnerability Assessment Interview
- Risk Identification and Analysis: Understanding methodologies like SWOT analysis, threat modeling, and vulnerability scanning to identify potential risks and vulnerabilities within systems and organizations.
- Vulnerability Assessment Methodologies: Practical application of various assessment techniques, including penetration testing, vulnerability scanning, and security audits. Understanding the differences and when to apply each method.
- Risk Prioritization and Mitigation: Applying frameworks like NIST Cybersecurity Framework or ISO 27005 to prioritize identified risks based on likelihood and impact. Developing and implementing mitigation strategies.
- Compliance and Regulatory Frameworks: Familiarity with relevant regulations and standards such as HIPAA, PCI DSS, GDPR, and SOC 2, and how they influence risk assessment processes.
- Risk Reporting and Communication: Effectively communicating risk assessments and mitigation plans to technical and non-technical audiences through clear and concise reporting.
- Quantitative and Qualitative Risk Analysis: Understanding the differences between these approaches and applying them appropriately in different scenarios. This includes understanding key concepts like Expected Monetary Value (EMV).
- Security Frameworks and Standards: Deep understanding of common security frameworks (e.g., NIST CSF, ISO 27001) and their application in a risk assessment context.
- Types of Vulnerabilities: In-depth knowledge of common vulnerabilities and exposures (CVEs) and their potential impact.
- Tools and Technologies: Familiarity with various risk assessment and vulnerability management tools, both open-source and commercial.
- Incident Response and Recovery: Understanding how risk assessments inform incident response planning and recovery strategies.
Next Steps
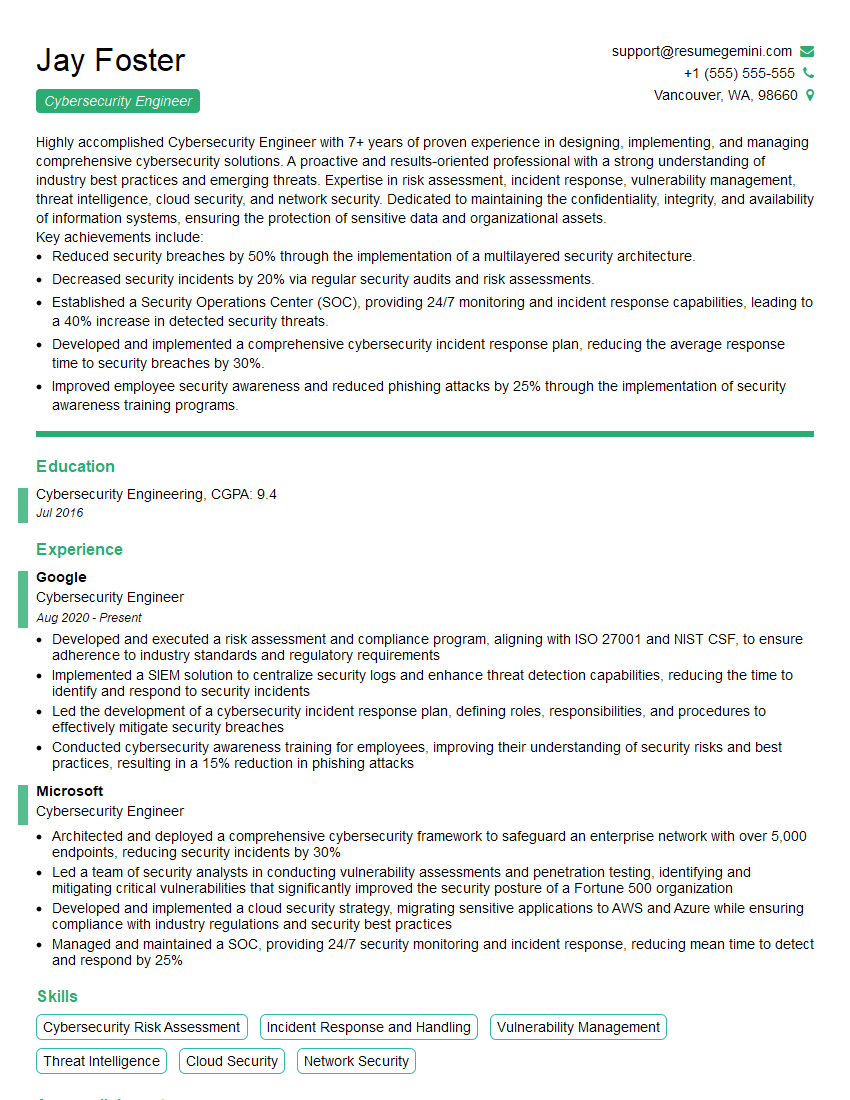
Mastering Risk and Vulnerability Assessment is crucial for career advancement in cybersecurity and related fields. Demonstrating a strong understanding of these concepts significantly improves your job prospects. To maximize your chances, create an ATS-friendly resume that showcases your skills and experience effectively. ResumeGemini is a trusted resource to help you build a professional and impactful resume. We provide examples of resumes tailored to Risk and Vulnerability Assessment to guide you through the process. Take the next step towards your dream career – invest in your resume today!
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good