The right preparation can turn an interview into an opportunity to showcase your expertise. This guide to SIGINT/COMINT Intercept Operations interview questions is your ultimate resource, providing key insights and tips to help you ace your responses and stand out as a top candidate.
Questions Asked in SIGINT/COMINT Intercept Operations Interview
Q 1. Explain the difference between SIGINT and COMINT.
SIGINT (Signals Intelligence) is a broad term encompassing all intelligence gathered from electronic signals. COMINT (Communications Intelligence) is a subset of SIGINT, focusing specifically on the interception and analysis of communications signals. Think of it like this: SIGINT is the entire pie, while COMINT is a significant slice. SIGINT might include things like radar emissions (ELINT – Electronic Intelligence), while COMINT deals specifically with intercepted voice, data, or other communications signals, regardless of the technology used.
For example, a nation might use SIGINT to track the movement of enemy aircraft via radar emissions (ELINT), while using COMINT to intercept and decipher the enemy’s radio chatter about their operational plans.
Q 2. Describe the process of intercepting and analyzing radio frequency signals.
Intercepting and analyzing radio frequency (RF) signals involves several steps. First, you need a receiver capable of tuning to the desired frequency range. This receiver could be a simple antenna and radio, or a sophisticated system with direction-finding capabilities. Next, the signal is received and amplified. Often, the signal is weak, so amplification is crucial. Then, the signal is demodulated; that is, the intelligence is extracted from the carrier wave. Different modulation techniques (like AM, FM, or digital modulation schemes) require different demodulation methods.
Analysis involves identifying the signal source, determining the type of modulation used, and finally, decoding the actual message. This might involve specialized software, signal processing techniques, and even linguistic analysis to decipher encrypted communications. For example, identifying a specific radio frequency signature could help pinpoint the location of a clandestine radio transmitter.
Imagine trying to hear a whispered conversation across a crowded room. Intercepting RF signals is similar; you need a sensitive ‘ear’ (receiver), a way to amplify the faint whisper (amplification), and finally, the skill to understand the conversation itself (demodulation and analysis).
Q 3. What are the common challenges in SIGINT/COMINT operations?
SIGINT/COMINT operations face numerous challenges. One significant challenge is the ever-evolving nature of communications technology. New encryption methods, advanced modulation techniques, and the use of diverse communication platforms constantly test the capabilities of interception systems. Another challenge is signal clutter and interference; separating the target signal from background noise and other interfering signals is difficult. The sheer volume of data intercepted also poses a significant challenge – efficient processing and analysis of vast amounts of data are critical.
Further complexities arise from legal and ethical considerations; the need to adhere to strict regulations while maintaining operational effectiveness. Finally, technological limitations of existing equipment may hinder the interception of new or advanced communications technologies.
Think of it as a high-stakes game of cat and mouse, with the ‘cat’ (SIGINT/COMINT) always striving to keep up with the evolving methods of the ‘mouse’ (the target).
Q 4. How do you ensure the security and integrity of intercepted data?
Securing and maintaining the integrity of intercepted data is paramount. This involves multiple layers of security. First, data encryption is employed at various stages, from interception to storage and analysis. Secure data storage solutions are essential, often involving dedicated, highly secured servers and robust access control mechanisms. The entire process follows strict chain-of-custody protocols to maintain data integrity, ensuring that the data is not tampered with, and that its provenance is clearly documented.
Access to intercepted data is strictly controlled through role-based access controls (RBAC), limiting access to authorized personnel with a need-to-know basis. Regular security audits and penetration testing are conducted to identify vulnerabilities and ensure systems are resilient to attacks. Any breaches or potential compromises are immediately addressed to minimize potential risks.
Imagine this as a high-security vault; multiple locks, strict access protocols, and constant monitoring are necessary to protect the valuable information within.
Q 5. What are the ethical considerations involved in SIGINT/COMINT?
Ethical considerations are central to SIGINT/COMINT. Operations must adhere to strict legal and ethical guidelines, respecting privacy rights and avoiding unwarranted intrusions into private communications. The collection and use of intercepted data must be justified, with clear legal authority and oversight. Transparency and accountability are vital, ensuring that all actions are justifiable and aligned with the rule of law. Data minimization is also crucial; only necessary data should be collected, processed, and retained.
Careful consideration of unintended consequences is paramount. The potential impact on individuals and society as a whole needs to be thoroughly assessed before engaging in any SIGINT/COMINT activity. Oversight mechanisms, such as independent review boards, are crucial to ensure ethical standards are maintained.
Balancing national security interests with individual privacy rights is a complex challenge requiring a delicate balancing act.
Q 6. Describe your experience with specific SIGINT/COMINT tools and technologies.
During my career, I’ve had extensive experience with various SIGINT/COMINT tools and technologies. I’ve worked with sophisticated direction-finding systems, allowing us to precisely locate the source of radio transmissions. I’m proficient in utilizing specialized software for signal demodulation, analysis, and decryption. This includes software capable of handling diverse modulation techniques and encryption algorithms. Experience also includes working with advanced signal processing techniques to extract intelligence from noisy or cluttered signals.
My experience also encompasses the use of various antenna systems, from simple dipole antennas to sophisticated phased array antennas capable of tracking multiple signals simultaneously. Data management and analysis tools are crucial, and I have experience with large-scale databases and analysis software for efficient processing and interpretation of vast amounts of intercepted data. I have also been involved in the development and implementation of secure data storage and access control mechanisms.
(Note: Due to the sensitive nature of specific tools and technologies used in SIGINT/COMINT, further detail cannot be provided.)
Q 7. Explain your understanding of different types of modulation techniques.
Modulation is the process of modifying a carrier wave to encode information. Different modulation techniques offer varying levels of efficiency, robustness to noise, and bandwidth requirements. Amplitude Modulation (AM) varies the amplitude of the carrier wave according to the information signal. Frequency Modulation (FM) varies the frequency of the carrier wave. These are analog modulation schemes.
Digital modulation schemes, such as Phase-Shift Keying (PSK), Quadrature Amplitude Modulation (QAM), and Frequency-Shift Keying (FSK), encode data as digital bits. Each digital bit changes a characteristic of the carrier wave (phase, amplitude, or frequency). These digital methods are much more robust to noise and allow for higher data rates compared to analog methods.
Understanding these modulation schemes is crucial for signal demodulation. Choosing the correct demodulation method based on the modulation scheme used by the intercepted signal is critical for successful intelligence gathering.
Imagine sending messages using Morse code. AM and FM are like sending the dots and dashes by varying the loudness or pitch of a whistle. Digital modulation schemes are more sophisticated, like using a complex code where different combinations of short and long whistles represent different letters or words.
Q 8. How do you identify and classify different types of signals?
Identifying and classifying signals involves a multi-step process that begins with signal detection and then progresses to detailed analysis of its characteristics. We utilize a combination of automated tools and human expertise to determine the nature of the intercepted signal.
Initially, we assess the signal’s physical characteristics: frequency, bandwidth, modulation type (e.g., AM, FM, Phase Shift Keying – PSK), pulse repetition rate (for radar signals), and signal strength. This initial analysis allows for a preliminary categorization – is it a radio broadcast, a satellite communication, a radar system, or something else?
Next, we look at the data content. If the signal is modulated and carries information, we analyze the type of data being transmitted. This might involve analyzing patterns in the signal’s structure or decoding the modulation scheme to reveal the underlying message. For instance, identifying a specific data protocol like TCP/IP suggests a computer network. Recognizing voice modulation leads us to classify it as a voice communication.
Finally, we analyze the signal’s context. This includes location data (if available), time of transmission, frequency usage patterns, and any available metadata. Knowing a signal is originating from a known military base, for example, drastically alters our interpretation of the data compared to one emanating from a commercial satellite. The entire process often leverages signal databases, specialized software, and collaborative expertise within the team.
- Example: A signal exhibiting a narrow bandwidth, frequency hopping, and pulse characteristics is likely a military communication employing spread spectrum techniques for anti-jamming.
- Example: A wideband signal with complex modulation and metadata pointing to a satellite uplink might indicate satellite television or data communication.
Q 9. What is your experience with signal processing and analysis techniques?
My signal processing and analysis experience encompasses a wide range of techniques, from basic Fourier transforms to advanced algorithms like wavelet transforms and cyclostationary analysis. I’m proficient in using software packages like MATLAB and specialized SIGINT/COMINT analysis tools to process raw signals.
For instance, I routinely employ Fourier transforms to break down complex signals into their constituent frequencies, aiding in identifying carrier frequencies and modulation types. Wavelet transforms help analyze non-stationary signals, which is crucial when dealing with signals with changing characteristics over time. Cyclostationary analysis helps to detect periodicities and patterns often masked by noise, especially important when dealing with digitally modulated signals.
Beyond these core techniques, I’ve extensive experience in signal filtering (noise reduction), equalization (compensating for channel distortion), and signal demodulation to recover the information embedded within the signal. My expertise also extends to designing and implementing custom signal processing algorithms using C++ and Python, adapting methods to meet the unique needs of different intercept scenarios.
//Example Python code snippet for simple signal filtering: import numpy as np from scipy.signal import butter, lfilter def butter_lowpass_filter(data, cutoff, fs, order=5): nyq = 0.5 * fs normal_cutoff = cutoff / nyq b, a = butter(order, normal_cutoff, btype='low', analog=False) y = lfilter(b, a, data) return y # Example usage: #... Q 10. Describe your experience with data mining and analysis in a SIGINT/COMINT context.
Data mining and analysis in a SIGINT/COMINT context is all about extracting meaningful intelligence from massive datasets of intercepted signals. My experience includes using various techniques to identify patterns, trends, and anomalies that could indicate significant events or activities.
For example, I’ve used clustering algorithms to group similar signals together, potentially identifying a network of communication devices or a specific type of activity. Association rule mining can uncover relationships between different communication events, such as specific calls made around a particular time or location.
Anomaly detection techniques are crucial for identifying unusual communication patterns that might signify something significant, such as a planned attack, a change in operational procedure, or even a technical malfunction. To handle the immense volume of data, I’ve utilized various database technologies and parallel processing techniques to optimize analysis speed. I’m also experienced in employing visualization tools to represent the data effectively and communicate key findings to stakeholders.
One project involved analyzing encrypted satellite communications. We used advanced decryption techniques and data mining to identify patterns of communication, revealing a clandestine network related to illicit arms trafficking. This required sophisticated data analysis techniques to extract meaningful information from partially decrypted data.
Q 11. How do you prioritize and manage multiple tasks in a fast-paced environment?
Prioritizing and managing multiple tasks in a fast-paced SIGINT/COMINT environment requires a structured approach. I use a combination of techniques to effectively handle competing demands and tight deadlines.
Firstly, I employ a prioritization matrix, categorizing tasks based on urgency and importance. This ensures that the most critical tasks are addressed first, even if many tasks demand immediate attention.
Secondly, I leverage project management tools, such as task management software, to track progress on multiple projects and tasks simultaneously. This improves organization and team coordination, especially when dealing with multiple analysts working on related but separate projects.
Finally, I emphasize effective communication with colleagues and supervisors, ensuring transparency on my workload and promptly seeking assistance when needed. This includes regularly updating my progress and proactively identifying potential roadblocks that could impact deadlines.
The ability to swiftly adapt to changing priorities is vital, and I’ve demonstrated this ability numerous times, especially when dealing with unexpected urgent requests or the sudden influx of large datasets needing immediate analysis.
Q 12. How do you handle incomplete or ambiguous data in your analysis?
Handling incomplete or ambiguous data is a common challenge in SIGINT/COMINT analysis. My approach involves several strategies to mitigate this problem and still draw meaningful conclusions, whenever possible.
Data imputation techniques are used to fill in missing values, although caution is always exercised to avoid introducing bias. Statistical methods or knowledge of the data’s source can help make reasonable estimates.
Sensitivity analysis helps assess how much impact incomplete data has on conclusions. This approach involves running analyses with various assumptions about missing data to see how sensitive results are to these changes.
Qualitative analysis may be necessary when dealing with truly ambiguous data. This involves using domain knowledge and experience to interpret the available information and formulate plausible explanations, recognizing that the lack of complete information will limit the certainty of the conclusions. It is crucial to clearly state the limitations of the analysis due to data incompleteness.
In some cases, it might be necessary to request additional data or clarify ambiguities with other teams or agencies to improve the quality of future analysis.
Q 13. Describe your experience working with large datasets.
Working with large datasets is an integral part of SIGINT/COMINT operations. I have extensive experience handling datasets ranging from gigabytes to terabytes in size, utilizing various techniques for efficient processing and analysis.
Distributed computing frameworks, such as Hadoop and Spark, are essential for processing datasets that exceed the capacity of a single machine. These frameworks enable parallel processing, significantly reducing processing time.
Database management systems (DBMS), including specialized tools designed for handling time-series data and geospatial information, are crucial for storing, querying, and managing these datasets efficiently.
Data reduction techniques, such as dimensionality reduction and feature selection, are employed to simplify the data while preserving essential information, making analysis more manageable and efficient.
I’ve also been involved in designing and implementing data pipelines to ingest, clean, transform, and load (ETL) large volumes of data into suitable storage and processing systems, maximizing the efficiency and reliability of the overall analysis workflow.
Q 14. Explain your understanding of different communication protocols.
Understanding communication protocols is fundamental to SIGINT/COMINT analysis. My knowledge encompasses a wide range of protocols, from traditional telephony systems to modern digital communication methods.
I’m familiar with various protocols at different layers of the OSI model: At the physical layer, understanding modulation techniques and signal encoding is crucial. At the data link layer, protocols like Ethernet and Wi-Fi are essential for understanding local area network communication. At the network layer, IP protocols (IPv4 and IPv6) dictate how data travels across networks, and at the transport layer, TCP and UDP determine reliable and unreliable data transmission. The application layer contains protocols such as HTTP (web traffic), SMTP (email), and many others specific to certain applications.
Specific experience includes: analyzing VoIP (Voice over IP) communications, identifying encrypted traffic using various cryptographic algorithms, and extracting information from various proprietary communication systems. Knowing these protocols allows us to recognize the type of communication, the level of security used, and ultimately, to interpret the intercepted data more effectively.
My understanding extends to recognizing protocol anomalies, which can often indicate malicious activity or technical issues. For instance, detecting unusual traffic patterns or the use of obfuscation techniques often signals a threat.
Q 15. How do you ensure the accuracy and reliability of your analysis?
Ensuring accuracy and reliability in SIGINT/COMINT analysis is paramount. It’s a multi-layered process involving rigorous verification and validation techniques. Think of it like solving a complex puzzle – you need multiple pieces of evidence fitting perfectly together before you can confidently present a picture.
Source Validation: We meticulously verify the authenticity and trustworthiness of intercepted signals. This involves analyzing signal characteristics, comparing them against known sources, and utilizing triangulation methods (where possible) to pinpoint the origin. For example, identifying a specific radio frequency used by a known organization enhances credibility.
Cross-Correlation: We never rely on a single piece of intelligence. Multiple independent sources and methods are used to corroborate findings. If three different intercepts all point to the same conclusion, the confidence level significantly increases.
Data Quality Control: Our processes incorporate strict data quality checks at every stage. This includes error detection, noise reduction, and data cleansing. Software tools and human expertise work in tandem to ensure the integrity of the data being analyzed.
Peer Review: All analyses undergo a rigorous peer review process. This is critical for identifying biases, overlooking crucial details, and improving overall accuracy. It’s a built-in safeguard against human error.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. Describe your experience with reporting and presenting your findings.
Reporting and presenting findings are crucial aspects of the job, demanding clarity, precision, and an ability to convey complex information to a diverse audience. Imagine explaining a sophisticated technical puzzle to a non-technical manager – that’s the challenge.
Structured Reporting: We utilize standardized report formats, including executive summaries for quick understanding and detailed technical sections for in-depth analysis. Visualizations like graphs and charts are used to illustrate key findings.
Tailored Communication: The level of technical detail adjusts depending on the audience. A technical report for analysts will differ significantly from a brief for senior management.
Data Visualization: We effectively use visualization tools to represent complex datasets. This might involve mapping geolocation data, illustrating network connections, or visualizing communication patterns over time. A clear visual representation greatly aids understanding.
Presentation Skills: I possess strong presentation skills, able to explain complex topics concisely and confidently, both verbally and in writing. I have presented findings at numerous briefings and conferences.
Q 17. How do you stay up-to-date with the latest advancements in SIGINT/COMINT technologies?
The field of SIGINT/COMINT is constantly evolving, so staying current is essential. Think of it as a continuous learning process. New technologies emerge regularly, demanding adaptation and learning.
Professional Development: I actively participate in professional development programs, conferences, and workshops to remain abreast of the latest advancements in signal processing, data analytics, and cybersecurity.
Industry Publications: I regularly read journals and publications specializing in SIGINT, COMINT, and related fields like cybersecurity and cryptography. This provides insight into cutting-edge research and techniques.
Online Resources: I utilize various online resources such as academic databases, industry blogs, and webinars to maintain my knowledge of emerging technologies and best practices.
Collaboration with Peers: Discussions and collaborations with colleagues from different organizations and backgrounds are invaluable for sharing knowledge and learning new approaches.
Q 18. How do you collaborate with other team members in a SIGINT/COMINT environment?
Collaboration is the cornerstone of successful SIGINT/COMINT operations. It’s a team effort, requiring seamless coordination and information sharing to achieve objectives. Think of it like a well-orchestrated symphony.
Data Sharing: We utilize secure platforms for sharing raw data and analytical findings among team members. This fosters transparency and allows for efficient collaboration.
Regular Briefings: We conduct regular team briefings to update each other on progress, share insights, and coordinate efforts. This ensures everyone is on the same page.
Specialized Skills: Our team consists of individuals with diverse skills, such as signal analysts, linguists, and network specialists. This diversity allows for a comprehensive approach to intelligence gathering and analysis.
Communication Tools: Secure communication tools facilitate immediate sharing of critical information and enable real-time collaboration during urgent situations.
Q 19. What is your experience with geolocation techniques in SIGINT/COMINT?
Geolocation techniques are vital in SIGINT/COMINT, allowing us to pinpoint the geographical location of communication sources. It’s like using a sophisticated map to pinpoint the source of a signal.
Triangulation: By using signals received at multiple intercept sites, we can triangulate the source’s location. This is a common method, especially for radio transmissions.
Direction Finding (DF): DF antennas help determine the direction of incoming signals, providing crucial information for geolocation. It’s like using a compass to narrow down the source’s position.
Cellular Network Analysis: Analyzing cellular network data (like cell tower IDs) associated with intercepted communications can pinpoint the approximate location of a mobile device.
IP Address Geolocation: Though less precise, the IP address associated with a network connection can provide a general geographical location of the source. This requires careful consideration and may not be completely accurate.
Q 20. Describe your experience with network analysis in a SIGINT/COMINT context.
Network analysis is crucial for understanding communication patterns and identifying key players within a network. Think of it as mapping the connections and relationships within a complex system.
Traffic Analysis: We analyze communication traffic volumes, patterns, and frequencies to identify significant activities and potential targets. This could reveal patterns of communication that indicate suspicious activity.
Protocol Analysis: We analyze the protocols used in communications, identifying protocols and decoding messages. Understanding the protocols used gives insight into the nature of the communication.
Network Mapping: We create visual representations of communication networks to identify relationships between various entities and potential vulnerabilities. Think of it as creating a visual network map to pinpoint relationships and weak points.
Malware Analysis: In many cases, network analysis plays a crucial role in identifying and analyzing malware used in cyberattacks. Identifying the spread of malware within a network is a key aspect of this analysis.
Q 21. Explain your understanding of cryptography and cryptanalysis.
Understanding cryptography and cryptanalysis is fundamental to SIGINT/COMINT. Cryptography protects information; cryptanalysis breaks those protections. It’s a continuous arms race.
Cryptography: This involves studying the mathematical principles and techniques used to create secure communication channels. We understand various encryption algorithms, hash functions, and digital signature schemes to interpret protected communications.
Cryptanalysis: This focuses on finding weaknesses and vulnerabilities in cryptographic systems, to recover the plaintext from ciphertext. Techniques range from brute force attacks to exploiting known vulnerabilities.
Modern Cryptography: I have a strong understanding of modern cryptographic techniques, including public-key cryptography (RSA, ECC), symmetric-key cryptography (AES, DES), and hash algorithms (SHA-256, MD5). The knowledge of these algorithms allows for a deep understanding of the strengths and weaknesses of their implementations.
Practical Application: My experience includes analyzing encrypted communications to extract intelligence, identifying weaknesses in encryption schemes used by targets, and developing countermeasures to protect our own communications.
Q 22. How do you handle conflicting information or contradictory data?
Conflicting information is a common challenge in SIGINT/COMINT. We approach it systematically, prioritizing verification and triangulation. Think of it like piecing together a puzzle with some missing or contradictory pieces.
- Source Evaluation: We critically assess the reliability of each source. Is it a known accurate source? Is the communication method secure? Has this source provided reliable information in the past?
- Cross-Referencing: We compare the conflicting information with other intelligence reports, technical data, and open-source information to identify patterns and inconsistencies. This is essentially corroborating the information with multiple sources.
- Data Analysis Techniques: We utilize advanced analytical methods, such as statistical analysis or network analysis, to identify potential biases or errors in the data. For instance, if two sources give conflicting location data, analyzing the signal strength and propagation could help determine the more credible location.
- Human Intelligence (HUMINT) Integration: Sometimes, human intelligence can be used to validate or refute the technical intelligence collected. Ground truth is key, and sometimes that comes from human sources.
- Reporting and Uncertainty: Finally, we clearly report any uncertainty associated with the intelligence. Transparency is paramount, especially in cases of conflicting information. We might highlight that there are discrepancies and explain the rational basis for our ultimate conclusion.
For example, if one intercept suggests a meeting between two individuals in location A while another indicates location B, we’d investigate both locations, examine the signal characteristics to pinpoint the most probable location and assess the reliability of the communication channels used.
Q 23. What is your experience with signal jamming and countermeasures?
Signal jamming and countermeasures are crucial aspects of SIGINT/COMINT. My experience encompasses both defensive and offensive techniques.
- Jamming Detection and Mitigation: I’m proficient in identifying various jamming techniques, like noise jamming or sweep jamming, and implementing countermeasures such as frequency hopping, spread spectrum techniques, and adaptive signal processing to overcome interference.
- Counter-Jamming Strategies: I’ve worked on developing and implementing strategies to circumvent jamming efforts, which often involves analyzing the jamming signal itself to learn its characteristics and developing methods to work around the noise. This might include predicting patterns or using different communication frequencies or waveforms.
- Signal Security Measures: I have experience implementing and maintaining security measures to protect our own communications from interception and jamming. This is often achieved using encryption techniques or robust communication protocols.
For instance, during a past operation, we encountered a sophisticated barrage jamming signal that was targeting our intercept capabilities. We analyzed the jamming signal’s characteristics, identified its frequency hopping pattern, and developed a countermeasure that effectively filtered out the interference while still allowing us to receive the target signals.
Q 24. Describe your experience with using specialized software for SIGINT/COMINT analysis.
My experience with specialized SIGINT/COMINT software is extensive. I am proficient in several platforms, including those for signal processing, traffic analysis, and data mining.
- Signal Processing Software: I’ve utilized software packages to perform tasks like digital signal processing, modulation recognition, and signal demodulation. Software such as
MATLABandGNU Radioare key tools for this. - Traffic Analysis Tools: I’m experienced in using software to analyze communication patterns, identify network topologies, and infer relationships between communication nodes. This often involves identifying unique identifiers and analyzing routing protocols.
- Data Mining and Analytics: I can leverage data mining techniques and algorithms to extract meaningful insights from large datasets of intercepted communications. This may involve using SQL, Python libraries (
Pandas,Scikit-learn), or specialized data analysis platforms to identify trends, anomalies and key data points. - Specialized SIGINT/COMINT Platforms: I have experience with various proprietary systems and software, which are generally restricted and require specialized training to use effectively. These systems often offer comprehensive analysis capabilities and integrated workflow processes.
One example involves using a specific traffic analysis platform to identify a covert communication network used by a criminal organization. Through analysis of call durations, frequencies and call times, we were able to build a detailed picture of the network’s structure, identifying key nodes and individuals.
Q 25. How do you maintain confidentiality and security protocols?
Maintaining confidentiality and security is paramount in SIGINT/COMINT. My approach involves adhering to strict protocols and best practices at all levels.
- Data Encryption: We employ robust encryption algorithms at every stage of the intelligence lifecycle, from interception to storage and analysis. This ensures that unauthorized access to sensitive data is prevented.
- Access Control: Strict access control measures are in place, using role-based access control, to restrict data access to authorized personnel only. This involves using strong passwords and multi-factor authentication.
- Secure Data Handling: All data is handled according to strict security protocols, including secure storage, transmission, and disposal techniques. Physical and cybersecurity protocols are carefully maintained to avoid compromising sensitive information.
- Compliance with Regulations: I meticulously adhere to all relevant laws, regulations, and policies pertaining to data security and handling of sensitive information. This often involves regularly updating our security systems to adapt to evolving threat landscape.
- Regular Security Audits: We conduct regular security audits and penetration tests to identify and address any vulnerabilities in our systems and processes. This helps to ensure that our security measures are always up-to-date and effective.
For example, all our systems are regularly monitored for unauthorized access attempts, and any detected attempts are immediately investigated and addressed. Data is also regularly backed up to secure locations and routinely purged following established retention policies.
Q 26. Describe a time you had to solve a complex technical problem related to SIGINT/COMINT.
One challenging problem involved identifying the source of an intermittent, highly encrypted communication signal. The signal was weak, fleeting, and heavily masked by background noise.
- Signal Enhancement Techniques: We employed advanced signal processing techniques, including adaptive filtering and wavelet transforms, to enhance the signal and minimize noise interference.
- Advanced Algorithm Development: We then needed to develop a custom algorithm for decrypting the communication signal. This involved examining the encryption method and crafting our own method to bypass the security implemented.
- Correlation with Other Data: Finally, we corroborated the decoded information with other intelligence, such as geolocation data and HUMINT reports, to verify the findings and gain a complete picture.
This multi-stage process resulted in the identification of the signal’s source and its significance, which eventually contributed to a major intelligence breakthrough. This experience demonstrated the importance of collaborative problem-solving, creativity, and the ability to integrate diverse data sources in SIGINT/COMINT operations.
Q 27. How do you adapt to changing priorities and unexpected challenges?
Adaptability is critical in SIGINT/COMINT. Prioritization and problem-solving skills are paramount.
- Prioritization: I use a risk-based approach to prioritize tasks, focusing on the most critical intelligence requirements first. This involves assessing the urgency, importance, and potential impact of each task.
- Flexible Workstyle: I’m comfortable working independently or as part of a team, adapting my workflow to meet the demands of each situation. This means being able to quickly shift focus and handle multiple priorities.
- Proactive Problem Solving: I anticipate potential challenges and develop contingency plans to mitigate risks. This includes having backup plans and processes in place to deal with unexpected changes or delays.
- Continuous Learning: I continually update my skills and knowledge to stay ahead of technological advancements and evolving threats. This means staying up-to-date with the latest software, hardware and analytical techniques.
For instance, during a rapidly evolving situation, we had to quickly shift our focus from a long-term project to analyze a high-priority target. I was able to quickly adapt my processes, prioritize relevant tasks, and collaborate with my team to deliver critical intelligence within the strict deadline.
Q 28. What are your salary expectations?
My salary expectations are commensurate with my experience and skills in the field, and I am open to discussing this further once I have a better understanding of the full scope of the role and the company’s compensation structure.
Key Topics to Learn for SIGINT/COMINT Intercept Operations Interview
- Signal Processing Fundamentals: Understanding concepts like signal modulation, demodulation, filtering, and digital signal processing is crucial. Consider exploring different types of modulation techniques and their strengths/weaknesses.
- COMINT Systems and Technologies: Familiarize yourself with various interception technologies, their capabilities, and limitations. This includes antenna systems, receivers, and signal analyzers. Understanding the practical applications of these technologies in real-world scenarios is key.
- SIGINT Data Analysis and Interpretation: Develop a strong understanding of how to analyze intercepted data, identify patterns, and extract meaningful intelligence. Practice interpreting complex data sets and drawing accurate conclusions.
- Cybersecurity and Network Protocols: A solid grasp of network protocols (TCP/IP, etc.) and common cybersecurity threats is essential for understanding the context of intercepted communications.
- Intelligence Gathering Methods and Legal Frameworks: Understand the legal and ethical considerations surrounding SIGINT/COMINT operations and the importance of adhering to regulations and guidelines. Familiarize yourself with different intelligence gathering methods and their implications.
- Problem-Solving and Critical Thinking: Practice applying your technical knowledge to solve complex problems related to signal analysis, data interpretation, and system troubleshooting. The ability to think critically and creatively is highly valued.
- Data Visualization and Reporting: Develop skills in presenting your findings in a clear, concise, and impactful manner through data visualization and reporting techniques.
Next Steps
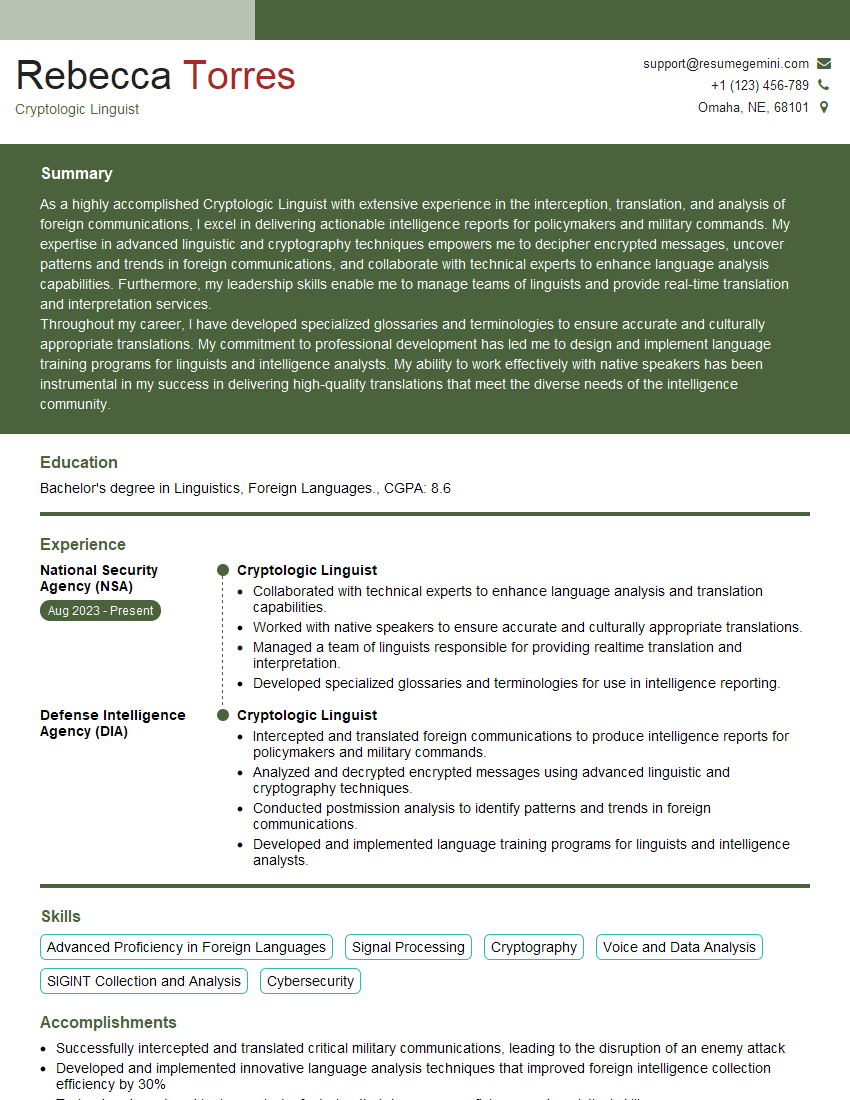
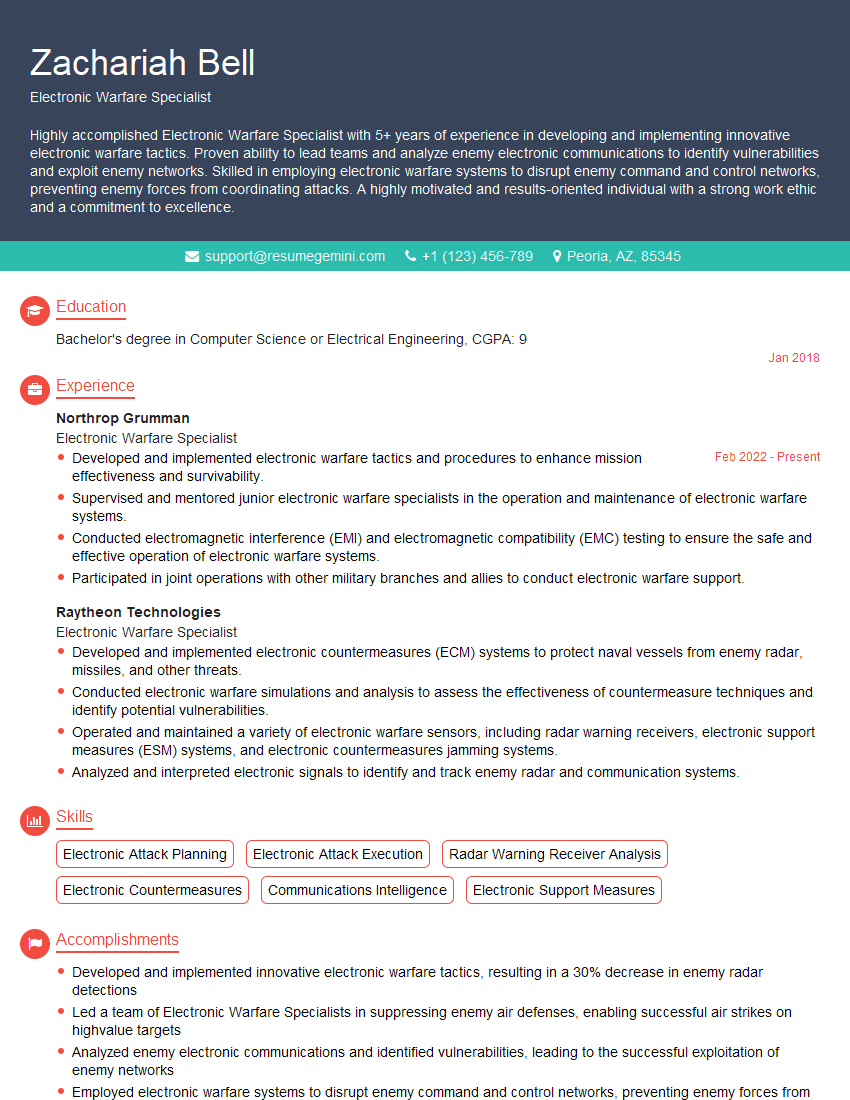
Mastering SIGINT/COMINT Intercept Operations opens doors to a rewarding career with significant growth potential in a dynamic and intellectually stimulating field. To maximize your job prospects, creating a strong, ATS-friendly resume is critical. ResumeGemini is a trusted resource that can help you build a professional and impactful resume tailored to highlight your skills and experience. ResumeGemini provides examples of resumes specifically designed for SIGINT/COMINT Intercept Operations roles, ensuring your application stands out. Invest time in crafting a compelling narrative that showcases your unique contributions and ambitions; this is your first opportunity to impress potential employers.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good