Feeling uncertain about what to expect in your upcoming interview? We’ve got you covered! This blog highlights the most important SIGINT/EW Tactics and Procedures interview questions and provides actionable advice to help you stand out as the ideal candidate. Let’s pave the way for your success.
Questions Asked in SIGINT/EW Tactics and Procedures Interview
Q 1. Explain the difference between COMINT, ELINT, and FISINT.
SIGINT (Signals Intelligence) is a broad term encompassing the interception and analysis of electronic signals. It’s broken down into several sub-disciplines, the most prominent being COMINT, ELINT, and FISINT.
- COMINT (Communications Intelligence): This focuses on the interception and analysis of communications, such as radio, telephone, and internet traffic. Think of it like listening to a conversation – the goal is to understand the content of the communication and what it reveals. For example, intercepting a terrorist group’s radio chatter planning an attack provides valuable COMINT.
- ELINT (Electronic Intelligence): This involves the interception and analysis of non-communication electronic signals. This could be radar emissions, electronic warfare signals, or even signals from satellites. Imagine identifying a new type of radar system based on its unique signal characteristics – that’s ELINT in action. It’s about understanding the technology and capabilities of the emitter.
- FISINT (Foreign Instrumentation Signals Intelligence): This deals with the interception and analysis of signals from foreign sensors and instrumentation systems. This might include data from foreign meteorological satellites or scientific research instruments. It is often used to understand a country’s scientific and technological advancements.
In essence, while all three fall under the SIGINT umbrella, COMINT focuses on what is being said, ELINT on what systems are being used, and FISINT on what data those systems are collecting.
Q 2. Describe the process of SIGINT collection and analysis.
SIGINT collection and analysis is a multi-stage process. It begins with the collection phase, which involves:
- Target Identification: Identifying potential sources of valuable intelligence.
- Sensor Deployment: Using various sensors (satellites, ground stations, aircraft) to intercept signals.
- Signal Reception: Capturing the raw signals.
Once collected, the data moves to the analysis phase, encompassing:
- Signal Processing: Filtering out noise and isolating relevant signals.
- Signal Identification: Determining the type of signal (e.g., voice, data, radar).
- Traffic Analysis: Analyzing communication patterns to gain insight even without fully understanding the content.
- Content Analysis: Decrypting or interpreting the message content.
- Data Fusion: Combining intelligence from multiple sources to create a complete picture.
- Reporting: Presenting the findings in a clear and concise manner to decision-makers.
Imagine trying to piece together a puzzle; the collection phase is gathering all the pieces, and the analysis phase is arranging them to reveal the complete picture. Each stage relies on specialized tools, techniques, and expertise to achieve the final goal of providing actionable intelligence.
Q 3. What are the key vulnerabilities of common communication systems?
Common communication systems face a range of vulnerabilities, often stemming from design flaws or operational weaknesses. Here are a few key ones:
- Weak Encryption: Many systems employ weak or outdated encryption algorithms, making them susceptible to decryption.
- Unpatched Software: Outdated software with known vulnerabilities provides attackers with easy entry points.
- Poor Physical Security: Insufficient protection of equipment or facilities allows for unauthorized access and interception.
- Man-in-the-Middle Attacks: Interceptors can position themselves between communicating parties to eavesdrop or manipulate the communication.
- Side-Channel Attacks: Attackers can exploit subtle information leaks (power consumption, timing variations) to glean sensitive information, even with strong encryption.
- Lack of Authentication: Absence of robust authentication mechanisms allows imposters to gain unauthorized access.
For instance, a poorly secured Wi-Fi network might be vulnerable to man-in-the-middle attacks, allowing an interceptor to steal login credentials or inject malicious code.
Q 4. How do you perform signal geolocation?
Signal geolocation involves pinpointing the location of a signal emitter. The accuracy depends on several factors, including the signal’s characteristics, the number of receiving stations, and the environment. Techniques used include:
- Triangulation: Using the time difference of arrival (TDOA) of a signal at multiple receiving stations to locate the source. Imagine three people listening to a gunshot; by noting the time difference in hearing the sound, they can approximate the gun’s location.
- Interferometry: This precise method uses the phase difference of signals at multiple receivers to achieve higher accuracy.
- Direction Finding (DF): Antennas with directional sensitivity are used to determine the bearing of the signal.
- Signal Signature Analysis: Analyzing signal characteristics can help to identify and locate specific types of emitters.
Often, multiple techniques are combined for improved accuracy. For example, DF can provide a bearing, which is then combined with TDOA measurements from multiple stations to achieve accurate geolocation. The complexity increases significantly in challenging environments with multipath propagation (signals bouncing off objects) or signal jamming.
Q 5. Explain the concept of electronic support measures (ESM).
Electronic Support Measures (ESM) encompass the passive detection, identification, location, and analysis of electromagnetic emissions. It’s like having highly sophisticated ears and eyes for electronic signals. The focus is solely on receiving and analyzing signals; there is no active transmission involved. ESM systems are used to:
- Identify Threats: Detect enemy radar, communication systems, and other emitters.
- Assess Capabilities: Determine the capabilities and locations of enemy forces.
- Provide Situational Awareness: Build a picture of the electronic battlefield.
Think of a military aircraft equipped with ESM; it can passively detect enemy radar emissions, allowing it to determine the location and type of radar, and potentially use that information to evade detection or plan countermeasures.
Q 6. Describe different types of electronic countermeasures (ECM).
Electronic Countermeasures (ECM) are active techniques employed to disrupt or deceive enemy electronic systems. It’s the active response to ESM, aiming to either degrade or deny the enemy’s ability to use their electronic systems. Types of ECM include:
- Jamming: Overpowering or interfering with an enemy signal to render it unusable. Think of it as shouting over someone to prevent them from being heard.
- Deception: Creating false signals to confuse or mislead enemy systems. This could involve creating fake radar returns to distract or misdirect enemy targeting systems.
- Spoofing: Sending false signals that mimic legitimate signals to manipulate or control enemy systems. This can involve sending a fake GPS signal to disrupt navigation systems.
- Chaff and Flare: These are physical countermeasures used to distract radar or other sensors. Chaff releases metallic strips that create false radar returns while flares release heat to distract infrared sensors.
The choice of ECM depends on the specific threat and the desired outcome. A simple jamming technique might be effective against a weak signal, whereas more sophisticated deception techniques might be necessary to counter advanced systems.
Q 7. How do you identify and analyze electronic signals in a complex environment?
Identifying and analyzing electronic signals in a complex environment is a challenging task. The process involves:
- Signal Sorting: Separating signals based on frequency, modulation, and other characteristics. This involves advanced signal processing techniques to differentiate between multiple overlapping signals.
- Signal Classification: Identifying the type of signal (e.g., radar, communication, navigation). This often requires a deep understanding of signal waveforms and modulation techniques.
- Signal Parameter Extraction: Determining key parameters like frequency, bandwidth, pulse repetition frequency (for radar), and modulation type.
- Pattern Recognition: Identifying patterns in the signals to determine their purpose and origin. This often requires specialized algorithms and expertise.
- Data Correlation: Combining information from multiple sources to create a more comprehensive picture. This might involve integrating ESM data with intelligence reports or geographic information.
Imagine a busy radio frequency spectrum; it’s like trying to pick out individual conversations in a crowded room. Advanced signal processing techniques, coupled with domain expertise, are essential to isolate and analyze signals in such complex environments. Tools like sophisticated spectral analyzers and specialized software play a crucial role in this process.
Q 8. What are the ethical considerations in SIGINT/EW operations?
Ethical considerations in SIGINT/EW operations are paramount. We’re dealing with the interception and manipulation of communications, potentially impacting privacy and national security. Key concerns include adherence to domestic and international laws, such as the Fourth Amendment in the US or the European Convention on Human Rights.
- Minimizing Intrusion: We must only collect the intelligence necessary for the mission and avoid unnecessary surveillance.
- Data Security and Privacy: Protecting collected data from unauthorized access and misuse is critical, often involving strict encryption and access control protocols.
- Transparency and Accountability: Clear oversight mechanisms and reporting procedures are needed to ensure responsible use of these powerful capabilities.
- Proportionality: The potential harm caused by the operation should not outweigh the intelligence gained.
- Targeting: Strict adherence to pre-approved targeting parameters to avoid civilian casualties and collateral damage. Unintended interception of communications needs to be addressed.
For example, imagine intercepting a phone call. While the call might contain valuable intelligence, we must only focus on the relevant portions and securely store that data, adhering to all privacy regulations.
Q 9. Explain the concept of signal jamming and its limitations.
Signal jamming involves transmitting a signal on the same frequency as a target communication, overwhelming it and rendering it unusable. Think of it like shouting over someone to prevent them from being heard.
However, jamming has limitations:
- Limited Range: Jamming effectiveness diminishes significantly with distance.
- Frequency-Specific: A jammer only disrupts transmissions on its specific frequency. A sophisticated target might shift frequencies or use alternative communication methods.
- Detection: Jamming activity itself can be detected, revealing the jammer’s location and potentially leading to countermeasures.
- Collateral Damage: Jamming can unintentionally disrupt friendly communications operating on the same or nearby frequencies.
- Power Consumption: High-power jamming requires significant energy, impacting operational endurance.
Imagine a scenario where a hostile entity is using a radio frequency to coordinate attacks. While jamming their communications might initially seem effective, they could switch to a backup system, utilize encrypted channels, or simply move to a different frequency band.
Q 10. Describe various techniques for electronic deception.
Electronic deception involves manipulating enemy sensors and systems to mislead or confuse them. This can involve various techniques:
- Spoofing: Mimicking legitimate signals to create false impressions, such as simulating the location of friendly aircraft to mislead enemy targeting systems.
- Masking: Concealing friendly transmissions by using techniques like low probability of intercept (LPI) radar.
- Simulation: Creating realistic simulations of enemy equipment to test their capabilities or draw their fire.
- Injection: Inserting false data into enemy systems to disrupt their operations or manipulate their decision-making.
- Deception jamming: Sending false signals to confuse or mislead enemy systems, for example, making it appear there are more friendly aircraft than there really are.
For example, during a military operation, we could employ spoofing to create false radar returns, making it appear that our forces are in a different location or in greater numbers than they actually are.
Q 11. How do you prioritize intelligence targets?
Prioritizing intelligence targets involves a systematic approach. We consider factors like:
- Relevance to current operational needs: Targets that provide the most immediate impact on mission objectives.
- Value of intelligence: The potential impact of intelligence gained from the target on the overall mission objective.
- Feasibility of collection: The likelihood of successfully gathering intelligence from the target, considering technical and operational challenges.
- Risk assessment: The potential risks of targeting a specific entity (e.g., exposure of our capabilities).
- Urgency: The time sensitivity of the information needed. Time-sensitive intelligence requires immediate prioritization.
This is often done through a structured process involving multi-disciplinary teams and often involves a weighted scoring system considering each factor.
Q 12. What are the challenges in operating SIGINT/EW systems in contested environments?
Contested environments present unique challenges for SIGINT/EW systems:
- Increased threat of detection and attack: Enemy forces actively seek to detect and disrupt SIGINT/EW operations.
- Electronic warfare (EW) countermeasures: The adversary might employ jamming, spoofing, or other techniques to hinder our capabilities.
- Signal degradation: Obstacles, terrain, and environmental factors can significantly degrade signal quality.
- Limited access and maneuverability: Deployment and operation might be restricted due to hostile activity.
- Cybersecurity threats: SIGINT/EW systems are vulnerable to cyberattacks, potentially compromising their integrity and functionality.
Consider the complexity of operating in a high-intensity conflict zone, where enemy EW systems attempt to blind our sensors while simultaneously using sophisticated methods to mask their own communications.
Q 13. How do you maintain operational security (OPSEC) during SIGINT/EW operations?
Maintaining OPSEC during SIGINT/EW operations is crucial. This includes:
- Emission control: Minimizing unintentional signal emissions that could reveal our location or capabilities.
- Communication security (COMSEC): Employing secure communication channels to prevent adversaries from intercepting sensitive information.
- Physical security: Protecting equipment and personnel from physical access and compromise.
- Compartmentalization: Restricting access to classified information and operational plans on a need-to-know basis.
- Situational awareness: Maintaining a constant awareness of the surrounding environment and potential threats.
For example, strict protocols on where and when we operate, combined with stringent communication security measures and regular audits of our systems, help ensure that no information leaks.
Q 14. What are the legal and regulatory aspects of SIGINT/EW activities?
Legal and regulatory aspects of SIGINT/EW activities are complex and vary by country. Key considerations include:
- Domestic laws: Adherence to national laws governing surveillance, privacy, and data protection.
- International treaties and agreements: Respect for international norms and agreements limiting interference with communications.
- Authorization and oversight: Clear authorization procedures and oversight mechanisms to prevent abuse of power.
- Targeting restrictions: Limitations on the types of targets that can be intercepted and the information that can be collected.
- Data handling and retention: Regulations on how intercepted data is handled, stored, and destroyed.
Imagine the legal ramifications of intercepting communications without proper authorization. This could lead to serious legal consequences, both domestically and internationally, for the individuals and organizations involved. All operations require meticulous planning and strict adherence to applicable laws.
Q 15. Explain the role of metadata in SIGINT analysis.
Metadata, in the context of SIGINT, is the information *about* the intercepted signal, rather than the content itself. Think of it as the ‘envelope’ containing the message. It’s surprisingly valuable. Analyzing metadata can reveal a wealth of information even without decrypting the signal’s content.
- Time stamps: Precise timestamps reveal communication patterns and potentially identify operational schedules or routines.
- Source and destination: Identifying the origin and recipient of a communication can pinpoint individuals, locations, or systems of interest.
- Frequency and bandwidth: These characteristics can help identify the type of communication system being used (e.g., satellite phone, radio, etc.).
- Signal strength: Fluctuations in signal strength can indicate the transmitter’s location or movement.
- Modulation type: The method used to encode information onto the signal can offer clues about the sophistication of the system and the potential encryption techniques.
For example, discovering numerous communications originating from a specific geographic location at unusual hours might suggest a clandestine operation. Similarly, a sudden increase in communication volume shortly before a known event could indicate preparation for an attack or other activity.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. Describe various methods for signal encryption and decryption.
Signal encryption and decryption are fundamental aspects of SIGINT. Encryption aims to render intercepted communications unintelligible, while decryption seeks to recover the original message.
- Symmetric Encryption: Both sender and receiver use the same key for encryption and decryption. Examples include AES (Advanced Encryption Standard) and DES (Data Encryption Standard). While simpler to implement, secure key exchange is a major challenge.
- Asymmetric Encryption: Uses a pair of keys – a public key for encryption and a private key for decryption. RSA (Rivest-Shamir-Adleman) is a prominent example. This allows secure communication without pre-sharing a secret key, but is computationally more intensive.
- Steganography: This technique hides the message within another, seemingly innocent, message. This isn’t technically encryption, but it avoids detection of the communication itself.
- Spread Spectrum: Spreads the signal across a wide frequency range making interception and analysis difficult. Techniques include Frequency Hopping Spread Spectrum (FHSS) and Direct Sequence Spread Spectrum (DSSS).
Decryption methods range from brute-force attacks (trying every possible key) to exploiting vulnerabilities in encryption algorithms. Advances in computing power and cryptanalysis continuously challenge and refine these methods.
Q 17. How do you assess the reliability of SIGINT sources?
Assessing the reliability of SIGINT sources is crucial for accurate intelligence analysis. It involves a multi-faceted approach.
- Source Provenance: Understanding the origin of the signal is paramount. Is it from a known system with a proven track record, or an unknown source with potential biases or deliberate misinformation?
- Signal Integrity: Is the signal clear, or is it corrupted by noise or interference? A degraded signal can lead to misinterpretations.
- Technical Validation: Does the intercepted signal conform to known communication protocols and standards? Deviations might indicate manipulation or deliberate obfuscation.
- Cross-Correlation: Comparing the information gathered from this source with information obtained from other, independent sources helps to verify or refute the initial findings.
- Historical Performance: How reliable has this source been in the past? A history of accurate reporting enhances confidence, whereas a history of inaccuracies raises concerns.
For example, a signal intercepted from a known enemy communication satellite will generally be considered more reliable than one from an unverified, untraceable source. Always consider the context and potential biases when evaluating a source’s reliability.
Q 18. Explain the concept of SIGINT integration with other intelligence disciplines.
SIGINT doesn’t operate in isolation; its effectiveness is significantly enhanced by integration with other intelligence disciplines. This fusion creates a more comprehensive understanding of the target.
- HUMINT (Human Intelligence): Information gathered from human sources can corroborate or contextualize SIGINT findings. For instance, HUMINT might identify the individuals involved in intercepted communications, providing a ‘who’ to the SIGINT’s ‘what’.
- IMINT (Imagery Intelligence): Satellite or aerial imagery can pinpoint the geographical location of communication equipment identified through SIGINT, adding a ‘where’ to the intelligence puzzle.
- OSINT (Open Source Intelligence): Publicly available information can provide background context and corroborate details from SIGINT. News reports, social media, and other open sources can often provide valuable supplementary information.
- MASINT (Measurement and Signature Intelligence): MASINT can provide details about the physical characteristics of a target’s technology or equipment, helping identify the specifics of the system producing the intercepted signal.
Consider a scenario where SIGINT intercepts coded messages. HUMINT might identify the individuals involved, IMINT might locate their position, and OSINT might reveal details about their known activities, building a cohesive understanding of their operation.
Q 19. Describe your experience with SIGINT/EW software and tools.
My experience encompasses a range of SIGINT/EW software and tools, from signal processing and analysis platforms to geolocation and decryption software. I’m proficient in using tools like [mention specific software – e.g., specialized signal analysis software, geospatial intelligence tools, cryptographic analysis packages]. This includes expertise in their application to real-world scenarios, from detecting and identifying signals to analyzing their content and metadata. I’m also familiar with operating various interception and direction-finding systems.
For example, in a recent project, I utilized [mention a specific tool and its function in a project] to [describe a specific achievement using the tools]. My experience covers both the technical aspects of operating and maintaining the systems and the analytical skills needed to interpret the data effectively.
Q 20. How do you handle conflicting intelligence information?
Conflicting intelligence information is a common challenge. Handling it requires a methodical and critical approach.
- Source Evaluation: Re-assess the reliability of each source. Which source has a stronger track record? Are there known biases that could explain the discrepancy?
- Data Triangulation: Look for corroborating information from other independent sources. Does another source support one claim over the other?
- Contextual Analysis: Consider the context in which the information was obtained. Might different circumstances have led to different reporting?
- Alternative Explanations: Explore other possible interpretations of the data. Are there any alternative hypotheses that could explain the apparent contradiction?
- Further Investigation: If the conflict remains unresolved, additional investigation might be necessary. This could involve gathering more data or using different analytical techniques.
A good analogy is a puzzle with missing or conflicting pieces. Careful analysis, cross-referencing, and persistence are needed to create a complete and accurate picture.
Q 21. How do you present your findings to non-technical audiences?
Presenting SIGINT findings to non-technical audiences requires careful communication strategies. The key is to translate technical jargon into plain language, utilizing visuals and analogies to enhance understanding.
- Simplify Terminology: Avoid technical terms or explain them clearly if unavoidable. Use metaphors and analogies to make abstract concepts relatable.
- Visual Aids: Use charts, maps, and graphs to illustrate key points. Visuals are more engaging and easier to grasp than dense text.
- Storytelling: Frame the findings as a narrative, focusing on the implications and consequences rather than technical details. This increases engagement and makes the information more memorable.
- Focus on the ‘So What?’: Emphasize the significance and relevance of the findings. What are the practical implications for decision-making?
- Interactive Sessions: Allow for questions and discussion to ensure clarity and address any uncertainties.
For example, instead of saying ‘we intercepted a series of frequency-hopped signals using a direction-finding array,’ I might say, ‘we detected several secret communications from a location we were able to pinpoint on a map, showing suspicious activity.’ This approach fosters understanding and buy-in.
Q 22. Explain your experience with data visualization and reporting.
Data visualization and reporting are crucial for effectively communicating complex SIGINT/EW data. My experience involves transforming raw signals and intercepted communications into actionable intelligence using various tools and techniques. This includes creating interactive dashboards showcasing trends, anomalies, and patterns in real-time.
For instance, I’ve used tools like Tableau and Python libraries (Matplotlib, Seaborn) to visualize network traffic, geolocation data from intercepted communications, and signal strength variations over time. These visualizations were instrumental in identifying potential threats, pinpointing enemy locations, and assisting in the development of countermeasures. I also have experience generating reports that clearly articulate findings, methodologies, and recommendations for decision-makers, often including statistical analysis to support conclusions. A key aspect of my reporting involves tailoring the complexity of the presentation to the audience, ensuring clear and concise delivery whether addressing technical experts or senior leadership.
Q 23. Describe a situation where you had to troubleshoot a SIGINT/EW system.
During a large-scale exercise simulating a cyberattack, our SIGINT system experienced a significant drop in data throughput. Initially, the issue manifested as incomplete data packets received from our primary collection node. My troubleshooting process began with a systematic investigation, using diagnostic tools to isolate the problem’s source. We first checked the network infrastructure for any connectivity issues. Finding none, we then inspected the system logs for error messages, which indicated a potential problem with the data processing module. We narrowed it down to a memory leak within the algorithm responsible for filtering raw data. We identified the specific code segment causing the leak by examining the system’s memory usage patterns using dedicated monitoring tools. The solution involved optimizing the algorithm to manage memory more efficiently, and deploying a patched version of the software. Post-patch, we conducted rigorous testing to validate the fix and ensure it didn’t introduce further complications. This experience highlighted the importance of meticulous logging, robust testing, and a systematic approach to troubleshooting complex systems.
Q 24. How do you stay up-to-date with the latest advancements in SIGINT/EW technology?
Staying current in the rapidly evolving field of SIGINT/EW requires a multifaceted approach. I regularly attend industry conferences and workshops, such as those hosted by IEEE or similar organizations, to learn about cutting-edge technologies and emerging threats. I actively participate in professional communities and online forums, engaging in discussions with peers and experts. This helps me stay abreast of the latest research and developments. I subscribe to industry-specific journals and publications, and carefully read reports from government and think tanks. Furthermore, I leverage online learning platforms for specialized training on new technologies and techniques. Finally, hands-on experience through practical application and simulations plays a crucial role in solidifying my understanding and keeping my skills sharp.
Q 25. What are your strengths and weaknesses in the context of SIGINT/EW work?
My strengths lie in my analytical abilities, my deep understanding of SIGINT/EW principles, and my experience in troubleshooting complex systems. I am adept at identifying patterns and anomalies in large datasets, and I possess strong problem-solving skills. I also pride myself on my ability to effectively communicate technical information to both technical and non-technical audiences. A weakness I am actively working on is delegation. While I’m highly detail-oriented, I sometimes find it challenging to relinquish control and trust others with specific tasks. I am actively working on improving my delegation skills through training and by consciously delegating more tasks in a structured manner to build the team’s capabilities.
Q 26. How do you manage stress and pressure in high-stakes situations?
SIGINT/EW work often involves high-pressure situations with tight deadlines and significant consequences. My approach to managing stress involves prioritizing tasks, breaking down complex problems into smaller, manageable components, and taking regular breaks to avoid burnout. I also prioritize maintaining a healthy work-life balance, engaging in activities like exercise and mindfulness practices to help mitigate stress. In high-stakes scenarios, I focus on maintaining clear communication with my team, ensuring everyone is aware of their roles and responsibilities. A calm and organized approach, coupled with a strong reliance on established procedures, helps maintain control and efficiency under pressure.
Q 27. Describe your experience with team collaboration in SIGINT/EW projects.
Team collaboration is essential in SIGINT/EW. My experience includes working in diverse teams, each possessing a unique blend of skills and expertise. I’ve actively participated in projects requiring seamless collaboration across different disciplines – from signal processing engineers to intelligence analysts. I believe in fostering a collaborative environment through open communication, mutual respect, and a shared understanding of goals. I contribute by actively sharing my knowledge, providing constructive feedback, and leveraging the strengths of each team member. I value the contributions of every member and actively work to ensure a supportive and inclusive team dynamic. In one specific instance, our team successfully identified a sophisticated enemy communication network through a combined effort where different skill sets (signal analysis, network mapping, linguistic analysis) were perfectly integrated.
Q 28. How do you approach problem-solving in a complex SIGINT/EW scenario?
Approaching problem-solving in a complex SIGINT/EW scenario requires a structured and systematic approach. My methodology typically begins with clearly defining the problem and identifying the available data. I then proceed with a thorough analysis of the data, looking for patterns and anomalies. Next, I develop and evaluate multiple hypotheses to explain the observed phenomena. This phase often involves employing various analytical tools and techniques. Crucially, I constantly iterate and refine my hypotheses based on new data and insights, and continually validate my findings. This iterative process, combined with clear documentation and communication with the team, ensures that the solution is both accurate and effective. Finally, I always consider the implications of the findings and develop actionable recommendations.
Key Topics to Learn for SIGINT/EW Tactics and Procedures Interview
- SIGINT Collection Methods: Understanding various SIGINT collection platforms (e.g., satellite, airborne, ground-based), their capabilities, limitations, and operational considerations. Explore the trade-offs between different collection methods in various operational scenarios.
- EW Principles and Techniques: Mastering the fundamentals of electronic warfare, including jamming, deception, and electronic protection. Analyze practical applications of EW techniques to counter adversary SIGINT capabilities and enhance operational security.
- SIGINT Processing and Exploitation: Familiarize yourself with the process of analyzing intercepted signals, identifying patterns, and extracting actionable intelligence. Consider the challenges involved in signal processing and data analysis in complex operational environments.
- SIGINT/EW Integration and Coordination: Understand how SIGINT and EW capabilities are integrated to support broader operational objectives. Explore collaborative strategies and communication protocols necessary for effective coordination between SIGINT and EW teams.
- Threat Modeling and Vulnerability Analysis: Develop a strong understanding of how adversaries employ SIGINT and EW techniques, and how to mitigate associated risks. Practice analyzing vulnerabilities in communication systems and developing countermeasures.
- Ethical and Legal Considerations: Grasp the ethical and legal implications of SIGINT and EW operations, including adherence to national and international laws and regulations. Understand the importance of responsible data handling and privacy protection.
- Mission Planning and Execution: Develop an understanding of the planning and execution phases of SIGINT/EW missions, from initial requirements gathering to post-mission analysis. Consider the role of risk assessment and contingency planning.
Next Steps
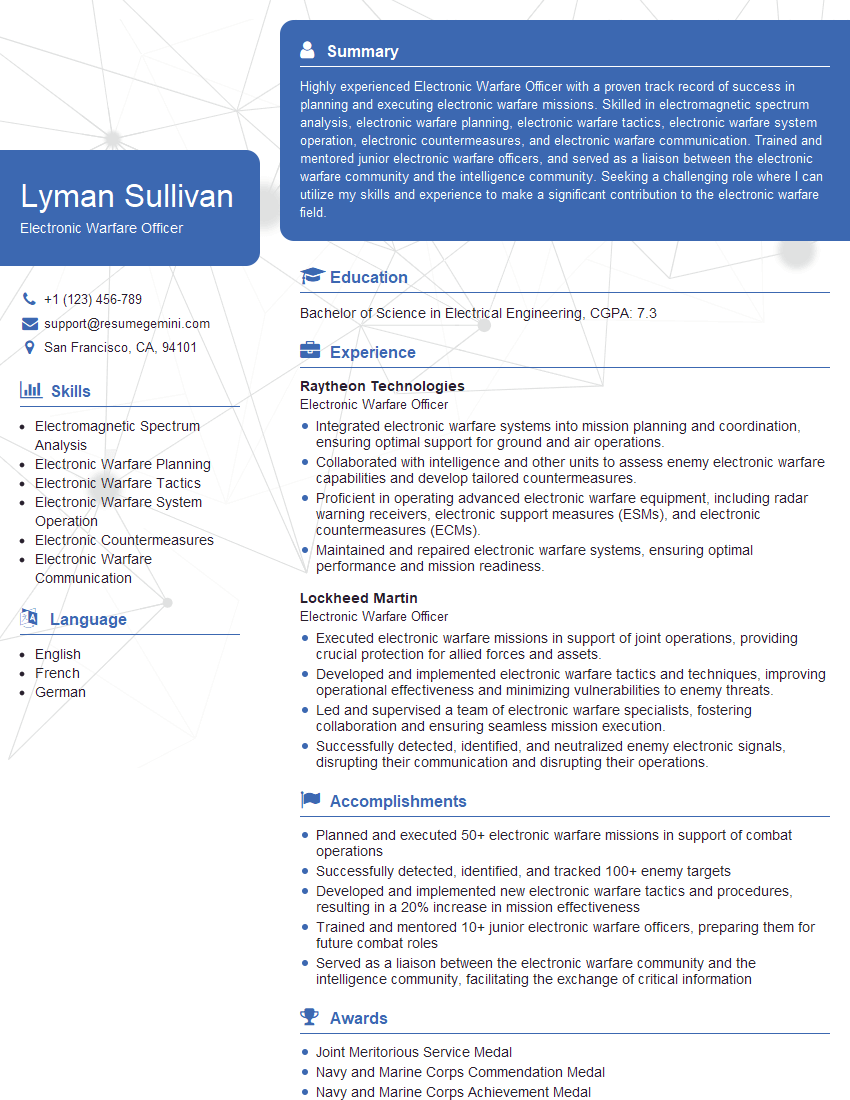
Mastering SIGINT/EW Tactics and Procedures is crucial for a successful and rewarding career in this dynamic field. It demonstrates a deep understanding of complex systems and your ability to contribute meaningfully to national security. To significantly boost your job prospects, crafting an ATS-friendly resume is essential. This ensures your qualifications are effectively communicated to potential employers. We strongly recommend using ResumeGemini, a trusted resource for building professional resumes that highlight your skills and experience. ResumeGemini provides examples of resumes tailored to SIGINT/EW Tactics and Procedures, further enhancing your preparation.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Very informative content, great job.
good